最新ccna题库_251-300知识讲解
ccna题库_51-100

Refer to the exhibit. What can be determined from the output?A. 192.168.1.2 is local to the router.B. 192.168.3.1 is local to the router.C. 192.168.1.2 will age out in less than 1 minute.D. 192.168.3.1 has aged out and is marked for deletion.QUESTION 52Refer to the exhibit. Which command would allow the translations to be created on the router?A. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 19B. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 19C. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 18D. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 18Refer to the exhibit. An administrator pings the default gateway at 10.10.10.1 and sees the output as shown. At which OSI layer is the problem?A. data link layerB. application layerC. access layerD. session layerE. network layerQUESTION 54Refer to the exhibit. Which value will be configured for Default Gateway of the Local Area Connection?A. 10.0.0.0B. 10.0.0.254C. 192.223.129.0D. 192.223.129.254QUESTION 55Refer to the exhibit. The user at Workstation B reports that Server A cannot be reached. What is preventing Workstation B from reaching Server A?A. The IP address for Server A is a broadcast address.B. The IP address for Workstation B is a subnet address.C. The gateway for Workstation B is not on the same subnet.D. The gateway for Server A is not on the same subnet.QUESTION 56Refer to the exhibit. What does the (*) represent in the output?A. Packet is destined for a local interface to the router.B. Packet was translated, but no response was received from the distant device.C. Packet was not translated, because no additional ports are available.D. Packet was translated and fast switched to the destination.QUESTION 57Refer to the exhibit. What command sequence will enable PAT from the inside to outside network?A. (config) ip nat pool isp-net 1.2.4.2 netmask 255.255.255.0 overloadB. (config-if) ip nat outside overloadC. (config) ip nat inside source list 1 interface ethernet1 overloadD. (config-if) ip nat inside overloadQUESTION 58Refer to the exhibit. What will happen to HTTP traffic coming from the Internet that is destined for 172.16.12.10 if the traffic is processed by this ACL?A. Traffic will be dropped per line 30 of the ACL.B. Traffic will be accepted per line 40 of the ACL.C. Traffic will be dropped, because of the implicit deny all at the end of the ACL.D. Traffic will be accepted, because the source address is not covered by the ACL.QUESTION 59Refer to the exhibit. Which statement describes the effect that the Router1 configuration has on devices in the 172.16.16.0 subnet when they try to connect to SVR-A using Telnet or SSH?A. Devices will not be able to use Telnet or SSH.B. Devices will be able to use SSH, but not Telnet.C. Devices will be able to use Telnet, but not SSH.D. Devices will be able to use Telnet and SSH.QUESTION 60What are three advantages of VLANs? (Choose three.)A. VLANs establish broadcast domains in switched networks.B. VLANs utilize packet filtering to enhance network security.C. VLANs provide a method of conserving IP addresses in large networks.D. VLANs provide a low-latency internetworking alternative to routed networks.E. VLANs allow access to network services based on department, not physical location.F. VLANs can greatly simplify adding, moving, or changing hosts on the network.QUESTION 61An administrator would like to configure a switch over a virtual terminal connection from locations outside of the local LAN. Which of the following are required in order for the switch to be configured from a remote location? (Choose two.)A. The switch must be configured with an IP address, subnet mask, and default gateway.B. The switch must be connected to a router over a VLAN trunk.C. The switch must be reachable through a port connected to its management VLAN.D. The switch console port must be connected to the Ethernet LAN.E. The switch management VLAN must be created and have a membership of at least one switch port.F. The switch must be fully configured as an SNMP agent.QUESTION 62Which of the following host addresses are members of networks that can be routed across the public Internet? (Choose three.)A. 10.172.13.65B. 172.16.223.125C. 172.64.12.29D. 192.168.23.252E. 198.234.12.95F. 212.193.48.254QUESTION 63Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to network hosts? (Choose three.)A. 15.234.118.63B. 92.11.178.93C. 134.178.18.56D. 192.168.16.87E. 201.45.116.159F. 217.63.12.192QUESTION 64Which of the following are benefits of VLANs? (Choose three.)A. They increase the size of collision domains.B. They allow logical grouping of users by function.C. They can enhance network security.D. They increase the size of broadcast domains while decreasing the number of collision domains.E. They increase the number of broadcast domains while decreasing the size of the broadcast domains.F. They simplify switch administration.QUESTION 65Which router IOS commands can be used to troubleshoot LAN connectivity problems? (Choose three.)A. pingB. tracertC. ipconfigD. show ip routeE. winipcfgF. show interfacesQUESTION 66Refer to the exhibit. After HostA pings HostB, which entry will be in the ARP cache of HostA to support this transmission?A.B.C.D.E.F.QUESTION 67Which two topologies are using the correct type of twisted-pair cables? (Choose two.)A.B.C.D.E.QUESTION 68Which of the following are true regarding bridges and switches? (Choose two.)A. Bridges are faster than switches because they have fewer ports.B. A switch is a multiport bridge.C. Bridges and switches learn MAC addresses by examining the source MAC address of each frame received.D. A bridge will forward a broadcast but a switch will not.E. Bridges and switches increase the size of a collision domain.QUESTION 69What are some of the advantages of using a router to segment the network? (Choose two.)A. Filtering can occur based on Layer 3 information.B. Broadcasts are eliminated.C. Routers generally cost less than switches.D. Broadcasts are not forwarded across the router.E. Adding a router to the network decreases latency.QUESTION 70Which of the following statements are true regarding bridges and switches? (Choose 3.)A. Switches are primarily software based while bridges are hardware based.B. Both bridges and switches forward Layer 2 broadcasts.C. Bridges are frequently faster than switches.D. Switches have a higher number of ports than most bridges.E. Bridges define broadcast domains while switches define collision domains.F. Both bridges and switches make forwarding decisions based on Layer 2 addresses.QUESTION 71Which characteristics are representative of a link-state routing protocol? (Choose three.)A. provides common view of entire topologyB. exchanges routing tables with neighborsC. calculates shortest pathD. utilizes event-triggered updatesE. utilizes frequent periodic updatesQUESTION 72Which of the following statements describe the network shown in the graphic? (Choose two.)A. There are two broadcast domains in the network.B. There are four broadcast domains in the network.C. There are six broadcast domains in the network.D. There are four collision domains in the network.E. There are five collision domains in the network.F. There are seven collision domains in the network.QUESTION 73Use the output from the router shown in the graphic above to determine which of the following are correct. (Choose two.)A. Router John uses a link-state routing protocol.B. Router John will receive routing updates on the Serial0/0 interface.C. Router John will receive routing updates on the Serial0/1 interface.D. Router John will send routing updates out the Serial0/0 interface.E. Router John will send routing updates out the FastEthernet0/0 interface.F. Router John will send routing updates out the Serial0/1 interface.QUESTION 74A national retail chain needs to design an IP addressing scheme to support a nationwide network. The company needs a minimum of 300 sub-networks and a maximum of 50 host addresses per subnet. Working with only one ClassB address, which of the following subnet masks will support an appropriate addressing scheme? (Choose two.)A. 255.255.255.0B. 255.255.255.128C. 255.255.252.0D. 255.255.255.224E. 255.255.255.192F. 255.255.248.0QUESTION 75Given the address 192.168.20.19/28, which of the following are valid host addresses on this subnet? (Choose two.)A. 192.168.20.29B. 192.168.20.16C. 192.168.20.17D. 192.168.20.31E. 192.168.20.0QUESTION 76An inbound access list has been configured on a serial interface to deny packet entry for TCP and UDP ports 21, 23 and 25. What types of packets will be permitted by this ACL? (Choose three.)A. FTPB. TelnetC. SMTPD. DNSE. HTTPF. POP3QUESTION 77Which are valid modes for a switch port used as a VLAN trunk? (Choose three.)A. transparentB. autoC. onD. desirableE. blockingF. forwardingQUESTION 78OSPF routing uses the concept of areas. What are the characteristics of OSPF areas? (Choose three.)A. Each OSPF area requires a loopback interface to be configured.B. Areas may be assigned any number from 0 to 65535.C. Area 0 is called the backbone area.D. Hierarchical OSPF networks do not require multiple areas.E. Multiple OSPF areas must connect to area 0.F. Single area OSPF networks must be configured in area 1.QUESTION 79What information does a router running a link-state protocol use to build and maintain its topological database? (Choose two.)A. hello packetsB. SAP messages sent by other routersC. LSAs from other routersD. beacons received on point-to-point linksE. routing tables received from other link-state routersF. TTL packets from designated routersQUESTION 80Which statements describe the routing protocol OSPF? (Choose three.)A. It supports VLSM.B. It is used to route between autonomous systems.C. It confines network instability to one area of the network.D. It increases routing overhead on the network.E. It allows extensive control of routing updates.F. It is simpler to configure than RIP v2.QUESTION 81The switches shown in the diagram, Core and Core2, are both Catalyst 2950s. The addressing scheme for each company site is as follows:Router Ethernet port - 1st usable addressCore - 2nd usable addressCore2 - 3rd usable addressFor this network, which of the following commands must be configured on Core2 to allow it to be managed remotely from any subnet on the network? (Choose three.)A.Core2(config)# interface f0/0Core2(config-if)# ip address 192.168.1.10 255.255.255.248B.Core2(config)# interface vlan 1Core2(config-if)# ip address 192.168.1.11 255.255.255.248C.Core2(config)# line con 0Core2(config-line)# password ciscoD.Core2(config)# line vty 0 4Core2(config-line)# password ciscoE. Core2(config)# ip default-gateway 192.168.1.9F. Core2(config)# ip route 0.0.0.0 0.0.0.0 192.168.1.8QUESTION 82An administrator is unsuccessful in adding VLAN 50 to a switch. While troubleshooting the problem, the administrator views the output of the show vtp status command, which is displayed in the graphic. What commands must be issued on this switch to add VLAN 50 to the database? (Choose two.)A. Switch(config-if)# switchport access vlan 50B. Switch(vlan)# vtp serverC. Switch(config)# config-revision 20D. Switch(config)# vlan 50 name TechE. Switch(vlan)# vlan 50F. Switch(vlan)# switchport trunk vlan 50。
计算机网络知识

CCNA认证试题一(附答案和解析)中文版(一)CCNA1 2007-09-30 15:49:59 阅读139 评论0 字号:大中小订阅1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住IEEE802.1-------IEEE802.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C***A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术与信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE定义的标准在工业界有极大的影响。
下面列出:IEEE802.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-X(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ()(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:11000000.10101000.00010011.1111111111111111.11111111.11110000.00000000主机位变成全0表示这个IP的网络地址主机槐涑扇?表示这个IP的广播地址RFC1918文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefix)172.16.0.0 - 172.31.255.255 (172.16/12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?()(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
