毕设外文翻译电子版
(完整版)_毕业设计外文翻译_外文原文
(完整版)_毕业设计外⽂翻译_外⽂原⽂Annual Reviews in Control 31 (2007) 211⼀20Future trends in process automation Helsinki University of Technology, Laboratory of Process Control and Automation, Kemistintie 1, FI Espoo, FinlandReceived 27 April 2007Accepted 29 August 2007Available online 29 October 2007AbstractThe importance of automation in the process industries recent years. In the serves to enhance product quality, master the whole range of products, improve process safety and plant availability, efficiently utilize resources and lower emissions. In the rapidly developing countries, mass production is the main motivation for applying process automation. The greatest demand for process automation is in the chemical industry, power generating industry, and petrochemical industry; the fastest growing demand for is in the pharmaceutical industry.The importance of automation technology continues to increase in the process industries. The traditional barriers between information, communication and automation technology are, in the operational context, gradually disappearing. The latest technologies, including wireless networks, field bus systems and asset management systems, boost the efficiency of process systems. New application fields like biotechnology and microtechnology pose challenges for future theoretical work in the modeling, analysis and design of control systems. In this paper the industry trends that are shaping current automation requirements, as well as the future trends in process automation, are presented and discussed.KeywordsProcess automation;Future trends1. IntroductionThe starting points in assessing the future needs for automation are, on the one the other, the way in which they are reflected in the development of society and the economy. Global risk management willattain ever greater importance in the future. In particular, better control and anticipation is needed in order to contain the risks related to the economy, environment, energy and infrastructure. Faced with climate change and a growing scarcity of raw materials, the world needs to find and develop new environmental and energy solutions. The world's water supply is also in need of development. International competition and global business environments reach everywhere. Business operations and capital markets are dynamic; they seek environments that offer the best opportunities for success in open competition. In addition to business and production, also R&D seeks the best possible operational environments. Economic, organizational and technological trends will cause significant changes in automation technology during the next few years.By developing technologies, it is possible to find solutions to the basic needs of society and the industry. The development of technology all of the current competitive advantages and to create new ones in many new fields, thus further improving prosperity and well-being. The development of of new cooperation models: networking among business companies, universities and research institutes, as well asdecision-makers in the public sector. A trans-disciplinary approach e.g. in materials development requires expertise in physics, chemistry, biomaterials, electronics, communications, programming and automation.Globalization along brings with it social challenges and problems in the interaction between different population groups and cultures. The growth of multiculturalism requires new management practices, knowledge of foreign cultures, and the ability to support and take advantage of the existence of minorities and difference. The management and development of skills and competences in a decentralized organization is becoming increasingly important.The importance of automation in the process industry recent years. It the entire chemical, oil, gas and biotechnology industries. Innovative instrumentation systems now control complex processes, ensuring process reliability and safety, and provide a basis for advanced maintenance strategies. Incessant cost pressures in the chemical and bioindustries leave no alternative to improved productivity. Companies need to take a engineering will play a central role. Process controlensures that the plant assets continuously operate predictably within the most profitable range, leading to a greater output of consistent products, reliability, yield and quality using less energy. This technology will and retrofitting activity designed to increase flexibility.In this paper the industry trends that are shaping current automation requirements, as well as the future trends in process automation, are presented and discussed. The paper is structured as follows: In Section 2 development of the automation market for the process industries up until 2010 is presented: market developments by industries, regions and product and services. In Section 3 future automation technology trends, like the integration of production and business operations and industrial communication technologies, are discussed. The paper ends with recent accomplishments and future application trends in process automation.2. Development of the automation market for the process industries up until 20102.1. Market developments by industriesAccording to the report by Intechno Consulting (Basel, Switzerland), the world market for process automation will grow at an average annualrate of 5.1% between 2005 and 2010 to reach 94.2 billion $ in 2010. The greatest demand for process automation is in the chemical industry, power generating industry, and petrochemical industry; the fastest growing demand for is in the pharmaceutical industry. The share of in individual application sectors.Fig.1. Development of the world market for process automation up until2010—segmentation by industries2.2. Market development by regionsNorth America is the leading market for process automation.Asia-Pacific and Eastern Europe are winning market shares from Western Europe and North America. China is a growing engine for automation in Asia, in spite of its lower levels of plant automation. India, too, is gaining market shares worldwide. In the serves to enhance product quality, master the whole range of products, improve process safety and plant availability, efficiently utilize resources and lower emissions. In the rapidly developing countries, mastering mass production is the main motivation for applying process automation. Quality and environmental aspects are, 2000 were for the process control level, and 60.7% for the field level, including all sensors, measurement equipment, and actuators integrated in the various process technological machines. By 2010, the share of control level in field bus communication and EthernetTCP-IP components. The former is expected to grow at a rate of 8.2%year, and that of the latter should be around 17%.The share of external engineering demand will keep increasing worldwide. It is expected to rise from 13.9% in 2000 to 15.5% in 2010. Engineering expenditures are expected to further increase, especially inthose industries with prototype plants. The trend towards rationalization and plant optimization, accompanied by increased integration of automation systems with the information systems of the production site and the enterprise level, will further addto the engineering share out of the total plant project costs.3. Future technology trends in automation3.1. Current status of the industrial communication technologiesEvolution of communication technologies changes in the structure of industrial automation systems. Up until now, communication support in plant automation systems defined according to the computer integrated manufacturing (CIM) concept. In this such a way that each device is designed for a specific task, and specific networks are used to interconnect devices at the same level, i.e. those running the same task.However, the devices one function, or module, which increases the intelligence level of the equipment automation. Devices like sensors that used for measurement now architecture. Nevertheless, themost of the process control strategies.A brief survey of the most important industrial, low-layer protocols(referring to the ISO model) is given in the following. In addition, some currently essential or emerging protocolsThe most widely available industrial networks at the present time can be classified into three main categories: traditional fieldbusses, Ethernet-based networks and wireless networks.The worldwide leaders within the automation domain with respect to the number of installed Fieldbus nodes are nodes) and Interbus (about 7 million nodes). A good commercial position is also Fieldbus. Fieldbus technology industrial automation, and fulfills the current technical requirements of local industrial communications at the field level of an enterprise.HART and Foundation Fieldbus this diagnostic capability to the process surrounding the instrument. As this trend continues, we will benefit from predictive intelligence. We will know more about the of potential problems and profit-draining inefficiencies. We will move from abnormal situation management to abnormal situation prevention.The increased data transfer needs of the currently popular office network technology – Ethernet-based networks – into industrialenvironments. Several organizations (e.g. IAONA (Industrial Automation Networking Alliance)) are promoting the use of Ethernet in industrial automation. In these applications, the fieldbus standards also include Ethernet-based networks, which implement the Ethernet protocol in low layers. The main development area is the real-time requirements of these networks. Currently, the working group IEC (International Electrotechnical Commission) WG11 is refining the RTE requirements. The Ethernet-based industrial networks included in the IEC 61784 standard are: EthernetIP, Profinet, Interbus, VnetIP, TCnet, EtherCAT, Powerlink, Modbus TCP and Sercos III.In the same way as for Ethernet, the wireless architectures , 2000) and the network currently under development IEEE 802.15.4ZigBee (IEEE, 2003).Wireless communication the process industry. The technology the production floor can remain in contact with the control centre. Isolated instrumentation, for example pump stations located at remote sites in the mountains, can be integrated into the automation strategy. Wireless technology also offers the advantage of flexibility. Ease of use,visualization, parametrization, and diagnostics through remote links are important considerations.3.1.2. High-layer data specificationsThe communication part of an automation device might order to manage these different types of data, the communication stack defines of the information sources and to the specification of the product data and safety and security data.The information standards for process operation and maintenance are driven by OpenO&M Initiative joint working groups, mainly representing three industrial organizations: MIMOSA (for the asset management related information standards), the OPC Foundation (for data transport standards) and ISA's SP95 (for Enterprise-Control System Integration Standards Committee). One of the most strongly established standards, the OPC, also enables the use of state of the art technologies such as web services, the ability to provide secure data exchange, and the use of encapsulated data with eXtensible Markup Language (XML). On the other Fieldbus) of field devices.3.2. Integration of production and business operationsPlants in the different process industry fields must be seen as production systems: their elements are the process (material transformation), inbound logistics (material transport), the plant (physical shell), automation (automatic operation) and organization (manual operation, supervision, management). Operation is a collaborative process of this production system.Optimization means the best allocation of functions to these components of the production system. This integrated approach is increasingly being expanded to production networks representing complete value-creating production chains. Suppliers and customers are often included in this approach.Virtually seamless of information, communications and automation technology throughout the whole organization is thus needed in order to address the complexity of today's processes. The buzzword in the industry is seamless communications. Manufacturing Execution Systems (MES), which are normally positioned between the Enterprise Resource Planning (ERP) and control system levels, can be used to optimize a business process on the shop floor, improve product quality, increase process reliability and reduce compliance and validation efforts. The well-known production control (MES) systems in the process industriesinclude ABB industrial IT production Planning, Honeywell Experion PKS-Optivision, Metso DNA MES, Tietoenator TIPS and Siemens Simatic IT-Systems. The main modules of the ERP systems are Master Production Schedule, Material Requirements Planning, Logistics and Customer Service Management. The market leader of the ERP systems is the German SAP AG. i2 Technolgies, and ASP AG APO systems are correspondingly the most common APS systems on the market for supply chain management. Plant optimization, accompanied by increased integration of automation systems with the information systems of the production site and the enterprise level, is justifiable also expected to be the main objective of the process automation in these enterprises in the near future.4. Recent accomplishments and future application trends in process automation4.1. Process control and MPCModel predictive control in the continuous process industry, and now covers over 90% of industrial implementations of multivariable control. One reason for its success is its ability to of MPC controlapplication was presented by Richalet, and the developed software was called IDCOM. The dynamic matrix control (DMC) algorithm also represented the first generation of MPC technology and was developed by Shell Oil engineers.A successful industrial controller for the process industries must maintain the system as close as possible to the constraints. The second generation MPC algorithm, like QDMC, provided a systematic way to implement these input and output constraints, but there was no clear way to MPC algorithms distinguished between several levels of constraints ( infeasible solution, addressed the issues resulting from a control structure that changes in real-time, provided a richer set of feedback options, and allowed for a wider range of process dynamics (stable, integrating and unstable) and controller specifications. The increased competition and mergers of several MPC vendors fourth generation MPC products: RMPCT offered by Honeywell, and DMC-plus offered by Aspen Technology with features such as multiple optimization levels to address prioritized control objectives, additional flexibility in thesteady-state target optimization including QP and economic objectives, direct consideration of model uncertainty (robust control design), andimproved identification technology based on prediction error methods and sub-space methods.Thousands of MPC applications reported in a wide variety of application areas. Most of them in refining, but a significant number of applications can also be found in the petrochemical and chemical sectors. Significant growth areas include the pulp and paper and food processing industries. The first multivariable MPC technology to cover the entire papermaking line published . The largest number of nonlinear MPC applications encompass chemicals, polymers and air and gas processing, The size and scope of NMPC applications are typically much smaller than those of linear MPC applications.Major developments in the process control community in general aiming at contributions to systems and control theory are expected, e.g. in nonlinear optimal control, combined state and parameter estimation for nonlinear systems, robustness analysis and robust synthesis methods for nonlinear systems, spatial decomposition, decentralization and of large-scale nonlinear network-like processes and future trends in process control see (Dochain.2006).4.2. Applications of AI methodsMost of the applications of the AI methods in the process industries designed for unit processes in the beginning of the production chain, especially in pulping, mineral and metal processing. A typical feature of these processes is the difficulties involved in constructing detailed mechanistic models. Increasing international competition is forcing the process industry to be more efficient and to emphasize the importance of the be found in the area of quality control of the end products, where a small improvement in control can give a considerable competitive edge to the enterprise compared to its competitors.The importance of artificial intelligence techniques in real-time process control is emphasized in many of the published articles, and the MM processes especially are reported to benefit from the application of AI techniques.4.3. Process monitoring and fault diagnosisMonitoring the quality of the product online and predictingpreventing process disturbances are the key issues in producing chain, and thereby improving the efficiency. Operational safety of processes is ofimportance and therefore should be the first objective of process control. Problems caused by operational faults range from increased operational costs to forced shutdown of processes. The increased complexity and the degree of integration of modern chemical plants means that the potential economic loss is greater and the diagnosis of fault locations more difficult. It is estimated that inadequate management of abnormal process situations causes annual losses of US$ 20 billion in the petrochemical industry in the USA. Consequently, managing disturbances is seen as the next challenge in developing and implementing new control systems.Venkatasubramanian published a review of monitoring methods, especially those applied in the field of chemical processes. They classified the methods according to the form of process knowledge used. One category is based on process models, and includes both qualitative causal models and quantitative methods. The other category is based on process reviewed,e.g. by Komulainen.4.4. The new extended role of operators and operator-support systemsIn recent years the process industry and information technologies in order to remain competitive. This where massive amounts of measurement data are now available. At the same time, the technology the operator's work are the management of critical situations and decision making in a range of problem situations. In critical situations, the decisions must be made quickly and therefore all the relevant information must be readily and easily accessible.A study to analyse the features and use of the operator's support systems at two Finnish paper mills carried out . Automation systems at the plant include a variety of solutions provided by different vendors and which in use for very different periods of time. The production lines management systems: process control, machine control, quality control, web inspection, process analysis, production planning, and condition and runnability monitoring systems. One planning systems. According to the study, only 30–40% of the existing operator-support systems currently installed at production sites were actually used due to the usability problems and operators’ poor knowledge of the systems. The main reasons for infrequent use of process operation support systems are presented in .Most of the information affecting the decision-making process during the critical situations is so called tacit knowledge. Ensuring that this tacit knowledge is retained as large groups of older operators retire, especially in Europe, will be an additional challenge for the process industry. In the future, the efficient management of knowledge supporting the decision making will thus become more and more important. One clear trend in the development of process control systems is to include features for knowledge and information management. The knowledge and performance support systems will be integrated as a part of process control systems, making it an optimal solution to support operations in the whole production line.The study of interactions between and machines is an important aspect in the adoption of control technologies, and involves both technical issues and social implications. Human machine studies consider all the conditions where , modeling and evaluation of machine systems (HMS), which include decision-making and cognitive processes, modeling of performance, real and virtual environments, design methodology, task allocation-sharing and job design, intelligent interfaces, operator support, work organization, and selection and。
毕业设计中英文翻译【范本模板】
英文The road (highway)The road is one kind of linear construction used for travel。
It is made of the roadbed,the road surface, the bridge, the culvert and the tunnel. In addition, it also has the crossing of lines, the protective project and the traffic engineering and the route facility。
The roadbed is the base of road surface, road shoulder,side slope, side ditch foundations. It is stone material structure, which is designed according to route's plane position .The roadbed, as the base of travel, must guarantee that it has the enough intensity and the stability that can prevent the water and other natural disaster from corroding.The road surface is the surface of road. It is single or complex structure built with mixture。
The road surface require being smooth,having enough intensity,good stability and anti—slippery function. The quality of road surface directly affects the safe, comfort and the traffic。
毕设外文原文及译文

