CCNA模拟测试(A)
思科认证CCNA认证试题和答案中文版

思科认证CCNA认证试题和答案中文版思科认证CCNA认证试题和答案中文版想要获得思科认证,首先要参加由思科推荐并授权的培训中心(Cisco Training Partner,简称CTP)所开设的培训课程。
完成学业后再到由全球考试机构Sylvan Prometric授权的.考试中心参加由思科指定的科目的认证考试。
通过指定的系列科目考试后,学员就可以获得相应分支系列等级的资格认证。
下面是店铺为大家搜集的相关试题,供大家参考练习。
16、路由器A串口0配置如下interface serial0link-protocol pppppp pap local-user huawei password simple quidwayip address 2.2.2.1 255.0.0.0路由器B串口及全局配置如下local-user huawei service-type ppp password simple quidway!interface serial0link-protocol pppppp authentication-mode papip address 2.2.2.2 255.0.0.0当两台路由器串口0相连时,两台路由器是否可以连接到对端()(A) 能(B) 不能答案:A17、关于千兆以太网,以下说法正确的是( )(A) IEEE802.3ab定义了千兆以太网(B) 在同一冲突域中,千兆以太网不允许中继器的互连(C) IEEE802.3z专门定义了千兆以太网在双绞线上的传输标准(D) 千兆以太网支持网络速率的自适应,可以与快速以太网自动协商传输速率答案:AB参考知识点:华为3com认证教材第一册3-8页18、高层的协议将数据传递到网络层后,形成( ),而后传送到数据链路层(A) 数据帧(B) 信元(C) 数据包(D) 数据段答案:C参考知识点:华为3com认证教材第一册1-20页19、在路由器上配置帧中继静态map必须指定( )参数(A) 本地的DLCI(B) 对端的DLCI(C) 本地的协议地址(D) 对端的协议地址答案:AD20、路由器的主要性能指标不包括( )(A) 延迟(B) 流通量(C) 帧丢失率(D) 语音数据压缩比答案:D【思科认证CCNA认证试题和答案中文版】。
完整版CCNA测试题库及答案

完整版CCNA测试题库及答案描述载波侦听多路由访问/冲突检测(CSMA/CD)的工作原理。
CSMA/CD是一种帮助设备均衡共享带宽的协议,可避免两台设备同时在网络介质上传输数据。
虽然他不能消除冲突,但有助于极大的减少冲突,进而避免重传,从而提高所的设备的数据传输效率。
区分半双工和全双工通信。
并指出两种方法的需求。
与半双工以太网使用一对导线不同,全双工以太网使用两队导线,全双工使用不同的导线来消除冲突,从而允许同时发送和接收数据,而半双工可接收或发送数据,但不能同时接收和发送数据,且仍会出现冲突。
要使用全双工,电缆两端的设备都必须支持全双工,并配置成一全双模式运行。
描述MAC地址的组成部分以及各部分包含的信息。
MAC(硬件)地址时一种使用十六进制表示的地址,长48位(6B)。
其中前24位(3B)称为OUI(Organizationally Unique Idebtifier,组织唯一表示符),有IEEE分配给NIC制造商;余下的部分呢唯一地标识了NIC识别十进制数对应的二进制值和十六进制值。
用这三种格式之一表示的任何数字都可以转换为其他两种格式,能够执行这种转换对理解IP地址和子网划分至关重要。
识别以太网帧中与数据链路层相关的字段。
在以太网中,与数据链路层相关的字段包括前导码,帧其实位置分隔符,目标MAC地址,源MAC地址,长度或者类型以及帧校验序列。
识别以太网布线相关的IEEE标准。
这些标准描述了各种电缆类型的功能和物理特征,包括(但不限于)10Base2、10Base5和10BaseT。
区分以太网电缆类型及其用途。
以太网电缆分3种:直通电缆,用于将PC或路由器的以太网接口连接到集线器或交换机;交叉电缆。
用于将集线器连接到集线器,集线器连接到交换机,交换机连接到交换机以及PC连接到PC;反转电缆,用于PC和路由器或交换机之间建立控制台连接。
描述数据封装过程及其在分组创建中的作用。
数据封装指的是在OSI模型各层给数据添加信息的过程,也成为分组创建。
CISCO模拟试题-CCNA考试自测题1
CISCO模拟试题:CCNA考试自测题1CISCO模拟试题:CCNA考试自测题1CISCO模拟试题:CCNA考试自测题11) match the following application layer services to their corresponding transport layer protocol port. (匹配下列的应用层服务和它们对应的传输层协议端口):a. smtp 1. tcp/23b. ftp 2. tcp/25c. tftp 3. tcp/80d. te l n e t 4. tcp/21e. http 5. udp/69f. dns 6. tcp/532) which osi reference model layer does telnet function at (te l n e t在哪一个o s i参考模型层运作)?a. transport 下载b. networkc. sessiond. application3) how many layers does the tcp/ip protocol suite have, compared to the osi reference model (和o s i参考模型相比,t c p / i p协议具有几层)?a. tcp model has 4, osi model has 6b. tcp model has 7, osi model has 8c. tcp model has 4, osi model has 7d. tcp model has 7, osi model has 44) the tcp/ip protocol suite has a formal session layer that includes netbios、rpcs and tli functions (tcp/ip协议套件具有包含n e t b i o s、r p c和t l i功能的一个正式的会话层)。
ccnaa
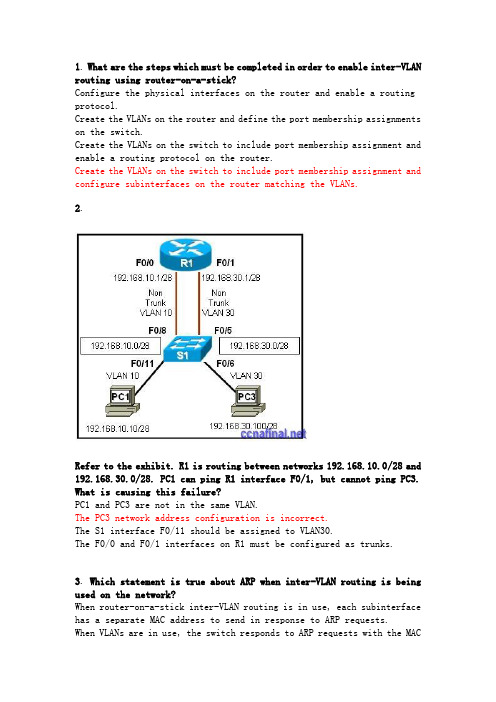
1. What are the steps which must be completed in order to enable inter-VLAN routing using router-on-a-stick?Configure the physical interfaces on the router and enable a routing protocol.Create the VLANs on the router and define the port membership assignments on the switch.Create the VLANs on the switch to include port membership assignment and enable a routing protocol on the router.Create the VLANs on the switch to include port membership assignment and configure subinterfaces on the router matching the VLANs.2.Refer to the exhibit. R1 is routing between networks 192.168.10.0/28 and 192.168.30.0/28. PC1 can ping R1 interface F0/1, but cannot ping PC3. What is causing this failure?PC1 and PC3 are not in the same VLAN.The PC3 network address configuration is incorrect.The S1 interface F0/11 should be assigned to VLAN30.The F0/0 and F0/1 interfaces on R1 must be configured as trunks.3. Which statement is true about ARP when inter-VLAN routing is being used on the network?When router-on-a-stick inter-VLAN routing is in use, each subinterface has a separate MAC address to send in response to ARP requests.When VLANs are in use, the switch responds to ARP requests with the MACaddress of the port to which the PC is connected.When router-on-a-stick inter-VLAN routing is in use, the router returns the MAC address of the physical interface in response to ARP requests. When traditional inter-VLAN routing is in use, devices on all VLANs use the same physical router interface as their source of proxy ARP responses.4. In which situation could individual router physical interfaces be used for InterVLAN routing, instead of a router-on-a-stick configuration?a network with more than 100 subnetworksa network with a limited number of VLANsa network with experienced support personnela network using a router with one LAN interface5.Refer to the exhibit. Switch1 is correctly configured for the VLANs that are displayed in the graphic. The configuration that is shown was applied to RTA to allow for interVLAN connectivity between hosts attached to Switch1. After testing the network, the administrator logged the following report:Hosts within each VLAN can communicate with each other.Hosts in VLAN5 and VLAN33 are able to communicate with each other. Hosts connected to Fa0/1 through Fa0/5 do not have connectivity to host in other VLANs.Why are hosts connected to Fa0/1 through Fa0/5 unable to communicate with hosts in different VLANs?The router interface is shut down.The VLAN IDs do not match the subinterface numbers.All of the subinterface addresses on the router are in the same subnet. The router was not configured to forward traffic for VLAN2.The physical interface, FastEthernet0/0, was not configured with an IP address.6. What is important to consider while configuring the subinterfaces ofa router when implementing inter-VLAN routing?The physical interface must have an IP address configured.The subinterface numbers must match the VLAN ID number.The no shutdown command must be given on each subinterface.The IP address of each subinterface must be the default gateway address for each VLAN subnet.7.Refer to the exhibit. Which two statements are true about the operation of the subinterfaces? (Choose two.)Incoming traffic that has a VLAN ID of 2 is processed by subinterface fa0/0.2.Incoming traffic with VLAN ID 0 is processed by interface fa0/0. Subinterfaces use unique MAC addresses by adding the 802.1Q VLAN ID to the hardware address.Traffic inbound on this router is processed by different subinterfaces, depending on the VLAN from which the traffic originated.Reliability of both subinterfaces is poor because ARP is timing out. Both subinterfaces remain up with line protocol up, even if fa0/0 line protocol is down.8.Refer to the exhibit. The commands for a router to connect to a trunked uplink are shown in the exhibit. A packet is received from IP address 192.168.1.54. The packet destination address is 192.168.1.120. What will the router do with this packet?The router will forward the packet out interface FastEthernet 0/1.1 tagged for VLAN 10.The router will forward the packet out interface FastEthernet 0/1.2 tagged for VLAN 60.The router will forward the packet out interface FastEthernet 0/1.3 tagged for VLAN 120.The router will not process the packet since the source and destination are on the same subnet.The router will drop the packet since no network that includes the source address is attached to the router.9.Refer to the exhibit. PC1 has attempted to ping PC2 but has been unsuccessful. What could account for this failure?PC1 and R1 interface F0/0.1 are on different subnets.The encapsulation is missing on the R1 interface F0/0.An IP address has not been assigned to the R1 physical interface.The encapsulation command on the R1 F0/0.3 interface is incorrect. 10.Refer to the exhibit. What two conclusions can be drawn from the output that is shown? (Choose two.)The no shutdown command has not been issued on the FastEthernet 0/0 interface.Both of the directly connected routes that are shown will share the same physical interface of the router.A routing protocol must be configured on the network in order for the inter-VLAN routing to be successful.Inter-VLAN routing between hosts on the 172.17.10.0/24 and 172.17.30.0/24 networks is successful on this network.Hosts in this network must be configured with the IP address that is assigned to the router physical interface as their default gateway.11.Refer to the exhibit. Which three statements describe the network design shown in the exhibit? (Choose three.)This design will not scale easily.The router merges the VLANs into a single broadcast domain.This design uses more switch and router ports than are necessary.This design exceeds the maximum number of VLANs that can be attached to a switch.This design requires the use of the ISL or 802.1q protocol on the links between the switch and the router.If the physical interfaces between the switch and router are operational, the devices on the different VLANs can communicate through the router.12. Devices on the network are connected to a 24-port Layer 2 switch that is configured with VLANs. Switch ports 0/2 to 0/4 are assigned to VLAN 10. Ports 0/5 to 0/8 are assigned to VLAN 20, and ports 0/9 to 0/12 are assigned to VLAN 30. All other ports are assigned to the default VLAN. Which solution allows all VLANs to communicate between each other while minimizing the number of ports necessary to connect the VLANs? Configure ports 0/13 to 0/16 with the appropriate IP addresses to perform routing between VLANs.Add a router to the topology and configure one FastEthernet interface on the router with multiple subinterfaces for VLANs 1, 10, 20, and 30.Obtain a router with multiple LAN interfaces and configure each interface for a separate subnet, thereby allowing communication between VLANs. Obtain a Layer 3 switch and configure a trunk link between the switch and router, and configure the router physical interface with an IP address on the native VLAN.13.Refer to the exhibit. Port Fa0/0 on router R1 is connected to port Fa0/1 on switch S1. After the commands shown are entered on both devices, the network administrator determines that the devices on VLAN 2 are unable to ping the devices on VLAN 1. What is the likely problem?R1 is configured for router-on-a-stick, but S1 is not configured for trunking.R1 does not have the VLANs entered in the VLAN database.Spanning Tree Protocol is blocking port Fa0/0 on R1.The subinterfaces on R1 have not been brought up with the no shutdown command yet.14.A router has two FastEthernet interfaces and needs to connect to four VLANs in the local network. How can this be accomplished using the fewest number of physical interfaces without unnecessarily decreasing network performance?Implement a router-on-a-stick configuration.Add a second router to handle the inter-VLAN traffic.Use a hub to connect the four VLANS with a FastEthernet interface on the router.Interconnect the VLANs via the two additional FastEthernet interfaces.15. What distinguishes traditional routing from router-on-a-stick? Traditional routing is only able to use a single switch interface. Router-on-a-stick can use multiple switch interfaces.Traditional routing requires a routing protocol. Router-on-a-stick only needs to route directly connected networks.Traditional routing uses one port per logical network. Router-on-a-stick uses subinterfaces to connect multiple logical networks to a single router port.Traditional routing uses multiple paths to the router and therefore requires STP. Router-on-a-stick does not provide multiple connections and therefore eliminates the need for STP.16. What two statements are true regarding the use of subinterfaces for inter-VLAN routing? (Choose two.)subinterfaces have no contention for bandwidthmore switch ports required than in traditional inter-VLAN routing fewer router ports required than in traditional inter-VLAN routing simpler Layer 3 troubleshooting than with traditional inter-VLAN routing less complex physical connection than in traditional inter-VLAN routing17. Which three elements must be used when configuring a router interface for VLAN trunking? (Choose three.)one subinterface per VLANone physical interface for each subinterfaceone IP network or subnetwork for each subinterfaceone trunked link per VLANa management domain for each subinterfacea compatible trunking protocol encapsulation for each subinterface18.Refer to the exhibit. The network administrator correctly configures RTA to perform inter-VLAN routing. The administrator connects RTA to port 0/4 on SW2, but inter-VLAN routing does not work. What could be the possible cause of the problem with the SW2 configuration?Port 0/4 is not active.Port 0/4 is not a member of VLAN1.Port 0/4 is configured in access mode.Port 0/4 is using the wrong trunking protocol.19. Which two statements are true about the interface fa0/0.10 command? (Choose two.)The command applies VLAN 10 to router interface fa0/0.The command is used in the configuration of router-on-a-stick inter-VLAN routing.The command configures a subinterface.The command configures interface fa0/0 as a trunk link.Because the IP address is applied to the physical interface, the command does not include an IP address.20.Refer to the exhibit. All devices are configured as shown in the exhibit. PC2 can successfully ping the F0/0 interface on R1. PC2 cannot ping PC1. What might be the reason for this failure?R1 interface F0/1 has not been configured for subinterface operation. S1 interface F0/6 needs to be configured for operation in VLAN10.S1 interface F0/8 is in the wrong VLAN.S1 port F0/6 is not in VLAN10。
