四川大学数据结构习题
2022年四川大学计算机科学与技术专业《数据结构与算法》科目期末试卷A(有答案)
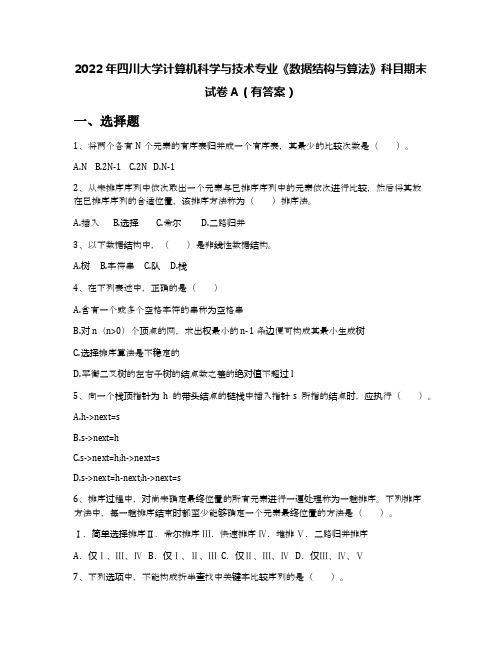
2022年四川大学计算机科学与技术专业《数据结构与算法》科目期末试卷A(有答案)一、选择题1、将两个各有N个元素的有序表归并成一个有序表,其最少的比较次数是()。
A.NB.2N-1C.2ND.N-12、从未排序序列中依次取出一个元素与已排序序列中的元素依次进行比较,然后将其放在已排序序列的合适位置,该排序方法称为()排序法。
A.插入B.选择C.希尔D.二路归并3、以下数据结构中,()是非线性数据结构。
A.树B.字符串C.队D.栈4、在下列表述中,正确的是()A.含有一个或多个空格字符的串称为空格串B.对n(n>0)个顶点的网,求出权最小的n-1条边便可构成其最小生成树C.选择排序算法是不稳定的D.平衡二叉树的左右子树的结点数之差的绝对值不超过l5、向一个栈顶指针为h的带头结点的链栈中插入指针s所指的结点时,应执行()。
A.h->next=sB.s->next=hC.s->next=h;h->next=sD.s->next=h-next;h->next=s6、排序过程中,对尚未确定最终位置的所有元素进行一遍处理称为一趟排序。
下列排序方法中,每一趟排序结束时都至少能够确定一个元素最终位置的方法是()。
Ⅰ.简单选择排序Ⅱ.希尔排序Ⅲ.快速排序Ⅳ.堆排Ⅴ.二路归并排序A.仅Ⅰ、Ⅲ、Ⅳ B.仅Ⅰ、Ⅱ、Ⅲ C.仅Ⅱ、Ⅲ、Ⅳ D.仅Ⅲ、Ⅳ、Ⅴ7、下列选项中,不能构成折半查找中关键字比较序列的是()。
A.500,200,450,180 B.500,450,200,180C.180,500,200,450 D.180,200,500,4508、每个结点的度或者为0或者为2的二叉树称为正则二叉树。
n个结点的正则二叉树中有()个叶子。
A.log2nB.(n-1)/2C.log2n+1D.(n+1)/29、有关二叉树下列说法正确的是()。
A.二叉树的度为2B.一棵二叉树的度可以小于2C.二叉树中至少有一个结点的度为2D.二叉树中任何一个结点的度都为210、对n个记录的线性表进行快速排序为减少算法的递归深度,以下叙述正确的是()。
数据结构03-04期末考试B答案
四川大学期末考试题解答(2003-2004学年第二学期)课程名: 数据结构(B) 计算机科学与技术专业适用人数:学院: 专业: 教师姓名:姓名: 学号: 成绩:一、设n个人围坐在一个圆桌周围,现在从第s个人开始报数,数到第m个人,让他出局;然后从出局的下一个人重新开始报数,数到第m个人,再让他出局,……,如此反复直到所有的人全部出局为止。
下面要解决的Josephus问题是:对于任意给定的n, s和m,求出这n个人的出局序列。
请以n = 9, s = 1, m = 5为例,人工模拟Josephus的求解过程以求得问题的解。
(9分)【解答】出局人的顺序为5, 1, 7, 4, 3, 6, 9, 2, 8。
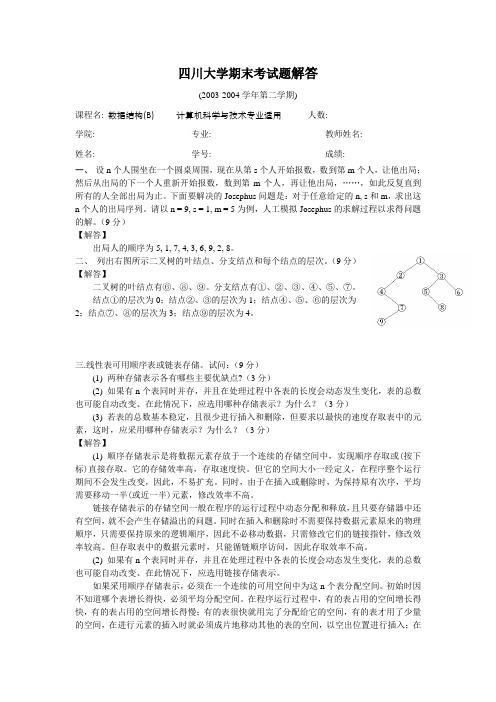
二、列出右图所示二叉树的叶结点、分支结点和每个结点的层次。
(9分)【解答】二叉树的叶结点有⑥、⑧、⑨。
分支结点有①、②、③、④、⑤、⑦。
结点①的层次为0;结点②、③的层次为1;结点④、⑤、⑥的层次为2;结点⑦、⑧的层次为3;结点⑨的层次为4。
三.线性表可用顺序表或链表存储。
试问:(9分)(1) 两种存储表示各有哪些主要优缺点?(3分)(2) 如果有n个表同时并存,并且在处理过程中各表的长度会动态发生变化,表的总数也可能自动改变、在此情况下,应选用哪种存储表示?为什么?(3分)(3) 若表的总数基本稳定,且很少进行插入和删除,但要求以最快的速度存取表中的元素,这时,应采用哪种存储表示?为什么?(3分)【解答】(1) 顺序存储表示是将数据元素存放于一个连续的存储空间中,实现顺序存取或(按下标)直接存取。
它的存储效率高,存取速度快。
但它的空间大小一经定义,在程序整个运行期间不会发生改变,因此,不易扩充。
同时,由于在插入或删除时,为保持原有次序,平均需要移动一半(或近一半)元素,修改效率不高。
链接存储表示的存储空间一般在程序的运行过程中动态分配和释放,且只要存储器中还有空间,就不会产生存储溢出的问题。
同时在插入和删除时不需要保持数据元素原来的物理顺序,只需要保持原来的逻辑顺序,因此不必移动数据,只需修改它们的链接指针,修改效率较高。
四川大学《数据结构2264》17春在线作业2
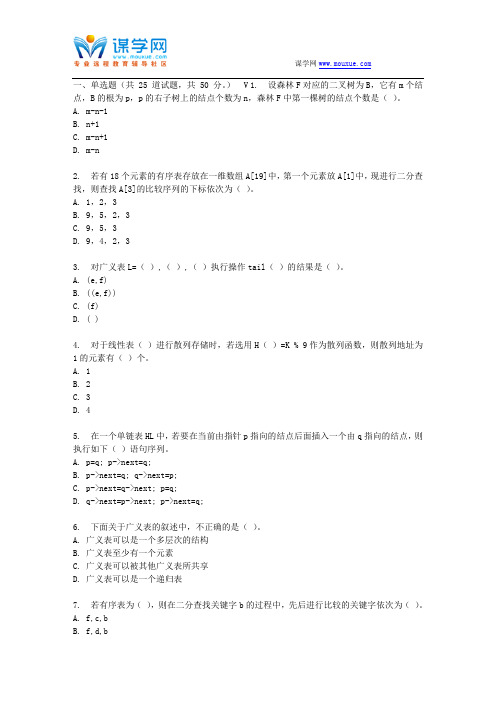
一、单选题(共 25 道试题,共 50 分。
) V 1. 设森林F对应的二叉树为B,它有m个结点,B的根为p,p的右子树上的结点个数为n,森林F中第一棵树的结点个数是()。
A. m-n-1B. n+1C. m-n+1D. m-n2. 若有18个元素的有序表存放在一维数组A[19]中,第一个元素放A[1]中,现进行二分查找,则查找A[3]的比较序列的下标依次为()。
A. 1,2,3B. 9,5,2,3C. 9,5,3D. 9,4,2,33. 对广义表L=(),(),()执行操作tail()的结果是()。
A. (e,f)B. ((e,f))C. (f)D. ( )4. 对于线性表()进行散列存储时,若选用H()=K % 9作为散列函数,则散列地址为1的元素有()个。
A. 1B. 2C. 3D. 45. 在一个单链表HL中,若要在当前由指针p指向的结点后面插入一个由q指向的结点,则执行如下()语句序列。
A. p=q; p->next=q;B. p->next=q; q->next=p;C. p->next=q->next; p=q;D. q->next=p->next; p->next=q;6. 下面关于广义表的叙述中,不正确的是()。
A. 广义表可以是一个多层次的结构B. 广义表至少有一个元素C. 广义表可以被其他广义表所共享D. 广义表可以是一个递归表7. 若有序表为(),则在二分查找关键字b的过程中,先后进行比较的关键字依次为()。
A. f,c,bB. f,d,bC. g,c,bD. g,d,b8. 对一个算法的评价,不包括如下()方面的内容。
A. 健壮性和可读性B. 并行性C. 正确性D. 时空复杂度9. 设Huffman树的叶子结点数为m,则结点总数为()。
A. 2mB. 2m-1C. 2m+1D. m+110. 若某二叉树结点的中序遍历的序列为A、B、C、D、E、F、G,后序遍历的序列为B、D、C、A、F、G、E。
《数据结构》四川大学_期终复习试题+答案

四川大学“精品课程”计算机科学与技术专业(本科)《数据结构与算法分析》课程考试说明与模拟试卷第一部分考试说明数据结构与算法分析》是计算机科学与技术专业统设的一门重要的必修专业基础课,它主要研究数据的各种逻辑结构和在计算机中的存储结构,还研究对数据进行的插入、查找、删除、排序、遍历等基本运算或操作以及这些运算在各种存储结构上具体实现的算法。
由于本课程的主教材采用C++语言描述算法,期末卷面考试也采用C++语言描述,因而要求在做平时作业和上机实验操作时用C++开发工具(如:Visual C++或C++ Builder或Borland C++)。
下面按照主教材中各章次序给出每章的具体复习要求,以便同学们更好地进行期末复习。
第一章绪论重点掌握的内容:1. 数据结构的二元组表示,对应的图形表示,序偶和边之间的对应关系。
2. 集合结构、线性结构、树结构和图结构的特点。
3. 抽象数据类型的定义和表示方法。
4. 一维和二维数组中元素的按下标和按地址的访问方式以及相互转换,元素地址和数组地址的计算,元素占用存储空间大小和数组占用存储空间大小的计算。
5. 普通函数重载和操作符函数重载的含义,定义格式和调用格式。
6. 函数定义中值参数和引用参数的说明格式及作用,函数被调用执行时对传送来的实际参数的影响。
7. 算法的时间复杂度和空间复杂度的概念,计算方法,数量级表示。
8. 一个简单算法的最好、最差和平均这三种情况的时间复杂度的计算。
对于本章的其余内容均作一般掌握。
第二章线性表重点掌握的内容:1. 线性表的定义及判别和抽象数据类型的描述,线性表中每一种操作的功能,对应的函数名、返回值类型和参数表中每个参数的作用。
2. 线性表的顺序存储结构的类型定义,即List类型的定义和每个域的定义及作用。
3. 线性表的每一种运算在顺序存储结构上实现的算法,及相应的时间复杂度。
4.链接存储的概念,线性表的单链接和双链接存储的结构,向单链表中一个结点之后插入新结点或从单链表中删除一个结点的后继结点的指针链接过程。
川大软件数据结构选择题库
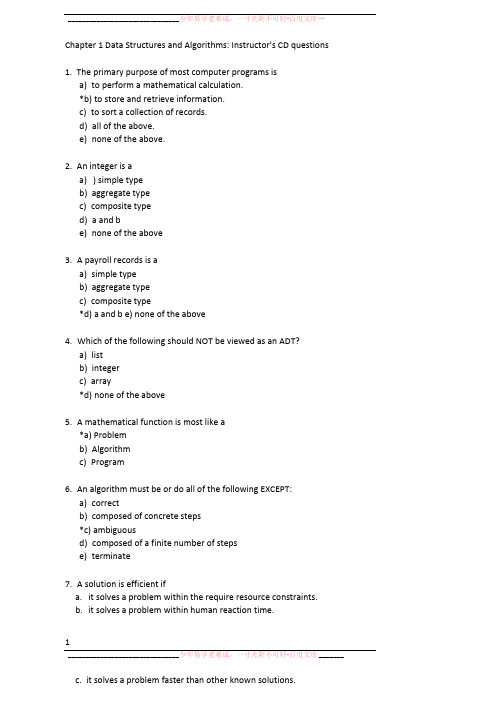
_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库一Chapter 1 Data Structures and Algorithms: Instructor's CD questions1.The primary purpose of most computer programs isa)to perform a mathematical calculation.*b) to store and retrieve information.c)to sort a collection of records.d)all of the above.e)none of the above.2.An integer is aa)) simple typeb)aggregate typec)composite typed)a and be)none of the above3.A payroll records is aa)simple typeb)aggregate typec)composite type*d) a and b e) none of the above4.Which of the following should NOT be viewed as an ADT?a)listb)integerc)array*d) none of the above5.A mathematical function is most like a*a) Problemb)Algorithmc)Program6.An algorithm must be or do all of the following EXCEPT:a)correctb)composed of concrete steps*c) ambiguousd)composed of a finite number of stepse)terminate7.A solution is efficient ifa.it solves a problem within the require resource constraints.b.it solves a problem within human reaction time.1_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库_______ c.it solves a problem faster than other known solutions.d.a and b.*e. a and c.f. b and c.8.An array isa)A contiguous block of memory locations where each memory location storesa fixed-length data item.b)An ADT composed of a homogeneous collection of data items, each data item identified by a particular number.c)a set of integer values.