北京联合大学毕业设计(论文)任务书题目:OFDM调制解调技术的设计与仿真实现专业:通信工程指导教师:张雪芬学院:信息学院学号:2011080331132班级:1101B姓名:徐嘉明一、外文原文Evolution Towards 5G Multi-tier Cellular WirelessNetworks:An Interference ManagementPerspectiveEkram Hossain, Mehdi Rasti, Hina Tabassum, and Amr AbdelnasserAbstract—The evolving fifth generation (5G) cellular wireless networks are envisioned to overcome the fundamental challenges of existing cellular networks, e.g., higher data rates, excellent end-to-end performance and user-coverage in hot-spots and crowded areas with lower latency, energy consumption and cost per information transfer. To address these challenges, 5G systems will adopt a multi-tier architecture consisting of macrocells, different types of licensed small cells, relays, and device-to-device (D2D) networks to serve users with different quality-of-service (QoS) requirements in a spectrum and energy-efficient manner. Starting with the visions and requirements of 5G multi-tier networks, this article outlines the challenges of interference management (e.g., power control, cell association) in these networks with shared spectrum access (i.e., when the different network tiers share the same licensed spectrum). It is argued that the existing interference management schemes will not be able to address the interference management problem in prioritized 5G multitier networks where users in different tiers have different priorities for channel access. In this context, a survey and qualitative comparison of the existing cell association and power control schemes is provided to demonstrate their limitations for interference management in 5G networks. Open challenges are highlighted and guidelines are provided to modify the existing schemes in order to overcome these limitations and make them suitable for the emerging 5G systems.Index Terms—5G cellular wireless, multi-tier networks, interference management, cell association, power control.I. INTRODUCTIONTo satisfy the ever-increasing demand for mobile broadband communications, the IMT-Advanced (IMT-A) standards have been ratified by the International Telecommunications Union (ITU) in November 2010 and the fourth generation (4G) wireless communication systems are currently being deployed worldwide. The standardization for LTE Rel-12, also known as LTE-B, is also ongoing and expected to be finalized in 2014. Nonetheless, existing wireless systems will not be able to deal with the thousand-fold increase in total mobile broadband data [1] contributed by new applications and services such as pervasive 3D multimedia, HDTV, VoIP, gaming, e-Health, and Car2x communication. In this context, the fifth generation (5G) wireless communication technologies are expected to attain 1000 times higher mobile data volume per unit area,10-100 times higher number of connecting devices and user data rate, 10 times longer battery life and 5 times reduced latency [2]. While for 4G networks the single-user average data rate is expected to be 1 Gbps, it is postulated that cell data rate of theorder of 10 Gbps will be a key attribute of 5G networks.5G wireless networks are expected to be a mixture of network tiers of different sizes, transmit powers, backhaul connections, different radio access technologies (RATs) that are accessed by an unprecedented numbers of smart and heterogeneous wireless devices. This architectural enhancement along with the advanced physical communications technology such as high-order spatial multiplexing multiple-input multiple-output (MIMO) communications will provide higher aggregate capacity for more simultaneous users, or higher level spectral efficiency, when compared to the 4G networks. Radio resource and interference management will be a key research challenge in multi-tier and heterogeneous 5G cellular networks. The traditional methods for radio resource and interference management (e.g., channel allocation, power control, cell association or load balancing) in single-tier networks (even some of those developed for two-tier networks) may not be efficient in this environment and a new look into the interference management problem will be required.First, the article outlines the visions and requirements of 5G cellular wireless systems. Major research challenges are then highlighted from the perspective of interference management when the different network tiers share the same radio spectrum. A comparative analysis of the existing approaches for distributed cell association and power control (CAPC) is then provided followed by a discussion on their limitations for5G multi-tier cellular networks. Finally, a number of suggestions are provided to modifythe existing CAPC schemes to overcome these limitations.II. VISIONS AND REQUIREMENTS FOR 5G MULTI-TIERCELLULAR NETWORKS5G mobile and wireless communication systems will require a mix of new system concepts to boost the spectral and energy efficiency. The visions and requirements for 5G wireless systems are outlined below.·Data rate and latency: For dense urban areas, 5G networks are envisioned to enable an experienced data rate of 300 Mbps and 60 Mbps in downlink and uplink, respectively, in 95% of locations and time [2]. The end-to- end latencies are expected to be in the order of 2 to 5 milliseconds. The detailed requirements for different scenarios are listed in [2].·Machine-type Communication (MTC) devices: The number of traditional human-centric wireless devices with Internet connectivity (e.g., smart phones, super-phones, tablets) may be outnumbered by MTC devices which can be used in vehicles, home appliances, surveillance devices, and sensors.·Millimeter-wave communication: To satisfy the exponential increase in traffic and the addition of different devices and services, additional spectrum beyond what was previously allocated to 4G standard is sought for. The use of millimeter-wave frequency bands (e.g., 28 GHz and 38 GHz bands) is a potential candidate to overcome the problem of scarce spectrum resources since it allows transmission at wider bandwidths than conventional 20 MHz channels for 4G systems.·Multiple RATs: 5G is not about replacing the existing technologies, but it is about enhancing and supporting them with new technologies [1]. In 5G systems, the existing RATs, including GSM (Global System for Mobile Communications), HSPA+ (Evolved High-Speed Packet Access), and LTE, will continue to evolve to provide a superior system performance. They will also be accompanied by some new technologies (e.g., beyondLTE-Advanced).·Base station (BS) densification: BS densification is an effective methodology to meet the requirements of 5G wireless networks. Specifically, in 5G networks, there will be deployments of a large number of low power nodes, relays, and device-to-device (D2D) communication links with much higher density than today’s macrocell networks.Fig. 1 shows such a multi-tier network with a macrocell overlaid by relays, picocells, femtocells, and D2D links. The adoption of multiple tiers in the cellular networkarchitecture will result in better performance in terms of capacity, coverage, spectral efficiency, and total power consumption, provided that the inter-tier and intratier interferences are well managed.·Prioritized spectrum access: The notions of both trafficbased and tier-based Prioriti -es will exist in 5G networks. Traffic-based priority arises from the different requirements of the users (e.g., reliability and latency requirements, energy constraints), whereas the tier-based priority is for users belonging to different network tiers. For example, with shared spectrum access among macrocells and femtocells in a two-tier network, femtocells create ―dead zones‖ around them in the downlink for macro users. Protection should, thus, be guaranteed for the macro users. Consequently, the macro and femtousers play the role of high-priority users (HPUEs) and lowpriority users (LPUEs), respectively. In the uplink direction, the macrocell users at the cell edge typically transmit with high powers which generates high uplink interference to nearby femtocells. Therefore, in this case, the user priorities should get reversed. Another example is a D2D transmission where different devices may opportunistically access the spectrum to establish a communication link between them provided that the interference introduced to the cellular users remains below a given threshold. In this case, the D2D users play the role of LPUEs whereas the cellular users play the role of HPUEs.·Network-assisted D2D communication: In the LTE Rel- 12 and beyond, focus will be on network controlled D2D communications, where the macrocell BS performs control signaling in terms of synchronization, beacon signal configuration and providing identity and security management [3]. This feature will extend in 5G networks to allow other nodes, rather than the macrocell BS, to have the control. For example, consider a D2D link at the cell edge and the direct link between the D2D transmitter UE to the macrocell is in deep fade, then the relay node can be responsible for the control signaling of the D2Dlink (i.e., relay-aided D2D communication).·Energy harvesting for energy-efficient communication: One of the main challenges in 5G wireless networks is to improve the energy efficiency of the battery-constrained wireless devices. To prolong the battery lifetime as well as to improve the energy efficiency, an appealing solution is to harvest energy from environmental energy sources (e.g., solar and wind energy). Also, energy can be harvested from ambient radio signals (i.e., RF energy harvesting) with reasonable efficiency over small distances. The havested energy could be used for D2D communication or communication within a small cell. Inthis context, simultaneous wireless information and power transfer (SWIPT) is a promising technology for 5G wireless networks. However, practical circuits for harvesting energy are not yet available since the conventional receiver architecture is designed for information transfer only and, thus, may not be optimal for SWIPT. This is due to the fact that both information and power transfer operate with different power sensitivities at the receiver (e.g., -10dBm and -60dBm for energy and information receivers, respectively) [4]. Also, due to the potentially low efficiency of energy harvesting from ambient radio signals, a combination of different energy harvesting technologies may be required for macrocell communication.III. INTERFERENCE MANAGEMENT CHALLENGES IN 5GMULTI-TIER NETWORKSThe key challenges for interference management in 5G multi-tier networks will arise due to the following reasons which affect the interference dynamics in the uplink and downlink of the network: (i) heterogeneity and dense deployment of wireless devices, (ii) coverage and traffic load imbalance due to varying transmit powers of different BSs in the downlink, (iii) public or private access restrictions in different tiers that lead to diverse interference levels, and (iv) the priorities in accessing channels of different frequencies and resource allocation strategies. Moreover, the introduction of carrier aggregation, cooperation among BSs (e.g., by using coordinated multi-point transmission (CoMP)) as well as direct communication among users (e.g., D2D communication) may further complicate the dynamics of the interference. The above factors translate into the following key challenges.·Designing optimized cell association and power control (CAPC) methods for multi-tier networks: Optimizing the cell associations and transmit powers of users in the uplink or the transmit powers of BSs in the downlink are classical techniques to simultaneously enhance the system performance in various aspects such as interference mitigation, throughput maximization, and reduction in power consumption. Typically, the former is needed to maximize spectral efficiency, whereas the latter is required to minimize the power (and hence minimize the interference to other links) while keeping theFig. 1. A multi-tier network composed of macrocells, picocells, femtocells, relays, and D2D links.Arrows indicate wireless links, whereas the dashed lines denote the backhaul connections. desired link quality. Since it is not efficient to connect to a congested BS despite its high achieved signal-to-interference ratio (SIR), cell association should also consider the status of each BS (load) and the channel state of each UE. The increase in the number of available BSs along with multi-point transmissions and carrier aggregation provide multiple degrees of freedom for resource allocation and cell-selection strategies. For power control, the priority of different tiers need also be maintained by incorporating the quality constraints of HPUEs. Unlike downlink, the transmission power in the uplink depends on the user’s batt ery power irrespective of the type of BS with which users are connected. The battery power does not vary significantly from user to user; therefore, the problems of coverage and traffic load imbalance may not exist in the uplink. This leads to considerable asymmetries between the uplink and downlink user association policies. Consequently, the optimal solutions for downlink CAPC problems may not be optimal for the uplink. It is therefore necessary to develop joint optimization frameworks that can provide near-optimal, if not optimal, solutions for both uplink and downlink. Moreover, to deal with this issue of asymmetry, separate uplink and downlink optimal solutions are also useful as far as mobile users can connect with two different BSs for uplink and downlink transmissions which is expected to be the case in 5G multi-tier cellular networks [3].·Designing efficient methods to support simultaneous association to multiple BSs: Compared to existing CAPC schemes in which each user can associate to a singleBS, simultaneous connectivity to several BSs could be possible in 5G multi-tier network. This would enhance the system throughput and reduce the outage ratio by effectively utilizing the available resources, particularly for cell edge users. Thus the existing CAPCschemes should be extended to efficiently support simultaneous association of a user to multiple BSs and determine under which conditions a given UE is associated to which BSs in the uplink and/or downlink.·Designing efficient methods for cooperation and coordination among multiple tiers: Cooperation and coordination among different tiers will be a key requirement to mitigate interference in 5G networks. Cooperation between the macrocell and small cells was proposed for LTE Rel-12 in the context of soft cell, where the UEs are allowed to have dual connectivity by simultaneously connecting to the macrocell and the small cell for uplink and downlink communications or vice versa [3]. As has been mentioned before in the context of asymmetry of transmission power in uplink and downlink, a UE may experience the highest downlink power transmission from the macrocell, whereas the highest uplink path gain may be from a nearby small cell. In this case, the UE can associate to the macrocell in the downlink and to the small cell in the uplink. CoMP schemes based on cooperation among BSs in different tiers (e.g., cooperation between macrocells and small cells) can be developed to mitigate interference in the network. Such schemes need to be adaptive and consider user locations as well as channel conditions to maximize the spectral and energy efficiency of the network. This cooperation however, requires tight integration of low power nodes into the network through the use of reliable, fast andlow latency backhaul connections which will be a major technical issue for upcoming multi-tier 5G networks. In the remaining of this article, we will focus on the review of existing power control and cell association strategies to demonstrate their limitations for interference management in 5G multi-tier prioritized cellular networks (i.e., where users in different tiers have different priorities depending on the location, application requirements and so on). Design guidelines will then be provided to overcome these limitations. Note that issues such as channel scheduling in frequency domain, timedomain interference coordination techniques (e.g., based on almost blank subframes), coordinated multi-point transmission, and spatial domain techniques (e.g., based on smart antenna techniques) are not considered in this article.IV. DISTRIBUTED CELL ASSOCIATION AND POWERCONTROL SCHEMES: CURRENT STATE OF THE ARTA. Distributed Cell Association SchemesThe state-of-the-art cell association schemes that are currently under investigation formulti-tier cellular networks are reviewed and their limitations are explained below.·Reference Signal Received Power (RSRP)-based scheme [5]: A user is associated with the BS whose signal is received with the largest average strength. A variant of RSRP, i.e., Reference Signal Received Quality (RSRQ) is also used for cell selection in LTE single-tier networks which is similar to the signal-to-interference (SIR)-based cell selection where a user selects a BS communicating with which gives the highest SIR. In single-tier networks with uniform traffic, such a criterion may maximize the network throughput. However, due to varying transmit powers of different BSs in the downlink of multi-tier networks, such cell association policies can create a huge traffic load imbalance. This phenomenon leads to overloading of high power tiers while leaving low power tiers underutilized.·Bias-based Cell Range Expansion (CRE) [6]: The idea of CRE has been emerged as a remedy to the problem of load imbalance in the downlink. It aims to increase the downlink coverage footprint of low power BSs by adding a positive bias to their signal strengths (i.e., RSRP or RSRQ). Such BSs are referred to as biased BSs. This biasing allows more users to associate with low power or biased BSs and thereby achieve a better cell load balancing. Nevertheless, such off-loaded users may experience unfavorable channel from the biased BSs and strong interference from the unbiased high-power BSs. The trade-off between cell load balancing and system throughput therefore strictly depends on the selected bias values which need to be optimized in order to maximize the system utility. In this context, a baseline approach in LTE-Advanced is to ―orthogonalize‖ the transmissions of the biased and unbiased BSs in time/frequency domain such that an interference-free zone is created.·Association based on Almost Blank Sub-frame (ABS) ratio [7]: The ABS technique uses time domain orthogonalization in which specific sub-frames are left blank by the unbiased BS and off-loaded users are scheduled within these sub-frames to avoid inter-tier interference. This improves the overall throughput of the off-loaded users by sacrificing the time sub-frames and throughput of the unbiased BS. The larger bias values result in higher degree of offloading and thus require more blank subframes to protect the offloaded users. Given a specific number of ABSs or the ratio of blank over total number of sub-frames (i.e., ABS ratio) that ensures the minimum throughput of the unbiased BSs, this criterion allows a user to select a cell with maximum ABS ratio and may even associate with the unbiased BS if ABS ratio decreases significantly. A qualitative comparison amongthese cell association schemes is given in Table I. The specific key terms used in Table I are defined as follows: channel-aware schemes depend on the knowledge of instantaneous channel and transmit power at the receiver. The interference-aware schemes depend on the knowledge of instantaneous interference at the receiver. The load-aware schemes depend on the traffic load information (e.g., number of users). The resource-aware schemes require the resource allocation information (i.e., the chance of getting a channel or the proportion of resources available in a cell). The priority-aware schemes require the information regarding the priority of different tiers and allow a protection to HPUEs. All of the above mentioned schemes are independent, distributed, and can be incorporated with any type of power control scheme. Although simple and tractable, the standard cell association schemes, i.e., RSRP, RSRQ, and CRE are unable to guarantee the optimum performance in multi-tier networks unless critical parameters, such as bias values, transmit power of the users in the uplink and BSs in the downlink, resource partitioning, etc. are optimized.B. Distributed Power Control SchemesFrom a user’s point of view, the objective of power control is to support a user with its minimum acceptable throughput, whereas from a system’s point of view it is t o maximize the aggregate throughput. In the former case, it is required to compensate for the near-far effect by allocating higher power levels to users with poor channels as compared to UEs with good channels. In the latter case, high power levels are allocated to users with best channels and very low (even zero) power levels are allocated to others. The aggregate transmit power, the outage ratio, and the aggregate throughput (i.e., the sum of achievable rates by the UEs) are the most important measures to compare the performance of different power control schemes. The outage ratio of a particular tier can be expressed as the ratio of the number of UEs supported by a tier with their minimum target SIRs and the total number of UEs in that tier. Numerous power control schemes have been proposed in the literature for single-tier cellular wireless networks. According to the corresponding objective functions and assumptions, the schemes can be classified into the following four types.