CCNA测试题
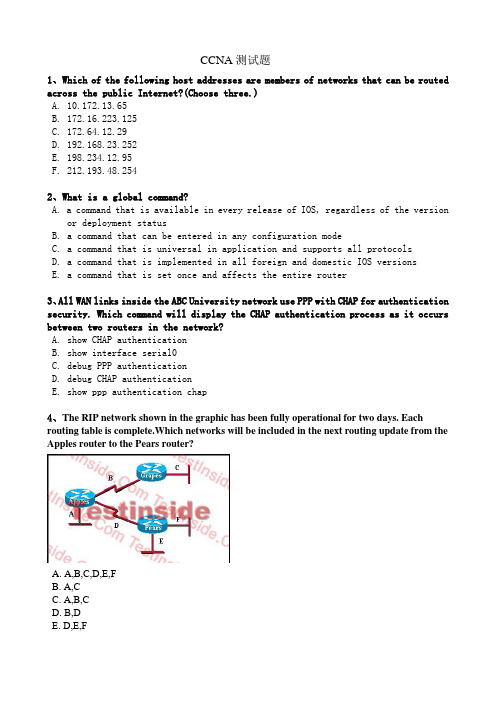
CCNA测试题1、Which of the following host addresses are members of networks that can be routed across the public Internet?(Choose three.)A. 10.172.13.65B. 172.16.223.125C. 172.64.12.29D. 192.168.23.252E. 198.234.12.95F. 212.193.48.2542、What is a global command?A. a command that is available in every release of IOS, regardless of the versionor deployment statusB. a command that can be entered in any configuration modeC. a command that is universal in application and supports all protocolsD. a command that is implemented in all foreign and domestic IOS versionsE. a command that is set once and affects the entire router3、All WAN links inside the ABC University network use PPP with CHAP for authentication security. Which command will display the CHAP authentication process as it occurs between two routers in the network?A. show CHAP authenticationB. show interface serial0C. debug PPP authenticationD. debug CHAP authenticationE. show ppp authentication chap4、The RIP network shown in the graphic has been fully operational for two days. Each routing table is complete.Which networks will be included in the next routing update from the Apples router to the Pears router?A. A,B,C,D,E,FB. A,CC. A,B,CD. B,DE. D,E,F5、How should a router that is being used in a Frame Relay network be configured to avoid split horizon issues from preventing routing updates?A. Configure a separate sub-interface for each PVC with a unique DLCI and subnetassigned to thesub-interface.B. Configure each Frame Relay circuit as a point-to-point line to support multicastand broadcast traffic.C. Configure many sub-interfaces on the same subnet.D. Configure a single sub-interface to establish multiple PVC connections tomultiple remoterouter interfaces.6、What three pieces of information can be used in an extended access list to filter traffic? (Choose three.)A. protocolB. VLAN numberC. TCP or UDP port numbersD. source switch port numberE. source IP address and destination IP addressF. source MAC address and destination MAC address7、Refer to the exhibit. A network technician enters the following lines into the router.What is the effect of this configuration?A. The change has no effect on the packets being filtered.B. All traffic from the 192.168.254.0 LAN to the Internet is permitted.C. Web pages from the Internet cannot be accessed by hosts in the 192.168.254.0 LAN.D. No hosts in the 192.168.254.0 LAN except 192.168.254.7 can access web pages from theInternet.8、Refer to the exhibit. The partial frame in the graphic represents select header information within a framearriving at a destination host. What can be determined from this information?A. The source host is a Telnet server.B. This frame contains the first segment in a Telnet session.C. The Layer 2 address of the source host is 192.168.14.2.D. The local host has received 42,335 bytes from the remote host as a part of thisconversation.9、Refer to the exhibit. The technician wants to upload a new IOS in the router while keeping the existing IOS.What is the maximum size of an IOS file that could be loaded if the original IOS is also kept in flash?A. 3 MBB. 4 MBC. 5 MBD. 7 MBE. 8 MB10、Refer to the exhibit. To what does the 128 refer in the router output O 192.168.12.240/30 [110/128] via 192.168.12.233,00:35:36, Serial 0?A. OSPF costB. OSPF priorityD. OSPF ID numberE. OSPF administrative distance11、Refer to the exhibit. Workstation A must be able to telnet to switch SW-A through router RTA for management purposes. What must be configured for this connection to be successful?A. VLAN 1 on RTAB. default gateway on SW-AC. IP routing on SW-AD. cross-over cable connecting SW-A and RTA12、Refer to the exhibit. A technician is testing connection problems in the internetwork. What is the problem indicated by the output from HostA?A. The routing on Router2 is not functioning properly.B. An access list is applied to an interface of Router3.C. The Fa0/24 interface of Switch1 is down.D. The gateway address of HostA is incorrect or not configured.13、A network administrator needs to force a high-performance switch that is located in the MDF to become the root bridge for a redundant path switched network. What can be done to ensure that this switch assumes the role as root bridge?A. Establish a direct link from the switch to all other switches in the network.B. Assign the switch a higher MAC address than the other switches in the networkhave.C. Configure the switch so that it has a lower priority than other switches in thenetwork.D. Configure the switch for full-duplex operation and configure the other switchesfor half-duplex operation.E. Connect the switch directly to the MDF router, which will force the switch toassume the role of root bridge.14、Which commands are required to properly configure a router to run OSPF and to add network 192.168.16.0/24 to OSPF area 0? (Choose two.)A. Router(config)# router ospf 0B. Router(config)# router ospf 1C. Router(config)# router ospf area 0D. Router(config-router)# network 192.168.16.0 0.0.0.255 0E. Router(config-router)# network 192.168.16.0 0.0.0.255 area 0F. Router(config-router)# network 192.168.16.0 255.255.255.0 area 015、Refer to graphic and examine the output from the London switch . What VTP functions will this switch perform?A. create, change, and delete VLANs for the VTP domainB. learn and save VTP configuration information in the running configuration onlyC. forward VTP configuration informationD. backup the VTP database for the closest VTP serverE. prevent VTP information from reaching workgroup switches16、Which wild card mask will enable a network administrator to permit access to the Internet for only hosts that are assigned an address in the range of 192.168.8.0 through 192.168.15.255?A. 0.0.0.0C. 0.0.255.255D. 0.0.7.255E. 0.0.3.25517、Refer to the exhibit. Based on the exhibited routing table, how will packets from a host within the 192.168.10.192/26 LAN be forwarded to 192.168.10.1?A. The router will forward packets from R3 to R2 to R1.B. The router will forward packets from R3 to R1 to R2.C. The router will forward packets from R3 to R2 to R1 AND from R3 to R1.D. The router will forward packets from R3 to R1.18、Refer to the topology shown in the exhibit. Which ports will be STP designated ports if all the links are operating at the same bandwidth? (Choose three.)A. Switch A - Fa0/0B. Switch A - Fa0/1C. Switch B - Fa0/019、Refer to the exhibit. Switch1 sends a VTP advertisement and Switch2 receives it. Which statement accurately describes how Switch2 will process this advertisement?A. Switch2 will ignore the summary advertisement.B. Switch2 will delete all its VLANs because it has a lower revision number thanSwitch1.C. Switch2 will increment the VTP revision number and forward the advertisement.D. Switch2 will create two new VLANs in response to the information contained in theadvertisement20、Refer to the exhibit. Host A needs to send data to Host B. Which Layer 2 and Layer 3 destination addresses will be used to send the data from Host A to Host B?A. 192.168.60.5 and 0011.43da.2c98B. 192.168.60.5 and 0007.0e56.ab2eC. 192.168.24.1 and 0007.0e56.ab2eD. 192.168.24.2 and 0007.0e84.acef21、Why has the network shown in the exhibit failed to converge?A. The no auto-summary command needs to be applied to the routers.B. The network numbers have not been properly configured on the routers.C. The subnet masks for the network numbers have not been properly configured.D. The autonomous system number has not been properly configured.E. The bandwidth values have not been properly configured on the serial interfaces22、Refer to the exhibit. After the power-on self test (POST), the system LED ofa Cisco 2950 switch turns amber.What is the status of the switch?A. The POST was successful.B. The switch has a problem with the internal power supply and needs an externalpower supply to be attached.C. POST failed and there is a problem that prevents the operating system of the switchfrom being loaded.D. The switch has experienced an internal problem but data can still be forwardedat a slower rate.E. The switch passed POST, but all the switch ports are busy.23、Refer to the exhibit. All switch ports are assigned to the correct VLANs, but none of the hosts connected to SwitchA can communicate with hosts in the same VLAN connected to SwitchB. Based on the output shown, what is the most likely problem?A. The access link needs to be configured in multiple VLANs.B. The link between the switches is configured in the wrong VLAN.C. The link between the switches needs to be configured as a trunk.D. VTP is not configured to carry VLAN information between the switches.E. Switch IP addresses must be configured in order for traffic to be forwarded betweenthe switches24、Two routers named Atlanta and Brevard are connected by their serial interfaces as shown in the exhibit, but there is no data connectivity between them. The Atlanta router is known to have a correct configuration. Given the partial configurations shown in the exhibit, what is the problem on the Brevard router that is causing the lack of connectivity?A. A loopback is not set.B. The IP address is incorrect.C. The subnet mask is incorrect.D. The serial line encapsulations are incompatible.E. The maximum transmission unit (MTU) size is too large.F. The bandwidth setting is incompatible with the connected interface.。
CCNA测试题英文版(题目)
CCNA Test:Selection:1. A receiving host computes the checksum on a frame and determines that determinesthat the frame is damaged. The frame is then discarded. At witch OSI layer did this happen?A:session B:network C:physical D:data link E:transport2.Where does routing occur within the DoD TCP/IP reference model?A:application B:internet C:network D:transport3.Which command can be a router to verify the layer 3 path to a host?A:traceroute address B:tracert address C:ssh address D:telnet address 4.Which are valid modes for a switch port used as a VLAN trunk?(Choose Three)A:transparent B:auto C:on D:Desirable E:blocking F:forwarding5.What is on benefit of PVST+?A:PVST+ reduces the CPU cycles for all the switches in the networkB:PVST+ automatically selects the root bridge location, to provide optimizedbandwidth usage.C:PVST+ allow the root switch location to be optimized per vlan.D:PVST+ supports Layers 3 load balancing loops6.If IP routing is enable, which command that you can configure a default-router in aroute?A:ip default-gateway 0.0.0.0B:ip route 172.16.2.1 0.0.0.0 0.0.0.0C:ip default-route 0.0.0.0 0.0.0.0 172.16.2.1D:ip route 0.0.0.0 0.0.0.0 172.16.2.17.Which command is userd to display the collection of OSPF link states?A:show ip ospf lsa databaseB:show ip ospf link-stateC:show ip ospf neighborsD:show ip ospf database8.Which command displays IOS version?A:show protocolB:show processC:show systemD:show version9.Which is the update time and the Multicast update address of RIPv2 Protocol?A:30s,255.255.255.255B:30s:224.0.0.9C:10s:255.255.255.255D:10s:224.0.0.910.Which command enable PVST+ on a switch?A:spanning-tree mode rapid-pvstB:spanning-tree uplinkfastC:spanning-tree backbonefastD:spanning-tree mode mstCompletion:1.Write out administrate distance of the following routing protocol:Connect_____、Static_____、RIP_____、OSPF_____、interior EIGRP_____,External EIGRP_____.2.Which modes of a switch in VTP domain?And what it is ?__________________________.3.Which command used to copy IOS file to TFTP server?____________________________.4.The largest hop of Routing Information Protocol is________________________________.5.Which command can configure the routing function in a Layer 3 Switch?______________.Question:Refer to the exhibit.Each of these four switches has been configured with a hostname, as well as being configured to run RSTP.No other configuration changes have been made. Please Find out the root bridge , root port ,designed port, blocking port of this spanning-tree.Configuration:Refer to the exhibit.What commands must be configured on the 2950 switch and the router to allow communication between host 1 and host 2?Please write out the configuration of the 2950 switch and the router in detail.。
ccna考试题库最新版
ccna考试题库最新版CCNA(Cisco Certified Network Associate)认证是全球范围内最受欢迎的网络工程师认证之一,具备CCNA认证可以证明一个人在建立、规划、运行、安装和配置中等规模的局域网和广域网方面的专业知识。
为了帮助广大考生顺利通过CCNA考试,不断更新的CCNA考试题库至关重要。
以下是最新版本的CCNA考试题库,希望对考生们有所帮助。
第一部分:网络基础知识1. 什么是OSI七层模型?简要介绍每一层的功能。
2. TCP和UDP之间有哪些区别?请分别举例说明。
3. 什么是IP地址?IP地址的类型有哪些?请列举并简要介绍各自的特点。
