现代操作系统(原书第3版)部分课后答案-第4章
现代操作系统(中文第三版)习题答案精编版

5002.395ns
11、一位校对人员注意到在一部将要出版的操作系统教科书手稿中有一个多次出 现的拼写错误。这本书大致有 700 页。每页 50 行,一行 80 个字符。若把文稿用 电子扫描,那么,主副本进入图 1-9 中的每个存储系统的层次要花费多少时间? 对于内存储方式,考虑所给定的存取时间是每次一个字符,对于磁盘设备,假定 存取时间是每次一个 1024 字符的盘块,而对于磁带,假设给定开始时间后的存 取时间和磁盘存取时间相同。
第2页
cztqwan 2017-06-19
答:原稿包含 80*50*700 = 2800000 字符。当然,这不可能放入任何目前的 CPU 中,但是如果可能的话,在寄存器中只需 2.8ms,在 Cache 中需要 5.6ms,在内 存中需要 28ms,整本书大约有 2700 个 1024 字节的数据块,因此从磁盘扫描大 约为 27 秒,从磁带扫描则需 2 分钟 7 秒。当然,这些时间仅为读取数据的时间。 处理和重写数据将增加时间。
cztqwan 2017-06-19
现代操作系统(第三版)习题答案
cztqwan 2017-06-19
(部分内容来源于网络,转载请注明出处)
cztqwan 2017-06-19
目录
第一章 绪论..................................................................................................................1 第二章 进程与线程......................................................................................................8 第三章 存储管理........................................................................................................21 第四章 文件系统........................................................................................................32 第五章 输入/输出 ......................................................................................................42 第六章 死锁................................................................................................................55 第七章 多媒体操作系统............................................................................................ 65 第八章 多处理机系统................................................................................................ 76 第九章 安全................................................................................................................88 第十章 实例研究 1:Linux .....................................................................................100 第十一章 实例研究 2:Windows Vista .................................................................. 110 第十二章 实例研究 3:Symbian 操作系统 ........................................................... 110 第十三章 操作系统设计.......................................................................................... 110
《操作系统》第三版第四章课后答案

2、Spooling技术
也备的技术
六、简答题
1、操作系统设备管理的目标是什么?
*提高I/O设备和CPU的利用率
*提高I/O速度
*为用户使用设备提供方便、统一的界面
3、引入Spooling系统有哪些好处
*提高了I/O速度,将独占设备改造成共享设备,实现了虚拟设备功能,提高了系统的并行性,减少了用户进程的等待时间,提高了进程的推进速度。
5、什么是设备独立性?引入设备独立性有哪些好处?
*设备独立性也称设备无关性,指应用程序与实际使用的物理设备无关,亦即它独立于具体的物理设备。用户程序中使用逻辑设备,由操作系统完成逻辑设备到物理设备的映射
第四章(与磁盘相关不做)
一、填空题
1:字符、块、字符
2:设备驱动
3:缓冲
5:输入井和输出井、输入缓冲区和输出缓冲区、输入进程和输出进程
6:中断源
7:中断、DMA、通道
二、单项选择题
1、B
2、B C
6、C
7、A
三、多项选择题
1、BC
2、AB
3、AB DE
四、判断题
1、×
2、√
3、√
4、×
五、名词解释
1、设备驱动程序
*好处:设备分配时的灵活性、易于实现I/O重定向、方便用户编程
计算机操作系统(第3版)课后习题参考答案(完整版)
1.设计现代OS的主要目标是什么?(1)有效性(2)方便性(3)可扩充性(4)开放性2.OS的作用可表现在哪几个方面?(1)OS作为用户与计算机硬件系统之间的接口(2)OS作为计算机系统资源的管理者(3)OS实现了对计算机资源的抽象3.为什么说OS实现了对计算机资源的抽象?答:OS首先在裸机上覆盖一层I/O设备管理软件,实现了对计算机硬件操作的第一层次抽象;在第一层软件上再覆盖文件管理软件,实现了对硬件资源操作的第二层次抽象。
OS 通过在计算机硬件上安装多层系统软件,增强了系统功能,隐藏了对硬件操作的细节,由它们共同实现了对计算机资源的抽象。
4.试说明推动多道批处理系统形成和发展的主要动力是什么?答:主要动力来源于四个方面的社会需求与技术发展:(1)不断提高计算机资源的利用率;(2)方便用户;(3)器件的不断更新换代;(4)计算机体系结构的不断发展。
5.何谓脱机I/O和联机I/O?答:脱机I/O 是指事先将装有用户程序和数据的纸带或卡片装入纸带输入机或卡片机,在外围机的控制下,把纸带或卡片上的数据或程序输入到磁带上。
该方式下的输入输出由外围机控制完成,是在脱离主机的情况下进行的。
而联机I/O方式是指程序和数据的输入输出都是在主机的直接控制下进行的。
6.试说明推动分时系统形成和发展的主要动力是什么?答:推动分时系统形成和发展的主要动力是更好地满足用户的需要。
主要表现在:CPU 的分时使用缩短了作业的平均周转时间;人机交互能力使用户能直接控制自己的作业;主机的共享使多用户能同时使用同一台计算机,独立地处理自己的作业。
7.实现分时系统的关键问题是什么?应如何解决?答:关键问题是当用户在自己的终端上键入命令时,系统应能及时接收并及时处理该命令,在用户能接受的时延内将结果返回给用户。
解决方法:针对及时接收问题,可以在系统中设置多路卡,使主机能同时接收用户从各个终端上输入的数据;为每个终端配置缓冲区,暂存用户键入的命令或数据。
现代操作系统第三版中文答案
现代操作系统第三版中文答案【篇一:操作系统课后答案】>思考与练习题1. 2. 3. 4. 5. 6. 7. 8. 9.什么是操作系统?它的主要功能是什么?什么是多道程序设计技术?多道程序设计技术的主要特点是什么?批处理系统是怎样的一种操作系统?它的特点是什么?什么是分时系统?什么是实时系统?试从交互性,及时性,独立性,多路性,可靠性等几个方面比较分时系统和实施系统。
实时系统分为哪俩种类型?操作系统主要特征是什么?操作系统也用户的接口有几种?它们各自用在什么场合?“操作系统是控制硬件的软件”这一说法确切吗?为什么?设内存中有三道程序,a,b,c,它们按a~b~c的先后顺序执行,它们进行“计算”和“i/o操作”的时间如表1-2所示,假设三道程序使用相同的i/o设备。
(1) 试画出单道运行时三道程序的时间关系图,并计算完成三道程序要花多少时间。
(2) 试画出多道运行时三道程序的时间关系图,并计算完成三道程序要花多少时间。
10.将下列左右两列词连接起来形成意义最恰当的5对。
dos 网络操作系统 os/2自由软件 unix多任务 linux单任务11.选择一个现代操作系统,查找和阅读相关的技术资料,写一篇关于操作系统如何进行内存管理、存储管理、设备管理和文件管理的文章。
答案1.答:操作系统是控制和管理计算机的软、硬件资源,合理地组织计算机的工作流程,以方便用户使用的程序集合。
2.答:把多个独立的程序同时放入内存,使她们共享系统中的资源。
1)多道,即计算机内存中同时放多道相互独立的程序。
2)宏观上并行,是指共识进入系统的多道程序都处于运行过程。
3)微观上串行,是指在单道处理机环境下,内存中的多道程序轮流地占有cpu,交替执行。
3.答:批处理操作系统是一种基本的操作系统类型。
在该系统中用户的作业被成批地输入到计算机中,然后在操作系统的控制下,用户的作业自动的执行。
特点是:资源利用率高。
系统吞吐量大。
现代操作系统(第三版)答案

MODERNOPERATINGSYSTEMSTHIRD EDITION PROBLEM SOLUTIONSANDREW S.TANENBAUMVrije UniversiteitAmsterdam,The NetherlandsPRENTICE HALLUPPER SADDLE RIVER,NJ07458Copyright Pearson Education,Inc.2008SOLUTIONS TO CHAPTER1PROBLEMS1.Multiprogramming is the rapid switching of the CPU between multiple proc-esses in memory.It is commonly used to keep the CPU busy while one or more processes are doing I/O.2.Input spooling is the technique of reading in jobs,for example,from cards,onto the disk,so that when the currently executing processes arefinished, there will be work waiting for the CPU.Output spooling consists offirst copying printablefiles to disk before printing them,rather than printing di-rectly as the output is generated.Input spooling on a personal computer is not very likely,but output spooling is.3.The prime reason for multiprogramming is to give the CPU something to dowhile waiting for I/O to complete.If there is no DMA,the CPU is fully occu-pied doing I/O,so there is nothing to be gained(at least in terms of CPU utili-zation)by multiprogramming.No matter how much I/O a program does,the CPU will be100%busy.This of course assumes the major delay is the wait while data are copied.A CPU could do other work if the I/O were slow for other reasons(arriving on a serial line,for instance).4.It is still alive.For example,Intel makes Pentium I,II,and III,and4CPUswith a variety of different properties including speed and power consumption.All of these machines are architecturally compatible.They differ only in price and performance,which is the essence of the family idea.5.A25×80character monochrome text screen requires a2000-byte buffer.The1024×768pixel24-bit color bitmap requires2,359,296bytes.In1980these two options would have cost$10and$11,520,respectively.For current prices,check on how much RAM currently costs,probably less than$1/MB.6.Consider fairness and real time.Fairness requires that each process be allo-cated its resources in a fair way,with no process getting more than its fair share.On the other hand,real time requires that resources be allocated based on the times when different processes must complete their execution.A real-time process may get a disproportionate share of the resources.7.Choices(a),(c),and(d)should be restricted to kernel mode.8.It may take20,25or30msec to complete the execution of these programsdepending on how the operating system schedules them.If P0and P1are scheduled on the same CPU and P2is scheduled on the other CPU,it will take20mses.If P0and P2are scheduled on the same CPU and P1is scheduled on the other CPU,it will take25msec.If P1and P2are scheduled on the same CPU and P0is scheduled on the other CPU,it will take30msec.If all three are on the same CPU,it will take35msec.2PROBLEM SOLUTIONS FOR CHAPTER19.Every nanosecond one instruction emerges from the pipeline.This means themachine is executing1billion instructions per second.It does not matter at all how many stages the pipeline has.A10-stage pipeline with1nsec per stage would also execute1billion instructions per second.All that matters is how often afinished instruction pops out the end of the pipeline.10.Average access time=0.95×2nsec(word is cache)+0.05×0.99×10nsec(word is in RAM,but not in cache)+0.05×0.01×10,000,000nsec(word on disk only)=5002.395nsec=5.002395μsec11.The manuscript contains80×50×700=2.8million characters.This is,ofcourse,impossible tofit into the registers of any currently available CPU and is too big for a1-MB cache,but if such hardware were available,the manuscript could be scanned in2.8msec from the registers or5.8msec from the cache.There are approximately27001024-byte blocks of data,so scan-ning from the disk would require about27seconds,and from tape2minutes7 seconds.Of course,these times are just to read the data.Processing and rewriting the data would increase the time.12.Maybe.If the caller gets control back and immediately overwrites the data,when the writefinally occurs,the wrong data will be written.However,if the driverfirst copies the data to a private buffer before returning,then the caller can be allowed to continue immediately.Another possibility is to allow the caller to continue and give it a signal when the buffer may be reused,but this is tricky and error prone.13.A trap instruction switches the execution mode of a CPU from the user modeto the kernel mode.This instruction allows a user program to invoke func-tions in the operating system kernel.14.A trap is caused by the program and is synchronous with it.If the program isrun again and again,the trap will always occur at exactly the same position in the instruction stream.An interrupt is caused by an external event and its timing is not reproducible.15.The process table is needed to store the state of a process that is currentlysuspended,either ready or blocked.It is not needed in a single process sys-tem because the single process is never suspended.16.Mounting afile system makes