·Target-SIR-tracking power control (TPC) [8]: In the TPC, each UE tracks its own predefined fixed target-SIR. The TPC enables the UEs to achieve their fixed target-TABLE IQUALITATIVE COMPARISON OF EXISTING CELL ASSOCIATION SCHEMESFOR MULTI-TIER NETWORKSSIRs at minimal aggregate transmit power, assuming thatthe target-SIRs are feasible. However, when the system is infeasible, all non-supported UEs (those who cannot obtain their target-SIRs) transmit at their maximum power, which causes unnecessary power consumption and interference to other users, and therefore, increases the number of non-supported UEs.·TPC with gradual removal (TPC-GR) [9], [10], and [11]:To decrease the outage ra -tio of the TPC in an infeasiblesystem, a number of TPC-GR algorithms were proposedin which non-supported users reduce their transmit power[10] or are gradually removed [9], [11].·Opportunistic power control (OPC) [12]: From the system’s point of view, OPC allocates high power levels to users with good channels (experiencing high path-gains and low interference levels) and very low power to users with poor channels. In this algorithm, a small difference in path-gains between two users may lead to a large difference in their actual throughputs [12]. OPC improves the system performance at the cost of reduced fairness among users.·Dynamic-SIR tracking power control (DTPC) [13]: When the target-SIR requirements for users are feasible, TPC causes users to exactly hit their fixed target-SIRs even if additional resources are still available that can otherwise be used to achieve higher SIRs (and thus better throughputs). Besides, the fixed-target-SIR assignment is suitable only for voice service for which reaching a SIR value higher than the given target value does not affect the service quality significantly. In contrast, for data services, a higher SIR results in a better throughput, which is desirable. The DTPC algorithm was proposed in [13] to address the problem of system throughput maximization subject to a given feasible lower bound for the achieved SIRs of all users in cellular networks. In DTPC, each user dynamically sets its target-SIR by using TPC and OPC in a selective manner. It was shown that when the minimum acceptable target-SIRs are feasible, the actual SIRs received by some users can be dynamically increased (to a value higher than their minimum acceptabletarget-SIRs) in a distributed manner so far as the required resources are available and the system remains feasible (meaning that reaching the minimum target-SIRs for the remaining users are guaranteed). This enhances the system throughput (at the cost of higher power consumption) as compared to TPC. The aforementioned state-of-the-art distributed power control schemes for satisfying various objectives in single-tier wireless cellular networks are unable to address the interference management problem in prioritized 5G multi-tier networks. This is due to the fact that they do not guarantee that the total interference caused by the LPUEs to the HPUEs remain within tolerable limits, which can lead to the SIR outage of some HPUEs. Thus there is a need to modify the existing schemes such that LPUEs track their objectives while limiting their transmit power to maintain a given interference threshold at HPUEs. A qualitative comparison among various state-of-the-art power control problems with different objectives and constraints and their corresponding existing distributed solutions are shown in Table II. This table also shows how these schemes can be modified and generalized for designing CAPC schemes for prioritized 5G multi-tier networks.C. Joint Cell Association and Power Control SchemesA very few work in the literature have considered the problem of distributed CAPC jointly (e.g., [14]) with guaranteed convergence. For single-tier networks, a distributed framework for uplink was developed [14], which performs cell selection based on the effective-interference (ratio of instantaneous interference to channel gain) at the BSs and minimizes the aggregate uplink transmit power while attaining users’ desire d SIR targets. Following this approach, a unified distributed algorithm was designed in [15] for two-tier networks. The cell association is based on the effective-interference metric and is integrated with a hybrid power control (HPC) scheme which is a combination of TPC and OPC power control algorithms.Although the above frameworks are distributed and optimal/ suboptimal with guaranteed convergence in conventional networks, they may not be directly compatible to the 5G multi-tier networks. The interference dynamics in multi-tier networks depends significantly on the channel access protocols (or scheduling), QoS requirements and priorities at different tiers. Thus, the existing CAPC optimization problems should be modified to include various types of cell selection methods (some examples are provided in Table I) and power control methods with different objectives and interference constraints (e.g., interference constraints for macro cell UEs, picocell UEs, or D2Dreceiver UEs). A qualitative comparison among the existing CAPC schemes along with the open research areas are highlighted in Table II. A discussion on how these open problems can be addressed is provided in the next section.V. DESIGN GUIDELINES FOR DISTRIBUTED CAPCSCHEMES IN 5G MULTI-TIER NETWORKSInterference management in 5G networks requires efficient distributed CAPC schemes such that each user can possibly connect simultaneously to multiple BSs (can be different for uplink and downlink), while achieving load balancing in different cells and guaranteeing interference protection for the HPUEs. In what follows, we provide a number of suggestions to modify the existing schemes.A. Prioritized Power ControlTo guarantee interference protection for HPUEs, a possible strategy is to modify the existing power control schemes listed in the first column of Table II such that the LPUEs limit their transmit power to keep the interference caused to the HPUEs below a predefined threshold, while tracking their own objectives. In other words, as long as the HPUEs are protected against existence of LPUEs, the LPUEs could employ an existing distributed power control algorithm to satisfy a predefined goal. This offers some fruitful direction for future research and investigation as stated in Table II. To address these open problems in a distributed manner, the existing schemes should be modified so that the LPUEs in addition to setting their transmit power for tracking their objectives, limit their transmit power to keep their interference on receivers of HPUEs below a given threshold. This could be implemented by sending a command from HPUEs to its nearby LPUEs (like a closed-loop power control command used to address the near-far problem), when the interference caused by the LPUEs to the HPUEs exceeds a given threshold. We refer to this type of power control as prioritized power control. Note that the notion of priority and thus the need of prioritized power control exists implicitly in different scenarios of 5G networks, as briefly discussed in Section II. Along this line, some modified power control optimization problems are formulated for 5G multi-tier networks in second column of Table II.To compare the performance of existing distributed power control algorithms, let us consider a prioritized multi-tier cellular wireless network where a high-priority tier consisting of 3×3 macro cells, each of which covers an area of 1000 m×1000 m, coexists with a low-priority tier consisting of n small-cells per each high-priority macro cell, each。
毕业设计外文翻译_英文版
A Design and Implementation of Active NetworkSocket ProgrammingK.L. Eddie Law, Roy LeungThe Edward S. Rogers Sr. Department of Electrical and Computer EngineeringUniversity of TorontoToronto, Canadaeddie@, roy.leung@utoronto.caAbstract—The concept of programmable nodes and active networks introduces programmability into communication networks. Code and data can be sent and modified on their ways to destinations. Recently, various research groups have designed and implemented their own design platforms. Each design has its own benefits and drawbacks. Moreover, there exists an interoperability problem among platforms. As a result, we introduce a concept that is similar to the network socket programming. We intentionally establish a set of simple interfaces for programming active applications. This set of interfaces, known as Active Network Socket Programming (ANSP), will be working on top of all other execution environments in future. Therefore, the ANSP offers a concept that is similar to “write once, run everywhere.” It is an open programming model that active applications can work on all execution environments. It solves the heterogeneity within active networks. This is especially useful when active applications need to access all regions within a heterogeneous network to deploy special service at critical points or to monitor the performance of the entire networks. Instead of introducing a new platform, our approach provides a thin, transparent layer on top of existing environments that can be easily installed for all active applications.Keywords-active networks; application programming interface; active network socket programming;I. I NTRODUCTIONIn 1990, Clark and Tennenhouse [1] proposed a design framework for introducing new network protocols for the Internet. Since the publication of that position paper, active network design framework [2, 3, 10] has slowly taken shape in the late 1990s. The active network paradigm allows program code and data to be delivered simultaneously on the Internet. Moreover, they may get executed and modified on their ways to their destinations. At the moment, there is a global active network backbone, the ABone, for experiments on active networks. Apart from the immaturity of the executing platform, the primary hindrance on the deployment of active networks on the Internet is more on the commercially related issues. For example, a vendor may hesitate to allow network routers to run some unknown programs that may affect their expected routing performance. As a result, alternatives were proposed to allow active network concept to operate on the Internet, such as the application layer active networking (ALAN) project [4] from the European research community. In the ALAN project, there are active server systems located at different places in the networks and active applications are allowed to run in these servers at the application layer. Another potential approach from the network service provider is to offer active network service as the premium service class in the networks. This service class should provide the best Quality of Service (QoS), and allow the access of computing facility in routers. With this approach, the network service providers can create a new source of income.The research in active networks has been progressing steadily. Since active networks introduce programmability on the Internet, appropriate executing platforms for the active applications to execute should be established. These operating platforms are known as execution environments (EEs) and a few of them have been created, e.g., the Active Signaling Protocol (ASP) [12] and the Active Network Transport System (ANTS) [11]. Hence, different active applications can be implemented to test the active networking concept.With these EEs, some experiments have been carried out to examine the active network concept, for example, the mobile networks [5], web proxies [6], and multicast routers [7]. Active networks introduce a lot of program flexibility and extensibility in networks. Several research groups have proposed various designs of execution environments to offer network computation within routers. Their performance and potential benefits to existing infrastructure are being evaluated [8, 9]. Unfortunately, they seldom concern the interoperability problems when the active networks consist of multiple execution environments. For example, there are three EEs in ABone. Active applications written for one particular EE cannot be operated on other platforms. This introduces another problem of resources partitioning for different EEs to operate. Moreover, there are always some critical network applications that need to run under all network routers, such as collecting information and deploying service at critical points to monitor the networks.In this paper, a framework known as Active Network Socket Programming (ANSP) model is proposed to work with all EEs. It offers the following primary objectives.• One single programming interface is introduced for writing active applications.• Since ANSP offers the programming interface, the design of EE can be made independent of the ANSP.This enables a transparency in developing andenhancing future execution environments.• ANSP addresses the interoperability issues among different execution environments.• Through the design of ANSP, the pros and cons of different EEs will be gained. This may help design abetter EE with improved performance in future.The primary objective of the ANSP is to enable all active applications that are written in ANSP can operate in the ABone testbed . While the proposed ANSP framework is essential in unifying the network environments, we believe that the availability of different environments is beneficial in the development of a better execution environment in future. ANSP is not intended to replace all existing environments, but to enable the studies of new network services which are orthogonal to the designs of execution environments. Therefore, ANSP is designed to be a thin and transparent layer on top of all execution environments. Currently, its deployment relies on automatic code loading with the underlying environments. As a result, the deployment of ANSP at a router is optional and does not require any change to the execution environments.II. D ESIGN I SSUES ON ANSPThe ANSP unifies existing programming interfaces among all EEs. Conceptually, the design of ANSP is similar to the middleware design that offers proper translation mechanisms to different EEs. The provisioning of a unified interface is only one part of the whole ANSP platform. There are many other issues that need to be considered. Apart from translating a set of programming interfaces to other executable calls in different EEs, there are other design issues that should be covered, e.g., • a unified thread library handles thread operations regardless of the thread libraries used in the EEs;• a global soft-store allows information sharing among capsules that may execute over different environmentsat a given router;• a unified addressing scheme used across different environments; more importantly, a routing informationexchange mechanism should be designed across EEs toobtain a global view of the unified networks;• a programming model that should be independent to any programming languages in active networks;• and finally, a translation mechanism to hide the heterogeneity of capsule header structures.A. Heterogeneity in programming modelEach execution environment provides various abstractions for its services and resources in the form of program calls. The model consists of a set of well-defined components, each of them has its own programming interfaces. For the abstractions, capsule-based programming model [10] is the most popular design in active networks. It is used in ANTS [11] and ASP [12], and they are being supported in ABone. Although they are developed based on the same capsule model, their respective components and interfaces are different. Therefore, programs written in one EE cannot run in anther EE. The conceptual views of the programming models in ANTS and ASP are shown in Figure 1.There are three distinct components in ANTS: application, capsule, and execution environment. There exist user interfaces for the active applications at only the source and destination routers. Then the users can specify their customized actions to the networks. According to the program function, the applications send one or more capsules to carry out the operations. Both applications and capsules operate on top of an execution environment that exports an interface to its internal programming resources. Capsule executes its program at each router it has visited. When it arrives at its destination, the application at destination may either reply it with another capsule or presents this arrival event to the user. One drawback with ANTS is that it only allows “bootstrap” application.Figure 1. Programming Models in ASP and ANTS.In contrast, ASP does not limit its users to run “bootstrap” applications. Its program interfaces are different from ANTS, but there are also has three components in ASP: application client, environment, and AAContext. The application client can run on active or non-active host. It can start an active application by simply sending a request message to the EE. The client presents information to users and allows its users to trigger actions at a nearby active router. AAContext is the core of the network service and its specification is divided into two parts. One part specifies its actions at its source and destination routers. Its role is similar to that of the application in ANTS, except that it does not provide a direct interface with the user. The other part defines its actions when it runs inside the active networks and it is similar to the functional behaviors of a capsule in ANTS.In order to deal with the heterogeneity of these two models, ANSP needs to introduce a new set of programming interfaces and map its interfaces and execution model to those within the routers’ EEs.B. Unified Thread LibraryEach execution environment must ensure the isolation of instance executions, so they do not affect each other or accessThe authors appreciate the Nortel Institute for Telecommunications (NIT) at the University of Toronto to allow them to access the computing facilitiesothers’ information. There are various ways to enforce the access control. One simple way is to have one virtual machine for one instance of active applications. This relies on the security design in the virtual machines to isolate services. ANTS is one example that is using this method. Nevertheless, the use of multiple virtual machines requires relatively large amount of resources and may be inefficient in some cases. Therefore, certain environments, such as ASP, allow network services to run within a virtual machine but restrict the use of their services to a limited set of libraries in their packages. For instance, ASP provides its thread library to enforce access control. Because of the differences in these types of thread mechanism, ANSP devises a new thread library to allow uniform accesses to different thread mechanisms.C. Soft-StoreSoft-store allows capsule to insert and retrieve information at a router, thus allowing more than one capsules to exchange information within a network. However, problem arises when a network service can execute under different environments within a router. The problem occurs especially when a network service inserts its soft-store information in one environment and retrieves its data at a later time in another environment at the same router. Due to the fact that execution environments are not allowed to exchange information, the network service cannot retrieve its previous data. Therefore, our ANSP framework needs to take into account of this problem and provides soft-store mechanism that allows universal access of its data at each router.D. Global View of a Unified NetworkWhen an active application is written with ANSP, it can execute on different environment seamlessly. The previously smaller and partitioned networks based on different EEs can now be merging into one large active network. It is then necessary to advise the network topology across the networks. However, different execution environments have different addressing schemes and proprietary routing protocols. In order to merge these partitions together, ANSP must provide a new unified addressing scheme. This new scheme should be interpretable by any environments through appropriate translations with the ANSP. Upon defining the new addressing scheme, a new routing protocol should be designed to operate among environments to exchange topology information. This allows each environment in a network to have a complete view of its network topology.E. Language-Independent ModelExecution environment can be programmed in any programming language. One of the most commonly used languages is Java [13] due to its dynamic code loading capability. In fact, both ANTS and ASP are developed in Java. Nevertheless, the active network architecture shown in Figure 2 does not restrict the use of additional environments that are developed in other languages. For instance, the active network daemon, anted, in Abone provides a workspace to execute multiple execution environments within a router. PLAN, for example, is implemented in Ocaml that will be deployable on ABone in future. Although the current active network is designed to deploy multiple environments that can be in any programming languages, there lacks the tool to allow active applications to run seamlessly upon these environments. Hence, one of the issues that ANSP needs to address is to design a programming model that can work with different programming languages. Although our current prototype only considers ANTS and ASP in its design, PLAN will be the next target to address the programming language issue and to improve the design of ANSP.Figure 2. ANSP Framework Model.F. Heterogeneity of Capsule Header StructureThe structures of the capsule headers are different in different EEs. They carries capsule-related information, for example, the capsule types, sources and destinations. This information is important when certain decision needs to be made within its target environment. A unified model should allow its program code to be executed on different environments. However, the capsule header prevents different environments to interpret its information successfully. Therefore, ANSP should carry out appropriate translation to the header information before the target environment receives this capsule.III. ANSP P ROGRAMMING M ODELWe have outlined the design issues encountered with the ANSP. In the following, the design of the programming model in ANSP will be discussed. This proposed framework provides a set of unified programming interfaces that allows active applications to work on all execution environments. The framework is shown in Figure 2. It is composed of two layers integrated within the active network architecture. These two layers can operate independently without the other layer. The upper layer provides a unified programming model to active applications. The lower layer provides appropriate translation procedure to the ANSP applications when it is processed by different environments. This service is necessary because each environment has its own header definition.The ANSP framework provides a set of programming calls which are abstractions of ANSP services and resources. A capsule-based model is used for ANSP, and it is currently extended to map to other capsule-based models used in ANTSand ASP. The mapping possibility to other models remains as our future works. Hence, the mapping technique in ANSP allows any ANSP applications to access the same programming resources in different environments through a single set of interfaces. The mapping has to be done in a consistent and transparent manner. Therefore, the ANSP appears as an execution environment that provides a complete set of functionalities to active applications. While in fact, it is an overlay structure that makes use of the services provided from the underlying environments. In the following, the high-level functional descriptions of the ANSP model are described. Then, the implementations will be discussed. The ANSP programming model is based upon the interactions between four components: application client , application stub , capsule , and active service base.Figure 3. Information Flow with the ANSP.