*d) a and b.e)a and c.f)b and c.9.Order the following steps to selecting a data structure to solve a problem.(1)Determine the basic operations to be supported.(2)Quantify the resource constraints for each operation.(3)Select the data structure that best meets these requirements.(4)Analyze the problem to determine the resource constraints that anysolution must meet.a)(1, 2, 3, 4)b)(2, 3, 1, 4)c)(2, 1, 3, 4)*d) (1, 2, 4, 3)e) (1, 4, 3, 2)10.Searching for all those records in a database with key value between 10 and 100 is known as:a) An exact match query.*b) A range query.c)A sequential search.d)A binary search.Chapter 2 Mathematical Preliminaries: Instructor's CD questions1.A set has the following properties:a)May have duplicates, element have a position.b)May have duplicates, elements do not have a position.c)May not have duplicates, elements have a position.*d) May not have duplicates, elements do not have a position._______________________________ 少年易学老难成,一寸光阴不可轻-百度文库2.A sequence has the following properties:a)) May have duplicates, element have a position.b)May have duplicates, elements do not have a position.c)May not have duplicates, elements have a position.d)May not have duplicates, elements do not have a position.3.For set F, the notation |P| indicatesa)) The number of elements in Pb)The inverse of Pc)The powerset of F.d)None of the above.4.Assume that P contains n elements. The number of sets in the powerset of P isa)nb)n A2*c) 2A nd)2A n - 1e) 2A n + 15.If a sequence has n values, then the number of permutations for that sequence will bea)nb)n A2c)n A2 - 1d)2A n*e) n!6.If R is a binary relation over set S, then R is reflexive if*a) aRa for all a in S.b)whenever aRb, then bRa, for all a, b in S.c)whenever aRb and bRa, then a = b, for all a, b in S.d)whenever aRb and aRc, then aRc, for all a, b, c in S.7.If R is a binary relation over set S, then R is transitive ifa)aRa for all a in S.b)whenever aRb, then bRa, for all a, b in S.c)whenever aRb and bRa, then a = b, for all a, b in S.*d) whenever aRb and aRc, then aRc, for all a, b, c in S.8.R is an equivalence relation on set S if it isa)) reflexive, symmetric, transitive.b)reflexive, antisymmetric, transitive.c)symmetric, transitive.少年易学老难成,一寸光阴不可轻-百度文库d)antisymmetric, transitive.e)irreflexive, symmetric, transitive.f)irreflexive, antisymmetric, transitive.9.For the powerset of integers, the subset operation defines *a) a partial order.b)a total order.c)a transitive order.d)none of the above.10.log nm is equal toa) n + m*b) log n + log mc)m log nd)log n - log m11.A close-form solution isa) an analysis for a program.*b) an equation that directly computes the value of a summation.c) a complete solution for a problem.12.Mathematical induction is most likea) iteration.*b) recursion.c)branching.d)divide and conquer.13.A recurrence relation is often used to model programs witha)for loops.b)branch control like "if" statements.*c) recursive calls.d) function calls.14.Which of the following is not a good proof technique.a) proof by contradiction.*b) proof by example.c) proof by mathematical induction.15.We can use mathematical induction to:a) Find a closed-form solution for a summation.*b) Verify a proposed closed-form solution for a summation.c) Both find and verify a closed-form solution for a summation._______________________________ 少年易学老难成,一寸光阴不可轻-百度文库一Chapter 3 Algorithm Analysis: Instructor's CD questions1.A growth rate applies to:a)the time taken by an algorithm in the average case.b)the time taken by an algorithm as the input size grows.c)the space taken by an algorithm in the average case.d)the space taken by an algorithm as the input size grows.e)any resource you wish to measure for an algorithm in the average case.*f) any resource you wish to measure for an algorithm as the input size grows.2.Pick the growth rate that corresponds to the most efficient algorithm as n gets large:a) 5n*b) 20 log nc)2nA2d)2A n3.Pick the growth rate that corresponds to the most efficient algorithm when n =4.a)5nb)20 log nc)2nA2*d)2A n4.Pick the quadratic growth rate.a)5nb)20 log n*c) 2nA2d) 2An5.Asymptotic analysis refers to:a) The cost of an algorithm in its best, worst, or average case.*b) The growth in cost of an algorithm as the input size grows towards infinity.c)The size of a data structure.d)The cost of an algorithm for small input sizes6.For an air traffic control system, the most important metric is:a)The best-case upper bound.b)The average-case upper bound.c)) The worst-case upper bound.d)The best-case lower bound._______________________________ 少年易学老难成,一寸光阴不可轻-百度文库__________e)The average-case lower bound.f)The worst-case lower bound.7.When we wish to describe the upper bound for a problem we use:a)) The upper bound of the best algorithm we know.b)The lower bound of the best algorithm we know.c)We can't talk about the upper bound of a problem because there can alwaysbe an arbitrarily slow algorithm.8.When we describe the lower bound for a problem we use:a)The upper bound for the best algorithm we know.b)the lower bound for the best algorithm we know.c)The smallest upper bound that we can prove for the best algorithm that could possibly exist.