-最新+CCNA第二学期章节测试++第十章+答案
CCNA 2 Chapter 10 V4.0 Answers

1. What action does a link-state router take immediately upon receipt of an LSP from a neighboring router?floods the LSP to neighborscalculates the SPF algorithmruns the Bellman-Ford algorithmcomputes the best path to the destination network2. Why is it difficult for routing loops to occur in networks that use link-state routing?Each router builds a simple view of the network based on hop count. Routers flood the network with LSAs to discover routing loops.Each router builds a complete and synchronized view of the network. Routers use hold-down timers to prevent routing loops.3.Refer to the exhibit. What kind of information would be seen in an LSP sent from router JAX to router ATL?hop countuptime of the routecost of the linka list of all the routing protocols in use4. To achieve network convergence, what three steps does each link state router take? (Choose three.)use automatic summarization to reduce the size of routing tablesbuild a Link State Packet (LSP) containing the state of each directly connected linkflood the LSP to all neighbors, who then store all LSPs received in a databasediscover neighbors and establish adjacencies using the hello packet sent at regular intervalsconstruct a complete map of the topology and compute the best path to each destination networkuse the DUAL FSM to select efficient, loop-free paths, and insert routes into the routing table5.Refer to the exhibit. When Router D is configured to use a link-state routing protocol and is added to the network, what is the first thing that it does to begin learning the network topology?It sends LSP packets to Routers B and C.It sends LSP packets to all routers in the network.It sends Hello packets to all routers in the network.It sends information about its directly connected neighbors to Routers A and E.It sends information about its directly connected neighbors to all routers in the network.It learns about its directly connected networks when its interfaces reach the up state.6. A new network administrator is given the task of selecting an appropriate dynamic routing protocol for a software development company. The company has over 100 routers, uses CIDR and VLSM, requires fast convergence, and uses both Cisco and non-Cisco equipment. Which routing protocol is appropriate for this company?RIP version 2IGRPEIGRPOSPFBGP7. What two events will cause a link state router to send LSPs to all neighbors? (Choose two.)30 second timer expireswhenever the network topology changesimmediately after the Bellman-Ford algorithm has runimmediately after the DUAL FSM has built the topology databaseupon initial startup of router or routing protocol8. What is the final step in the link state routing process? successors are placed into the routing tableSPF computes best path to each destination networkLSPs are flooded to all neighbors to converge the networkDUAL algorithm is run to find best path to destination networks9.Refer to the exhibit. What does JAX do with link-state packets from ORL? sends out its updated routing table to both ORL and BOS routerssends out the individual link-state packets out the interface connected to BOSqueries BOS to see if it has a better routeonly adds it to the local routing table and performs no other actions10. What two statements correctly describe the link state routing process? (Choose two.)each router in the area floods LSPs to all neighborsall routers in the area have identical link state databasesLSPs use the reserved multicast address of 224.0.0.10 to reach neighbors routing loops are prevented by running the Diffusing Update Algorithm (DUAL)Reliable Transport Protocol (RTP) is the protocol used by for the delivery and reception of LSPs11. Which database or table must be identical on all link-state routers within an area in order to construct an accurate SPF tree?routing tableadjacency tablelink-state databaseneighbor tabletopology database12.Refer to the exhibit. Which statement correctly describes the path traffic would take from the 10.0.0.0/24 network to the 192.168.1.0/24 network if a link-state routing protocol was in use?BOS -> ATL because this path is the least hopsBOS -> ATL because this path is highest costBOS -> ORL -> JAX -> ATL because this path is the lowest costtraffic would load balance across all links13. What feature do modern link-state protocols provide to minimize processing and memory requirements?splitting routing topologies into smaller areasassigning lower process priorities to route calculationsusing update timers to restrict routing updatesstrict split horizon rules to reduce routing table entries14. What speeds up convergence in a network using link-state routing? updates triggered by network changesupdates sent at regular intervalsupdates sent only to directly connected neighborsupdates that include complete routing tables15. Which algorithm is run by link-state routing protocols to calculate the shortest path to destination networks?DUALDijkstraBellman-FordDiffie-Hellman16. What are some of the advantages of using a link-state routing protocol instead of a distance vector routing protocol? (Choose two.)The topology database eliminates the need for a routing table.Frequent periodic updates are sent to minimize the number of incorrect routes in the topological database.Routers have direct knowledge of all links in the network and how they are connected.After the inital LSA flooding, they generally require less bandwidth to communicate changes in a topology.Link-state protocols require less router processor power than distance vector protocols.17.Refer to the exhibit. If all routers and interfaces are configured to use a link-state routing protocol, from which routers will router D receive hello packets?A and EB and CA, B, C, and EC only18. Which two routing protocols use Dijkstra’s shortest path first algorithm? (Choose two.)RIPv1RIPv2IS-ISBGPEIGRPOSPF19. When are link-state packets sent to neighbors?every 30 secondsevery 180 secondsafter the holddown time expireswhen a link goes up or downwhen a routing loop occurs20. What are two advantages of using a link-state routing protocol instead of a distance vector routing protocol? (Choose two.)The topology database eliminates the need for a routing table.Each router independently determines the route to each network.Link-state protocols require less router processor power than distance vector protocols.After the inital LSP flooding, they generally require less bandwidth to communicate changes in a topology.Frequent periodic updates are sent to minimize the number of incorrect routes in the topological database.21. To achieve network convergence, what three steps does each link state router take? (Choose three.)use automatic summarization to reduce the size of routing tables build a Link State Packet (LSP) containing the state of each directly connected linkflood the LSP to all neighbors, who then store all LSPs received in a databasesend hello packages at regular intervals to discover neighbors and establish adjacenciesconstruct a complete map of the topology and compute the best path to each destination networkuse the DUAL FSM to select efficient, loop-free paths, and insert routes into the routing table。
ccna章节与期末答案

第一章:正确答案:2.4.5解析:由于不需要使用网络设备和专用服务器,对等网络易于创建,复杂性更低,且成本更少。
而且对等网络也没有集中管理。
这种网络安全性更低,不可扩展,而且那些同时充当客户端和服务器的设备可能性能更差正确答案:1解析:正确答案:解析:选择网络介质的条件包括:所选介质可以成功传送信号的距离、要安装所选介质的环境、必须传输的数据量和速度以及介质和安装的成本。
正确答案:3和4解析:终端设备上的应用程序可以生成数据,更改数据内容并且负责启动封装过程。
正确答案:1和4解析:终端设备会发出通过网络传输的数据。
中间设备会在链路发生故障时通过备用路径传输数据,并且会过滤数据传输以增强安全性。
网络介质提供网络消息的传输通道。
正确答案:4解析:外联网是公司外部的人或企业合作伙伴访问数据的网络区域。
内部网只描述通常仅供内部人员访问的网络区域。
当设备连接到有线网络时,有线 LAN 会受 BYOD(自带设备)影响。
使用大学无线 LAN 的设备多为平板电脑和智能手机。
大学生主要使用无线 WAN 来访问他们的手机运营商网络。
.正确答案:2解析:由于通过 Internet 可以联系在线供应商,所以家庭用户通过 Internet 进行网上购物。
内联网基本上是仅供内部使用的局域网。
外联网是外部合作伙伴访问组织内部特定资源的网络。
家庭用户并不一定使用 LAN 来访问 Internet。
例如,PC 可以通过调制解调器直接连接到 ISP。
正确答案:1解析:内部网这个术语用于表示一个组织的私有局域网和广域网连接。
内部网的设计旨在仅允许该组织的成员、员工或其他获得授权的人员进行访问。
正确答案:2和4解析:电缆和 DSL 均能实现高带宽、始终联网,并提供到主机计算机或 LAN 的以太网连接。
10正确答案:2和3解析:移动电话连接需要使用移动电话网络。
卫星连接通常用于家庭或企业外部不便使用物理布线的位置。
11正确答案:2解析:当对网络资源的请求超出了可用容量时,网络就会变得拥堵。
新CCNA第章考试练习题完整版

新C C N A第章考试练习题HEN system office room 【HEN16H-HENS2AHENS8Q8-HENH1688】1.填空题。
请勿使用缩写。
网络工程师正在对网络上新的 VLAN 配置进行故障排除。
哪个命令用于显示交换机上存在的 VLAN 的列表Show vlan2.在多层交换机的多个 VLAN 之间,流量如何路由?流量通过内部 VLAN 接口路由。
流量通过子接口路由。
流量通过物理接口路由。
流量从所有物理接口广播出去。
3.GigabitEthernet 0/ 上缺少 no shutdown 命令GigabitEthernet 0/0 接口缺少 IP 地址。
在 GigabitEthernet 0/ 上配置了错误的 VLAN在 GigabitEthernet 0/ 上配置了错误的 IP 地址。
4.哪种类型的 VLAN 间通信设计需要配置多个子接口?单臂路由器通过多层交换机路由传统 VLAN 间路由管理 VLAN 的路由5.请参见图示。
VLAN 之间没有通信。
可能是什么问题?交换机和路由器之间都存在双工问题。
路由器上使用了错误的端口。
Gi1/1 交换机端口不处于中继模式。
默认网关没有针对每个 VLAN 进行配置。
6.路由器会将该数据包从接口 FastEthernet 0/ 转发出去。
路由器会将该数据包从接口 FastEthernet 0/ 和接口 FastEthernet 0/ 转发出去。
路由器会将该数据包从接口 FastEthernet 0/ 转发出去。
路由器将丢弃该数据包。
路由器会将该数据包从接口 FastEthernet 0/ 转发出去。
7.请参见图示。
网络管理员已使用上述命令配置了路由器 CiscoVille,从而提供 VLAN 间路由。
连接到路由器 CiscoVille 的 Gi0/0 接口的交换机上需要哪条命令,才能允许 VLAN 间路由?switchport mode trunkswitchport mode accessno switchportswitchport mode dynamic desirable8.打开 PT 练习。
完整版CCNA测试题库及答案

完整版CCNA测试题库及答案描述载波侦听多路由访问/冲突检测(CSMA/CD)的工作原理。
CSMA/CD是一种帮助设备均衡共享带宽的协议,可避免两台设备同时在网络介质上传输数据。
虽然他不能消除冲突,但有助于极大的减少冲突,进而避免重传,从而提高所的设备的数据传输效率。
区分半双工和全双工通信。
并指出两种方法的需求。
与半双工以太网使用一对导线不同,全双工以太网使用两队导线,全双工使用不同的导线来消除冲突,从而允许同时发送和接收数据,而半双工可接收或发送数据,但不能同时接收和发送数据,且仍会出现冲突。
要使用全双工,电缆两端的设备都必须支持全双工,并配置成一全双模式运行。
描述MAC地址的组成部分以及各部分包含的信息。
MAC(硬件)地址时一种使用十六进制表示的地址,长48位(6B)。
其中前24位(3B)称为OUI(Organizationally Unique Idebtifier,组织唯一表示符),有IEEE分配给NIC制造商;余下的部分呢唯一地标识了NIC识别十进制数对应的二进制值和十六进制值。
用这三种格式之一表示的任何数字都可以转换为其他两种格式,能够执行这种转换对理解IP地址和子网划分至关重要。
识别以太网帧中与数据链路层相关的字段。
在以太网中,与数据链路层相关的字段包括前导码,帧其实位置分隔符,目标MAC地址,源MAC地址,长度或者类型以及帧校验序列。
识别以太网布线相关的IEEE标准。
这些标准描述了各种电缆类型的功能和物理特征,包括(但不限于)10Base2、10Base5和10BaseT。
区分以太网电缆类型及其用途。
以太网电缆分3种:直通电缆,用于将PC或路由器的以太网接口连接到集线器或交换机;交叉电缆。
用于将集线器连接到集线器,集线器连接到交换机,交换机连接到交换机以及PC连接到PC;反转电缆,用于PC和路由器或交换机之间建立控制台连接。
描述数据封装过程及其在分组创建中的作用。
数据封装指的是在OSI模型各层给数据添加信息的过程,也成为分组创建。
CCNA认证基础课程-课后作业.习题答案
