cisco asa 5520配置实例
asa5520防火墙透明模式的配置例子

asa5520防火墙透明模式的配置例子ciscoasa# sh run: Saved:ASA Version 7.2(3)!firewall transparenthostname ciscoasadomain-name default.domain.invalidenable password 8Ry2YjIyt7RRXU24 encryptednames!interface GigabitEthernet0/0nameif outsidesecurity-level 0!interface GigabitEthernet0/1nameif insidesecurity-level 100!interface GigabitEthernet0/2shutdownno nameifno security-level!interface GigabitEthernet0/3shutdownno nameifno security-level!interface Management0/0nameif managementsecurity-level 100ip address 192.168.1.1 255.255.255.0management-only!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivedns server-group DefaultDNSdomain-name default.domain.invalidaccess-list acl_inside extended permit ip any any access-list acl_inside extended permit icmp any anyaccess-list acl_outside extended permit tcp any any eq 3306access-list acl_outside extended permit tcp any any eq wwwaccess-list acl_outside extended permit tcp any any eq 8080access-list acl_outside extended permit tcp any any eq httpsaccess-list acl_outside extended permit tcp any any eq sqlnetaccess-list acl_outside extended permit tcp any any eq ftpaccess-list acl_outside extended permit tcp any any eq 1433access-list acl_outside extended permit esp any anyaccess-list acl_outside extended permit udp any any eq isakmpaccess-list acl_outside extended permit tcp any any eq pop3access-list acl_outside extended permit tcp any any eq smtpaccess-list acl_outside extended permit icmp any anypager lines 24mtu outside 1500mtu inside 1500mtu management 1500ip address 172.16.177.208 255.255.255.0no failovericmp unreachable rate-limit 1 burst-size 1asdm image disk0:/ASDM-523.BINno asdm history enablearp timeout 14400access-group acl_outside in interface outsideaccess-group acl_inside in interface insidetimeout xlate 3:00:00timeout conn 0:20:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolutehttp server enablehttp 192.168.1.0 255.255.255.0 managementhttp 0.0.0.0 0.0.0.0 insideno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstarttelnet timeout 5ssh timeout 5console timeout 0!class-map inspection_defaultmatch default-inspection-traffic!!policy-map type inspect dns preset_dns_mapparametersmessage-length maximum 512policy-map global_policyclass inspection_defaultinspect dns preset_dns_mapinspect ftpinspect h323 h225inspect h323 rasinspect rshinspect rtspinspect esmtpinspect sqlnetinspect skinnyinspect sunrpcinspect xdmcpinspect sipinspect netbiosinspect tftpinspect pptp!service-policy global_policy globalusername cisco password 3USUcOPFUiMCO4Jk encryptedprompt hostname contextCryptochecksum:4682fd668f251c28d32a0cb82a3ac5f3: endciscoasa#注意点:语句ip address 172.16.177.208 255.255.255.0是在interface GigabitEthernet0/0下配的,自己跑到外面来了,如果不配这个,好像ping不通。
Cisco ASA5520防火墙配置
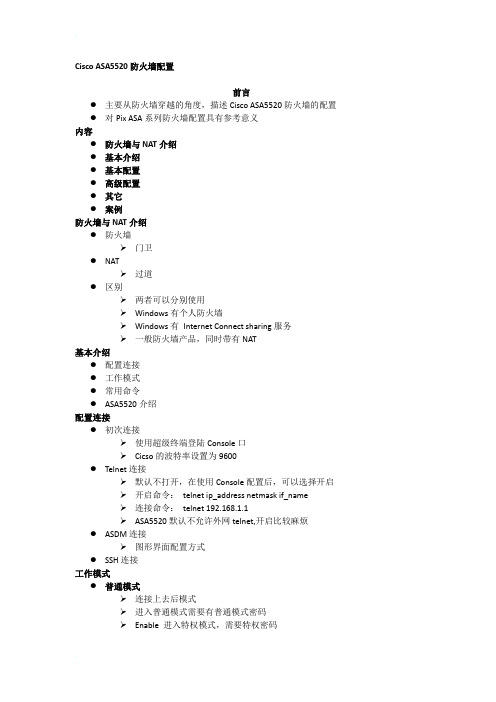
ip address ip_address [netmask]
ip address ip_address dhcp
打开端口: no shutdown
配置安全级别
security-level [0-100]
数据从安全级别高的流向底的,不能倒流
倒流需要保安允许
所以外网一般配置为0,内网为100
配置别名
连接命令:telnet 192.168.1.1
ASA5520默认不允许外网telnet,开启比较麻烦
ASDM连接
图形界面配置方式
SSH连接
工作模式
普通模式
连接上去后模式
进入普通模式需要有普通模式密码
Enable进入特权模式,需要特权密码
特权模式
Config terminal进入配置模式
配置模式
模式转换
Policy pat : static (real_interface,mapped_interface) {tcp | udp} {mapped_ip |interface} mapped_port access-list acl_name
举例
hostname(config)# access-list NET1 permit ip 10.1.2.0 255.255.255.0 209.165.201.0
动态分配给内网一个独立的IP
PAT
PAT使用1个地址+65535个端口为内网提供地址转换
地址池中只有一个值时,就是PAT
分配给内网连接一个固定IP和一个动态的端口
Static NAT
Static NAT
允许外网先发起连接
是一个外网IP固定一个内网IP
可以称为IP映射
ASA5520防火墙双机配置

ASA5520防火墙的安装配置说明一、通过超级终端连接防火墙。
先将防火墙固定在机架上,接好电源;用随机带来的一根蓝色的线缆将防火墙与笔记本连接起来。
注意:该线缆是扁平的,一端是RJ-45接口,要接在防火墙的console端口;另一端是串口,要接到笔记本的串口上.建立新连接,给连接起个名字。
选择COM口,具体COM1还是COM3应该根据自己接的COM来选择,一般接COM1就可以。
选择9600,回车就可以连接到命令输入行。
二、防火墙提供4种管理访问模式:1.非特权模式。
防火墙开机自检后,就是处于这种模式。
系统显示为firewall> 2.特权模式。
输入enable进入特权模式,可以改变当前配置。
显示为firewall# 3.配置模式。
在特权模式下输入configure terminal进入此模式,绝大部分的系统配置都在这里进行。
显示为firewall(config)#4.监视模式。
PIX防火墙在开机或重启过程中,按住Escape键或发送一个“Break”字符,进入监视模式。
这里可以更新操作系统映象和口令恢复。
显示为monitor>三、基本配置步骤在PC机上用串口通过cisco产品控制线连接防火墙的Console口(9600-N-8-1),使用超级终端连接。
在提示符的后面有一个大于号“>”,你处在asa用户模式。
使用en或者enable命令修改权限模式。
asafirewall> en //输入en 或 enable 回车Password: //若没有密码则直接回车即可asafirewall# //此时便拥有了管理员模式,此模式下可以显示内容但不能配置,若要配置必须进入到通用模式asafirewall# config t // 进入到通用模式的命令asafirewall(config)# hostname sjzpix1 //设置防火墙的名称Sjzpix1(config)# password zxm10 //设置登陆口令为zxm10Sjzpix1(config)# enable password zxm10 //设置启动模式口令,用于获得管理员模式访问1.配置各个网卡Sjzpix1(config)# interface GigabitEthernet0/0 //配置防火墙的E0 端口Sjzpix1(config-if)# security-level 0 //设置成最低级别Sjzpix1(config-if)# nameif outside //设置E0 端口为外部端口Sjzpix1(config-if)# speed auto //设置成自动设置网口速率Sjzpix1(config-if)# ip address 10.0.1.50 255.255.255.0 standby 10.0.1.51// 10.0.1.50 为该防火墙分配的公网IP,255.255.255.0为该防火墙公网IP对应的掩码,若该防火墙没有主备用方式则配置命令中的红色字体部分不需要配置。
cisco asa5200双isp