•Application Client : In a typical scenario, an active application requires some means to present information to its users, e.g., the state of the networks. A graphical user interface (GUI) is designed to operate with the application client if the ANSP runs on a non-active host.•Application Stub : When an application starts, it activates the application client to create a new instance of application stub at its near-by active node. There are two responsibilities for the application stub. One of them is to receive users’ instructions from the application client. Another one is to receive incoming capsules from networks and to perform appropriate actions. Typically, there are two types of actions, thatare, to reply or relay in capsules through the networks, or to notify the users regarding the incoming capsule. •Capsule : An active application may contain several capsule types. Each of them carries program code (also referred to as forwarding routine). Since the application defines a protocol to specify the interactions among capsules as well as the application stubs. Every capsule executes its forwarding routine at each router it visits along the path between the source and destination.•Active Service Base : An active service base is designed to export routers’ environments’ services and execute program calls from application stubs and capsules from different EEs. The base is loaded automatically at each router whenever a capsule arrives.The interactions among components within ANSP are shown in Figure 3. The designs of some key components in the ANSP will be discussed in the following subsections. A. Capsule (ANSPCapsule)ANSPXdr decode () ANSPXdr encode () int length ()Boolean execute ()New types of capsule are created by extending the abstract class ANSPCapsule . New extensions are required to define their own forwarding routines as well as their serialization procedures. These methods are indicated below:The execution of a capsule in ANSP is listed below. It is similar to the process in ANTS.1. A capsule is in serial binary representation before it issent to the network. When an active router receives a byte sequence, it invokes decode() to convert the sequence into a capsule. 2. The router invokes the forwarding routine of thecapsule, execute(). 3. When the capsule has finished its job and forwardsitself to its next hop by calling send(), this call implicitly invokes encode() to convert the capsule into a new serial byte representation. length() isused inside the call of encode() to determine the length of the resulting byte sequence. ANSP provides a XDR library called ANSPXdr to ease the jobs of encoding and decoding.B. Active Service Base (ANSPBase)In an active node, the Active Service Base provides a unified interface to export the available resources in EEs for the rest of the ANSP components. The services may include thread management, node query, and soft-store operation, as shown in Table 1.TABLE I. ACTIVE SERVICE BASE FUNCTION CALLSFunction Definition Descriptionboolean send (Capsule, Address) Transmit a capsule towards its destination using the routing table of theunderlying environment.ANSPAddress getLocalHost () Return address of the local host as an ANSPAddress structure. This isuseful when a capsule wants to check its current location.boolean isLocal (ANSPAddress) Return true if its input argument matches the local host’s address andreturn false otherwise.createThread () Create a new thread that is a class ofANSPThreadInterface (discussed later in Section VIA “Unified Thread Abstraction”).putSStore (key, Object) Object getSStore (key) removeSStore (key)The soft-store operations are provided by putSStore(), getSSTore(), and removeSStore(), and they put, retrieve, and remove data respectively. forName (PathName) Supported in ANSP to retrieve a classobject corresponding to the given path name in its argument. This code retrieval may rely on the code loading mechanism in the environment whennecessary.C. Application Client (ANSPClient)boolean start (args[])boolean start (args[],runningEEs) boolean start (args[],startClient)boolean start (args[],startClient, runningEE)Application Client is an interface between users and the nearby active source router. It does the following responsibilities.1. Code registration: It may be necessary to specify thelocation and name of the application code in some execution environments, e.g., ANTS. 2. Application initialization: It includes selecting anexecution environment to execute the application among those are available at the source router. Each active application can create an application client instance by extending the abstract class, ANSPClient . The extension inherits a method, start(), to automatically handle both the registration and initialization processes. All overloaded versions of start() accept a list of arguments, args , that are passed to the application stub during its initialization. An optional argument called runningEEs allows an application client to select a particular set of environment variables, specified by a list of standardized numerical environment ID, the ANEP ID, to perform code registration. If this argument is not specified, the default setting can only include ANTS and ASP. D. Application Stub (ANSPApplication)receive (ANSPCapsule)Application stubs reside at the source and destination routers to initialize the ANSP application after the application clients complete the initialization and registration processes. It is responsible for receiving and serving capsules from the networks as well as actions requested from the clients. A new instance is created by extending the application client abstract class, ANSPApplication . This extension includes the definition of a handling routine called receive(), which is invoked when a stub receives a new capsule.IV. ANSP E XAMPLE : T RACE -R OUTEA testbed has been created to verify the design correctnessof ANSP in heterogeneous environments. There are three types of router setting on this testbed:1. Router that contains ANTS and a ANSP daemonrunning on behalf of ASP; 2. Router that contains ASP and a ANSP daemon thatruns on behalf of ANTS; 3. Router that contains both ASP and ANTS.The prototype is written in Java [11] with a traceroute testing program. The program records the execution environments of all intermediate routers that it has visited between the source and destination. It also measures the RTT between them. Figure 4 shows the GUI from the application client, and it finds three execution environments along the path: ASP, ANTS, and ASP. The execution sequence of the traceroute program is shown in Figure 5.Figure 4. The GUI for the TRACEROUTE Program.The TraceCapsule program code is created byextending the ANSPCapsule abstract class. When execute() starts, it checks the Boolean value of returning to determine if it is returning from the destination. It is set to true if TraceCapsule is traveling back to the source router; otherwise it is false . When traveling towards the destination, TraceCapsule keeps track of the environments and addresses of the routers it has visited in two arrays, path and trace , respectively. When it arrives at a new router, it calls addHop() to append the router address and its environment to these two arrays. When it finally arrives at the destination, it sets returning to false and forwards itself back to the source by calling send().When it returns to source, it invokes deliverToApp() to deliver itself to the application stub that has been running at the source. TraceCapsule carries information in its data field through the networks by executing encode() and decode(), which encapsulates and de-capsulates its data using External Data Representation (XDR) respectively. The syntax of ANSP XDR follows the syntax of XDR library from ANTS. length() in TraceCapsule returns the data length, or it can be calculated by using the primitive types in the XDRlibrary.Figure 5. Flow of the TRACEROUTE Capsules.V. C ONCLUSIONSIn this paper, we present a new unified layered architecture for active networks. The new model is known as Active Network Socket Programming (ANSP). It allows each active application to be written once and run on multiple environments in active networks. Our experiments successfully verify the design of ANSP architecture, and it has been successfully deployed to work harmoniously with ANTS and ASP without making any changes to their architectures. In fact, the unified programming interface layer is light-weighted and can be dynamically deployable upon request.R EFERENCES[1] D.D. Clark, D.L. Tennenhouse, “Architectural Considerations for a NewGeneration of Protocols,” in Proc. ACM Sigcomm’90, pp.200-208, 1990. [2] D. Tennenhouse, J. M. Smith, W. D. Sicoskie, D. J. Wetherall, and G. J.Minden, “A survey of active network research,” IEEE Communications Magazine , pp. 80-86, Jan 1997.[3] D. Wetherall, U. Legedza, and J. Guttag, “Introducing new internetservices: Why and how,” IEEE Network Magazine, July/August 1998. [4] M. Fry, A. Ghosh, “Application Layer Active Networking,” in ComputerNetworks , Vol.31, No.7, pp.655-667, 1999.[5] K. W. Chin, “An Investigation into The Application of Active Networksto Mobile Computing Environments”, Curtin University of Technology, March 2000.[6] S. Bhattacharjee, K. L. Calvert, and E. W. Zegura, “Self OrganizingWide-Area Network Caches”, Proc. IEEE INFOCOM ’98, San Francisco, CA, 29 March-2 April 1998.[7] L. H. Leman, S. J. Garland, and D. L. Tennenhouse, “Active ReliableMulticast”, Proc. IEEE INFOCOM ’98, San Francisco, CA, 29 March-2 April 1998.[8] D. Descasper, G. Parulkar, B. Plattner, “A Scalable, High PerformanceActive Network Node”, In IEEE Network, January/February 1999.[9] E. L. Nygren, S. J. Garland, and M. F. Kaashoek, “PAN: a high-performance active network node supporting multiple mobile code system”, In the Proceedings of the 2nd IEEE Conference on Open Architectures and Network Programming (OpenArch ’99), March 1999. [10] D. L. Tennenhouse, and D. J. Wetherall. “Towards an Active NetworkArchitecture”, In Proceeding of Multimedia Computing and Networking , January 1996.[11] D. J. Wetherall, J. V. Guttag, D. L. Tennenhouse, “ANTS: A toolkit forBuilding and Dynamically Deploying Network Protocols”, Open Architectures and Network Programming, 1998 IEEE , 1998 , Page(s): 117 –129.[12] B. Braden, A. Cerpa, T. Faber, B. Lindell, G. Phillips, and J. Kann.“Introduction to the ASP Execution Environment”: /active-signal/ARP/index.html .[13] “The java language: A white paper,” Tech. Rep., Sun Microsystems,1998.。
毕业设计外文文献翻译(原文+译文)
Environmental problems caused by Istanbul subway excavation and suggestionsfor remediation伊斯坦布尔地铁开挖引起的环境问题及补救建议Ibrahim Ocak Abstract:Many environmental problems caused by subway excavations have inevitably become an important point in city life. These problems can be categorized as transporting and stocking of excavated material, traffic jams, noise, vibrations, piles of dust mud and lack of supplies. Although these problems cause many difficulties,the most pressing for a big city like Istanbul is excava tion,since other listed difficulties result from it. Moreover, these problems are environmentally and regionally restricted to the period over which construction projects are underway and disappear when construction is finished. Currently, in Istanbul, there are nine subway construction projects in operation, covering approximately 73 km in length; over 200 km to be constructed in the near future. The amount of material excavated from ongoing construction projects covers approximately 12 million m3. In this study, problems—primarily, the problem with excavation waste(EW)—caused by subway excavation are analyzed and suggestions for remediation are offered.摘要:许多地铁开挖引起的环境问题不可避免地成为城市生活的重要部分。
毕业设计外文文献翻译范文
毕业设计外文文献翻译专业学生姓名班级学号指导教师优集学院外文资料名称:Knowledge-Based Engineeri--ng Design Methodology外文资料出处:Int.J.Engng Ed.Vol.16.No.1附件: 1.外文资料翻译译文2.外文原文基于知识工程(KBE)设计方法D. E. CALKINS1.背景复杂系统的发展需要很多工程和管理方面的知识、决策,它要满足很多竞争性的要求。
设计被认为是决定产品最终形态、成本、可靠性、市场接受程度的首要因素。
高级别的工程设计和分析过程(概念设计阶段)特别重要,因为大多数的生命周期成本和整体系统的质量都在这个阶段。
产品成本的压缩最可能发生在产品设计的最初阶段。
整个生命周期阶段大约百分之七十的成本花费在概念设计阶段结束时,缩短设计周期的关键是缩短概念设计阶段,这样同时也减少了工程的重新设计工作量。
工程权衡过程中采用良好的估计和非正式的启发进行概念设计。
传统CAD工具对概念设计阶段的支持非常有限。
有必要,进行涉及多个学科的交流合作来快速进行设计分析(包括性能,成本,可靠性等)。
最后,必须能够管理大量的特定领域的知识。
解决方案是在概念设计阶段包含进更过资源,通过消除重新设计来缩短整个产品的时间。
所有这些因素都主张采取综合设计工具和环境,以在早期的综合设计阶段提供帮助。
这种集成设计工具能够使由不同学科的工程师、设计者在面对复杂的需求和约束时能够对设计意图达成共识。
那个设计工具可以让设计团队研究在更高级别上的更多配置细节。
问题就是架构一个设计工具,以满足所有这些要求。
2.虚拟(数字)原型模型现在需要是一种代表产品设计为得到一将允许一产品的早发展和评价的真实事实上原型的过程的方式。
虚拟样机将取代传统的物理样机,并允许设计工程师,研究“假设”的情况,同时反复更新他们的设计。
真正的虚拟原型,不仅代表形状和形式,即几何形状,它也代表如重量,材料,性能和制造工艺的非几何属性。
毕业设计(论文)外文原文及译文
毕业设计(论文)外文原文及译文一、外文原文MCUA microcontroller (or MCU) is a computer-on-a-chip. It is a type of microcontroller emphasizing self-sufficiency and cost-effectiveness, in contrast to a general-purpose microprocessor (the kind used in a PC).With the development of technology and control systems in a wide range of applications, as well as equipment to small and intelligent development, as one of the single-chip high-tech for its small size, powerful, low cost, and other advantages of the use of flexible, show a strong vitality. It is generally better compared to the integrated circuit of anti-interference ability, the environmental temperature and humidity have better adaptability, can be stable under the conditions in the industrial. And single-chip widely used in a variety of instruments and meters, so that intelligent instrumentation and improves their measurement speed and measurement accuracy, to strengthen control functions. In short,with the advent of the information age, traditional single- chip inherent structural weaknesses, so that it show a lot of drawbacks. The speed, scale, performance indicators, such as users increasingly difficult to meet the needs of the development of single-chip chipset, upgrades are faced with new challenges.The Description of AT89S52The AT89S52 is a low-power, high-performance CMOS 8-bit microcontroller with 8K bytes of In-System Programmable Flash memory. The device is manufactured using Atmel's high-density nonvolatile memory technology and is compatible with the industry-standard 80C51 instruction set and pinout. The on-chip Flash allows the program memory to be reprogrammed in-system or by a conventional nonvolatile memory programmer. By combining a versatile 8-bit CPU with In-System Programmable Flash on a monolithic chip, the Atmel AT89S52 is a powerful microcontroller which provides a highly-flexible and cost-effective solution to many embedded control applications.The AT89S52 provides the following standard features: 8K bytes ofFlash, 256 bytes of RAM, 32 I/O lines, Watchdog timer, two data pointers, three 16-bit timer/counters, a six-vector two-level interrupt architecture, a full duplex serial port, on-chip oscillator, and clock circuitry. In addition, the AT89S52 is designed with static logic for operation down to zero frequency and supports two software selectable power saving modes. The Idle Mode stops the CPU while allowing the RAM, timer/counters, serial port, and interrupt system to continue functioning. The Power-down mode saves the RAM contents but freezes the oscillator, disabling all other chip functions until the next interrupt or hardware reset.Features• Compatible with MCS-51® Products• 8K Bytes of In-System Programmable (ISP) Flash Memory– Endurance: 1000 Write/Erase Cycles• 4.0V to 5.5V Operating Range• Fully Static Operation: 0 Hz to 33 MHz• Three-level Program Memory Lock• 256 x 8-bit Internal RAM• 32 Programmable I/O Lines• Three 16-bit Timer/Counters• Eight Interrupt Sources• Full Duplex UART Serial Channel• Low-power Idle and Power-down Modes• Interrupt Recovery from Power-down Mode• Watchdog Timer• Dual Data Pointer• Power-off FlagPin DescriptionVCCSupply voltage.GNDGround.Port 0Port 0 is an 8-bit open drain bidirectional I/O port. As an output port, each pin can sink eight TTL inputs. When 1s are written to port 0 pins, the pins can be used as high-impedance inputs.Port 0 can also be configured to be the multiplexed low-order address/data bus during accesses to external program and data memory. In this mode, P0 has internal pullups.Port 0 also receives the code bytes during Flash programming and outputs the code bytes during program verification. External pullups are required during program verification.Port 1Port 1 is an 8-bit bidirectional I/O port with internal pullups. The Port 1 output buffers can sink/source four TTL inputs. When 1s are written to Port 1 pins, they are pulled high by the internal pullups and can be used as inputs. As inputs, Port 1 pins that are externally being pulled low will source current (IIL) because of the internal pullups.In addition, P1.0 and P1.1 can be configured to be the timer/counter 2 external count input (P1.0/T2) and the timer/counter 2 trigger input (P1.1/T2EX), respectively.Port 1 also receives the low-order address bytes during Flash programming and verification.Port 2Port 2 is an 8-bit bidirectional I/O port with internal pullups. The Port 2 output buffers can sink/source four TTL inputs. When 1s are written to Port 2 pins, they are pulled high by the internal pullups and can be used as inputs. As inputs, Port 2 pins that are externally being pulled low will source current (IIL) because of the internal pullups.Port 2 emits the high-order address byte during fetches from external program memory and during accesses to external data memory that use 16-bit addresses (MOVX @ DPTR). In this application, Port 2 uses strong internal pull-ups when emitting 1s. During accesses to external data memory that use 8-bit addresses (MOVX @ RI), Port 2 emits the contents of the P2 Special Function Register.Port 2 also receives the high-order address bits and some control signals during Flash programming and verification.Port 3Port 3 is an 8-bit bidirectional I/O port with internal pullups. The Port 3 output buffers can sink/source four TTL inputs. When 1s are written to Port 3 pins, they are pulled high by the internal pullups and can be used as inputs. As inputs, Port 3 pins that are externally being pulled low will source current (IIL) because of the pullups.Port 3 also serves the functions of various special features of the AT89S52, as shown in the following table.Port 3 also receives some control signals for Flash programming and verification.RSTReset input. A high on this pin for two machine cycles while the oscillator is running resets the device. This pin drives High for 96 oscillator periods after the Watchdog times out. The DISRTO bit in SFR AUXR (address 8EH) can be used to disable this feature. In the default state of bit DISRTO, the RESET HIGH out feature is enabled.ALE/PROGAddress Latch Enable (ALE) is an output pulse for latching the low byte of the address during accesses to external memory. This pin is also the program pulse input (PROG) during Flash programming.In normal operation, ALE is emitted at a constant rate of 1/6 the oscillator frequency and may be used for external timing or clocking purposes. Note, however, that one ALE pulse is skipped during each access to external data memory.If desired, ALE operation can be disabled by setting bit 0 of SFR location 8EH. With the bit set, ALE is active only during a MOVX or MOVC instruction. Otherwise, the pin is weakly pulled high. Setting the ALE-disable bit has no effect if the microcontroller is in external execution mode.PSENProgram Store Enable (PSEN) is the read strobe to external program memory. When the AT89S52 is executing code from external program memory, PSENis activated twice each machine cycle, except that two PSEN activations are skipped during each access to external data memory.EA/VPPExternal Access Enable. EA must be strapped to GND in order to enable