anyfiles already in the mount point directoryinaccessible,so mount points are normally empty.However,a system admin-istrator might want to copy some of the most importantfiles normally located in the mounted directory to the mount point so they could be found in their normal path in an emergency when the mounted device was being repaired.PROBLEM SOLUTIONS FOR CHAPTER13 17.A system call allows a user process to access and execute operating systemfunctions inside the er programs use system calls to invoke operat-ing system services.18.Fork can fail if there are no free slots left in the process table(and possibly ifthere is no memory or swap space left).Exec can fail if thefile name given does not exist or is not a valid executablefile.Unlink can fail if thefile to be unlinked does not exist or the calling process does not have the authority to unlink it.19.If the call fails,for example because fd is incorrect,it can return−1.It canalso fail because the disk is full and it is not possible to write the number of bytes requested.On a correct termination,it always returns nbytes.20.It contains the bytes:1,5,9,2.21.Time to retrieve thefile=1*50ms(Time to move the arm over track#50)+5ms(Time for thefirst sector to rotate under the head)+10/100*1000ms(Read10MB)=155ms22.Block specialfiles consist of numbered blocks,each of which can be read orwritten independently of all the other ones.It is possible to seek to any block and start reading or writing.This is not possible with character specialfiles.23.System calls do not really have names,other than in a documentation sense.When the library procedure read traps to the kernel,it puts the number of the system call in a register or on the stack.This number is used to index into a table.There is really no name used anywhere.On the other hand,the name of the library procedure is very important,since that is what appears in the program.24.Yes it can,especially if the kernel is a message-passing system.25.As far as program logic is concerned it does not matter whether a call to a li-brary procedure results in a system call.But if performance is an issue,if a task can be accomplished without a system call the program will run faster.Every system call involves overhead time in switching from the user context to the kernel context.Furthermore,on a multiuser system the operating sys-tem may schedule another process to run when a system call completes, further slowing the progress in real time of a calling process.26.Several UNIX calls have no counterpart in the Win32API:Link:a Win32program cannot refer to afile by an alternative name or see it in more than one directory.Also,attempting to create a link is a convenient way to test for and create a lock on afile.4PROBLEM SOLUTIONS FOR CHAPTER1Mount and umount:a Windows program cannot make assumptions about standard path names because on systems with multiple disk drives the drive name part of the path may be different.Chmod:Windows uses access control listsKill:Windows programmers cannot kill a misbehaving program that is not cooperating.27.Every system architecture has its own set of instructions that it can execute.Thus a Pentium cannot execute SPARC programs and a SPARC cannot exe-cute Pentium programs.Also,different architectures differ in bus architecture used(such as VME,ISA,PCI,MCA,SBus,...)as well as the word size of the CPU(usually32or64bit).Because of these differences in hardware,it is not feasible to build an operating system that is completely portable.A highly portable operating system will consist of two high-level layers---a machine-dependent layer and a machine independent layer.The machine-dependent layer addresses the specifics of the hardware,and must be implemented sepa-rately for every architecture.This layer provides a uniform interface on which the machine-independent layer is built.The machine-independent layer has to be implemented only once.To be highly portable,the size of the machine-dependent layer must be kept as small as possible.28.Separation of policy and mechanism allows OS designers to implement asmall number of basic primitives in the kernel.These primitives are sim-plified,because they are not dependent of any specific policy.They can then be used to implement more complex mechanisms and policies at the user level.29.The conversions are straightforward:(a)A micro year is10−6×365×24×3600=31.536sec.(b)1000meters or1km.(c)There are240bytes,which is1,099,511,627,776bytes.(d)It is6×1024kg.SOLUTIONS TO CHAPTER2PROBLEMS1.The transition from blocked to running is conceivable.Suppose that a processis blocked on I/O and the I/Ofinishes.If the CPU is otherwise idle,the proc-ess could go directly from blocked to running.The other missing transition, from ready to blocked,is impossible.A ready process cannot do I/O or any-thing else that might block it.Only a running process can block.PROBLEM SOLUTIONS FOR CHAPTER25 2.You could have a register containing a pointer to the current process tableentry.When I/O completed,the CPU would store the current machine state in the current process table entry.Then it would go to the interrupt vector for the interrupting device and fetch a pointer to another process table entry(the ser-vice procedure).This process would then be started up.3.Generally,high-level languages do not allow the kind of access to CPU hard-ware that is required.For instance,an interrupt handler may be required to enable and disable the interrupt servicing a particular device,or to manipulate data within a process’stack area.Also,interrupt service routines must exe-cute as rapidly as possible.4.There are several reasons for using a separate stack for the kernel.Two ofthem are as follows.First,you do not want the operating system to crash be-cause a poorly written user program does not allow for enough stack space.Second,if the kernel leaves stack data in a user program’s memory space upon return from a system call,a malicious user might be able to use this data tofind out information about other processes.5.If each job has50%I/O wait,then it will take20minutes to complete in theabsence of competition.If run sequentially,the second one willfinish40 minutes after thefirst one starts.With two jobs,the approximate CPU utiliza-tion is1−0.52.Thus each one gets0.375CPU minute per minute of real time.To accumulate10minutes of CPU time,a job must run for10/0.375 minutes,or about26.67minutes.Thus running sequentially the jobsfinish after40minutes,but running in parallel theyfinish after26.67minutes.6.It would be difficult,if not impossible,to keep thefile system consistent.Sup-pose that a client process sends a request to server process1to update afile.This process updates the cache entry in its memory.Shortly thereafter,anoth-er client process sends a request to server2to read thatfile.Unfortunately,if thefile is also cached there,server2,in its innocence,will return obsolete data.If thefirst process writes thefile through to the disk after caching it, and server2checks the disk on every read to see if its cached copy is up-to-date,the system can be made to work,but it is precisely all these disk ac-cesses that the caching system is trying to avoid.7.No.If a single-threaded process is blocked on the keyboard,it cannot fork.8.A worker thread will block when it has to read a Web page from the disk.Ifuser-level threads are being used,this action will block the entire process, destroying the value of multithreading.Thus it is essential that kernel threads are used to permit some threads to block without affecting the others.9.Yes.If the server is entirely CPU bound,there is no need to have multiplethreads.It just adds unnecessary complexity.As an example,consider a tele-phone directory assistance number(like555-1212)for an area with1million6PROBLEM SOLUTIONS FOR CHAPTER2people.If each(name,telephone number)record is,say,64characters,the entire database takes64megabytes,and can easily be kept in the server’s memory to provide fast lookup.10.When a thread is stopped,it has values in the registers.They must be saved,just as when the process is stopped the registers must be saved.Multipro-gramming threads is no different than multiprogramming processes,so each thread needs its own register save area.11.Threads in a process cooperate.They are not hostile to one another.If yield-ing is needed for the good of the application,then a thread will yield.After all,it is usually the same programmer who writes the code for all of them. er-level threads cannot be preempted by the clock unless the whole proc-ess’quantum has been used up.Kernel-level threads can be preempted indivi-dually.In the latter case,if a thread runs too long,the clock will interrupt the current process and thus the current thread.The kernel is free to pick a dif-ferent thread from the same process to run next if it so desires.13.In the single-threaded case,the cache hits take15msec and cache misses take90msec.The weighted average is2/3×15+1/3×90.Thus the mean re-quest takes40msec and the server can do25per second.For a multithreaded server,all the waiting for the disk is overlapped,so every request takes15 msec,and the server can handle662/3requests