*d) The greatest lower bound that we can prove for the best algorithm that could possibly exist.9.When the upper and lower bounds for an algorithm are the same, we use:a)big-Oh notation.b)big-Omega notation.*c) Theta notation.d)asymptotic analysis.e)Average case analysis.f)Worst case analysis.10. When performing asymptotic analysis, we can ignore constants and low order terms because:*a) We are measuring the growth rate as the input size gets large.b)We are only interested in small input sizes.c)We are studying the worst case behavior.d)We only need an approximation.11.The best case for an algorithm refers to:a) The smallest possible input size.*b) The specific input instance of a given size that gives the lowest cost.c)The largest possible input size that meets the required growth rate.d)The specific input instance of a given size that gives the greatest cost.12.For any algorithm:a)) The upper and lower bounds always meet, but we might not know what they are.少年易学老难成,一寸光阴不可轻-百度文库b)The upper and lower bounds might or might not meet.c)We can always determine the upper bound, but might not be able to determine the lower bound.d)We can always determine the lower bound, but might not be able to determine the upper bound.13.If an algorithm is Theta(f(n)) in the average case, then it is: a) Omega(f(n)) in the best case.*b) Omega(f(n)) in the worst case.c) O(f(n)) in the worst case.14.For the purpose of performing algorithm analysis, an important property ofa basic operation is that:a)It be fast.b)It be slow enough to measure.c)Its cost does depend on the value of its operands.*d) Its cost does not depend on the value of its operands.15.For sequential search,a) The best, average, and worst cases are asymptotically the same.*b) The best case is asymptotically better than the average and worst cases.c)The best and average cases are asymptotically better than the worst case.d)The best case is asymptotically better than the average case, and the average case is asymptotically better than the worst case.Chapter 4 Lists, Stacks and Queues: Instructor's CD questions1.An ordered list is one in which:a) The element values are in sorted order.*b) Each element a position within the list.2.An ordered list is most like a:a)set.b)bag.c)) sequence.3.As compared to the linked list implementation for lists, the array-based listimplementation requires:a)More spaceb)Less space*c) More or less space depending on how many elements are in the list._______________________________ 少年易学老难成,一寸光阴不可轻-百度文库4.Here is a series of C++ statements using the list ADT in the book.L1.append(10);L1.append(20);L1.append(15);If these statements are applied to an empty list, the result will look like:a)< 10 20 15 >*b) < | 10 20 15 >c)< 10 20 15 | >d)< 15 20 10 >e)< | 15 20 10 >f)< 15 20 10 | >5.When comparing the array-based and linked implementations, the array-based implementation has:a)) faster direct access to elements by position, but slower insert/delete from the current position.b)slower direct access to elements by position, but faster insert/delete from the current position.c)both faster direct access to elements by position, and faster insert/delete from the current position.d)both slower direct access to elements by position, and slower insert/delete from the current position.6.For a list of length n, the linked-list implementation's prev function requiresworst-case time:a)O(1).b)O(log n).*c) O(n).d) O(n A2).7.Finding the element in an array-based list with a given key value requiresworst case time:a)O(1).b)O(log n).*c) O(n).d) O(n A2).8.In the linked-list implementation presented in the book, a header node isused:*a) To simplify special cases._______________________________ 少年易学老难成,一寸光阴不可轻-百度文库一b)Because the insert and delete routines won't work correctly without it.c)Because there would be no other way to make the current pointer indicatethe first element on the list.9.When a pointer requires 4 bytes and a data element requires 4 bytes, thelinked list implementation requires less space than the array-based list implementation when the array would be:a)less than 1/4 full.b)less than 1/3 full.*c) less than half full.d)less than 第full.e)less than 34 fullf)never.10.When a pointer requires 4 bytes and a data element requires 12 bytes, thelinked list implementation requires less space than the array-based list implementation when the array would be:a)) less than 1/4 full.b)less than 1/3 full.c)less than half full.d)less than 2/3 full.e)less than 34 fullf)never.11.When we say that a list implementation enforces homogeneity, we meanthat:a) All list elements have the same size.*b) All list elements have the same type.c) All list elements appear in sort order.12.When comparing the doubly and singly linked list implementations, we findthat the doubly linked list implementation*a) Saves time on some operations at the expense of additional space.b)Saves neither time nor space, but is easier to implement.c)Saves neither time nor space, and is also harder to implement.13. We use a comparator function in the Dictionary class ADT:a)to simplify implementation.