the device to fetch code from external program memory locations starting at 0000H up to FFFFH. Note, however, that if lock bit 1 is programmed, EA will be internally latched on reset. EA should be strapped to VCC for internal program executions.This pin also receives the 12-volt programming enable voltage (VPP) during Flash programming.XTAL1Input to the inverting oscillator amplifier and input to the internal clock operating circuit.XTAL2Output from the inverting oscillator amplifier.Special Function RegistersNote that not all of the addresses are occupied, and unoccupied addresses may not be implemented on the chip. Read accesses to these addresses will in general return random data, and write accesses will have an indeterminate effect.User software should not write 1s to these unlisted locations, since they may be used in future products to invoke new features. In that case, the reset or inactive values of the new bits will always be 0.Timer 2 Registers:Control and status bits are contained in registers T2CON and T2MOD for Timer 2. The register pair (RCAP2H, RCAP2L) are the Capture/Reload registers for Timer 2 in 16-bit capture mode or 16-bit auto-reload mode.Interrupt Registers:The individual interrupt enable bits are in the IE register. Two priorities can be set for each of the six interrupt sources in the IP register.Dual Data Pointer Registers: To facilitate accessing both internal and external data memory, two banks of 16-bit Data Pointer Registers areprovided: DP0 at SFR address locations 82H-83H and DP1 at 84H-85H. Bit DPS = 0 in SFR AUXR1 selects DP0 and DPS = 1 selects DP1. The user should always initialize the DPS bit to the appropriate value before accessing the respective Data Pointer Register.Power Off Flag:The Power Off Flag (POF) is located at bit 4 (PCON.4) in the PCON SFR. POF is set to “1” during power up. It can be set and rest under software control and is not affected by reset.Memory OrganizationMCS-51 devices have a separate address space for Program and Data Memory. Up to 64K bytes each of external Program and Data Memory can be addressed.Program MemoryIf the EA pin is connected to GND, all program fetches are directed to external memory. On the AT89S52, if EA is connected to VCC, program fetches to addresses 0000H through 1FFFH are directed to internal memory and fetches to addresses 2000H through FFFFH are to external memory.Data MemoryThe AT89S52 implements 256 bytes of on-chip RAM. The upper 128 bytes occupy a parallel address space to the Special Function Registers. This means that the upper 128 bytes have the same addresses as the SFR space but are physically separate from SFR space.When an instruction accesses an internal location above address 7FH, the address mode used in the instruction specifies whether the CPU accesses the upper 128 bytes of RAM or the SFR space. Instructions which use direct addressing access of the SFR space. For example, the following direct addressing instruction accesses the SFR at location 0A0H (which is P2).MOV 0A0H, #dataInstructions that use indirect addressing access the upper 128 bytes of RAM. For example, the following indirect addressing instruction, where R0 contains 0A0H, accesses the data byte at address 0A0H, rather than P2 (whose address is 0A0H).MOV @R0, #dataNote that stack operations are examples of indirect addressing, so the upper 128 bytes of data RAM are available as stack space.Timer 0 and 1Timer 0 and Timer 1 in the AT89S52 operate the same way as Timer 0 and Timer 1 in the AT89C51 and AT89C52.Timer 2Timer 2 is a 16-bit Timer/Counter that can operate as either a timer or an event counter. The type of operation is selected by bit C/T2 in the SFR T2CON (shown in Table 2). Timer 2 has three operating modes: capture, auto-reload (up or down counting), and baud rate generator. The modes are selected by bits in T2CON.Timer 2 consists of two 8-bit registers, TH2 and TL2. In the Timer function, the TL2 register is incremented every machine cycle. Since a machine cycle consists of 12 oscillator periods, the count rate is 1/12 of the oscillator frequency.In the Counter function, the register is incremented in response to a1-to-0 transition at its corresponding external input pin, T2. In this function, the external input is sampled during S5P2 of every machine cycle. When the samples show a high in one cycle and a low in the next cycle, the count is incremented. The new count value appears in the register during S3P1 of the cycle following the one in which the transition was detected. Since two machine cycles (24 oscillator periods) are required to recognize a 1-to-0 transition, the maximum count rate is 1/24 of the oscillator frequency. To ensure that a given level is sampled at least once before it changes, the level should be held for at least one full machine cycle.InterruptsThe AT89S52 has a total of six interrupt vectors: two external interrupts (INT0 and INT1), three timer interrupts (Timers 0, 1, and 2), and the serial port interrupt. These interrupts are all shown in Figure 10.Each of these interrupt sources can be individually enabled or disabledby setting or clearing a bit in Special Function Register IE. IE also contains a global disable bit, EA, which disables all interrupts at once.Note that Table 5 shows that bit position IE.6 is unimplemented. In the AT89S52, bit position IE.5 is also unimplemented. User software should not write 1s to these bit positions, since they may be used in future AT89 products. Timer 2 interrupt is generated by the logical OR of bits TF2 and EXF2 in register T2CON. Neither of these flags is cleared by hardware when the service routine is vectored to. In fact, the service routine may have to determine whether it was TF2 or EXF2 that generated the interrupt, and that bit will have to be cleared in software.The Timer 0 and Timer 1 flags, TF0 and TF1, are set at S5P2 of the cycle in which the timers overflow. The values are then polled by the circuitry in the next cycle. However, the Timer 2 flag, TF2, is set at S2P2 and is polled in the same cycle in which the timer overflows.二、译文单片机单片机即微型计算机,是把中央处理器、存储器、定时/计数器、输入输出接口都集成在一块集成电路芯片上的微型计算机。
毕业设计(论文)外文翻译【范本模板】
华南理工大学广州学院本科生毕业设计(论文)翻译英文原文名Review of Vibration Analysis Methods for Gearbox Diagnostics and Prognostics中文译名对变速箱振动分析的诊断和预测方法综述学院汽车工程学院专业班级车辆工程七班学生姓名刘嘉先学生学号201130085184指导教师李利平填写日期2015年3月15日英文原文版出处:Proceedings of the 54th Meeting of the Society for Machinery Failure Prevention Technology, Virginia Beach,V A, May 1-4,2000,p. 623-634译文成绩:指导教师(导师组长)签名:译文:简介特征提取技术在文献中有描述;然而,大多数人似乎掩盖所需的特定的预处理功能。
一些文件没有提供足够的细节重现他们的结果,并没有一个全面的比较传统的功能过渡齿轮箱数据。
常用术语,如“残差信号”,是指在不同的文件不同的技术.试图定义了状态维修社区中的常用术语和建立所需的特定的预处理加工特性。
本文的重点是对所使用的齿轮故障检测功能。
功能分为五个不同的组基于预处理的需要。
论文的第一部分将提供预处理流程的概述和其中每个特性计算的处理方案。
在下一节中,为特征提取技术描述,将更详细地讨论每一个功能。
最后一节将简要概述的宾夕法尼亚州立大学陆军研究实验室的CBM工具箱用于齿轮故障诊断。
特征提取概述许多类型的缺陷或损伤会增加机械振动水平。
这些振动水平,然后由加速度转换为电信号进行数据测量。
原则上,关于受监视的计算机的健康的信息被包含在这个振动签名。
因此,新的或当前振动签名可以与以前的签名进行比较,以确定该元件是否正常行为或显示故障的迹象。
在实践中,这种比较是不能奏效的。
由于大的变型中,签名的直接比较是困难的。
相反,一个涉及从所述振动署名数据特征提取更多有用的技术也可以使用。
毕业设计(论文)外文资料翻译〔含原文〕【范本模板】
南京理工大学毕业设计(论文)外文资料翻译教学点: 南京信息职业技术学院专业:电子信息工程姓名:陈洁学号:014910253034外文出处:《Pci System Architecture 》(用外文写)附件: 1.外文资料翻译译文;2。
外文原文。
附件1:外文资料翻译译文64位PCI扩展1.64位数据传送和64位寻址:独立的能力PCI规范给出了允许64位总线主设备与64位目标实现64位数据传送的机理。
在传送的开始,如果回应目标是一个64位或32位设备,64位总线设备会自动识别.如果它是64位设备,达到8个字节(一个4字)可以在每个数据段中传送。
假定是一串0等待状态数据段。
在33MHz总线速率上可以每秒264兆字节获取(8字节/传送*33百万传送字/秒),在66MHz总线上可以528M字节/秒获取.如果回应目标是32位设备,总线主设备会自动识别并且在下部4位数据通道上(AD[31::00])引导,所以数据指向或来自目标。
规范也定义了64位存储器寻址功能。
此功能只用于寻址驻留在4GB地址边界以上的存储器目标。
32位和64位总线主设备都可以实现64位寻址。
此外,对64位寻址反映的存储器目标(驻留在4GB地址边界上)可以看作32位或64位目标来实现。
注意64位寻址和64位数据传送功能是两种特性,各自独立并且严格区分开来是非常重要的。
一个设备可以支持一种、另一种、都支持或都不支持。
2.64位扩展信号为了支持64位数据传送功能,PCI总线另有39个引脚。
●REQ64#被64位总线主设备有效表明它想执行64位数据传送操作.REQ64#与FRAME#信号具有相同的时序和间隔。
REQ64#信号必须由系统主板上的上拉电阻来支持.当32位总线主设备进行传送时,REQ64#不能又漂移。
●ACK64#被目标有效以回应被主设备有效的REQ64#(如果目标支持64位数据传送),ACK64#与DEVSEL#具有相同的时序和间隔(但是直到REQ64#被主设备有效,ACK64#才可被有效).像REQ64#一样,ACK64#信号线也必须由系统主板上的上拉电阻来支持。
毕业设计(论文)外文资料翻译【范本模板】
南京理工大学紫金学院毕业设计(论文)外文资料翻译系:机械系专业:车辆工程专业姓名:宋磊春学号:070102234外文出处:EDU_E_CAT_VBA_FF_V5R9(用外文写)附件:1。
外文资料翻译译文;2.外文原文.附件1:外文资料翻译译文CATIA V5 的自动化CATIA V5的自动化和脚本:在NT 和Unix上:脚本允许你用宏指令以非常简单的方式计划CATIA。
CATIA 使用在MS –VBScript中(V5.x中在NT和UNIX3。
0 )的共用部分来使得在两个平台上运行相同的宏。
在NT 平台上:自动化允许CATIA像Word/Excel或者Visual Basic程序那样与其他外用分享目标。
ATIA 能使用Word/Excel对象就像Word/Excel能使用CATIA 对象。
在Unix 平台上:CATIA将来的版本将允许从Java分享它的对象。
这将提供在Unix 和NT 之间的一个完美兼容。
CATIA V5 自动化:介绍(仅限NT)自动化允许在几个进程之间的联系:CATIA V5 在NT 上:接口COM:Visual Basic 脚本(对宏来说),Visual Basic 为应用(适合前:Word/Excel ),Visual Basic。
COM(零部件目标模型)是“微软“标准于几个应用程序之间的共享对象。
Automation 是一种“微软“技术,它使用一种解释环境中的COM对象。
ActiveX 组成部分是“微软“标准于几个应用程序之间的共享对象,即使在解释环境里。
OLE(对象的链接与嵌入)意思是资料可以在一个其他应用OLE的资料里连结并且可以被编辑的方法(在适当的位置编辑).在VBScript,VBA和Visual Basic之间的差别:Visual Basic(VB)是全部的版本。
它能产生独立的计划,它也能建立ActiveX 和服务器。
它可以被编辑。
VB中提供了一个补充文件名为“在线丛书“(VB的5。
毕业设计(论文)外文资料翻译
毕业设计(论文)外文资料翻译学院:艺术学院专业:环境设计姓名:学号:外文出处: The Swedish Country House附件: 1.外文资料翻译译文;2.外文原文附件1:外文资料翻译译文室内装饰简述一室内装饰设计要素1 空间要素空间的合理化并给人们以美的感受是设计基本的任务。
要勇于探索时代、技术赋于空间的新形象,不要拘泥于过去形成的空间形象。
2 色彩要求室内色彩除对视觉环境产生影响外,还直接影响人们的情绪、心理。
科学的用色有利于工作,有助于健康。
色彩处理得当既能符合功能要求又能取得美的效果。
室内色彩除了必须遵守一般的色彩规律外,还随着时代审美观的变化而有所不同。
3 光影要求人类喜爱大自然的美景,常常把阳光直接引入室内,以消除室内的黑暗感和封闭感,特别是顶光和柔和的散射光,使室内空间更为亲切自然。
光影的变换,使室内更加丰富多彩,给人以多种感受。
4 装饰要素室内整体空间中不可缺少的建筑构件、如柱子、墙面等,结合功能需要加以装饰,可共同构成完美的室内环境。
充分利用不同装饰材料的质地特征,可以获得千变完化和不同风格的室内艺术效果,同时还能体现地区的历史文化特征。
5 陈设要素室内家具、地毯、窗帘等,均为生活必需品,其造型往往具有陈设特征,大多数起着装饰作用。
实用和装饰二者应互相协调,求的功能和形式统一而有变化,使室内空间舒适得体,富有个性。
6 绿化要素室内设计中绿化以成为改善室内环境的重要手段。
室内移花栽木,利用绿化和小品以沟通室内外环境、扩大室内空间感及美化空间均起着积极作用。
二室内装饰设计的基本原则1 室内装饰设计要满足使用功能要求室内设计是以创造良好的室内空间环境为宗旨,使室内环境合理化、舒适化、科学化;要考虑人们的活动规律处理好空间关系,空间尺寸,空间比例;合理配置陈设与家具,妥善解决室内通风,采光与照明,注意室内色调的总体效果。
2 室内装饰设计要满足精神功能要求室内设计的精神就是要影响人们的情感,乃至影响人们的意志和行动,所以要研究人们的认识特征和规律;研究人的情感与意志;研究人和环境的相互作用。
毕业设计(论文)外文资料翻译(学生用)
毕业设计外文资料翻译学院:信息科学与工程学院专业:软件工程姓名: XXXXX学号: XXXXXXXXX外文出处: Think In Java (用外文写)附件: 1.外文资料翻译译文;2.外文原文。
附件1:外文资料翻译译文网络编程历史上的网络编程都倾向于困难、复杂,而且极易出错。
程序员必须掌握与网络有关的大量细节,有时甚至要对硬件有深刻的认识。
一般地,我们需要理解连网协议中不同的“层”(Layer)。
而且对于每个连网库,一般都包含了数量众多的函数,分别涉及信息块的连接、打包和拆包;这些块的来回运输;以及握手等等。
这是一项令人痛苦的工作。
但是,连网本身的概念并不是很难。
我们想获得位于其他地方某台机器上的信息,并把它们移到这儿;或者相反。
这与读写文件非常相似,只是文件存在于远程机器上,而且远程机器有权决定如何处理我们请求或者发送的数据。
Java最出色的一个地方就是它的“无痛苦连网”概念。
有关连网的基层细节已被尽可能地提取出去,并隐藏在JVM以及Java的本机安装系统里进行控制。
我们使用的编程模型是一个文件的模型;事实上,网络连接(一个“套接字”)已被封装到系统对象里,所以可象对其他数据流那样采用同样的方法调用。
除此以外,在我们处理另一个连网问题——同时控制多个网络连接——的时候,Java内建的多线程机制也是十分方便的。
本章将用一系列易懂的例子解释Java的连网支持。
15.1 机器的标识当然,为了分辨来自别处的一台机器,以及为了保证自己连接的是希望的那台机器,必须有一种机制能独一无二地标识出网络内的每台机器。
早期网络只解决了如何在本地网络环境中为机器提供唯一的名字。
但Java面向的是整个因特网,这要求用一种机制对来自世界各地的机器进行标识。
为达到这个目的,我们采用了IP(互联网地址)的概念。
IP以两种形式存在着:(1) 大家最熟悉的DNS(域名服务)形式。
我自己的域名是。
所以假定我在自己的域内有一台名为Opus的计算机,它的域名就可以是。
毕业设计外文文献翻译

毕业设计外文文献翻译Graduation design of foreign literature translation 700 words Title: The Impact of Artificial Intelligence on the Job Market Abstract:With the rapid development of artificial intelligence (AI), concerns arise about its impact on the job market. This paper explores the potential effects of AI on various industries, including healthcare, manufacturing, and transportation, and the implications for employment. The findings suggest that while AI has the potential to automate repetitive tasks and increase productivity, it may also lead to job displacement and a shift in job requirements. The paper concludes with a discussion on the importance of upskilling and retraining for workers to adapt to the changing job market.1. IntroductionArtificial intelligence (AI) refers to the development of computer systems that can perform tasks that typically require human intelligence. AI has made significant advancements in recent years, with applications in various industries, such as healthcare, manufacturing, and transportation. As AI technology continues to evolve, concerns arise about its impact on the job market. This paper aims to explore the potential effects of AI on employment and discuss the implications for workers.2. Potential Effects of AI on the Job Market2.1 Automation of Repetitive TasksOne of the major impacts of AI on the job market is the automation of repetitive tasks. AI systems can perform tasks faster and moreaccurately than humans, particularly in industries that involve routine and predictable tasks, such as manufacturing and data entry. This automation has the potential to increase productivity and efficiency, but also poses a risk to jobs that can be easily replicated by AI.2.2 Job DisplacementAnother potential effect of AI on the job market is job displacement. As AI systems become more sophisticated and capable of performing complex tasks, there is a possibility that workers may be replaced by machines. This is particularly evident in industries such as transportation, where autonomous vehicles may replace human drivers, and customer service, where chatbots can handle customer inquiries. While job displacement may lead to short-term unemployment, it also creates opportunities for new jobs in industries related to AI.2.3 Shifting Job RequirementsWith the introduction of AI, job requirements are expected to shift. While AI may automate certain tasks, it also creates a demand for workers with the knowledge and skills to develop and maintain AI systems. This shift in job requirements may require workers to adapt and learn new skills to remain competitive in the job market.3. Implications for EmploymentThe impact of AI on employment is complex and multifaceted. On one hand, AI has the potential to increase productivity, create new jobs, and improve overall economic growth. On the other hand, it may lead to job displacement and a shift in job requirements. To mitigate the negative effects of AI on employment, it is essentialfor workers to upskill and retrain themselves to meet the changing demands of the job market.4. ConclusionIn conclusion, the rapid development of AI has significant implications for the job market. While AI has the potential to automate repetitive tasks and increase productivity, it may also lead to job displacement and a shift in job requirements. To adapt to the changing job market, workers should focus on upskilling and continuous learning to remain competitive. Overall, the impact of AI on employment will depend on how it is integrated into various industries and how workers and policymakers respond to these changes.。
毕设外文翻译电子版
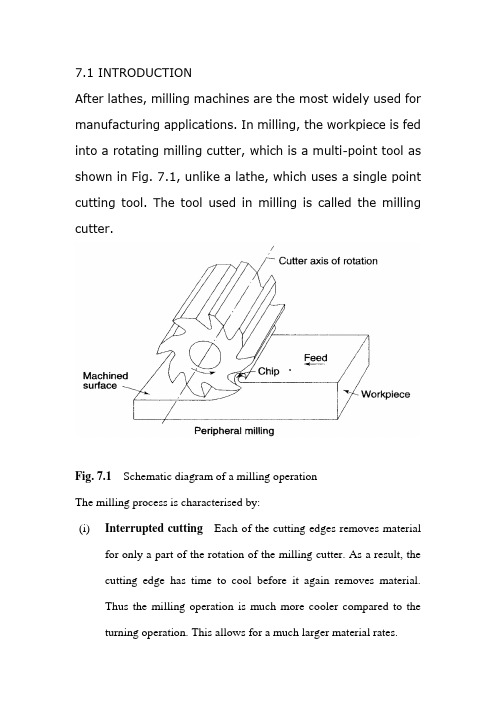
7.1 INTRODUCTIONAfter lathes, milling machines are the most widely used for manufacturing applications. In milling, the workpiece is fed into a rotating milling cutter, which is a multi-point tool as shown in Fig. 7.1, unlike a lathe, which uses a single point cutting tool. The tool used in milling is called the milling cutter.Fig. 7.1Schematic diagram of a milling operationThe milling process is characterised by:(i)Interrupted cutting Each of the cutting edges removes materialfor only a part of the rotation of the milling cutter. As a result, the cutting edge has time to cool before it again removes material.Thus the milling operation is much more cooler compared to the turning operation. This allows for a much larger material rates.(ii)Small size of chips Though the size of the chips is small, in view of the multiple cutting edges in contact a large amount of material is removed and as a result the component is generally completed ina single pass unlike the turning process which requires a largenumber of cuts for finishing.(iii)Variation in chip thickness This contributes to the non-steady state cyclic conditions of varying cutting forces during the contact of the cutting edge with the chip thickness varying from zero to maximum size or vice versa. This cyclic variation of the force can excite any of the natural frequencies of the machine tool system and is harmful to the tool life and surface finish generatedA milling machine is one of the most versatile machine tools. It is adaptable for quantity production as well as in job shops and tool rooms. The versatility of milling is because of the large variety of accessories and tools available with milling machines. The typical tolerance expected from the process is about ±0.050 mm.7.2 TYPES OF MILLING MACHINESTo satisfy various requirements milling machines come in a number of sizes and varieties. In view of the large material removal ratesmilling machines come with a very rigid spindle and large power. The varieties of milling machines available are:(i) Knee and Column type(a) horizontal(b) vertical(c) universal(d) turret typeThese are the general purpose milling machines, which have a high degree of flexibility and are employed for all types of works including batch manufacturing. A large variety of attachments to improve the flexibility are available for this class of milling machines.(ii) Production (Bed) type(a) simplex(b) duplex(c) triplexThese machines are generally meant for regular production involving large batch sizes. The flexibility is relatively less in these machines which is suitable for productivity enhancement.(iii) Plano millersThese machines are used only for very large workpieces involving table travels in meters.(iv) Special type(a) Rotary table(b) Drum type(c) Copy milling (Die sinking machines)(d) Key way milling machines(e) Spline shaft milling machinesThese machines provide special facilities to suit specific applications that are not catered to by the other classes of milling machines.7.2.1 Knee and Column Milling MachinesThe knee(升降台) and column type is the most commonly used machine in view of its flexibility and easier setup. A typical machine construction is shown in Fig. 7.2 for the horizontal axis. The knee houses the feed mechanism and mounts the saddle and table. The table basically has the T-slots running along the X-axis for the purpose of work holding. The table moves along the X-axis on the saddle while the saddle moves along the Y-axis on the guide ways provided on the knee.The feed is provided either manually with a hand wheel or connected for automatic by the lead screw, which in turn is coupled to the main spindle drive. The knee can move up and down (Z-axis) on a dovetail provided on the column.Fig. 7.2 Horizontal knee and column type milling machineThe massive column at the back of the machine houses all the power train including the motor and the spindle gearbox. The power for feeding the table lead screw is taken from the main motor through a separate feed gearbox. Sometimes a separate feed motor is provided for the feed gearbox as well.While the longitudinal and traverse motions are provided with automatic motion, the raising of the knee is generally made manually.The spindle is located at the top end of the column. The arbour used to mount the milling cutters is mounted in the spindle and is provided with a support on the other end to take care of the heavy cutting forces by means of an overarm with bearing. As shown in Fig.7.2 the overarm extends from the column with a rigid design. The spindle nose has the standard Morse taper of the suitable sizedepending upon the machine size.The milling cutters are mounted on the arbour at any desired position, the rest of the length being filled by standard hardened collars of varying widths to fix the position of the cutter. The arbour is clamped in the spindle with the help of a draw bar and then fixed with nuts.Milling machines are generally specified on the following basis:(i) Size of the table, which specifies the actual working area on the table and relates to the maximum size of the workpiece that can be accommodated.(ii) Amount of table travel, which gives the maximum axis movement that is possible.(iii) Horse power of the spindle, which actually specifies the power of the spindle motor used. Smaller machines may come with 1 to 3 hp while the production machines may go from 10 to 50 hp.Another type of knee and column milling machine is the vertical axis type. Its construction is very similar to the horizontal axis type, except for the spindle type and location.The vertical axis milling machine is relatively more flexible (Fig. 7.4) and suitable for machining complex cavities such as die cavities in tool rooms. The vertical head is provided with a swiveling facility in horizontal direction whereby the cutter axis can be swivelled. This isuseful for tool rooms where more complex milling operations are carried out.The spindle is located in the vertical direction and is suitable for using the shank mounted milling cutters such as end mills, In view of the location of the tool, the setting up of the workpiece and observing the machining operation is more convenient.Fig, 7.3 Vertical knee and column type milling machineFig.7.4 Some of the milling operations normally carried out on vertical axis machinesThe universal machine has the table which can be swivelled in a horizontal plane at about 45o to either the left or right. This makes the universal machine suitable for milling spur and helical gears as well as worm gears and cams.7.2.2 Bed Type Milling MachineIn production milling machines it is desirable to increase the metal removal rates. If it is done on conventional machines by increasingthe depth of cut, there is possibility of chatter. Hence another varietyof milling machines named as bed type machines are used which are made more rugged and are capable of removing more material. The ruggedness is obtained as a consequence of the reduction in versatility.The table in the case of bed type machines is directly mounted on the bed and is provided with only longitudinal motion.The spindle moves along with the column to provide the cutting action. Simplex machines (Fig. 7.5) are the ones with only one spindle head while duplex machines have two spindles (Fig. 7.6). The two spindles are located on either side of a heavy workpiece and remove material from both sides simultaneously.Fig. 7.5 Simplex bed type milling machineFig. 7.6 Duplex bed type milling machine7.3 MILLING CUTTERSThere are a large variety of milling cutters available to suit specific requirements. The versatility of the milling machine is contributed toa great extent by the variety of milling cutters that are available.7.3.1 Types of Milling CuttersMilling cutters are classified into various types based on a variety of methods.