per second.14.The biggest advantage is the efficiency.No traps to the kernel are needed toswitch threads.The biggest disadvantage is that if one thread blocks,the en-tire process blocks.15.Yes,it can be done.After each call to pthread create,the main programcould do a pthread join to wait until the thread just created has exited before creating the next thread.16.The pointers are really necessary because the size of the global variable isunknown.It could be anything from a character to an array offloating-point numbers.If the value were stored,one would have to give the size to create global,which is all right,but what type should the second parameter of set global be,and what type should the value of read global be?17.It could happen that the runtime system is precisely at the point of blocking orunblocking a thread,and is busy manipulating the scheduling queues.This would be a very inopportune moment for the clock interrupt handler to begin inspecting those queues to see if it was time to do thread switching,since they might be in an inconsistent state.One solution is to set aflag when the run-time system is entered.The clock handler would see this and set its ownflag, then return.When the runtime systemfinished,it would check the clockflag, see that a clock interrupt occurred,and now run the clock handler.PROBLEM SOLUTIONS FOR CHAPTER27 18.Yes it is possible,but inefficient.A thread wanting to do a system callfirstsets an alarm timer,then does the call.If the call blocks,the timer returns control to the threads package.Of course,most of the time the call will not block,and the timer has to be cleared.Thus each system call that might block has to be executed as three system calls.If timers go off prematurely,all kinds of problems can develop.This is not an attractive way to build a threads package.19.The priority inversion problem occurs when a low-priority process is in itscritical region and suddenly a high-priority process becomes ready and is scheduled.If it uses busy waiting,it will run forever.With user-level threads,it cannot happen that a low-priority thread is suddenly preempted to allow a high-priority thread run.There is no preemption.With kernel-level threads this problem can arise.20.With round-robin scheduling it works.Sooner or later L will run,and eventu-ally it will leave its critical region.The point is,with priority scheduling,L never gets to run at all;with round robin,it gets a normal time slice periodi-cally,so it has the chance to leave its critical region.21.Each thread calls procedures on its own,so it must have its own stack for thelocal variables,return addresses,and so on.This is equally true for user-level threads as for kernel-level threads.22.Yes.The simulated computer could be multiprogrammed.For example,while process A is running,it reads out some shared variable.Then a simula-ted clock tick happens and process B runs.It also reads out the same vari-able.Then it adds1to the variable.When process A runs,if it also adds one to the variable,we have a race condition.23.Yes,it still works,but it still is busy waiting,of course.24.It certainly works with preemptive scheduling.In fact,it was designed forthat case.When scheduling is nonpreemptive,it might fail.Consider the case in which turn is initially0but process1runsfirst.It will just loop forever and never release the CPU.25.To do a semaphore operation,the operating systemfirst disables interrupts.Then it reads the value of the semaphore.If it is doing a down and the sema-phore is equal to zero,it puts the calling process on a list of blocked processes associated with the semaphore.If it is doing an up,it must check to see if any processes are blocked on the semaphore.If one or more processes are block-ed,one of them is removed from the list of blocked processes and made run-nable.When all these operations have been completed,interrupts can be enabled again.8PROBLEM SOLUTIONS FOR CHAPTER226.Associated with each counting semaphore are two binary semaphores,M,used for mutual exclusion,and B,used for blocking.Also associated with each counting semaphore is a counter that holds the number of up s minus the number of down s,and a list of processes blocked on that semaphore.To im-plement down,a processfirst gains exclusive access to the semaphores, counter,and list by doing a down on M.It then decrements the counter.If it is zero or more,it just does an up on M and exits.If M is negative,the proc-ess is put on the list of blocked processes.Then an up is done on M and a down is done on B to block the process.To implement up,first M is down ed to get mutual exclusion,and then the counter is incremented.If it is more than zero,no one was blocked,so all that needs to be done is to up M.If, however,the counter is now negative or zero,some process must be removed from the list.Finally,an up is done on B and M in that order.27.If the program operates in phases and neither process may enter the nextphase until both arefinished with the current phase,it makes perfect sense to use a barrier.28.With kernel threads,a thread can block on a semaphore and the kernel canrun some other thread in the same process.Consequently,there is no problem using semaphores.With user-level threads,when one thread blocks on a semaphore,the kernel thinks the entire process is blocked and does not run it ever again.Consequently,the process fails.29.It is very expensive to implement.Each time any variable that appears in apredicate on which some process is waiting changes,the run-time system must re-evaluate the predicate to see if the process can be unblocked.With the Hoare and Brinch Hansen monitors,processes can only be awakened on a signal primitive.30.The employees communicate by passing messages:orders,food,and bags inthis case.In UNIX terms,the four processes are connected by pipes.31.It does not lead to race conditions(nothing is ever lost),but it is effectivelybusy waiting.32.It will take nT sec.33.In simple cases it may be possible to determine whether I/O will be limitingby looking at source code.For instance a program that reads all its inputfiles into buffers at the start will probably not be I/O bound,but a problem that reads and writes incrementally to a number of differentfiles(such as a compi-ler)is likely to be I/O bound.If the operating system provides a facility such as the UNIX ps command that can tell you the amount of CPU time used by a program,you can compare this with the total time to complete execution of the program.This is,of course,most meaningful on a system where you are the only user.34.For multiple processes in a pipeline,the common parent could pass to the op-erating system information about the flow of data.With this information the OS could,for instance,determine which process could supply output to a process blocking on a call for input.35.The CPU efficiency is the useful CPU time divided by the total CPU time.When Q ≥T ,the basic cycle is for the process to run for T and undergo a process switch for S .Thus (a)and (b)have an efficiency of T /(S +T ).When the quantum is shorter than T ,each run of T will require T /Q process switches,wasting a time ST /Q .The efficiency here is thenT +ST /QT which reduces to Q /(Q +S ),which is the answer to (c).For (d),we just sub-stitute Q for S and find that the efficiency is 50%.Finally,for (e),as Q →0the efficiency goes to 0.36.Shortest job first is the way to minimize average response time.0<X ≤3:X ,3,5,6,9.3<X ≤5:3,X ,5,6,9.5<X ≤6:3,5,X ,6,9.6<X ≤9:3,5,6,X ,9.X >9:3,5,6,9,X.37.For round robin,during the first 10minutes each job gets 1/5of the CPU.Atthe end of 10minutes,C finishes.During the next 8minutes,each job gets 1/4of the CPU,after which time D finishes.Then each of the three remaining jobs gets 1/3of the CPU for 6minutes,until B finishes,and so on.The fin-ishing times for the five jobs are 10,18,24,28,and 30,for an average of 22minutes.For priority scheduling,B is run first.After 6minutes it is finished.The other jobs finish at 14,24,26,and 30,for an average of 18.8minutes.If the jobs run in the order A through E ,they finish at 10,16,18,22,and 30,for an average of 19.2minutes.Finally,shortest job first yields finishing times of 2,6,12,20,and 30,for an average of 14minutes.38.The first time it gets 1quantum.On succeeding runs it gets 2,4,8,and 15,soit must be swapped in 5times.39.A check could be made to see if the program was expecting input and didanything with it.A program that was not expecting input and did not process it would not get any special priority boost.40.The sequence of predictions is 40,30,35,and now 25.41.The fraction of the CPU used is35/50+20/100+10/200+x/250.To beschedulable,this must be less than1.Thus x must be less than12.5msec. 42.Two-level scheduling is needed when memory is too small to hold all theready processes.Some set of them is put into memory,and a choice is made from that set.From time to time,the set of in-core processes is adjusted.This algorithm is easy to implement and reasonably efficient,certainly a lot better than,say,round robin without regard to whether a process was in memory or not.43.Each voice call runs200times/second and uses up1msec