CCNA最新题库

一.1.mac地址的作用:(1)在二层唯一确定一台设备(2)使同一网络的不同设备可以通信2.同构设备使用交叉线,异构设备使用直通线PC to switch 是异构设备1236,1236PC to router,server to router 同构设备1236,36123.OSI网络层中routing提供了路径选择和流量转发,通过手动或者动态学习路由条目实现。
4.mac地址的前24位称为唯一标识(OUI),也就是固定分配的。
5.相同设备用crossover,不同设备用cut-thought,console使用的是roller线缆6.路由器一个端口一个broadcast交换机一个端口一个冲突域集线机一个冲突域7.fiber-option:1000base-cx 25米100base-fx 100米1000base-sx 550米1000base-lx 3000米1000base-zx 70km8.使用router进行network的分割作用:(1)可以基于层三的信息过滤数据(2)广播不会穿越路由器二.1.流控制有哪些:(1).buffering缓存(2).windowing窗口机制(3).congestion avoidance拥塞避免2.SSH 为建立在应用层和传输层基础上的安全协议。
SSH 是目前较可靠,专为远程登录会话和其它网络服务提供安全性的协议。
3.TCP/UDP端口的使用:FTP 21端口TELNET 23端口SMTP 25端口简单邮件传输协议DNS53端口HTTP 80端口POP3 110端口4.DHCP的主要作用是想主机提供地址租约lease,并定期联系DHCP Server重新续约5.ICMP是网络层,第三层三.1.10.0.0.0/8-10.255.255.255/8172.16.0.0/16-172.31.255.255/16192.168.0.0/24-192.168.255.255/24为私有IP2.4.1-5.1-6.1-7.1-8.1172.25.32 64 96 108四.1.串口通过keepalive来保活端口,协议层down通常是时钟,封装,线缆使用不对造成。
CCNA认证精彩试题中文+问题详解

CCNA认证试题一(附答案和解析)中文版(一)1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住IEEE802.1-------IEEE802.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C***A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术与信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE定义的标准在工业界有极大的影响。
下面列出:IEEE802.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-X(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ()(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:11000000.10101000.00010011.1111111111111111.11111111.11110000.00000000主机位变成全0表示这个IP的网络地址主机槐涑扇?表示这个IP的广播地址RFC1918文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefix)172.16.0.0 - 172.31.255.255 (172.16/ 12 prefix)192.168.0.0 - 192.168.255.255 (192.168/16 prefix)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?()(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
完整版CCNA测试题库及答案

完整版CCNA测试题库及答案描述载波侦听多路由访问/冲突检测(CSMA/CD)的工作原理。
CSMA/CD是一种帮助设备均衡共享带宽的协议,可避免两台设备同时在网络介质上传输数据。
虽然他不能消除冲突,但有助于极大的减少冲突,进而避免重传,从而提高所的设备的数据传输效率。
区分半双工和全双工通信。
并指出两种方法的需求。
与半双工以太网使用一对导线不同,全双工以太网使用两队导线,全双工使用不同的导线来消除冲突,从而允许同时发送和接收数据,而半双工可接收或发送数据,但不能同时接收和发送数据,且仍会出现冲突。
要使用全双工,电缆两端的设备都必须支持全双工,并配置成一全双模式运行。
描述MAC地址的组成部分以及各部分包含的信息。
MAC(硬件)地址时一种使用十六进制表示的地址,长48位(6B)。
其中前24位(3B)称为OUI(Organizationally Unique Idebtifier,组织唯一表示符),有IEEE分配给NIC制造商;余下的部分呢唯一地标识了NIC识别十进制数对应的二进制值和十六进制值。
用这三种格式之一表示的任何数字都可以转换为其他两种格式,能够执行这种转换对理解IP地址和子网划分至关重要。
识别以太网帧中与数据链路层相关的字段。
在以太网中,与数据链路层相关的字段包括前导码,帧其实位置分隔符,目标MAC地址,源MAC地址,长度或者类型以及帧校验序列。
识别以太网布线相关的IEEE标准。
这些标准描述了各种电缆类型的功能和物理特征,包括(但不限于)10Base2、10Base5和10BaseT。
区分以太网电缆类型及其用途。
以太网电缆分3种:直通电缆,用于将PC或路由器的以太网接口连接到集线器或交换机;交叉电缆。
用于将集线器连接到集线器,集线器连接到交换机,交换机连接到交换机以及PC连接到PC;反转电缆,用于PC和路由器或交换机之间建立控制台连接。
描述数据封装过程及其在分组创建中的作用。
数据封装指的是在OSI模型各层给数据添加信息的过程,也成为分组创建。
CCNA基础知识考题汇总.doc

1、OSI模型包括哪7层?答:从上到下分别为:应用层、表示层、会话层、传输层、网络层、数据链路层、物理层2、TCP/IP模型包括哪4层?答:从上到下分别为:过程/应用层、主机到主机层、因特网层、网络接入层3、思科组网模型包括哪3层?答:核心层、汇聚层、接入层4、TCP与UDP有何区别?答:1. TCP是基于全双工的、血向连接的、可靠传输协议,而UDP是无连接、不可靠传输协议。
2、TCP采用的是虚电路方式,而UDP不采用虚电路。
3、TCP的数据段格式与UDP的数据段格式不一样4、TCP含有窗口流量控制,而UDP没有5、TCP如何实现传输的可靠性?答:建立起虚电路连接的“三次握手”原则这是由于TCP的数据段格式而决定了TCP能进行面向连接的可靠传输。
6、DHCP服务提供了哪些内容?答:IP地址、子网掩码、域名、默认网关、DNS. WINS信息Windows杳看木机ARP信息的命令是什么?答:arp-a7、Windows跟踪路径的命令是什么?答:Traceroute8、Windows长ping并改变包大小的命令是什么?答:ping -1 size +ip 地址.9、Windows 5看木机路由表的命令是什么?答:show ip route10、IP地址分成哪两个部分?答:ip地址分成主机地址和网络地址11、如何快速计算某个IP所在的网络地址及广播地址?答:划分了网就需要计算了网掩码和分配相应的主机块,采用十进制计算方法。
12、VLSM及Cl DR的全称是什么?答:VLSM是变长了网掩码;CIDR是无类的内部域路由13、WWW、FTP、DNS、Telnets POP3、SMTP、远程桌面这些应用分别使用的TCRUDP的哪些端口?答: www端口: 80> ftp 端口: 21 dns 端口: 53telnet 端口: 23 pop3 端口: 110 smtp 端口: 25 windows终端(远程桌面)端口: 338914、电脑对路由器交换机输入配置命令的途径有哪两种?15、笔记木电脑上没有OOM端口时如何连接路由器交换机的console 口?答:用一个USB转换com端口器16、路由器模拟成PC需要哪些配置?答:router (config) #no ip routingrouter (config) #ip default-gateway *・*.*.*router(config)#int f*/*router (conf ig-if)#ip address *.*.*.*. (了网掩码)*.*.*.*router(confi-if)#no shutdown17、静态路由有哪两种写法?答:1、router (config) #ip route (目的地址)*.*.*.* (子网掩码)*.*.*.* (下一跳地址)*. *. *. *2、Router (config) #ip route (0 的地址)*.*.*.* (了网掩码)*.*.*.* (本路由器的夕卜出接口)f*/*18、如何配置/32的主机静态路由?19、静态路由、RIP、日GRP、OSPF的默认管理距离是多少?答:静态路由的ad是1 rip的ad是120 eigrp的ad是90 ospf的ad是11020、默认路由和静态路由并存时,如何选路?答:静态21、静态路由配置后,进入路由表的条件是什么?答:1、接口存在,并且是激活的;2、下一跳可达22、PC-R1-R2-R3-Server,为了让PC访问Server, 3台路由雅最少共需要配置儿条静态路由?答:至少4条静态路由23、静态路由如何修改管理距离?答:ip route目地ip地址了网掩码下一跳地址/本地出接口后直接加要修改的AD号(0-255)24、RIP、EIGRP、OSPF的全称分别是什么?答:路由信息协议、增强内部网关路由协议、开放最短路径优先25、RIP协议属于哪种类型的路由协议,这种类型的路由协议有何特点?答:属于动态路由协议;其特点是能较好地适应网络状态的变化,但实现起来较为复杂, 开销也比较大。
思科ccna复习题
思科ccna复习题思科CCNA复习题是许多IT从业者在准备网络认证考试时面临的重要挑战。
CCNA(Cisco Certified Network Associate)认证是全球范围内最受认可的网络认证之一,它涵盖了网络基础知识、路由和交换技术、网络安全、无线网络等方面的内容。
在复习CCNA考试的过程中,掌握并解答复习题是一种非常有效的学习方法。
本文将介绍一些常见的CCNA复习题,并给出相应的解答和解析。
一、网络基础知识1. 什么是IP地址?IP地址有几种类型?答:IP地址是用于标识网络上设备(如计算机、路由器等)的一串数字。
IP地址分为IPv4和IPv6两种类型。
IPv4使用32位二进制数表示,通常以四个十进制数表示,每个数的取值范围是0-255。
IPv6使用128位二进制数表示,通常以八组四位十六进制数表示。
2. 什么是子网掩码?如何计算子网掩码?答:子网掩码是用于划分IP地址的网络部分和主机部分的一串二进制数。
计算子网掩码的方法是将IP地址中网络部分的位全部设置为1,主机部分的位全部设置为0。
例如,对于IP地址192.168.0.1,如果要将前24位作为网络部分,剩余8位作为主机部分,那么子网掩码为255.255.255.0。
二、路由和交换技术1. 什么是路由器?它的作用是什么?答:路由器是一种网络设备,用于在不同的网络之间传输数据包。
它通过查找路由表,将数据包从源地址传输到目标地址。
路由器的作用是实现不同网络之间的互联和数据转发。
2. 什么是交换机?与路由器有何区别?答:交换机是一种网络设备,用于在局域网内传输数据包。
它通过学习MAC地址,将数据包从源地址传输到目标地址。
交换机与路由器的区别在于作用范围不同,交换机只能在局域网内传输数据,而路由器可以在不同网络之间传输数据。
三、网络安全1. 什么是防火墙?它的作用是什么?答:防火墙是一种网络安全设备,用于监控和控制网络数据流。
它通过过滤、检测和阻止不安全的网络流量,保护网络免受未经授权的访问、攻击和数据泄露。
新10月CCNA题库word版1~100题共24页
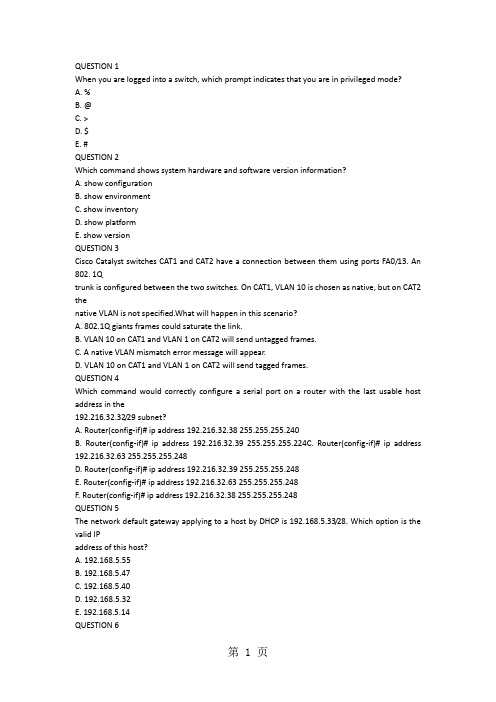
QUESTION 1When you are logged into a switch, which prompt indicates that you are in privileged mode?A. %B. @C. >D. $E. #QUESTION 2Which command shows system hardware and software version information?A. show configurationB. show environmentC. show inventoryD. show platformE. show versionQUESTION 3Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802. 1Qtrunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 thenative VLAN is not specified.What will happen in this scenario?A. 802.1Q giants frames could saturate the link.B. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send untagged frames.C. A native VLAN mismatch error message will appear.D. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send tagged frames.QUESTION 4Which command would correctly configure a serial port on a router with the last usable host address in the192.216.32.32/29 subnet?A. Router(config-if)# ip address 192.216.32.38 255.255.255.240B. Router(config-if)# ip address 192.216.32.39 255.255.255.224C. Router(config-if)# ip address 192.216.32.63 255.255.255.248D. Router(config-if)# ip address 192.216.32.39 255.255.255.248E. Router(config-if)# ip address 192.216.32.63 255.255.255.248F. Router(config-if)# ip address 192.216.32.38 255.255.255.248QUESTION 5The network default gateway applying to a host by DHCP is 192.168.5.33/28. Which option is the valid IPaddress of this host?A. 192.168.5.55B. 192.168.5.47C. 192.168.5.40D. 192.168.5.32E. 192.168.5.14QUESTION 6Which two addresses can be assigned to a host with a subnet mask of 255.255.254.0? (Choose two.)A. 113.10.4.0B. 186.54.3.0C. 175.33.3.255D. 26.35.2.255E. 17.35.36.0QUESTION 7The network administrator has asked you to check the status of the workstation's IP stack by pinging theloopback address. Which address would you ping to perform this task?A. 10.1.1.1B. 127.0.0.1C. 192.168.0.1D. 239.1.1.1QUESTION 8Workstation A has been assigned an IP address of 192.0.2.24/28. Workstation B has been assigned an IPaddress of 192.0.2.100/28. The two workstations are connected with a straight-through cable. Attempts toping between the hosts are unsuccessful. What two things can be done to allow communications betweenthe hosts? (Choose two.)A. Replace the straight-through cable with a crossover cable.B. Change the subnet mask of the hosts to /25.C. Change the subnet mask of the hosts to /26.D. Change the address of Workstation A to 192.0.2.15.E. Change the address of Workstation B to 192.0.2.111.QUESTION 9Your ISP has given you the address 223.5.14.6/29 to assign to your router's interface. They have alsogiven you the default gateway address of 223.5.14.7. After you have configured the address, the router isunable to ping any remote devices. What is preventing the router from pinging remote devices?A. The default gateway is not an address on this subnet.B. The default gateway is the broadcast address for this subnet.C. The IP address is the broadcast address for this subnet.D. The IP address is an invalid class D multicast address.QUESTION 10Which command is used to copy the configuration from RAM into NVRAM?A. copy running-config startup-configB. copy startup-config: running-config:C. copy running config startup configD. copy startup config running configE. write terminalQUESTION 11Which command is used to load a configuration from a TFTP server and merge the configuration intoRAM?A. copy running-config: TFTP:B. copy TFTP: running-configC. copy TFTP: startup-configD. copy startup-config: TFTP:QUESTION 12A system administrator types the command to change the hostname of a router. Where on the Cisco IFS isthat change stored?A. NVRAMB. RAMC. FLASHD. ROME. PCMCIAQUESTION 13Which command is used to configure a default route?A. ip route 172.16.1.0 255.255.255.0 0.0.0.0B. ip route 172.16.1.0 255.255.255.0 172.16.2.1C. ip route 0.0.0.0 255.255.255.0 172.16.2.1D. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 14If IP routing is enabled, which two commands set the gateway of last resort to the default gateway?(Choose two.)A. ip default-gateway 0.0.0.0B. ip route 172.16.2.1 0.0.0.0 0.0.0.0C. ip default-network 0.0.0.0D. ip default-route 0.0.0.0 0.0.0.0 172.16.2.1E. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 15Which command would you configure globally on a Cisco router that would allow you to view directlyconnected Cisco devices?A. enable cdpB. cdp enableC. cdp runD. run cdpQUESTION 16Which command is used to see the path taken by packets across an IP network?A. show ip routeB. show routeC. tracerouteD. trace ip routeQUESTION 17Which command is used to debug a ping command?A. debug icmpB. debug ip icmpC. debug tcpD. debug packetQUESTION 18Which command displays CPU utilization?A. show protocolsB. show processC. show systemD. show versionQUESTION 19When configuring a serial interface on a router, what is the default encapsulation?A. atm-dxiB. frame-relayC. hdlcD. lapbE. pppQUESTION 20What must be set correctly when configuring a serial interface so that higher-level protocols calculate thebest route?A. bandwidthB. delayC. loadD. reliabilityQUESTION 21A company implements video conferencing over IP on their Ethernet LAN. The users notice that thenetwork slows down, and the video either stutters or fails completely. What is the most likely reason forthis?A. minimum cell rate (MCR)B. quality of service (QoS)C. modulationD. packet switching exchange (PSE)E. reliable transport protocol (RTP)QUESTION 22Which layer in the OSI reference model is responsible for determining the availability of the receivingprogram and checking to see if enough resources exist for that communication?A. transportB. networkC. presentationD. sessionE. applicationQUESTION 23Data transfer is slow between the source and destination. The quality of service requested by the transportlayer in the OSI reference model is not being maintained. To fix this issue, at which layer should thetroubleshooting process begin?A. presentationB. sessionC. transportD. networkE. physicalQUESTION 24Which protocols are found in the network layer of the OSI reference model and are responsible for pathdetermination and traffic switching?A. LANB. routingC. WAND. networkQUESTION 25Which command reveals the last method used to powercycle a router?A. show reloadB. show bootC. show running-configD. show versionQUESTION 26Which three options are valid WAN connectivity methods? (Choose three.)A. PPPB. WAPC. HDLCD. MPLSE. L2TPv3CCNA考试报名1700元7F. ATMQUESTION 27Refer to the exhibit. Which WAN protocol is being used?A. ATMB. HDLCC. Frame RelayD. PPPQUESTION 28What is the difference between a CSU/DSU and a modem?A. A CSU/DSU converts analog signals from a router to a leased line; a