*b) to increase the opportunity for code reuse.c) to improve asymptotic efficiency of some functions.14.All operations on a stack can be implemented in constant time except:少年易学老难成,一寸光阴不可轻-百度文库a) Pushb)Popc)The implementor's choice of push or pop (they cannot both be implementedin constant time).*d) None of the above.15.Recursion is generally implemented usinga) A sorted list.*b) A stack.c) A queue.Chapter 5 Binary Trees: Instructor's CD questions1.The height of a binary tree is:a)The height of the deepest node.b)The depth of the deepest node.*c) One more than the depth of the deepest node.2.A full binary tree is one in which:*a) Every internal node has two non-empty children.b) all of the levels, except possibly the bottom level, are filled.3.The relationship between a full and a complete binary tree is:a)Every complete binary tree is full.b)Every full binary tree is complete.*c) None of the above.4.The Full Binary Tree Theorem states that:a)) The number of leaves in a non-empty full binary tree is one more than the number of internal nodes.b)The number of leaves in a non-empty full binary tree is one less than the number of internal nodes.c)The number of leaves in a non-empty full binary tree is one half of the number of internal nodes.d)The number of internal nodes in a non-empty full binary tree is one half of the number of leaves.5.The correct traversal to use on a BST to visit the nodes in sorted order is:a) Preorder traversal.*b) Inorder traversal.c) Postorder traversal.6. When every node of a full binary tree stores a 4-byte data field,10少年易学老难成,一寸光阴不可轻-百度文库two 4-byte child pointers, and a 4-byte parent pointer, theoverhead fraction is approximately:a)one quarter.b)one third.c)one half.d)two thirds.*e) three quarters.f) none of the above.7.When every node of a full binary tree stores an 8-byte data field and two 4-byte child pointers, the overhead fraction is approximately:a)one quarter.b)one third.*c) one half.d)two thirds.e)three quarters.f)none of the above.8.When every node of a full binary tree stores a 4-byte data field and theinternal nodes store two 4-byte child pointers, the overhead fraction is approximately:a)one quarter.b)one third.*c) one half.d)two thirds.e)three quarters.f)none of the above.9.If a node is at position r in the array implementation for a complete binarytree, then its parent is at:a)) (r - 1)/2 if r > 0b)2r + 1 if (2r + 1) < nc)2r + 2 if (2r + 2) < nd)r - 1 if r is evene)r + 1 if r is odd.10.If a node is at position r in the array implementation for a complete binarytree, then its right child is at:a)(r - 1)/2 if r > 0b)2r + 1 if (2r + 1) < n*c) 2r + 2 if (2r + 2) < nd)r - 1 if r is evene)r + 1 if r is odd.11_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库—11.Assume a BST is implemented so that all nodes in the left subtree of agiven node have values less than that node, and all nodes in the rightsubtree have values greater than or equal to that node. Whenimplementing the delete routine, we must select as its replacement:a) The greatest value from the left subtree.*b) The least value from the right subtree.c) Either of the above.12.Which of the following is a true statement:a)In a BST, the left child of any node is less than the right child, and in a heap, the left child of any node is less than the right child.*b) In a BST, the left child of any node is less than the right child, but in a heap, the left child of any node could be less than or greater than the right child.c)In a BST, the left child of any node could be less or greater than the right child, but in a heap, the left child of any node must be less than the right child.d)In both a BST and a heap, the left child of any node could be either less than or greater than the right child.13.When implementing heaps and BSTs, which is the best answer?a)The time to build a BST of n nodes is O(n log n), and the time to build a heap of n nodes is O(n log n).b)The time to build a BST of n nodes is O(n), and the time to build a heap of n nodes is O(n log n).*c) The time to build a BST of n nodes is O(n log n), and the time to build a heap of n nodes is O(n).d) The time to build a BST of n nodes is O(n), and the time to build a heap of n nodes is O(n).14.The Huffman coding tree works best when the frequencies for letters area) Roughly the same for all letters.*b) Skewed so that there is a great difference in relative frequencies for various letters.15.Huffman coding provides the optimal coding when:a)The messages are in English.b)The messages are binary numbers.