ASA5520,双ISP接入配置实现功能如下:1,部分网通站点走网通线路,其余走电信实现负载均衡(电信为主)2,任何一条链路断掉,另一条可以继续用3,电信网通口上都启用VPNClient,保证电信,网通客户端都可以顺利拨入jxwsj(config)# show run: Saved:ASA Version 7.0(5)!hostname jxwsjdomain-name enable password fCoWG.vztqKmZjts encryptednamesdns-guard!interface GigabitEthernet0/0description tocncnameif outsidesecurity-level 0ip address 网通IP 255.255.255.248!interface GigabitEthernet0/1nameif insidesecurity-level 100ip address 192.1.5.2 255.255.255.0!interface GigabitEthernet0/2description to cntnameif ctsecurity-level 0ip address 电信IP 255.255.255.248!interface GigabitEthernet0/3nameif govsecurity-level 40ip address 21.36.255.14 255.255.255.0!interface Management0/0nameif managementsecurity-level 100ip address 192.168.1.1 255.255.255.0management-only!passwd nRRwDj.AHmVtB9jY encryptedftp mode passiveaccess-list 110 extended permit ip any anyaccess-list 150 extended permit tcp any any eq wwwaccess-list 150 extended permit tcp any any eq 8080access-list 150 extended permit tcp any any eq lotusnotesaccess-list 150 extended permit icmp any anyaccess-list 150 extended deny ip any anyaccess-list inside_in extended permit ip any anyaccess-list 102 extended permit ip 192.168.0.0 255.255.255.0 192.168.200.0 255.255.255.0 access-list 102 extended permit ip 192.168.1.0 255.255.255.0 192.168.200.0 255.255.255.0 access-list 102 extended permit ip 192.168.3.0 255.255.255.0 192.168.200.0 255.255.255.0 access-list 102 extended permit ip 192.168.4.0 255.255.255.0 192.168.200.0 255.255.255.0 access-list 102 extended permit ip 192.1.5.0 255.255.255.0 192.168.200.0 255.255.255.0 access-list tempdeny extended deny ip host 192.168.3.11 anyaccess-list tempdeny extended deny ip host 192.168.3.12 anyaccess-list tempdeny extended deny ip host 192.168.3.13 anyaccess-list tempdeny extended deny ip host 192.168.3.14 anyaccess-list tempdeny extended permit ip any anyaccess-list 111 extended permit ip any anypager lines 24logging asdm informationalmtu outside 1500mtu inside 1500mtu gov 1500mtu management 1500mtu ct 1500ip local pool vpdn 192.168.200.1-192.168.200.100no failoverasdm image disk0:/asdm505.binno asdm history enablearp inside 192.168.3.14 0016.1727.a178arp inside 192.168.3.13 000a.480b.2295arp inside 192.168.3.12 0030.1b31.a88barp inside 192.168.3.11 000a.480e.24a4arp timeout 14400global (outside) 1 interfaceglobal (gov) 1 interfaceglobal (ct) 1 interfacenat (inside) 0 access-list 102nat (inside) 1 0.0.0.0 0.0.0.0access-group 110 in interface outsideaccess-group tempdeny in interface insideaccess-group 150 in interface govaccess-group 111 in interface ctroute outside 0.0.0.0 0.0.0.0 网通网关254route outside 222.160.0.0 255.224.0.0 网通网关1 route outside 222.162.0.0 255.255.0.0 网通网关1 route outside 222.160.0.0 255.254.0.0 网通网关1 route outside 222.136.0.0 255.248.0.0 网通网关1 route outside 222.132.0.0 255.252.0.0 网通网关1 route outside 222.128.0.0 255.252.0.0 网通网关1 route outside 221.216.0.0 255.248.0.0 网通网关1 route outside 221.213.0.0 255.255.0.0 网通网关1 route outside 221.212.0.0 255.255.0.0 网通网关1 route outside 221.208.0.0 255.252.0.0 网通网关1 route outside 221.207.0.0 255.255.192.0 网通网关1 route outside 221.204.0.0 255.254.0.0 网通网关1 route outside 221.200.0.0 255.252.0.0 网通网关1 route outside 221.199.192.0 255.255.240.0 网通网关1 route outside 221.199.128.0 255.255.192.0 网通网关1 route outside 221.199.32.0 255.255.240.0 网通网关1 route outside 221.199.0.0 255.255.224.0 网通网关1 route outside 221.198.0.0 255.255.0.0 网通网关1 route outside 221.196.0.0 255.254.0.0 网通网关1 route outside 221.192.0.0 255.252.0.0 网通网关1 route outside 221.14.0.0 255.254.0.0 网通网关1 route outside 221.13.128.0 255.255.128.0 网通网关1 route outside 221.13.64.0 255.255.224.0 网通网关1 route outside 221.13.0.0 255.255.192.0 网通网关1 route outside 125.210.0.0 255.255.0.0 网通网关1 route outside 58.100.0.0 255.255.0.0 网通网关1 route outside 219.82.0.0 255.255.0.0 网通网关1 route outside 218.108.0.0 255.255.0.0 网通网关1 route outside 221.12.128.0 255.255.192.0 网通网关1 route outside 221.12.0.0 255.255.128.0 网通网关1 route outside 221.11.128.0 255.255.224.0 网通网关1 route outside 221.11.0.0 255.255.128.0 网通网关1 route outside 221.10.0.0 255.255.0.0 网通网关1 route outside 221.8.0.0 255.254.0.0 网通网关1route outside 221.7.128.0 255.255.128.0 网通网关1 route outside 221.7.64.0 255.255.224.0 网通网关1 route outside 221.7.0.0 255.255.192.0 网通网关1 route outside 221.6.0.0 255.255.0.0 网通网关1route outside 221.4.0.0 255.254.0.0 网通网关1route outside 221.3.128.0 255.255.128.0 网通网关1 route outside 221.0.0.0 255.252.0.0 网通网关1route outside 218.67.128.0 255.255.128.0 网通网关1 route outside 218.60.0.0 255.254.0.0 网通网关1 route outside 218.56.0.0 255.252.0.0 网通网关1 route outside 218.28.0.0 255.254.0.0 网通网关1 route outside 218.26.0.0 255.254.0.0 网通网关1 route outside 218.24.0.0 255.254.0.0 网通网关1 route outside 218.12.0.0 255.255.0.0 网通网关1 route outside 218.11.0.0 255.255.0.0 网通网关1 route outside 218.10.0.0 255.255.0.0 网通网关1 route outside 218.8.0.0 255.254.0.0 网通网关1route outside 218.7.0.0 255.255.0.0 网通网关1route outside 202.111.160.0 255.255.224.0 网通网关1 route