modem converts analog signalsfrom a router to a leased line.B. A CSU/DSU converts analog signals from a router to a phone line; a modem converts digital signalsfrom a router to a leased line.C. A CSU/DSU converts digital signals from a router to a phone line; a modem converts analog signalsfrom a router to a phone line.D. A CSU/DSU converts digital signals from a router to a leased line; a modem converts digital signalsfrom a router to a phone line.QUESTION 29A network administrator must configure 200 switch ports to accept traffic from only the currently attachedCCNA考试报名1700元8host devices. What would be the most efficient way to configure MAC-level security on all these ports?A. Visually verify the MAC addresses and then telnet to the switches to enter the switchport-port securitymac-address command.B. Have end users e-mail their MAC addresses. Telnet to the switch to enter the switchport-port securitymac-address command.C. Use the switchport port-security MAC address sticky command on all the switch ports that have enddevices connected to them.D. Use show mac-address-table to determine the addresses that are associated with each portand thenenter the commands on each switch for MAC address port-security.QUESTION 30When troubleshooting a Frame Relay connection, what is the first step when performing a loopback test?A. Set the encapsulation of the interface to HDLC.B. Place the CSU/DSU in local-loop mode.C. Enable local-loop mode on the DCE Frame Relay router.D. Verify that the encapsulation is set to Frame Relay.What occurs on a Frame Relay network when the CIR is exceeded?A. All TCP traffic is marked discard eligible.B. All UDP traffic is marked discard eligible and a BECN is sent.C. All TCP traffic is marked discard eligible and a BECN is sent.D. All traffic exceeding the CIR is marked discard eligible.QUESTION 32What are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two.)A. They create split-horizon issues.B. They require a unique subnet within a routing domain.C. They emulate leased lines.D. They are ideal for full-mesh topologies.E. They require the use of NBMA options when using OSPF.QUESTION 33Refer to the exhibit. Addresses within the range 10.10.10.0/24 are not being translated to the 1.128.0/16range. Which command shows if 10.10.10.0/24 are allowed inside addresses?A. debug ip natB. show access-listC. show ip nat translationD. show ip nat statisticsQUESTION 34A wireless client cannot connect to an 802.11b/g BSS with a b/g wireless card. The client section of theaccess point does not list any active WLAN clients. What is a possible reason for this?A. The incorrect channel is configured on the client.B. The client's IP address is on the wrong subnet.C. The client has an incorrect pre-shared key.D. The SSID is configured incorrectly on the client.QUESTION 35Which two features did WPAv1 add to address the inherent weaknesses found in WEP? (Choose two.)CCNA考试报名1700元10艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyA. a stronger encryption algorithmB. key mixing using temporal keysC. shared key authenticationD. a shorter initialization vectorE. per frame sequence countersQUESTION 36Which two wireless encryption methods are based on the RC4 encryption algorithm? (Choose two.)A. WEPB. CCKMC. AESD. TKIPE. CCMPQUESTION 37What are two characteristics of RIPv2? (Choose two.)A. classful routing protocolB. variable-length subnet masksC. broadcast addressingD. manual route summarizationE. uses SPF algorithm to compute pathQUESTION 38Which two Ethernet fiber-optic modes support distances of greater than 550 meters?A. 1000BASE-CXCCNA考试报名1700元11艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyB. 100BASE-FXC. 1000BASE-LXD. 1000BASE-SXE. 1000BASE-ZXQUESTION 39What two things will a router do when running a distance vector routing protocol? (Choose two.)A. Send periodic updates regardless of topology changes.B. Send entire routing table to all routers in the routing domain.C. Use the shortest-path algorithm to the determine best path.D. Update the routing table based on updates from their neighbors.E. Maintain the topology of the entire network in its database.QUESTION 40Refer to the exhibit. According to the routing table, where will the router send a packet destined for10.1.5.65?A. 10.1.1.2B. 10.1.2.2C. 10.1.3.3D. 10.1.4.4QUESTION 41Which command shows if an access list is assigned to an interface?A. show ip interface [interface] access-listsB. show ip access-lists interface [interface]C. show ip interface [interface]D. show ip access-lists [interface]QUESTION 42Refer to the exhibit. Which rule does the DHCP server use when there is an IP address conflict?A. The address is removed from the pool until the conflict is resolved.B. The address remains in the pool until the conflict is resolved.C. Only the IP detected by Gratuitous ARP is removed from the pool.D. Only the IP detected by Ping is removed from the pool.E. The IP will be shown, even after the conflict is resolved.QUESTION 43Refer to the exhibit. You are connected to the router as user Mike. Which command allows you to seeoutput from the OSPF debug command?A. terminal monitorB. show debuggingC. show sessionsD. show ip ospf interfaceQUESTION 44Refer to the exhibit. If number 2 is selected from the setup script, what happens when the user runs setupfrom a privileged prompt?A. Setup is additive and any changes will be added to the config script.B. Setup effectively starts the configuration over as if the router was booted for the first time.C. Setup will not run if an enable secret password exists on the router.D. Setup will not run, because it is only viable when no configuration exists on the router. QUESTION 45Refer to the exhibit. Which (config-router) command will allow the network represented on the interface tobe advertised by RIP?A. redistribute ethernet0B. network ethernet0CCNA考试报名1700元14艾迪飞论坛http://bbs.edify艾迪飞论坛http://bbs.edifyC. redistribute 10.12.0.0D. network 10.12.0.0QUESTION 46Refer to the exhibit. What information can be gathered from the output?A. One router is running RIPv1.B. RIP neighbor is 224.0.0.9.C. The network contains a loop.D. Network 10.10.1.0 is reachable.QUESTION 47Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to routerD. router to routerQUESTION 48Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to switchD. switch to routerQUESTION 49Which two statements describe the Cisco implementation of VLANs? (Choose two.)A. VLAN 1 is the default Ethernet VLAN.B. CDP advertisements are only sent on VLAN 1002.C. By default, the management VLAN is VLAN 1005.D. By default, the switch IP address is in VLAN 1005.E. VLAN 1002 through 1005 are automatically created and cannot be deleted.QUESTION 50Refer to the exhibit. What can be determined about the router from the console output?A. No configuration file was found in NVRAM.B. No configuration file was found in flash.C. No configuration file was found in the PCMCIA card.D. Configuration file is normal and will load in 15 seconds.QUESTION 52Refer to the exhibit. Which command would allow the translations to be created on the router?A. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 19B. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 19C. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 18D. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 18QUESTION 53Refer to the exhibit. An administrator pings the default gateway at 10.10.10.1 and sees the output asshown. At which OSI layer is the problem?A. data link layerB. application layerC. access layerD. session layerE. network layerQUESTION 54Refer to the exhibit. Which value will be configured for Default Gateway of the Local Area Connection?A. 10.0.0.0B. 10.0.0.254C. 192.223.129.0D. 192.223.129.254QUESTION 55Refer to the exhibit. The user at Workstation B reports that Server A cannot be reached. What is preventing Workstation B from reaching Server A?A. The IP address for Server A is a broadcast address.B. The IP address for Workstation B is a subnet address.C. The gateway for Workstation B is not on the same subnet.D. The gateway for Server A is not on the same subnet.QUESTION 56Refer to the exhibit. What does the (*) represent in the output?A. Packet is destined for a local interface to the router.B. Packet was translated, but no response was received from the distant device.C. Packet was not translated, because no additional ports are available.D. Packet was translated and fast switched to the destination.QUESTION 57Refer to the exhibit. What command sequence will enable PAT from the inside to outside network?A. (config) ip nat pool isp-net 1.2.4.2 netmask 255.255.255.0 overloadB. (config-if) ip nat outside overloadC. (config) ip nat inside source list 1 interface ethernet1 overloadD. (config-if) ip nat inside overloadQUESTION 58Refer to the exhibit. What will happen to HTTP traffic coming from the Internet that is destined for172.16.12.10 if the traffic is processed by this ACL?A. Traffic will be dropped per line 30 of the ACL.B. Traffic will be accepted per line 40 of the ACL.C. Traffic will be dropped, because of the implicit deny all at the end of the ACL.D. Traffic will be accepted, because the source address is not covered by the ACL.QUESTION 59Refer to the exhibit. Which statement describes the effect that the Router1 configuration has on devices inthe 172.16.16.0 subnet when they try to connect to SVR-A using Telnet or SSH?A. Devices will not be able to use Telnet or SSH.B. Devices will be able to use SSH, but not Telnet.C. Devices will be able to use Telnet, but not SSH.D. Devices will be able to use Telnet and SSH.QUESTION 60What are three advantages of VLANs? (Choose three.)A. VLANs establish broadcast domains in switched networks.B. VLANs utilize packet filtering to enhance network security.C. VLANs provide a method of conserving IP addresses in large networks.D. VLANs provide a low-latency internetworking alternative to routed networks.E. VLANs allow access to network services based on department, not physical location.F. VLANs can greatly simplify adding, moving, or changing hosts on the network.QUESTION 61An administrator would like to configure a switch over a virtual terminal connection from locations outsideof the local LAN. Which of the following are required in order for the switch to be configured from a remotelocation? (Choose two.)A. The switch must be configured with an IP address, subnet mask, and default gateway.B. The switch must be connected to a router over a VLAN trunk.C. The switch must be reachable through a port connected to its management VLAN.D. The switch console port must be connected to the Ethernet LAN.E. The switch management VLAN must be created and have a membership of at least one switch port.F. The switch must be fully configured as an SNMP agent.QUESTION 62Which of the following host addresses are members of networks that can be routed across the publicInternet? (Choose three.)A. 10.172.13.65B. 172.16.223.125C. 172.64.12.29D. 192.168.23.252E. 198.234.12.95F. 212.193.48.254QUESTION 63Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to networkhosts? (Choose three.)A. 15.234.118.63B. 92.11.178.93C. 134.178.18.56D. 192.168.16.87E. 201.45.116.159F. 217.63.12.192QUESTION 64Which of the following are benefits of VLANs? (Choose three.)A. They increase the size of collision domains.B. They allow logical grouping of users by function.C. They can enhance network security.D. They increase the size of broadcast domains while decreasing the number of collision domains.E. They increase the number of broadcast domains while decreasing the size of the broadcast domains.F. They simplify switch administration.Which router IOS commands can be used to troubleshoot LAN connectivity problems? (Choose three.)A. pingB. tracertC. ipconfigD. show ip routeE. winipcfgF. show interfacesQUESTION 67。
CCNA考试题