*c) The frequency of occurrence for a letter is independent of its context within the message.d) Never.12_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库一Chapter 6 Binary Trees: Instructor's CD questions1.The primary ADT access functions used to traverse a general tree are: a) left child and right siblingb) left child and right child*c) leftmost child and right siblingd) leftmost child and next child2.The tree traversal that makes the least sense for a general treeis:a) preorder traversal*b) inorder traversalc) postorder traversal3.The primary access function used to navigate the general tree when performing UNION/FIND is:a)left childb)leftmost childc)right childd)right sibling*e) parent4.When using the weighted union rule for merging disjoint sets, the maximum depth for any node in a tree of size n will be:a) nearly constant*b) log nc)nd)n log ne)n A25.We use the parent pointer representation for general trees to solve which problem?a)Shortest pathsb)General tree traversal*c) Equivalence classesd) Exact-match query6. When using path compression along with the weighted union rule for merging disjoint sets, the average cost for any UNION or FIND operation in a tree of size n will be:*a) nearly constantb)log nc)nd)n log n13_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库一7.The most space efficient representation for general trees will typically be:a) List of children*b) Left-child/right siblingc) A K-ary tree.8.The easiest way to represent a general tree is to:a) convert to a list.*b) convert to a binary tree.c) convert to a graph.9.As K gets bigger, the ratio of internal nodes to leaf nodes:a)) Gets smaller.b)Stays the same.c)Gets bigger.d)Cannot be determined, since it depends on the particular configuration of the tree.10.A sequential tree representation is best used for:*a) Archiving the tree to disk.b)Use in dynamic in-memory applications.c)Encryption algorithms.d)It is never better than a dynamic representation.Chapter 7 Internal Sorting: Instructor's CD questions1.A sorting algorithm is stable if it:a) Works for all inputs.*b) Does not change the relative ordering of records with identical key values.c) Always sorts in the same amount of time (within a constant factor) for a given input size.2.Which sorting algorithm does not have any practical use?a) Insertion sort.*b) Bubble sort.c)Quicksort.d)Radix Sort.e)a and b.3.When sorting n records, Insertion sort has best-case cost:a)O(log n).14_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库*b) O(n).c)O(n log n).e)O(n!)f)None of the above.4.When sorting n records, Insertion sort has worst-case cost:a)O(log n).b)O(n).c)O(n log n).*d) O(n A2)e)O(n!)f)None of the above.5.When sorting n records, Quicksort has worst-case cost:a)O(log n).b)O(n).c)O(n log n).*d) O(n A2)e)O(n!)f)None of the above.6.When sorting n records, Quicksort has average-case cost:a)O(log n).b)O(n).c)) O(n log n).d)O(n A2)e)O(n!)f)None of the above.7.When sorting n records, Mergesort has worst-case cost:a)O(log n).b)O(n).*c) O(n log n).d)O(n A2)e)O(n!)f)None of the above.8.When sorting n records, Radix sort has worst-case cost:a)O(log n).b)O(n).c)O(n log n).d)O(n A2)e)O(n!)15少年易学老难成,一寸光阴不可轻-百度文库*f) None of the above.9.When sorting n records with distinct keys, Radix sort has a lower bound of:a)Omega(log n).b)Omega(n).*c) Omega(n log n).d)Omega(n A2)e)Omega(n!)f)None of the above.10.Any sort that can only swap adjacent records as an average case lower bound of:a)Omega(log n).b)Omega(n).c)Omega(n log n).*d) Omega(n A2)e)Omega(n!)f)None of the above.11.The number of permutations of size n is:a)O(log n).b)O(n).c)O(n log n).d)O(n A2)*e) O(n!)f)None of the above.12.When sorting n records, Selection sort will perform how many swaps in the worst case?a) O(log n).*b) O(n).c)O(n log n).d)O(n A2)e)O(n!)f)None of the above.13.Shellsort takes advantage of the best-case behavior of which sort?*a) Insertion sortb)Bubble sortc)Selection sortd)Shellsorte)Quicksortf)Radix sort16_______________________________ 少年易学老难成,一寸光阴不可轻-百度文库_______________14.A poor result from which step causes the worst-case behavior for Quicksort?*a) Selecting the pivotb)Partitioning the listc)The recursive call15.In the worst case, the very best that a sorting algorithm can do when sorting n records is:a)O(log n).b)O(n).*c) O(n log n).d)O(n A2)e)O(n!)f)None of the above.Chapter 8 File Processing and External Sorting: Instructor's CD questions1.As compared to the time required to access one unit of data frommain memory, accessing one unit of data from disk is:a)10 times faster.b)1000 times faster.c)1,000,000 time faster.d)10 times slower.e)1000 times slower.*f) 1,000,000 times slower.2.The most effective way to reduce the time required by a disk-based program is to:a) Improve the basic operations.*b) Minimize the number of disk accesses.c)Eliminate the recursive calls.d)Reduce main memory use.3.The basic unit of I/O when accessing a disk drive is:a)A byte.*b) A sector.c)A cluster.d)A track.e)An extent.4.The basic unit for disk allocation under DOS or Windows is:a)A byte.b)A sector.*c) A cluster.17少年易学老难成,一寸光阴不可轻-百度文库d) A track.e) An extent.5.The most time-consuming part of a random access to disk is usually: *a) The seek.b)The rotational delay.c)The time for the data to move under the I/O head.6.The simplest and most commonly used buffer pool replacement strategy is:a)First in/First out.b)Least Frequently Used.*c) Least Recently Used.7.The C++ programmer's view of a disk file is most like:a)) An array.b)A list.c)A tree.d)A heap.8.In external sorting, a run is:a)) A sorted sub-section for a list of records.b)One pass through a file being sorted.c)The external sorting process itself.9.The sorting algorithm used as a model for most external sorting algorithms is:a)Insertion sort.b)Quicksort.