outside 202.111.128.0 255.255.224.0 网通网关1 route outside 202.110.192.0 255.255.192.0 网通网关1 route outside 202.110.64.0 255.255.192.0 网通网关1 route outside 202.110.0.0 255.255.192.0 网通网关1 route outside 202.108.0.0 255.255.0.0 网通网关1 route outside 202.107.0.0 255.255.128.0 网通网关1 route outside 202.106.0.0 255.255.0.0 网通网关1 route outside 202.102.224.0 255.255.224.0 网通网关1 route outside 202.102.128.0 255.255.192.0 网通网关1 route outside 202.99.224.0 255.255.224.0 网通网关1 route outside 202.99.192.0 255.255.224.0 网通网关1 route outside 202.99.128.0 255.255.192.0 网通网关1 route outside 202.99.64.0 255.255.192.0 网通网关1 route outside 202.99.0.0 255.255.192.0 网通网关1 route outside 202.98.0.0 255.255.224.0 网通网关1 route outside 202.97.192.0 255.255.192.0 网通网关1 route outside 202.97.160.0 255.255.224.0 网通网关1 route outside 202.97.128.0 255.255.224.0 网通网关1 route outside 202.96.64.0 255.255.224.0 网通网关1 route outside 202.96.0.0 255.255.192.0 网通网关1 route outside 61.189.0.0 255.255.128.0 网通网关1 route outside 61.182.0.0 255.255.0.0 网通网关1 route outside 61.181.0.0 255.255.0.0 网通网关1 route outside 61.180.128.0 255.255.128.0 网通网关1 route outside 61.179.0.0 255.255.0.0 网通网关1 route outside 61.176.0.0 255.255.0.0 网通网关1 route outside 61.168.0.0 255.255.0.0 网通网关1 route outside 61.167.0.0 255.255.0.0 网通网关1 route outside 61.163.0.0 255.255.0.0 网通网关1 route outside 61.162.0.0 255.255.0.0 网通网关1 route outside 61.161.128.0 255.255.128.0 网通网关1route outside 61.159.0.0 255.255.192.0 网通网关1route outside 61.158.128.0 255.255.128.0 网通网关1route outside 61.156.0.0 255.255.0.0 网通网关1route outside 61.148.0.0 255.254.0.0 网通网关1route outside 61.139.128.0 255.255.192.0 网通网关1route outside 61.138.128.0 255.255.192.0 网通网关1route outside 61.138.64.0 255.255.192.0 网通网关1route outside 61.138.0.0 255.255.192.0 网通网关1route outside 61.137.128.0 255.255.128.0 网通网关1route outside 61.136.64.0 255.255.192.0 网通网关1route outside 61.135.0.0 255.255.0.0 网通网关1route outside 61.134.96.0 255.255.224.0 网通网关1route outside 61.133.0.0 255.255.128.0 网通网关1route outside 61.55.0.0 255.255.0.0 网通网关1route outside 61.54.0.0 255.255.0.0 网通网关1route outside 61.52.0.0 255.254.0.0 网通网关1route outside 61.48.0.0 255.252.0.0 网通网关1route outside 60.220.0.0 255.252.0.0 网通网关1route outside 60.216.0.0 255.254.0.0 网通网关1route outside 60.208.0.0 255.248.0.0 网通网关1route outside 60.31.0.0 255.255.0.0 网通网关1route outside 60.24.0.0 255.248.0.0 网通网关1route outside 60.16.0.0 255.248.0.0 网通网关1route outside 60.13.128.0 255.255.128.0 网通网关1route outside 60.13.0.0 255.255.192.0 网通网关1route outside 60.12.0.0 255.255.0.0 网通网关1route outside 60.10.0.0 255.255.0.0 网通网关1route outside 60.8.0.0 255.254.0.0 网通网关1route outside 60.0.0.0 255.248.0.0 网通网关1route inside 192.168.0.0 255.255.255.0 192.1.5.1 1route inside 192.168.3.0 255.255.255.0 192.1.5.1 1route inside 192.168.4.0 255.255.255.0 192.1.5.1 1route inside 192.168.1.0 255.255.255.0 192.1.5.1 1route gov 21.0.0.0 255.0.0.0 21.36.255.1 1route ct 0.0.0.0 0.0.0.0 电信网关1timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00timeout uauth 0:05:00 absolutegroup-policy clientgroup internalgroup-policy clientgroup attributesvpn-idle-timeout 20split-tunnel-policy tunnelallwebvpnusername zmkm password B1MJgn6i2mF.NKjz encrypted username owen password G7ZPUlDLDg6W94ag encrypted username cisco password e1OkT/res2LB3io6 encryptedhttp server enablehttp 192.168.0.2 255.255.255.255 insidehttp 192.168.1.0 255.255.255.0 managementno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart crypto ipsec transform-set aaades esp-3des esp-md5-hmaccrypto ipsec transform-set aaades1 esp-3des esp-md5-hmaccrypto dynamic-map dynomap 10 set transform-set aaadescrypto dynamic-map dynomap1 20 set transform-set aaades1crypto map vpnpeer 20 ipsec-isakmp dynamic dynomapcrypto map vpnpeer interface outsidecrypto map vpnpeer1 30 ipsec-isakmp dynamic dynomap1crypto map vpnpeer1 interface ctisakmp identity addressisakmp enable outsideisakmp enable ctisakmp policy 10 authentication pre-shareisakmp policy 10 encryption 3desisakmp policy 10 hash md5isakmp policy 10 group 2isakmp policy 10 lifetime 86400tunnel-group huhao type ipsec-ratunnel-group huhao general-attributesaddress-pool vpdnauthorization-server-group LOCALdefault-group-policy clientgrouptunnel-group huhao ipsec-attributespre-shared-key *tunnel-group cnt type ipsec-ratunnel-group cnt general-attributesaddress-pool vpdnauthentication-server-group noneauthorization-server-group LOCALdefault-group-policy clientgrouptunnel-group cnt ipsec-attributespre-shared-key *telnet 0.0.0.0 0.0.0.0 insidetelnet timeout 5ssh 0.0.0.0 0.0.0.0 outsidessh 0.0.0.0 0.0.0.0 ctssh timeout 60console timeout 0dhcpd address 192.168.1.2-192.168.1.254 management dhcpd lease 3600dhcpd ping_timeout 50Cryptochecksum:38caa994b55d5b8bf627a1e972ed56ee : end。
ASA5520的双机A-A方式配置

拓朴图如下,现有点不明白怎么样将防火墙的接口怎样分配IP ,两个context中的路由指向同一个IP 网关,
原来防火墙的OUTSIDE :10。180。48。253 INS做成两个context a.contextb 两个接口的IP 该怎样做?????