per burst,so eachvoice call needs200msec per second or400msec for the two of them.The video runs25times a second and uses up20msec each time,for a total of 500msec per second.Together they consume900msec per second,so there is time left over and the system is schedulable.44.The kernel could schedule processes by any means it wishes,but within eachprocess it runs threads strictly in priority order.By letting the user process set the priority of its own threads,the user controls the policy but the kernel handles the mechanism.45.The change would mean that after a philosopher stopped eating,neither of hisneighbors could be chosen next.In fact,they would never be chosen.Sup-pose that philosopher2finished eating.He would run test for philosophers1 and3,and neither would be started,even though both were hungry and both forks were available.Similarly,if philosopher4finished eating,philosopher3 would not be started.Nothing would start him.46.If a philosopher blocks,neighbors can later see that she is hungry by checkinghis state,in test,so he can be awakened when the forks are available.47.Variation1:readers have priority.No writer may start when a reader is ac-tive.When a new reader appears,it may start immediately unless a writer is currently active.When a writerfinishes,if readers are waiting,they are all started,regardless of the presence of waiting writers.Variation2:Writers have priority.No reader may start when a writer is waiting.When the last ac-tive processfinishes,a writer is started,if there is one;otherwise,all the readers(if any)are started.Variation3:symmetric version.When a reader is active,new readers may start immediately.When a writerfinishes,a new writer has priority,if one is waiting.In other words,once we have started reading,we keep reading until there are no readers left.Similarly,once we have started writing,all pending writers are allowed to run.48.A possible shell script might beif[!–f numbers];then echo0>numbers;ficount=0while(test$count!=200)docount=‘expr$count+1‘n=‘tail–1numbers‘expr$n+1>>numbersdoneRun the script twice simultaneously,by starting it once in the background (using&)and again in the foreground.Then examine thefile numbers.It will probably start out looking like an orderly list of numbers,but at some point it will lose its orderliness,due to the race condition created by running two cop-ies of the script.The race can be avoided by having each copy of the script test for and set a lock on thefile before entering the critical area,and unlock-ing it upon leaving the critical area.This can be done like this:if ln numbers numbers.lockthenn=‘tail–1numbers‘expr$n+1>>numbersrm numbers.lockfiThis version will just skip a turn when thefile is inaccessible,variant solu-tions could put the process to sleep,do busy waiting,or count only loops in which the operation is successful.SOLUTIONS TO CHAPTER3PROBLEMS1.It is an accident.The base register is16,384because the program happened tobe loaded at address16,384.It could have been loaded anywhere.The limit register is16,384because the program contains16,384bytes.It could have been any length.That the load address happens to exactly match the program length is pure coincidence.2.Almost the entire memory has to be copied,which requires each word to beread and then rewritten at a different location.Reading4bytes takes10nsec, so reading1byte takes2.5nsec and writing it takes another2.5nsec,for a total of5nsec per byte compacted.This is a rate of200,000,000bytes/sec.To copy128MB(227bytes,which is about1.34×108bytes),the computer needs227/200,000,000sec,which is about671msec.This number is slightly pessimistic because if the initial hole at the bottom of memory is k bytes, those k bytes do not need to be copied.However,if there are many holes andmany data segments,the holes will be small,so k will be small and the error in the calculation will also be small.3.The bitmap needs1bit per allocation unit.With227/n allocation units,this is224/n bytes.The linked list has227/216or211nodes,each of8bytes,for a total of214bytes.For small n,the linked list is better.For large n,the bitmap is better.The crossover point can be calculated by equating these two formu-las and solving for n.The result is1KB.For n smaller than1KB,a linked list is better.For n larger than1KB,a bitmap is better.Of course,the assumption of segments and holes alternating every64KB is very unrealistic.Also,we need n<=64KB if the segments and holes are64KB.4.Firstfit takes20KB,10KB,18KB.Bestfit takes12KB,10KB,and9KB.Worstfit takes20KB,18KB,and15KB.Nextfit takes20KB,18KB,and9 KB.5.For a4-KB page size the(page,offset)pairs are(4,3616),(8,0),and(14,2656).For an8-KB page size they are(2,3616),(4,0),and(7,2656).6.They built an MMU and inserted it between the8086and the bus.Thus all8086physical addresses went into the MMU as virtual addresses.The MMU then mapped them onto physical addresses,which went to the bus.7.(a)M has to be at least4,096to ensure a TLB miss for every access to an ele-ment of X.Since N only affects how many times X is accessed,any value of N will do.(b)M should still be atleast4,096to ensure a TLB miss for every access to anelement of X.But now N should be greater than64K to thrash the TLB, that is,X should exceed256KB.8.The total virtual address space for all the processes combined is nv,so thismuch storage is needed for pages.However,an amount r can be in RAM,so the amount of disk storage required is only nv−r.This amount is far more than is ever needed in practice because rarely will there be n processes ac-tually running and even more rarely will all of them need the maximum al-lowed virtual memory.9.The page table contains232/213entries,which is524,288.Loading the pagetable takes52msec.If a process gets100msec,this consists of52msec for loading the page table and48msec for running.Thus52%of the time is spent loading page tables.10.(a)We need one entry for each page,or224=16×1024×1024entries,sincethere are36=48−12bits in the page numberfield.。
操作系统(第三)孙钟秀主编课后习题参考答案汇总

操作系统答案目录习题一1习题二3习题三7习题四16习题五23习题六27习题一一.思考题3. 什么是操作系统?计算机系统中配置操作系统的主要目标是什么?答(p1>:操作系统是管理系统资源、控制程序执行、改善人机界面、提供各种服务,合理组织计算机工作流程和为用户有效使用计算机提供良好运行环境的一种系统软件。
b5E2RGbCAP配置操作系统的主要目标可归结为:(1> 方便用户使用(2> 扩大机器功能(3> 管理系统资源(4> 提高系统效率(5> 构筑开放环境。
p1EanqFDPw5. 操作系统要为用户提供哪些基本和共性的服务?答(p25>:操作系统提供给程序和用户的共性服务大致有:(1> 创建程序(2> 执行程序(3> 数据I/O(4> 信息存取(5> 通信服务(6> 错误检测和处理DXDiTa9E3d9.试叙述系统调用的实现原理。
答<p28)系统调用的实现有以下几点:⑴编写系统调用处理程序⑵设计一张系统调用入口地址表,每个入口地址都指向一个系统调用的处理程序,有的系统还包含系统调用自带参数的个数⑶陷入处理机制,需开辟现场保护,以保存发生系统调用时的处理器现场。
RTCrpUDGiT10.试叙述系统调用与过程调用的主要区别。
答<p29)⑴调用形式不同⑵被调用代码的位置不同⑶提供方式不同⑷调用的实现不同二.应用题2. 一个计算机系统,有一台输入机和一台打印机,现有两道程序投入运行,且程序A先开始做,程序B后开始运行。
程序A的运行轨迹为:计算50ms、打印100ms、再计算50ms、打印100ms,结束。
程序B的运行轨迹为:计算50ms、输入80ms、再计算100ms,结束。
试说明(1>两道程序运行时,CPU有无空闲等待?若有,在哪段时间内等待?为什么会等待?(2>程序A、B有无等待CPU的情况?若有,指出发生等待的时刻。
操作系第3版答案

部分习题参考答案针对书中习题的重点和难点部分给出参考答案,而其余习题可在书中相应章节处得到答案。
3•操作系统是裸机之上的第一层软件,它只在核心态模式下运行,受硬件保护,与硬件关系尤为密切。
操作系统是整个计算机系统的控制管理中心,其他所有软件都建立在操作系统之上。
操作系统对它们既具有支配权力,又为其运行建造必备环境。
4•脱机I/O是指输入/输出工作不受主机直接控制,而由卫星机专门负责完成I/O,主机专门完成快速计算任务,从而二者可以并行操作。
联机I/O是指作业的输入、调入内存及结果输出都在CPU直接控制下进行。
&硬件一一是指计算机物理装置本身,它是计算机系统的物理基础。
如CPU内存、设备等。
软件一一是相对硬件而言的,它是与数据处理系统的操作有关的计算机程序、过程、规则及相关文档资料的总称。
简单地说,软件是计算机执行的程序。
多道程序设计一一在这种设计技术下,内存中能同时存放多道程序,在管理程序的控制下交替地执行。
这些作业共享CPU和系统中的其他资源。
并发一一是指两个或多个活动在同一给定的时间间隔中进行。
它是宏观上的概念。
吞吐量一一在一段给定的时间内,计算机所能完成的总工作量。
分时一一就是对时间的共享。
在分时系统中,分时主要是指若干并发程序对CPU寸间的共享。
实时一一表示“及时”或“即时”。
系统调用一一是用户在程序中能以“函数调用”形式调用的、由操作系统提供的子功能的集合。
每一个子功能称做一条系统调用命令。
它是操作系统对外的接口,是用户级程序取得操作系统服务的唯一途径。
10. 通常,大家会熟悉以下操作系统:Windows 2000, Windows XP, UNIX或Linux。
在上机工作过程中,操作系统为用户提供的服务包括:命令和数据输入/输出的管理,内存的分配,用户文件的管理,CPU的分配,设备管理等。
12. 当执行操作系统程序时,处理机处于核心态。
它有较高的特权,可以执行所有的指令,包括一般用户程序中不能使用的特权指令,从而能对所有寄存器和内存进行访问、启动I/O操作等。
现代操作系统(中文第三版)习题答案
14、陷阱和中断的主要差别是什么? 答:陷阱由程序造成的,并且与它同步。如果程序一而再地被运行,陷阱将总在 指令流中相同位置的精确发生。而中断则是由外部事件和其时钟造成的,不具有 重复性。
5、缓慢采用 GUI 的一个原因是支持它的硬件的成本(高昂)。为了支持 25 行 80 列字符的单色文本屏幕应该需要多少视颊 RAM? 对于 1024x768 像素 24 位色彩 位图需要多少视频 RAM? 在 1980 年($5/KB)这些 RAM 的成本是多少?现在它的 成本是多少? 答:25*80 字符的单色文本屏幕需要 2000 字节的缓冲器。1024*768 像素 24 位颜 色的位图需要 2359296 字节。1980 年这两种选择将分别地耗费$10 和$11520。而 对于当前的价格,将少于$1/MB。
12、在用户程序进行一个系统调用,以读写磁盘文件时,该程序提供指示说明了 所需要的文件,一个指向数据缓冲区的指针以及计数。然后,控制权转给操作系 统,它调用相关的驱动程序。假设驱动程序启动磁盘并且直到中断发生才终止。 在从磁盘读的情况下,很明显,调用者会被阻塞(因为文件中没有数据)。在向 磁盘写时会发生什么情况?需要把调用者阻塞一直等到磁盘传送完成为止吗? 答:也许。如果调用者取回控制,并且在最终发生写操作时立即重写数据,将会 写入错误的数据。然而,如果驱动程序在返回之前首先复制将数据复制到一个专 用的缓冲器,那么调用者可以立即继续执行。另一个可能性是允许调用者继续, 并且在缓冲器可以再用时给它一个信号,但是这需要很高的技巧,而且容易出错。
第1页
标准答案)
现代操作系统课后习题答案
第二章进程管理令狐采学第一部分教材习题(P81)3、为什么程序并发执行会产生间断性特征?(P36)4、程序并发执行,为何会失去封闭性和可再现性?(P37)【解】程序在并发执行时,是多个程序共享系统中的各种资源,因而这些资源的状态将由多个程序来改变,致使程序的运行已失去了封闭性。
同时由于失去了封闭性,也将导致其再失去可再现性。
程序在并发执行时,由于失去了封闭性,程序经过多次执行后,其计算机结果已与并发程序的执行速度有关,从而使程序的执行失去了可再现性。
5、在操作系统中为什么要引入进程概念?(P37)它会产生什么样的影响?【解】在操作系统中引入进程的概念,是为了实现多个程序的并发执行。
传统的程序不能与其他程序并发执行,只有在为之创建进程后,才能与其他程序(进程)并发执行。
这是因为并发执行的程序(即进程)是“停停走走”地执行,只有在为它创建进程后,在它停下时,方能将其现场信息保存在它的PCB中,待下次被调度执行是,再从PCB中恢复CPU现场并继续执行,而传统的程序却无法满足上述要求。
建立进程所带来的好处是使多个程序能并发执行,这极大地提高了资源利用率和系统吞吐量。
但管理进程也需付出一定的代价,包括进程控制块及协调各运行机构所占用的内存空间开销,以及为进行进程间的切换、同步及通信等所付出的时间开销。
6、试从动态性、并发性和独立性上比较进程和程序?(P37)【解】(1)动态性:进程既然是进程实体的执行过程,因此,动态性是进程最基本的特性。
动态性还表现为:“它由创建而产生,由调度而执行,因得不到资源而暂停执行,以及由撤消而消亡”。
可见,进程有一定的生命期。
而程序只是一组有序指令的集合,并存放在某种介质上,本身并无运动的含义,因此,程序是个静态实体。
(2)并发性:所谓进程的并发,指的是多个进程实体,同存于内存中,能在一段时间内同时运行。