CCNA认证基础-习题分析讲义第一部分第一章1. Convert the binary number 10111010 into its hexadecimal equivalent. Select thecorrect answer from the list below. (3)1) 852) 903) BA4) A15) B36) 1C2. Convert the Hexadecimal number A2 into its Base 10 equivalent. Select thecorrect answer from the list below. (4)1) 1562) 1583) 1604) 1625) 1646) 1663. Which binary number is a representation of the decimal number 248? (3)1) 111010002) 111101003) 111110004) 111110104. Which of the following will test the internal loopback of a node? (3)1) ping 10.10.10.12) ping 192.168.1.13) ping 127.0.0.14) ping 223.223.223.2235) ping 255.255.255.2555. What can be verified by successfully pinging the reserved loopback address ona host? (2)1) Connectivity exists between two hosts on the LAN.2) The TCP/IP stack of the local host is configured correctly.3) A connection exists between a host and the default gateway.4) The route a packet takes from the local host to a remote host is valid.6. Which of the following commands could be used on a Windows-basedcomputer to view the current IP configuration of the system? (Choose two.) (3,4)1) configip2) ifconfig3) ipconfig4) winipcfg5) Winipconfig7.Refer to the exhibit. What must be configured on Host B to allow it to communicate withthe Host C? (Choose three.) (2,4,6)1)the MAC address of RTA router interface connected to Switch 12) a unique host IP address3)the IP address of Switch 14)the default gateway address5)the MAC address of Host C6)the subnet mask for the LAN8. What are important characteristics to consider when purchasing a networkinterface card? (Choose two.) (2,3)1) security used on the network2) media used on the network3) system bus used on the computer4) software installed on the network5) diagnostic tools installed on the network第二章1. Select the necessary information that is required to compute the estimated timeit would take to transfer data from one location to another. (Choose two.) (1,5)1) file size2) data format3) network in use4) type of medium5) bandwidth of the link2. Using the data transfer calculation T=S/BW, how long would it take a 4MB file tobe sent over a 1.5Mbps connection? (2)1) 52.2 seconds2) 21.3 seconds3) 6.4 seconds4) 2 seconds5) 0.075 seconds6) 0.0375 seconds3. What are features of the TCP/IP Transport layer? (Choose two.) (3,5)1) path determination2) handles representation, encoding and dialog control3) uses TCP and UDP protocols4) packet switching5) reliability, flow control and error correction4. Which of the following is the Layer 4 PDU? (4)1) bit2) frame3) packet4) Segment5. What is important to remember about the data link layer of the OSI model whenconsidering Peer to Peer communication? (Choose three.) (3,4,5)1) It links data to the transport layer.2) It encapsulates frames into packets.3) It provides a service to the network layer.4) It encapsulates the network layer information into a frame.5) Its header contains a physical address which is required to complete the datalink functions.6) It encodes the data link frame into a pattern of 1s and 0s (bits) for transmissionon the medium.6. Which statement describes a star topology? (2)1) Each host in the network is connected to a backbone cable that is terminated atboth ends.2) Each host is connected to a hub or switch, either of which acts as a central pointfor all network connections.3) Each host is directly connected to two other hosts to form a long chain of hosts.4) Each host has a connection to all other hosts in the network.7. Which statements describe the logical token-passing topology? (Choose two.)(2)1) Network usage is on a first come, first serve basis.2) Computers are allowed to transmit data only when they possess a token.3) Data from a host is received by all other hosts. Electronic tokens are passedsequentially to each other.4) Token passing networks have problems with high collision rates.8. Which technologies are considered to be LAN technologies? (Choose two.) (2,5)1) DSL2) Token Ring3) Frame Relay4) ISDN5) Ethernet9.Refer to the exhibit. Host A wants to send a message to host B. Place the following stepsin the correct order so that the message can be sent. (4)A - add network layer addressesB - transmit bitsC - create application dataD - add data link layer addresses1) B, A, D, C2) D, A, C, B3) A, D, A, B4) C, A, D, B5) C, D, A, B6) C, B, A, D10.After an uns u ccessful ping to the local router, the technician decides to investigate therouter. The technician observes that the lights and fan on the router are not operational.In which layer of the OSI model is the problem most likely occurring? (4)1) transport2) network3) data link4) physical11. Refer t o the exhibit. What is the order of the TCP/IP Protocol Data Units as datais moved as indicated through the OSI model? (3)1) data, segments, frames, packets, bits2) data, packets, segments, frames, bits3) data, segments, packets, frames, bits4) data, packets, frames, segments, bits第三章1. Which combinations of charges will be repelled by electric force? (Choose two.)(4,6)1) neutral and neutral2) neutral and positive3) neutral and negative4) positive and positive5) positive and negative6) negative and negative2. Which of the following are considered the best media for use in data networkcommunications? (Choose three.) (2,3,6)1) glass2) fibers3) copper4) gold5) plastic6) silicon7) Silver3. Which of the following wireless standards increased transmission capabilitiesto 11 Mbps? (2)1) 802.11a2) 802.11b3) 802.11c4) 802.11d4. What is attenuation? (3)1) opposition to the flow of current2) measurement of electrical signals relative to time3) degradation of a signal as it travels along the medium4) amount or volume of traffic that is flowing on the medium5. Which cable specifications are indicated by 10BASE-T? (3)1) 10 Mbps transmission speed, baseband signal, 500 meter cable length, coaxialcable2) 10 Mbps transmission speed, broadband signal, 100 meter cable length, coaxialcable3) 10 Mbps transmission speed, baseband signal, 100 meter cable length,twisted-pair cable4) 10 Gbps transmission speed, broadband signal, 500 meter cable length,twisted-pair cable6. For which Ethernet installations would fiber optic rather than Cat5 UTP be abetter media choice? (Choose two.) (2,4)1) a 3 meter connection between two 10BASE-T hubs2) an environment with many potential sources of EMI and RFI3) a peer to peer connection between two NICs with RJ45 connectors4) an installation between two buildings that are located 500 meters apart5) a single building installation where installation costs are the major concern7. Refer to the exhibit. Which type of UTP cable should be used to connect Host Ato Switch1? (4)1) rollover2) console3) crossover4) straight-through8. Refer to the exhibit. Which type of Category 5 cable is used to make an Ethernetconnection between Host A and Host B? (3)1) coax cable2) rollover cable3) crossover cable4) straight-through cable第四章1. During cable testing, which of the following are used to calculate theinformation carrying capacity of a data cable? (Choose two.) (2,5)1) bit speed2) attenuation3) wire map4) saturation limit5) analog bandwidth2. What type of wiring problem is depicted in this sample of a cable tester? (3)1) a fault2) a short3) an open4) a split a good map3. In a new network installation, the network administrator has decided to use amedium that is not affected by electrical noise. Which cable type will best meet this standard? (5)1) coaxial2) screened twisted pair3) shielded twisted pair4) unshielded twisted pair5) fiber optic4. How does network cable length affect attenuation? (3)1) Category 5 cable that is run in metal conduit has the highest attenuation in theshortest distance.2) Shorter cable lengths have greater signal attenuation.3) Longer cable lengths have greater signal attenuation.4) The length of the cable has no effect on signal attenuation.第五章1. The highest capacity Ethernet technologies should be implemented in whichareas of a network? (Choose three.) (3,4,5)1) between workstation and backbone switch2) between individual workstations3) between backbone switches4) between enterprise server and switch5) on aggregate access links2. What device must be used between an AUI port of a networking device and themedia to which it is being connected? (3)1) a transducer2) a transmitter3) a transceiver4) a transponder5) a port replicator3. An ISDN Basic Rate Interface (BRI) is composed of how many signalingchannels? (1)1) 12) 23) 34) 44. Which layer of the OSI model covers physical media? (1)1) Layer 12) Layer 23) Layer 34) Layer 45) Layer 56) Layer 65. What type of network cable is used between a terminal and a console port? (3)1) cross-over2) straight-through3) rollover4) patch cable6. What is the recommended maximum number of workstations configured on apeer-to-peer network? (3)1) 252) 153) 104) 55) 27. Which of the following increases the potential for a collision to occur? (4)1) the use of an active hub instead of an intelligent hub2) the use of an intelligent hub instead of an active hub3) a reduction in the number of devices attached to the hub4) an increase in the number of devices attached to the hub8. What is the maximum length of a media segment used for 100BASE-TX? (1)1) 100 meters2) 185 meters3) 400 meters4) 500 meters9. Which cable diagram displays the end to end pinout for a crossover cable usedwith Cisco devices? (3)1) Cable A2) Cable B3) Cable C4) Cable D第六章1. What does the "10" in 10Base2 indicate about this version of Ethernet? (2)1) The version uses Base10 numbering within the frames.2) The version operates at a transmission rate of 10 Mbps.3) Frames can travel 10 meters unrepeated.4) The maximum frame length is 10 octets.2. How is a MAC address represented? (4)1) four groups of eight binary digits separated by a decimal point2) four Base10 digits separated by a decimal point3) six hexadecimal digits4) twelve hexadecimal digits5) twenty-four Base10 digits3. Which of the following statements are correct about CSMA/CD? (Choose three.)