ASA5520/test1(config-if)# ip address 192.168.10.1 255.255.255.0 standby
192.168.10.2
ASA5520(config)# failover //全局模式下面开始failover
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------在第二台ASA5520设备上配置
failover
剩下的ASA会自动同步它的配置
两个5520实现双A,非常好的方案啊,而且这个配置绝对可行,前几天刚刚做过实验了,我觉得八楼的兄弟把中文解释都写出来了,
值得借鉴啊,等有空的时候,我也把做双A的完整配置写出来的
用透明模式完成比较好
在65上起两个VLAN
能給一份完整的配置嗎。特別是兩臺FIREWALL都在透明模式下的,如何做A/A,謝謝!!
ASA5520(config-fover-group)# preempt //配置抢占参数
ASA5520(config-fover-group)# replication http
ASA5520双机配置案例(带状态state link的双机配置AA模式 带状态的多个state link接口)

hostname asa-1enable password cisco!interface GigabitEthernet0/0nameif insidesecurity-level 100ip address 192.200.31.249 255.255.255.192 standby 192.200.31.248!interface GigabitEthernet0/1description LAN Failover Interface(做failover link的接口不需要做地址配置)!interface GigabitEthernet0/2description STATE Failover Interface!interface GigabitEthernet0/3nameif outsidesecurity-level 100ip address 192.200.31.4 255.255.255.224 standby 192.200.31.5!interface Management0/0shutdownnameif managementsecurity-level 100ip address 10.168.1.1 255.255.255.0management-only!same-security-traffic permit inter-interface!failoverfailover lan unit primaryfailover lan interface faillink(自己起的failover名字)GigabitEthernet0/1(心跳线接口)failover polltime unit 1 holdtime 3failover link statelink GigabitEthernet0/2failover interface ip faillink 10.168.100.1 255.255.255.0 standby 10.168.100.2 failover interface ip statelink 10.168.101.1 255.255.255.0 standby 10.168.101.2 monitor-interface outsidemonitor-interface insideicmp permit any insideicmp permit any outsideroute inside 192.200.31.32 255.255.255.224 192.200.31.250 1route inside 192.200.31.64 255.255.255.192 192.200.31.250 1route inside 192.200.31.128 255.255.255.192 192.200.31.250 1route inside 192.200.31.192 255.255.255.192 192.200.31.250 1route outside 0.0.0.0 0.0.0.0 192.200.31.1 1telnet 0.0.0.0 0.0.0.0 insidetelnet 0.0.0.0 0.0.0.0 outside!hostname asa-2enable password 2KFQnbNIdI.2KYOU encryptedpasswd 2KFQnbNIdI.2KYOU encryptednamesno dns-guard!interface Ethernet0/0nameif insidesecurity-level 100ip address 192.200.31.249 255.255.255.192 standby 192.200.31.248 !interface Ethernet0/1description LAN Failover Interface!interface Ethernet0/2description STATE Failover Interfaceshutdown!interface Ethernet0/3nameif outsidesecurity-level 100ip address 192.200.31.4 255.255.255.224 standby 192.200.31.5!interface Management0/0nameif managementsecurity-level 100ip address 10.168.1.1 255.255.255.0management-only!no ftp mode passiveclock timezone CST 8same-security-traffic permit inter-interfacepager lines 24logging asdm informationalmtu inside 1500mtu outside 1500mtu management 1500failoverfailover lan unit primaryfailover lan interface faillink Ethernet0/1failover polltime unit 1 holdtime 3failover link statelink Ethernet0/2failover interface ip faillink 10.168.100.1 255.255.255.0 standby 10.168.100.2 failover interface ip statelink 10.168.101.1 255.255.255.0 standby 10.168.101.2 icmp permit any insideicmp permit any outsideno asdm history enablearp timeout 14400route inside 192.200.31.128 255.255.255.192 192.200.31.250 1route inside 192.200.31.64 255.255.255.192 192.200.31.250 1route inside 192.200.31.32 255.255.255.224 192.200.31.250 1route outside 0.0.0.0 0.0.0.0 192.200.31.1 1timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00timeout uauth 0:05:00 absolutehttp server enableno snmp-server locationno snmp-server contactcrypto ipsec security-association lifetime seconds 28800crypto ipsec security-association lifetime kilobytes 4608000telnet 0.0.0.0 0.0.0.0 insidetelnet 0.0.0.0 0.0.0.0 outsidetelnet timeout 5ssh timeout 5console timeout 0dhcpd ping_timeout 50!