*c) Mergesort.d) Radix Sort.10.Assume that we wish to sort ten million records each 10 bytes long (for a total file size of 100MB of space). We have working memory of size 1MB, broken into 1024 1K blocks. Using replacement selection and multiway merging, we can expect to sort this file using how many passes through the file?a)About 26 or 27 (that is, log n).b)About 10.c)4.*d) 2.Chapter 9 Searching: Instructor's CD questions18少年易学老难成,一寸光阴不可轻-百度文库1.Which is generally more expensive?a) A successful search.*b) An unsuccessful search.2.When properly implemented, which search method is generally the most efficient for exact-match queries?a)Sequential search.b)Binary search.c)Dictionary search.d)Search in self-organizing lists*e) Hashing3.Self-organizing lists attempt to keep the list sorted by:a) value*b) frequency of record accessc) size of record4.The 80/20 rule indicates that:a) 80% of searches in typical databases are successful and 20% are not.*b) 80% of the searches in typical databases are to 20% of the records.c) 80% of records in typical databases are of value, 20% are not.5.Which of the following is often implemented using a self-organizing list? *a) Buffer pool.b)Linked list.c)Priority queue.6.A hash function must:a)) Return a valid position within the hash table.b)Give equal probability for selecting an slot in the hash table.c)Return an empty slot in the hash table.7.A good hash function will:a)Use the high-order bits of the key value.b)Use the middle bits of the key value.c)Use the low-order bits of the key value.*d) Make use of all bits in the key value.8.A collision resolution technique that places all records directlyinto the hash table is called:a)Open hashing.b)Separate chaining.*c) Closed hashing.d) Probe function.19少年易学老难成,一寸光阴不可轻-百度文库9.Hashing is most appropriate for:a)In-memory applications.b)Disk-based applications.*c) Either in-memory or disk-based applications.10.Hashing is most appropriate for:a)) Range queries.b)Exact-match queries.c)Minimum/maximium value queries.11.In hashing, the operation that will likely require more record accesses is: *a) insertb) deleteChapter 10 Indexing: Instructor's CD questions1.An entry-sequenced file stores records sorted by:a)Primary key value.b)Secondary key value.*c) Order of arrival.d) Frequency of access.2.Indexing is:a) Random access to an array.*b) The process of associating a key with the location of a corresponding data record.c) Using a hash table.3.The primary key is:a)) A unique identifier for a record.b)The main search key used by users of the database.c)The first key in the index.4.Linear indexing is good for all EXCEPT:a)Range queries.b)Exact match queries.*c) Insertion/Deletion.d)In-memory applications.e)Disk-based applications.5.An inverted list provides access to a data record from its:a) Primary key.20______________________________ 少年易学老难成,一寸光阴不可轻-百度文库*b) Secondary key.c) Search key.6.ISAM degrades over time because:a) Delete operations empty out some cylinders.*b) Insert operations cause some cylinders to overflow.c) Searches disrupt the data structure.7.Tree indexing methods are meant to overcome what deficiency in hashing? *a) Inability to handle range queries.。
2009-2010《数据结构与算法》试卷及答案

四川大学期末考试试题(闭卷)(2009~2010学年第2学期)课程号: 311036030 课程名称:数据结构与算法(B卷)任课教师:孙界平杨秋辉张卫华适用专业年级:软件工程 2009级学号:姓名:考试须知四川大学学生参加由学校组织或由学校承办的各级各类考试,必须严格执行《四川大学考试工作管理办法》和《四川大学考场规则》。
有考试违纪作弊行为的,一律按照《四川大学学生考试违纪作弊处罚条例》进行处理。
四川大学各级各类考试的监考人员,必须严格执行《四川大学考试工作管理办法》、《四川大学考场规则》和《四川大学监考人员职责》。
有违反学校有关规定的,严格按照《四川大学教学事故认定及处理办法》进行处理。
题号一(30%) 二(10%) 三(15%) 四(20%) 五(25%) 卷面成绩得分阅卷时间注意事项:1. 请务必将本人所在学院、姓名、学号、任课教师姓名等信息准确填写在试题纸和添卷纸上;2. 请将答案全部填写在本试题纸上;3. 考试结束,请将试题纸、添卷纸和草稿纸一并交给监考老师。
一、单项选择题(本大题共15小题,每小题2分,共30分)提示:在每小题列评阅教师得分出的四个备选项中只有一个是符合题目要求的,请将其代码填写在答题纸上。
错选、多选或未选均无分。
1. A mathematical function is most like a ( A )(A) Problem(B) Algorithm(C) Program(D) Code2. A recurrence relation is often used to model programs with ( C )(A) for loops.(B) branch control like "if" statements.(C) recursive calls.(D) function calls.3. For an air traffic control system, the most important metric is: ( C )(A) The best-case upper bound.(B) The average-case upper bound.(C) The worst-case upper bound.(D) The best-case lower bound.4. For a list of length n, the linked-list implementation's prev() function requires worst-case time: ( C )(A) O(1).(B) O(log n).(C) O(n).(D) O(n2).5. Assume a BST is implemented so that all nodes in the left subtree of a given node have values less than that node, and all nodes in the right subtree have values greater than or equal to that node. When implementing the delete routine, we must select as its replacement: ( B )(A) The greatest value from the left subtree.(B) The least value from the right subtree.(C) Either of the above.(D) The root.6. The primary ADT access functions used to traverse a general tree are: ( C )(A) left child and right sibling(B) left child and right child(C) leftmost child and right sibling(D) leftmost child and next child7. A sorting algorithm is stable if it: ( B )(A) Works for all inputs.(B) Does not change the relative ordering of records with identical key values.