(1,3,6)1) It is a media access method used in LANs.2) It is a media access method used in FDDI WANs.3) When a device needs to transmit, it checks to see if the media is available.4) A device sends data without checking media availability because all deviceshave equal access.5) Multiple devices can successfully transmit simultaneously.6) Only one device can successfully transmit at a time.4. Which devices shown in the graphic must have a MAC address? (5)1) only PC2) only router3) PC and router4) PC, hub, and router5) PC, printer, and router第七章1. Which of the following items are common to all 100BASE technologies?(Choose three.) (1,4,5)1) frame format2) media3) connectors4) timing5) multi-part encoding2. Which of the following does 1000BASE-T use to accomplish gigabit speeds onCat 5e cable? (4)1) the use of four conductors in full-duplex mode2) the use of two multiplexed pairs of wires, simultaneously3) the use of three pairs of wires for data and the fourth for stabilization andforward error correction4) the use of all four pairs of wires in full-duplex mode, simultaneously3. For which of the following is Ethernet considered the standard? (Choose three.)(1,4,5)1) inter-building connection2) mid-length voice3) video conferencing4) vertical wiring5) horizontal wiring6) diagonal wiring4. To make sure timing limitations are not violated when implementing a 10 MbpsEthernet network involving hubs or repeaters, a technician should adhere to which rule? (4)1) the 4-5-3 rule2) the 6-4-2 rule3) the 3-4-5 rule4) the 5-4-3 rule5. What is the maximum distance that 10BASE-T will transmit data before signalattenuation affects the data delivery? (1)1) 100 meters2) 185 meters3) 300 meters4) 500 meters6. When using Category 5 UTP cable, which RJ-45 pin pairs are used to exchangedata between hosts on an Ethernet network? (2)1) 1 and 2; 4 and 52) 1 and 2; 3 and 63) 3 and 6; 7 and 84) 4 and 5; 7 and 8第八章1. John has been hired as the network administrator of a local company and hasdecided to add more hubs to the company's existing network. Which of the following has been caused by John's inexperience? (1)1) collision domain extended2) an increased number of collision domains3) increased network performance4) increased bandwidth5) extended bandwidth2. "CompA" is trying to locate a new computer named "CompB" on the network.Which of the following does "CompA" broadcast to find the MAC address of "CompB"? (2)1) MAC request2) ARP request3) ping4) Telnet5) proxy ARP3. Which of the following is a term associated with replacing hubs with switchesto increase the number of collision domains? (3)1) encapsulation2) latency3) segmentation4) layered model5) broadcast domain6) Extended4. The accumulation of traffic from which of the following can cause a networkcondition called broadcast radiation? (Choose three.) (3,5,6)1) anonymous FTP servers2) telnet sessions3) video over IP applications4) NAS services5) ARP requests6) RIP updates5. Which of the following describes the use of Spanning Tree Protocol (STP)? (4)1) resolve routing loops2) eliminate Split Horizon errors3) limit collisions4) resolve switching loops6. Which term describes the delay in time that occurs when a frame leaves itssource device and reaches its destination? (4)1) collision2) backoff3) attenuation4) latency5) broadcast7. Based on the graphic above, which of the following occurs as each host systemcomes on line in the topology? (2)1) The switch sends its MAC address to each host.2) The switch adds MAC address to the bridge table as each host sends a frame.3) Each host exchanges MAC addresses with each other.4) The switch listens for data traffic to block since the switch lacks an IP address. 8. Which devices segment collision domains? (Choose two.) (2,3)1) transceiver2) router3) switch4) hub5) media9. Which protocol is used to eliminate switching loops? (3)1) Transmission Control Protocol2) Routing Information Protocol3) Spanning Tree Protocol4) Interior Gateway Routing Protocol5) Internetworking Protocol10. Refer to the exhibit. A network associate needs to establish an Ethernetconnection between Host A and Host B. However, the distance between the two hosts is further than the cabling standards allow. Which two devices that operate at the physical layer of the OSI can be used to allow Host A and Host B to communicate? (2,5)1) switch2) hub3) bridge4) router5) repeater第九章1. Which term describes an ARP response by a router on behalf of a requestinghost? (3)1) ARP2) RARP3) Proxy ARP4) Proxy RARP2. Which protocol functions at the internet layer of the TCP/IP protocol suite? (4)1) File Transfer Protocol (FTP)2) Trivial File Transfer Protocol (TFTP)3) Transmission Control Protocol (TCP)4) Internet Protocol (IP)5) User Datagram Protocol (UDP)6) Simple Mail Transport Protocol (SMTP)3. Which of these workstation installation and setup tasks are concerned withnetwork access layer functions? (Choose two.) (2,4)1) configuring the e-mail client2) installing NIC drivers3) configuring IP network settings4) connecting the network cable5) using FTP to download application software updates4. Which part of an IP address identifies a specific device on a network? (4)1) first two octets2) third and fourth octets3) network portion4) host portion5) only the fourth octet5. Which of the following are features of the Internet Protocol (IP)? (Choose two.)(1,3)1) It is the most widely implemented global addressing scheme.2) It allows two hosts to share a single address on a local area network.3) It is a hierarchical addressing scheme allowing addresses to be grouped.4) It is only locally significant, used primarily on local area networks.6. Which of the following are useable Class A IP addresses with a default subnetmask? (Choose three.) (2,3,5)1) 127.0.39.12) 111.9.28.303) 123.1.2.1324) 128.50.38.25) 105.1.34.16) 0.23.92.37. Which application layer protocols use UDP at the transport layer? (Choose two.)(2,4)1) FTP2) SNMP3) Telnet4) DHCP5) SMTP第十章1. Which OSI layer encapsulates data into packets? (3)1) session2) transport3) network4) data link2. Which OSI layer defines the functions of a router? (3)1) physical2) data link3) network4) transport5) session3. Which of the following are Cisco proprietary routing protocols? (Choose two.)(2,6)1) RIPv22) IGRP3) OSPF4) BGP5) RIPv16) EIGRP4. A company with a Class B license needs to have a minimum of 1,000 subnetswith each subnet capable of accommodating 50 hosts. Which mask below is the appropriate one? (4)1) 255.255.0.02) 255.255.240.03) 255.255.255.04) 255.255.255.1925) 255.255.255.2245. A small company has a class C network license and needs to create five usablesubnets, each subnet capable of accommodating at least 20 hosts. Which of the following is the appropriate subnet mask? (3)1) 255.255.255.02) 255.255.255.1923) 255.255.255.2244) 255.255.255.2406. When a network administrator applies the subnet mask 255.255.255.248 to aClass A address, for any given subnet, how many IP addresses are available to be assigned to devices? (6)1) 10222) 5103) 2544) 1265) 306) 67. Host A is assigned the IP address 10.18.97.55 /21. How many more networkdevices can be assigned to this subnetwork if Host A is the only one that has an IP address assigned so far? (4)1) 2542) 5093) 10214) 20455) 40946) 81908.Refe r to the exhibit. The network administrator wants to create a subnet for thepoint-to-point connection between the two routers. Which subnetwork mask would provide enough addresses for the point-to-point link with the least number of wasted addresses?1) 255.255.255.1922) 255.255.255.2243) 255.255.255.2404) 255.255.255.2485) 255.255.255.2529. What is the correct number of usable subnetworks and hosts for the IP networkaddress 192.168.35.0 subnetted with a /28 mask?1) 6 networks / 64 hosts2) 14 networks / 32 hosts3) 14 networks / 14 hosts4) 30 networks / 64 hosts10. Which subnet masks would be valid for a subnetted Class B address? (Choosetwo.) (5,6)1) 255.0.0.02) 255.254.0.03) 255.224.0.04) 255.255.0.05) 255.255.252.06) 255.255.255.19211. Refer to the exhibit. How will the Fohi router dynamically learn routes to the192.168.16.16/28, 192.168.16.32/28, and 192.168.16.48/28 subnetworks? (3)1) with a static route2) with a routed protocol3) with a routing protocol4) with a directly connected route12. How many broadcast domains are shown in the diagram? (1)1) three2) four3) five4) six5) seven6) eight13. How many collision domains are shown in the diagram? (5)1) three2) four3) five4) six5) seven6) eight14. A router interface has been assigned an IP address of 172.16.192.166 with amask of 255.255.255.248. To which subnet does the IP address belong?1) 172.16.0.02) 172.16.192.03) 172.16.192.1284) 172.16.192.1605) 172.16.192.1686) 172.16.192.17615. Refer to the exhibit. Host A is sending data to Host B. Once R2 determines thatdata from Host A must be forwarded to R1 to reach Host B, which layer of the OSI model will R2 use to address and build the frames destined for R1?1) physical2) data link3) network4) transport5) session6) presentation16. Which type of address is 192.168.170.112/28?1) host address2) subnetwork address3) broadcast address4) multicast address17. Which type of address is 223.168.17.167/29?1) host address2) multicast address3) broadcast address4) subnetwork address18. Which combination of network id and subnet mask correctly identifies all IPaddresses from 172.16.128.0 through 172.16.159.255?1) 172.16.128.0 255.255.255.2242) 172.16.128.0 255.255.0.03) 172.16.128.0 255.255.192.04) 172.16.128.0 255.255.224.05) 172.16.128.0 255.255.255.19219. Refer to the exhibit. The internetwork in the exhibit has been assigned the IPaddress 172.20.0.0. What would be the appropriate subnet mask to maximize the number of networks available for future growth?1) 255.255.224.02) 255.255.240.03) 255.255.248.04) 255.255.252.05) 255.255.254.06) 255.255.255.0第十一章1. If a network administrator needed to download files from a remote server, whichprotocols could the administrator use to remotely access those files? (Choose two.) (3,5)1) NFS2) ASCII3) TFTP4) IMAP5) FTP6) UDP2. What is established during a connection-oriented file transfer betweencomputers? (Choose two.) (2,5)1) a temporary connection to establish authentication of hosts2) a connection used for ASCII or binary mode data transfer3) a connection used to provide the tunnel through which file headers aretransported4) a command connection which allows the transfer of