C C N A考试题(总9页) -CAL-FENGHAI.-(YICAI)-Company One1-CAL-本页仅作为文档封面,使用请直接删除第一部分:选择题1:提供可靠数据传输、流控的是OSI的第几层()A、表示层B、网络层C、传输层D、会话层E、链路层2:子网掩码产生在那一层()A、表示层B、网络层C、传输层D、会话层3:当路由器接收的IP报文的目的地址不是本路由器的接口IP地址,并且在路由表中未找到匹配的路由项,采取的策略是()A、丢掉该分组B、将该分组分片C、转发该分组D、以上答案均不对4:当一台主机从一个网络移到另一个网络时,以下说法正确的是()A、必须改变它的IP地址和MAC地址B、必须改变它的IP地址,但不需改动MAC地址C、必须改变它的MAC地址,但不需改动IP地址D、MAC地址、IP地址都不需改动5:ISO提出OSI的关键是()A、系统互联B、提高网络速度C、为计算机制定标准D、经济利益6:OSI参考模型按顺序有哪些层()A、应用层、传输层、网络层、物理层B、应用层、表示层、会话层、网络层、传输层、数据链路层、物理层C、应用层、表示层、会话层、传输层、网络层、数据链路层、物理层D、应用层、会话层、传输层、物理层7:LAN的拓扑形式一般以()为主。
A、总线型B、环型C、令牌环D、载波侦听与冲突检测CSMA/CD8:网段地址154.27.0.0的网络,若不做子网划分,能支持()台主机A、254B、1024C、65,534D、16,777,2069:路由器网络层的基本功能是()。
A、配置IP地址B、寻找路由和转发报文C、将MAC地址解释成IP地址10:选出基于TCP协议的应用程序()。
A、PINGB、TFTPC、TELNETD、OSPF11:某公司申请到一个C类IP地址,但要连接6个的子公司,最大的一个子公司有26台计算机,每个子公司在一个网段中,则子网掩码应设为()。
A、255.255.255.0B、255.255.255.128C、255.255.255.192D、255.255.255.22412:B类地址的缺省掩码是()。
CCNA新版题库知识点总结_CCNA(200-120)_CCNA新版题库
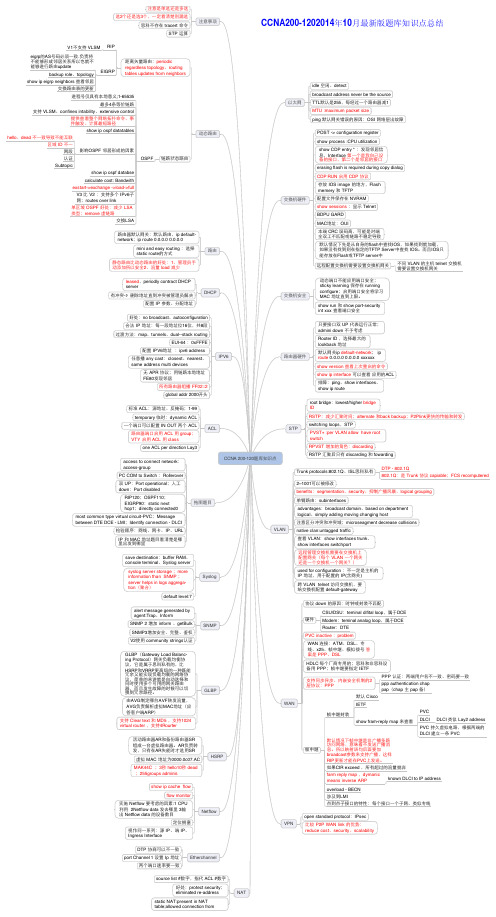
只要接口口双 UP 代表运行行正常; admini down 不予考虑
Rooter ID ,选择最大大的 lookback 地址
默认⺴网网关ip default-network; ip route 0.0.0.0 0.0.0.0 xxxxxx
show version 查看上次重启的命令
show ip interface 可以查看 应用用的ACL
好处:protect security; eliminated re-address
static NAT:present in NAT table;allowed connection from
PVC 持久虚拟电路,根据两端的 DLCI 建立立一一条 PVC
如果CIR exceed ,所有超过的流量抛弃
farm reply map ,dymanic
means inverse ARP
known DLCI to IP address
overload - BECN 涉及到LMI 点到点子子接口口的特性:每个接口口一一个子子⺴网网、类似专线
注意是单选还是多选 选2个还是选3个,一一定看清楚别漏选
思科不存在 tracert 命令 STP 运算
注意事项
本页已使用福昕阅读器进行编辑。 福昕软件(C)2005-2009,版权所有, 仅供试用。
CCNA200-1202014年10月最新版题库知识点总结
V1不支支持 VLSM RIP
eigrp的AS号码必须一一致.负责将 不能够形成邻居关系所以也就不 能够进行行路由update
远程配置交换机需要设置交换机⺴网网关
不同 VLAN 的主机 telnet 交换机 需要设置交换机⺴网网关
leased,periodly contract DHCP server
CCNA第一学期各章知识题及答案解析
诶了我累了目录第二章网络通信P2-8第三章应用层功能及协议P9-14 第四章OSI传输层P15-20第五章OSI网络层P21-27第六章网络编址-IPv4 P28-34第七章数据链路层P35-40第八章OSI物理层P41-45第九章以太网P46-51第十章网络规划和布线P52-61 第十一章配置和测试网络P62-70 第一学期末考试P71-91文档末尾返回目录第二章网络通信001 TCP/IP 网络接入层有何作用?路径确定和数据包交换数据表示、编码和控制可靠性、流量控制和错误检测详细规定构成物理链路的组件及其接入方法将数据段划分为数据包002下列哪些陈述正确指出了中间设备在网络中的作用?(选择三项)确定数据传输路径发起数据通信重新定时和重新传输数据信号发送数据流管理数据流数据流最后的终止点003下列哪三项陈述是对局域网(LAN) 最准确的描述?(选择三项)LAN 通常位于一个地域内。
此类网络由由一个组织管理。
LAN 中的不同网段之间一般通过租用连接的方式连接。
此类网络的安全和访问控制由服务提供商控制。
LAN 为同一个组织内的用户提供网络服务和应用程序访问。
此类网络的每个终端通常都连接到电信服务提供商(TSP)。
004 什么是PDU?传输期间的帧损坏在目的设备上重组的数据因通信丢失而重新传输的数据包特定层的封装005 OSI 模型哪两层的功能与TCP/IP 模型的网络接入层相同?(选择两项)网络层传输层物理层数据链路层会话层006请参见图示。
所示网络属于哪一类型?WANMANLANWLAN007 以下哪种特征正确代表了网络中的终端设备?管理数据流发送数据流重新定时和重新传输数据信号确定数据传输路径008 第4 层端口指定的主要作用是什么?标识本地介质中的设备标识源设备和目的设备之间的跳数向中间设备标识通过该网络的最佳路径标识正在通信的源终端设备和目的终端设备标识终端设备内正在通信的进程或服务009 请参见图示。
CISCOCCNA网络工程师题库

培训大讲堂官方YY 频道:3660mCCNA题库考试代号: 640-802考试时间:英文110+30=140分钟通过分数: 825鸿鹄论坛招募CCNA、CCNP答疑讲师答疑地点:鸿鹄官方YY频道3660V104系列是官方的终结版本,以后不会再出V105 V106 V108等等========================================更新内容:增加5道新题,分别是519、520、521、522、523题修改176题、375题、443题、482题答案错误修改59题、88题、453题、107题、270题注释错误增加个别疑难拖图题注释,优化实验题=============================================QUESTION 1When you are logged into a switch, which prompt indicates that you are in privileged mode(当您登录到交换机,哪种提示表明你在特权模式?)A. %B. @C. >D. $E. #Answer: ESection: Chapter 4: Introduction to Cisco IOSExplanation/Reference:特权模式就是#提示符QUESTION 2Which command shows system hardware and software version information(哪些命令显示系统硬件和软件的版本信息?)A. show configurationB. show environmentC. show inventoryD. show platformE. show versionAnswer: ESection: Chapter 4: Introduction to Cisco IOSExplanation/Reference:查看系统的软件和硬件信息使用的命令是show versionQUESTION 3Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802. 1Q trunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 the(思科Catalyst 交换机CAT1 和CAT2 有它们之间的连接使用端口FA0/13。
ccna考试题及答案
ccna考试题及答案1. 以下哪项是网络层的功能?A. 路由选择B. 错误检测C. 流量控制D. 封装数据包答案:A2. 在OSI模型中,哪一层负责在网络中传输数据?A. 应用层B. 传输层C. 会话层D. 网络层答案:D3. 以下哪个协议是用于在IP网络中发现网络设备的?A. ARPB. RARPC. ICMPD. OSPF答案:A4. 在TCP/IP模型中,哪一层与OSI模型的传输层相对应?A. 应用层B. 互联网层C. 网络接口层D. 传输层答案:D5. 以下哪个地址是一个有效的IPv4地址?A. 192.168.1.256B. 192.168.1.1C. 10.0.0.0D. 172.16.300.1答案:B6. 在配置路由器时,以下哪个命令用于进入全局配置模式?A. enableB. configure terminalC. privileged execD. user exec答案:B7. 以下哪个命令用于在Cisco设备上显示当前配置?A. show running-configB. show startup-configC. show configD. show current-config答案:A8. 在Cisco设备上,以下哪个命令用于保存当前的配置到启动配置文件?A. copy running-config startup-configB. copy startup-config running-configC. save running-configD. save startup-config答案:A9. 以下哪个命令用于在Cisco设备上查看所有接口的状态?A. show interfacesB. show ip interface briefC. show interface statusD. show running-config interface答案:B10. 在Cisco设备上,以下哪个命令用于关闭接口?A. shutdownB. no shutdownC. disableD. no enable答案:A11. 以下哪个命令用于在Cisco设备上启用接口?A. shutdownB. no shutdownC. disableD. no enable答案:B12. 在配置静态路由时,以下哪个命令用于指定下一跳地址?B. ip static-routeC. route ipD. static-route ip答案:A13. 以下哪个命令用于在Cisco设备上清除ARP表?A. clear arp-cacheB. clear arpC. clear arp tableD. clear ip arp答案:D14. 在配置动态路由协议时,以下哪个命令用于在接口上启用RIP?A. ip rip enableB. ip rip receiveD. network rip答案:C15. 以下哪个命令用于在Cisco设备上查看RIP路由表?A. show ip ripB. show ip route ripC. show ripD. show ip protocols答案:B16. 在配置EIGRP时,以下哪个命令用于指定自动汇总?A. metric weightsB. auto-summaryC. network auto-summaryD. no auto-summary答案:B17. 以下哪个命令用于在Cisco设备上查看EIGRP邻居?A. show ip eigrp neighborsB. show eigrp neighborsC. show ip eigrpD. show eigrp interfaces答案:A18. 在配置OSPF时,以下哪个命令用于指定路由器ID?A. router-idB. router ospfC. networkD. area答案:A19. 以下哪个命令用于在Cisco设备上查看OSPF路由表?A. show ip ospfB. show ip ospf databaseC. show ospfD. show ip route ospf答案:D20. 在配置VLAN时,以下哪个命令用于创建一个新的VLAN?A. vlan databaseB. configure terminalC. vlan [vlan-id]D. new-vlan答案:C21. 以下哪个命令用于将接口分配给VLAN?A. switchport mode accessB. switchport mode trunkC. switchport access vlan [vlan-id]D. switchport trunk vlan [vlan-id]答案:C22. 在配置交换机时,以下哪个命令用于将接口设置为Trunk 模式?A. switchport mode accessB. switchport mode trunkC. switchport access vlan [vlan-id]D. switchport trunk vlan [vlan-id]答案:B23. 以下哪个命令用于在Cisco设备上查看VLAN配置?A. show vlanB. show vlan briefC. show vlan detailD. show vlan all答案:B24. 在配置VTP时,以下哪个命令用于将交换机设置为VTP服务器模式?A. vtp mode serverB. vtp mode clientC. vtp mode transparentD. vtp mode off答案:A25. 以下哪个命令用于在Cisco设备上查看VTP状态?A. show vtp statusB. show vtp statisticsC. show vtp passwordD. show vtp configuration答案:A26. 在配置STP时,以下哪个命令用于设置根桥?A. spanning-tree root primaryB. spanning-tree root secondaryC. spanning-tree root primary [priority]D. spanning-tree root secondary [priority]答案:C27. 以下哪个命令用于在Cisco设备上查看STP状态?A. show spanning-treeB. show spanning-tree detailC. show spanning-tree summaryD. show spanning-tree interface答案:A28. 在配置VLAN Trunking Protocol (VTP) 时,以下哪个命令用于设置VTP域名?A. vtp domain [domain-name]B. vtp password [password]C. vtp mode [mode]D. vtp version [version]答案:A29. 以下哪个命令用于在Cisco设备上查看当前的VTP版本?A. show vtp statusB. show vtp statisticsC. show vtp passwordD. show vtp configuration答案:A30. 在配置端口安全时,以下哪个命令用于限制接口上可以学习到的最大MAC地址数量?A. switchport port-security maximum [mac-count]B. port-security maximum [mac-count]C. switchport port-security violation restrictD. port-security violation shutdown答案:A这些题目和答案仅供学习和参考之用,实际的CCNA考试内容和形式可能会有所不同。
CCNA考试题库中英文翻译版及答案

CCNA考试题库中英⽂翻译版及答案CCNA考试题库中英⽂翻译版及答案1[1]1、 What are two reasons that a network administrator would use access lists? (Choose two、)1、出于哪两种理由,⽹络管理员会使⽤访问列表?A、 to control vty access into a routerA、控制通过VTY访问路由器B、 to control broadcast traffic through a routerB、控制⼴播流量穿越路由器2、⼀个默认得帧中继WAN被分类为哪种物理⽹络类型?A、 point-to-pointA、点到点B、 broadcast multi-accessB、⼴播多路访问C、 nonbroadcast multi-accessC、⾮⼴播多路访问D、 nonbroadcast multipointD、⾮⼴播多点E、 broadcast point-to-multipointE、⼴播点到多点Answer: C3、 A single 802、11g access point has been configured and installed in the center of a squarA few wireless users are experiencing slow performance and drops while most users are oat peak efficiency、 What are three likely causes of this problem? (Choose three、)3、⼀个802、11接⼊点被部署在⼀个⽅形办公室得中央,当⼤多数⽤户在⼤流量传输数⼀些⽆线⽤户发现⽆线⽹络变得缓慢与出现丢包A、 mismatched TKIP encryptionB、 null SSIDC、 cordless phonesD、 mismatched SSIDE、 metalF、 antenna type or directionAnswer: CEF4、 Refer to the exhibit、 How many broadcast domains exist in the exhibited topology?根据下图,图中得拓扑中存在多少个⼴播域?A、 one A、1B、 two B、2C、 three C、3D、 four D、4E、 five E、5F、 six F、6Answer: C5、 Refer to the exhibit、 What two facts can be determined from the WLAN diagram? (Choose two、) 5、根据下图,WLAN diagram决定了哪两个事实A、 The area of overlap of the two cells represents a basic service set (BSS)、A、两个 cells得overlap得区域描述了⼀个basic service setB、 The network diagram represents an extended service set (ESS)、B、⽹络描述了⼀个extended service setC、 Access points in each cell must be configured to use channel 1、C、再每个CELL中得AP必须被配置成使⽤channel 1D、 The area of overlap must be less than 10% of the area to ensure connectivity、D、为了确保连通性,重叠区域必须⼩于10%E、 The two APs should be configured to operate on different channels、E、两个访问点应该被配置成⼯作在不同得频道Answer: BE6、 The command frame-relay map ip 10、121、16、8 102 broadcast was entered on the router、Which of the following statements is true concerning this command?6、路由器上输⼊命令frame-relay map ip 10、121、16、8 102 broadcast,以下选项正确得就是?A、 This command should be executed from the global configuration mode、A、该命令应该在全局配置模式下被执⾏B、 The IP address 10、121、16、8 is the local router port used to forward data、B、IP地址10、121、16、8就是本地路由器⽤来转发数据得接⼝C、 102 is the remote DLCI that will receive the information、C、102就是远端得DLCI它将接受信息。
2011最新10月CCNA题库word版201~300题

QUESTION 201Which two values are used by Spanning Tree Protocol to elect a root bridge? (Choose two.)A. amount of RAMB. bridge priorityC. IOS versionD. IP addressE. MAC addressF. speed of the linksQUESTION 202Refer to the exhibit. Assume that the routing protocol referenced in each choice below is configured with itsdefault settings and the given routing protocol is running on all the routers. Which two conditionalstatements accurately state the path that will be chosen between networks 10.1.0.0 and 10.3.2.0 for therouting protocol mentioned? (Choose two.)A. If OSPF is the routing protocol, the path will be from R1 to R3 to R4 to R5.B. If OSPF is the routing protocol, the path will be from R1 to R2 to R5.C. If OSPF is the routing protocol, the path will be from R1 to R5.D. If RIPv2 is the routing protocol, the path will be from R1 to R3 to R4 to R5.E. If RIPv2 is the routing protocol, the path will be from R1 to R5.QUESTION 203Refer to the exhibit. A network administrator is adding two new hosts to SwitchA. Which three values couldbe used for the configuration of these hosts? (Choose three.)A. host A IP address: 192.168.1.79B. host A IP address: 192.168.1.64C. host A default gateway: 192.168.1.78D. host B IP address: 192.168.1.128E. host B default gateway: 192.168.1.129F. host B IP address: 192.168.1.190QUESTION 204A network administrator changes the configuration register to 0x2142 and reboots the router. What are tworesults of making this change? (Choose two.)A. The IOS image will be ignored.B. The router will prompt to enter initial configuration mode.C. The router will boot to ROM.D. Any configuration entries in NVRAM will be ignored.E. The configuration in flash memory will be booted.QUESTION 205Refer to the exhibit. The networks connected to router R2 have been summarized as a 192.168.176.0/21route and sent to R1. Which two packet destination addresses will R1 forward to R2? (Choosetwo.)A. 192.168.194.160B. 192.168.183.41C. 192.168.159.2D. 192.168.183.255E. 192.168.179.4F. 192.168.184.45QUESTION 206Which three statements are typical characteristics of VLAN arrangements? (Choose three.)A. A new switch has no VLANs configured.B. Connectivity between VLANs requires a Layer 3 device.C. VLANs typically decrease the number of collision domains.D. Each VLAN uses a separate address space.CCNA考试报名1700元99艾迪飞论坛艾迪飞论坛E. A switch maintains a separate bridging table for each VLAN.F. VLANs cannot span multiple switches.QUESTION 207QoS policies are applied on the switches of a LAN. Which type of command will show the effects of thepolicy in real time?A. show commandB. debug commandC. configuration commandD. rommon commandQUESTION 208Which command will show the MAC addresses of stations connected to switch ports?A. show mac-addressB. show arpC. show tableD. show switchportQUESTION 209What is the name of the VTP mode of operation that enables a switch to forward only VTP advertisements while still permitting the editing of local VLAN information?A. serverB. clientC. tunnelD. transparentQUESTION 210Which port state is introduced by