4. 什么是子网掩码?为什么在网络中使用子网掩码?5. 简述常见的网络设备有哪些,以及各自的功能与作用。
第二部分:路由和交换技术1. 路由器和交换机之间有何区别?请进行比较并指出各自的优势和劣势。
2. 什么是VLAN?VLAN的作用及在网络中的应用场景是什么?3. OSPF和EIGRP是两种常见的路由协议,请比较它们的特点并举例说明。
4. 请解释静态路由和动态路由的概念以及在网络中的应用。
5. 交换机在网络中扮演什么角色?交换机的MAC地址表是如何工作的?第三部分:网络安全和管理1. 网络安全的重要性是什么?请列举几种常见的网络安全威胁并介绍应对策略。
2. 什么是ACL(访问控制列表)?ACL的作用是什么?请给出一个ACL的配置示例。
3. VPN是什么?VPN的工作原理及在企业网络中的应用。
4. SNMP是网络管理中常用的协议,它的作用是什么?请解释SNMP中的几个重要概念。
5. 如何保护无线网络的安全?请列举几种方法。
第四部分:WAN技术1. 什么是WAN?WAN的主要特点是什么?2. PPP协议和HDLC协议分别是什么?请比较它们的异同。
3. 什么是Frame Relay?Frame Relay的工作原理及在WAN中的应用。
4. 请解释T1和E1的概念,以及它们在传输速率和应用方面的差异。
新10月CCNA题库word版1~100题共24页
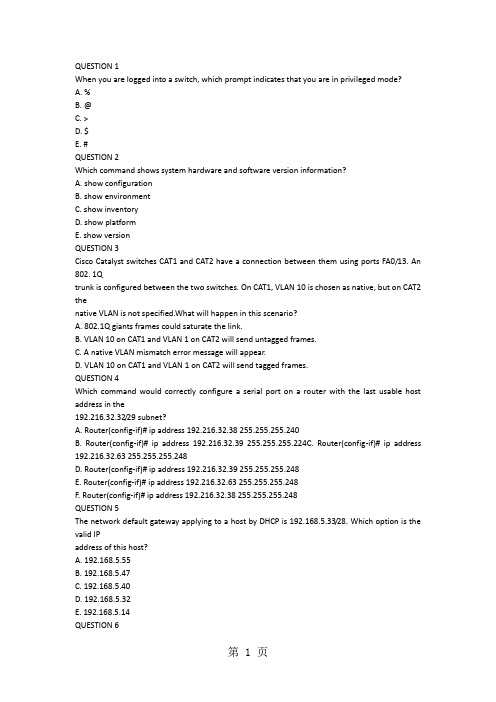
QUESTION 1When you are logged into a switch, which prompt indicates that you are in privileged mode?A. %B. @C. >D. $E. #QUESTION 2Which command shows system hardware and software version information?A. show configurationB. show environmentC. show inventoryD. show platformE. show versionQUESTION 3Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802. 1Qtrunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 thenative VLAN is not specified.What will happen in this scenario?A. 802.1Q giants frames could saturate the link.B. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send untagged frames.C. A native VLAN mismatch error message will appear.D. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send tagged frames.QUESTION 4Which command would correctly configure a serial port on a router with the last usable host address in the192.216.32.32/29 subnet?A. Router(config-if)# ip address 192.216.32.38 255.255.255.240B. Router(config-if)# ip address 192.216.32.39 255.255.255.224C. Router(config-if)# ip address 192.216.32.63 255.255.255.248D. Router(config-if)# ip address 192.216.32.39 255.255.255.248E. Router(config-if)# ip address 192.216.32.63 255.255.255.248F. Router(config-if)# ip address 192.216.32.38 255.255.255.248QUESTION 5The network default gateway applying to a host by DHCP is 192.168.5.33/28. Which option is the valid IPaddress of this host?A. 192.168.5.55B. 192.168.5.47C. 192.168.5.40D. 192.168.5.32E. 192.168.5.14QUESTION 6Which two addresses can be assigned to a host with a subnet mask of 255.255.254.0? (Choose two.)A. 113.10.4.0B. 186.54.3.0C. 175.33.3.255D. 26.35.2.255E. 17.35.36.0QUESTION 7The network administrator has asked you to check the status of the workstation's IP stack by pinging theloopback address. Which address would you ping to perform this task?A. 10.1.1.1B. 127.0.0.1C. 192.168.0.1D. 239.1.1.1QUESTION 8Workstation A has been assigned an IP address of 192.0.2.24/28. Workstation B has been assigned an IPaddress of 192.0.2.100/28. The two workstations are connected with a straight-through cable. Attempts toping between the hosts are unsuccessful. What two things can be done to allow communications betweenthe hosts? (Choose two.)A. Replace the straight-through cable with a crossover cable.B. Change the subnet mask of the hosts to /25.C. Change the subnet mask of the hosts to /26.D. Change the address of Workstation A to 192.0.2.15.E. Change the address of Workstation B to 192.0.2.111.QUESTION 9Your ISP has given you the address 223.5.14.6/29 to assign to your router's interface. They have alsogiven you the default gateway address of 223.5.14.7. After you have configured the address, the router isunable to ping any remote devices. What is preventing the router from pinging remote devices?A. The default gateway is not an address on this subnet.B. The default gateway is the broadcast address for this subnet.C. The IP address is the broadcast address for this subnet.D. The IP address is an invalid class D multicast address.QUESTION 10Which command is used to copy the configuration from RAM into NVRAM?A. copy running-config startup-configB. copy startup-config: running-config:C. copy running config startup configD. copy startup config running configE. write terminalQUESTION 11Which command is used to load a configuration from a TFTP server and merge the configuration intoRAM?A. copy running-config: TFTP:B. copy TFTP: running-configC. copy TFTP: startup-configD. copy startup-config: TFTP:QUESTION 12A system administrator types the command to change the hostname of a router. Where on the Cisco IFS isthat change stored?A. NVRAMB. RAMC. FLASHD. ROME. PCMCIAQUESTION 13Which command is used to configure a default route?A. ip route 172.16.1.0 255.255.255.0 0.0.0.0B. ip route 172.16.1.0 255.255.255.0 172.16.2.1C. ip route 0.0.0.0 255.255.255.0 172.16.2.1D. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 14If IP routing is enabled, which two commands set the gateway of last resort to the default gateway?(Choose two.)A. ip default-gateway 0.0.0.0B. ip route 172.16.2.1 0.0.0.0 0.0.0.0C. ip default-network 0.0.0.0D. ip default-route 0.0.0.0 0.0.0.0 172.16.2.1E. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 15Which command would you configure globally on a Cisco router that would allow you to view directlyconnected Cisco devices?A. enable cdpB. cdp enableC. cdp runD. run cdpQUESTION 16Which command is used to see the path taken by packets across an IP network?A. show ip routeB. show routeC. tracerouteD. trace ip routeQUESTION 17Which command is used to debug a ping command?A. debug icmpB. debug ip icmpC. debug tcpD. debug packetQUESTION 18Which command displays CPU utilization?A. show protocolsB. show processC. show systemD. show versionQUESTION 19When configuring a serial interface on a router, what is the default encapsulation?A. atm-dxiB. frame-relayC. hdlcD. lapbE. pppQUESTION 20What must be set correctly when configuring a serial interface so that higher-level protocols calculate thebest route?A. bandwidthB. delayC. loadD. reliabilityQUESTION 21A company implements video conferencing over IP on their Ethernet LAN. The users notice that thenetwork slows down, and the video either stutters or fails completely. What is the most likely reason forthis?A. minimum cell rate (MCR)B. quality of service (QoS)C. modulationD. packet switching exchange (PSE)E. reliable transport protocol (RTP)QUESTION 22Which layer in the OSI reference model is responsible for determining the availability of the receivingprogram and checking to see if enough resources exist for that communication?A. transportB. networkC. presentationD. sessionE. applicationQUESTION 23Data transfer is slow between the source and destination. The quality of service requested by the transportlayer in the OSI reference model is not being maintained. To fix this issue, at which layer should thetroubleshooting process begin?A. presentationB. sessionC. transportD. networkE. physicalQUESTION 24Which protocols are found in the network layer of the OSI reference model and are responsible for pathdetermination and traffic switching?A. LANB. routingC. WAND. networkQUESTION 25Which command reveals the last method used to powercycle a router?A. show reloadB. show bootC. show running-configD. show versionQUESTION 26Which three options are valid WAN connectivity methods? (Choose three.)A. PPPB. WAPC. HDLCD. MPLSE. L2TPv3CCNA考试报名1700元7F. ATMQUESTION 27Refer to the exhibit. Which WAN protocol is being used?A. ATMB. HDLCC. Frame RelayD. PPPQUESTION 28What is the difference between a CSU/DSU and a modem?A. A CSU/DSU converts analog signals from a router to a leased line; a modem converts analog signalsfrom a router to a leased line.B. A CSU/DSU converts analog signals from a router to a phone line; a modem converts digital signalsfrom a router to a leased line.C. A CSU/DSU converts digital signals from a router to a phone line; a modem converts analog signalsfrom a router to a phone line.D. A CSU/DSU converts digital signals from a router to a leased line; a modem converts digital signalsfrom a router to a phone line.QUESTION 29A network administrator must configure 200 switch ports to accept traffic from only the currently attachedCCNA考试报名1700元8host devices. What would be the most efficient way to configure MAC-level security on all these ports?A. Visually verify the MAC addresses and then telnet to the switches to enter the switchport-port securitymac-address command.B. Have end users e-mail their MAC addresses. Telnet to the switch to enter the switchport-port securitymac-address command.C. Use the switchport port-security MAC address sticky command on all the switch ports that have enddevices connected to them.D. Use show mac-address-table to determine the addresses that are associated with each portand thenenter the commands on each switch for MAC address port-security.QUESTION 30When troubleshooting a Frame Relay connection, what is the first step when performing a loopback test?A. Set the encapsulation of the interface to HDLC.B. Place the CSU/DSU in local-loop mode.C. Enable local-loop mode on the DCE Frame Relay router.D. Verify that the encapsulation is set to Frame Relay.What occurs on a Frame Relay network when the CIR is exceeded?A. All TCP traffic is marked discard eligible.B. All UDP traffic is marked discard eligible and a BECN is sent.C. All TCP traffic is marked discard eligible and a BECN is sent.D. All traffic exceeding the CIR is marked discard eligible.QUESTION 32What are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two.)A. They create split-horizon issues.B. They require a unique subnet within a routing domain.C. They emulate leased lines.D. They are ideal for full-mesh topologies.E. They require the use of NBMA options when using OSPF.QUESTION 33Refer to the exhibit. Addresses within the range 10.10.10.0/24 are not being translated to the 1.128.0/16range. Which command shows if 10.10.10.0/24 are allowed inside addresses?A. debug ip natB. show access-listC. show ip nat translationD. show ip nat statisticsQUESTION 34A wireless client cannot connect to an 802.11b/g BSS with a b/g wireless card. The client section of theaccess point does not list any active WLAN clients. What is a possible reason for this?A. The incorrect channel is configured on the client.B. The client's IP address is on the wrong subnet.C. The client has an incorrect pre-shared key.D. The SSID is configured incorrectly on the client.QUESTION 35Which two features did WPAv1 add to address the inherent weaknesses found in WEP? (Choose two.)CCNA考试报名1700元10艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyA. a stronger encryption algorithmB. key mixing using temporal keysC. shared key authenticationD. a shorter initialization vectorE. per frame sequence countersQUESTION 36Which two wireless encryption methods are based on the RC4 encryption algorithm? (Choose two.)A. WEPB. CCKMC. AESD. TKIPE. CCMPQUESTION 37What are two characteristics of RIPv2? (Choose two.)A. classful routing protocolB. variable-length subnet masksC. broadcast addressingD. manual route summarizationE. uses SPF algorithm to compute pathQUESTION 38Which two Ethernet fiber-optic modes support distances of greater than 550 meters?A. 1000BASE-CXCCNA考试报名1700元11艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyB. 100BASE-FXC. 1000BASE-LXD. 1000BASE-SXE. 1000BASE-ZXQUESTION 39What two things will a router do when running a distance vector routing protocol? (Choose two.)A. Send periodic updates regardless of topology changes.B. Send entire routing table to all routers in the routing domain.C. Use the shortest-path algorithm to the determine best path.D. Update the routing table based on updates from their neighbors.E. Maintain the topology of the entire network in its database.QUESTION 40Refer to the exhibit. According to the routing table, where will the router send a packet destined for10.1.5.65?A. 10.1.1.2B. 10.1.2.2C. 10.1.3.3D. 10.1.4.4QUESTION 41Which command shows if an access list is assigned to an interface?A. show ip interface [interface] access-listsB. show ip access-lists interface [interface]C. show ip interface [interface]D. show ip access-lists [interface]QUESTION 42Refer to the exhibit. Which rule does the DHCP server use when there is an IP address conflict?A. The address is removed from the pool until the conflict is resolved.B. The address remains in the pool until the conflict is resolved.C. Only the IP detected by Gratuitous ARP is removed from the pool.D. Only the IP detected by Ping is removed from the pool.E. The IP will be shown, even after the conflict is resolved.QUESTION 43Refer to the exhibit. You are connected to the router as user Mike. Which command allows you to seeoutput from the OSPF debug command?A. terminal monitorB. show debuggingC. show sessionsD. show ip ospf interfaceQUESTION 44Refer to the exhibit. If number 2 is selected from the setup script, what happens when the user runs setupfrom a privileged prompt?A. Setup is additive and any changes will be added to the config script.B. Setup effectively starts the configuration over as if the router was booted for the first time.C. Setup will not run if an enable secret password exists on the router.D. Setup will not run, because it is only viable when no configuration exists on the router. QUESTION 45Refer to the exhibit. Which (config-router) command will allow the network represented on the interface tobe advertised by RIP?A. redistribute ethernet0B. network ethernet0CCNA考试报名1700元14艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyC. redistribute 10.12.0.0D. network 10.12.0.0QUESTION 46Refer to the exhibit. What information can be gathered from the output?A. One router is running RIPv1.B. RIP neighbor is 224.0.0.9.C. The network contains a loop.D. Network 10.10.1.0 is reachable.QUESTION 47Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to routerD. router to routerQUESTION 48Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to switchD. switch to routerQUESTION 49Which two statements describe the Cisco implementation of VLANs? (Choose two.)A. VLAN 1 is the default Ethernet VLAN.B. CDP advertisements are only sent on VLAN 1002.C. By default, the management VLAN is VLAN 1005.D. By default, the switch IP address is in VLAN 1005.E. VLAN 1002 through 1005 are automatically created and cannot be deleted.QUESTION 50Refer to the exhibit. What can be determined about the router from the console output?A. No configuration file was found in NVRAM.B. No configuration file was found in flash.C. No configuration file was found in the PCMCIA card.D. Configuration file is normal and will load in 15 seconds.QUESTION 52Refer to the exhibit. Which command would allow the translations to be created on the router?A. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 19B. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 19C. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 18D. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 18QUESTION 53Refer to the exhibit. An administrator pings the default gateway at 10.10.10.1 and sees the output asshown. At which OSI layer is the problem?A. data link layerB. application layerC. access layerD. session layerE. network layerQUESTION 54Refer to the exhibit. Which value will be configured for Default Gateway of the Local Area Connection?A. 10.0.0.0B. 10.0.0.254C. 192.223.129.0D. 192.223.129.254QUESTION 55Refer to the exhibit. The user at Workstation B reports that Server A cannot be reached. What is preventing Workstation B from reaching Server A?A. The IP address for Server A is a broadcast address.B. The IP address for Workstation B is a subnet address.C. The gateway for Workstation B is not on the same subnet.D. The gateway for Server A is not on the same subnet.QUESTION 56Refer to the exhibit. What does the (*) represent in the output?A. Packet is destined for a local interface to the router.B. Packet was translated, but no response was received from the distant device.C. Packet was not translated, because no additional ports are available.D. Packet was translated and fast switched to the destination.QUESTION 57Refer to the exhibit. What command sequence will enable PAT from the inside to outside network?A. (config) ip nat pool isp-net 1.2.4.2 netmask 255.255.255.0 overloadB. (config-if) ip nat outside overloadC. (config) ip nat inside source list 1 interface ethernet1 overloadD. (config-if) ip nat inside overloadQUESTION 58Refer to the exhibit. What will happen to HTTP traffic coming from the Internet that is destined for172.16.12.10 if the traffic is processed by this ACL?A. Traffic will be dropped per line 30 of the ACL.B. Traffic will be accepted per line 40 of the ACL.C. Traffic will be dropped, because of the implicit deny all at the end of the ACL.D. Traffic will be accepted, because the source address is not covered by the ACL.QUESTION 59Refer to the exhibit. Which statement describes the effect that the Router1 configuration has on devices inthe 172.16.16.0 subnet when they try to connect to SVR-A using Telnet or SSH?A. Devices will not be able to use Telnet or SSH.B. Devices will be able to use SSH, but not Telnet.C. Devices will be able to use Telnet, but not SSH.D. Devices will be able to use Telnet and SSH.QUESTION 60What are three advantages of VLANs? (Choose three.)A. VLANs establish broadcast domains in switched networks.B. VLANs utilize packet filtering to enhance network security.C. VLANs provide a method of conserving IP addresses in large networks.D. VLANs provide a low-latency internetworking alternative to routed networks.E. VLANs allow access to network services based on department, not physical location.F. VLANs can greatly simplify adding, moving, or changing hosts on the network.QUESTION 61An administrator would like to configure a switch over a virtual terminal connection from locations outsideof the local LAN. Which of the following are required in order for the switch to be configured from a remotelocation? (Choose two.)A. The switch must be configured with an IP address, subnet mask, and default gateway.B. The switch must be connected to a router over a VLAN trunk.C. The switch must be reachable through a port connected to its management VLAN.D. The switch console port must be connected to the Ethernet LAN.E. The switch management VLAN must be created and have a membership of at least one switch port.F. The switch must be fully configured as an SNMP agent.QUESTION 62Which of the following host addresses are members of networks that can be routed across the publicInternet? (Choose three.)A. 10.172.13.65B. 172.16.223.125C. 172.64.12.29D. 192.168.23.252E. 198.234.12.95F. 212.193.48.254QUESTION 63Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to networkhosts? (Choose three.)A. 15.234.118.63B. 92.11.178.93C. 134.178.18.56D. 192.168.16.87E. 201.45.116.159F. 217.63.12.192QUESTION 64Which of the following are benefits of VLANs? (Choose three.)A. They increase the size of collision domains.B. They allow logical grouping of users by function.C. They can enhance network security.D. They increase the size of broadcast domains while decreasing the number of collision domains.E. They increase the number of broadcast domains while decreasing the size of the broadcast domains.F. They simplify switch administration.Which router IOS commands can be used to troubleshoot LAN connectivity problems? (Choose three.)A. pingB. tracertC. ipconfigD. show ip routeE. winipcfgF. show interfacesQUESTION 67。
思科认证考试(CCNA)考试模拟题集锦(1-71题)及答案
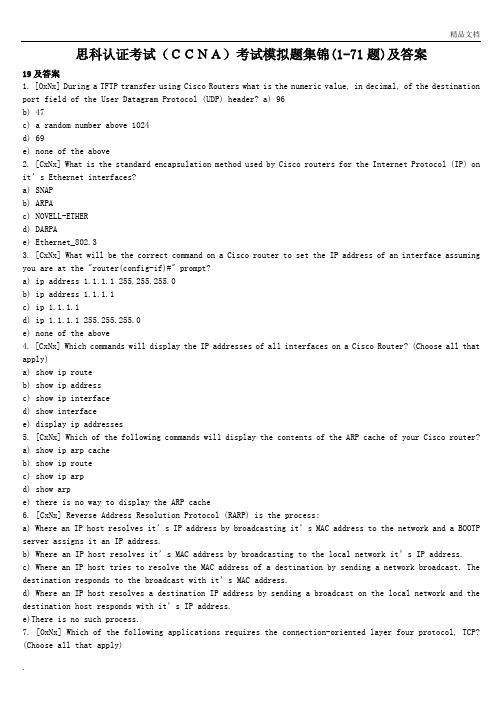
思科认证考试(CCNA)考试模拟题集锦(1-71题)及答案19及答案1. [OxNx] During a TFTP transfer using Cisco Routers what is the numeric value, in decimal, of the destination port field of the User Datagram Protocol (UDP) header? a) 96b) 47c) a random number above 1024d) 69e) none of the above2. [CxNx] What is the standard encapsulation method used by Cisco routers for the Internet Protocol (IP) on it’s Ethernet interfaces?a) SNAPb) ARPAc) NOVELL-ETHERd) DARPAe) Ethernet_802.33. [CxNx] What will be the correct command on a Cisco router to set the IP address of an interface assuming you are at the "router(config-if)#" prompt?a) ip address 1.1.1.1 255.255.255.0b) ip address 1.1.1.1c) ip 1.1.1.1d) ip 1.1.1.1 255.255.255.0e) none of the above4. [CxNx] Which commands will display the IP addresses of all interfaces on a Cisco Router? (Choose all that apply)a) show ip routeb) show ip addressc) show ip interfaced) show interfacee) display ip addresses5. [CxNx] Which of the following commands will display the contents of the ARP cache of your Cisco router?a) show ip arp cacheb) show ip routec) show ip arpd) show arpe) there is no way to display the ARP cache6. [CxNx] Reverse Address Resolution Protocol (RARP) is the process:a) Where an I P host resolves it’s IP address by broadcasting it’s MAC address to the network and a BOOTP server assigns it an IP address.b) Where an IP host resolves it’s MAC address by broadcasting to the local network it’s IP address.c) Where an IP host tries to resolve the MAC address of a destination by sending a network broadcast. The destination responds to the broadcast with it’s MAC address.d) Where an IP host resolves a destination IP address by sending a broadcast on the local network and the destination host responds with it’s IP address.e)There is no such process.7. [OxNx] Which of the following applications requires the connection-oriented layer four protocol, TCP? (Choose all that apply)a) Telnetb) FTPc) TFTPd) SNMPe) none of the above8. [RxNx] Which of the following are link state Routing Protocols.(Choose all that apply.)a) IPb) OSPFc) RIPd) EIGRPe) IS-IS9. [CxNx] Of the following commands, identify the correct one for clearing the IP arp table in memory of the router.a) clear ip arp-cacheb) clear ip arp-tablec) clear arp-cached) clear arp-tablee) clear arp-ram10. [CxNx] Which of the following explains the correct definition of administrative distance as it pertains to Cisco’s IOS?a) The process by which routers select an administrator for an autonomous system.b) The process where a router will select the best path to a destination network.c) The process where a router will distance itself from other routers due to it’s lack of administrative experience.d) The process where a router will prioritize routing protocols so that in the event two routing protocols have conflicting next hop addresses, the routing protocol with the lowest administrative distance will take priority.e) The process where a router will prioritize routing protocols so that in the event two routing protocols have conflicting next hop addresses, the routing protocol with the highest administrative distance will take priority.11. [ExNx] Collisions occur whena) multiple packets are placed on a serial linkb) multiple stations listen for traffic and transmit at the same timec) when multiple tokens are on a ring simultaneouslyd) beaconing process takes place12. [RINx] How many subnets are possible with a Class C address and a subnet mask of 255.255.255.252?a) 32b) 30c) 60d) 62e) 413. [RxNx] What commands will list all protocols that are currently being routed? (Choose all that apply.)a) show ip protocolb) show protocolc) show rund) show starte) All of the above14. [xxNx] Which of the following are true of access lists?a) Access list should have at least one permit statement.b) The last configured line should always be a permit statement.c) Every access-list will implicitly deny all traffic.d) Access-lists are processed top down.e) All of the above.15. [xxNx] If the access-group command is configured on an interface and there is no access-list created which of the following is most correct?a) An error message will appear.b) The command will be executed and deny all traffic out.c) The command will be executed and permit all traffic out.d) The command will be executed and permit all traffic in and out.e) The command will be executed and deny all traffic in and out.16. [xxNx] What is the result of the command?" access-list 101 permit tcp any 172.16.0.0 0.0.255.255 established"a) telnet sessions will be permitted regardless of the source addressb) telnet sessions will be denied regardless of the source addressc) telnet sessions will be denied if initiated from any address other than 172.16.0.0 networkd) telnet sessions will be permitted to the 172.16.0.0 network onlye) telnet sessions will be denied to the 172.16.0.0 network only17. [xxNx] Which is generally true of the location of access-lists? (Choose all that apply.)a) Standard lists will most likely be placed close to the destination.b) Standard lists will most likely be placed close to the source.c) Extended lists will most likely be placed close to the destination.d) Extended lists will most likely be placed close to the source.e) It does not matter.18. [RxNx] Which of the following is most correct?a) IP is to TCP. as IPX is to SPX.b) RTMP is to Appletalk as IP RIP is to IP.c) NLSP is to IPX as OSPF is to IP.d) a is true.e) b is true.f) a & b are true.g) c is true.h) b & c are true.i) a, b and c are true.19. [ExNx] If Host A sends a packet to Host B over ethernet and Host B is not active:a) The packet will time out.b) The packet will be removed by Host A.c) The NVRAM of Host B will remove the packet.d) The packet will "die" when it reaches the terminator.e) The packet will be removed by the token monitor.Coding Key and InformationThe first character represents the category of question.A - ATMB - BridgingC - Cisco specificE - EthernetF - Frame relayH - HDLCI - FDDIN - ISDNO - OSI modelP - PPPR - RoutingS - SwitchingT - Token ringX - X.25x - Not applicableThe second character represents protocol.A - AppletalkB - Banyan VinesD - DecnetI - IPL - Dial on DemandN - NLSPO - OSPFX - IPXx - Not ApplicableThe third character represents the certification that the question will help you prepare for.N - CCNA Exam #640-407P - CCNPAdvanced Cisco Router Configuration (ACRC) Exam 640-403Cisco LAN Switch Configuration (CLSC) Exam #640-404Cisco Monitoring and Troubleshooting Dial-up Services Exam #640-405Cisco Internetworking Troubleshooting ( CIT) Exam #640-406D - CCDA & CCDPCisco Design Specialist Exam #9E0-004Cisco Internetwork Design#640-025We will reserve the fourth character