multiple commands directlyto the remote server system5) a control connection between the client and server3. Which of the following protocols are used for e-mail transfer between clientsand servers? (Choose three.) (3,4,5)1) TFTP2) SNMP3) POP34) SMTP5) IMAP46) postoffice4. Which type of institution does the domain suffix .org represent? (4)1) government2) education3) network4) non-profit5. Which of the following services is used to translate a web address into an IPaddress? (1)1) DNS2) WINS3) DHCP4) Telnet6. Which part of the URL http://www.awsb.ca/teacher gives the name of thedomain? (4)1) www2) http://3) /teacher4) awsb.ca7. Which protocols are TCP/IP application layer protocols? (Choose two.) (2,4)1) UDP2) FTP3) IP4) SMTP5) TCP8. What are three characteristics of the TCP protocol? (Choose three.) (3,4,6)1) has less overhead than UDP2) is used for IP error messages3) forces the retransmission undelivered packets4) creates a virtual session between end-user applications5) carries the IP address of destination host in the TCP header6) is responsible for breaking messages into segments and reassembling9. Two peer hosts are exchanging data using TFTP. During the current session, adatagram fails to arrive at the destination. Which statement is true regarding the retransmission of the datagram? (2)1) Datagram retransmission requires user authentication.2) Datagram retransmission is controlled by the application.3) Datagram retransmission relies on the acknowledgements at transport layer.4) Datagram retransmission occurs when the retransmission timer expires in thesource host.案例学习1. 子网计算练习:Answer2. 子网号及广播地址计算练习Answer3. 子网规划练习:已知:给定一个C类地址201.16.5.0/24。
思科CCNA学习试题答案!!!
思科CCNA学习试题答案CCNA课程测试一、单项选择题:1、介质100BaseT的最大传输距离是:( )A: 10m B:100m C:1000m D:500m2、路由器下,由一般用户模式进入特权用户模式的命令是:()A:enable B:config C: interface D:router3、哪个命令可以成功测试网络:( )A: Router> ping 192.5.5.0B: Router# ping 192.5.5.30C: Router> ping 192.5.5.256D: Router# ping 192.5.5.2554、介质工作在OSI的哪一层()A:物理层 B:数据链路层 C:网络层 D:传输层5、100baseT的速率是( )Mbit/sA: 1 B:10 C:100 D:10006、在启用IGRP协议时,所需要的参数是:( )A:网络掩码 B:子网号C:自治系统号 D:跳数7、基本IP访问权限表的表号范围是:( )A: 1—100 B:1-99 C:100-199 D:800-8998、查看路由表的命令是:( )A:show interface B:show run C:show ip route D:show table9、工作在OSI第三层的设备是:( )A:网卡B:路由器 C: 交换机 D:集线器10、OSI第二层数据封装完成后的名称是:( )A:比特 B: 包C:帧 D:段11、为了禁止网络210.93.105.0 ftp到网络223.8.151.0,允许其他信息传输,则能实现该功能的选项是:( )A:access-list 1 deny 210.93.105.0.0.0.0.0.0B:access-list 100 deny tcp 210.93.105.0 0.0.0.255 223.8.151.00.0.0.255 eq ftpC:access-list 100 permit ip any anyD:access-list 100 deny tcp 210.93.105.0 0.0.0.255 223.8.151.0 0.0.0.255 eq ftpaccess-list 100 permit ip any any12、路由器下“特权用户模式”的标识符是:( )A: > B:! C:# D: (config-if)#13、把指定端口添加到VLAN的命令是:( )A: vlan B: vlan-membership C: vtp D:switchport14、交换机工作在OSI七层模型的哪一层( )A:物理层B:数据链路层C:网络层 D:传输层15、在OSI七层模型中,介质工作在哪一层( )A:传输层 B:会话层C:物理层 D:应用层16、交换机转发数据到目的地依靠( )A:路由表B:MAC地址表 C:访问权限表 D:静态列表17、为了使配置私有IP的设备能够访问互联网,应采用的技术是( )?A:NAT B:VLAN C:ACCESS-LIST D:DDR18、VLAN主干协议VTP的默认工作模式是( )A:服务器模式B:客户端模式C:透明模式D:以上三者都不是19、路由器的配置文件startup-config存放在( )里A:RAM B:ROM C:FLASH D:NVRAM20、配置路由器特权用户“加密密码”的命令是:( )A:password B:enable password C:enable secretD:passwd21、某网络中,拟设计10子网,每个子网中放有14台设备,用IP 地址段为199.41.10.X ,请问符合此种规划的子网掩码是( ) A: 255.255.255.0 B:255.255.240.0C: 255.255.255.240 D:255.248.0.022、在路由表中到达同一网络的路由有:静态路由、RIP路由、IGRP 路由,OSPF路由,则路由器会选用哪条路由传输数据:( ) A:静态路由 B: RIP路由 C:IGRP路由 D:OSPF路由23、扩展IP访问权限表的表号范围是:( )A: 1—100 B:1-99 C:100-199 D:800-89924、把访问权限表应用到路由器端口的命令是:( )A: permit access-list 101 out B: ip access-group 101 out C: apply access-list 101 out D: access-class 101 out 25、混合型协议既具有“距离矢量路由协议”的特性,又具有“链路状态路由协议”的特性,下列协议中属于混合型协议的是:( ) A: RIP B: OSPF C:EIGRP D: IGRP26、在路由器上,命令show access-list的功能是():A:显示访问控制列表内容 B:显示路由表内容C:显示端口配置信息 D:显示活动配置文件27、RIP路由协议认为“网络不可到达”的跳数是:( )A: 8 B:16 C:24 D:10028、查看E0端口配置信息的命令是:( )A:show access-list B:show ip routeC:show version D:show interface e029、配置路由器时,封装PPP协议的命令是:( )A:encap ppp B:ppp C: group ppp D: int ppp30、路由器上“水平分割”的功能是:( )A:分离端口B:阻止路由环路C:简化配置D:方便故障处理31、OSI七层模型中,“包”是哪一层数据封装的名称()A:物理层 B:数据链路层C:网络层 D:传输层32、OSI七层模型中,“段”是哪一层数据封装的名称()A:物理层 B:数据链路层 C:网络层 D:传输层33、备份路由器IOS的命令是:( )A: copy flash tftpB: copy running-config tftpC: copy IOS tftpD: copy startup-config tftp34、PPP工作在OSI的哪一层()A:物理层B:数据链路层 C:网络层 D:传输层35、FTP工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层36、TELNET工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层37、SMTP工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层38、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的子网号为()A:192.168.50.32 B:192.168.80.64C:192.168.50.96 D:192.168.50.7139、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的广播地址为()A:192.168.50.32 B:192.168.80.64C:192.168.50.96 D:192.168.50.7140、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的子网有效IP为()A:192.168.50.33---192.168.50.39B:192.168.50.41---192.168.50.50C:192.168.50.65---192.168.50.70D:192.168.50.66---192.168.50.7541、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP和掩码结合,共划分了多少个子网(不包括全0子网和全1子网)()A: 8 B:30 C:6 D:1442、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP和掩码结合划分子网时,每个子网的容量为()A:8 B:4 C:12 D:643、网络172.12.0.0需要划分子网,要求每个子网中有效IP数为458个,为了保证子网数最大,则掩码应为()A:255.255.255.0 B:255.255.254.0 C:255.255.0.0D:255.255.248.044、哪一个命令可以设置路由器特权用户的“明文密码”()A:enable password B:password C:enable secretD: secret45、RIP协议的管理距离是()A:100 B:110 C:120 D:15046、下列路由协议中,属于链路状态路由协议的是()A:RIP B:EIGRP C:IGRP D:OSPF47、默认情况下,RIP定期发送路由更新的时间是()A:15S B:30S C:60S D:90S48、如果网络中的路由器都是cisco路由器,则优先选择哪一个路由协议()A:RIP B:EIGRP C:IGRP D:OSPF49、下列对RIP的配置中,合法的命令是()A: router rip 100network 10.12.0.0B: router rip 100network 10.0.0.0C: router ripnetwork 10.12.0.0D: router rip 100network 10.0.0.050、为了查看路由器的E0端口上,是否挂接了访问权限表,应该使用的命令是()A:show access-list B:show interface e0C: show ip interface e0 D:show e051、关于帧中继的说法,正确的是()A:速率最大为1Mbit/s B: 不提供差错校验功能C:可以偷占带宽 D:数据传输质量高于DDN52、关于PPP和HDLC的说法中,错误的是()A:PPP是通用协议,HDLC是CISCO私有协议B:PPP有验证功能,HDLC无验证功能C:PPP效率低,HDLC效率高D:在配置ISDN时,广域网协议不能封装成PPP,但可以封装成HDLC 53、对交换机的描述,正确的是()A:单广播域,单冲突域的设备B:单广播域,多冲突域的设备C:多广播域,单冲突域的设备D:多广播域,多冲突域的设备54、对路由器的描述,正确的是()A:单广播域,单冲突域的设备B:单广播域,多冲突域的设备C:多广播域,单冲突域的设备D:多广播域,多冲突域的设备55、交换机上VLAN的功能描述中,正确的是()A:可以减少广播域的个数B:可以减少广播对网络性能的影响C: 可以减少冲突域的个数D: 可以减小冲突域的容量56、两个VLAN之间要想通信,应该使用的设备是()A:集线器 B:二层交换机C:路由器 D:PC机57、要把交换机的配置文件保存到tftp服务器,应使用的命令为()A:copy ios tftp B:copy running-config tftpC: copy flash tftp D:copy config tftp58、命令“ping 127.0.0.1”的功能是()A:测试网卡是否正常 B:测试网关是否正常C:测试TCP/IP协议是否正常 D:测试介质是否正常59、路由器上的命令“show version”的功能是()A:显示版本信息 B:显示端口配置信息 C:显示路由表D:显示路由协议信息60、路由器上激活端口的命令是()A:shutdown B:no shutdown C: up D:no up61、某台PC,能ping通路由器,但不能telnet到路由器,可能的原因是(D )A:PC的IP地址设置错误 B:路由器端口IP设置错误C:路由器端口处于关闭状态D:telnet密码未设置62、OSI七层模型中,网络层的数据封装名称为()A:比特 B:帧C:包 D:段63、OSI七层模型中,物理层的数据封装名称为()A:比特 B:帧 C:包 D:段64、OSI七层模型中,数据链路层的数据封装名称为()A:比特B:帧 C:包 D:段65、OSI七层模型中,传输层的数据封装名称为()A:比特 B:帧 C:包D:段66、帧中继环境下,为了区分虚电路,应该使用的地址是()A:IP地址 B:MAC地址 C:DLCI D:IPX地址67、路由器“路由模式”的提示符号是()A: # B: (config)# C:(config-if)# D:(config-router)# 68、EIGRP 的管理距离()A:90 B:100 C:110 D:12069、RIP协议负载均衡的路径数量为()A:无限制B:最多4条C:最多5条D:最多6条70、下面有关交换机的描述中,正确的是()A:所有交换机都支持VLAN功能B:交换机端口数量最多为48口C:交换机独占带宽D:交换机端口的最大速率为100Mbit/s71、为了阻止交换机环路,交换机上所采用的技术为()A:水平分割B:生成树协议C:触发更新D:地址学习72、帧中继环境中,CIR的含义是()A:提高线路速率B:保证线路速率C:降低线路速率D:配置线路速率73、路由器上端口fa0/0,其最大传输速率是()Mbit/sA:128 B: 10 C:100 D: 100074、帧中继环境中,在物理端口上,建立子接口的命令是()A:create B:interface C:encapsulation D:ip address 75、路由器上,命令“show int s0”的显示结果为:Serial0 is up , line protocol is down出现该结果的可能原因是()A:端口处于关闭状态 B:物理端口被烧毁C:两端设备协议不一致 D:路由表中无路由76、如果把路由器的某个端口的IP配置为:192.168.10.64,掩码配置为:255.255.255.248,则该端口()A:能和其他设备正常通信B:会变成“administratively down”状态C:端口被烧毁D:出现错误提示,配置命令执行失败77、网关的功能()A:过滤数据包B:不同网段通信 C:校验数据帧D:把数据封装成“段”78、能够分配给设备的IP,应该是()A:网络有效IP B:网络号 C:网络广播地址 D:任意IP 79、路由器“全局模式”的提示符为()A: > B: # C: (config)# D: (config-router)#80、路由器当前的模式为“端口模式”,要退回到“特权模式”,应该使用的快捷键为()A:ctrl+b B: ctrl+z C:ctrl+c D:ctrl+p81、下列命令中,无法正确执行的是()A:Router(config)#show runB: Router#ping 127.0.0.1C: Router(config)#hostname ciscoD: Router#reload82、路由器上,设置端口速率的命令是()A:clock rate B:bandwidth C:set D:encap83、路由器上,清空路由表的命令是()A:clear ip B:delete ip route C:delete routeD: clear ip route *84、路由表中,某条路由的“路由代码为D”,则表明该路由为()A:直连路由 B:静态路由 C:IGRP路由 D:EIGRP路由85、两台路由器直连到一起,应该使用的线缆为()A:交叉线缆B:直通线缆C:反转线缆D:任意线缆86、通过路由器的“配置端口console”对路由器进行配置,应该使用的线缆为()A:交叉线缆B:直通线缆C:反转线缆D:任意线缆87、下面对Cisco2621路由器和Cisco2501路由器描述中,错误的是()A:Cisco2621路由器的可扩展性优于Cisco2501路由器B:Cisco2621是模块化路由器C:Cisco2501上提供一个100Mbit/s的快速以太网端口D:Cisco2501是固定端口的路由器88、为了连接“帧中继”线路,网络中的路由器需要提供的端口类型为()A:FastEthernet B:Serial C:BRI D:Ethernet89、路由器“特权模式”的提示符是:()A:> B:# C:(config)# D: (config-if)#90、下列关于路由器和交换机的描述中,错误的是()A:路由器可以用来连接internetB:二层交换机可以用来实现“异地网络”互连C:路由器可以用来做路径选择D:交换机可以转发广播二、多项选择题:正确答案的个数在每题的题后括号中有说明91、在路由器上,可以使用的命令有:( ) [选3个]A:ping B:show interfaces C:show ip route D:ipconfig E:wincfg92、在配置帧中继子接口时,在物理接口上应该配置的内容是:( )[选3个]A:配置IP地址B:封装帧中继协议C:指定子接口类型D:设定子接口 E:配置密码93、请选出交换机处理帧的三种模式:( )[选3个]A:直通模式 B:存储转发模式 C:侦测模式 D:分段模式E:阻塞模式94、对于IP为199.41.27.0,子网掩码为255.255.255.240,则该IP地址和子网掩码相作用会得到一系列IP,从下列选项中选出属于“有效IP”的选项:( ) [选3个]A:199.141.27.33 B:199.141.27.112 C:199.141.27.119D:199.141.27.126 E:199.141.27.175 F:199.141.27.208 95、属于私有IP段的是( )[选3个]A:10.0.0.0-10.255.255.255B:172.16.0.0-172.31.255.255 C:202.110.100.0-202.110.100.255D:192.168.0.0-192.168.255.255E:126.0.0.0-126.255.255.25596、下列哪一设备工作时,要用到OSI的七个层(一层到七层)()[选3个]A:PC B:网管机 C:WEB服务器 D:交换机 E:路由器97、网络中经常使用DDN服务,请选出DDN的优点()[选3个] A:传输质量高 B:接入方式灵活 C:偷占带宽D:使用虚电路E:专用线路98、网络中经常使用“帧中继”服务,请选出帧中继的优点()[选3个]A:偷占带宽B:提供拥塞管理机制C:可以使用任意广域网协议D:灵活的接入方式99、默认情况下,IGRP衡量路径好坏时,考虑的因素为()[选2个]A:带宽 B:可靠性 C:最大传输单元D:延时100、交换机的三大功能为()[选3个]A:地址学习 B:转发过滤 C:消除回路 D:发送数据包。
CCNA第二学期答案

.请参见图示。
对于发往的数据包,R2 会采取什么操作?它会丢弃数据包。
2.请参见图示。
R1 会使用哪一总结地址来向R2 通告其网络?3.请参见图示。
尽管R2 已配置正确,但主机A 还是无法访问Internet。
可以在R1 上配置哪两条可让主机 A 访问Internet 的静态路由?(选择两项。
ip route Fa0/1ip route4.请参见图示。
网络管理员已按图示配置了R1,并且所有接口都运作正常。
但从R1 ping 时失败。
造成此问题的原因可能是什么?默认路由配置有误。
5.请参见图示。
所有接口都已编址,并且运行正常。
网络管理员在主机A 上运行了tracert 命令。
得到这种输出的原因可能是什么?(选择两项。
)R2 的路由表中缺少的条目。
R1 的路由表中缺少的条目。
6.请参见图示。
从主机A 到主机B 的ping 成功,但从主机A ping 在Internet 上正常运行的主机却失败了。
此问题的原因是什么?未在这两台路由器上配置路由协议。
7.网络管理员使用RIP 路由协议在一个自治系统内实施路由。
下列哪两项是该协议的特征?(选择两项。
使用贝尔曼-福特算法确定最佳路径。
定期将完整的路由表发送给所有连接的设备。
8.请参见图示。
两台路由器无法建立相邻关系。
此问题的原因可能是什么?这两台路由器上的hello 间隔和dead 间隔不同9.在两台路由器能够使用OSPF 形成邻居邻接关系之前必须完成哪两项任务?(选择两项。