<--- More --->class-map inspection_defaultmatch default-inspection-traffic!!policy-map global_policyclass inspection_defaultinspect dns maximum-length 512inspect ftpinspect h323 h225inspect h323 rasinspect rshinspect rtspinspect esmtpinspect sqlnetinspect skinnyinspect sunrpcinspect xdmcpinspect sipinspect netbiosinspect tftp!Cryptochecksum:a0b294ccce697e561e4e0fcf9e1cae91 : endasa-2#### END LOG - DATE: 090313, TIME: 024509 ###。
ciscoasa5520的基本配置
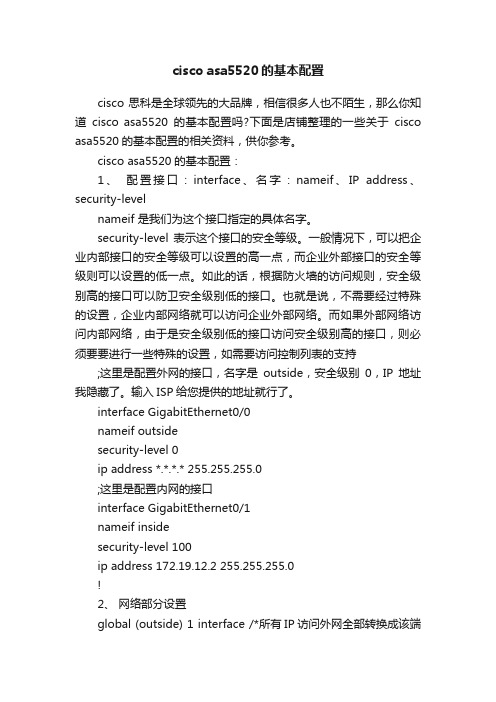
cisco asa5520的基本配置cisco思科是全球领先的大品牌,相信很多人也不陌生,那么你知道cisco asa5520的基本配置吗?下面是店铺整理的一些关于cisco asa5520的基本配置的相关资料,供你参考。
cisco asa5520的基本配置:1、配置接口:interface、名字:nameif、IP address、security-levelnameif 是我们为这个接口指定的具体名字。
security-level表示这个接口的安全等级。
一般情况下,可以把企业内部接口的安全等级可以设置的高一点,而企业外部接口的安全等级则可以设置的低一点。
如此的话,根据防火墙的访问规则,安全级别高的接口可以防卫安全级别低的接口。
也就是说,不需要经过特殊的设置,企业内部网络就可以访问企业外部网络。
而如果外部网络访问内部网络,由于是安全级别低的接口访问安全级别高的接口,则必须要要进行一些特殊的设置,如需要访问控制列表的支持;这里是配置外网的接口,名字是outside,安全级别0,IP地址我隐藏了。
输入ISP给您提供的地址就行了。
interface GigabitEthernet0/0nameif outsidesecurity-level 0ip address *.*.*.* 255.255.255.0;这里是配置内网的接口interface GigabitEthernet0/1nameif insidesecurity-level 100ip address 172.19.12.2 255.255.255.0!2、网络部分设置global (outside) 1 interface /*所有IP访问外网全部转换成该端口的IP出去,即PATnat (inside) 1 0.0.0.0 0.0.0.0 /*表示转换网段中的所有地址。
定义内部网络地址将要翻译成的全局地址或地址范围route outside 0.0.0.0 0.0.0.0 *.*.*.* 1 /*设置外网路由的网关,最后的1是路由的跳数route inside 172.19.74.0 255.255.254.0 172.19.12.1 1 /*设定路由回指到内部的子网route inside 172.19.76.0 255.255.252.0 172.19.12.1 13、 !开启asdmhttp server enablehttp 0.0.0.0 0.0.0.0 inside!允许内网用户使用telnet连接防火墙telnet 0.0.0.0 0.0.0.0 insidetelnet timeout 5!允许内网用户使用ssh连接防火墙ssh 0.0.0.0 0.0.0.0 insidessh timeout 5。
asg5520 使用手册
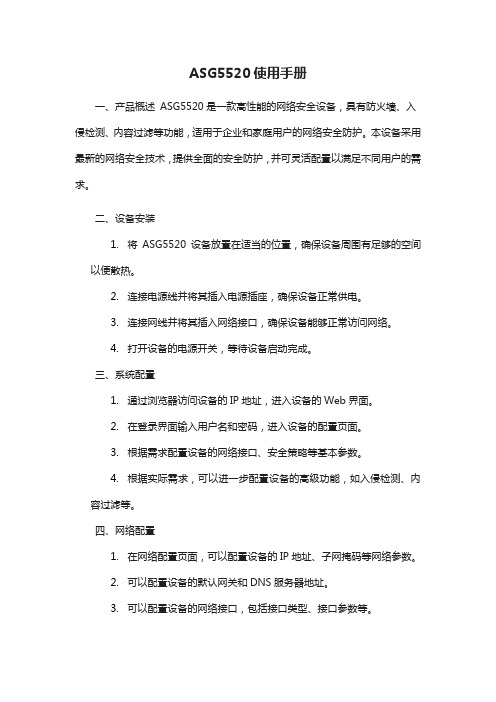
ASG5520使用手册一、产品概述ASG5520是一款高性能的网络安全设备,具有防火墙、入侵检测、内容过滤等功能,适用于企业和家庭用户的网络安全防护。
本设备采用最新的网络安全技术,提供全面的安全防护,并可灵活配置以满足不同用户的需求。
二、设备安装1.将ASG5520设备放置在适当的位置,确保设备周围有足够的空间以便散热。
2.连接电源线并将其插入电源插座,确保设备正常供电。
3.连接网线并将其插入网络接口,确保设备能够正常访问网络。
4.打开设备的电源开关,等待设备启动完成。
三、系统配置1.通过浏览器访问设备的IP地址,进入设备的Web界面。
2.在登录界面输入用户名和密码,进入设备的配置页面。
3.根据需求配置设备的网络接口、安全策略等基本参数。
4.根据实际需求,可以进一步配置设备的高级功能,如入侵检测、内容过滤等。
四、网络配置1.在网络配置页面,可以配置设备的IP地址、子网掩码等网络参数。
2.可以配置设备的默认网关和DNS服务器地址。
3.可以配置设备的网络接口,包括接口类型、接口参数等。
4.可以配置设备的路由表,以实现不同网络之间的通信。
五、安全管理1.在安全管理页面,可以配置设备的安全策略,包括访问控制、防火墙规则等。
2.可以配置设备的身份认证和访问控制,以确保设备的安全性。
3.可以配置设备的安全日志,以便对安全事件进行记录和分析。
4.可以定期更新设备的病毒库和安全补丁,以确保设备的安全性。
六、故障排除1.检查设备的电源和网线是否正常连接。
2.检查设备的网络接口是否正常工作。
3.检查设备的配置是否正确。
4.如果以上步骤无法解决问题,可以尝试重启设备,看是否能够解决问题。
如果问题仍然存在,建议联系技术支持人员进行进一步排查和解决。
七、高级设置1、可以配置设备的定时任务,以便自动执行一些计划任务。
2、可以配置设备的SNMP参数,以便通过SNMP协议进行管理。
3、可以配置设备的流量控制参数,以便对设备的数据流量进行管理。
CISCO 5520防火墙配置实例