(C) Always sorts in the same amount of time (within a constant factor) for a given input size.(D) Most efficient.8. When sorting n records, Quicksort has worst-case cost: ( D )(A) O(log n).(B) O(n).(C) O(n log n).(D) O(n2)9. The basic unit of I/O when accessing a disk drive is: ( B )(A) A byte.(B) A sector.(C) A cluster.(D) A track.10. The sorting algorithm used as a model for most external sorting algorithms is: ( C )(A) Insertion sort.(B) Quicksort.(C) Mergesort.(D) Radix Sort.11. Which of the following is often implemented using a self-organizing list? ( A )(A) Buffer pool.(B) Linked list.(C) Priority queue.(D) B-Tree12. An entry-sequenced file stores records sorted by: ( C )(A) Primary key value.(B) Secondary key value.(C) Order of arrival.(D) Frequency of access.13. The primary difference between a B-tree and a B+-tree is: ( A )(A) The B+-tree store records only at the leaf nodes.(B) The B+-tree has a higher branching factor.(C) The B+-tree is hight balanced.(D) The B+-tree is smaller.14. The goal of a topological sort is to: ( B )(A) Sort all of the graph vertices by value.(B) Sort all of the graph vertices so that each vertex is listed prior to any others that depend onit.(C) Sort all of the graph vertices by distance from the source vertex.(D) None of the above.15. Which is a good example of a greedy algorithm? ( B )(A) Floyd's all-pairs shortest path algorithm.(B) Prim's minimal-cost spanning tree algorithm.(C) Depth-first search.(D) T opological sorting.二、判断题(本大题共5小题,每小题2分,共10分)提示:正确打T,错误打F,评阅教师得分将其结果填写在答题纸上。
四川大学《数据结构》课程综合练习题——高起专计算机应用技术专业5

四、算法设计题 1、二维数组 a[m][n]和 b[m][n] void matrixadd(int a[m][n], int b[m][n], c[m][n]) { int j, k; for (j = 0; j < m; j++) { for (k = 0; k < n; k++) { c[j][k] = a[j][k] + b[j][k]; } } } 2、上面所列的几种排序方法的速度都很块,但快速排序、归并排序、基数排序和希尔排序都是在
(n-1)+(n-2)+(n-3)+…+2+1=n(n-1)/2 所以其结论成立。 3、不合适。因为一个城市的设计和规划涉及非常多的项目,很复杂,经常需要修改、 扩充和删除 各种信息,才能适应不断发展的需要。有鉴于此,顺序线性表不能很好适应其需要,故是不合适的。
4、具有 3 个结点的树
具有 3 个结点的二叉树
CBED 和 HGIJF 依此可推出前序遍历的左、右子树的结点序列为
BCDE 和 FGHIJ B 和 F 又分别为左、右子树的根结点,进而又可推出以 B 为根结点的左、右子树,以及 以 F 为根 结点的左、右子树。依此类推,可推出二叉树见下图。ABFC
DG
EH
I
J
三、简答题 1、共有 5 种不同形态的二叉树,具体如下:
2、证明 方法一:用归纳法证明 当 n=1 时,边数为 0,结论成立。 当 n=2 时,边数为 1,结论成立。 当 n=1,2…,k 时均成立,即当 n=k 时,边数为 k(k-1)/2。现证明当 n=k+1 时若仍然 成立,
则结论正确。 由前面证得,对于有 k 个顶点时,其边数总和为 k(k-1)/2。 当再增加一个新顶点时,由于是无向完全图,故该顶点到原来各个顶点均有一条边, 这样就共有
(完整word版)四川大学计算机学院数据结构与算法分析期末试题(2013级A)
注:试题字迹务必清晰,书写工整。
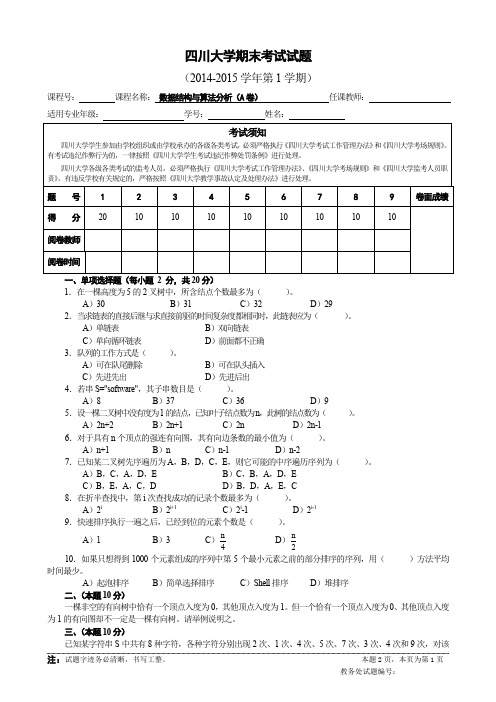
本题2页,本页为第1页教务处试题编号:四川大学期末考试试题(2014-2015学年第1学期)课程号: 课程名称: 数据结构与算法分析(A 卷) 任课教师:适用专业年级: 学号:姓名:1.在一棵高度为5的2叉树中,所含结点个数最多为( )。
A )30B )31C )32D )292.当求链表的直接后继与求直接前驱的时间复杂度都相同时,此链表应为( )。
A )单链表B )双向链表C )单向循环链表D )前面都不正确 3.队列的工作方式是( )。
A )可在队尾删除B )可在队头插入C )先进先出D )先进后出 4.若串S="software",其子串数目是( )。
A )8B )37C )36D )95.设一棵二叉树中没有度为1的结点,已知叶子结点数为n ,此树的结点数为( )。
A )2n+2B )2n+1C )2nD )2n-1 6.对于具有n 个顶点的强连有向图,其有向边条数的最小值为( )。
A )n+1B )nC )n-1D )n-27.已知某二叉树先序遍历为A ,B ,D ,C ,E ,则它可能的中序遍历序列为( )。
A )B ,C ,A ,D ,E B )C ,B ,A ,D ,E C )B ,E ,A ,C ,D D )B ,D ,A ,E ,C 8.在折半查找中,第i 次查找成功的记录个数最多为( )。
A )2iB )2i+1C )2i -1D )2i-1 9.快速排序执行一遍之后,已经到位的元素个数是( )。
A )1B )3C )4nD )2n10.如果只想得到1000个元素组成的序列中第5个最小元素之前的部分排序的序列,用( )方法平均时间最少。
A )起泡排序B )简单选择排序C )Shell 排序D )堆排序 二、(本题10分)一棵非空的有向树中恰有一个顶点入度为0,其他顶点入度为1。
但一个恰有一个顶点入度为0、其他顶点入度为1的有向图却不一定是一棵有向树。
【精品】川大数据结构期终复习.doc

模拟试题(一)一、单项选择题(每小题2分,共20分)(1)以下数据结构中哪一个是线性结构?()A)有向图B)队列C)线索二叉树D) B树(2)在一个单链表HL屮,若要在当前由指针p指向的结点后面插入一个由q指向的结点,则执行如下()语句序列。
A)p=q; p->next=q; B ) p->next=q; q->next=p;C) p->next=q->next; p=q; D) q->next=p->next; p->next=q;(3)()不是队列的基本运算。
A)在队列第i个元素之后插入一个元素B)从队头删除一个元素C)判断一个队列是否为空D)读取队头元素的值(4)字符A、B、C依次进入一个栈,按出栈的先后顺序组成不同的字符串,至多可以组成()个不同的字符串。
A)14 B) 5 C) 6 D) 8(5)由权值分别为3,&6,2的叶子生成一棵哈夫曼树,它的带权路径长度为()o A)11 B) 35 C) 19 D) 53 以下6・8题基于下图:(6)该二叉树结点的前序遍历的序列为()。
A) E、G、F、A、C、D、B B)E、A、G、C、F、B、DC) E、A、C、B、D、G、F D)E、G、A、C、D、F、B (7)该二叉树结点的中序遍历的序列为()OA) A、B、C、D、E、G、F B)E、A^ G^ C、F、B、DC) E、A、C、B、D、G、F D)B、D、C、A^ F、G^ E (8)该二叉树的按层遍历的序列为()OA) E、G、F、A、C、D、B B)E> A、C、B、D、G、FC) E、A、G、C、F、B、D D)E、G、A^ C^ D、F、B (9)下血关于图的存储的叙述中正确的()oA)用邻接表法存储图,占用的存储空间大小只与图中边数有关,而与顶点个数无关B)用邻接表法存储图,占用的存储空间大小与图中边数和顶点个数都有关C)用邻接矩阵法存储图,占用的存储空间大小与图中顶点个数和边数都有关D)用邻接矩阵法存储图,占用的存储空间大小只与图中边数有关,而与顶点个数无关(10)设有关键字序列Cq; g, W, 'z; 'a; h, p, 'x; h),下面哪一个序列是从上述序列出发建堆的结果?()A)匕,g V, d, p, q, 乂, *z B)工g 'h; q, h, p, * N c)g m, q, x h,p, ‘X;h, h D) h, g m,p, 'a',h, q, ‘X; r二、(每小题4分,共8分)已知一个6x5稀疏矩阵如下所示,试:(1)写出它的三元组线性表;(2)给岀三元组线性表的顺序存储表示。
数据结构与算法分析习题及参考答案
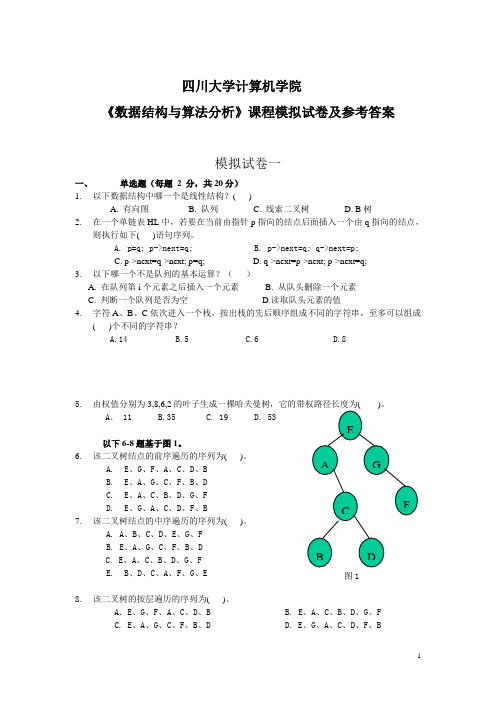
四川大学计算机学院《数据结构与算法分析》课程模拟试卷及参考答案模拟试卷一一、单选题(每题2 分,共20分)1.以下数据结构中哪一个是线性结构?( )A. 有向图B. 队列C. 线索二叉树D. B树2.在一个单链表HL中,若要在当前由指针p指向的结点后面插入一个由q指向的结点,则执行如下( )语句序列。
A. p=q; p->next=q;B. p->next=q; q->next=p;C. p->next=q->next; p=q;D. q->next=p->next; p->next=q;3.以下哪一个不是队列的基本运算?()A. 在队列第i个元素之后插入一个元素B. 从队头删除一个元素C. 判断一个队列是否为空D.读取队头元素的值4.字符A、B、C依次进入一个栈,按出栈的先后顺序组成不同的字符串,至多可以组成( )个不同的字符串?A.14B.5C.6D.85.由权值分别为3,8,6,2A. 11 B.35 C. 19 D. 53以下6-8题基于图1。
6.该二叉树结点的前序遍历的序列为( )。
A.E、G、F、A、C、D、BB.E、A、G、C、F、B、DC.E、A、C、B、D、G、FD.E、G、A、C、D、F、B7.该二叉树结点的中序遍历的序列为( )。
A. A、B、C、D、E、G、FB. E、A、G、C、F、B、DC. E、A、C、B、D、G、FE.B、D、C、A、F、G、E8.该二叉树的按层遍历的序列为( )。
A.E、G、F、A、C、D、B B. E、A、C、B、D、G、FC. E、A、G、C、F、B、DD. E、G、A、C、D、F、B9.下面关于图的存储的叙述中正确的是( )。