)路由器必须在网络类型方面达成一致。
路由器必须使用相同的dead 时间间隔。
10.下列关于链路状态路由协议的陈述,哪两项是正确的?(选择两项。
)运行链路状态协议的路由器可以建立完整的网络拓扑使用最短路径优先算法。
11.请参见图示。
下列关于Router1 路由表的陈述,哪三项是正确的?(选择三项。
)EIGRP 路由的AD 已经手动更改为默认值以外的其它值。
Router1 正同时运行着EIGRP 和OSPF 路由过程尚未配置任何默认路由。
ccna章节与期末答案
第一章:正确答案:2.4.5解析:由于不需要使用网络设备和专用服务器,对等网络易于创建,复杂性更低,且成本更少。
而且对等网络也没有集中管理。
这种网络安全性更低,不可扩展,而且那些同时充当客户端和服务器的设备可能性能更差正确答案:1解析:正确答案: 3.5解析:选择网络介质的条件包括:所选介质可以成功传送信号的距离、要安装所选介质的环境、必须传输的数据量和速度以及介质和安装的成本。
正确答案:3和4解析:终端设备上的应用程序可以生成数据,更改数据内容并且负责启动封装过程。
正确答案:1和4解析:终端设备会发出通过网络传输的数据。
中间设备会在链路发生故障时通过备用路径传输数据,并且会过滤数据传输以增强安全性。
网络介质提供网络消息的传输通道。
正确答案:4解析:外联网是公司外部的人或企业合作伙伴访问数据的网络区域。
内部网只描述通常仅供内部人员访问的网络区域。
当设备连接到有线网络时,有线 LAN 会受 BYOD(自带设备)影响。
使用大学无线 LAN 的设备多为平板电脑和智能手机。
大学生主要使用无线 WAN 来访问他们的手机运营商网络。
.正确答案:2解析:由于通过 Internet 可以联系在线供应商,所以家庭用户通过 Internet 进行网上购物。
内联网基本上是仅供内部使用的局域网。
外联网是外部合作伙伴访问组织内部特定资源的网络。
家庭用户并不一定使用 LAN 来访问 Internet。
例如,PC 可以通过调制解调器直接连接到 ISP。
正确答案:1解析:内部网这个术语用于表示一个组织的私有局域网和广域网连接。
内部网的设计旨在仅允许该组织的成员、员工或其他获得授权的人员进行访问。
正确答案:2和4解析:电缆和 DSL 均能实现高带宽、始终联网,并提供到主机计算机或 LAN 的以太网连接。
10正确答案:2和3解析:移动电话连接需要使用移动电话网络。
卫星连接通常用于家庭或企业外部不便使用物理布线的位置。
11正确答案:2解析:当对网络资源的请求超出了可用容量时,网络就会变得拥堵。
最新CCNA题库 V102上卷(含答案无水印)

学网络技术去鸿鹄网网络技术从零开始梦想之路鸿鹄开启鸿鹄论坛:鸿鹄团队致力于为每一位网络技术爱好者提供帮助有事您发帖,斑竹为您跑腿,给您答疑。
CCNA CCNP最新题库/最新战报发布区:/thread.php?fid-166.html 鸿鹄客服QQ:712023090请加QQ群:96564501103107466鸿鹄题库新纪元CCNA V102上卷(共上下两卷,加lab集)1What can a network administrator utilize by using PPP Layer2encapsulation?(Choose three.)A.VLAN supportpressionC.AuthenticationD.Sliding windowsE.Multilink supportF.Quality of serviceAnswer:B,C,E2Which two statements best describe the wireless security standard that is defined by WPA? (Choose two.)A.It specifies use of a static encryption key that must be changed frequently to enhance security.B.It requires use of an open authentication method.C.It specifies the use of dynamic encryption keys that change each time a client establishes a connection.D.It requires that all access points and wireless devices use the same encryption key.E.It includes authentication by PSK.Answer:C,E3While troubleshooting a connectivity problem,a network administrator notices that a port status LED on a Cisco Catalyst series switch is alternating green and amber.Which condition could this indicate?A.The port is experiencing errors.B.The port is administratively disabled.C.The port is blocked by spanning tree.D.The port has an active link with normal traffic activity.Answer:A4Refer to the exhibit.The network shown in the exhibit is running the RIPv2routing protocol.The network has converged, and the routers in this network are functioning properly.The FastEthernet0/0interface on R1goes down.In which two ways will the routers in this networkrespond to this change?(Choose two.)A.All routers will reference their topology database to determine if any backup routes to the192.168.1.0network are known.B.Routers R2and R3mark the route as inaccessible and will not accept any further routing updates from R1until their hold-down timers expire.C.Because of the split-horizon rule,router R2will be prevented from sending erroneous information to R1about connectivity to the192.168.1.0network.D.When router R2learns from R1that the link to the192.168.1.0network has been lost,R2will respond by sending a route back to R1with an infinite metric to the192.168.1.0network.E.R1will send LSAs to R2and R3informing them of this change,and then all routers will send periodic updates at an increased rate until the network again converges.Answer:C,D5Which three statements are correct about RIP version2?(Choose three.)A.It has the same maximum hop count as version1.B.It uses broadcasts for its routing updates.C.It is a classless routing protocol.D.It has a lower default administrative distance than RIP version1.E.It supports authentication.F.It does not send the subnet mask in updates.Answer:A,C,E6What should be part of a comprehensive network security plan?A.Allow users to develop their own approach to network security.B.Physically secure network equipment from potential access by unauthorized individuals.C.Encourage users to use personal information in their passwords to minimize the likelihood of passwords being forgotten.D.Delay deployment of software patches and updates until their effect on end-user equipment is well known and widely reported.E.Minimize network overhead by deactivating automatic antivirus client updates.Answer:B7How should a router that is being used in a Frame Relay network be configured to avoid split horizonissues from preventing routing updates?A.Configure a separate sub-interface for each PVC with a unique DLCI and subnet assigned to thesub-interface.B.Configure each Frame Relay circuit as a point-to-point line to support multicast and broadcast traffic.C.Configure many sub-interfaces on the same subnet.D.Configure a single sub-interface to establish multiple PVC connections to multiple remote router interfaces.Answer:A8Refer to the exhibit.Which statement describes DLCI17?A.DLCI17xn R2and R3.B.DLCI17describes a PVC on R2.It cannot be used on R3or R1.C.DLCI17is the Layer2address used by R2to describe a PVC to R3.D.DLCI17describes the dial-up circuit from R2and R3to the service provider. Answer:C9Which routing protocol by default uses bandwidth and delay as metrics?A.RIPB.BGPC.OSPFD.EIGRPAnswer:D10Refer to the exhibit.Switch-1needs to send data to a host with a MAC address of00b0.d056.efa4.What will Switch-1do with this data?A.Switch-1will drop the data because it does not have an entry for that MAC address.B.Switch-1will flood the data out all of its ports except the port from which the data originated.C.Switch-1will send an ARP request out all its ports except the port from which the data originated.D.Switch-1will forward the data to its default gateway.Answer:B11Refer to the exhibit.Why would the network administrator configure RA in this manner?A.To give students access to the InternetB.To prevent students from accessing the command prompt of RAC.To prevent administrators from accessing the console of RAD.To give administrators access to the InternetE.To prevent students from accessing the InternetF.To prevent students from accessing the Admin networkAnswer:B12While troubleshooting a network connectivity problem,a technician observes steady link lights on boththe workstation NIC and the switch port to which the workstation is connected.However,when the ping command is issued from the workstation,the output message"Request timed out."is displayed.At which layer of the OSI model does the problem most likely exist?A.The session layerB.The protocol layerC.The data link layerD.The access layerE.The network layerF.The application layerAnswer:E13A network administrator has configured two switches,named London and Madrid,to use VTP. However,the switches are not sharing VTP messages.Given the command output shown in the graphicWhy are these switches not sharing VTP messages?A.The VTP version is not correctly configured.B.The VTP operating mode is not correctly configured.C.The VTP domain name is not correctly configured.D.VTP pruning mode is disabled.E.VTP V2mode is disabled.F.VTP traps generation is disabled.Answer:C14On point-to-point networks,OSPF hello packets are addressed to which address?A.127.0.0.1B.172.16.0.1C.192.168.0.5D.223.0.0.1E.224.0.0.5F.254.255.255.255Answer:E15Refer to the exhibit.The switches on a campus network have been interconnected as shown.All of the switches are running Spanning Tree Protocol with its default settings.Unusual traffic patterns are observed and it is discovered that Switch9is the root bridge.Which change will ensure that Switch1will be selected as the root bridge instead of Switch9?A.Lower the bridge priority on Switch1.B.Raise the bridge priority on Switch1.C.Lower the bridge priority on Switch9.D.Raise the bridge priority on Switch9.E.Disable spanning tree on Switch9.F.Physically replace Switch9with Switch1in the topology.Answer:A16You just entered the following command:Company(config)#line console0A.Configure the terminal type.B.Enter protocol parameters for a serial line.C.Create a password on the console terminal line.D.Establish a terminal type4connection to a remote host.Answer:C17The part of Company network is shown below:According to the diagram,which of the following is true about the internetwork?pany2is the root bridge.B.Spanning Tree is not runn ing.C.No collisions can occur in traffic between CompanyB and CompanyC.panyD and Company Server1are in the same network.E.If Fa0/0is down on Company-R,PassGuideA cannot access Company Server1Answer:E18Which three of the following are reasons for assigning ports to VLANs on a switch?(Choose three.)A.to permit more devices to connect to the networkB.to iscC.to logically group hosts on the basis of functionD.to increase network securityAnswer:B,C,D19The Company network is shown below:Based on the information shown above,when the Company network administrator attempts to ping Host Company-PC2from Host Company-PC1and shown.What is a possible problem?A.The link between Company1and Company2is down.B.Interface Fa0/0on Company2is shutdown.C.The link between Company2and Company3is down.D.The default gateway on Company-PC1is incorrect.Answer:C20What is the objective of a default route?A.Offering routing to override the configured dynamic routing protocolB.Offering routing to a local web serverC.Offering routing from an ISP to a stub networkD.Offering routing to a destination that is not specified in the routing table and which is outside the local networkAnswer:D21Which three benefits are of VLANs?