并发性是进程的重要特征,同时也成为OS的重要特征。
引入进程的目的也正是为了使其程序能和其它进程的程序并发执行,而程序是无法并发执行的。
现代操作系统第三版课后答案1~6章
SOLUTIONS TO CHAPTER 1 PROBLEMS1.An operating system must provide the users with an extended (i.e., virtual) machine, and it must manage the I/O devices and other system resources.2.Multiprogramming is the rapid switching of the CPU between multiple processes in memory. It is commonly used to keep the CPU busy while one or more processes are doing I/O.3. Input spooling is the technique of reading in jobs, for example, from cards, onto the disk, so that when the currently executing processes are finished,there will be work waiting for the CPU. Output spooling consists of first copying printable files to disk before printing them, rather than printing directly as the output is generated. Input spooling on a personal computer is not very likely, but output spooling is.4.The prime reason for multiprogramming is to give the CPU something to do while waiting for I/O to complete. If there is no DMA, the CPU is fully occupied doing I/O, so there is nothing to be gained (at least in terms of CPU utilization) by multiprogramming. No matter how much I/O a program does, the CPU will be 100 percent busy. This of course assumes the major delay is the wait while data are copied. A CPU could do other work if the I/O were slow for other reasons (arriving on a serial line, for instance).5.Second generation computers did not have the necessary hardware to protect the operating system from malicious user programs.6.It is still alive. For example, Intel makes Pentium I, II, and III, and 4 CPUs with a variety of different properties including speed and power consumption. All of these machines are architecturally compatible. They differ only in price and performance, which is the essence of the family idea.7. A 25 ×80 character monochrome text screen requires a 2000-byte buffer. The 1024 ×768 pixel24-bit color bitmap requires 2,359,296 bytes. In 1980 these two options would have cost $10 and $11,520, respectively. For current prices, check on how much RAM currently costs, probably less than $1/MB.8.Choices (a), (c), and (d) should be restricted to kernel mode.9.Personal computer systems are always interactive, often with only a single user. Mainframe systems nearly always emphasize batch or timesharing with many users. Protection is much more of an issue on mainframe systems, as is efficient use of all resources.10.Every nanosecond one instruction emerges from the pipeline. This means the machine is executing 1 billion instructions per second. It does not matter at all how many stages the pipeline has. A 10-stage pipeline with 1 nsec per stage would also execute 1 billion instructions per second. All that matters is how often a finished instructions pops out the end of the pipeline.11.The manuscript contains 80 ×50 ×700 = 2.8 million characters. This is, of course, impossible to fit into the registers of any currently available CPU and is too big for a 1-MB cache, but if such hardware were available, the manuscript could be scanned in 2.8 msec from the registers or 5.8 msec from the cache. There are approximately 2700 1024-byte blocks of data, so scanning from the disk would require about 27 seconds, and from tape 2 minutes 7seconds. Of course, these times are just to read the data. Processing and rewriting the data would increase the time.12.Logically, it does not matter if the limit register uses a virtual address or a physical address. However, the performance of the former is better. If virtual addresses are used, the addition of the virtual address and the base register can start simultaneously with the comparison and then can run in parallel. If physical addresses are used, the comparison cannot start until the addition is complete, increasing the access time.13.Maybe. If the caller gets control back and immediately overwrites the data, when the write finally occurs, the wrong data will be written. However, if the driver first copies the data to a private buffer before returning, then the caller can be allowed to continue immediately. Another possibility is to allow the caller to continue and give it a signal when the buffer may be reused, but this is tricky and error prone.14. A trap is caused by the program and is synchronous with it. If the program is run again and again, thetrap will always occur at exactly the same position in the instruction stream. An interrupt is caused by an external event and its timing is not reproducible.15.Base = 40,000 and limit = 10,000. An answer of limit = 50,000 is incorrect for the way the system was described in this book. It could have been implemented that way, but doing so would have required waiting until the address+ base calculation was completed before starting the limit check, thus slowing down the computer.16.The process table is needed to store the state of a process that is currently suspended, either ready or blocked. It is not needed in a single process system because the single process is never suspended.17.Mounting a file system makes any files already in the mount point directory inaccessible, so mount points are normally empty. However, a system administrator might want to copy some of the most important files normally located in the mounted directory to the mount point so they could be found in their normal path in an emergency when the mounted device was being checked or repaired18.Fork can fail if there are no free slots left in the process table (and possibly if there is no memory or swap space left). Exec can fail if the file name give ndoes not exist or is not a valid executable file. Unlink can fail if the file to be unlinked does not exist or the calling process does not have the authority to unlink it.19.If the call fails, for example because fd is incorrect, it can return −1. It can also fail because the disk is full and it is not possible to write the number of bytes requested. On a correct termination, it always returns nbytes.20.It contains the bytes: 1, 5, 9, 2.21.Block special files consist of nu mbered blocks, each of which can be read or written independently of all the other ones. It is possible to seek to any block and start reading or writing. This is not possible with character special files.22.System calls do not really have names, other than in a documentation sense. When the library procedure read traps to the kernel, it puts the number of the system call in a register or on the stack. This number is used to index into a table. There is really no name used anywhere. On the other hand, the name of the library procedure is very important, since that is what appears in the program.23.Yes it can, especially if the kernel is a message-passing system.24.As far as program logic is concerned it does not matter whether a call to a library procedure results ina system call. But if performance is an issue, if a task can be accomplished without a system call the program will run faster. Every system call involves overhead time in switching from the user context to the kernel context. Furthermore, on a multiuser system the operating system may schedule another process to run when a system call completes,further slowing the progress in real time of a calling process.25.Several UNIX calls have no counterpart in the Win32 API:Link: a Win32 program can not refer to a file by an alternate name or see it in more than one directory. Also, attempting to create a link is a convenient way to test for and create a lock on a file.Mount and umount: a Windows program cannot make assumptions about standard path names because on systems with multiple disk drives the drive name part of the path may be different.Chmod: Windows programmers have to assume that every user can access every file. Kill: Windows programmers cannot kill a misbehaving program that is not cooperating.26.The conversions are straightforward:(a) A micro year is 10-6 ×365 ×24 ×3600 31.536 sec.(b) 1000 meters or 1 km.(c) There are 240bytes, which is 1,099,511,627,776 bytes.