(i) Based on construction:(a) Solid(b) Inserted tooth typeBased on mounting:(a) Arbor mounted(b) Shank mounted(c) Nose mountedBase on rotation:(a) Right hand rotation (counter clockwise)(b) Left hand rotation (clockwise)Based on helix:(a) Right hand helix(b) Left hand helixMilling cutters are generally made of high speed steel or cemented carbides. The cemented carbide cutters can be of a brazed tip variety or with indexable tips. The indexable variety is more common since it is normally less expensive to replace the worn out cutting edges than to regrind them.Plain milling cutters These are also called slab milling cutters and are basically cylindrical with the cutting teeth on the periphery as shown in Fig. 7.7. These are generally used for machining flat surfaces.Fig. 7.7 Arbor mounted milling cutters for general purposeLight duty slab milling cutters generally have a face width, which is small of the order of 25 mm. They generally have straight teeth and large number of teeth.Heavy duty slab milling cutters come with a smaller number of teeth to allow for more chip space. This allows taking deeper cuts and consequently high material removal rates.Helical milling cutters have a very small number of teeth but a large helix angle. This type of cutter cuts with a shearing action, which can produce a very fine finish. The large helix angle allows the cutter to absorb most of the end load and therefore the cutter enters and leaves the workpiece very smoothly.Side and face milling cutters These have the cutting edges not only onthe face like the slab milling cutters, but also on both the sides. As aresult, these cutters become more versatile since they can be used for side milling as well as for slot milling.Staggered tooth side milling cutters are a variation where the teeth are arranged in an alternate helix pattern. This type is generally used for milling deep slots, since the staggering of teeth provides for greater chip space.Another variation of the side and face cutter is the half side milling cutter, which has cutting edges only on one side. This arrangement provides a positive rake angle and is useful for machining on only one side. These have a much smoother cutting action and a long tool life. The power consumed is also less for these cutters.Fig. 7.8Special forms of arbor mounted milling cuttersSlitting saws The other common form of milling cutters in the arbor mounted category is the slitting saw. This is very similar to a saw blade inappearance as well as function. Most of these have teeth around the circumference while some have side teeth as well. The thickness of these cutters is generally very small and is used for cutting off operations or for deep slots.Special form cutters In addition to the general type of milling cutters described above, there are a large number of special form milling cutters available which are used for machining specific profiles.Angular milling cutters are made in single or double angle cutters for milling any angle such as 30, 45 or 60o Form relieved cutters are made of various shapes such as circular, corner rounding, convex or concave shapes.T-slot milling cutters are used for milling T-slots such as those in the milling machine table. The central slot is to be milled first using an end mill before using the T-slot milling cutter. Woodruff key seat milling cutters are used for milling as the name suggests, woodruff key seats Some other special form cutters are dovetail milling cutters and gear milling cutters.End mills These are shank mounted as shown in Fig. 7.9 and are generally used in vertical axis milling machines. They are used for milling slots, key ways and pockets where other type of milling cutters cannot be used. A depth of cut of almost half the diameter can be taken with the end mills.The end mills have the cutting edge running through the length of the cutting portion as well as on the face radially up to a certain length. The helix angle of the cutting edge promotes smooth and efficient cutting even at high cutting speeds and feed rates. High cutting speeds(转速?) are generally recommended for this type of milling cutters.Fig. 7.9 Shank mounted milling cutters and various types of end mills There are a large variety of end mills. One of the distinctions is based on the method of holding, i.e., the end mill shank can be straight or tapered. The straight shank is used on end mills of small size and held in the milling machine spindle with the help of a suitable collet. The tapered shank can be directly mounted in the spindle with the help of the selfholding taper. If the taper is small compared to the spindle taper, then an adopter accommodating both the tapers is used.The end teeth of the end mills may be terminated at a distance from the cutter center or may proceed till the center (Fig. 7.9 f). Those with the cutting edge up to the center are called slot drills or end cutting end mills since they have the ability to cut into the solid material (Fig. 7.9 g). The other type of end mills which have a larger number of teeth cannot cut into solid material and hence require a pilot hole drilled before a pocket is machined.The cutting edge along the side of an end mill is generally straight and sometimes can be tapered by grinding on a tool and cutter grinder such that the draft required for mould and die cavities can be automatically generated.。
1.毕设外文翻译(原版)

IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. AC-19, NO.
5,
OCTOBER
1974
H. P. Geering, “ O p t k l control theory for nonscalar-valued [22] L. A. Zadeh, “Optimality and non-scalar-valued performance performance criteria, Ph.D. dissertation, Dept. Elec. Eng., criteria,” I E E E Trans. Automat. Contr. (Corresp.), vol. AC-8, Mass. Inst. Technol., Cambridge, Aug. 1971 (available in the pp. 59-60, 1963. form of Microfiche Nr. AD 731213, NTIS, U. S. Dept. of Comm.). theory for H. P. Geering and M. Athans,“Optimalcontrol non-scalar-valued performance criteria,” in Proc. 5th Ann. Princeton Conf. Information Sciences and Systems, Princeton, N.J., Mar. 1971. H. Halkin, “On the necessary condition for optimal control of non-linear systems,” J . Analyse Mathhatique, vol. 12, pp. IHans P. Geering (S’7&M’71) was bornon 82, 1964. June 7, 1942. H e received the degree of H. Halkin, “Topological aspects of optimal control of dynamicalpolysystems,” Contrib. Differential Equations, vol. 3, pp. Diplomierter Elektroingenieur from the Eid377-385. 1964. genoesische Technische Hochschulein Zurich, E. B. Lee and L. Markus, Foundations of Optimal Control Switzerland, in 1966, and the M.S. and Ph.D. Theory. New York: Wiley, 1967. degrees from the Massachusetts Institute of L. W.-Neustadt, “A general theory of extremals,” J . Comput. Technology, Cambridge,in 1969 and 1971, Sci. Syst., V O ~ .3, pp. 57-92, 1969. respectively. C. Olech, “Existence theorems for optimal problems with vecIn 1967 and 1968, he worked with Sprecher tor valued cost function,” Center of Dynamical Systems, & Schuh AG in Suhr, Switzerland, and Brown University, Providence, R.I., Tech. Rep. 67-6, 1967. Oerlikon-Buehrle AG in Zurich, Switzerland, K. Ritter, “Optimization theory in linear spaces-Part I,” Math. Annul., vol. 182, pp. 189-206, 1969. From September, 1968 to August, 1971 he was a Research Assistant , “Optimization theory in linear spaces-Part 11,” Math. in the M.I.T. Electronic Systems Laboratory and a Teaching AsAnnal., vol. 183, pp. 169-180, 1969. sistant in the Department of Electrical Engineering at M.I.T. He is , “Optimization theory in linear spaces-Part 111,”Math. presently with Oerlikon-Buehrle AG. His research interests are in Annul., vol. 184, pp. 133-154, 1970. estimation and control theory. R.. T. ltockafellar, Con.vexAnalysis. Princeton, N.J.: Princeton Dr. Geel.ing is a member of Schweizerische Gesellschaft fur AutoUniv. Press, 1970. E. Tse. “On the oDtimal control of linear svstems with in- matik (IFAC) and Schweizerischer Elektrotechnischer Verein. completeinformati&,” Ph.D. dissertation, U*ep. Elec. Eng., Mass. Inst. Technol., Cambridge, Nov., 1969. [20] B. Z. Vulikh, Introduction to the Theory of Partially Ordered Spaces. Groningen, The Netherlands: Wolters-Noordhoff Sc., 1967. [21] H. S. Witsenhausen, “Minimax control of uncertain system,” Electronic Systems Lab., Mass. Inst. Technol., Cambridge, Michael Athans (S’58-M%-SM’69-F’73) for a photograph and Rep. ESGIt-269, 1966. biography see page 30 of February the issue of TRANSACTIONS. this
毕业设计英文原文

-/L
t
1
Rise time of input signal
Input Response of probe to perfect input Scope probe
~--~-/L v-- t
3
Response of vertical amplifier to perfect input
Vertical amplifier
2Equation 3.1 holds strictly true only when each impulse response in Figure 3.2 is gaussian. For other impulse response shapes Equation 3.1 is very close to true, but not exact. See Appendix B for more information about the exact calculation of rise time in cascaded systems.
T.
10-90 -
_ 0.338
F
[3.2]
3dB
Specifications from instrument manufacturers quoting RMS bandwidth, or equivalent noise bandwidth F RMS ' should be converted according to (see also Equation 1.7)
Figure 3.2
Rise time of oscilloscope components.
When a realistic input feeds the combination of probe and vertical amplifier, as in Figure 3.3, the rise time of the result is equal to the square root of the sum of the squares of the rise times of each component.
毕业设计英文 翻译(原文)
编号:毕业设计(论文)外文翻译(原文)院(系):桂林电子科技大学专业:电子信息工程学生姓名: xx学号: xxxxxxxxxxxxx 指导教师单位:桂林电子科技大学姓名: xxxx职称: xx2014年x月xx日Timing on and off power supplyusesThe switching power supply products are widely used in industrial automation and control, military equipment, scientific equipment, LED lighting, industrial equipment,communications equipment,electrical equipment,instrumentation, medical equipment, semiconductor cooling and heating, air purifiers, electronic refrigerator, LCD monitor, LED lighting, communications equipment, audio-visual products, security, computer chassis, digital products and equipment and other fields.IntroductionWith the rapid development of power electronics technology, power electronics equipment and people's work, the relationship of life become increasingly close, and electronic equipment without reliable power, into the 1980s, computer power and the full realization of the switching power supply, the first to complete the computer Power new generation to enter the switching power supply in the 1990s have entered into a variety of electronic, electrical devices, program-controlled switchboards, communications, electronic testing equipment power control equipment, power supply, etc. have been widely used in switching power supply, but also to promote the rapid development of the switching power supply technology .Switching power supply is the use of modern power electronics technology to control the ratio of the switching transistor to turn on and off to maintain a stable output voltage power supply, switching power supply is generally controlled by pulse width modulation (PWM) ICs and switching devices (MOSFET, BJT) composition. Switching power supply and linear power compared to both the cost and growth with the increase of output power, but the two different growth rates. A power point, linear power supply costs, but higher than the switching power supply. With the development of power electronics technology and innovation, making the switching power supply technology to continue to innovate, the turning points of this cost is increasingly move to the low output power side, the switching power supply provides a broad space for development.The direction of its development is the high-frequency switching power supply, high frequency switching power supply miniaturization, and switching power supply into a wider range of application areas, especially in high-tech fields, and promote the miniaturization of high-tech products, light of. In addition, the development and application of the switching power supply in terms of energy conservation, resource conservation and environmental protection are of great significance.classificationModern switching power supply, there are two: one is the DC switching power supply; the other is the AC switching power supply. Introduces only DC switching power supply and its function is poor power quality of the original eco-power (coarse) - such as mains power or battery power, converted to meet the equipment requirements of high-quality DC voltage (Varitronix) . The core of the DC switching power supply DC / DC converter. DC switching power supply classification is dependent on the classification of DC / DC converter. In other words, the classification of the classification of the DC switching power supply and DC/DC converter is the classification of essentially the same, the DC / DC converter is basically a classification of the DC switching power supply.DC /DC converter between the input and output electrical isolation can be divided into two categories: one is isolated called isolated DC/DC converter; the other is not isolated as non-isolated DC / DC converter.Isolated DC / DC converter can also be classified by the number of active power devices. The single tube of DC / DC converter Forward (Forward), Feedback (Feedback) two. The double-barreled double-barreled DC/ DC converter Forward (Double Transistor Forward Converter), twin-tube feedback (Double Transistor Feedback Converter), Push-Pull (Push the Pull Converter) and half-bridge (Half-Bridge Converter) four. Four DC / DC converter is the full-bridge DC / DC converter (Full-Bridge Converter).Non-isolated DC / DC converter, according to the number of active power devices can be divided into single-tube, double pipe, and four three categories. Single tube to a total of six of the DC / DC converter, step-down (Buck) DC / DC converter, step-up (Boost) DC / DC converters, DC / DC converter, boost buck (Buck Boost) device of Cuk the DC / DC converter, the Zeta DC / DC converter and SEPIC, the DC / DC converter. DC / DC converters, the Buck and Boost type DC / DC converter is the basic buck-boost of Cuk, Zeta, SEPIC, type DC / DC converter is derived from a single tube in this six. The twin-tube cascaded double-barreled boost (buck-boost) DC / DC converter DC / DC converter. Four DC / DC converter is used, the full-bridge DC / DC converter (Full-Bridge Converter).Isolated DC / DC converter input and output electrical isolation is usually transformer to achieve the function of the transformer has a transformer, so conducive to the expansion of the converter output range of applications, but also easy to achieve different voltage output , or a variety of the same voltage output.Power switch voltage and current rating, the converter's output power is usually proportional to the number of switch. The more the number of switch, the greater the output power of the DC / DC converter, four type than the two output power is twice as large,single-tube output power of only four 1/4.A combination of non-isolated converters and isolated converters can be a single converter does not have their own characteristics. Energy transmission points, one-way transmission and two-way transmission of two DC / DC converter. DC / DC converter with bi-directional transmission function, either side of the transmission power from the power of lateral load power from the load-lateral side of the transmission power.DC / DC converter can be divided into self-excited and separately controlled. With the positive feedback signal converter to switch to self-sustaining periodic switching converter, called self-excited converter, such as the the Luo Yeer (Royer,) converter is a typical push-pull self-oscillating converter. Controlled DC / DC converter switching device control signal is generated by specialized external control circuit.the switching power supply.People in the field of switching power supply technology side of the development of power electronic devices, while the development of the switching inverter technology, the two promote each other to promote the switching power supply annual growth rate of more than two digits toward the light, small, thin, low-noise, high reliability, the direction of development of anti-jamming. Switching power supply can be divided into AC / DC and DC / DC two categories, AC / AC DC / AC, such as inverters, DC / DC converter is now modular design technology and production processes at home and abroad have already matured and standardization, and has been recognized by the user, but AC / DC modular, its own characteristics make the modular process, encounter more complex technology and manufacturing process. Hereinafter to illustrate the structure and characteristics of the two types of switching power supply.Self-excited: no external signal source can be self-oscillation, completely self-excited to see it as feedback oscillation circuit of a transformer.Separate excitation: entirely dependent on external sustain oscillations, excited used widely in practical applications. According to the excitation signal structure classification; can be divided into pulse-width-modulated and pulse amplitude modulated two pulse width modulated control the width of the signal is frequency, pulse amplitude modulation control signal amplitude between the same effect are the oscillation frequency to maintain within a certain range to achieve the effect of voltage stability. The winding of the transformer can generally be divided into three types, one group is involved in the oscillation of the primary winding, a group of sustained oscillations in the feedback winding, there is a group of load winding. Such as Shanghai is used in household appliances art technological production of switching power supply, 220V AC bridge rectifier, changing to about 300V DC filter added tothe collector of the switch into the transformer for high frequency oscillation, the feedback winding feedback to the base to maintain the circuit oscillating load winding induction signal, the DC voltage by the rectifier, filter, regulator to provide power to the load. Load winding to provide power at the same time, take up the ability to voltage stability, the principle is the voltage output circuit connected to a voltage sampling device to monitor the output voltage changes, and timely feedback to the oscillator circuit to adjust the oscillation frequency, so as to achieve stable voltage purposes, in order to avoid the interference of the circuit, the feedback voltage back to the oscillator circuit with optocoupler isolation.technology developmentsThe high-frequency switching power supply is the direction of its development, high-frequency switching power supply miniaturization, and switching power supply into the broader field of application, especially in high-tech fields, and promote the development and advancement of the switching power supply, an annual more than two-digit growth rate toward the light, small, thin, low noise, high reliability, the direction of the anti-jamming. Switching power supply can be divided into AC / DC and DC / DC two categories, the DC / DC converter is now modular design technology and production processes at home and abroad have already matured and standardized, and has been recognized by the user, but modular AC / DC, because of its own characteristics makes the modular process, encounter more complex technology and manufacturing process. In addition, the development and application of the switching power supply in terms of energy conservation, resource conservation and environmental protection are of great significance.The switching power supply applications in power electronic devices as diodes, IGBT and MOSFET.SCR switching power supply input rectifier circuit and soft start circuit, a small amount of applications, the GTR drive difficult, low switching frequency, gradually replace the IGBT and MOSFET.Direction of development of the switching power supply is a high-frequency, high reliability, low power, low noise, jamming and modular. Small, thin, and the key technology is the high frequency switching power supply light, so foreign major switching power supply manufacturers have committed to synchronize the development of new intelligent components, in particular, is to improve the secondary rectifier loss, and the power of iron Oxygen materials to increase scientific and technological innovation in order to improve the magnetic properties of high frequency and large magnetic flux density (Bs), and capacitor miniaturization is a key technology. SMT technology allows the switching power supply has made considerable progress, the arrangement of the components in the circuit board on bothsides, to ensure that the light of the switching power supply, a small, thin. High-frequency switching power supply is bound to the traditional PWM switching technology innovation, realization of ZVS, ZCS soft-switching technology has become the mainstream technology of the switching power supply, and a substantial increase in the efficiency of the switching power supply. Indicators for high reliability, switching power supply manufacturers in the United States by reducing the operating current, reducing the junction temperature and other measures to reduce the stress of the device, greatly improve the reliability of products.Modularity is the overall trend of switching power supply, distributed power systems can be composed of modular power supply, can be designed to N +1 redundant power system, and the parallel capacity expansion. For this shortcoming of the switching power supply running noise, separate the pursuit of high frequency noise will also increase, while the use of part of the resonant converter circuit technology to achieve high frequency, in