(Choose three.)A.To increase the size of collision domains.B.To allow logical grouping of users by function.C.To enhance network security.D.To increase the number of broadcast domains while decreasing the size of the broadcast domains. Answer:B,C,D22A default Frame Relay WAN is classified as what type of physical network?A.Point-to-pointB.Broadcast multi-accessC.Nonbroadcast multi-accessD.Nonbroadcast multipointE.Broadcast point-to-multipointAnswer:C23Refer to the exhibit.How many broadcast domains exist in the exhibited topology?A.OneB.TwoC.ThreeD.FourE.FiveF.SixAnswer:C24The command frame-relay map ip10.121.16.8102broadcast was entered on the router.Which of thefollowing statements is true concerning this command?A.This command should be executed from the global configuration mode.B.The IP address10.121.16.8is the local router port used to forward data.C.102is the remote DLCI that will receive the information.D.This command is required for all Frame Relay configurations.E.The broadcast option allows packets,such as RIP updates,to be forwarded across the PVC. Answer:E25Which type of attack is characterized by a flood of packets that are requesting a TCP connection to a server?A.Denial of serviceB.Brute forceC.ReconnaissanceD.Trojan horseAnswer:A26Which of the following are associated with the application layer of the OSI model?(Choose two.)A.PingB.TelnetC.FTPD.TCPE.IPAnswer:B,C27What are two recommended ways of protecting network device configuration files from outside network security threats?(Choose two.)A.Allow unrestricted access to the console or VTY ports.e a firewall to restrict access from the outside to the network devices.C.Always use Telnet to access the device command line because its data is automatically encrypted.e SSH or another encrypted and authenticated transport to access device configurations.E.Prevent the loss of passwords by disabling password encryption.Answer:B,D28Refer to the exhibit.Switch1has just been restarted and has passed the POST routine.Host A sends its initial frame to Host C.What is the first thing the switch will do as regards populating the switching table?A.Switch1will add192.168.23.4to the switching table.B.Switch1will add192.168.23.12to the switching table.C.Switch1will add000A.8A47.E612to the switching table.D.Switch1will add000B.DB95.2EE9to the switching table.Answer:C29Exhibit:The user of Host1wants to ping the DSL modem/router at192.168.1.254.Based on the Host1 ARP table that is shown in the exhibit,what will Host1do?A.Send a unicast ARP packet to the DSL modem/routerB.Send unicast ICMP packets to the DSL modem/routerC.Send Layer3broadcast packets to which the DSL modem/router respondsD.Send a Layer2broadcast that is received by Host2,the switch,and the DSL modem/router Answer:B30Which spread spectrum technology does the802.11b standard define for operation?A.IRB.DSSSC.FHSSD.DSSS and FHSSE.IR,FHSS,and DSSSAnswer:B31Refer to the exhibit.Assume that all router interfaces are operational and correctly configured.In addition,assume that OSPF has been correctly configured on router R2.How will the default route configured on R1affect the operation of R2?A.Any packet destined for a network that is not directly connected to router R1will be dropped.B.Any packet destined for a network that is not directly connected to router R2will be dropped immediately.C.Any packet destined for a network that is not directly connected to router R2will be dropped immediately because of the lack of a gateway on R1.D.The networks directly connected to router R2will not be able to communicate with the172.16.100.0, 172.16.100.128,and172.16.100.64subnetworks.E.Any packet destined for a network that is not referenced in the routing table of router R2will be directed to R1.R1will then send that packet back to R2and a routing loop will occur.Answer:E32A network interface port has collision detection and carrier sensing enabled on a shared twisted pair network.From this statement,what is known about the network interface port?A.This is a10Mb/s switch port.B.This is a100Mb/s switch port.C.This is an Ethernet port operating at half duplex.D.This is an Ethernet port operating at full duplex.E.This is a port on a network interface card in a PC.Answer:C33Refer to the topology and router configuration shown in the graphic.A host on the LAN is accessing an FTP server across the Internet.Which of the following addresses could appear as a source address for the packets forwarded by the router to the destination server?A.10.10.0.1B.10.10.0.2C.199.99.9.33D.199.99.9.57E.200.2.2.17F.200.2.2.18Answer:D34What is the purpose of the Cisco VLAN Trunking Protocol?A.To allow traffic to be carried from multiple VLANs over a single link between switchesB.To allow native VLAN information to be carried over a trunk linkC.To allow for managing the additions,deletions,and changes of VLANs between switchesD.To provide a mechanism to manually assign VLAN membership to switch portsE.To provide a mechanism to dynamically assign VLAN membership to switch portsAnswer:C35Which two statements describe the Cisco implementation of VLANs?(Choose two.)A.VLAN1is the default Ethernet VLAN.B.CDP advertisements are only sent on VLAN1002.C.By default,the switch IP address is in VLAN1005.D.VLANs1002through1005are automatically created and cannot be deleted.Answer:A,D36Refer to the exhibit.What two results would occur if the hub were to be replaced with a switch that is configured with one Ethernet VLAN?(Choose two.)A.The number of collision domains would remain the same.B.The number of collision domains would decrease.C.The number of collision domains would increase.D.The number of broadcast domains would remain the same.E.The number of broadcast domains would decrease.F.The number of broadcast domains would increase.Answer:C,D37Three access points have been installed and configured to cover a small office.What term defines thewireless topology?A.BSSB.IBSSC.ESSD.SSIDAnswer:C38A TCP/IP transfer is diagrammed in the exhibit.A window size of three has been negotiated for this transfer.Which message will be returned from the receiver to the sender as part of this TCP/IP transfer?A.Send ACK1-3B.Send ACK3C.Send ACK4D.Send ACK4-6E.Send ACK6F.Send ACK7Answer:C39Which two statements are true based the output of the show frame-relay lmi command issued on the Branch router?(Choose two.)A.LMI messages are being sent on DLCI0.B.LMI messages are being sent on DLCI1023.C.Interface Serial0/0is not configured to encapsulate Frame Relay.D.The Frame Relay switch is not responding to LMI requests from the router.E.The LMI exchange between the router and Frame Relay switch is functioning properly.F.The router is providing a clock signal on Serial0/0on the circuit to the Frame Relay switch. Answer:A,D40.Refer to the graphic.A static route to the10.5.6.0/24network is to be configured on the HFD router. Which commands will accomplish this?(Choose two.)A.HFD(config)#ip route10.5.6.00.0.0.255fa0/0B.HFD(config)#ip route10.5.6.00.0.0.25510.5.4.6C.HFD(config)#ip route10.5.6.0255.255.255.0fa0/0D.HFD(config)#ip route10.5.6.0255.255.255.010.5.4.6E.HFD(config)#ip route10.5.4.60.0.0.25510.5.6.0F.HFD(config)#ip route10.5.4.6255.255.255.010.5.6.0Answer:CD41.What should be done prior to backing up an IOS image to a TFTP server?(Choose three.)A.Make sure that the server can be reached across the network.B.Check that authentication for TFTP access to the server is set.C.Assure that the network server has adequate space for the IOS image.D.Verify file naming and path requirements.E.Make sure that the server can store binary files.F.Adjust the TCP window size to speed up the transfer.Answer:ACD42.What are the possible trunking modes for a switch port?(Choose three.)A.transparentB.autoC.onD.desirableE.clientF.forwardingAnswer:BCD43.The network172.25.0.0has been divided into eight equal subnets.Which of the following IP addresses can be assigned to hosts in the third subnet if the ip subnet-zero command is configured on the router?(Choose three.)A.172.25.78.243B.172.25.98.16C.172.25.72.0D.172.25.94.255E.172.25.96.17F.172.25.100.16Answer:ACD44.Refer to the graphic.Host1cannot receive packets from Host2.Assuming that RIP v1is the routing protocol in use,what is wrong with the IP configuration information shown?(Choose two.)A.The fa0/1interface of router R2has been assigned a broadcast address.B.The fa0/1network on router R2overlaps with the LAN attached to R1.C.Host2has been assigned the incorrect subnet mask.D.Host1has been configured with the255.255.248.0subnet mask.E.Host2on router R2is on a different subnet than its gateway.Answer:BC45.What are three valid reasons to assign ports to VLANs on a switch?(Choose three.)A.to make VTP easier to implementB.to isolate broadcast trafficC.to increase the size of the collision domainD.to allow more devices to connect to the networkE.to logically group hosts according to functionF.to increase network securityAnswer:BEF46.Refer to the topology shown in the exhibit.Which ports will be STP designated ports if all the links areoperating at the same bandwidth?(Choose three.)A.Switch A-Fa0/0B.Switch A-Fa0/1C.Switch B-Fa0/0D.Switch B-Fa0/1E.Switch C-Fa0/0F.Switch C-Fa0/1Answer:BCD47.Which statements describe two of the benefits of VLAN Trunking Protocol?(Choosetwo.)A.VTP allows routing between VLANs.B.VTP allows a single switch port to carry information to more than one VLAN.C.VTP allows physically redundant links while preventing switching loops.D.VTP simplifies switch administration by allowing switches to automatically share VLAN configuration information.E.VTP helps to limit configuration errors by keeping VLAN naming consistent across the VTP domain.F.VTP enhances security by preventing unauthorized hosts from connecting to the VTP domain. Answer:DE48What are two results of entering the Switch(config)#vtp mode client command on a Catalyst switch?(Choose two.)A.The switch will ignore VTP summary advertisements.B.The switch will forward VTP summary advertisements.C.The switch will process VTP summary advertisementsD.The switch will originate VTP summary advertisements.E.The switch will create,modify and delete VLANs for the entire VTP domain.Answer:BC49.A network administrator issues the ping192.168.2.5command and successfully tests connectivity to a host that has been newly connected to the network.Which protocols were used during the test? (Choose two.)A.ARPB.CDPC.DHCPD.DNSE.ICMPAnswer:AE50.Refer to the exhibit.Host A is to send data to Host B.How will Router1handle the data frame received from Host A?