(d) It is 6 ×1024kg.SOLUTIONS TO CHAPTER 2 PROBLEMS1.The transition from blocked to running is conceivable. Suppose that a process is blocked on I/O and the I/O finishes. If the CPU is otherwise idle, the process could go d irectly from blocked to running. The other missing transition, from ready to blocked, is impossible. A ready process cannot do I/O or anything else that might block it. Only a running process can block.2.You could have a register containing a pointer to the current process table entry. When I/O completed, the CPU would store the current machine state in the current process table entry. Then it would go to the interrupt vector forthe interrupting device and fetch a pointer to another process table entry (the service procedure). This process would then be started up.3.Generally, high-level languages do not allow one the kind of access to CPU hardware that is required. For instance, an interrupt handler may be required to enable and disable the interrupt servicing a particular device, or to manipulate data within a process’ stack area. Also, interrupt service routines must execute as rapidly as possible.4.There are several reasons for using a separate stack for the kernel. Two of them are as follows. First, you do not want the operating system to crash because a poorly written user program does not allow for enough stack space. Second, if the kernel leaves stack data in a user program’s memory space upon return from a system call, a malicious user might be able to use this data to find out information about other processes.5.It would be difficult, if not impossible, to keep the file system consistent. Suppose that a client process sends a request to server process 1 to update a file. This process updates the cache entry in its memory. Shortly thereafter, another client process sends a request to server 2 to read that file. Unfortunately, if the file is also cached there, server 2, in its innocence, will return obsolete data. If thefirst process writes the file through to the disk after caching it, and server 2 checks the disk on every read to see if its cached copy is up-to-date, the system can be made to work, but it is precisely all these disk accesses that the caching system is trying to avoid6.When a thread is stopped, it has values in the registers. They must be saved, just as when the process is stopped the registers must be saved. Timesharing threads is no different than timesharing processes, so each thread needs itsown register save area.7.No. If a single-threaded process is blocked on the keyboard, it cannot fork.8. A worker thread will block when it has to read a Web page from the disk. If user-level threads are being used, this action will block the entire process, destroying the value of multithreading. Thus it is essential that kernel threads are used to permit some threads to block without affecting the others.9.Threads in a process cooperate. They are not hostile to one another. If yielding is needed for the good of the application, then a thread will yield. After all, it is usually the same programmer who writes the code for all of them.er-level threads cannot be preempted by the clock uless the whole process’ quantum has been used up. Kernel-level threads can be preempted individually. In the latter case, if a thread runs too long, the clock will interrupt the current process and thus the current thread. The kernel is free to pick a different thread from the same process to run next if it so desires.11.In the single-threaded case, the cache hits take 15 msec and cache misses take 90 msec. The weighted average is 2/3 15 1 /3 90. Thus the mean request takes 40 msec and the server can do 25 per second. For a multithreaded server, all the waiting for the disk is overlapped, so every request takes15 msec, and the server can handle 66 2/3 requests per second.12.Yes. If the server is entirely CPU bound, there is no need to have multiple threads. It just adds unnecessary complexity. As an example, consider a telephone directory assistance number (like 555-1212) for an area with 1 million people. If each (name, telephone number) record is, say, 64 characters, the entire database takes 64 megabytes, and can easily be kept in the server’s memory to provide fast lookup.13.The pointers are really necessary because the size of the global variable is unknown. It could be anything from a character to an array of floating-point numbers. If the value were stored, one would have to give the size to create 3 global, which is all right, but what type should the second parameter of set 3 global be, and what type should the value of read 3 global be?14.It could happen that the runtime system is precisely at the point of blocking or unblocking a thread, and is busy manipulating the scheduling queues. This would be a very inopportune moment for the clock interrupt handler to begin inspecting those queues to see if it was time to do thread switching, since they might be in an inconsistent state. One solution is to set a flag when the runtime system is entered. The clock handler would see this and set its own flag,then return. When the runtime system finished, it would check the clock flag, see that a clock interrupt occurred, and now run the clock handle15.Yes it is po ssible, but inefficient. A thread wanting to do a system call first sets an alarm timer, then does the call. If the call blocks, the timer returns control to the threads package. Of course, most of the time the call will not block, and the timer has to be cleared. Thus each system call that might block has to be executed as three system calls. If timers go off prematurely, all kinds of problems can develop. This is not an attractive way to build a threads package.16.The priority inversion problem occurs when a low-priority process is in its critical region and suddenly a high-priority process becomes ready and is scheduled. If it uses busy waiting, it will run forever. With user-level threads, it cannot happen that a low-priority thread is suddenly preempted to allow a high-priority thread run. There is no preemption. With kernel-level threads this problem can arise.17.Each thread calls procedures on its own, so it must have its own stack for the local variables, return addresses, and so on. This is equally true for user-level threads as for kernel-level threads.18. A race condition is a situation in which two (or more) processes are about to perform some action. Depending on the exact timing, one or the other goes first. If one of the processes goes first, everything works, but if another one goes first, a fatal error occurs.19.Yes. The simulated computer could be multiprogrammed. For example, while process A is running, it reads out some shared variable. Then a simulated clock tick happens and process B runs. It also reads out the same variable. Then it adds 1 to the variable. When process A runs, if it also adds one to the variable, we have a race condition20. Yes, it still works, but it still is busy waiting, of course.21. It certainly works with preemptive scheduling. In fact, it was designed for that case. When scheduling is nonpreemptive, it might fail. Consider the case in which turn is initially 0 but process 1 runs first. It will just loop forever and never release the CPU.22.Yes it can. The memory word is used as a flag, with 0 meaning that no one is using the critical variables and 1 meaning that someone is using them. Put a1 in the register, and swap the memory word and the register. If the register contains a 0 after the swap, access has been granted. If it contains a 1, access has been denied. When a process is done, it stores a 0 in the flag in memory23.To do a semaphore ope ration, the operating system first disables interrupts. Then it reads the value of the semaphore. If it is doing a down and the semaphore is equal to zero, it puts the calling process on a list of blocked processes associated with the semaphore. If it is doing an up, it must check to see if any processes are blocked on the semaphore. If one or more processes are blocked, one of then is removed from the list of blocked processes and made runnable. When all these operations have been completed, interrupts can be enabled again.24.Associated with each counting semaphore are two binary semaphores, M, used for mutual exclusion, and B, used for blocking. Also associated with each counting semaphore is a counter that holds the number of ups minus the number of downs, and a list of processes blocked on that semaphore. To implement down, a process first gains exclusive access to the semaphores, counter, and list by doing a down on M. It then decrements the counter. If it is zero or more, it just does an up on M and exits. If M is negative, the proc- ess is put on the list of blocked processes. Then an up is done on M and a down is done on B to block the process. To implement up, first M is downed to get mutual exclusion, and then the counter is incremented. If it is more than zero, no one was blocked, so all that needs to bedone is to up M. If, however, the counter is now negative or zero, some process must be removed from the list. Finally, an up is done on B and M in that order.25.If the program operates in phases and neither process may enter the next phase until both arefinished with the current phase, it makes perfect sense to use a barrier.26.With round-robin scheduling it works. Sooner or later L will run, and eventually it will leave its critical region. The point is, with priority scheduling, L never gets to run at all; with round robin, it gets a normal time slice periodically, so it has the chance to leave its critical region.27.With kernel threads, a thread can block on a semaphore and the kernel can run some other thread in the same process. Consequently, there is no problem using semaphores. With user-level threads, when one thread blocks on a semaphore, the kernel thinks the entire process is blocked and does not run it ever again. Consequently, the process fails.28.It is very expensive to implement. Each time any variable that appears in a predicate on which some process is waiting changes, the runtime system must re-evaluate the predicate to see if the process can be unblocked. With the Hoare and Brinch Hansen monitors, processes can only be awakened on a signal primitive.29.The