CISCO 5520防火墙配置实例本人在项目中已经两次接触到思科5500系列防火墙的配置应用了,根据项目的需求不同,详细的配置也不一样,因此汇总了一个通用版本的思科5500系列防火墙的配置,不详之处,请各位大虾给予指点,谢谢!CD-ASA5520# show run : Saved:ASA Version 7.2(2)!hostname CD-ASA5520 &nb sp; //给防火墙命名domain-name default.domain.invalid //定义工作域enable password 9jNfZuG3TC5tCVH0 encrypted //进入特权模式的密码namesdns-guard !内网接口:duplex full //接口作工模式:xx,半双,自适应nameif inside //为端口命名:内部接口inside security-level 100 //设置安全级别0~100值越大越安全ip address 192.168.1.1 255.255.255.0 //设置本端口的IP地址!外网接口nameif outside //为外部端口命名:外部接口outsidesecurity-level 0ip address 202.98.131.122 255.255.255.0 //IP地址配置!nameif dmzsecurity-level 50ip address 192.168.2.1 255.255.255.0!shutdownno nameifno security-levelno ip address !防火墙管理地址shutdownno nameifno security-levelno ip address !passwd 2KFQnbNIdI.2KYOU encryptedftp mode passiveclock timezone CST 8dns server-group DefaultDNSdomain-name default.domain.invalidaccess-list outside_permit extended permit tcp any interface outside eq 3389//访问控制列表access-list outside_permit extended permit tcp any interface outside range 300 30010//允许外部任何用户可以访问outside 接口的300-30010的端口。
【免费下载】asa5520防火墙透明模式的配置例子
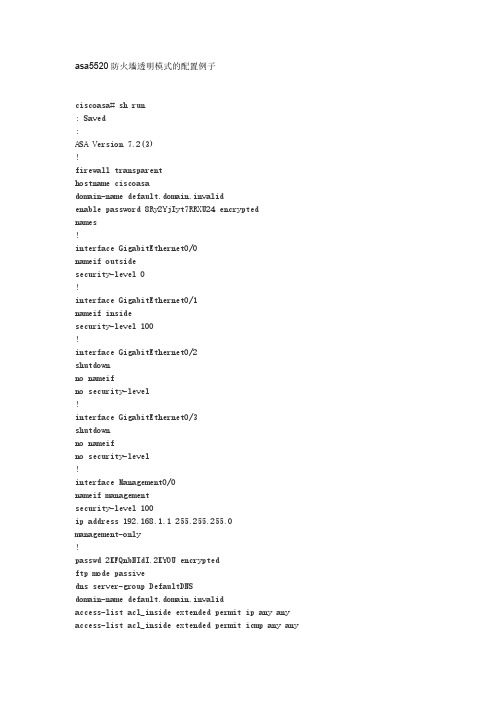
parameters message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect pptp ! service-policy global_policy global username cisco password 3USUcOPFUiMCO4Jk encrypted prompt hostname context Cryptochecksum:4682fd668f251c28d32a0cb82a3ac5f3 : end ciscoasa#
access-list acl_outside extended permit tcp any any eq 3306 access-list acl_outside extended permit tcp any any eq www access-list acl_outside extended permit tcp any any eq 8080 access-list acl_outside extended permit tcp any any eq https access-list acl_outside extended permit tcp any any eq sqlnet access-list acl_outside extended permit tcp any any eq ftp access-list acl_outside extended permit tcp any any eq 1433 access-list acl_outside extended permit esp any any access-list acl_outside extended permit udp any any eq isakmp access-list acl_outside extended permit tcp any any eq pop3 access-list acl_outside extended permit tcp any any eq smtp access-list acl_outside extended permit icmp any any pager lines 24 mtu outside 1500 mtu inside 1500 mtu management 1500 ip address 172.16.177.208 255.255.255.0 no failover icmp unreachable rate-limit 1 burst-size 1 asdm image disk0:/ASDM-523.BIN no asdm history enable arp timeout 14400 access-group acl_outside in interface outside access-group acl_inside in interface inside timeout xlate 3:00:00 timeout conn 0:20:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolute http server enable http 192.168.1.0 255.255.255.0 management http 0.0.0.0 0.0.0.0 inside no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5 ssh timeout 5 console timeout 0 ! class-map inspection_fault match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map
cisco asa5520 配置讲解幻灯片PPT

第二层
asa802(config)# class-map type inspect http http_url_class asa802(config-cmap)# match not request header host regex class url_class
asa802(config)# policy-map type inspect http http_url_policy asa802(config-pmap)# class http_url_class
asa802(config-pmap-c)# drop-connection log 采用哪种思路实 现要由具体情况 而定
第三层
asa802(config)# regex url1 "\.out\.com" asa802(config)# class-map type regex match-any url_class asa802(config-cmap)# match regex url1
技能展示了解cisco防火墙产品系列会对asa安全设备进行基本配置会配置asa安全设备的高级应用本章结构cisco防火墙cisco防火墙简介asa基本配置配置接口配置路由asa高级应用配置远程管理接入配置acl配置网络地址转换url过滤日志管理配置安全功能cisco防火墙简介硬件与软件防火墙软件防火墙硬件防火墙芯片级防火墙asa安全设备asa5500系列常见型号
cisco asa5520 配置讲解幻灯片 PPT
本PPT课件仅供大家学习使用 请学习完及时删除处理 谢谢!
课程回顾
在IP首部中,与分片有关的字段是哪几个? 终止TCP连接可以通过哪个控制位来实现? UDP有没有流量控制?