(Choose three.)A.Router1will strip off the source MAC address and replace it with the MAC address on the forwardingFastEthernet interface.B.Router1will strip off the source IP address and replace it with the IP address on the forwarding FastEthernetinterface.C.Router1will strip off the destination MAC address and replace it with the MAC address of Host B.D.Router1will strip off the destination IP address and replace it with the IP address of Host B.E.Router1will forward the data frame out interface FastEthernet0/1.F.Router1will forward the data frame out interface FastEthernet0/2.Answer:ACF51.Refer to the exhibit.What will Router1do when it receives the data frame shown?(Choose three.)A.Router1will strip off the source MAC address and replace it with the MAC address0000.0c36.6965.B.Router1will strip off the source IP address and replace it with the IP address192.168.40.1.C.Router1will strip off the destination MAC address and replace it with the MAC address0000.0c07.4320.D.Router1will strip off the destination IP address and replace it with the IP address of192.168.40.1.E.Router1will forward the data packet out interface FastEthernet0/1.F.Router1will forward the data packet out interface FastEthernet0/2.Answer:ACF52.Refer to the exhibit.Host A pings Host B.What source MAC address and source IP address are contained in the frame as the frame leaves R2destined for host B?A.abcd.abcd.a001B.abcd.abcd.b002C.abcd.abcd.c003D.10.2.0.15E.10.0.64.1F.10.0.128.15Answer:BD53.Refer to the exhibit.A network associate has configured OSPF with the command:City(config-router)#network192.168.12.640.0.0.63area0After completing the configuration,the associate discovers that not all the interfaces are participating in OSPF.Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement?(Choose three.)A.FastEthernet0/0B.FastEthernet0/1C.Serial0/0D.Serial0/1.102E.Serial0/1.103F.Serial0/1.104Answer:BCD54.A Catalyst2950needs to be reconfigured.What steps will ensure that the old configuration is erased?(Choose three.)A.Erase flash.B.Restart the switch.C.Delete the VLAN database.D.Erase the runnin configuration.E.Erase the startup configuration.F.Modify the configurationregister.Answer:BCE55.Refer to the exhibit.The FMJ manufacturing company is concerned about unauthorized access to the Payroll Server.The Accounting1,CEO,Mgr1,and Mgr2workstations should be the only computers with access to the Payroll Server.What two technologies should be implemented to help prevent unauthorized access to the server?(Choose two.)A.access listsB.encrypted router passwordsC.STPD.VLANsE.VTPF.wireless LANsAnswer:AD56.Refer to the exhibit.What commands must be configured on the2950switch and the router to allow communication between host1and host2?(Choose two.)A.Router(config)#interface fastethernet0/0Router(config-if)#ip address192.168.1.1255.255.255.0Router(config-if)#no shut downB.Router(config)#interface fastethernet0/0Router(config-if)#no shut downRouter(config)#interface fastethernet0/0.1Router(config-subif)#encapsulation dot1q10Router(config-subif)#ip address192.168.10.1255.255.255.0Router(config)#interface fastethernet0/0.2Router(config-subif)#encapsulation dot1q20Router(config-subif)#ip address192.168.20.1255.255.255.0C.Router(config)#router eigrp100Router(config-router)#network192.168.10.0Router(config-router)#network192.168.20.0D.Switch1(config)#vlan databaseSwitch1(config-vlan)#vtp domain XYZSwitch1(config-vlan)#vtp serverE.Switch1(config)#interface fastethernet0/1Switch1(config-if)#switchport mode trunkF.Switch1(config)#interface vlan1Switch1(config-if)#ip default-gateway192.168.1.1Answer:BE57.Which three Layer2encapsulation types would be used on a WAN rather than a LAN?(Choose three.)A.HDLCB.EthernetC.Token RingD.PPPE.FDDIF.Frame RelayAnswer:ADF58.Refer to the exhibit.The two connected ports on the switch are not turning orange or green.What would be the most effective steps to troubleshoot this physical layer problem?(Choose three.)A.Ensure that the Ethernet encapsulations match on the interconnected router and switch ports.B.Ensure that cables A and B are straight-through cables.C.Ensure cable A plugged into a trunk port.D.Ensure the switch has power.E.Reboot all of the devices.F.Reseat all cables.Answer:BDF59.What can be determined from the line of show ip route output shown in the exhibit?(Choose two.)A.The next routing update can be expected in35seconds.B.The IP address10.10.10.6is configured on S0/1.C.The IP address10.10.10.8is configured on S0/1.D.This route is using the default administrative distance.E.The10.10.10.8network is two hops away from this router.Answer:DE60.Refer to the exhibit.All of the routers in the network are configured with the ip subnet-zero command.Which network addresses should be used for Link A and Network A?(Choose two.)work A-172.16.3.48/26work A-172.16.3.128/25work A-172.16.3.192/26D.Link A-172.16.3.0/30E.Link A-172.16.3.40/30F.Link A-172.16.3.112/30Answer:BD61.Which two subnetworks would be included in the summarized address of172.31.80.0/20? (Choose two.)A.172.31.17.4/30B.172.31.51.16/30C.172.31.64.0/18D.172.31.80.0/22E.172.31.92.0/22F.172.31.192.0/18Answer:DE62.The network administrator has discovered that the power supply has failed on a switch in the company LAN and that the switch has stopped functioning.It has been replaced with a Cisco Catalyst 2950series switch.What must be done to ensure that this new switch becomes the root bridge on the network?A.Lower the bridge prioritynumber.B.Change the MAC address of the switch.C.Increase the VTP revision number for the domain.D.Lower the root path cost on the switch ports.E.Assign the switch an IP address with the lowestvalue.Answer:A63.Refer to the exhibit.Assume that all of the router interfaces are operational and configured correctly.How will router R2be affected by the configuration of R1that is shown in the exhibit?A.Router R2will not form a neighbor relationship with R1.B.Router R2will obtain a full routing table,including a default route,from R1.C.R2will obtain OSPF updates from R1,but will not obtain a default route from R1.D.R2will not have a route for the directly connected serial network,but all other directly connected networks will be present,as well as the two Ethernet networks connected to R1.Answer:D64.Which three IP addresses can be assigned to hosts if the subnet mask is/27and subnet zero is usable? (Choose three.)A.10.15.32.17B.17.15.66.128C.66.55.128.1D.135.1.64.34E.129.33.192.192F.192.168.5.63Answer:ACD65.Refer to the exhibit.A packet with a source IP address of192.168.2.4and a destination IP address of 10.1.1.4arrives at the HokesB router.What action does the router take?A.forwards the received packet out the Serial0/0interfaceB.forwards a packet containing an EIGRP advertisement out the Serial0/1interfaceC.forwards a packet containing an ICMP message out the FastEthernet0/0interfaceD.forwards a packet containing an ARP request out the FastEthernet0/1interfaceAnswer:C66.Refer to the exhibit.From RouterA,a network administrator is able to ping the serial interface of RouterB but unable to ping any of the subnets attached to RouterB.Based on the partial outputs in the exhibit,what could be the problem?。
ccna第二学期练习答案中文
ERouting Chapter 1 - CCNA Exploration: 路由协议和概念(版本4.0)1口令可用于限制对Cisco IOS 所有或部分内容的访问。
请选择可以用口令保护的模式和接口。
(选择三项。
)VTY 接口控制台接口特权执行模式2路由器从相连的以太网接口收到消息后,会更改哪项报头地址,再将消息从另一个接口发送出去?第 2 层源地址和目的地址3请参见图示。
网络管理员已经为路由器连接到直连网络的接口配置了如图所示的IP 地址。
从路由器ping 相连网络上的主机口之间相互ping 都会遭到失败。
此问题最可能的原因是什么?必须使用no shutdown命令启用接口。
4请参见图示。
主机 A ping 主机B。
当R4 收到对以太网接口的ping 时,哪两块报头信息包括在内?(选择两项。
)目的IP 地址:192.168.10.134目的MAC 地址:9999.DADC.12345网络管理员刚把新配置输入Router1。
要将配置更改保存到NVRAM,应该执行哪一条命令?Router1# copy running-config startup-config6您需要配置图中所示的串行连接,必须在Sydney 路由器上发出以下哪条配置命令才能与Melbourne 站点建立连接?(选Sydney(config-if)# ip address 201.100.53.2 255.255.255.0Sydney(config-if)# no shutdownSydney(config-if)# clock rate 560007请参见图示。
从路由器的运行配置输出可得出什么结论?显示的命令决定了路由器的当前运行情况。
8请参见图示。
在主机 2 连接到LAN 上的交换机后,主机2 无法与主机 1 通信。
导致此问题的原因是什么?主机 1 和主机2 位于不同的网络中。
9输入以下命令的作用是什么?R1(config)# line vty 0 4R1(config-line)# password check123R1(config-line)# login设置通过Telnet 连接该路由器时使用的口令10以下哪一项正确描述了路由器启动时的顺序?加载bootstrap、加载IOS、应用配置11加载配置文件时的默认顺序是怎样的?NVRAM、TFTP、CONSOLE12请参见图示。
CCNA Exploration网络基础知识考试答案

CCNA Exploration:网络基础知识考试答案CCNA Exploration: 网络基础知识第二章网络通信001 TCP/IP 网络接入层有何作用?路径确定和数据包交换数据表示、编码和控制可靠性、流量控制和错误检测详细规定构成物理链路的组件及其接入方法将数据段划分为数据包002下列哪些陈述正确指出了中间设备在网络中的作用?(选择三项)确定数据传输路径发起数据通信重新定时和重新传输数据信号发送数据流管理数据流数据流最后的终止点003下列哪三项陈述是对局域网(LAN) 最准确的描述?(选择三项)LAN 通常位于一个地域内。
此类网络由由一个组织管理。
LAN 中的不同网段之间一般通过租用连接的方式连接。
此类网络的安全和访问控制由服务提供商控制。
LAN 为同一个组织内的用户提供网络服务和应用程序访问。
此类网络的每个终端通常都连接到电信服务提供商(TSP)。
004 什么是PDU?传输期间的帧损坏在目的设备上重组的数据因通信丢失而重新传输的数据包特定层的封装005 OSI 模型哪两层的功能与TCP/IP 模型的网络接入层相同?(选择两项)网络层传输层物理层数据链路层会话层006请参见图示。
所示网络属于哪一类型?WANMANLANWLAN007 以下哪种特征正确代表了网络中的终端设备?管理数据流发送数据流重新定时和重新传输数据信号确定数据传输路径008 第4 层端口指定的主要作用是什么?标识本地介质中的设备标识源设备和目的设备之间的跳数向中间设备标识通过该网络的最佳路径标识正在通信的源终端设备和目的终端设备标识终端设备内正在通信的进程或服务009 请参见图示。
下列哪组设备仅包含终端设备?A、C、DB、E、G、HC、D、G、H、I、JE、F、H、I、J010 选择关于网络协议的正确陈述。
(选择三项)定义特定层PDU 的结构规定实现协议层功能的方式概述层与层之间通信所需的功能限制了硬件兼容性需要取决于协议层的封装过程杜绝厂商之间的标准化011请参见图示。
ccna第二学期练习答案

c c n a第二学期练习答案(总45页)--本页仅作为文档封面,使用时请直接删除即可----内页可以根据需求调整合适字体及大小--ERouting Chapter 1 - CCNA Exploration: 路由协议和概念(版本1口令可用于限制对 Cisco IOS 所有或部分内容的访问。
请选择可以用口令保护的模式和接口。
(选择三项。
)VTY 接口控制台接口特权执行模式2路由器从相连的以太网接口收到消息后,会更改哪项报头地址,再将消息从另一个接口发送出去第 2 层源地址和目的地址3请参见图示。
网络管理员已经为路由器连接到直连网络的接口配置了如图所示的 IP 地址。
从路由器 ping 相连网络路由器接口之间相互 ping 都会遭到失败。
此问题最可能的原因是什么必须使用no shutdown命令启用接口。
4请参见图示。
主机 A ping 主机 B。
当 R 网接口的 ping 时,哪两块报头信息包括在内(选择两项。
)目的 IP 地址:目的 MAC 地址:5网络管理员刚把新配置输入 Router1。
要将配置更改保存到 NVRAM,应该执行哪一条命令Router1# copy running-config startup-config6您需要配置图中所示的串行连接,必须在 Sydney 路由下哪条配置命令才能与 Melbourne 站点建立连接(选择三项)Sydney(config-if)# ip addressSydney(config-if)# no shutdownSydney(config-if)# clock rate 560007请参见图示。
从路由器的运行配置输出可得出什么结论显示的命令决定了路由器的当前运行情况。
8请参见图示。
在主机 2 连接到 LAN 上的交换机后,主主机 1 通信。
导致此问题的原因是什么主机 1 和主机 2 位于不同的网络中。
9输入以下命令的作用是什么?R1(config)# line vty 0 4R1(config-line)# password check123R1(config-line)# login设置通过 Telnet 连接该路由器时使用的口令10以下哪一项正确描述了路由器启动时的顺序加载 bootstrap、加载 IOS、应用配置11加载配置文件时的默认顺序是怎样的NVRAM、TFTP、CONSOLE12请参见图示。
ccna考试题及答案