theory, but also reduce noise, but some The practical application of the resonant converter technology, there are still technical problems, it is still a lot of work in this field, so that the technology to be practical.Power electronics technology innovation, switching power supply industry has broad prospects for development. To accelerate the pace of development of the switching power supply industry in China, it must take the road of technological innovation, out of joint production and research development path with Chinese characteristics and contribute to the rapid development of China's national economy.Developments and trends of the switching power supply1955 U.S. Royer (Roger) invented the self-oscillating push-pull transistor single-transformer DC-DC converter is the beginning of the high-frequency conversion control circuit 1957 check race Jen, Sen, invented a self-oscillating push-pull dual transformers, 1964, U.S. scientists canceled frequency transformer in series the idea of switching power supply, the power supply to the size and weight of the decline in a fundamental way. 1969 increased due to the pressure of the high-power silicon transistor, diode reverse recovery time shortened and other components to improve, and finally made a 25-kHz switching power supply.At present, the switching power supply to the small, lightweight and high efficiency characteristics are widely used in a variety of computer-oriented terminal equipment, communications equipment, etc. Almost all electronic equipment is indispensable for a rapid development of today's electronic information industry power mode. Bipolar transistor made of 100kHz, 500kHz power MOS-FET made, though already the practical switching power supply is currently available on the market, but its frequency to be further improved. Toimprove the switching frequency, it is necessary to reduce the switching losses, and to reduce the switching losses, the need for high-speed switch components. However, the switching speed will be affected by the distribution of the charge stored in the inductance and capacitance, or diode circuit to produce a surge or noise. This will not only affect the surrounding electronic equipment, but also greatly reduce the reliability of the power supply itself. Which, in order to prevent the switching Kai - closed the voltage surge, RC or LC buffers can be used, and the current surge can be caused by the diode stored charge of amorphous and other core made of magnetic buffer . However, the high frequency more than 1MHz, the resonant circuit to make the switch on the voltage or current through the switch was a sine wave, which can reduce switching losses, but also to control the occurrence of surges. This switch is called the resonant switch. Of this switching power supply is active, you can, in theory, because in this way do not need to greatly improve the switching speed of the switching losses reduced to zero, and the noise is expected to become one of the high-frequency switching power supply The main ways. At present, many countries in the world are committed to several trillion Hz converter utility.the principle of IntroductionThe switching power supply of the process is quite easy to understand, linear power supplies, power transistors operating in the linear mode and linear power, the PWM switching power supply to the power transistor turns on and off state, in both states, on the power transistor V - security product is very small (conduction, low voltage, large current; shutdown, voltage, current) V oltammetric product / power device is power semiconductor devices on the loss.Compared with the linear power supply, the PWM switching power supply more efficient process is achieved by "chopping", that is cut into the amplitude of the input DC voltage equal to the input voltage amplitude of the pulse voltage. The pulse duty cycle is adjusted by the switching power supply controller. Once the input voltage is cut into the AC square wave, its amplitude through the transformer to raise or lower. Number of groups of output voltage can be increased by increasing the number of primary and secondary windings of the transformer. After the last AC waveform after the rectifier filter the DC output voltage.The main purpose of the controller is to maintain the stability of the output voltage, the course of their work is very similar to the linear form of the controller. That is the function blocks of the controller, the voltage reference and error amplifier can be designed the same as the linear regulator. Their difference lies in the error amplifier output (error voltage) in the drive before the power tube to go through a voltage / pulse-width conversion unit.Switching power supply There are two main ways of working: Forward transformand boost transformation. Although they are all part of the layout difference is small, but the course of their work vary greatly, have advantages in specific applications.the circuit schematicThe so-called switching power supply, as the name implies, is a door, a door power through a closed power to stop by, then what is the door, the switching power supply using SCR, some switch, these two component performance is similar, are relying on the base switch control pole (SCR), coupled with the pulse signal to complete the on and off, the pulse signal is half attentive to control the pole voltage increases, the switch or transistor conduction, the filter output voltage of 300V, 220V rectifier conduction, transmitted through the switching transformer secondary through the transformer to the voltage increase or decrease for each circuit work. Oscillation pulse of negative semi-attentive to the power regulator, base, or SCR control voltage lower than the original set voltage power regulator cut-off, 300V power is off, switch the transformer secondary no voltage, then each circuit The required operating voltage, depends on this secondary road rectifier filter capacitor discharge to maintain. Repeat the process until the next pulse cycle is a half weeks when the signal arrival. This switch transformer is called the high-frequency transformer, because the operating frequency is higher than the 50HZ low frequency. Then promote the pulse of the switch or SCR, which requires the oscillator circuit, we know, the transistor has a characteristic, is the base-emitter voltage is 0.65-0.7V is the zoom state, 0.7V These are the saturated hydraulic conductivity state-0.1V-0.3V in the oscillatory state, then the operating point after a good tune, to rely on the deep negative feedback to generate a negative pressure, so that the oscillating tube onset, the frequency of the oscillating tube capacitor charging and discharging of the length of time from the base to determine the oscillation frequency of the output pulse amplitude, and vice versa on the small, which determines the size of the output voltage of the power regulator. Transformer secondary output voltage regulator, usually switching transformer, single around a set of coils, the voltage at its upper end, as the reference voltage after the rectifier filter, then through the optocoupler, this benchmark voltage return to the base of the oscillating tube pole to adjust the level of the oscillation frequency, if the transformer secondary voltage is increased, the sampling coil output voltage increases, the positive feedback voltage obtained through the optocoupler is also increased, this voltage is applied oscillating tube base, so that oscillation frequency is reduced, played a stable secondary output voltage stability, too small do not have to go into detail, nor it is necessary to understand the fine, such a high-power voltage transformer by switching transmission, separated and after the class returned by sampling the voltage from the opto-coupler pass separated after class, so before the mains voltage, and after the classseparation, which is called cold plate, it is safe, transformers before power is independent, which is called switching power supply.the DC / DC conversionDC / DC converter is a fixed DC voltage transformation into a variable DC voltage, also known as the DC chopper. There are two ways of working chopper, one Ts constant pulse width modulation mode, change the ton (General), the second is the frequency modulation, the same ton to change the Ts, (easy to produce interference). Circuit by the following categories:Buck circuit - the step-down chopper, the average output voltage U0 is less than the input voltage Ui, the same polarity.Boost Circuit - step-up chopper, the average output voltage switching power supply schematic U0 is greater than the input voltage Ui, the same polarity.Buck-Boost circuit - buck or boost chopper, the output average voltage U0 is greater than or less than the input voltage Ui, the opposite polarity, the inductance transmission.Cuk circuit - a buck or boost chopper, the output average voltage U0 is greater than or less than the input voltage Ui, the opposite polarity, capacitance transmission.The above-mentioned non-isolated circuit, the isolation circuit forward circuits, feedback circuit, the half-bridge circuit, the full bridge circuit, push-pull circuit. Today's soft-switching technology makes a qualitative leap in the DC / DC the U.S. VICOR company design and manufacture a variety of ECI soft-switching DC / DC converter, the maximum output power 300W, 600W, 800W, etc., the corresponding power density (6.2 , 10,17) W/cm3 efficiency (80-90)%. A the Japanese Nemic Lambda latest using soft-switching technology, high frequency switching power supply module RM Series, its switching frequency (200 to 300) kHz, power density has reached 27W/cm3 with synchronous rectifier (MOSFETs instead of Schottky diodes ), so that the whole circuit efficiency by up to 90%.AC / DC conversionAC / DC conversion will transform AC to DC, the power flow can be bi-directional power flow by the power flow to load known as the "rectification", referred to as "active inverter power flow returned by the load power. AC / DC converter input 50/60Hz AC due must be rectified, filtered, so the volume is relatively large filter capacitor is essential, while experiencing safety standards (such as UL, CCEE, etc.) and EMC Directive restrictions (such as IEC, FCC, CSA) in the AC input side must be added to the EMC filter and use meets the safety standards of the components, thus limiting the miniaturization of the volume of AC / DC power, In addition, due to internal frequency, high voltage, current switching, making the problem difficult to solve EMC also high demands on the internal high-density mountingcircuit design, for the same reason, the high voltage, high current switch makes power supply loss increases, limiting the AC / DC converter modular process, and therefore must be used to power system optimal design method to make it work efficiency to reach a certain level of satisfaction.AC / DC conversion circuit wiring can be divided into half-wave circuit, full-wave circuit. Press the power phase can be divided into single-phase three-phase, multiphase. Can be divided into a quadrant, two quadrant, three quadrants, four-quadrant circuit work quadrant.he selection of the switching power supplySwitching power supply input on the anti-jamming performance, compared to its circuit structure characteristics (multi-level series), the input disturbances, such as surge voltage is difficult to pass on the stability of the output voltage of the technical indicators and linear power have greater advantages, the output voltage stability up to (0.5)%. Switching power supply module as an integrated power electronic devices should be selected。
毕业设计(论文)外文资料翻译
1、外文原文(复印件)2、外文资料翻译译文节能智能照明控制系统Sherif Matta and Syed Masud Mahmud, SeniorMember, IEEE Wayne State University, Detroit,Michigan 48202Sherif.Matta@,smahmud@摘要节约能源已成为当今最具挑战性的问题之一。
最浪费能源的来自低效利用的电能消耗的人工光源设备(灯具或灯泡)。
本文提出了一种通过把人工照明的强度控制到令人满意的水平,来节约电能,并且有详细设计步骤的系统。
在白天使用照明设备时,尽可能的节约。
当记录超过预设的照明方案时,引入改善日光采集和控制的调光系统。
设计原理是,如果它可以通过利用日光这样的一种方式,去控制百叶窗或窗帘。
否则,它使用的是人工建筑内部的光源。
光通量是通过控制百叶窗帘的开启角度来控制,同时,人工光源的强度的控制,通过控制脉冲宽度来调制(PWM)对直流灯的发电量或剪切AC灯泡的AC波。
该系统采用控制器区域网络(CAN),作为传感器和致动器通信用的介质。
该系统是模块化的,可用来跨越大型建筑物。
该设计的优点是,它为用户提供了一个单点操作,而这个正是用户所希望的光的亮度。
该控制器的功能是确定一种方法来满足所需的最小能量消耗光的量。
考虑的主要问题之一是系统组件的易于安装和低成本。
该系统显示出了显著节省的能源量,和在实际中实施的可行性。
关键词:智能光控系统,节能,光通量,百叶帘控制,控制器区域网络(CAN),光强度的控制一简介多年来,随着建筑物的数量和建筑物房间内的数量急剧增加,能源的浪费、低效光控制和照明分布难以管理。
此外,依靠用户对光的手动控制,来节省能源是不实际的。
很多技术和传感器最近已经向管理过多的能量消耗转变,例如在一定区域内的检测活动采用运动检测。
当有人进入房间时,自动转向灯为他们提供了便利。
他们通过在最后人员离开房间后不久关闭转向灯来减少照明能源的使用。
毕业设计(论文)外文文献原文及译文
毕业设计(论文)外文文献原文及译文Chapter 11. Cipher Techniques11.1 ProblemsThe use of a cipher without consideration of the environment in which it is to be used may not provide the security that the user expects. Three examples will make this point clear.11.1.1 Precomputing the Possible MessagesSimmons discusses the use of a "forward search" to decipher messages enciphered for confidentiality using a public key cryptosystem [923]. His approach is to focus on the entropy (uncertainty) in the message. To use an example from Section 10.1(page 246), Cathy knows that Alice will send one of two messages—BUY or SELL—to Bob. The uncertainty is which one Alice will send. So Cathy enciphers both messages with Bob's public key. When Alice sends the message, Bob intercepts it and compares the ciphertext with the two he computed. From this, he knows which message Alice sent.Simmons' point is that if the plaintext corresponding to intercepted ciphertext is drawn from a (relatively) small set of possible plaintexts, the cryptanalyst can encipher the set of possible plaintexts and simply search that set for the intercepted ciphertext. Simmons demonstrates that the size of the set of possible plaintexts may not be obvious. As an example, he uses digitized sound. The initial calculations suggest that the number of possible plaintexts for each block is 232. Using forward search on such a set is clearly impractical, but after some analysis of the redundancy in human speech, Simmons reduces the number of potential plaintexts to about 100,000. This number is small enough so that forward searches become a threat.This attack is similar to attacks to derive the cryptographic key of symmetric ciphers based on chosen plaintext (see, for example, Hellman's time-memory tradeoff attack [465]). However, Simmons' attack is for public key cryptosystems and does not reveal the private key. It only reveals the plaintext message.11.1.2 Misordered BlocksDenning [269] points out that in certain cases, parts of a ciphertext message can be deleted, replayed, or reordered.11.1.3 Statistical RegularitiesThe independence of parts of ciphertext can give information relating to the structure of the enciphered message, even if the message itself is unintelligible. The regularity arises because each part is enciphered separately, so the same plaintext always produces the same ciphertext. This type of encipherment is called code book mode, because each part is effectively looked up in a list of plaintext-ciphertext pairs.11.1.4 SummaryDespite the use of sophisticated cryptosystems and random keys, cipher systems may provide inadequate security if not used carefully. The protocols directing how these cipher systems are used, and the ancillary information that the protocols add to messages and sessions, overcome these problems. This emphasizes that ciphers and codes are not enough. The methods, or protocols, for their use also affect the security of systems.11.2 Stream and Block CiphersSome ciphers divide a message into a sequence of parts, or blocks, and encipher each block with the same key.Definition 11–1. Let E be an encipherment algorithm, and let Ek(b) bethe encipherment of message b with key k. Let a message m = b1b2…, whereeach biis of a fixed length. Then a block cipher is a cipher for whichE k (m) = Ek(b1)Ek(b2) ….Other ciphers use a nonrepeating stream of key elements to encipher characters of a message.Definition 11–2. Let E be an encipherment algorithm, and let Ek(b) bethe encipherment of message b with key k. Let a message m = b1b2…, whereeach bi is of a fixed length, and let k = k1k2…. Then a stream cipheris a cipher for which Ek (m) = Ek1(b1)Ek2(b2) ….If the key stream k of a stream cipher repeats itself, it is a periodic cipher.11.2.1 Stream CiphersThe one-time pad is a cipher that can be proven secure (see Section 9.2.2.2, "One-Time Pad"). Bit-oriented ciphers implement the one-time pad by exclusive-oring each bit of the key with one bit of the message. For example, if the message is 00101 and the key is 10010, the ciphertext is01||00||10||01||10 or 10111. But how can one generate a random, infinitely long key?11.2.1.1 Synchronous Stream CiphersTo simulate a random, infinitely long key, synchronous stream ciphers generate bits from a source other than the message itself. The simplest such cipher extracts bits from a register to use as the key. The contents of the register change on the basis of the current contents of the register.Definition 11–3. An n-stage linear feedback shift register (LFSR)consists of an n-bit register r = r0…rn–1and an n-bit tap sequence t =t 0…tn–1. To obtain a key bit, ris used, the register is shifted one bitto the right, and the new bit r0t0⊕…⊕r n–1t n–1 is inserted.The LFSR method is an attempt to simulate a one-time pad by generating a long key sequence from a little information. As with any such attempt, if the key is shorter than the message, breaking part of the ciphertext gives the cryptanalyst information about other parts of the ciphertext. For an LFSR, a known plaintext attack can reveal parts of the key sequence. If the known plaintext is of length 2n, the tap sequence for an n-stage LFSR can be determined completely.Nonlinear feedback shift registers do not use tap sequences; instead, the new bit is any function of the current register bits.Definition 11–4. An n-stage nonlinear feedback shift register (NLFSR)consists of an n-bit register r = r0…rn–1. Whenever a key bit is required,ris used, the register is shifted one bit to the right, and the new bitis set to f(r0…rn–1), where f is any function of n inputs.NLFSRs are not common because there is no body of theory about how to build NLFSRs with long periods. By contrast, it is known how to design n-stage LFSRs with a period of 2n– 1, and that period is maximal.A second technique for eliminating linearity is called output feedback mode. Let E be an encipherment function. Define k as a cryptographic key,(r) and define r as a register. To obtain a bit for the key, compute Ekand put that value into the register. The rightmost bit of the result is exclusive-or'ed with one bit of the message. The process is repeated until the message is enciphered. The key k and the initial value in r are the keys for this method. This method differs from the NLFSR in that the register is never shifted. It is repeatedly enciphered.A variant of output feedback mode is called the counter method. Instead of using a register r, simply use a counter that is incremented for every encipherment. The initial value of the counter replaces r as part of the key. This method enables one to generate the ith bit of the key without generating the bits 0…i – 1. If the initial counter value is i, set. In output feedback mode, one must generate all the register to i + ithe preceding key bits.11.2.1.2 Self-Synchronous Stream CiphersSelf-synchronous ciphers obtain the key from the message itself. The simplest self-synchronous cipher is called an autokey cipher and uses the message itself for the key.The problem with this cipher is the selection of the key. Unlike a one-time pad, any statistical regularities in the plaintext show up in the key. For example, the last two letters of the ciphertext associated with the plaintext word THE are always AL, because H is enciphered with the key letter T and E is enciphered with the key letter H. Furthermore, if theanalyst can guess any letter of the plaintext, she can determine all successive plaintext letters.An alternative is to use the ciphertext as the key stream. A good cipher will produce pseudorandom ciphertext, which approximates a randomone-time pad better than a message with nonrandom characteristics (such as a meaningful English sentence).This type of autokey cipher is weak, because plaintext can be deduced from the ciphertext. For example, consider the first two characters of the ciphertext, QX. The X is the ciphertext resulting from enciphering some letter with the key Q. Deciphering, the unknown letter is H. Continuing in this fashion, the analyst can reconstruct all of the plaintext except for the first letter.A variant of the autokey method, cipher feedback mode, uses a shift register. Let E be an encipherment function. Define k as a cryptographic(r). The key and r as a register. To obtain a bit for the key, compute Ek rightmost bit of the result is exclusive-or'ed with one bit of the message, and the other bits of the result are discarded. The resulting ciphertext is fed back into the leftmost bit of the register, which is right shifted one bit. (See Figure 11-1.)Figure 11-1. Diagram of cipher feedback mode. The register r is enciphered with key k and algorithm E. The rightmost bit of the result is exclusive-or'ed with one bit of the plaintext m i to produce the ciphertext bit c i. The register r is right shifted one bit, and c i is fed back into the leftmost bit of r.Cipher feedback mode has a self-healing property. If a bit is corrupted in transmission of the ciphertext, the next n bits will be deciphered incorrectly. But after n uncorrupted bits have been received, the shift register will be reinitialized to the value used for encipherment and the ciphertext will decipher properly from that point on.As in the counter method, one can decipher parts of messages enciphered in cipher feedback mode without deciphering the entire message. Let the shift