employees communicate by passing messages: orders, food, and bags in this case. In UNIX terms, the four processes are connected by pipes.30.It does not lead to race conditions (nothing is ever lost), but it is effectively busy waiting.31.If a philosopher blocks, neighbors can later see that he is hungry by checking his state, in test, so he can be awakened when the forks are available.32.The change would mean that after a philosopher stopped eating, neither of his neighbors could be chosen next. In fact, they would never be chosen. Suppose that philosopher 2 finished eating. He would run test for philosophers 1 and 3, and neither would be started, even though both were hungry and both forks were available. Similary, if philosopher 4 finished eating, philosopher 3 would not be started. Nothing would start him.33.Variation 1: readers have priority. No writer may start when a reader is active. When a new reader appears, it may start immediately unless a writer is currently active. When a writer finishes, if readers are waiting, they are all started, regardless of the presence of waiting writers. Variation 2: Writers have priority. No reader may start when a writer is waiting. When the last active process finishes, a writer is started, if there is one; otherwise, all the readers (if any) are started. Variation 3: symmetric version. When a reader is active, new readers may start immediately. When a writer finishes, a new writer has priority, if one is waiting. In other words, once we have started reading, we keep reading until there are no readers left. Similarly, once we have started writing, all pending writers are allowed to run.34.It will need nT sec.35.If a process occurs multiple times in the list, it will get multiple quanta per cycle. This approach could be used to give more important processes a larger share of the CPU. But when the process blocks, all entries had better be removed from the list of runnable processes.36.In simple cases it may be possible to determine whether I/O will be limiting by looking at source code. For instance a program that reads all its input files into buffers at the start will probably not be I/O bound, but a problem that reads and writes increment ally to a number of different files (such as a compiler) is likely to be I/O bound. If the operating system provides a facility such as the UNIX ps command that can tell you the amount of CPU time used by a program , you can compare this with total time to complete execution of the program. This is, of course, most meaningful on a system where you are the only user.37.For multiple processes in a pipeline, the common parent could pass to the operating system information about the flow of data. With this inf ormation the OS could, for instance, determine which process could supply output to a process blocking on a call for input.38.The CPU efficiency is the useful CPU time divided by the total CPU time.When Q≥T, the basic cycle is for the process to run for T and undergo aprocess switch for S. Thus (a) and (b) have an efficiency of T /(S T ). Whenthe quantum is shorter than T, each run of T will require T /Q processswitches, wasting a time ST /Q. The efficiency here is then333333333T T ST /Q which reduces to Q / (Q S ), which is the answer to (c). For (d), we just substitute Q for S and find that the efficiency is 50 percent. Finally, for (e), as Q→0 the efficiency goes to 0.39.Shortest job first is the way to minimize average response time.0 < X≤3: X, 3, 5, 6, 9.3 < X≤5: 3, X, 5, 6, 9.5 < X≤6: 3, 5, X, 6, 9.6 < X≤9: 3, 5, 6, X, 9.X > 9: 3, 5, 6, 9, X.40.For round robin, during the first 10 minutes each job gets 1/5 of the CPU. At the end of 10 minutes, Cfinishes. During the next 8 minutes, each job gets1/4 of the CPU, after which time Dfinishes. Then each of the three remaining jobs gets 1/3 of the CPU for 6 minutes, until Bfinishes, and so on. The finishing times for the five jobs are 10, 18, 24, 28, and 30, for an average of22 mi nutes. For priority scheduling, B is run first. After 6 minutes it is finished. The other jobs finish at 14, 24, 26, and 30, for an average of 18.8 minutes. If the jobs run in the order A through E, they finish at 10, 16, 18, 22, and 30, for an average of 19.2 minutes. Finally, shortest job first yields finishing times of 2, 6, 12, 20, and 30, for an average of 14 minutes.41.The first time it gets 1 quantum. On succeeding runs it gets 2, 4, 8, and 15, so it must be swapped in 5 times.42. A check could be made to see if the program was expecting input and did anything with it. A program that was not expecting input and did not process it would not get any special priority boost.43.The sequence of predictions is 40, 30, 35, and now 25.44.The fraction of the CPU used is 35/50 + 20/100 + 10/200 + x/250. To be chedulable, this must be less than 1. Thus x must be less than 12.5 msecs45.Two-level scheduling is needed when memory is too small to hold all the ready processes. Some set of them is put into memory, and a choice is made from that set. From time to time, the set of in-core processes is adjusted. This algorithm is easy to implement and reasonably efficient, certainly a lot better than say, round robin without regard to whether a process was in memory or not.46.The kernel could schedule processes by any means it wishes, but within each process it runs threads strictly in priority order. By letting the user process set the priority of its own threads, the user controls the policy but the kernel handles the mechanism.47.A possible shell script might beif [ ! –f numbers ]; then echo 0 > numbers; ficount=0while (test $count != 200 )docount=‘expr $count + 1 ‘n=‘tail –1 numbers‘expr $n + 1 >>numbersdoneRun the script twice simultaneously, by starting it once in the background(using &) and again in the foreground. Then examine the file numbers. It will probably start out looking like an orderly list of numbers, but at some point it will lose its orderliness, due to the race condition created by running two copies of the script. The race can be avoided by having each copy of the script test for and set a lock on the file before entering the critical area, and unlocking it upon leaving the critical area. This can be done like this: if ln numbers numbers.lockthenn=‘tail –1 numbers‘expr $n + 1 >>numbersrm numbers.lockfiThis version will just skip a turn when the file is inaccessible, variant solutions could put the process to sleep, do busy waiting, or count only loops in which the operation is successful.SOLUTIONS TO CHAPTER 3 PROBLEMS1.In the U.S., consider a presidential election in which three or more candidates are trying for the nomination of some party. After all the primary elections are finished, when the delegates arrive at the party convention, it could happen that no candidate has a majority and that no delegate is willing to change his or her vote. This is a deadlock. Each candidate has some resources(votes) but needs more to get the job done. In countries with multiple political parties in the parliament, it could happen that each party supports a different version of the annual budget and that it is impossible to assemble a majority to pass the budget. This is also a deadlock.2.If the printer starts to print a file before the entire file ha s been received (this is often allowed to speed response), the disk may fill with other requests that can’t be printed until the first file is done, but which use up disk space needed to receive the file currently being printed. If the spooler does not start t o print a file until the entire file has been spooled it can reject a request that is too big. Starting to print a file is equivalent to reserving the printer; if the reservation is deferred until it is known that the entire file can be received, a deadlock of the entire system can be avoided. The user with the file that won’t fit is still deadlocked of course, and must go to another facility that permits printing bigger files.3.The printer is nonpreemptable; the system cannot start printing another job until the previous one is complete. The spool disk is preemptable; you can delete an incomplete file that is growing too large and have the user send it later, assuming the protocol allows that4.Yes. It does not make any difference whatsoever.5.Yes, illegal graphs exist. We stated that a resource may only be held by a single process. An arc from a resource square to a process circle indicates that the process owns the resource. Thus a square with arcs going from it to two or more processes means that all those processes hold the resource, which violates the rules. Consequently, any graph in which multiple arcs leave a square and end in different circles violates the rules. Arcs from squares to squares or from circles to circles also violate the rules.6.A portion of all such resources could be reserved for use only by processes owned by the administrator, so he or she could always run a shell and programs needed to evaluate a deadlock and make decisions about which processes to kill to make the system usable again.7.Neither change leads to deadlock. There is no circular wait in either case.8.Voluntary relinquishment of a resource is most similar to recovery through preemption. The essential difference is that computer processes are not expected to solve such problems on their own. Preemption is analogous to th operator or the operating system acting as a policeman, overriding the normal rules individual processes obey.9.The process is asking for more resources than the system has. There is no conceivable way it can get these resources, so it can never finish, even if no other processes want any resources at all.10.If the system had two or more CPUs, two or more processes could run in parallel, leading to diagonal trajectories.11.Yes. Do the whole thing in three dimensions. The z-axis measures the number of instructions executed by the third process.12.The method can only be used to guide the scheduling if the exact instant at which a resource is going to be claimed is known in advance. In practice, this is rarely the case.13.A request from D is unsafe, but one from C is safe.14.There are states that are neither safe nor deadlocked, but which lead to deadlocked states. As an example, suppose we have four resources: tapes, plotters, scanners, and CD-ROMs, as in the text, and three processes competing for them. We could have the following situation:。