ccna考试题及答案1. 以下哪项是网络层的功能?A. 路由选择B. 错误检测C. 流量控制D. 封装数据包答案:A2. 在OSI模型中,哪一层负责在网络中传输数据?A. 应用层B. 传输层C. 会话层D. 网络层答案:D3. 以下哪个协议是用于在IP网络中发现网络设备的?A. ARPB. RARPC. ICMPD. OSPF答案:A4. 在TCP/IP模型中,哪一层与OSI模型的传输层相对应?A. 应用层B. 互联网层C. 网络接口层D. 传输层答案:D5. 以下哪个地址是一个有效的IPv4地址?A. 192.168.1.256B. 192.168.1.1C. 10.0.0.0D. 172.16.300.1答案:B6. 在配置路由器时,以下哪个命令用于进入全局配置模式?A. enableB. configure terminalC. privileged execD. user exec答案:B7. 以下哪个命令用于在Cisco设备上显示当前配置?A. show running-configB. show startup-configC. show configD. show current-config答案:A8. 在Cisco设备上,以下哪个命令用于保存当前的配置到启动配置文件?A. copy running-config startup-configB. copy startup-config running-configC. save running-configD. save startup-config答案:A9. 以下哪个命令用于在Cisco设备上查看所有接口的状态?A. show interfacesB. show ip interface briefC. show interface statusD. show running-config interface答案:B10. 在Cisco设备上,以下哪个命令用于关闭接口?A. shutdownB. no shutdownC. disableD. no enable答案:A11. 以下哪个命令用于在Cisco设备上启用接口?A. shutdownB. no shutdownC. disableD. no enable答案:B12. 在配置静态路由时,以下哪个命令用于指定下一跳地址?B. ip static-routeC. route ipD. static-route ip答案:A13. 以下哪个命令用于在Cisco设备上清除ARP表?A. clear arp-cacheB. clear arpC. clear arp tableD. clear ip arp答案:D14. 在配置动态路由协议时,以下哪个命令用于在接口上启用RIP?A. ip rip enableB. ip rip receiveD. network rip答案:C15. 以下哪个命令用于在Cisco设备上查看RIP路由表?A. show ip ripB. show ip route ripC. show ripD. show ip protocols答案:B16. 在配置EIGRP时,以下哪个命令用于指定自动汇总?A. metric weightsB. auto-summaryC. network auto-summaryD. no auto-summary答案:B17. 以下哪个命令用于在Cisco设备上查看EIGRP邻居?A. show ip eigrp neighborsB. show eigrp neighborsC. show ip eigrpD. show eigrp interfaces答案:A18. 在配置OSPF时,以下哪个命令用于指定路由器ID?A. router-idB. router ospfC. networkD. area答案:A19. 以下哪个命令用于在Cisco设备上查看OSPF路由表?A. show ip ospfB. show ip ospf databaseC. show ospfD. show ip route ospf答案:D20. 在配置VLAN时,以下哪个命令用于创建一个新的VLAN?A. vlan databaseB. configure terminalC. vlan [vlan-id]D. new-vlan答案:C21. 以下哪个命令用于将接口分配给VLAN?A. switchport mode accessB. switchport mode trunkC. switchport access vlan [vlan-id]D. switchport trunk vlan [vlan-id]答案:C22. 在配置交换机时,以下哪个命令用于将接口设置为Trunk 模式?A. switchport mode accessB. switchport mode trunkC. switchport access vlan [vlan-id]D. switchport trunk vlan [vlan-id]答案:B23. 以下哪个命令用于在Cisco设备上查看VLAN配置?A. show vlanB. show vlan briefC. show vlan detailD. show vlan all答案:B24. 在配置VTP时,以下哪个命令用于将交换机设置为VTP服务器模式?A. vtp mode serverB. vtp mode clientC. vtp mode transparentD. vtp mode off答案:A25. 以下哪个命令用于在Cisco设备上查看VTP状态?A. show vtp statusB. show vtp statisticsC. show vtp passwordD. show vtp configuration答案:A26. 在配置STP时,以下哪个命令用于设置根桥?A. spanning-tree root primaryB. spanning-tree root secondaryC. spanning-tree root primary [priority]D. spanning-tree root secondary [priority]答案:C27. 以下哪个命令用于在Cisco设备上查看STP状态?A. show spanning-treeB. show spanning-tree detailC. show spanning-tree summaryD. show spanning-tree interface答案:A28. 在配置VLAN Trunking Protocol (VTP) 时,以下哪个命令用于设置VTP域名?A. vtp domain [domain-name]B. vtp password [password]C. vtp mode [mode]D. vtp version [version]答案:A29. 以下哪个命令用于在Cisco设备上查看当前的VTP版本?A. show vtp statusB. show vtp statisticsC. show vtp passwordD. show vtp configuration答案:A30. 在配置端口安全时,以下哪个命令用于限制接口上可以学习到的最大MAC地址数量?A. switchport port-security maximum [mac-count]B. port-security maximum [mac-count]C. switchport port-security violation restrictD. port-security violation shutdown答案:A这些题目和答案仅供学习和参考之用,实际的CCNA考试内容和形式可能会有所不同。
CCNA第二学期考试答案
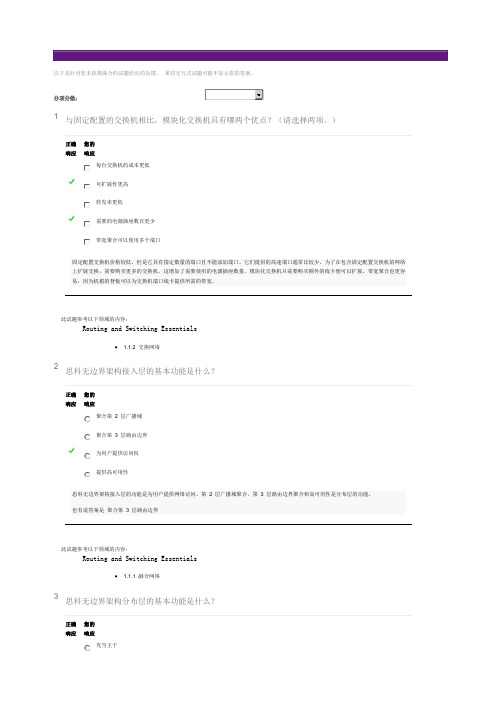
以下是针对您未获得满分的试题给出的反馈。
某些交互式试题可能不显示您的答案。
分项分数:1与固定配置的交换机相比,模块化交换机具有哪两个优点?(请选择两项。
)正确响应您的响应每台交换机的成本更低可扩展性更高转发率更低需要的电源插座数目更少带宽聚合可以使用多个端口固定配置交换机价格较低,但是它具有指定数量的端口且不能添加端口。
它们提供的高速端口通常比较少。
为了在包含固定配置交换机的网络上扩展交换,需要购买更多的交换机。
这增加了需要使用的电源插座数量。
模块化交换机只需要购买额外的线卡便可以扩展。
带宽聚合也更容易,因为机箱的背板可以为交换机端口线卡提供所需的带宽。
此试题参考以下领域的内容:Routing and Switching Essentials• 1.1.2 交换网络2思科无边界架构接入层的基本功能是什么?正确响应您的响应聚合第 2 层广播域聚合第 3 层路由边界为用户提供访问权提供高可用性思科无边界架构接入层的功能是为用户提供网络访问。
第 2 层广播域聚合、第 3 层路由边界聚合和高可用性是分布层的功能。
也有说答案是聚合第 3 层路由边界此试题参考以下领域的内容:Routing and Switching Essentials• 1.1.1 融合网络3思科无边界架构分布层的基本功能是什么?正确响应您的响应充当主干聚合所有园区块聚合第 3 层路由边界为用户提供访问权思科无边界架构的分布层的一项基本功能是在不同的VLAN 之间路由。
充当主干和聚合园区块是核心层的功能。
为用户提供访问是接入层的功能。
此试题参考以下领域的内容:Routing and Switching Essentials• 1.1.1 融合网络4若将大端口密度、容错和低价作为重要指标,应使用哪个交换机外形因素?正确响应您的响应固定配置交换机模块化交换机可配备机架的1U 交换机可堆叠式交换机堆叠式交换机可以使用特殊电缆实现互联,从而在交换机之间提供高带宽的吞吐量,并像单个大型交换机一样运行。
CCNA第二学期官方章节考试题之《距离矢量路由协议》(附答案)46doc

数据包在路由器的两个环回接口之间来回传递
从目的地返回的路径与出发路径不同而形成
数据包在一系列路由器间不断传输却始终无法到达其真正的目的地的情况路由从一种路由协议到另一种路由协议的分布
2
用于在发送到其它路由器的更新中将路由标记为不可达
防止定期更新消息错误地恢复已经不可用的路由
防止从收到更新的接口通告同一网络
限制数据包在被丢弃之前在网络中传输的时间或跳数
通过设置最大跳数来为每一距离矢量路由协议定义最大度量值
4以
路由环路
不一致的流量转发
除非系统收敛,否则不会转发任何流量
路由表条目不一致
路由表更新被发送到错误的目的地
6运
立即将其加入路由表中
调整新路由的度量以显示增加的路由距离
将该路由从其传入接口以外的所有其它接口通告出去
发送
8下
它会在更新从路由器接口送出时缓冲更新,以此防止路由更新同步。
它会从下一次路由更新间隔中减去随机时间段(大小为指定间隔时间的
它会使路由器跳过每一个其它计划更新时间,以此防止路由更新同步。
它会强制路由器在发送自身更新之前侦听链路上的其它更新是何时发送的,以此防止路由更新同步10
13以15水
17R
19哪
抑制计时器将等候
如果在
更新计时器将请求有关从路由器Hello。
CCNA_ENetwork_Chapter_10_答案(中文版)-dengwenhui

1以下哪种设备用于创建或划分广播域?集线器交换机网桥路由器中继器2网络管理员必须在网络中使用电缆长度无需中继器即可达100 米的介质。
所选介质必须价格适中并易于安装,而且需要在布制的现成建筑物内实施安装。
哪种类型的介质最适合这些要求?STPUTP同轴单模光纤多模光纤3请参见图示。
PC1 会将哪个目的IP 地址放入发往PC2 的数据包报头中?192.168.1.1192.168.2.1192.168.2.2192.168.3.1192.168.3.544一家公司计划将其网络分为多个子网,每个子网最多支持27 台主机。
哪一子网掩码可支持所需的主机数,同时让每个子网址最少?255.255.255.0255.255.255.192255.255.255.224255.255.255.240255.255.255.2485“衰减”一词在数据通信中是什么意思?信号强度随着距离的增加而减弱信号到达其目的地的时间信号从一个线对泄露到另一个线对网络设备对信号的强化6请参见图示。
网络管理员决定使用数据包捕获软件评估从学生子网到Internet 之间的所有流量。
要确保捕获所有数据包,应络设备将监控站点连接到R1 和R2 之间的网络?集线器路由器防火墙设备无线接入点7下列哪些因素使光缆比铜缆更适用于连接不同建筑物?(选择三项)每根电缆覆盖的距离更远安装成本更低EMI/RFI 的影响有限耐用的连接潜在带宽更高易于端接8将UTP 以太网端口设置为MDI 或MDIX 运行的两种常用方法是什么?(选择两项)与电缆的颜色代码关联选择和配置电缆使用电缆测试仪确定线序自动检测和协商端口的MDI/MDIX 运行通过电子方式调换发射线对和接收线对9请参见图示。
下列关于图示拓扑的陈述,哪三项是正确的?(选择三项)主机 B 和 C 位于同一个子网中。
存在五个广播域。
主机 B 使用交叉电缆连接到路由器。
存在四个广播域。
显示了五个网络。
主机 B 使用全反电缆连接到路由器。
最新CCNA认证试题及答案「中文版」

最新CCNA认证试题及答案「中文版」1、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ( )(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:11000000.10101000.00010011.1111111111111111.11111111.11110000.00000000主机位变成全0表示这个IP的网络地址主机槐涑扇?表示这个IP的广播地址RFC1918文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefix)172.16.0.0 - 172.31.255.255 (172.16/12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)2、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住IEEE802.1-------IEEE802.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
2022年CCNA认证试题及答案
2022年CCNA认证试题及答案1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住.1-------.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C某某某A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术与信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE定义的标准在工业界有极大的影响。
下面列出:.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-某(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ( )(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:..00010011. (00000000)主机位变成全0表示这个IP的.网络地址主机槐涑扇?表示这个IP的广播地址文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefi某)172.16.0.0 - 172.31.255.255 (172.16/12 prefi某)192.168.0.0 - 192.168.255.255 (192.168/16 prefi某)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?( )(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
ccna章节与期末答案

第一章:正确答案:2.4.5解析:由于不需要使用网络设备和专用服务器,对等网络易于创建,复杂性更低,且成本更少。
而且对等网络也没有集中管理。
这种网络安全性更低,不可扩展,而且那些同时充当客户端和服务器的设备可能性能更差正确答案:1析正确答案: 3.5解析:选择网络介质的条件包括:所选介质可以成功传送信号的距离、要安装所选介质的环境、必须传输的数据量和速度以及介质和安装的成本。
正确答案:3和4解析:终端设备上的应用程序可以生成数据,更改数据内容并且负责启动封装过程。
正确答案:1和4解析:终端设备会发出通过网络传输的数据。
中间设备会在链路发生故障时通过备用路径传输数据,并且会过滤数据传输以增强安全性。
网络介质提供网络消息的传输通道。
正确答案:4解析:外联网是公司外部的人或企业合作伙伴访问数据的网络区域。
内部网只描述通常仅供内部人员访问的网络区域。
当设备连接到有线网络时,有线 LAN 会受 BYOD(自带设备)影响。
使用大学无线 LAN 的设备多为平板电脑和智能手机。
大学生主要使用无线 WAN 来访问他们的手机运营商网络。
.正确答案:2解析:由于通过 Internet 可以联系在线供应商,所以家庭用户通过 Internet 进行网上购物。
内联网基本上是仅供内部使用的局域网。
外联网是外部合作伙伴访问组织内部特定资源的网络。
家庭用户并不一定使用 LAN 来访问 Internet。
例如,PC 可以通过调制解调器直接连接到 ISP。
正确答案:1解析:内部网这个术语用于表示一个组织的私有局域网和广域网连接。
内部网的设计旨在仅允许该组织的成员、员工或其他获得授权的人员进行访问。
正确答案:2和4解析:电缆和 DSL 均能实现高带宽、始终联网,并提供到主机计算机或 LAN 的以太网连接。
10正确答案:2和3解析:移动电话连接需要使用移动电话网络。
卫星连接通常用于家庭或企业外部不便使用物理布线的位置。
11正确答案:2解析:当对网络资源的请求超出了可用容量时,网络就会变得拥堵。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1.
请参见图示。
网络192.168.0.0/28 断开。
Router2 会立即向Router1 和Router3 发送什么类型的数据包?
查询网络192.168.0.0/28 的查询数据包
到224.0.0.9 的确认数据包
发送到255.255.255.255 的更新数据包
包含R2 新路由表的数据包
发送到192.168.1.1 和192.168.2.1 的单播更新数据包
2.哪两种事件将会导致链路状态路由器向所有邻居发送LSP?(选择两项。
)
30 秒计时器超时
网络拓扑结构发生变化时
运行贝尔曼-福特算法之后立即发送
DUAL FSM 建立拓扑数据库之后立即发送
路由器或路由协议初次启动时
3.链路状态路由过程的最后一步是什么?
将后继路由加入路由表中
SPF 计算到达每个目的网络的最佳路径
向所有邻居发送LSP 以收敛网络
运行DUAL 算法以找出到达目的网络的最佳路径
4.哪两项陈述正确描述了链路状态路由过程?(选择两项。
)
区域中的所有路由器都有链路状态数据库
区域中的每个路由器都将向所有邻居发送LSP
LSP 使用保留的组播地址224.0.0.10 来访问邻居
通过运行扩散更新算法(DUAL) 来防止路由环路
可靠传输协议(RTP) 是用于发送和接收LSP 的协议
5.
请参见图示。
在从路由器JAX 发送到路由器ATL 的LSP 中,可以看到哪种类型的信息?
跳数
路由的正常运行时间
链路的开销
正在使用的所有路由协议的列表
6.现代链路状态协议通过哪些功能来尽可能降低处理器和内存要求?
将路由拓扑结构分割成更小的区域
为路由计算分配较低的处理优先级
使用更新计时器限制路由更新
严格执行水平分割规则以减少路由表条目
7.为使网络达到收敛,每台链路状态路由器会执行哪三个步骤?(选择三项。
)
使用自动总结缩小路由表大小
构建一个链路状态数据包(LSP),其中包含每条直连链路的状态
向所有邻居发送LSP,邻居随后把接收到的所有LSP 存储到数据库中
按一定时间间隔发送Hello 数据包来发现邻居并建立相邻关系
构建完整的拓扑图并计算到达每个目的网络的最佳路径
使用DUAL FSM 选择有效且无环路的路径,并将路由插入到路由表中
8.在使用链路状态路由的网络中,什么可以加速收敛过程?
由网络变更触发的更新
按固定间隔发送的更新
仅发送给直连邻居的更新
包含完整路由表的更新
9.为什么使用链路状态路由的网络中很少发生路由环路?
每台路由器都根据跳数建立起对网络的直观印象。
路由器在网络中发送大量LSA 以检测路由环路。
每台路由器都建立起对网络的完整而且同步的印象。
路由器使用抑制计时器来防止路由环路
10.与距离矢量路由协议相比,链路状态路由协议有哪两项优势?(选择两项。
)
由于有了拓扑数据库,不再依赖于路由表。
每台路由器独立确定到每个网络的路由。
链路状态协议对路由器处理器能力的要求比距离矢量协议更低。
在初始LSP 泛洪后,传播拓扑结构的变更时占用更小带宽。
通过频繁发送定期更新,拓扑数据库中不正确路由数目降至最低
11.链路状态路由协议运行什么算法来计算到达目的网络的最短路径?
DUAL
Dijkstra
贝尔曼-福特
Diffie-Hellman
12.
请参见图示。
如果使用链路状态路由协议,以下哪项陈述正确描述了从10.0.0.0/24 网络到192.168.1.0/24 网络的流量所使用的路径?
BOS -> ATL,因为该路径的跳数最少
BOS -> ATL,因为该路径的开销最高
BOS -> ORL -> JAX -> ATL,因为该路径开销最低
流量将在所有链路间实施负载均衡
13.为了构建准确的SPF 树,区域内所有链路状态路由器上的哪个数据库或表必须相同?
路由表
邻接表
链路状态数据库
邻居表
拓扑数据库
14.以下哪两种路由协议使用Dijkstra 的最短路径优先算法?(选择两项。
)
RIPv1
RIPv2
IS-IS
BGP
EIGRP
OSPF
15.链路状态数据包何时发给邻居?
每30 秒
每180 秒
抑制计时器超时之后
链路进入运行状态或断开时
发生路由环路时
16.
请参见图示。
JAX 会如何处理来自ORL 的链路状态数据包?
向ORL 和BOS 路由器发送其更新后的路由表
将单独的链路状态数据包从连接到BOS 的接口发送出去
查询BOS 以了解是否有更佳的路由
只将其添加到本地路由表中,不执行任何其它操作
17.新任网络管理员的任务是为某软件开发公司选择合适的动态路由协议。
该公司拥有超过100 台路由
器,使用CIDR 和VLSM,要求快速收敛,并能同时使用Cisco 和非Cisco 设备。
该公司适合采用哪种路由协议?
RIP 第2 版
IGRP
EIGRP
OSPF
BGP
18.链路状态路由器在接收到来自邻居路由器的LSP 后会立即执行什么操作?
向邻居发送LSP
计算SPF 算法
运行贝尔曼-福特算法
计算到达目的网络的最佳路径
19.
请参见图示。
如果所有路由器和接口都配置为使用链路状态路由协议,则路由器 D 将从哪台路由器
收到hello 数据包?
A 和E
B 和C
A、B、C 和E
仅C
20.
请参见图示。
当使用链路状态路由协议的路由器 D 添加到网络中后,在它了解网络拓扑结构的过程中,其所做的第一件事是它向路由器 B 和 C 发送LSP 数据包。
它向网络中的所有路由器发送LSP 数据包。
它向网络中的所有路由器发送Hello 数据包。
它向路由器 A 和 E 发送有关其直连邻居的信息。
它向网络中的所有路由器发送有关其直连邻居的信息。
当其接口处于up 状态时,它便能获知自己的直连网络。