ASA5520的硬件介绍及相关配置
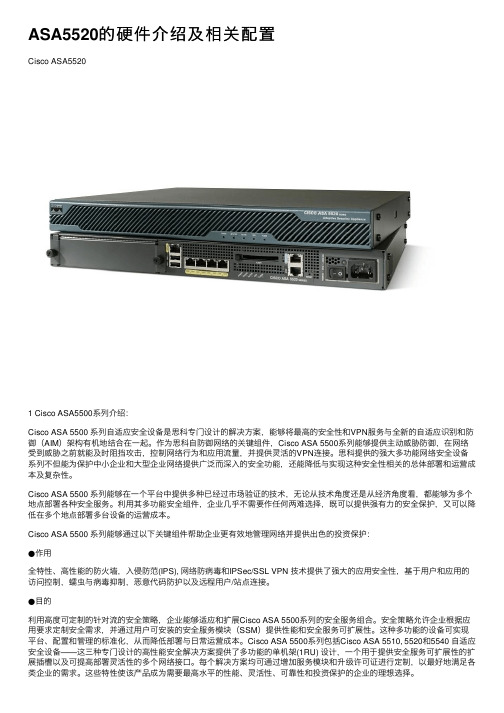
ASA5520的硬件介绍及相关配置Cisco ASA55201 Cisco ASA5500系列介绍:Cisco ASA 5500 系列⾃适应安全设备是思科专门设计的解决⽅案,能够将最⾼的安全性和VPN服务与全新的⾃适应识别和防御(AIM)架构有机地结合在⼀起。
作为思科⾃防御⽹络的关键组件,Cisco ASA 5500系列能够提供主动威胁防御,在⽹络受到威胁之前就能及时阻挡攻击,控制⽹络⾏为和应⽤流量,并提供灵活的VPN连接。
思科提供的强⼤多功能⽹络安全设备系列不但能为保护中⼩企业和⼤型企业⽹络提供⼴泛⽽深⼊的安全功能,还能降低与实现这种安全性相关的总体部署和运营成本及复杂性。
Cisco ASA 5500 系列能够在⼀个平台中提供多种已经过市场验证的技术,⽆论从技术⾓度还是从经济⾓度看,都能够为多个地点部署各种安全服务。
利⽤其多功能安全组件,企业⼏乎不需要作任何两难选择,既可以提供强有⼒的安全保护,⼜可以降低在多个地点部署多台设备的运营成本。
Cisco ASA 5500 系列能够通过以下关键组件帮助企业更有效地管理⽹络并提供出⾊的投资保护:●作⽤全特性、⾼性能的防⽕墙,⼊侵防范(IPS), ⽹络防病毒和IPSec/SSL VPN 技术提供了强⼤的应⽤安全性,基于⽤户和应⽤的访问控制,蠕⾍与病毒抑制,恶意代码防护以及远程⽤户/站点连接。
●⽬的利⽤⾼度可定制的针对流的安全策略,企业能够适应和扩展Cisco ASA 5500系列的安全服务组合。
安全策略允许企业根据应⽤要求定制安全需求,并通过⽤户可安装的安全服务模块(SSM)提供性能和安全服务可扩展性。
这种多功能的设备可实现平台、配置和管理的标准化,从⽽降低部署与⽇常运营成本。
Cisco ASA 5500系列包括Cisco ASA 5510, 5520和5540 ⾃适应安全设备——这三种专门设计的⾼性能安全解决⽅案提供了多功能的单机架(1RU) 设计,⼀个⽤于提供安全服务可扩展性的扩展插槽以及可提⾼部署灵活性的多个⽹络接⼝。
cisco ASA5520 详细配置

nat (inside) 0 access-list No-nat
(anyconnect ssl-vpn)
webvpn
enable outside
username sxwz008 password 1234567
username sxwz009 password 1234567
username sxwz010 password 1234567
username sxwz011 password 1234567
username sxwz012 password 1234567
username sxwz013 password 1234567
username sxwz014 password 1234567
username sxwz015 password 1234567
(IPsecDynamicLAN-to-LAN VPN 动态VPN)
isakmp enable outside
nat-con
nat (inside) 1 0 0
global (outside) 1 interface
(开启ASDM)
http server enable 443
http 0 0 inside
http 0 0 outside
username sxwz password cisco privilege 15
group-policy SSLCLientPolicy internal
ASA5520防火墙VPN配置详解

ASA Version 7.2(3)!hostname ciscoasaenable password 8Ry2YjIyt7RRXU24 encryptednames======================配置接口IP====================================== interface E0/0nameif insidesecurity-level 100ip address 10.1.1.1 255.255.255.0!interface E0/1nameif outsidesecurity-level 0ip address 222.222.222.1 255.255.255.0=======================定义内外网数据流ACL========================access-list INSIDE_IN extended permit icmp any anyaccess-list INSIDE_IN extended permit IP any anyaccess-list OUTSIDE_IN extended permit icmp any anyaccess-list NO_NAT extended permit ip 10.1.1.0 255.255.255.0 192.168.1.0 255.25 5.0.0access-list NO_NAT extended permit ip 192.168.1.0 255.255.255.0 10.1.1.0 255.25 5.255.0======================定义分配拨号用户地址池===========================ip local pool vpnpool 192.168.1.100-192.168.1.199======================NAT转换语句=================================global (outside) 1 interfacenat (inside) 0 access-list NO-NATnat (inside) 1 10.1.1.0 255.255.255.0======================路由==========================================route outside 0.0.0.0 0.0.0.0 222.222.222.2 1========================应用ACL到接口==============================access-group INSIDE_IN in interface insideaccess-group OUTSIDE_IN in interface outside========================定义加密算法及加密图=====================crypto ipsec transform-set ESP esp-des esp-md5-hmaccrypto dynamic-map outside_dyn_map 10 set transform-set ESPcrypto dynamic-map outside_dyn_map 10 set reverse-routecrypto map outsidemap 10 ipsec-isakmp dynamic outside_dyn_mapcrypto map outsidemap interface outsidecrypto isakmp enable outsidecrypto isakmp policy 1authentication pre-shareencryption deshash md5group 2=======================定义策略组=====================service-policy global_policy globalgroup-policy MYGROUP internalgroup-policy MYGROUP attributesvpn-tunnel-protocol IPSec=====================配置用户和密码==================username cisco password cisco============定义隧道组并应用拨号地址池,定义共享密钥================== tunnel-group hivpn type ipsec-ratunnel-group hivpn general-attributesaddress-pool vpnpooldefault-group-policy MYGROUPtunnel-group hivpn ipsec-attributespre-shared-key ciscoprompt hostname contextCryptochecksum:d4fe4080014deada00b8e2d2952fb69b: endciscoasa#。
思科防火墙ASA5520配置

思科防火墙ASA5520配置博客分类:网络思科防火墙ASA5520配置:目的:1、内网可以上网2、内网可以访问DMZ区域的服务器3、外网可以通过公网IP访问DMZ区域的服务器要求:1、内网的网段192.168.10.02、DMZ的网段192.168.5.03、外网IP地址:200.200.200.82 200.200.200.83 网关255.255.255.248(这个地址一般是运营商提供)4、外网路由:200.200.200.815、DMZ区域的服务器IP地址:192.168.5.2步骤1:配置接口inside、outside和dmzinterface g0/0speed autoduplex autonameif insideSecurity-level 100ip address 192.168.10.1 255.255.255.0no shutexitinterface g0/1speed autoduplex autonameif outsideSecurity-level 0ip address 200.200.200.82 255.255.255.248 no shutexitinterface g0/2speed autoduplex autonameif dmzSecurity-level 50ip address 192.168.5.1 255.255.255.0no shutexit步骤2、添加外网路由route outside 0 0 200.200.200.81步骤3、做nat转换,使得内网可以上网,同时内网可以访问dmz区域的服务器nat-controlnat (inside) 1 192.168.10.0 255.255.255.0global (outside) 1 interfaceglobal (dmz) 1 interface步骤4、做静态nat,将对外网IP的访问转换到dmz区域的服务器static (dmz,outside) 200.200.200.83 192.168.5.2 netmask255.255.255.255 dns注意:这里的外网IP不是outside的接口地址,是另外一个公网IP步骤5、配置ACL规则,允许外网访问DMZ服务器access-list out_dmz extended permit tcp any host 200.200.200.83 eq wwwaccess-group out_dmz in interface outside到此配置结束,正常情况下上面的要求都可以实现了,但是可能由于每个机房的环境不一样,结果会有一些错误。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