for future use.As an example, when you come across a question coded "BXDx", it signifies a question that will help you gain the CCDA or CCDP certification.CCNA试题1-19答案1. [OxNx] During a TFTP transfer using Cisco Routers what is the numeric value, in decimal, of the destination port field of the User Datagram Protocol (UDP) header?a) 96b) 47c) a random number above 1024d) 69e) none of the aboveAnswerd) 69Here is a sampling of other port numbers and the application they are associated with. The first 8 of these protocols are automatically forwarded through the router by using the helper-address commandTrivial File Transfer (TFTP) (port 69)Domain Name System (port 53)IEN-116 Name Server (port 42)Time service (port 37)NetBIOS Name Server (port 137)NetBIOS Datagram Server (port 138)Boot Protocol (BootP) client and server datagrams (port 67)TACACS service (port 49)Simple Mail Transfer Protocol (25)File Transfer Protocol (21)Simple Network Management Protocol (161)2. [CxNx] What is the standard encapsulation method used by Cisco routers for the Internet Protocol (IP) on it’s Ethernet interfaces?a) SNAPb) ARPAc) NOVELL-ETHERd) DARPAe) Ethernet_802.3Answerb) ARPASNAP is the default encapsulation for a token ring interface NOVELL-ETHER is the default encapsulation for a ipx interface.3. [CxNx] What will be the correct command on a Cisco router to set the IP address of an interface assuming you are at the "router(config-if)#" prompt?a) ip address 1.1.1.1 255.255.255.0b) ip address 1.1.1.1c) ip 1.1.1.1d) ip 1.1.1.1 255.255.255.0e) none of the aboveAnswera) ip address 1.1.1.1 255.255.255.0If you are not in the configuration mode, the ip address can be set by using the setup mode.Configuring interface Ethernet0/0:Is this interface in use? [yes]:Configure IP on this interface? [yes]:IP address for this interface [10.10.10.1]: 10.10.10.1Number of bits in subnet field [16]: 16Class A network is 10.0.0.0, 16 subnet bits; mask is /24Take note when using the setup mode the mask is configured using the number of subnet bits.4. [CxNx] Which commands will display the IP addresses of all interfaces on a Cisco Router? (Choose all that apply)a) show ip routeb) show ip addressc) show ip interfaced) show interfacee) display ip addressesAnswerc) show ip interfaced) show interfaceExamples of each of these commands are shown below: Router_A#sh int e0/0Ethernet0/0 is up, line protocol is upHardware is AmdP2, address is0010.7b15.bd41(bia 0010.7b15.bd41)Internet address is 10.10.10.1/24MTU 1500 bytes, BW 10000 Kbit,DLY 1000 usec,rely 255/255, load 1/255Encapsulation ARPA, loopback not set,keepalive set (10 sec)ARP type: ARPA, ARP Timeout 04:00:00Last input never, output 00:00:06,output hang neverLast clearing of "show interface"counters neverQueueing strategy: fifoOutput queue 0/40, 0 drops;input queue 0/75,0 drops5 minute input rate 0 bits/sec,0 packets/sec5 minute output rate 0 bits/sec,0 packets/sec0 packets input, 0 bytes,0 no bufferReceived 0 broadcasts, 0 runts,0 giants,0 throttles, 0 input errors, 0 CRC,0 frame, 0 overrun, 0 ignored,0 abort0 input packets with dribblecondition detected127 packets output, 11802 bytes,0 underruns0 output errors, 0 collisions,2 interface resets0 babbles, 0 late collision,0 deferred0 lost carrier, 0 no carrier0 output buffer failures, 0 outputbuffers swapped outRouter_A#sh ip int e0/0Ethernet0/0 is up, line protocol is upInternet address is 10.10.10.1/24Broadcast address is 255.255.255.255Address determined bynon-volatile memoryMTU is 1500 bytesHelper address is not setDirected broadcast forwarding is enabledOutgoing access list is not setInbound access list is not setProxy ARP is enabledSecurity level is defaultSplit horizon is enabledICMP redirects are always sentICMP unreachables are always sentICMP mask replies are never sentIP fast switching is enabledIP fast switching on the sameinterface is disabledIP multicast fast switching is enabledRouter Discovery is disabledIP output packet accounting is disabledIP access violation accounting isdisabledTCP/IP header compression is disabledProbe proxy name replies are disabledGateway Discovery is disabledPolicy routing is disabledNetwork address translation is disabled5. [CxNx] Which of the following commands will display the contents of the ARP cache of your Cisco router?a) show ip arp cacheb) show ip routec) show ip arpd) show arpe) there is no way to display the ARP cacheAnswerc) show ip arpExample:Router_A#sh ip arpProtocol Address Age(min) Hardware Address Type InterfaceInternet 1.1.1.2 - 0010.7b15.bd50 ARPA FastEthernet1/0Internet 10.10.10.1 - 0010.7b15.bd41 ARPA Ethernet0/06. [CxNx] Reverse Address Resolution Protocol (RARP) is the process:a) Where an IP host resolves it’s IP address by broadcasting it’s MAC address to the network a nd a BOOTP server assigns it an IP address.b) Where an IP host resolves it’s MAC address by broadcasting to the local network it’s IP address.c) Where an IP host tries to resolve the MAC address of a destination by sending a network broadcast. The dest ination responds to the broadcast with it’s MAC address.d) Where an IP host resolves a destination IP address by sending a broadcast on the local network and the destination host responds with it’s IP address.e)There is no such process.Answera) Whe re an IP host resolves it’s IP address by broadcasting it’s MAC address to the network and a BOOTP server assigns it an IP address.Choice C describes Address Resolution Protocol (ARP). A host never has to resolve it’s own MAC address. The MAC address is burned into the Network Interface card. When the host is booted the MAC address will be loaded into memory.7. [OxNx] Which of the following applications requires the connection-oriented layer four protocol, TCP? (Choose all that apply)a) Telnetb) FTPc) TFTPd) SNMPe) none of the aboveAnswera) Telnetb) FTPTFTP and SNMP use layer 4 UDP.8. [RxNx] Which of the following are link state Routing Protocols.(Choose all that apply.)a) IPb) OSPFc) RIPd) EIGRPe) IS-ISAnswerb) OSPFe) IS-ISA link state routing protocol advertises, to it’s neighbors, the state of the link when the state of the link changes.A distance vector routing protocol advertises its routing table periodically.9. [CxNx] Of the following commands, identify the correct one for clearing the IP arp table in memory of the router.a) clear ip arp-cacheb) clear ip arp-tablec) clear arp-cached) clear arp-tablee) clear arp-ramAnswerc) clear arp-cacheIf you have changed an ip address or a NIC card on a host you might use this command to reset the cache.10. [CxNx] Which of the following explains the correct definition of administrative distance as it pertains to Cisco’s IOS?a) The process by which routers select an administrator for an autonomous system.b) The process where a router will select the best path to a destination network.c) The process where a router will distance itself from other routers due to it’s lack of administrative experience.d) The process where a router will prioritize routing protocols so that in the event two routing protocols have conflicting next hop addresses, the routing protocol with the lowest administrative distance will take priority.e) The process where a router will prioritize routing protocols so that in the event two routing protocols have conflicting next hop addresses, the routing protocol with the highest administrative distance will take priority.Answerd) The process where a router will prioritize routing protocols so that in the event two routing protocols have conflicting next hop addresses, the routing protocol with the lowest administrative distance will take priority.Cisco uses administrative distances (AD) to measure the reliability of the routing protocol. The lower the (AD) the more reliable the protocol.Router_C#sh ip routeCodes: C - connected, S - static,I - IGRP, R - RIP,M - mobile, B - BGPD - EIGRP, EX - EIGRP external, O - OSPF,IA - OSPF inter areaN1 - OSPF NSSA external type 1, N2 - OSPFNSSA external type 2E1 - OSPF external type 1,E2 - OSPF external type 2,E - EGPi - IS-IS, L1 - IS-IS level-1,L2 - IS-IS level-2, * -candidate defaultU - per-user static route, o - ODRGateway of last resort is not set172.16.0.0/24 is subnetted, 2 subnetsC 172.16.1.0 is directly connected,Serial1C 172.16.2.0 is directly connected,Serial0I 10.0.0.0/8 [100/8576] via 172.16.1.1,00:00:09, Serial1[100/8576] via 172.16.2.1, 00:00:19,Serial0The 100 in bold is the administrativedistance for IGRP.A partial list of administrative distances is included below:Protocol ADEIGRP 90IGRP 100OSPF 110RIP 120BGP 180If a router hears a IP RIP and a IGRP update for the same network the router will discard the rip information. IP RIP uses hop count as it’s metric, while IGRP uses a composite metric including bandwidth and load, speed is the primary consideration.11. [ExNx] Collisions occur whena) multiple packets are placed on a serial linkb) multiple stations listen for traffic and transmit at the same timec) when multiple tokens are on a ring simultaneouslyd) beaconing process takes placeAnswerb) multiple stations listen for traffic and transmit at the same timeCollisions is a term that is used in an ethernet environment. Ethernet can be described as a listen then transmit scenario. First a station will listen for traffic if no traffic is sensed then a transmission will take place. If two stations transmit at the same time collisions will occur. The first station to detect the collision sends out a jamming signal to alert all stations a collision has occurred. At this point these stations set up a random interval timer when the timer expires re-transmission will occur.Token ring is a token passing process a station can transmit only when he has the token. There never can be multiple tokens on the ring. Early token release allows up to two data frames to be transmitted on a token ring LAN at the same time. Collisions do not occur on a token ring.Because of the point to point nature of serial links collisions do not occur.Beaconing is a term used in a token passing environment.12. [RINx] How many subnets are possible with a Class C address and a subnet mask of 255.255.255.252?a) 32b) 30c) 60d) 62e) 4Answerd) 62The above mask is using 6 bits to describe subnets. The formula used to determine the number of subnets (not including the all 0’s or all 1’s subnet) is 2n - 2 were n is the number of subnet bits. This is the number to use when configuring a ip address with the setup dialog.13. [RxNx] What commands will list all protocols that are currently being routed? (Choose all that apply.)a) show ip protocolb) show protocolc) show rund) show starte) All of the aboveAnswerb) show protocolc) show runShow ip protocol will show just the ip routing protocols that are currently configured. Show start may or may not show the current routed protocols.Below is the output of show protocolRouter_B#show protocolGlobal values:Internet Protocol routing is enabledAppletalk routing is enabledBRI0 is administratively down, line protocol is downBRI0:1 is administratively down, line protocol is downBRI0:2 is administratively down, line protocol is downSerial0 is administratively down, line protocol is downSerial1 is administratively down, line protocol is downSerial2 is administratively down, line protocol is downSerial3 is administratively down, line protocol is downTokenRing0 is administratively down, line protocol is down14. [xxNx] Which of the following are true of access lists?a) Access list should have at least one permit statement.b) The last configured line should always be a permit statement.c) Every access-list will implicitly deny all traffic.d) Access-lists are processed top down.e) All of the above.Answere) All of the above.Every access list has an implicit deny all at the end. What would the need be to create a access list with just deny statements. Access-list are processed from the top down therefore the order of each statement could be critical, for instance suppose you created an access list and the first line was a permit any and the next line was a deny. Since it’s top down processing a packet would be permitted to pass on the first line and the second line would never be executed. An extended list will give you a "match count" that will help in determining what the most efficient order should be.15. [xxNx] If the access-group command is configured on an interface and there is no access-list created which of the following is most correct?a) An error message will appear.b) The command will be executed and deny all traffic out.c) The command will be executed and permit all traffic out.d) The command will be executed and permit all traffic in and out.e) The command will be executed and deny all traffic in and out.d) The command will be executed and permit all traffic in and out.There are two steps to use an access list .1. Create the list2. Place the access list on a interfaceThe analogy I use in class is:Suppose you reside in a gated