register contain n bits. The analyst obtains the previous n bits of ciphertext. This is the value in the shift register before the bit under consideration was enciphered. The decipherment can then continue from that bit on.11.2.2 Block CiphersBlock ciphers encipher and decipher multiple bits at once, rather than one bit at a time. For this reason, software implementations of block ciphers run faster than software implementations of stream ciphers. Errors in transmitting one block generally do not affect other blocks, but as each block is enciphered independently, using the same key, identical plaintext blocks produce identical ciphertext blocks. This allows the analyst to search for data by determining what the encipherment of a specific plaintext block is. For example, if the word INCOME is enciphered as one block, all occurrences of the word produce the same ciphertext.To prevent this type of attack, some information related to the block's position is inserted into the plaintext block before it is enciphered. The information can be bits from the preceding ciphertext block [343] or a sequence number [561]. The disadvantage is that the effective block size is reduced, because fewer message bits are present in a block.Cipher block chaining does not require the extra information to occupy bit spaces, so every bit in the block is part of the message. Before a plaintext block is enciphered, that block is exclusive-or'ed with the preceding ciphertext block. In addition to the key, this technique requires an initialization vector with which to exclusive-or the initial plaintext block. Taking Ekto be the encipherment algorithm with key k, and I to be the initialization vector, the cipher block chaining technique isc 0 = Ek(m⊕I)c i = Ek(mi⊕ci–1) for i > 011.2.2.1 Multiple EncryptionOther approaches involve multiple encryption. Using two keys k and k' toencipher a message as c = Ek' (Ek(m)) looks attractive because it has aneffective key length of 2n, whereas the keys to E are of length n. However, Merkle and Hellman [700] have shown that this encryption technique can be broken using 2n+1encryptions, rather than the expected 22n(see Exercise 3).Using three encipherments improves the strength of the cipher. There are several ways to do this. Tuchman [1006] suggested using two keys k and k':c = Ek (Dk'(Ek(m)))This mode, called Encrypt-Decrypt-Encrypt (EDE) mode, collapses to a single encipherment when k = k'. The DES in EDE mode is widely used in the financial community and is a standard (ANSI X9.17 and ISO 8732). It is not vulnerable to the attack outlined earlier. However, it is vulnerable to a chosen plaintext and a known plaintext attack. If b is the block size in bits, and n is the key length, the chosen plaintext attacktakes O(2n) time, O(2n) space, and requires 2n chosen plaintexts. The known plaintext attack requires p known plaintexts, and takes O(2n+b/p) time and O(p) memory.A second version of triple encipherment is the triple encryption mode [700]. In this mode, three keys are used in a chain of encipherments.c = Ek (Ek'(Ek''(m)))The best attack against this scheme is similar to the attack on double encipherment, but requires O(22n) time and O(2n) memory. If the key length is 56 bits, this attack is computationally infeasible.11.3 Networks and CryptographyBefore we discuss Internet protocols, a review of the relevant properties of networks is in order. The ISO/OSI model [990] provides an abstract representation of networks suitable for our purposes. Recall that the ISO/OSI model is composed of a series of layers (see Figure 11-2). Each host, conceptually, has a principal at each layer that communicates with a peer on other hosts. These principals communicate with principals at the same layer on other hosts. Layer 1, 2, and 3 principals interact only with similar principals at neighboring (directly connected) hosts. Principals at layers 4, 5, 6, and 7 interact only with similar principals at the other end of the communication. (For convenience, "host" refers to the appropriate principal in the following discussion.)Figure 11-2. The ISO/OSI model. The dashed arrows indicate peer-to-peer communication. For example, the transport layers are communicating with each other. The solid arrows indicate the actual flow of bits. For example, the transport layer invokes network layer routines on the local host, which invoke data link layer routines, which put the bits onto the network. The physical layer passes the bits to the next "hop," or host, on the path. When the message reaches the destination, it is passed up to the appropriatelevel.Each host in the network is connected to some set of other hosts. They exchange messages with those hosts. If host nob wants to send a message to host windsor, nob determines which of its immediate neighbors is closest to windsor (using an appropriate routing protocol) and forwards the message to it. That host, baton, determines which of its neighbors is closest to windsor and forwards the message to it. This process continues until a host, sunapee, receives the message and determines that windsor is an immediate neighbor. The message is forwarded to windsor, its endpoint.Definition 11–5. Let hosts C0, …, Cnbe such that Ciand Ci+1are directlyconnected, for 0 i < n. A communications protocol that has C0 and Cnasits endpoints is called an end-to-end protocol. A communications protocolthat has Cj and Cj+1as its endpoints is called a link protocol.The difference between an end-to-end protocol and a link protocol is that the intermediate hosts play no part in an end-to-end protocol other than forwarding messages. On the other hand, a link protocol describes how each pair of intermediate hosts processes each message.The protocols involved can be cryptographic protocols. If the cryptographic processing is done only at the source and at the destination, the protocol is an end-to-end protocol. If cryptographic processing occurs at each host along the path from source to destination, the protocolis a link protocol. When encryption is used with either protocol, we use the terms end-to-end encryption and link encryption, respectively.In link encryption, each host shares a cryptographic key with its neighbor. (If public key cryptography is used, each host has its neighbor's public key. Link encryption based on public keys is rare.) The keys may be set on a per-host basis or a per-host-pair basis. Consider a network with four hosts called windsor, stripe, facer, and seaview. Each host is directly connected to the other three. With keys distributed on a per-host basis, each host has its own key, making four keys in all. Each host has the keys for the other three neighbors, as well as its own. All hosts use the same key to communicate with windsor. With keys distributed on a per-host-pair basis, each host has one key per possible connection, making six keys in all. Unlike the per-host situation, in the per-host-pair case, each host uses a different key to communicate with windsor. The message is deciphered at each intermediate host, reenciphered for the next hop, and forwarded. Attackers monitoring the network medium will not be able to read the messages, but attackers at the intermediate hosts will be able to do so.In end-to-end encryption, each host shares a cryptographic key with each destination. (Again, if the encryption is based on public key cryptography, each host has—or can obtain—the public key of each destination.) As with link encryption, the keys may be selected on a per-host or per-host-pair basis. The sending host enciphers the message and forwards it to the first intermediate host. The intermediate host forwards it to the next host, and the process continues until the message reaches its destination. The destination host then deciphers it. The message is enciphered throughout its journey. Neither attackers monitoring the network nor attackers on the intermediate hosts can read the message. However, attackers can read the routing information used to forward the message.These differences affect a form of cryptanalysis known as traffic analysis.A cryptanalyst can sometimes deduce information not from the content ofthe message but from the sender and recipient. For example, during the Allied invasion of Normandy in World War II, the Germans deduced which vessels were the command ships by observing which ships were sending and receiving the most signals. The content of the signals was not relevant; their source and destination were. Similar deductions can reveal information in the electronic world.第十一章密码技术11.1问题在没有考虑加密所要运行的环境时,加密的使用可能不能提供用户所期待的安全。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
7.1 INTRODUCTIONAfter lathes, milling machines are the most widely used for manufacturing applications. In milling, the workpiece is fed into a rotating milling cutter, which is a multi-point tool as shown in Fig. 7.1, unlike a lathe, which uses a single point cutting tool. The tool used in milling is called the milling cutter.Fig. 7.1Schematic diagram of a milling operationThe milling process is characterised by:(i)Interrupted cutting Each of the cutting edges removes materialfor only a part of the rotation of the milling cutter. As a result, the cutting edge has time to cool before it again removes material.Thus the milling operation is much more cooler compared to the turning operation. This allows for a much larger material rates.(ii)Small size of chips Though the size of the chips is small, in view of the multiple cutting edges in contact a large amount of material is removed and as a result the component is generally completed ina single pass unlike the turning process which requires a largenumber of cuts for finishing.(iii)Variation in chip thickness This contributes to the non-steady state cyclic conditions of varying cutting forces during the contact of the cutting edge with the chip thickness varying from zero to maximum size or vice versa. This cyclic variation of the force can excite any of the natural frequencies of the machine tool system and is harmful to the tool life and surface finish generatedA milling machine is one of the most versatile machine tools. It is adaptable for quantity production as well as in job shops and tool rooms. The versatility of milling is because of the large variety of accessories and tools available with milling machines. The typical tolerance expected from the process is about ±0.050 mm.7.2 TYPES OF MILLING MACHINESTo satisfy various requirements milling machines come in a number of sizes and varieties. In view of the large material removal ratesmilling machines come with a very rigid spindle and large power. The varieties of milling machines available are:(i) Knee and Column type(a) horizontal(b) vertical(c) universal(d) turret typeThese are the general purpose milling machines, which have a high degree of flexibility and are employed for all types of works including batch manufacturing. A large variety of attachments to improve the flexibility are available for this class of milling machines.(ii) Production (Bed) type(a) simplex(b) duplex(c) triplexThese machines are generally meant for regular production involving large batch sizes. The flexibility is relatively less in these machines which is suitable for productivity enhancement.(iii) Plano millersThese machines are used only for very large workpieces involving table travels in meters.(iv) Special type(a) Rotary table(b) Drum type(c) Copy milling (Die sinking machines)(d) Key way milling machines(e) Spline shaft milling machinesThese machines provide special facilities to suit specific applications that are not catered to by the other classes of milling machines.7.2.1 Knee and Column Milling MachinesThe knee(升降台) and column type is the most commonly used machine in view of its flexibility and easier setup. A typical machine construction is shown in Fig. 7.2 for the horizontal axis. The knee houses the feed mechanism and mounts the saddle and table. The table basically has the T-slots running along the X-axis for the purpose of work holding. The table moves along the X-axis on the saddle while the saddle moves along the Y-axis on the guide ways provided on the knee.The feed is provided either manually with a hand wheel or connected for automatic by the lead screw, which in turn is coupled to the main spindle drive. The knee can move up and down (Z-axis) on a dovetail provided on the column.Fig. 7.2 Horizontal knee and column type milling machineThe massive column at the back of the machine houses all the power train including the motor and the spindle gearbox. The power for feeding the table lead screw is taken from the main motor through a separate feed gearbox. Sometimes a separate feed motor is provided for the feed gearbox as well.While the longitudinal and traverse motions are provided with automatic motion, the raising of the knee is generally made manually.The spindle is located at the top end of the column. The arbour used to mount the milling cutters is mounted in the spindle and is provided with a support on the other end to take care of the heavy cutting forces by means of an overarm with bearing. As shown in Fig.7.2 the overarm extends from the column with a rigid design. The spindle nose has the standard Morse taper of the suitable sizedepending upon the machine size.The milling cutters are mounted on the arbour at any desired position, the rest of the length being filled by standard hardened collars of varying widths to fix the position of the cutter. The arbour is clamped in the spindle with the help of a draw bar and then fixed with nuts.Milling machines are generally specified on the following basis:(i) Size of the table, which specifies the actual working area on the table and relates to the maximum size of the workpiece that can be accommodated.(ii) Amount of table travel, which gives the maximum axis movement that is possible.(iii) Horse power of the spindle, which actually specifies the power of the spindle motor used. Smaller machines may come with 1 to 3 hp while the production machines may go from 10 to 50 hp.Another type of knee and column milling machine is the vertical axis type. Its construction is very similar to the horizontal axis type, except for the spindle type and location.The vertical axis milling machine is relatively more flexible (Fig. 7.4) and suitable for machining complex cavities such as die cavities in tool rooms. The vertical head is provided with a swiveling facility in horizontal direction whereby the cutter axis can be swivelled. This isuseful for tool rooms where more complex milling operations are carried out.The spindle is located in the vertical direction and is suitable for using the shank mounted milling cutters such as end mills, In view of the location of the tool, the setting up of the workpiece and observing the machining operation is more convenient.Fig, 7.3 Vertical knee and column type milling machineFig.7.4 Some of the milling operations normally carried out on vertical axis machinesThe universal machine has the table which can be swivelled in a horizontal plane at about 45o to either the left or right. This makes the universal machine suitable for milling spur and helical gears as well as worm gears and cams.7.2.2 Bed Type Milling MachineIn production milling machines it is desirable to increase the metal removal rates. If it is done on conventional machines by increasingthe depth of cut, there is possibility of chatter. Hence another varietyof milling machines named as bed type machines are used which are made more rugged and are capable of removing more material. The ruggedness is obtained as a consequence of the reduction in versatility.The table in the case of bed type machines is directly mounted on the bed and is provided with only longitudinal motion.The spindle moves along with the column to provide the cutting action. Simplex machines (Fig. 7.5) are the ones with only one spindle head while duplex machines have two spindles (Fig. 7.6). The two spindles are located on either side of a heavy workpiece and remove material from both sides simultaneously.Fig. 7.5 Simplex bed type milling machineFig. 7.6 Duplex bed type milling machine7.3 MILLING CUTTERSThere are a large variety of milling cutters available to suit specific requirements. The versatility of the milling machine is contributed toa great extent by the variety of milling cutters that are available.7.3.1 Types of Milling CuttersMilling cutters are classified into various types based on a variety of methods.(i) Based on construction:(a) Solid(b) Inserted tooth typeBased on mounting:(a) Arbor mounted(b) Shank mounted(c) Nose mountedBase on rotation:(a) Right hand rotation (counter clockwise)(b) Left hand rotation (clockwise)Based on helix:(a) Right hand helix(b) Left hand helixMilling cutters are generally made of high speed steel or cemented carbides. The cemented carbide cutters can be of a brazed tip variety or with indexable tips. The indexable variety is more common since it is normally less expensive to replace the worn out cutting edges than to regrind them.Plain milling cutters These are also called slab milling cutters and are basically cylindrical with the cutting teeth on the periphery as shown in Fig. 7.7. These are generally used for machining flat surfaces.Fig. 7.7 Arbor mounted milling cutters for general purposeLight duty slab milling cutters generally have a face width, which is small of the order of 25 mm. They generally have straight teeth and large number of teeth.Heavy duty slab milling cutters come with a smaller number of teeth to allow for more chip space. This allows taking deeper cuts and consequently high material removal rates.Helical milling cutters have a very small number of teeth but a large helix angle. This type of cutter cuts with a shearing action, which can produce a very fine finish. The large helix angle allows the cutter to absorb most of the end load and therefore the cutter enters and leaves the workpiece very smoothly.Side and face milling cutters These have the cutting edges not only onthe face like the slab milling cutters, but also on both the sides. As aresult, these cutters become more versatile since they can be used for side milling as well as for slot milling.Staggered tooth side milling cutters are a variation where the teeth are arranged in an alternate helix pattern. This type is generally used for milling deep slots, since the staggering of teeth provides for greater chip space.Another variation of the side and face cutter is the half side milling cutter, which has cutting edges only on one side. This arrangement provides a positive rake angle and is useful for machining on only one side. These have a much smoother cutting action and a long tool life. The power consumed is also less for these cutters.Fig. 7.8Special forms of arbor mounted milling cuttersSlitting saws The other common form of milling cutters in the arbor mounted category is the slitting saw. This is very similar to a saw blade inappearance as well as function. Most of these have teeth around the circumference while some have side teeth as well. The thickness of these cutters is generally very small and is used for cutting off operations or for deep slots.Special form cutters In addition to the general type of milling cutters described above, there are a large number of special form milling cutters available which are used for machining specific profiles.Angular milling cutters are made in single or double angle cutters for milling any angle such as 30, 45 or 60o Form relieved cutters are made of various shapes such as circular, corner rounding, convex or concave shapes.T-slot milling cutters are used for milling T-slots such as those in the milling machine table. The central slot is to be milled first using an end mill before using the T-slot milling cutter. Woodruff key seat milling cutters are used for milling as the name suggests, woodruff key seats Some other special form cutters are dovetail milling cutters and gear milling cutters.End mills These are shank mounted as shown in Fig. 7.9 and are generally used in vertical axis milling machines. They are used for milling slots, key ways and pockets where other type of milling cutters cannot be used. A depth of cut of almost half the diameter can be taken with the end mills.The end mills have the cutting edge running through the length of the cutting portion as well as on the face radially up to a certain length. The helix angle of the cutting edge promotes smooth and efficient cutting even at high cutting speeds and feed rates. High cutting speeds(转速?) are generally recommended for this type of milling cutters.Fig. 7.9 Shank mounted milling cutters and various types of end mills There are a large variety of end mills. One of the distinctions is based on the method of holding, i.e., the end mill shank can be straight or tapered. The straight shank is used on end mills of small size and held in the milling machine spindle with the help of a suitable collet. The tapered shank can be directly mounted in the spindle with the help of the selfholding taper. If the taper is small compared to the spindle taper, then an adopter accommodating both the tapers is used.The end teeth of the end mills may be terminated at a distance from the cutter center or may proceed till the center (Fig. 7.9 f). Those with the cutting edge up to the center are called slot drills or end cutting end mills since they have the ability to cut into the solid material (Fig. 7.9 g). The other type of end mills which have a larger number of teeth cannot cut into solid material and hence require a pilot hole drilled before a pocket is machined.The cutting edge along the side of an end mill is generally straight and sometimes can be tapered by grinding on a tool and cutter grinder such that the draft required for mould and die cavities can be automatically generated.。