A.用邻接表法存储图,占用的存储空间大小只与图中边数有关,而与结点个数无关B.用邻接表法存储图,占用的存储空间大小与图中边数和结点个数都有关C. 用邻接矩阵法存储图,占用的存储空间大小与图中结点个数和边数都有关D.用邻接矩阵法存储图,占用的存储空间大小只与图中边数有关,而与结点个数无关10.设有关键码序列(q,g,m,z,a,n,p,x,h),下面哪一个序列是从上述序列出发建堆的结果?( )A. a,g,h,m,n,p,q,x,zB. a,g,m,h,q,n,p,x,zC. g,m,q,a,n,p,x,h,zD. h,g,m,p,a,n,q,x,z二、填空题(每空1分,共26分)1.数据的物理结构被分为_________、________、__________和___________四种。
数据结构与算法分析 复习试卷B1

四川大学期末考试试题(闭卷)(2009~2010学年第1学期)课程号:311036030课程名称:数据结构与算法分析(B卷)任课教师:孙界平,张卫华适用专业年级:软件工程 2008级学号:姓名:注意事项:1. 请务必将本人所在学院、姓名、学号、任课教师姓名等信息准确填写在试题纸和添卷纸上;2. 请将答案全部填写在本试题纸上;3. 考试结束,请将试题纸、添卷纸和草稿纸一并交给监考老师。
一、单项选择题(本大题共20小题,每小题2分,共40分)提示:在每小题列评阅教师得分出的备选项中只有一个是符合题目要求的,请将其代码写到答题纸上。
错选、多选或未选均无分。
1. A set has the following properties:a) May have duplicates, element have a position.b) May have duplicates, elements do not have a position.c) May not have duplicates, elements have a position.*d) May not have duplicates, elements do not have a position.2 Which of the following is not a good proof technique.a) proof by contradiction.*b) proof by example.c) proof by mathematical induction.3. When we wish to describe the upper bound for a problem we use:*a) The upper bound of the best algorithm we know.b) The lower bound of the best algorithm we know.c) We can't talk about the upper bound of a problem because there can always be an arbitrarily slow algorithm.4. The best case for an algorithm refers to:a) The smallest possible input size.*b) The specific input instance of a given size that gives the lowest cost.c) The largest possible input size that meets the required growth rate.d) The specific input instance of a given size that gives the greatest cost.5. In the linked-list implementation presented in the book, a header node is used:*a) T o simplify special cases.b) Because the insert and delete routines won't work correctly without it.c) Because there would be no other way to make the current pointer indicate the first element on the list.6. Recursion is generally implemented usinga) A sorted list.*b) A stack.c) A queue.7. The relationship between a full and a complete binary tree is:a) Every complete binary tree is full.b) Every full binary tree is complete.*c) None of the above.8. When every node of a full binary tree stores a 4-byte data field and the internal nodes store two 4-byte child pointers, the overhead fraction is approximately:a) one quarter.b) one third.*c) one half.d) two thirds.e) three quarters.f) none of the above.9. Which of the following is a true statement:a) In a BST, the left child of any node is less than the right child, and in a heap, the left child of any node is less than the right child.*b) In a BST, the left child of any node is less than the right child, but in a heap, the left child of any node could be less than or greater than the right child.c) In a BST, the left child of any node could be less or greater than the right child, but in a heap, the left child of any node must be less than the right child.d) In both a BST and a heap, the left child of any node could be either less than or greater than the right child.10. Huffman coding provides the optimal coding when:a) The messages are in English.b) The messages are binary numbers.*c) The frequency of occurrence for a letter is independent of its context within the message.d) Never.11. A sorting algorithm is stable if it:a) Works for all inputs.*b) Does not change the relative ordering of records with identical key values.c) Always sorts in the same amount of time (within a constant factor) for a given input size.12. When sorting n records, Quicksort has worst-case cost:a) O(log n).b) O(n).c) O(n log n).*d) O(n^2)e) O(n!)f) None of the above.13. A poor result from which step causes the worst-case behavior for Quicksort?*a) Selecting the pivotb) Partitioning the listc) The recursive call14. The basic unit of I/O when accessing a disk drive is:a) A byte.*b) A sector.c) A cluster.d) A track.e) An extent.15. The most time-consuming part of a random access to disk is usually:*a) The seek.b) The rotational delay.c) The time for the data to move under the I/O head.16. Self-organizing lists attempt to keep the list sorted by:a) value*b) frequency of record accessc) size of record17. A hash function must:*a) Return a valid position within the hash table.b) Give equal probability for selecting an slot in the hash table.c) Return an empty slot in the hash table.18. An entry-sequenced file stores records sorted by:a) Primary key value.b) Secondary key value.*c) Order of arrival.d) Frequency of access.19. An inverted list provides access to a data record from its:a) Primary key.*b) Secondary key.c) Search key.20. The goal of a topological sort is to:a) Sort all of the graph vertices by value.*b) Sort all of the graph vertices so that each vertex is listed prior to any others that depend on it.c) Sort all of the graph vertices by distance from the source vertex.二、判断题(本大题共8小题,每小题1分,共8分)提示:正确答T,错误答F,评阅教师得分将其结果写到答题纸上。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
第3章算法分析
课后习题:(第三版)3.3 3.8
课后习题:(第三版)3.12 3.14
补充作业题
综合题
1.某学校对教师每月工资的计算公式如下:固定工资+课时补贴。
教授的固定工资为5000元,每个课时补贴50元;副教授的固定工资为3000元,每个课时补贴30元;讲师的固定工资为2000元,每个课时补贴20元。
定义教师抽象类,派生不同职称的教师类,编写程序求若干教师的月工资。
2.定义类模板CThree储存三个成员变量,成员函数Min返回其中的最小值,成员函数Max 返回其中的最大值。
并自拟数据调用成员函数求最大值最小值。