Rapid-PVST?A. learningCCNA考试报名1700元100艾迪飞论坛艾迪飞论坛B. listeningC. discardingD. forwardingQUESTION 211What speeds must be disabled in a mixed 802.11b/g WLAN to allow only 802.11g clients to connect?A. 6, 9, 12, 18B. 1, 2, 5.5, 6C. 5.5, 6, 9, 11D. 1, 2, 5.5, 11QUESTION 212Refer to the exhibit. Which VLSM mask will allow for the appropriate number of host addresses for NetworkA?A. /25B. /26C. /27D. /28QUESTION 213Refer to the exhibit. Which subnet mask will place all hosts on Network B in the same subnet with the leastamount of wasted addresses?A. 255.255.255.0B. 255.255.254.0C. 255.255.252.0D. 255.255.248.0QUESTION 214Refer to the exhibit. Which mask is correct to use for the WAN link between the routers that will provideconnectivity while wasting the least amount of addresses?A. /23B. /24C. /25D. /30QUESTION 215Refer to the exhibit. What is the most appropriate summarization for these routes?A. 10.0.0.0 /21B. 10.0.0.0 /22C. 10.0.0.0 /23D. 10.0.0.0 /24QUESTION 216CCNA考试报名1700元102艾迪飞论坛艾迪飞论坛Which two tasks does the Dynamic Host Configuration Protocol perform? (Choose two.)A. Set the IP gateway to be used by the network.B. Perform host discovery used DHCPDISCOVER message.C. Configure IP address parameters from DHCP server to a host.D. Provide an easy management of layer 3 devices.E. Monitor IP performance using the DHCP server.F. Assign and renew IP address from the default pool.QUESTION 217Which two benefits are provided by using a hierarchical addressing network addressing scheme? (Choosetwo.)A. reduces routing table entriesB. auto-negotiation of media ratesC. efficient utilization of MAC addressesD. dedicated communications between devicesE. ease of management and troubleshootingQUESTION 218Which two benefits are provided by creating VLANs? (Choose two.)A. added securityB. dedicated bandwidthC. provides segmentationD. allows switches to route traffic between subinterfacesE. contains collisionsWhich two link protocols are used to carry multiple VLANs over a single link? (Choose two.)A. VTPB. 802.1qC. IGPD. ISLE. 802.3uQUESTION 220Which two protocols are used by bridges and/or switches to prevent loops in a layer 2 network? (Choosetwo.)A. 802.1dB. VTPC. 802.1qD. STPE. SAPQUESTION 221On the network 131.1.123.0/27, what is the last IP address that can be assigned to a host?A. 131.1.123.30B. 131.1.123.31C. 131.1.123.32D. 131.1.123.33QUESTION 222The ip subnet zero command is not configured on a router. What would be the IP address of Ethernet0/0using the first available address from the sixth subnet of the network 192.168.8.0/29?A. 192.168.8.25B. 192.168.8.41C. 192.168.8.49D. 192.168.8.113QUESTION 223For the network 192.0.2.0/23, which option is a valid IP address that can be assigned to a host?A. 192.0.2.0B. 192.0.2.255C. 192.0.3.255D. 192.0.4.0QUESTION 224How many addresses for hosts will the network 124.12.4.0/22 provide?A. 510B. 1022C. 1024D. 2048QUESTION 225Where does routing occur within the DoD TCP/IP reference model?A. applicationB. internetC. networkD. transportWhich VTP mode is capable of creating only local VLANs and does not synchronize with other switches inthe VTP domain?A. clientB. dynamicC. serverD. staticE. transparentQUESTION 227Which switch would STP choose to become the root bridge in the selection process?A. 32768: 11-22-33-44-55-66B. 32768: 22-33-44-55-66-77C. 32769: 11-22-33-44-55-65D. 32769: 22-33-44-55-66-78QUESTION 228A switch is configured with all ports assigned to vlan 2 with full duplex FastEthernet to segment existingdepartmental traffic. What is the effect of adding switch ports to a new VLAN on the switch?A. More collision domains will be created.B. IP address utilization will be more efficient.C. More bandwidth will be required than was needed previously.D. An additional broadcast domain will be created.QUESTION 229Which two statements about the use of VLANs to segment a network are true? (Choose two.)A. VLANs increase the size of collision domains.B. VLANs allow logical grouping of users by function.C. VLANs simplify switch administration.D. VLANs enhance network security.QUESTION 230On corporate network, hosts on the same VLAN can communicate with each other, but they are unable tocommunicate with hosts on different VLANs. What is needed to allow communication between the VLANs?A. a router with subinterfaces configured on the physical interface that is connected to the switchB. a router with an IP address on the physical interface connected to the switchC. a switch with an access link that is configured between the switchesD. a switch with a trunk link that is configured between the switchesQUESTION 231When a DHCP server is configured, which two IP addresses should never be assignable to hosts? (Choosetwo.)A. network or subnetwork IP addressB. broadcast address on the networkC. IP address leased to the LAND. IP address used by the interfacesE. manually assigned address to the clientsF. designated IP address to the DHCP serverQUESTION 232Which statement describes the process of dynamically assigning IP addresses by the DHCP server?A. Addresses are allocated after a negotiation between the server and the host to determine the length ofthe agreement.B. Addresses are permanently assigned so that the hosts uses the same address at all times.C. Addresses are assigned for a fixed period of time, at the end of the period, a new request for anaddress must be made.D. Addresses are leased to hosts, which periodically contact the DHCP server to renew the lease.QUESTION 233Which network protocol does DNS use?A. FTPB. TFTPC. TCPD. UDPE. SCPAnswer: DExplanation/Reference:此题答案并不严格,严格讲DNS有两个端口号一个为TCP一个为UDP并且端口号都为53 DNS解析用UDP 效率高但不能保证完整性DNS服务器之间同步使用TCP保证数据正确QUESTION 234When two hosts are trying to communicate across a network, how does the host originating the communication determine the hardware address of the host that it wants to "talk" to?A. RARP requestB. Show Network Address requestC. Proxy ARP requestD. ARP requestE. Show Hardware Address requestQUESTION 235Host 1 is trying to communicate with Host 2. The e0 interface on Router C is down. Which of the followingare true? (Choose two.)CCNA考试报名1700元107艾迪飞论坛艾迪飞论坛A. Router C will use ICMP to inform Host 1 that Host 2 cannot be reached.B. Router C will use ICMP to inform Router B that Host 2 cannot be reached.C. Router C will use ICMP to inform Host 1, Router A, and Router B that Host 2 cannot be reached.D. Router C will send a Destination Unreachable message type.E. Router C will send a Router Selection message type.F. Router C will send a Source Quench message typeQUESTION 236To configure the VLAN trunking protocol to communicate VLAN information between two switches, whattwo requirements must be met? (Choose two.)A. Each end of the trunk line must be set to IEEE 802.1E encapsulation.B. The VTP management domain name of both switches must be set the same.C. All ports on both the switches must be set as access ports.D. One of the two switches must be configured as a VTP server.E. A rollover cable is required to connect the two switches together.F. A router must be used to forward VTP traffic between VLANs.QUESTION 237Which of the following describe the process identifier that is used to run OSPF on a router? (Choose two.)A. It is locally significant.B. It is globally significant.C. It is needed to identify a unique instance of an OSPF database.D. It is an optional parameter required only if multiple OSPF processes are running on the router.E. All routers in the same OSPF area must have the same process ID if they are to exchange routinginformation.QUESTION 238What functions do routers perform in a network? (Choose two.)A. packet switchingB. access layer securityC. path selectionD. VLAN membership assignmentE. bridging between LAN segmentsF. microsegmentation of broadcast domainsQUESTION 239Which series of commands will configure router R1 for LAN-to-LAN communication with router R2? Theenterprise network address is 192.1.1.0/24 and the routing protocol in use is RIP. (Choose three.)A. R1(config)# interface ethernet 0R1(config-if)# ip address 192.1.1.129 255.255.255.192R1(config-if)# no shutdownB. R1(config)# interface ethernet 0R1(config-if)# ip address 192.1.1.97 255.255.255.192R1(config-if)# no shutdownC. R1(config)# interface serial 0R1(config-if)# ip address 192.1.1.4 255.255.255.252R1(config-if)# clock rate 56000D. R1(config)# interface serial 0R1(config-if)# ip address 192.1.1.6 255.255.255.252R1(config-if)# no shutdownCCNA考试报名1700元109艾迪飞论坛艾迪飞论坛E. R1(config)# router ripR1(config-router)# network 192.1.1.4R1(config-router)# network 192.1.1.128F. R1(config)# router ripR1(config-router)# version 2R1(config-router)# network 192.1.1.0QUESTION 240A network administrator wants to ensure that only the server can connect to port Fa0/1 on a Catalystswitch. The server is plugged into the switch Fa0/1 port and the network administrator is about to bring theserver online. What can the administrator do to ensure that only the MAC address of the server is allowedby switch port Fa0/1? (Choose two.)A. Configure port Fa0/1 to accept connections only from the static IP address of the server.B. Employ a proprietary connector type on Fa0/1 that is incompatible with other host connectors.C. Configure the MAC address of the server as a static entry associated with port Fa0/1.D. Bind the IP address of the server to its MAC address on the switch to prevent other hosts from spoofingthe server IP address.E. Configure port security on Fa0/1 to reject traffic with a source MAC address other than that of theserver.F. Configure an access list on the switch to deny server traffic from entering any port other than Fa0/1.QUESTION 241The internetwork infrastructure of company XYZ consists of a single OSPF area as shown in the graphic.There is concern that a lack of router resources is impeding internetwork performance. As part of examining the router resources, the OSPF DRs need to be known. All the router OSPF priorities are at thedefault and the router IDs are shown with each router. Which routers are likely to have been elected asDR? (Choose two.)A. Corp-1B. Corp-2C. Corp-3D. Corp-4E. Branch-1F. Branch-2QUESTION 242At which layers of the OSI model do WANs operate? (Choose two.)A. application layerB. session layerC. transport layerD. network layerE. datalink layerF. physical layerQUESTION 243Which routing protocols can be used within the enterprise network shown in the diagram? (Choose three.)A. RIP v1B. RIP v2C. IGRPD. OSPFE. BGPF. EIGRPQUESTION 244Refer to the graphic. R1 is unable to establish an OSPF neighbor relationship with R3. What are possiblereasons for this problem? (Choose two.)A. All of the routers need to be configured for backbone Area 1.B. R1 and R2 are the DR and BDR, so OSPF will not establish neighbor adjacency with R3.C. A static route has been configured from R1 to R3 and prevents the neighbor adjacency from beingestablished.D. The hello and dead interval timers are not set to the same values on R1 and R3.E. EIGRP is also configured on these routers with a lower administrative distance.F. R1 and R3 are configured in different areas.QUESTION 245Which statements are true about EIGRP successor routes? (Choose two.)A. A successor route is used by EIGRP to forward traffic to a destination.B. Successor routes are saved in the topology table to be used if the primary route fails.C. Successor routes are flagged as "active" in the routing table.D. A successor route may be backed up by a feasible successor route.E. Successor routes are stored in the neighbor table following the discovery process.QUESTION 246CCNA考试报名1700元112艾迪飞论坛Refer to the diagram. All hosts have connectivity with one another. Which statements describe theaddressing scheme that is in use in the network? (Choose three.)A. The subnet mask in use is 255.255.255.192.B. The subnet mask in use is 255.255.255.128.C. The IP address 172.16.1.25 can be assigned to hosts in VLAN1D. The IP address 172.16.1.205 can be assigned to hosts in VLAN1E. The LAN interface of the router is configured with one IP address.F. The LAN interface of the router is configured