community. The community is not protected until you hire the guard and then place him at the gate. If you hire the guard and never place him at the gate all traffic will be permitted. When there is no access list on an interface it is implicit permit anyWhen an access list is placed on a interface it is implicit deny any16. [xxNx] What is the result of the command?" access-list 101 permit tcp any 172.16.0.0 0.0.255.255 established"a) telnet sessions will be permitted regardless of the source addressb) telnet sessions will be denied regardless of the source addressc) telnet sessions will be denied if initiated from any address other than 172.16.0.0 networkd) telnet sessions will be permitted to the 172.16.0.0 network onlye) telnet sessions will be denied to the 172.16.0.0 network onlyAnswerc) telnet sessions will be denied if initiated from any address other than 172.16.0.0 networkThe secret to this question is the key word "established." Established means that the packet will be permitted unless it is the first part of the three way handshake. Recall that when we initiate a TCP connection we have no ACK. How can we acknowledge a sequence number from the other side when we have not established a session with him?17. [xxNx] Which is generally true of the location of access-lists? (Choose all that apply.)a) Standard lists will most likely be placed close to the destination.b) Standard lists will most likely be placed close to the source.c) Extended lists will most likely be placed close to the destination.d) Extended lists will most likely be placed close to the source.e) It does not matter.Answera) Standard lists will most likely be placed close to the destination.d) Extended lists will most likely be placed close to the source.A standard list will only check the source address. It makes no difference where the packet is going. If you place a standard list close to the source you could very well be denying that traffic to go to other destinations. An extended list can be placed close to the source because we can permit or deny traffic based upon the source and destination address. This insures that only traffic we wish to have denied is denied.18. [RxNx] Which of the following is most correct?a) IP is to TCP. as IPX is to SPX.b) RTMP is to Appletalk as IP RIP is to IP.c) NLSP is to IPX as OSPF is to IP.d) a is true.e) b is true.f) a & b are true.g) c is true.h) b & c are true.i) a, b and c are true.i) a, b and c are true.19. [ExNx] If Host A sends a packet to Host B over ethernet and Host B is not active:a) The packet will time out.b) The packet will be removed by Host A.c) The NVRAM of Host B will remove the packet.d) The packet will "die" when it reaches the terminator.e) The packet will be removed by the token monitor.Answerd) The packet will "die" when it reaches the terminator.20—39及答案20. [TxNx] If Host A sends a packet to Host B over token ring, and Host B is not active: a) The packet will time out.b) The packet will be removed by Host A.c) The NVRAM of Host B will remove the packet.d) The packet will "die" when it reaches the terminator.e) The packet will be removed by the token monitor.21. [TxNx] If Host A sends a packet to Host B over token ring: Host A dies after transmitting, and Host B is not active:a) The packet will time out.b) The packet will be removed by Host A.c) The NVRAM of Host B will remove the packet.d) The packet will "die" when it reaches the terminator.e) The packet will be removed by the Active monitor.22. [FxNx] BECN and FECN are:a) Used to provide keepalives in a Frame Relay environmentb) Used to provide error checking in a Frame Relay environmentc) Used to provide congestion information in a Frame Relay environmentd) Used to provide flow control parameters in a Frame Relay environmente) BECN and FECN are not used in a Frame Relay environment.23. [RxNx] Which of the following are benefits of a Link-State routing protocol? (Choose all that apply.)a) Allows the use of a more robust addressing scheme.b) Allows for a larger scalable networkc) Reduces convergence timed) Allows "supernetting"e) All of the above.24. [OxNx] Which of the following are reasons for the OSI model?a) Standardizes interfacesb) Allows modular engineeringc) Facilitates learning and teachingd) All of the above.25. [RxNx] Which of the following is NOT a ROUTING protocol:a) OSPFb) RIPc) IPXd) EIGRP26. [RxNx] Which statement is NOT true about link state protocols:a) Link state advertisements are sent to all routers in an area.b) Each router executes the SPF algorithm.c) Link state routers keep a topological database of the network.d) Link state routers include the originating router s routing table.e) Link state routers know of possible alternate paths to a particular network.27. [RxNx] Which of the following would NOT appear in a routing table?a) Next hop addressb) Interface Port referencesc) MAC addressd) Network addresse) Metrics28. [OxNx] Which statement is true of the Datalink OSI layer ?a) 802.3 is the MAC sub layer.b) No such thingc) MAC sublayer provides the connection to the network layer.d) MAC sublayer uses SAPS to access the network layer.e) SAP sublayer uses the MAC layer to access the LAN medium.29. [RINx] Given the IP address of 193.243.12.43 and a subnet mask of 255.255.255.128, what is the subnet address?a) 194.243.12.32b) 193.243.0.0c) 194.243.12.43d) 193.243.12.128e) None of the above.30. [CxNx] Cisco uses a naming convention to identify frame types. Which four of the following mappings are correct?Cisco_name = Common_namea) cisco_II = Ethernet_IIb) arpa = Ethernet_IIc) sap = Ethernet_802.3d) sap = Ethernet_802.2 LLCe) Novell Ether = Ethernet_802.2 LLCf) cisco_802 = Ethernet_802.2 LLCg) snap = Token Ring Snaph) snap = Ethernet_SNAP31. [RxNx] In order to communicate throughout an internetwork, which of the following are required. Choose Two.a) The use of a routable protocol such as NetBEUI or LATb) A hierarchical naming scheme server such as DNSc) A host file at each communicating deviced) A two part network addressing scheme such as Network/Hoste) The use of a routable protocol such as IP or IPXf) The use of a routable protocol such as TCP or IPX32. [CxNx] What is the default route on an IP network? Choose one.a) This is the route that will be chosen first by IP for delivery of a datagram.。
CCNA期末测试多选题

CCNA期末测试多选题多选题:1、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ()(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE2、下面有关NAT叙述正确的是()(A) NAT是英文“地址转换”的缩写,又称地址翻译(B) NAT用来实现私有地址与公用网络地址之间的转换(C) 当内部网络的主机访问外部网络的时候,一定不需要NAT(D) 地址转换的提出为解决IP地址紧张的问题提供了一个有效途径答案:ABD3、关于VLAN下面说法正确的是()(A) 隔离广播域(B) 相互间通信要通过路由器(C) 可以限制网上的计算机互相访问的权限(D) 只能在同一个物理网络上的主机进行逻辑分组答案:ABC4、下面对路由器的描述正确的是(交换机指二层交换机)()(A) 相对于交换机和网桥来说,路由器具有更加复杂的功能(B) 相对于交换机和网桥来说,路由器具有更低的延迟(C) 相对于交换机和网桥来说,路由器可以提供更大的带宽和数据转发功能(D) 路由器可以实现不同子网之间的通信,交换机和网桥不能(E) 路由器可以实现虚拟局域网之间的通信,交换机和网桥不能答案:ADE5、关于IP报文头的TTL字段,以下说法正确的有()(多选)(A) TTL的最大可能值是65535(B) 在正常情况下,路由器不应该从接口收到TTL=0的报文(C) TTL主要是为了防止IP报文在网络中的循环转发,浪费网络带宽(D) IP报文每经过一个网络设备,包括Hub、LAN SWITCH和路由器,TTL值都会被减去一定的数值答案:BC6、VLAN的划分方法有(多选)()(A) 基于设备端口(B) 协议(C) MAC(D) 物理地址答案:ABCD7、路由项10.0.24.0/21由哪几条子网路由聚合而来()(A) 10.0.0.25/16(B) 10.0.0.23/16(C) 10.0.0.26/16(D) 10.0.0.22/16答案:AC8、在OSPF中,以下()是两台路由器成为邻居关系的必要条件。
CCNA期末考试题及答案试卷A(仅供参考)
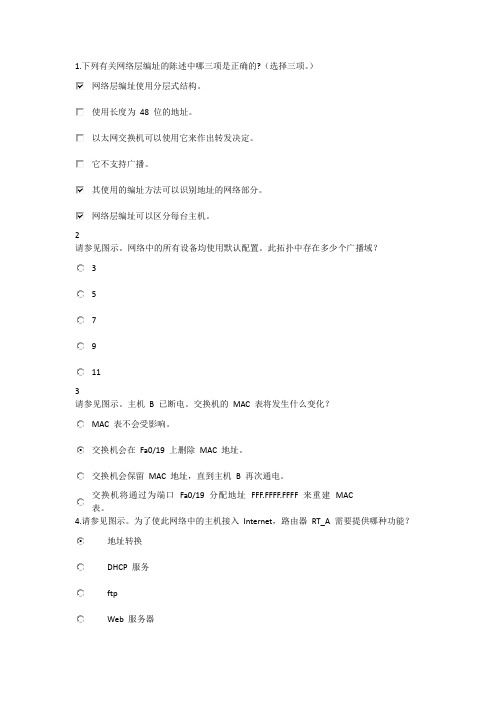
1.下列有关网络层编址的陈述中哪三项是正确的?(选择三项。
)网络层编址使用分层式结构。
使用长度为48 位的地址。
以太网交换机可以使用它来作出转发决定。
它不支持广播。
其使用的编址方法可以识别地址的网络部分。
网络层编址可以区分每台主机。
2请参见图示。
网络中的所有设备均使用默认配置。
此拓扑中存在多少个广播域?3579113请参见图示。
主机B 已断电。
交换机的MAC 表将发生什么变化?MAC 表不会受影响。
交换机会在Fa0/19 上删除MAC 地址。
交换机会保留MAC 地址,直到主机B 再次通电。
交换机将通过为端口Fa0/19 分配地址FFF.FFFF.FFFF 来重建MAC表。
4.请参见图示。
为了使此网络中的主机接入Internet,路由器RT_A 需要提供哪种功能?地址转换DHCP 服务ftpWeb 服务器5.哪三个地址属于私有IP 地址?(选择三项。
)10.0.0.1127.0.0.1150.0.0.1172.16.0.1192.168.0.1200.100.50.16请参见图示。
电缆1 和电缆2 分别按照特定的物理层要求接线。
表中按编号列出了每个网段以及该网段中用来连接网络组件的电缆。
哪三个网段安装的电缆是正确的?(选择三项。
)网段1网段2网段3网段4网段5网段67.OSI 模型的哪两项功能在第2 层实现?(选择两项)物理编址编码路由布线介质访问控制8.请参见图示。
网络管理员想通过Modem1 从PC1 远程访问路由器的CLI。
要实现此访问,应将路由器的哪一个端口连接到Modem2?控制台端口以太网端口辅助端口串行端口9请参见图示。
某学生对5e 类电缆两端的接线方法如图所示。
结果是什么?(选择两项)电缆无法使用,必须重新接线。
该电缆适合作为全反电缆使用。
该电缆适合作为快速以太网交叉电缆使用。
该电缆适合作为千兆以太网直通电缆使用。
该电缆适合在支持Auto-MDIX 的两台100 Mbps 交换机之间使用。
ccna试题
ccna试题一、单选题1. 下面哪个是OSI模型的物理层?A. TCPB. IPC. EthernetD. HTTP答案:C2. 以下哪个是IPv6的全球未经分配地址?A. FC00::/7B. 2000::/3C. 8000::/4D. FFFF::/8答案:A3. 以下哪个在OSI模型的会话层工作?A. HTTPB. IPC. TCPD. NetBIOS答案:D二、多选题4. 下面哪些是用于路由器接口配置的命令?(选择两个)A. ip addressB. mac addressC. interfaceD. enable答案:A, C5. 下面哪些是IP协议的特点?(选择三个)A. 可靠传输B. 无连接C. 不可靠传输D. 面向连接答案:B, C, D6. 下面哪些是TCP的特点?(选择三个)A. 面向连接B. 可靠传输C. 无连接D. 面向字节流答案:A, B, D三、填空题7. TCP/IP协议族中,网络接口层对应的是__________。
答案:网络接口8. 在IPv6地址中,一个冒号表示__________。
答案:前缀和后缀之间的分隔符9. 在TCP连接终止过程中,主动关闭连接的一方发送的最后一个ACK分组中ACK标志位的值是__________。
答案:1四、解答题10. 请简要解释TCP/IP协议族中IP协议的作用。
答案:IP(Internet Protocol)协议是TCP/IP协议族中的一种网络层协议,主要负责在网络之间传输数据包。
它使用IP地址来标识网络上的设备,并通过路由选择算法实现数据包的正确传递。
IP协议是一种无连接的协议,不提供数据包的可靠传输,也不保证数据包按顺序到达目的地。
它使用IP头部来存储必要的控制信息,如源IP地址、目的IP地址、数据包长度等。
11. 请简要描述TCP三次握手的过程。
答案:TCP三次握手用于建立一个TCP连接。
过程如下:1. 客户端向服务器发送一个SYN(同步)分组,其中设置SYN标志位为1,并选择一个初始序列号。
CCNA认证考试真题
为⼤家收集整理了《CCNA认证考试真题》供⼤家参考,希望对⼤家有所帮助(1)TCP/IP Addressing and Protocol1: Your junior network administrator wants to know what the default subnet mask is for a Class C IP address. What do you tell him?A. 255.0.0.0B. 255.255.0.0C. 255.245.255.0D. 255.255.255.0E. 255.255.255.255 2: An application needs to have reliable, end-to-end connect-ivity. Which of the following protocols will give you reliable connectivity?A. TCPB. UDPC. IPD. ICMP 3: You are designing a network, which needs to support 55 users. You don't plan to extend the segment beyond the current number of users. Which subnet mask would best meet your needs?A. 255.255.0.0B. 255.255.255.0C. 255.255.255.192D. 255.255.255.160 4: You have added a new switch to your network. You want to manage it remotely, so you need to assign it an IP address. Your router that connects to the switch has an IP address of 172.16.12.33/27. Which of the following addresses can you assign to this switch?A. 172.16.12.33/28B. 172.16.12.32/27C. 172.16.12.33/27D. 172.16.12.34/27E. 172.16.12.35/28F. 172.16.12.38/28G. 172.16.12.63/27 5: The address 172.16.208.16/20 is a host address in which of the following subnets? A. 172.16.176.0–255.255.240.0B. 172.16.192.0–255.255.240.0C. 172.16.208.0–255.255.240.0D. 172.16.224.0–255.255.240.0 6: You are designing an IP address scheme for your brand new remote office. The vice president of IT calls to tell you that you will be in charge of the 192.168.1.64/26 subnetwork. This supplies you with a single subnetwork with 62 hosts. You need to have at least two subnets with 14 hosts in each subnet. What custom subnet mask should you use?A. 255.255.255.128B. 255.255.255.192C. 255.255.255.224D. 255.255.255.240E. 255.255.255.248 7: You have subnetted the 210.106.14.0 network with a /24 mask. Your boss at Acme, Inc. wants to know how many usable subnetworks and usable host addresses per subnet this would provide. What should you tell her?A. One network with 254 hostsB. Two networks with 128 hostsC. Four networks with 64 hostsD. Six networks with 30 hosts 8: Identify three valid host addresses in any subnet of the 201.168.27.0 network, assuming a fixed subnet mask of 255.255.255.240. (Choose three.)A. 201.168.27.33B. 201.168.27.112C. 201.168.27.119D. 201.168.27.126E. 201.168.27.175F. 201.168.27.208 9: What is the subnetwork address for a host with the IP address 201.100.5.68/28?A. 201.100.5.0B. 201.100.5.32C. 201.100.5.64D. 201.100.5.65E. 201.100.5.31F. 201.100.5.1 10: Which of the following protocols uses a three-way handshake mechanism to establish sessions?A. TCPB. IPC. UDPD. IPXE. Frame relay 11: Which of the following protocols is connection-oriented? A. TCPB. IPC. IPXD. Frame relay 12: You are using an application on your Windows 2000 client machines that provides error correction. You need a protocol to provide fast transport. Which protocol should your application use?A. TCPB. IPC. UDPD. SPXE. AppleTalk 13: When using TCP, after a session is open, the applications can adjust the number of segments they receive before sending an acknowledgment. This behavior is known as ______________.A. MTU adjustmentB. WindowingC. Flexible Send PathD. FCS 14: If the destination did not receive a segment, how will the TCP host know to resend the information?A. The ACK received will not include the segment number that was not received.B. The ACK received will include the segment number that was not received.C. The sending host will send a PACK to verify segment receipt.D. The destination host will send a YACK message back to the sending host. 15: You are planning on using a single network that supports 208 users. Which IP address class would you choose to be the most efficient?A. Class AB. Class BC. Class CD. Class DE. Class E 16: RFC 1918 defines the private IP address ranges. Which of the following IP addresses are considered part of these ranges? (Choose three.)A. 10.23.45.67B. 126.21.34.56C. 172.16.32.1D. 172.31.234.55E. 192.169.4.5 17: A new network is being designed for your company, Acme, Inc. If you use a Class C IP network, which subnet mask will provide one usable subnet per department while allowing enough usable host addresses for each department specified in the table?Department Number of Users Corporate 7 Customer Support 15 Financial 13 HR 7 Engineering 16 A. 255.255.255.0B. 255.255.255.192C. 255.255.255.224D. 255.255.255.240E. 255.255.255.248 18: Which of these protocols provides data transport, relying on the error correction capabilities of the application itself?A. UDPB. TCPC. SNMPD. ICMP 19: Which of the following are used by TCP to ensure reliable delivery of data? (Choose two.)A. MAC address resolutionB. Sequence numbersC. AcknowledgmentsD. PingE. Routing updates 20: You discover that you are able to adjust the window size of the TCP segment. You increase the window size to test the results. What will you observe happening on your network?A. Increased throughputB. Decreased throughputC. Increased latencyD. Decreased reliability21: Your organization is using the 192.168.1.0/24 address space. You need 28 subnets. What subnet mask would you use to create these subnets?A. 255.255.255.0B. 255.255.255.128C. 255.255.255.192D. 255.255.255.224E. 255.255.255.240F. 255.255.255.248 22: Which of the following protocols maps IP addresses to MAC addresses for connectivity to occur between two hosts?A. ARPB. RARPC. SLARPD. DHCP 23: Your junior network administrator cannot seem to ping a host in another network and asks you why it isn't working. Which of the following is not an answer that you would give him?A. The host's default gateway is down.B. The destination host is not powered on.C. The IP address of the router interface is incorrect.D. The IP address of the switch to which the destination host connects is incorrect.E. The host is in a different subnet. 