操作系统课后答案——第四章

第四章存储器管理1. 为什么要配置层次式存储器?这是因为:a.设置多个存储器可以使存储器两端的硬件能并行工作。
b.采用多级存储系统,特别是Cache技术,这是一种减轻存储器带宽对系统性能影响的最佳结构方案。
c.在微处理机内部设置各种缓冲存储器,以减轻对存储器存取的压力。
增加CPU中寄存器的数量,也可大大缓解对存储器的压力。
2. 可采用哪几种方式将程序装入内存?它们分别适用于何种场合?将程序装入内存可采用的方式有:绝对装入方式、重定位装入方式、动态运行时装入方式;绝对装入方式适用于单道程序环境中,重定位装入方式和动态运行时装入方式适用于多道程序环境中。
3. 何为静态链接?何谓装入时动态链接和运行时动态链接?a.静态链接是指在程序运行之前,先将各自目标模块及它们所需的库函数,链接成一个完整的装配模块,以后不再拆开的链接方式。
b.装入时动态链接是指将用户源程序编译后所得到的一组目标模块,在装入内存时,采用边装入边链接的一种链接方式,即在装入一个目标模块时,若发生一个外部模块调用事件,将引起装入程序去找相应的外部目标模块,把它装入内存中,并修改目标模块中的相对地址。
c.运行时动态链接是将对某些模块的链接推迟到程序执行时才进行链接,也就是,在执行过程中,当发现一个被调用模块尚未装入内存时,立即由OS去找到该模块并将之装入内存,把它链接到调用者模块上。
4. 在进行程序链接时,应完成哪些工作?a.对相对地址进行修改b.变换外部调用符号6. 为什么要引入动态重定位?如何实现?a.程序在运行过程中经常要在内存中移动位置,为了保证这些被移动了的程序还能正常执行,必须对程序和数据的地址加以修改,即重定位。
引入重定位的目的就是为了满足程序的这种需要。
b.要在不影响指令执行速度的同时实现地址变换,必须有硬件地址变换机构的支持,即须在系统中增设一个重定位寄存器,用它来存放程序在内存中的起始地址。
程序在执行时,真正访问的内存地址是相对地址与重定位寄存器中的地址相加而形成的。
操作系统第三版,课后答案

多道批处理系统:把多个作业同时放入内存,当某个作业因某种原因运行不下去时,系统就转向下一作业运行。
特点:1.多个作业同时存在于内存。
2.作业完成顺序与进入顺序无关。
3.作业由系统程序调入内存。
分时系统:作业直接进入内存。
不允许一个作业长期占有CPU.多个用户分时使用主机,每一用户分得一个时间片,用完这个时间片后操作系统将处理机分给另一用户,如此循环,每一用户可以周期性地获得CPU使用权,这样每一用户都有一种独占CPU的感觉。
分时系统的特征:多路性、独立性、及时性、交互性。
程序的并发执行是指:若干个程序同时在系统中执行,这些程序的执行在时间上是重叠的,一个程序的执行尚未结束,另一个程序的执行已经开始。
进程的定义:可并发执行的程序段,在某个数据集合上的一次执行过程。
⏹进程是程序的一次执行。
⏹进程是一个程序及其数据在处理机上顺序执行时所发生的活动。
⏹进程是程序在一个数据集合上运行的过程,它是系统进行资源分配和调度的一个独立单位。
进程与程序的区别与联系:1.进程是动态的概念,程序是静态的概念;进程离开程序就失去了意义。
2.程序可永久保存,而进程具有短暂生命周期。
3.一个程序可对应于多个进程;4.进程更能真实地描述并发,而程序不能。
进程的状态及其转化:1.运行:该进程已占有了处理机,其程序正在执行。
2.就绪:该进程已准备好,占有了执行所需的除处理机之外的所有资源和条件。
3.阻塞:该进程正在等待系统中某事件发生(例如I/O操作的完成)。
进程的物理结构:两部分:进程控制块(PCB),进程体(程序部分,数据部分)PCB:为系统提供控制、管理进程信息的数据结构,是进程在系统中存在的唯一标识。
一个用户进程其实体存在于内存用户工作区。
其PCB存放于内存操作系统工作区。
PCB内容:进程标识符,处理机状态,进程调度信息,进程控制信息。
PCB的组织方式:链接方式,索引方式。
资源分配原则:子进程只能占有父进程所拥有的资源,撤消进程时,子孙进程全部随之撤消。
操作系统第三章,第四章,第九章课后习题整理

操作系统第三章,第四章,第九章课后习题整理第3章进程描述和控制复习题:什么是指令跟踪?答:指令跟踪是指为该进程而执行的指令序列。
通常那些事件会导致创建一个进程?答:新的批处理作业;交互登录;操作系统因为提供一项服务而创建;由现有的进程派生。
(详情请参考表3.1)对于图3.6中的进程模型,请简单定义每个状态。
答:运行态:该进程正在执行。
就绪态:进程做好了准备,只要有机会就开始执行。
阻塞态:进程在某些事件发生前不能执行,如I/O 操作完成。
新建态:刚刚创建的进程,操作系统还没有把它加入到可执行进程组中。
退出态:操作系统从可执行进程组中释放出的进程,或者是因为它自身停止了,或者是因为某种原因被取消。
抢占一个进程是什么意思?答:处理器为了执行另外的进程而终止当前正在执行的进程,这就叫进程抢占。
什么是交换,其目的是什么?答:交换是指把主存中某个进程的一部分或者全部内容转移到磁盘。
当主存中没有处于就绪态的进程时,操作系统就把一个阻塞的进程换出到磁盘中的挂起队列,从而使另一个进程可以进入主存执行。
为什么图3.9(b)中有两个阻塞态?答:有两个独立的概念:进程是否在等待一个事件(阻塞与否)以及进程是否已经被换出主存(挂起与否)。
为适应这种2*2的组合,需要两个阻塞态和两个挂起态。
列出挂起态进程的4个特点。
答:1.进程不能立即执行。
2.进程可能是或不是正在等待一个事件。
如果是,阻塞条件不依赖于挂起条件,阻塞事件的发生不会使进程立即被执行。
3.为了阻止进程执行,可以通过代理把这个进程置于挂起态,代理可以是进程自己,也可以是父进程或操作系统。
4.除非代理显式地命令系统进行状态转换,否则进程无法从这个状态中转移。
对于哪类实体,操作系统为了管理它而维护其信息表?答:内存、I/O、文件和进程。
列出进程控制块中的三类信息。
答:进程标识,处理器状态信息,进程控制信息。
为什么需要两种模式(用户模式和内核模式)?答:用户模式下可以执行的指令和访问的内存区域都受到限制。
操作系统(第三版)刘振鹏王煜张明编著答案解析
WORD 格式可编辑格式可编辑专业知识整理分享专业知识整理分享 第1章 引论1.什么是硬件系统?什么是软件环境?它们之间有什么联系?答:计算机硬件是指计算机系统中由电子、机械和光电元件等组成的各种计算机部件和计算机设备。
这些部件和设备依据计算机系统结构的要求构成的有机整体,称为计算机硬件系统。
软件是计算机系统中的程序和有关的文件。
程序是计算任务的处理对象和处理规则的描述;文件是为了便于了解程序所需的资料说明。
硬件为软件提供具体实现的基础,软件是用户与硬件之间的接口界面。
2.什么是操作系统?操作系统追求的主要目标是什么?答:操作系统是计算机系统中的一个系统软件,是能有效地组织和管理计算机系统中的硬件和软件资源,合理地组织计算机工作流程,控制程序的执行,并向用户提供各种服务功能,使得用户能够灵活、方便、有效地使用计算机,并使整个计算机系统能高效地运行的一组程序 模块的集合。
操作系统追求的主要目标包括四个方面,分别是:方便性、有效性、可扩充性、开放性。
3.在用户程序与硬件裸机之间,操作系统可以分为那几个模块?答:在用户程序与硬件裸机之间,操作系统可以分为:系统软件、支撑软件和应用软件三个模块。
4.操作系统如何实现计算机操作的自动化?如何看待操作系统在计算机系统中的地位?答:(1)计算机操作系统是实现自动化控制的一部分,大致可以把操作系统分为以下几类:批处理操作系统、分时操作系统、实时操作系统、网络操作系统和分布式操作系统。
其中批处理操作系统、分时操作系统、实时操作系统是基本的操作系统。
批处理操作系统按照用户预先规定好的步骤控制作业的执行,实现计算机操作的自动化。
又可分为批处理单道系统和批处理多道系统。
单道系统每次只有一个作业装入计算机系统的主存储器运行,多个作业可自动、顺序地被装入运行。
批处理多道系统则允许多个作业同时装入主存储器,中央处理器轮流地执行各个作业,各个作业可以同时使用各自所需的外围设备,这样可以充分利用计算机系统的资源,缩短作业时间,提高系统的吞吐率。
操作系统(第三版)孙钟秀主编课后习题4应用题参考答案

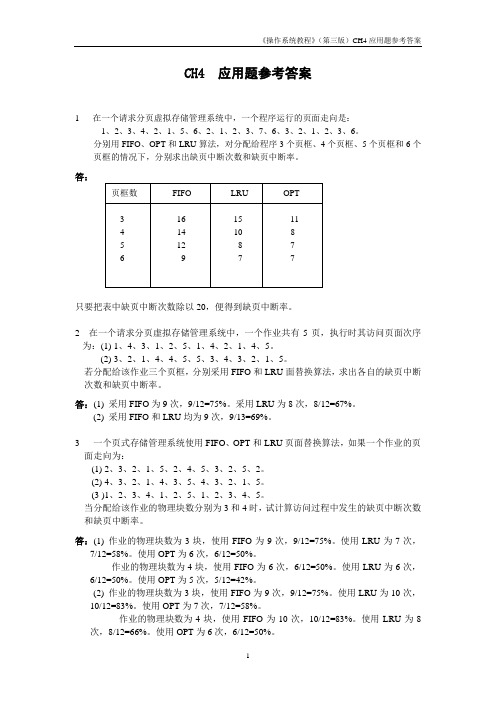
CH4 应用题参考答案1 在一个请求分页虚拟存储管理系统中,一个程序运行的页面走向是:1、2、3、4、2、1、5、6、2、1、2、3、7、6、3、2、1、2、3、6。
分别用FIF O、OPT和LRU算法,对分配给程序3个页框、4个页框、5个页框和6个页框的情况下,分别求出缺页中断次数和缺页中断率。
答:只要把表中缺页中断次数除以20,便得到缺页中断率。
2 在一个请求分页虚拟存储管理系统中,一个作业共有5页,执行时其访问页面次序为:(1) 1、4、3、1、2、5、1、4、2、1、4、5。
(2) 3、2、1、4、4、5、5、3、4、3、2、1、5。
若分配给该作业三个页框,分别采用FI FO和LR U面替换算法,求出各自的缺页中断次数和缺页中断率。
答:(1) 采用FIFO为9次,9/12=75%。
采用LRU为8次,8/12=67%。
(2) 采用FIFO和LRU均为9次,9/13=69%。
3 一个页式存储管理系统使用FIFO、OPT和LR U页面替换算法,如果一个作业的页面走向为:(1) 2、3、2、1、5、2、4、5、3、2、5、2。
(2) 4、3、2、1、4、3、5、4、3、2、1、5。
(3 )1、2、3、4、1、2、5、1、2、3、4、5。
当分配给该作业的物理块数分别为3和4时,试计算访问过程中发生的缺页中断次数和缺页中断率。
答:(1) 作业的物理块数为3块,使用FIFO为9次,9/12=75%。
使用LRU为7次,7/12=58%。
使用OPT为6次,6/12=50%。
作业的物理块数为4块,使用FIFO为6次,6/12=50%。
使用LRU为6次,6/12=50%。
使用OPT为5次,5/12=42%。
(2) 作业的物理块数为3块,使用FIFO为9次,9/12=75%。
使用LRU为10次,10/12=83%。
操作系统(第三版)孙钟秀主编 课后习题4应用题参考答案
CH4 应用题参考答案1 在一个请求分页虚拟存储管理系统中,一个程序运行的页面走向是:1、2、3、4、2、1、5、6、2、1、2、3、7、6、3、2、1、2、3、6。
分别用FIFO、OPT和LRU算法,对分配给程序3个页框、4个页框、5个页框和6个页框的情况下,分别求出缺页中断次数和缺页中断率。
答:只要把表中缺页中断次数除以20,便得到缺页中断率。
2 在一个请求分页虚拟存储管理系统中,一个作业共有5页,执行时其访问页面次序为:(1) 1、4、3、1、2、5、1、4、2、1、4、5。
(2) 3、2、1、4、4、5、5、3、4、3、2、1、5。
若分配给该作业三个页框,分别采用FIFO和LRU面替换算法,求出各自的缺页中断次数和缺页中断率。
答:(1) 采用FIFO为9次,9/12=75%。
采用LRU为8次,8/12=67%。
(2) 采用FIFO和LRU均为9次,9/13=69%。
3 一个页式存储管理系统使用FIFO、OPT和LRU页面替换算法,如果一个作业的页面走向为:(1) 2、3、2、1、5、2、4、5、3、2、5、2。
(2) 4、3、2、1、4、3、5、4、3、2、1、5。
(3 )1、2、3、4、1、2、5、1、2、3、4、5。
当分配给该作业的物理块数分别为3和4时,试计算访问过程中发生的缺页中断次数和缺页中断率。
答:(1) 作业的物理块数为3块,使用FIFO为9次,9/12=75%。
使用LRU为7次,7/12=58%。
使用OPT为6次,6/12=50%。
作业的物理块数为4块,使用FIFO为6次,6/12=50%。
使用LRU为6次,6/12=50%。
使用OPT为5次,5/12=42%。
(2) 作业的物理块数为3块,使用FIFO为9次,9/12=75%。
使用LRU为10次,10/12=83%。
使用OPT为7次,7/12=58%。
作业的物理块数为4块,使用FIFO为10次,10/12=83%。
使用LRU为8次,8/12=66%。
现代操作系统课后答案

现代操作系统课后答案【篇一:现代操作系统习题答案】>(汤小丹编电子工业出版社2008.4)第1章操作系统引论习题及答案1.11 os有哪几大特征?其最基本的特征是什么?答:并发、共享、虚拟和异步四个基本特征,其中最基本的特征是并发和共享。
1.15 处理机管理有哪些主要功能?其主要任务是什么?答案略,见p17。
1.22 (1)微内核操作系统具有哪些优点?它为何能有这些优点?(2)现代操作系统较之传统操作系统又增加了哪些功能和特征?第2章进程的描述与控制习题及答案略第3章进程的同步与通信习题及答案3.9 在生产者-消费者问题中,如果缺少了signal(full)或signal(empty),对执行结果将会有何影响?答:资源信号量full表示缓冲区中被占用存储单元的数目,其初值为0,资源信号量empty表示缓冲区中空存储单元的数目,其初值为n,signal(full)在生产者进程中,如果在生产者进程中缺少了signal(full),致使消费者进程一直阻塞等待而无法消费由生产者进程生产的数据;signal(empty)在消费者进程中,如果在消费者进程中缺少了signal(empty),致使生产者进程一直阻塞等待而无法将生产的数据放入缓冲区。
3.13 试利用记录型信号量写出一个不会出现死锁的哲学家进餐问题的算法。
答:参考答案一:至多只允许有四位哲学家同时去拿左边的筷子,最终能保证至少有一位哲学家能够进餐,并在用毕时能释放出他用过的两支筷子,从而使更多的哲学家能够进餐。
采用此方案的算法如下:var chopstick:array[0,…,4] of semaphore :=1;room:semphore:=4;repeatwait(room);wait(chopstick[i]);wait(chopstick[(i+1) mod 5]);…eat;…signal(chopstick[i]);signal(chopstick[(i+1) mod 5);signal(room);…think;until false;第4章处理机调度与死锁习题及答案4.1 高级调度与低级调度的主要任务是什么?为什么要引入中级调度?答:略,见p73。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1.
这些系统直接把程序载入内存,并且从word0(魔数)开始执行。
为了避免将header作为代码执行,魔数是一条branch指令,其目标地址正好在header之上。
按这种方法,就可能把二进制文件直接读取到新的进程地址空间,并且从0开始运行。
5.
rename 调用不会改变文件的创建时间和最后的修改时间,但是创建一个新的文件,其创建时间和最后的修改时间都会改为当前的系统时间。
另外,如果磁盘满,复制可能会失败。
10.
由于这些被浪费的空间在分配单元(文件)之间,而不是在它们内部,因此,这是外部碎片。
这类似于交换系统或者纯分段系统中出现的外部碎片。
11.
传输前的延迟是9ms,传输速率是2^23Bytes/s,文件大小是2^13Bytes,故从内存读取或写回磁盘的时间都是9+2^13/2^23=9.977ms,总共复制一个文件需要9.977*2=19.954ms。
为了压缩8G磁盘,也就是2^20个文件,每个需要19.954ms,总共就需要20,923 秒。
因此,在每个文件删除后都压缩磁盘不是一个好办法。
12.
因为在系统删除的所有文件都会以碎片的形式存在磁盘中,当碎
片到达一定量磁盘就不能再装文件了,必须进行外部清理,所以紧缩磁盘会释放更多的存储空间,但在每个文件删除后都压缩磁盘不是一个好办法。
15.
由于1024KB = 2^20B, 所以可以容纳的磁盘地址个数是2^20/4 = 2^18个磁盘地址,间接块可以保存2^18个磁盘地址。
与 10 个直接的磁盘地址一道,最大文件有 262154 块。
由于每块为 1 MB,最大的文件是262154 MB。
19.
每个磁盘地址需要D位,且有F个空闲块,故需要空闲表为DF位,采用位图法则需要B位,当DF<B时,空闲表采用的空间少于位图,当D=16时,得F/B<1/D=6.25%,即空闲空间的百分比少于6.25%.
20.
a)1111 1111 1111 0000
b)1000 0001 1111 0000
c)1111 1111 1111 1100
d)1111 1110 0000 1100
27.
平均时间T = 1*h + 40*(1-h)=-39h+40ms
28.
1500rpm(每分钟1500转),60s/1500=0.004s=4ms,即每转需要4ms,平均旋转延迟为2ms;
读取一个k个字节的块所需要的时间T是平均寻道时间,平均旋转延迟和传送时间之和。
此题中T = 8+2+(k/262144)* 4 ms,将k=1KB 代入得,T = 10.015625ms同理当k=2KB,T=10.03125ms ,当k=4KB,T=10.0625ms。
转换为速率为1KB/10.015625ms = 99.84KB/s, 2KB/10.03125ms = 199.38KB/s, 4KB/10.0625ms =397.52KB/s。
29.
1KB / 2KB * 100% = 50%
32.
由于1KB=1024B,所以1KB磁盘块可以容纳的磁盘地址个数是2^10B/4 = 256个。
故一个一次间接块存储256个磁盘地址。
一个二次间接块存储256^2磁盘地址。
一个三次间接块存储256^3磁盘地址。
把这些全部加起来,10+256+256^2+256^3 = 16843018块,每一
块1K,即16843018KB,约16.06 GB.
33.
(1) directory /
(2) i-node for /usr
(3) directory /usr
(4) i-node for /usr/ast
(5) directory /usr/ast
(6) i-node for /usr/ast/courses
(7) directory /usr/ast/courses
(8) i-node for /usr/ast/courses/os
(9)directory /usr/ast/courses/os/
(10)i-node for /usr/ast/courses/os/handout.t。