with multiple IP addresses.QUESTION 247Refer to the diagram. Which three statements describe the router port configuration and the switch portconfiguration as shown in the topology? (Choose three.)A. The Router1 WAN port is configured as a trunking port.B. The Router1 port connected to Switch1 is configured using subinterfaces.C. The Router1 port connected to Switch1 is configured as 10 Mbps.D. The Switch1 port connected to Router1 is configured as a trunking port.E. The Switch1 port connected to Host B is configured as an access port.F. The Switch1 port connected to Hub1 is configured as full duplex.QUESTION 248Which routing protocols will support the following IP addressing scheme? (Choose three.) Network 1 - 192.168.10.0 /26Network 2 - 192.168.10.64 /27Network 3 - 192.168.10.96 /27Network 4 - 192.168.10.128 /30Network 5 - 192.168.10.132 /30A. RIP version 1B. RIP version 2C. IGRPD. EIGRPE. OSPFQUESTION 249Refer to the partial command output shown. Which two statements are correct regarding the routerhardware? (Choose two.)A. Total RAM size is 32 KB.B. Total RAM size is 16384 KB (16 MB).C. Total RAM size is 65536 KB (64 MB).D. Flash size is 32 KB.E. Flash size is 16384 KB (16 MB).F. Flash size is 65536 KB (64 MB)QUESTION 250The Ethernet networks connected to router R1 in the graphic have been summarized for router R2 as192.1.144.0/20. Which of the following packet destination addresses will R2 forward to R1, according to thissummary? (Choose two.)A. 192.1.159.2B. 192.1.160.11C. 192.1.138.41D. 192.1.151.254E. 192.1.143.145F. 192.1.1.144QUESTION 251The show interfaces serial 0/0 command resulted in the output shown in the graphic. What are possiblecauses for this interface status? (Choose three.)A. The interface is shut down.B. No keepalive messages are received.C. The clockrate is not set.D. No loopback address is set.E. No cable is attached to the interface.F. There is a mismatch in the encapsulation type.QUESTION 252Which of the following describe private IP addresses? (Choose two.)A. addresses chosen by a company to communicate with the InternetB. addresses that cannot be routed through the public InternetC. addresses that can be routed through the public InternetD. a scheme to conserve public addressesE. addresses licensed to enterprises or ISPs by an Internet registry organizationQUESTION 253Refer to the exhibit. The network shown in the diagram is experiencing connectivity problems. Which of thefollowing will correct the problems? (Choose two.)A. Configure the gateway on Host A as 10.1.1.1.B. Configure the gateway on Host B as 10.1.2.254.C. Configure the IP address of Host A as 10.1.2.2.D. Configure the IP address of Host B as 10.1.2.2.E. Configure the masks on both hosts to be 255.255.255.224.F. Configure the masks on both hosts to be 255.255.255.240.QUESTION 254A network associate is trying to understand the operation of the FLD Corporation by studying the network inthe exhibit. The associate knows that the server in VLAN 4 provides the necessary resources to support theuser hosts in the other VLANs. The associate needs to determine which interfaces are access ports. WhichCCNA考试报名1700元116艾迪飞论坛interfaces are access ports? (Choose three.)A. Switch1 - Fa 0/2B. Switch1 - Fa 0/9C. Switch2 - Fa 0/3D. Switch2 - Fa 0/4E. Switch2 - Fa 0/8F. Router - Fa 1/0QUESTION 255Refer to the exhibit. Which destination addresses will Host A use to send data to Host B? (Choose two.)A. the IP address of Switch1B. the IP address of Router1 Fa0/0C. the IP address of HostBD. the MAC address of Switch1E. the MAC address of Router1 Fa0/0CCNA考试报名1700元117艾迪飞论坛F. the MAC address of HostBQUESTION 256The network security policy requires that only one host be permitted to attach dynamically to each switchinterface. If that policy is violated, the interface should shut down. Which two commands must the networkadministrator configure on the 2950 Catalyst switch to meet this policy? (Choose two.)A. Switch1(config-if)# switchport port-security maximum 1B. Switch1(config)# mac-address-table secureC. Switch1(config)# access-list 10 permit ip hostD. Switch1(config-if)# switchport port-security violation shutdownE. Switch1(config-if)# ip access-group 10QUESTION 257Refer to the graphic. A static route to the 10.5.6.0/24 network is to be configured on the HFD router. Whichcommands will accomplish this? (Choose two.)A. HFD(config)# ip route 10.5.6.0 0.0.0.255 fa0/0B. HFD(config)# ip route 10.5.6.0 0.0.0.255 10.5.4.6C. HFD(config)# ip route 10.5.6.0 255.255.255.0 fa0/0D. HFD(config)# ip route 10.5.6.0 255.255.255.0 10.5.4.6E. HFD(config)# ip route 10.5.4.6 0.0.0.255 10.5.6.0F. HFD(config)# ip route 10.5.4.6 255.255.255.0 10.5.6.0QUESTION 258What should be done prior to backing up an IOS image to a TFTP server? (Choose three.)A. Make sure that the server can be reached across the network.CCNA考试报名1700元118艾迪飞论坛B. Check that authentication for TFTP access to the server is set.C. Assure that the network server has adequate space for the IOS image.D. Verify file naming and path requirements.E. Make sure that the server can store binary files.F. Adjust the TCP window size to speed up the transfer.QUESTION 259What are the possible trunking modes for a switch port? (Choose three.)A. transparentB. autoC. onD. desirableE. clientF. forwardingQUESTION 260The network 172.25.0.0 has been divided into eight equal subnets. Which of the following IP addresses canbe assigned to hosts in the third subnet if the ip subnet-zero command is configured on the router? (Choosethree.)A. 172.25.78.243B. 172.25.98.16C. 172.25.72.0D. 172.25.94.255E. 172.25.96.17F. 172.25.100.16QUESTION 261Refer to the graphic. Host 1 cannot receive packets from Host 2. Assuming that RIP v1 is the routingprotocol in use, what is wrong with the IP configuration information shown? (Choose two.)A. The fa0/1 interface of router R2 has been assigned a broadcast address.B. The fa0/1 network on router R2 overlaps with the LAN attached to R1.C. Host 2 has been assigned the incorrect subnet mask.D. Host 1 has been configured with the 255.255.248.0 subnet mask.E. Host 2 on router R2 is on a different subnet than its gateway.QUESTION 262What are three valid reasons to assign ports to VLANs on a switch? (Choose three.)A. to make VTP easier to implementB. to isolate broadcast trafficC. to increase the size of the collision domainD. to allow more devices to connect to the networkE. to logically group hosts according to functionF. to increase network securityQUESTION 263Refer to the topology shown in the exhibit. Which ports will be STP designated ports if all the links areoperating at the same bandwidth? (Choose three.)A. Switch A - Fa0/0B. Switch A - Fa0/1C. Switch B - Fa0/0D. Switch B - Fa0/1E. Switch C - Fa0/0F. Switch C - Fa0/1QUESTION 264Which statements describe two of the benefits of VLAN Trunking Protocol? (Choose two.)A. VTP allows routing between VLANs.B. VTP allows a single switch port to carry information to more than one VLAN.C. VTP allows physically redundant links while preventing switching loops.D. VTP simplifies switch administration by allowing switches to automatically share VLAN configurationinformation.E. VTP helps to limit configuration errors by keeping VLAN naming consistent across the VTP domain.F. VTP enhances security by preventing unauthorized hosts from connecting to the VTP domain.QUESTION 265What are two results of entering the Switch(config)# vtp mode client command on a Catalyst switch?CCNA考试报名1700元121艾迪飞论坛艾迪飞论坛(Choose two.)A. The switch will ignore VTP summary advertisements.B. The switch will forward VTP summary advertisements.C. The switch will process VTP summary advertisements.D. The switch will originate VTP summary advertisements.E. The switch will create, modify and delete VLANs for the entire VTP domain.QUESTION 266A network administrator issues the ping 192.168.2.5 command and successfully tests connectivity to a hostthat has been newly connected to the network. Which protocols were used during the test? (Choose two.)A. ARPB. CDPC. DHCPD. DNSE. ICMPQUESTION 267Refer to the exhibit. Host A is to send data to Host B. How will Router1 handle the data frame receivedfrom Host A? (Choose three.)A. Router1 will strip off the source MAC address and replace it with the MAC address on the forwardingFastEthernet interface.B. Router1 will strip off the source IP address and replace it with the IP address on the forwarding FastEthernet interface.C. Router1 will strip off the destination MAC address and replace it with the MAC address of Host B.D. Router1 will strip off the destination IP address and replace it with the IP address of Host B.E. Router1 will forward the data frame out interface FastEthernet0/1.F. Router1 will forward the data frame out interface FastEthernet0/2.QUESTION 268Refer to the exhibit. What will Router1 do when it receives the data frame shown? (Choose three.)A. Router1 will strip off the source MAC address and replace it with the MAC address 0000.0c36.6965.B. Router1 will strip off the source IP address and replace it with the IP address 192.168.40.1.C. Router1 will strip off the destination MAC address and replace it with the MAC address 0000.0c07.4320.D. Router1 will strip off the destination IP address and replace it with the IP address of 192.168.40.1.E. Router1 will forward the data packet out interface FastEthernet0/1.F. Router1 will forward the data packet out interface FastEthernet0/2.QUESTION 269Refer to the exhibit. Host A pings Host B. What source MAC address and source IP address are containedin the frame as the frame leaves R2 destined for host B?A. abcd.abcd.a001B. abcd.abcd.b002C. abcd.abcd.c003D. 10.2.0.15E. 10.0.64.1F. 10.0.128.15QUESTION 270Refer to the exhibit. A network associate has configured OSPF with the command:City(config-router)# network 192.168.12.64 0.0.0.63 area 0After completing the configuration, the associate discovers that not all the interfaces are participating inOSPF. Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement? (Choose three.)A. FastEthernet0 /0CCNA考试报名1700元124艾迪飞论坛B. FastEthernet0 /1C. Serial0/0D. Serial0/1.102E. Serial0/1.103F. Serial0/1.104QUESTION 271A Catalyst 2950 needs to be reconfigured. What steps will ensure that the old configuration is erased?(Choose three.)A. Erase flash.B. Restart the switch.C. Delete the VLAN database.D. Erase the running configuration.E. Erase the startup configuration.F. Modify the configuration register.QUESTION 272Refer to the exhibit. The FMJ manufacturing company is concerned about unauthorized access to thePayroll Server. The Accounting1, CEO, Mgr1, and Mgr2 workstations should be the only computers withaccess to the Payroll Server. What two technologies should be implemented to help prevent unauthorizedaccess to the server? (Choose two.)A. access listsB. encrypted router passwordsC. STPD. VLANsCCNA考试报名1700元125艾迪飞论坛E. VTP。
2022年CCNA认证试题及答案
2022年CCNA认证试题及答案1、目前,我国应用最为广泛的LAN标准是基于()的以太网标准.(A) IEEE 802.1(B) IEEE 802.2(C) IEEE 802.3(D) IEEE 802.5答案:C参考知识点:现有标准:IEEE 802.1 局域网协议高层IEEE 802.2 逻辑链路控制IEEE 802.3 以太网IEEE 802.4 令牌总线IEEE 802.5 令牌环IEEE 802.8 FDDIIEEE 802.11 无线局域网记住.1-------.5的定义以太网是一种计算机局域网组网技术。
IEEE制定的IEEE 802.3标准给出了以太网的技术标准。
它规定了包括物理层的连线、电信号和介质访问层协议的内容。
以太网是当前应用最普遍的局域网技术。
它很大程度上取代了其他局域网标准,如令牌环、FDDI和ARCNET。
以太网的标准拓扑结构为总线型拓扑,但目前的快速以太网(100BASE-T、1000BASE-T标准)为了最大程度的减少冲突,最大程度的提高网络速度和使用效率,使用交换机(Switch)来进行网络连接和组织,这样,以太网的拓扑结构就成了星型,但在逻辑上,以太网仍然使用总线型拓扑的C某某某A/CD介质访问控制方法。
电气电子工程师协会或IEEE(Institute of Electrical and Electronics Engineers)是一个国际性的电子技术与信息科学工程师的协会。
建会于1963年1月1日。
总部在美国纽约市。
在150多个国家中它拥有300多个地方分会。
目前会员数是36万。
专业上它有35个专业学会和两个联合会。
IEEE发表多种杂志,学报,书籍和每年组织300多次专业会议。
IEEE定义的标准在工业界有极大的影响。
下面列出:.3以太网标准802.3--------- 10Base以太网标准802.3u-------- 100Base-T(快速以太网)802.3z-------- 1000Base-某(光纤吉比特以太网)802.3ab-------- 1000Base-T(双绞线吉比特以太网)2、对于这样一个地址,192.168.19.255/20,下列说法正确的是: ( )(A) 这是一个广播地址(B) 这是一个网络地址(C) 这是一个私有地址(D) 地址在192.168.19.0网段上(E) 地址在192.168.16.0网段上(F) 这是一个公有地址答案:CE注:IP地址中关键是看她的主机位,将子网掩码划为二进制,1对应上面的地址是网络位,0对应的地址是主机位192.168.19.255/20划为二进制为:..00010011. (00000000)主机位变成全0表示这个IP的.网络地址主机槐涑扇?表示这个IP的广播地址文件规定了保留作为局域网使用的私有地址:10.0.0.0 - 10.255.255.255 (10/8 prefi某)172.16.0.0 - 172.31.255.255 (172.16/12 prefi某)192.168.0.0 - 192.168.255.255 (192.168/16 prefi某)3、Quidway系列路由器在执行数据包转发时,下列哪些项没有发生变化(假定没有使用地址转换技术)?( )(A) 源端口号(B) 目的端口号(C) 源网络地址(D) 目的网络地址(E) 源MAC地址(F) 目的MAC地址答案:ABCD参考知识点:路由功能就是指选择一条从源网络到目的网络的路径,并进行数据包的转发。