24: Which of the following classes of IP addresses is utilized for multicasting?A. Class AB. Class BC. Class CD. Class D 25: You give your IT department a spreadsheet of IP addresses and their subnets. You receive a call from one of the junior techs asking what the /26 means next to the IP addresses. You tell her: A. It represents the number of hosts possible on that subnetwork.B. It represents the number of subnetworks that are being used.C. It represents the class of IP address being used.D. It represents the number of bits in the subnet mask that are 1. 26: You are given an IP network of 192.168.5.0 and told that you need to separate this network into subnetworks that can support a maximum of 16 hosts per subnet. This will help alleviate congestion on the network. What subnet mask can you use to create the subnets necessary to meet the given criteria?A. 255.0.0.0B. 255.255.0.0C. 255.255.255.0D. 255.255.255.224E. 255.255.255.240 27: Which of the following would a Class A network be assigned to?A. Government agencyB. Small-to-medium sized corporationD. An individual 28: A client has the IP address 192.168.5.98/27. Which of the following addresses are on the same subnet as this host? (Choose two.)A. 192.168.5.95B. 192.168.5.100C. 192.168.5.128D. 192.168.5.110 29: Which of the following IP addresses is not a public IP address that can be routed over the Internet?A. 2.3.4.5B. 11.12.13.14C. 165.23.224.2D. 172.31.45.34E. 203.33.45.22 30: You are given a Class B network. What is the default subnet mask assigned to the Class B network?A. 255.255.255.255B. 255.255.0.0C. 255.224.0.0D. 0.0.0.0 31: You are troubleshooting your router's interfaces. For some reason, the Ethernet interface will not accept the IP address of 192.168.5.95/27 that you've assigned. Which of the following explains the router's refusal to take the IP address?A. Class C addresses cannot be assigned to Ethernet interfaces.B. The /27 is an invalid mask.C. It is a broadcast address.D. It is a public IP address.E. It is a private IP address. 32: You are a network technician at Acme, Inc. You are required to divide the 172.12.0.0 network into subnets. Each subnet must have the capacity of 458 IP addresses. Also, according to the requirements, you must provide the maximum number of subnets. Which subnet mask should you use?A. 255.255.255.254B. 255.255.254.0C. 255.255.240.254D. 255.255.0.0 33: What is the subnetwork and broadcast IP address of 192.168.2.37 with the subnet mask of255.255.255.248?A. 192.168.2.24/192.168.2.31B. 192.168.2.32/192.168.2.39C. 192.168.2.40/192.168.2.47D. 192.168.2.48/192.168.2.55E. 192.168.2.56/192.168.2.63 34: One of your co-workers at Acme, Inc., needs to convert the binary number 11011010 into a decimal. What is the decimal equivalent?A. 218B. 219C. 220E. 222 35: One of your co-workers at Acme, Inc., needs to convert the binary number 01011010 into a decimal. What is the decimal equivalent?A. 75B. 83C. 90D. 97 36: One of your co-workers at Acme, Inc., needs to convert the binary num b e r 1 1 0 1 0 1 1 0 i n t o a d e c i m a l . W h a t i s t h e d e c i m a l e q u i v a l e n t ? / p > p b d s f i d = " 2 1 0 " > A . 1 9 8 / p > p b d s f i d = " 2 1 1 " > B . 2 1 4 / p > p b d s f i d = " 2 1 2 " > C . 2 5 2 / p > p b d s f i d = " 2 1 3 " > D . 2 5 5 3 7 : O n e o f y o u r c o - w o r k e r s a t A c m e , I n c . , n e e d s t o c o n v e r t t h e b i n a r y n u m b e r 1 0 1 1 0 1 1 0 i n t o a d e c i m a l . W h a t i s t h e d e c i m a l e q u i v a l e n t / p > p b d s f i d = " 2 1 4 " > A . 1 8 2 / p > p b d s f i d = " 2 1 5 " > B . 1 9 2 / p > p b d s f i d = " 2 1 6 " > C . 2 0 2 / p > p b d s f i d = " 2 1 7 " > D . 2 1 2 3 8 : Y o u a r e c o n f i g u r i n g a s u b n e t f o r t h e A c m e , I n c . , b r a n c h o f f i c e i n B e i j i n g . Y o u n e e d t o a s s i g n I P a d d r e s s e s t o h o s t s i n t h i s s u b n e t . Y o u h a v e b e e n g i v e n t h e s u b n e t m a s k o f 2 5 5 . 2 5 5 . 2 5 5 . 2 2 4 . W h i c h o f t h e s e I P a d d r e s s e s w o u l d b e v a l i d ? ( C h o o s e t h r e e . ) / p > p b d s f i d = " 2 1 8 " > A . 1 5 . 2 3 4 . 1 1 8 . 6 3 / p > p b d s f i d = " 2 1 9 " > B . 9 2 . 1 1 . 1 7 8 . 9 3 / p > p b d s f i d = " 2 2 0 " > C . 1 3 4 . 1 7 8 . 1 8 . 5 6 / p > p b d s f i d = " 2 2 1 " > D . 1 9 2 . 1 6 8 . 1 6 . 8 7 / p > p b d s f i d = " 2 2 2 " > E . 2 0 1 . 4 5 . 1 1 6 . 1 5 9 / p > p b d s f i d = " 2 2 3 " > F . 2 1 7 . 6 3 . 1 2 . 1 9 2 3 9 : Y o u a r e a n e t w o r k t e c h n i c i a n a t A c m e , I n c . Y o u h a v e s u b n e t t e d t h e 2 0 8 . 9 8 . 1 1 2 . 0 n e t w o r k w i t h a / 2 8 m a s k . Y o u r b o s s a s k s y o u h o w m a n y u s a b l e s u b n e t w o r k s a n d u s a b l e h o s t a d d r e s s e s p e r s u b n e t t h i s w i l l p r o v i d e . W h a t s h o u l d y o u t e l l h e r , a s s u m i n g y o u r r o u t e r i s u s i n g i p s u b n e t - z e r o ? / p > p b d s f i d = " 2 2 4 " > A . 62 n e t w o r k s a n d 2 h o s t s / p > p b d s f i d = " 2 2 5 " > B . 6 n e t w o r k s a n d3 0 h o s t s / p > p b d s f i d = " 2 2 6 " >C . 8 n e t w o r k s a n d 3 2 h o s t s / p > p b d s f i d = " 2 2 7 " >D . 1 6 n e t w o r k s a n d 1 6 h o s t s / p > p b d s f i d = " 22 8 " > E . 1 6 n e t w o r k s a n d 1 4 h o s t s 4 0 : W h a t i s a d i s a d v a n t a g e o f u s i n g a c o n n e c t i o n - o r i e n t ed p r o t o c o l s u c h a s T C P ? / p > p b d s f i d = " 2 2 9 " > A . P a c ke t a c k n o w l e d g m e n t m i g h t a d d o v e r h ea d . / p > pb d s f i d = " 2 3 0 " > B . P ac k e t s a r e n o t t a g g ed w i t h se q u e n c e n u m b e r s . / p > p b d sf i d = " 23 1 " > C . L o s s o r d u p l i c a t i o n o f d a t a p a c k e t s i s m o r e l i k e l y t o o c c u r . / p > p b d s f i d = " 2 3 2 " > D . Th e a p p l i c a t i o n l a y e r m u s t a s s u m e r e s p o n s i b i l i t y f o r t h e c o r r e c t s e q u e n c i n g o f t h e d a t a p ac k e t s . 4 1 : Y o u a r e a n e t w o r k t e c h n i c i a n a t A c m e , I n c . Y o u h a v e s u b n e t t ed t he 1 9 2 . 1 6 8 . 7 2 .0 n e t w o r k w i t h a / 3 0 m a s k f o r c o n n e c t i o n s b e t w e e n y o u r r o u t e r s . Y o u r b o s s a s k s y o u h o w m a n y u s a b l e s u b n e t w o r k s a n d u s a b l e h o s t a d d r e s s e s p e r s u b n e t t h i s w i l l p r o v i d e . W h a t s h o u l d y o u t e l l h e r , a s s u m i n g y o u r r o u t e r c a n n o t u s e i p s u b n e t - z e r o ? / p > p b d s f i d = " 2 3 3 " > A . 6 2 n e t w o r k s a n d 2 h o s t s / p > p b d s f i d = " 2 3 4 " > B . 6 n e t w o r k s a n d 3 0 h o s t s / p > p b d s f i d = " 2 3 5 " > C .8 n e t w o r k s a n d 3 2 h o s t s / p > p b d s f i d = " 2 3 6 " > D . 1 6 n e t w o r k s a n d 1 6 h o s t s / p > p b d s f i d = " 2 3 7 " > E . 1 4 n e t w o r k s a n d 1 4 h o s t s 4 2 : W h i c h o f t h e f o l l o w i n g I P a d d r e s s e s a r e c o n s i d e r e d " n e t w o r k " a d d r e s s e s w i t h a / 2 6 p r e f i x ? ( C h o o s e t w o . ) / p > p b d s f i d = " 2 3 8 " > A . 1 6 5 . 2 0 3 . 2 . 0 / p > p b d s f i d = " 2 3 9 " > B . 1 6 5 . 2 0 3 . 5 . 1 9 2 / p > p b d s f i d = " 2 4 0 " > C . 1 6 5 . 2 0 3 . 6 . 6 3 / p > p b d s f i d = " 2 4 1 " > D . 1 6 5 . 2 0 3 . 6 . 1 9 1 / p > p b d s f i d = " 2 4 2 " > E . 1 6 5 . 2 0 3 . 8 . 2 5 5 4 3 : I d e n t i f y t h r e e v a l i d h o s t s i n a n y s u b n e t o f 1 9 2 . 1 6 8 . 3 2 . 0 , a s s u m i n g t h e s u b n e t m a s k u s e d i s 2 5 5 . 2 5 5 . 2 5 5 . 2 4 0 . ( C h o o s e t h r e e . ) / p > p b d s f i d = " 2 4 3 " > A . 1 9 2 . 1 6 8 . 3 2 . 3 3 / p > p b d s f i d = " 2 4 4 " > B . 1 9 2 . 1 6 8 . 3 2 . 1 1 2 / p > p b d s f i d = " 2 4 5 " > C . 1 9 2 . 1 6 8 . 3 2 . 1 1 9 / p > p b d s f i d = " 2 4 6 " > D . 1 9 2 . 1 6 8 . 3 2 . 1 2 6 / p > p b d s f i d = " 2 4 7 " > E . 1 9 2 . 1 6 8 . 3 2 . 1 7 5 / p > p b d s f i d = " 2 4 8 " > F . 1 9 2 . 1 6 8 . 3 2 . 2 0 8 4 4 : A C l a s s C n e t w o r k a d d r e s s h a s b e e n s u b n e t t e d w i t h a / 2 7 m a s k . W h i c h o f t h e f o l l o w i n g a d d r e s s e s i s a b r o a d c a s t a d d r e s s f o r o n e o f t h e r e s u l t i n g s u b n e t s ? / p > p b d s f i d = " 2 4 9 " > A . 1 9 8 . 5 7 . 7 8 . 3 3 / p > p b d s fi d = " 2 5 0 " > B . 1 9 8 . 5 7 . 7 8 . 6 4 / p > p b d s f i d = " 2 5 1 " > C . 1 9 8 . 5 7 . 7 8 . 9 7 / p > p b d s f i d = " 2 5 2 " > D . 1 98 . 5 7 . 7 8 . 9 7 / p > p b d s f i d = " 2 5 3 " > E . 1 9 8 . 5 7 . 7 8 . 1 5 9 / p > p b d s f i d = " 2 5 4 " > F . 1 9 8 . 5 7 . 7 8 . 2 5 4 4 5 : W h a t i s t h e s u b n e t w o r k a d d r e s s f o r a h o s t w i t h I P a d d r e s s 1 6 5 . 1 0 0 . 5 . 6 8 / 2 8 ? / p > p b d s f i d = " 2 5 5 " > A . 1 6 5 . 1 0 0 . 5 . 0 / p > p b d s f i d = " 2 5 6 " > B . 1 6 5 . 1 0 0 . 5 . 3 2 / p > p b d s f i d = " 2 5 7 " > C . 1 6 5 . 1 0 0 . 5 . 6 4 / p > p b d s f i d = " 2 5 8 " > D . 1 6 5 . 1 0 0 . 5 . 6 5 / p > p b d s f i d = " 2 5 9 " > E . 1 6 5 . 1 0 0 . 5 . 3 1 / p > p b d s f i d = " 2 6 0 " > F . 1 6 5 . 1 0 0 . 5 . 1 4 6 : Y o u r b o s s w a n t s t o k n o w w h a t T C P s t a n d s f o r . W h a t d o y o u t e l l h i m ? / p > p b d s f i d = " 2 6 1 " > A . T r a n s m i s s i o n C h e c k P r o t o c o l / p > p b d s f i d = " 2 6 2 " > B . T r a n s p o r t C h e c k P r o t o c o l / p > p b d s f i d = " 2 6 3 " > C . T r a n s m i s s i o n C o n t r o l P r o t o c o l / p > p b d s f i d = " 2 6 4 " > D . T r a n s p o r t C o n t r o l P r o t o c o l 4 7 : Y o u r b o s s w a n t s t o k n o w w h a t U D P s t a n d s f o r . W h a t d o y o u t e l l h i m ? / p > p b d s f i d = " 2 6 5 " > A . U n r e l i a b l e D a t a P r o t o c o l / p > p b d s f i d = " 2 6 6 " > B . U n r e l i a b l e D a t a P r o g r a m / p > p b d s f i d = " 2 6 7 " > C . U s e r - D e f i n e d P r o t o c o l / p > p b d s f i d = " 2 6 8 " > D . U s e r D a t a g r a m P r o t o c o l 4 8 : W h i c h o f t h e f o l l o w i n g s t a t e m e n t s a c c u r a t e l y d e s c r i b e s U D P ? / p > p b d s f i d = " 2 6 9 " > A . U D P c o p i e s f i l e s b e t w e e n a c o m p u t e r a n d a s y s t e m r u n n i n g r s h d , t h e r e m o t e s h e l l s e r v i c e ( d a e m o n ) . / p > p b d s f i d = " 2 7 0 " > B . U D P i s a m e m b e r o f t h e T C P / I P s u i t e o f p r o t o c o l s t h a t g o v e r n s t h e e x c h a n g e o f e l e c t r o n i c m a i l b e t w e e n m e s s a g e t r a n sf e r ag e n t s . / p > p b d s f i d = " 2 7 1 " > C . U D P i s a m e m b e r o f th e T C P / I P s ui t e o f p r o t o c o l s a n d i s u s e d t o c o p y f i l e s b e t w e e n t w o c o m p u t e r s o n t h e I n t e r n e t . B o t h c o m p u t e r s m u s t s u p p o r t t h e i r r e s p e c t i v e r o l e s : o n e m u s t b e a c l i e n t , a n d t h e o t h e r a s e r v e r . / p > p b d s f i d = " 2 7 2 " > D . U D P i s a T C P c o m p l e m e n t t h a t o f f e r s a c o n n e c t i o n l e s s d a t a g r a m s e r v i c e g u a r a n t e e i n g n e i t h e r d e l i v e r y n o r c o r r e c t s e q u e n c i n g o f d e l i v e r e d p a c k e t s ( m u c h l i k e I P ) . 4 9 : W h i c h o f t h e f o l l o w i n g h o s t a d d r e s s e s a r e m e m b e r s o f n e t w o r k s t h a t c a n b e r o u t e d a c r o s s t h e p u b l i c I n t e r n e t ( C h o o s e t h r e e . ) / p > p b d s f i d = " 2 7 3 " > A . 1 0 . 2 0 . 1 2 . 6 4 / p > p b d s f i d = " 2 7 4 " > B . 1 7 2 . 1 6 . 3 2 . 12 9 / p > p b d s f i d = " 2 7 5 " > C . 1 7 2 . 6 4 .3 2 . 34 / p > p b d s f i d = " 2 7 6 " > D . 1 9 2 . 1 6 8 . 2 3 . 25 2 / p > p b d s f id = " 2 7 7 " > E . 1 9 6 . 1 0 4 . 1 2 . 9 5 / p > p b d s f i d = " 2 7 8 " > F . 2 1 4 . 1 9 2 . 4 8 . 2 5 4 5 0 : Y o u a re c o n n e c t i n g y o u r S e r i a l 0 / 1 i n t e rf a c e t o t h e I n t e r n e t . W h i c h o f t h e f o l l o w i ng n e e d t o b e d o n e f o r th e c o n n e c ti o n t o w o r k ? ( C h o o s e t w o . ) / p > p b d s f i d = " 2 7 9 " > A . A s s i g n a p u b l i c I P a d d r e s s . / p > p b d s f i d = " 2 8 0 " > B . U s e t h e s h u t d o w n c o m m a n d . / p > p b d s f i d = " 2 8 1 " > C . U s e t h e n o s h u t d o w n c o m m a n d . / p > p b d s f i d = " 2 8 2 " > D . M a k e s u r e t h e i n t e r f a c e i s r u n n i n g i n f u l l - d u p l e x . / p >。