security-level 100 //设置安全级别 0~100 值越大越安全
ip address 192.168.1.1 255.255.255.0 //设置本端口的IP地址
arp timeout 14400 //arp空闲时间为14400秒
global (outside) 1 interface //由于没有配置NAT 故这里是不允许内部用户上INTERNET
static (dmz,outside) tcp interface 30000 192.168.2.2 30000 netmask 255.255.255.255
access-group outside_permit in interface outside
//把outside_permit控制列表运用在外部接口的入口方向。
route outside 0.0.0.0 0.0.0.0 202.98.131.126 1 //定义一个默认路由。
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
//配置转集(定义了IPSC隧道使用的加密和信息完整性算法集合)
crypto dynamic-map vpn_dyn_map 10 set transform-set ESP-DES-MD5
//为动态加密图条目定义传换集
crypto map outside_map 10 ipsec-isakmp dynamic vpn_dyn_map
group-policy vpnclient attributes //设置vpnclient组策略的参数
wins-server value 192.168.1.10 //定义WINS-SERVER 的IP地址。
dns-server value 192.168.1.10 61.139.2.69 //定义dns-server的IP地址。
static (dmz,outside) tcp interface 30002 192.168.2.2 30002 netmask 255.255.255.255
static (dmz,outside) tcp interface 30003 192.168.2.2 30003 netmask 255.255.255.255
logging enable //启动日志功能
logging asdm informational
mtu inside 1500 内部最大传输单元为1500字节
mtu outside 1500
mtu dmz 1500
ip local pool vpnclient 192.168.200.1-192.168.200.200 mask 255.255.255.0
static (dmz,outside) tcp interface 30010 192.168.2.2 30010 netmask 255.255.255.255
static (dmz,outside) tcp interface 3389 192.168.2.2 3389 netmask 255.255.255.255
no nameif
no security-level
no ip address
!
interface Management0/0 //防火墙管理地址
shutdown
no nameif
no security-level
no ip address
!
passwd 2KFQnbNIdI.2KYOU encrypted
//定义一个命名为vpnclient的IP地址池,为remote用户分配IP地址
no failover
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-522.bin
no asdm history enable
!
interface GigabitEthernet0/2
nameif dmz
security-level 50
ip address 192.168.2.1 255.255.255.0
!
interface GigabitEthernet0/3
shutdown
//端口映射 可以解决内部要公布的服务太多,而申请公网IP少问题。
static (dmz,outside) tcp interface 30001 192.168.2.2 30001 netmask 255.255.255.255
//把dmz区192.168.2.2 30002 映射给外部30002端口上。
crypto isakmp policy 20 //isakmmp权值,值越小权值越高
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
//snmp的默认配置
crypto ipsec transform-set ESP-DES-MD5 esp-des esp-md5-hmac
static (dmz,outside) tcp interface 30006 192.168.2.2 30006 netmask 255.255.255.255
static (dmz,outside) tcp interface 30007 192.168.2.2 30007 netmask 255.255.255.255
timeout uauth 0:05:00 absolute
------------定义一个命名为vpnclient的组策略-------------------------
group-policy vpnclient internal //创建一个内部的组策略。
!
interface GigabitEthernet0/1 //外网接口
nameif outside //为外部端口命名 :外部接口outside
security-level 0
ip address 202.98.131.122 255.255.255.0 //IP地址配置
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
vpn-idle-timeout none
vpn-session-timeout none
vpn-tunnel-protocol IPSec
username test password P4ttSyrm33SV8TYp encrypted privilege 0
//创建一个远程访问用户来访问安全应用
//创建一个使用动态加密条目的加密图
crypto map outside_map interface outside
//将 outside_map加密图应用到outside端口
------------配置IKE--------------
crypto isakmp enable outside //在ostside 接口启动ISAKMP
vpn-idle-timeout none //终止连接时间设为默认值
vpn-session-timeout none //会话超时采用默认值
vpn-tunn
username cisco password 3USUcOPFUiMCO4Jk encrypted
http server enable //启动HTTP服务
http 0.0.0.0 0.0.0.0 inside //允许内部主机HTTP连接
no snmp-server location
static (dmz,outside) tcp interface 30008 192.168.2.2 3008 netmask 255.255.255.255
static (dmz,outside) tcp interface 30009 192.168.2.2 30009 netmask 255.255.255.255
group-policy l2lvpn internal
group-policy l2lvpn attributes
wins-server value 192.168.1.10
dns-server value 192.168.1.10 61.139.2.69
vpn-simultaneous-logins 3
ftp mode passive
clock timezone CST 8
dns server-group DefaultDNS
domain-name default.domain.invalid
access-list outside_permit extended permit tcp any interface outside eq 3389
static (dmz,outside) tcp interface 30004 192.168.2.2 30004 netmask 255.255.255.255
static (dmz,outside) tcp interface 30005 192.168.2.2 30005 netmask 255.255.255.255