CCNA问答题及答案

CCNA问答题及答案1、CIDR、VLSM分别叫什么?CIDR:无类型域间选路VLSM:可变长子网掩码2、路由的作用1、改进网络分段(每个网段的结点数是有限的)。
相同类型的局域网互连,划分子网段,三层交换,避免“广播风暴”。
2、不同局域网之间的路由能力,实现三层的数据报文的转换。
3、连接W AN的路由能力。
3、被动路由与主动路由1.主动路由协议是路由器在互联网上动态找寻所有网络,并确保所有路由器拥有相同路由表的协议. 它基本上就是决定数据包通过互联网最右路径的协议. RIPv1,RIPv2,EIGRP 和OSPF都是主动路由协议.2. 被动路由协议:是路由器不自动搜寻网络,需要手工配置。
一旦所有的路由器都了解了所有的网络,被动路由协议便可用来发送用户数据(数据包),通过互联网络被动路由协议被分派到接口上并决定数据包的传送方式.IP和IPv6就是被动路由协议4、查看路由表可以使用什么命令,常用路由方式的缩写show ip route5、IP路由选择过程6、静态路由及其配置方法静态路由是指由网络管理员手工配置的路由信息router(config)#hostname A (更改路由器主机名)A(config)#interface f0/0 (进入接口f0/0)A(config-if)#ip address 192.168.1.1 255.255.255.0 (设置接口ip地址和子网掩码)A(config-if)#no shutdown (启用接口)A(config)#interface f0/1A(config-if)#ip address 192.168.2.1 255.255.255.0A(config-if)#no shutdown ×××以下二选一:A(config)#ip route 192.168.3.0 255.255.255.0 f0/1(目标网段ip地址目标子网掩码送出接口(路由器A))或者A(config)#ip route 192.168.3.0 255.255.255.0 192.168.2.2 (目标网段ip地址目标子网掩码下一路由器接口ip地址)router(config)#hostname BB(config)#interface f0/0B(config-if)#ip address 192.168.3.1 255.255.255.0B(config-if)#no shutdownB(config)#interface f0/1B(config-if)#ip address 192.168.2.2 255.255.255.0B(config-if)#no shutdown ×××以下二选一:B(config)#ip route 192.168.1.0 255.255.255.0 192.168.2.1 或者:B(config)#ip route 192.168.1.0 255.255.255.0 f0/1(目标网段ip地址目标子网掩码送出接口(路由器B))×××注1:此网络链路为以太网链路,如果是串行链路,送出接口也就是本地路由器的串行接口。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
QUESTION 251The show interfaces serial 0/0 command resulted in the output shown in the graphic. What are possible causes for this interface status? (Choose three.)A. The interface is shut down.B. No keepalive messages are received.C. The clockrate is not set.D. No loopback address is set.E. No cable is attached to the interface.F. There is a mismatch in the encapsulation type.QUESTION 252Which of the following describe private IP addresses? (Choose two.)A. addresses chosen by a company to communicate with the InternetB. addresses that cannot be routed through the public InternetC. addresses that can be routed through the public InternetD. a scheme to conserve public addressesE. addresses licensed to enterprises or ISPs by an Internet registry organizationQUESTION 253Refer to the exhibit. The network shown in the diagram is experiencing connectivity problems. Which of the following will correct the problems? (Choose two.)A. Configure the gateway on Host A as 10.1.1.1.B. Configure the gateway on Host B as 10.1.2.254.C. Configure the IP address of Host A as 10.1.2.2.D. Configure the IP address of Host B as 10.1.2.2.E. Configure the masks on both hosts to be 255.255.255.224.F. Configure the masks on both hosts to be 255.255.255.240.QUESTION 254A network associate is trying to understand the operation of the FLD Corporation by studying the network in the exhibit. The associate knows that the server in VLAN 4 provides the necessary resources to support the user hosts in the other VLANs. The associate needs to determine which interfaces are access ports. Which interfaces are access ports? (Choose three.)A. Switch1 - Fa 0/2B. Switch1 - Fa 0/9C. Switch2 - Fa 0/3D. Switch2 - Fa 0/4E. Switch2 - Fa 0/8F. Router - Fa 1/0QUESTION 255Refer to the exhibit. Which destination addresses will Host A use to send data to Host B? (Choose two.)A. the IP address of Switch1B. the IP address of Router1 Fa0/0C. the IP address of HostBD. the MAC address of Switch1E. the MAC address of Router1 Fa0/0F. the MAC address of HostBQUESTION 256The network security policy requires that only one host be permitted to attach dynamically to each switch interface. If that policy is violated, the interface should shut down. Which two commands must the network administrator configure on the 2950 Catalyst switch to meet this policy? (Choose two.)A. Switch1(config-if)# switchport port-security maximum 1B. Switch1(config)# mac-address-table secureC. Switch1(config)# access-list 10 permit ip hostD. Switch1(config-if)# switchport port-security violation shutdownE. Switch1(config-if)# ip access-group 10QUESTION 257Refer to the graphic. A static route to the 10.5.6.0/24 network is to be configured on the HFD router. Which commands will accomplish this? (Choose two.)A. HFD(config)# ip route 10.5.6.0 0.0.0.255 fa0/0B. HFD(config)# ip route 10.5.6.0 0.0.0.255 10.5.4.6C. HFD(config)# ip route 10.5.6.0 255.255.255.0 fa0/0D. HFD(config)# ip route 10.5.6.0 255.255.255.0 10.5.4.6E. HFD(config)# ip route 10.5.4.6 0.0.0.255 10.5.6.0F. HFD(config)# ip route 10.5.4.6 255.255.255.0 10.5.6.0QUESTION 258What should be done prior to backing up an IOS image to a TFTP server? (Choose three.)A. Make sure that the server can be reached across the network.B. Check that authentication for TFTP access to the server is set.C. Assure that the network server has adequate space for the IOS image.D. Verify file naming and path requirements.E. Make sure that the server can store binary files.F. Adjust the TCP window size to speed up the transfer.QUESTION 259What are the possible trunking modes for a switch port? (Choose three.)A. transparentB. autoC. onD. desirableE. clientF. forwardingQUESTION 260The network 172.25.0.0 has been divided into eight equal subnets. Which of the following IP addresses can be assigned to hosts in the third subnet if the ip subnet-zero command is configured on the router? (Choose three.)A. 172.25.78.243B. 172.25.98.16C. 172.25.72.0D. 172.25.94.255E. 172.25.96.17F. 172.25.100.16QUESTION 261Refer to the graphic. Host 1 cannot receive packets from Host 2. Assuming that RIP v1 is the routing protocol in use, what is wrong with the IP configuration information shown? (Choose two.)A. The fa0/1 interface of router R2 has been assigned a broadcast address.B. The fa0/1 network on router R2 overlaps with the LAN attached to R1.C. Host 2 has been assigned the incorrect subnet mask.D. Host 1 has been configured with the 255.255.248.0 subnet mask.E. Host 2 on router R2 is on a different subnet than its gateway.QUESTION 262What are three valid reasons to assign ports to VLANs on a switch? (Choose three.)A. to make VTP easier to implementB. to isolate broadcast trafficC. to increase the size of the collision domainD. to allow more devices to connect to the networkE. to logically group hosts according to functionF. to increase network securityQUESTION 263Refer to the topology shown in the exhibit. Which ports will be STP designated ports if all the links are operating at the same bandwidth? (Choose three.)A. Switch A - Fa0/0B. Switch A - Fa0/1C. Switch B - Fa0/0D. Switch B - Fa0/1E. Switch C - Fa0/0F. Switch C - Fa0/1QUESTION 264Which statements describe two of the benefits of VLAN Trunking Protocol? (Choose two.)A. VTP allows routing between VLANs.B. VTP allows a single switch port to carry information to more than one VLAN.C. VTP allows physically redundant links while preventing switching loops.D. VTP simplifies switch administration by allowing switches to automatically share VLAN configuration information.E. VTP helps to limit configuration errors by keeping VLAN naming consistent across the VTP domain.F. VTP enhances security by preventing unauthorized hosts from connecting to the VTP domain.QUESTION 265What are two results of entering the Switch(config)# vtp mode client command on a Catalyst switch? (Choose two.)A. The switch will ignore VTP summary advertisements.B. The switch will forward VTP summary advertisements.C. The switch will process VTP summary advertisements.D. The switch will originate VTP summary advertisements.E. The switch will create, modify and delete VLANs for the entire VTP domain.QUESTION 266A network administrator issues the ping 192.168.2.5 command and successfully tests connectivity to a host that has been newly connected to the network. Which protocols were used during the test? (Choose two.)A. ARPB. CDPC. DHCPD. DNSE. ICMPQUESTION 267Refer to the exhibit. Host A is to send data to Host B. How will Router1 handle the data frame received from Host A? (Choose three.)A. Router1 will strip off the source MAC address and replace it with the MAC address on the forwarding FastEthernet interface.B. Router1 will strip off the source IP address and replace it with the IP address on the forwarding FastEthernet interface.C. Router1 will strip off the destination MAC address and replace it with the MAC address of Host B.D. Router1 will strip off the destination IP address and replace it with the IP address of Host B.E. Router1 will forward the data frame out interface FastEthernet0/1.F. Router1 will forward the data frame out interface FastEthernet0/2.QUESTION 268Refer to the exhibit. What will Router1 do when it receives the data frame shown? (Choose three.)A. Router1 will strip off the source MAC address and replace it with the MAC address 0000.0c36.6965.B. Router1 will strip off the source IP address and replace it with the IP address 192.168.40.1.C. Router1 will strip off the destination MAC address and replace it with the MAC address 0000.0c07.4320.D. Router1 will strip off the destination IP address and replace it with the IP address of 192.168.40.1.E. Router1 will forward the data packet out interface FastEthernet0/1.F. Router1 will forward the data packet out interface FastEthernet0/2.QUESTION 269Refer to the exhibit. Host A pings Host B. What source MAC address and source IP address are contained in the frame as the frame leaves R2 destined for host B?A. abcd.abcd.a001B. abcd.abcd.b002C. abcd.abcd.c003D. 10.2.0.15E. 10.0.64.1F. 10.0.128.15QUESTION 270Refer to the exhibit. A network associate has configured OSPF with the command:City(config-router)# network 192.168.12.64 0.0.0.63 area 0After completing the configuration, the associate discovers that not all the interfaces are participating in OSPF. Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement? (Choose three.)A. FastEthernet0 /0B. FastEthernet0 /1C. Serial0/0D. Serial0/1.102E. Serial0/1.103F. Serial0/1.104QUESTION 271A Catalyst 2950 needs to be reconfigured. What steps will ensure that the old configuration is erased? (Choose three.)A. Erase flash.B. Restart the switch.C. Delete the VLAN database.D. Erase the running configuration.E. Erase the startup configuration.F. Modify the configuration register.QUESTION 272Refer to the exhibit. The FMJ manufacturing company is concerned about unauthorized access to the Payroll Server. The Accounting1, CEO, Mgr1, and Mgr2 workstations should be the only computers with access to the Payroll Server. What two technologies should be implemented to help prevent unauthorized access to the server? (Choose two.)A. access listsB. encrypted router passwordsC. STPD. VLANsE. VTPF. wireless LANsQUESTION 273Refer to the exhibit. What commands must be configured on the 2950 switch and the router to allow communication between host 1 and host 2? (Choose two.)A.Router(config)# interface fastethernet 0/0Router(config-if)# ip address 192.168.1.1 255.255.255.0Router(config-if)# no shut downB.Router(config)# interface fastethernet 0/0Router(config-if)# no shut downRouter(config)# interface fastethernet 0/0.1Router(config-subif)# encapsulation dot1q 10Router(config-subif)# ip address 192.168.10.1 255.255.255.0Router(config-subif)# interface fastethernet 0/0.2Router(config-subif)# encapsulation dot1q 20Router(config-subif)# ip address 192.168.20.1 255.255.255.0C.Router(config)# router eigrp 100Router(config-router)# network 192.168.10.0Router(config-router)# network 192.168.20.0D.Switch1(config)# vlan databaseSwitch1(config-vlan)# vtp domain XYZSwitch1(config-vlan)# vtp serverE.Switch1(config)# interface fastethernet 0/1Switch1(config-if)# switchport mode trunkF.Switch1(config)# interface vlan 1Switch1(config-if)# ip default-gateway 192.168.1.1QUESTION 274Which three Layer 2 encapsulation types would be used on a WAN rather than a LAN? (Choose