CCNA考试自测题2新
CCNA考试自测题2我为大家收集整理了《CCNA考试自测题2》供大家参考,盼望对大家有所关心!!!25) Which statement is true of WinSock (下面对Wi n S o c k的哪一句陈述是正确的)?A. It is a MAC applicationB. It represents a graphical user interfaceC. It represents a network layerD. It provides the means for sharing an Internet connection between multiple IP protocol suite utilities26) Which statement is true of TLI (下面关于T L I的哪一句陈述是正确的)?A. It is a layer in the OSI modelB. It is a layer in the TCP/IP modelC. It is a System V APID. It is part of the UNIX Kernel27) Which statement is true of Windows Name Server (WINS) (下面对于Windows 命名服务器( W I N S )的陈述中,哪一句是正确的)?A. It is a protocolB. It provides capability for name resolutionC. It is a network layerD. It is a proprietary name serverE. A, B, and D onlyF. B and D only28) ICMP、I P、ARP and RARP of the IP protocol suite map to (IP协议套件的I C M P、I P、A R P和R A R P映射到):A. OSI layers 1 and 2B. OSI layer 5C. OSI layer 3D. OSI layer 229) Which layer is most important in providing reliable data exchange between two systems (在两个系统之间供应牢靠的数据交换中,哪一层是最重要的)?A. Physical layerB. Data link layerC. Session layerD. Transport layer30) Which of the following does TCP provide (TCP供应了下面的哪一个功能)?A. Unreliable data streamB. Connectionless virtual circuitC. Flow controlD. Structured byte stream movement31) Of the following, which field is not a part of the TCP header (在下面各项中,哪一个字段不是T C P报头的一部分)?A. Subnet maskB. Sequence numberC. Data offsetD. Destination port32) What is the sequence number in a TCP header used for (在T C P 报头中的挨次号的作用是什么)?A. AcknowledgmentsB. Reordering of the octets receivedC. Rejecting duplicate octets33) Variable sliding windows provide an explicit mechanism for notifying TCP if an intermediate node (for example, a router) becomes congested (在中间节点,例如一个路由器拥塞的状况下,可变滑动窗口供应了通知T C P的显式机制)。
ccna测试题及答案
ccna测试题及答案CCNA测试题及答案一、选择题1. 在Cisco设备上,以下哪个命令用于查看当前的路由表?A. show ip routeB. show running-configC. show interface statusD. show version答案:A2. 以下哪个协议用于在网络中自动发现其他设备?A. ARPB. CDPC. ICMPD. TCP答案:B3. 以下哪个命令用于配置Cisco设备上的接口?A. configure terminalB. interfaceC. ip addressD. hostname答案:A二、填空题4. 在Cisco设备上,使用命令_________可以查看接口的配置信息。
答案:show interface5. 静态路由配置中,_________命令用于指定下一跳地址。
答案:ip route6. 动态路由协议可以自动适应网络变化,其中_________是最常见的一种。
答案:RIP(路由信息协议)三、简答题7. 请简述VLAN(虚拟局域网)的作用。
答案:VLAN是一种将局域网内不同物理位置的设备划分为同一逻辑网络的技术,主要用于隔离广播域,提高网络的安全性和效率。
8. 描述交换机和路由器在网络中的基本功能。
答案:交换机主要用于局域网内部,通过MAC地址表来转发数据帧,实现数据包在局域网内的快速交换。
路由器则工作在网络层,使用IP地址来转发数据包,连接不同的网络,并进行路径选择。
四、计算题9. 假设一个子网掩码为255.255.255.192,计算这个子网的可用IP地址范围。
答案:可用IP地址范围为192.168.1.0到192.168.1.62(包含两端)。
五、实验题10. 请根据以下配置文件,列出Router1的接口配置信息。
```Router1show running-configinterface FastEthernet0/0ip address 192.168.1.1 255.255.255.0duplex autospeed auto!interface FastEthernet0/1no ip addressshutdown!interface Serial0/0/0ip address 10.0.0.1 255.255.255.252clock rate 64000!router ospf 1network 192.168.1.0 0.0.0.255 area 0network 10.0.0.0 0.0.0.3 area 0!```答案:- FastEthernet0/0: IP地址为192.168.1.1,子网掩码为255.255.255.0,双工模式和速度均为自动。
CCNA路由部分测试题(含答案)

CCNA路由部分测试题(共50题)1.当路由器接收的IP报文的目的地址不是本路由器的接口IP地址,并且在路由表中未找到匹配的路由项,采取的策略是什么?A.丢掉该分组B.将该分组分片C.转发该分组D.以上答案均不对ANSWER:A2.IGP 的作用范围是?A.区域内B.自然子网范围内C.局域网内D.自治系统内ANSWER:D3.距离矢量协议包括?(多选)A.RIPB.IS-ISC.OSPFD.EIGRPANSWER:A D4.解决路由环问题的办法是?(多选)A.定义路由权的最大值B.路由保持法C.水平分割D.路由器重启ANSWER:A B C5.在rip 中metric 等于什么值为不可达?A.8B.10C.15D.16ANSWER:D6.下列关于OSPF 协议的说法正确的是?(多选)A.OSPF 支持基于接口的报文验证B.OSPF 支持到同一目的地址的多条等值路由C.OSPF 是一个基于链路状态算法的边界网关路由协议D.OSPF 发现的路由可以根据不同的类型而有不同的优先级ANSWER:A B D7.如果一个内部网络对外的出口只有一个,那么最好配置?A.缺省路由B.主机路由C.动态路由ANSWER:A8.以下不属于动态路由协议的是?A.RIPB.ICMPC.EIGRPD.OSPFANSWER:B9.关于矢量距离算法以下哪些说法是错误的?A.矢量距离算法不会产生路由环路问题B.矢量距离算法是靠传递路由信息来实现的C.路由信息的矢量表示法是(目标网络,metric)D.使用矢量距离算法的协议只从自己的邻居获得信息ANSWER:A10.以下哪些路由表项要由网络管理员手动配置?(多选)A.静态路由B.直接路由C.缺省路由D.动态路由ANSWER:A C11.关于RIP 协议,下列说法正确的有?(多选)A.RIP 协议是一种IGPB.RIP 协议是一种EGPC.RIP 协议是一种距离矢量路由协议D.RIP 协议是一种链路状态路由协议ANSWER:A C12.下列关于链路状态算法的说法正确的是?(多选)A.链路状态是对路由的描述B.链路状态是对网络拓扑结构的描述C.链路状态算法本身不会产生自环路由D.OSPF 和RIP 都使用链路状态算法ANSWER:B C13.路由器中时刻维持着一张路由表,这张路由表可以是静态配置的,也可以是什么协议产生的?A.生成树协议B.链路控制协议C.动态路由协议D.被承载网络层协议ANSWER:C14.在路由器中,如果去往同一目的地有多条路由,则决定最佳路由的因素有?(多选)A.路由的优先级B.路由的发布者C.路由的metric 值D.路由的生存时间ANSWER:A C15.下面哪一项正确描述了路由协议?A.允许数据包在主机间转送的一种协议B.定义数据包中域的格式和用法的一种方式C.通过执行一个算法来完成路由选择的一个协议D.指定MAC 地址和IP 地址捆绑的方式和时间的一种协议ANSWER:C16.IGP 包括如下哪些协议?(多选)A.RIPB.BGPC.IS-ISD.EIGRPE.OSPFANSWER:A C D E17.RIP 协议引入路由保持机制的作用是?A.节省网络带宽B.防治网络中形成路由环路C.将路由不可达信息在全网扩散D.通知邻居路由器哪些路由是从其处得到ANSWER:B18.对路由理解正确的是?A.路由是路由器B.路由是信息在网络路径的交叉点C.路由是用以配置报文的目的地址D.路由就是指导报文发送的路径信息ANSWER:D19.路由协议RIP,OSPF和静态路由各自得到了条到达目标网络,在CISCO路由器默认情况下,最终选选定哪种路由作为最优路由?A.RIPB.OSPFC.静态路由ANSWER:C20.在RIP 协议中,计算metric 值的参数是?A.MTUB.时延C.带宽D.路由跳数ANSWER:D21.衡量路由算法好坏的原则不包括?A.快速收敛性B.灵活性,弹性C.拓扑结构先进D.选径是否是最佳ANSWER:C22.RIP 协议是基于?A.UDPB.TCPC.ICMPD.Raw IPANSWER:A23.禁止RIP 协议的路由聚合功能的命令是?A.no route ripB.summanyC.no auto summanyD.undo networkANSWER:C24.解决路由环路的方法有?(多选)A.水平分割B.抑制时间C.毒性逆转D.触发更新ANSWER:A B C D25.路由环问题会引起哪些问题?(多选)A.慢收敛B.广播风暴C.路由器重起D.路由不一致ANSWER:A D26.下列哪些路由协议存在路由自环问题?(多选)A.RIPB.IGRPC.OSPFD.IS-ISE.EIGRPANSWER:A B27.关于RIP V1 和RIP V2,下列说法哪些正确?(多选)A.RIP V1 报文支持子网掩码B.RIP V2 报文支持子网掩码C.RIP V2 缺省使用路由聚合功能D.RIP V1 只支持报文的简单口令认证,而RIP V2 支持MD5 认证ANSWER:B C28.在一个运行OSPF 的自治系统之内?(多选)A.骨干区域自身也必须连通的B.非骨干区域自身也必须连通的C.必须存在一个骨干区域(区域号为0)D.非骨干区域与骨干区域必须直接相连或逻辑上相连ANSWER:A C D29.以下关于Rip 路由聚合的说法正确的是?(多选)A.Rip V1 默认支持路由聚合,需要时可以关闭路由聚合功能B.华为Quidway 系列路由器Rip V2 的实现可以关闭路由聚合功能C.Rip V1 不支持子网路由聚合到一个非自然子网路由D.Rip V2 支持子网路由聚合到一个非自然子网路由ANSWER:B C D30.假设有这样的组网实例:两台路由器(假设为RTA 和RTB)通过串口相接,其中RTA 的串口IP 地址是,RTB 的串口IP 地址是,RTA 通过以太口连接的本地局域网的IP 地址是,RTB 通过以太口连接的本地局域网IP 地址是,在上面所有的接口上都启动RIP V1(仅仅RIP V1)协议,那么,下列说法正确的是?(多选)A.在RTA 的本地局域网上的计算机可以访问在RTB 本地局域网上的计算机B.在RTB 的本地局域网上的计算机可以访问在RTA 本地局域网上的计算机C.在RTA 的本地局域网上的计算机不能访问在RTB 本地局域网上的计算机D.在RTB 的本地局域网上的计算机不能访问在RTA 本地局域网上的计算机ANSWER:C D31.根据路由的目的地不同,路由表可被划分为?(多选)A.子网路由B.直连路由C.缺省路由D.主机路由E.静态路由ANSWER:A D32.对路由器A 配置RIP 协议,并在接口S0(IP 地址为路由协议,在全局配置模式下使用的第一条命令是?A.router ripwork allworkworkANSWER:A33.当接口运行在RIP-2 广播方式时,它可以接受的报文有?(多选)A.RIP-1 广播报文B.RIP-1 组播报文C.RIP-2 广播报文D.RIP-2 组播报文ANSWER:A C34.RIP 协议的路由项在多少时间内没有更新会变为不可达?A.90sB.120sC.180sD.240sANSWER:C35.VLSM 的含义是?A.Variable Length Subnet MaskingB.Variable Length Shortest MaskingC.Very Long/Shortest MaskingD.Variable Long Subnet MaskingE.Variable Length Short MeasurementANSWER:A36.距离矢量路由协议使用水平分割(split horizon)技术的目的是什么?(多选)A.避免在毗邻路由器之间产生路由环路B.确保路由更新数据报文沿着接收路线方向发送C.与保持间隔(holddown)机制协同工作,为保持间隔的计算提供更多的可靠性D.代替路由中毒(poison reverse)算法ANSWER:A C37.作为一个网络维护人员,对于OSPF 区域体系机构的原则必须有清楚地了解,下面的论述表达正确的是?(多选)A.所有的OSPF 区域必须通过边界路由器与区域0 相连,或采用OSPF 虚链路B.所有区域间通信必须通过骨干区域0,因此所有区域路由器必须包含到区域0 的路由C.单个区域不能包含没有物理链路的两个区域边界路由器D.虚链路可以穿越stub 区域ANSWER:A B38.支持可变长子网掩码的路由协议有?(多选)A.RIP v1B.RIP v2C.OSPFD.EIGRPANSWER:B C D39.因为在生成路由表的过程中,OSPF 协议需要进行复杂的SPF 算法来计算网络拓扑结构,所以相对距离矢量路由选择协议来说,它需要更大的开销,更多的延迟,更高的CPU 占用率。
CCNA测试题一
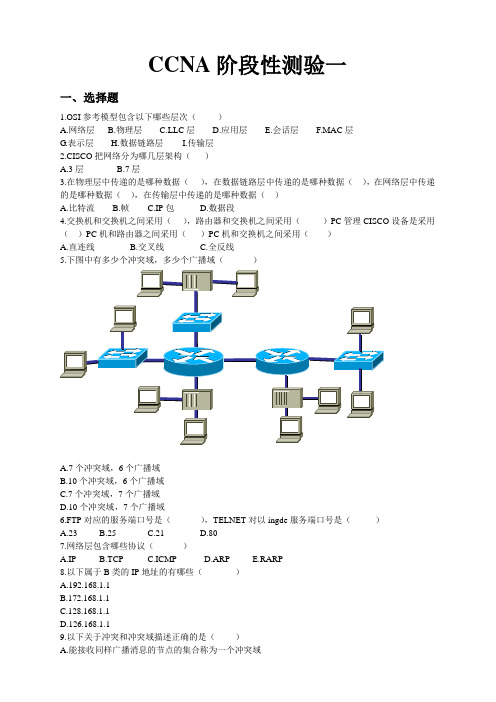
CCNA阶段性测验一一、选择题1.OSI参考模型包含以下哪些层次()A.网络层B.物理层C.LLC层D.应用层E.会话层F.MAC层G.表示层H.数据链路层I.传输层2.CISCO把网络分为哪几层架构()A.3层B.7层3.在物理层中传递的是哪种数据(),在数据链路层中传递的是哪种数据(),在网络层中传递的是哪种数据(),在传输层中传递的是哪种数据()A.比特流B.帧C.IP包D.数据段4.交换机和交换机之间采用(),路由器和交换机之间采用()PC管理CISCO设备是采用()PC机和路由器之间采用()PC机和交换机之间采用()A.直连线B.交叉线C.全反线A.7个冲突域,6个广播域B.10个冲突域,6个广播域C.7个冲突域,7个广播域D.10个冲突域,7个广播域6.FTP对应的服务端口号是(),TELNET对以ingde服务端口号是()A.23B.25C.21D.807.网络层包含哪些协议()A.IPB.TCPC.ICMPD.ARPE.RARP8.以下属于B类的IP地址的有哪些()A.192.168.1.1B.172.168.1.1C.128.168.1.1D.126.168.1.19.以下关于冲突和冲突域描述正确的是()A.能接收同样广播消息的节点的集合称为一个冲突域B.如果为每台设备都建立收发双向的专用通道,就可以避免冲突C.在多台设备共享一条链路时会产生冲突D.位于同一冲突域中的多个设备之间必须采用一种机制,来决定共享介质由谁来使用,否则就会产生冲突10.ABC 公司现在需要划分VLAN,因此,需要按照部门来划分IP 子网,目前使用的网段是192.168.10.0/24,现在需要划分为6 个部门,每个部门中至少包含25 台主机,那么子网掩码应该是()A.255.255.255.192B.255.255.255.224C.255.255.255.240D.255.255.255.248二、判断题1.OSI参考模型是OSI组织提出的网络互联参考模型。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
B. Router(config-if)#passive-interface
C. Router(config-router)#passive-interface s0
D. Router(config-router)#no routing updates
D.The existing routing table entry will be deleted from the routing table and all routers will exchange routing updates to reach c2.Which EIGRP information is held in RAM and maintained through the use of Hello and update packets?(choose two)
A. RARP
B. ARP
C. IP
D. ICMP
E. BootP
B
10. Which class of IP address provides a maximum of only 254 host addresses per network ID?
A. Class A
B. Class B
A. It divides the network communication process into smaller and simpler components, thus aiding component development, design, and troubleshooting.
B. It enables equipment from different vendors to use the same electronic components, thus saving research and development funds.
B. Presentation
C. Session
D. Transport
A
15. Which two of the following are private IP addresses?
A. 12.0.0.1
B. 168.172.19.39
C. 172.20.14.36
D. 172.33.194.30
E. It provides a framework by which changes in functionality in one layer require changes in other layers.
AD
5. Which of the following are unique characteristics of half-duplex Ethernet when compared to full-duplex Ethernet? (Choose two.)
A. Switch
B. NIC
C. Hub
D. Repeater
E. RJ45 transceiver
CD
3. Which of the following describe router functions? (Choose four. )
A. Packet switching
B. Collision prevention
C. It supports the evolution of multiple competing standards and thus provides business opportunities for equipment manufacturers.
D. It encourages industry standardization by defining what functions occur at each layer of the model.
A. DHCP
B. SR/ITP
C. SNMP
D. FTP
E. HTTP
F. TFTP
BDE
13. Which of the following are TCP/IP protocols used at the Application layer of the OSI model? (Choose three.)
D. Half-duplex Ethernet has lower effective throughput.
E. Half-duplex Ethernet operates in a private broadcast domain.
AD
6. What is the purpose of flow control?
A. FTP
B. SMTP
C. Telnet
D. DNS
D
18. What command is used to stop RIP routing updates from exiting out an interface but still allow the interface to receive RIP route updates
A. IP
B. TCP
C. Telnet
D. FTP
E. TFTP
CDE
14. If you use either Telnet or FTP, which is the highest layer you are using to transmit data?
A. Application
A. Half-duplex Ethernet operates in a shared collision domain.
B. Half-duplex Ethernet operates in a private collision domain.
C. Half-duplex Ethernet has higher effective throughput.
A. Send a different source port number.
B. Restart the virtual circuit.
C. Decrease the sequence number.
D. Decrease the window size.
D
2. Which layer 1 devices can be used to enlarge the area covered by a single LAN segment? (Choose two. )
A. Gateway DP
B. Reverse ARP(RARP)
C. Proxy ARP
D. Inverse ARP(IARP)
E. Address Resolution Protocol(ARP)
C
9. What protocol is used to find the hardware address of a local device?
1. A receiving host has failed to receive all of the segments that it should acknowledge. What can the host do to improve the reliability of this communication session?
A. Straight-through
B. Crossover cable
C. Crossover with a CSU/DSU
D. Rolled
D
8. Which of the following allows a router to respond to an ARP request that is intended for a remote host?
C. Class C
D. Class D
E. Class E
C
11. Which layer 4 protocol is used for a Telnet connection?
A. IP
B. TCP
C. TCP/IP
D. UDP
E. ICMP
B
12. Which of the following services use TCP? (Choose three.)
A. To ensure that data is retransmitted if an acknowledgment is not received
B. To reassemble segments in the correct order at the destination device
C. To provide a means for the receiver to govern the amount of data sent by the sender
D. To regulate the size of each segment
C
7. What type of RJ45 UTP cable do you use to connect a PCs COM port to a router or switch console port?
E. 192.168.24.43
CE
16. Which statements are true regarding ICMP packets? (Choose two)
A. ICMP guarantees datagram delivery.