three.)A. HDLCB. EthernetC. Token RingD. PPPE. FDDIF. Frame RelayQUESTION 275Refer to the exhibit. The two connected ports on the switch are not turning orange or green. What would be the most effective steps to troubleshoot this physical layer problem? (Choose three.)A. Ensure that the Ethernet encapsulations match on the interconnected router and switch ports.B. Ensure that cables A and B are straight-through cables.C. Ensure cable A is plugged into a trunk port.D. Ensure the switch has power.E. Reboot all of the devices.F. Reseat all cables.QUESTION 276Refer to the exhibit. Which three statements are true about how router JAX will choose a path to the 10.1.3.0/24 network when different routing protocols are configured? (Choose three.)A. By default, if RIPv2 is the routing protocol, only the path JAX-ORL will be installed into the routing table.B. The equal cost paths JAX-CHI-ORL and JAX- NY-ORL will be installed in the routing table if RIPv2 is the routing protocol.C. When EIGRP is the routing protocol, only the path JAX-ORL will be installed in the routing table by default.D. When EIGRP is the routing protocol, the equal cost paths JAX-CHI-ORL, and JAX-NY-ORL will be installed in the routing table by default.E. With EIGRP and OSPF both running on the network with their default configurations, the EIGRP paths will be installed in the routing table.F. The OSPF paths will be installed in the routing table, if EIGRP and OSPF are both running on the network with their default configurations.QUESTION 277Refer to the exhibit. Which three statements correctly describe Network Device A? (Choose three.)A. With a network wide mask of 255.255.255.128, each interface does not require an IP address.B. With a network wide mask of 255.255.255.128, each interface does require an IP address on a unique IP subnet.C. With a network wide mask of 255.255.255.0, must be a Layer 2 device for the PCs to communicate with each other.D. With a network wide mask of 255.255.255.0, must be a Layer 3 device for the PCs to communicate with each other.E. With a network wide mask of 255.255.254.0, each interface does not require an IP address.QUESTION 278Switch ports operating in which two roles will forward traffic according to the IEEE 802.1w standard? (Choose two.)A. alternateB. backupC. designatedD. disabledE. rootQUESTION 279Refer to the exhibit. Given the output shown from this Cisco Catalyst 2950, what is the most likely reason that interface FastEthernet 0/10 is not the root port for VLAN 2?A. This switch has more than one interface connected to the root network segment in VLAN 2.B. This switch is running RSTP while the elected designated switch is running 802.1d Spanning Tree.C. This switch interface has a higher path cost to the root bridge than another in the topology.D. This switch has a lower bridge ID for VLAN 2 than the elected designated switch.QUESTION 280Refer to the exhibit. The network administrator must establish a route by which London workstations can forward traffic to the Manchester workstations. What is the simplest way to accomplish this?A. Configure a dynamic routing protocol on London to advertise all routes to Manchester.B. Configure a dynamic routing protocol on London to advertise summarized routes to Manchester.C. Configure a dynamic routing protocol on Manchester to advertise a default route to the London router.D. Configure a static default route on London with a next hop of 10.1.1.1.E. Configure a static route on London to direct all traffic destined for 172.16.0.0/22 to 10.1.1.2.F. Configure Manchester to advertise a static default route to London.QUESTION 281Refer to the exhibit. This command is executed on 2960Switch:2960Switch(config)# mac-address-table static 0000.00aa.aaaa vlan 10 interfacefa0/1Which two of these statements correctly identify results of executing the command? (Choose two.)A. Port security is implemented on the fa0/1 interface.B. MAC address 0000.00aa.aaaa does not need to be learned by this switch.C. Only MAC address 0000.00aa.aaaa can source frames on the fa0/1 segment.D. Frames with a Layer 2 source address of 0000.00aa.aaaa will be forwarded out fa0/1.E. MAC address 0000.00aa.aaaa will be listed in the MAC address table for interface fa0/1 only.QUESTION 282Which of the following describes the roles of devices in a WAN? (Choose three.)A. A CSU/DSU terminates a digital local loop.B. A modem terminates a digital local loop.C. A CSU/DSU terminates an analog local loop.D. A modem terminates an loop.E. A router is commonly considered a DTE device.F. A router is commonly considered a DCE device.QUESTION 283What are two characteristics of Telnet? (Choose two.)A. It sends data in clear text format.B. It is no longer supported on Cisco network devices.C. It is more secure than SSH.D. It requires an enterprise license in order to be implemented.E. It requires that the destination device be configured to support Telnet connections.QUESTION 284What are two security appliances that can be installed in a network? (Choose two.)A. ATMB. IDSC. IOSD. IOXE. IPSF. SDMQUESTION 285A single 802.11g access point has been configured and installed in the center of a square office. A few wireless users are experiencing slow performance and drops while most users are operating at peak efficiency. What are three likely causes of this problem? (Choose three.)A. mismatched TKIP encryptionB. null SSIDC. cordless phonesD. mismatched SSIDE. metal file cabinetsF. antenna type or directionQUESTION 286A host is attempting to send data to another host on a different network. What is the first action that the sending host will take?A. Drop the data.B. Send the data frames to the default gateway.C. Create an ARP request to get a MAC address for the receiving host.D. Send a TCP SYN and wait for the SYN ACK with the IP address of the receiving host.QUESTION 287Refer to the exhibit. What two facts can be determined from the WLAN diagram? (Choose two.)A. The area of overlap of the two cells represents a basic service set (BSS).B. The network diagram represents an extended service set (ESS).C. Access points in each cell must be configured to use channel 1.D. The area of overlap must be less than 10% of the area to ensure connectivity.E. The two APs should be configured to operate on different channels.QUESTION 288Which two devices can interfere with the operation of a wireless network because they operate on similar frequencies? (Choose two.)A. copierB. microwave ovenC. toasterD. cordless phoneE. IP phoneF. AM radioQUESTION 289Which two statements describe characteristics of IPv6 unicast addressing? (Choose two.)A. Global addresses start with 2000::/3.B. Link-local addresses start with FE00:/12.C. Link-local addresses start with FF00::/10.D. There is only one loopback address and it is ::1.E. If a global address is assigned to an interface, then that is the only allowable address for the interface.QUESTION 290Refer to the exhibit. Which statement is true?A. The Fa0/11 role confirms that SwitchA is the root bridge for VLAN 20.B. VLAN 20 is running the Per VLAN Spanning Tree Protocol.C. The MAC address of the root bridge is 0017.596d.1580.D. SwitchA is not the root bridge, because not all of the interface roles are designated.QUESTION 291Which two of these statements are true of IPv6 address representation? (Choose two.)A. There are four types of IPv6 addresses: unicast, multicast, anycast, and broadcast.B. A single interface may be assigned multiple IPv6 addresses of any type.C. Every IPv6 interface contains at least one loopback address.D. The first 64 bits represent the dynamically created interface ID.E. Leading zeros in an IPv6 16 bit hexadecimal field are mandatory.QUESTION 292What are three basic parameters to configure on a wireless access point? (Choose three.)A. SSIDB. RTS/CTSC. AES-CCMPD. TKIP/MICE. RF channelF. authentication methodQUESTION 293Refer to the exhibit. A system administrator installed a new switch using a script to configure it. IP connectivity was tested using pings to SwitchB. Later attempts to access NewSwitch using Telnet from SwitchA failed. Which statement is true?A. Executing password recovery is required.B. The virtual terminal lines are misconfigured.C. Use Telnet to connect to RouterA and then to NewSwitch to correct the error.D. Power cycle of NewSwitch will return it to a default configuration.QUESTION 294Which two of these statements regarding RSTP are correct? (Choose two.)A. RSTP cannot operate with PVST+.B. RSTP defines new port roles.C. RSTP defines no new port states.D. RSTP is a proprietary implementation of IEEE 802.1D STP.E. RSTP is compatible with the original IEEE 802.1D STP.QUESTION 295Which three of these statements regarding 802.1Q trunking are correct? (Choose three.)A. 802.1Q native VLAN frames are untagged by default.B. 802.1Q trunking ports can also be secure ports.C. 802.1Q trunks can use 10 Mb/s Ethernet interfaces.D. 802.1Q trunks require full-duplex, point-to-point connectivity.E. 802.1Q trunks should have native VLANs that are the same at both ends.QUESTION 296Refer to the exhibit. Each of these four switches has been configured with a hostname, as well as being configured to run RSTP. No other configuration changes have been made. Which three of these show the correct RSTP port roles for the indicated switches and interfaces? (Choose three.)A. SwitchA, Fa0/2, designatedB. SwitchA, Fa0/1, rootC. SwitchB, Gi0/2, rootD. SwitchB, Gi0/1, designatedE. SwitchC, Fa0/2, rootF. SwitchD, Gi0/2, rootQUESTION 297Refer to the exhibit. A junior network administrator was given the task of configuring port security on SwitchA to allow only PC_A to access the switched network through port fa0/1. If any other device is detected, the port is to drop frames from this device. The administrator configured the interface and tested it with successful pings from PC_A to RouterA, and then observes the output from these two show commands.Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two.)A. Port security needs to be globally enabled.B. Port security needs to be enabled on the interface.C. Port security needs to be configured to shut down the interface in the event of a violation.D. Port security needs to be configured to allow only one learned MAC address.E. Port security interface counters need to be cleared before using the show command.F. The port security configuration needs to be saved to NVRAM before it can become active.QUESTION 298Which of the following correctly describe steps in the OSI data encapsulation process? (Choose two.)A. The transport layer divides a data stream into segments and may add reliability and flow control information.B. The data link layer adds physical source and destination addresses and an FCS to the segment.C. Packets are created when the network layer encapsulates a frame with source and destination host addresses and protocol-related control information.D. Packets are created when the network layer adds Layer 3 addresses and control information to a segment.E. The presentation layer translates bits into voltages for transmission across the physical link.QUESTION 299For which type of connection should a straight-through cable be used?A. switch to switchB. switch to hubC. switch to routerD. hub to hubE. router to PCAnswer: CQUESTION 300Which set of commands is recommended to prevent the use of a hub in the access layer?A.switch(config-if)#switchport mode trunkswitch(config-if)#switchport port-security maximum 1B.switch(config-if)#switchport mode trunkswitch(config-if)#switchport port-security mac-address 1C.switch(config-if)#switchport mode accessswitch(config-if)#switchport port-security maximum 1D.switch(config-if)#switchport mode accessswitch(config-if)#switchport port-security mac-address 1Unit 12 Life is full of the unexpected.Section A 1 (1a-2d)一、教学目标:1. 语言知识目标:1) 能掌握以下单词及短语:unexpected, by the time, backpack, oversleep, ring, give …a lift, 2)掌握By the time I got outside, the bus had already left.When I got to school, I realized I had left my backpack at home.3) 掌握过去完成时时态,结构及用法。
