AES计数器模式C实现
AES加密算法c语言实现代码
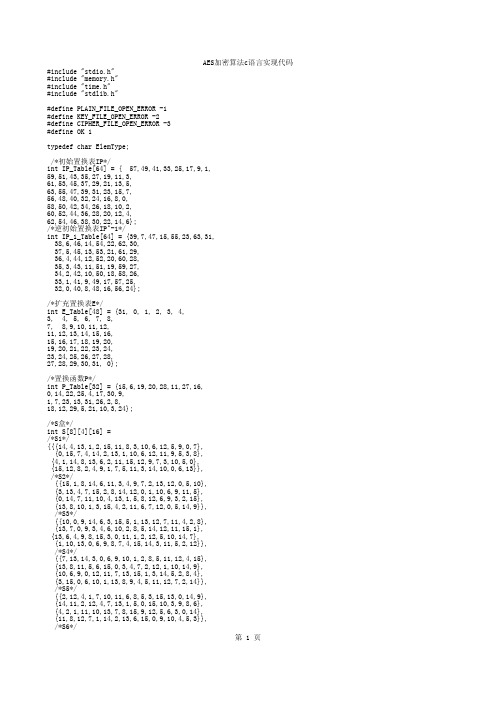
/*密钥置换1*/ int DES_PC1_Transform(ElemType key[64], ElemType tempbts[56]){ int cnt; for(cnt = 0; cnt < 56; cnt++){
AES加密算法c语言实现代码
/*将二进制位串转为长度为8的字符串*/ int Bit64ToChar8(ElemType bit[64],ElemType ch[8]){ int cnt; memset(ch,0,8); for(cnt = 0; cnt < 8; cnt++){
BitToByte(bit+(cnt<<3),ch+cnt); } return 0; }
/*扩充置换表E*/ int E_Table[48] = {31, 0, 1, 2, 3, 4, 3, 4, 5, 6, 7, 8, 7, 8,9,10,11,12, 11,12,13,14,15,16, 15,16,17,18,19,20, 19,20,21,22,23,24, 23,24,25,26,27,28, 27,28,29,30,31, 0};
/*对左移次数的规定*/ int MOVE_TIMES[16] = {1,1,2,2,2,2,2,2,1,2,2,2,2,2,2,1};
int ByteToBit(ElemType ch,ElemType bit[8]); int BitToByte(ElemType bit[8],ElemType *ch); int Char8ToBit64(ElemType ch[8],ElemType bit[64]); int Bit64ToChar8(ElemType bit[64],ElemType ch[8]); int DES_MakeSubKeys(ElemType key[64],ElemType subKeys[16][48]); int DES_PC1_Transform(ElemType key[64], ElemType tempbts[56]); int DES_PC2_Transform(ElemType key[56], ElemType tempbts[48]); int DES_ROL(ElemType data[56], int time); int DES_IP_Transform(ElemType data[64]); int DES_IP_1_Transform(ElemType data[64]); int DES_E_Transform(ElemType data[48]); int DES_P_Transform(ElemType data[32]); int DES_SBOX(ElemType data[48]); int DES_XOR(ElemType R[48], ElemType L[48],int count); int DES_Swap(ElemType left[32],ElemType right[32]); int DES_EncryptBlock(ElemType plainBlock[8], ElemType subKeys[16][48], ElemType cipherBlock[8]); int DES_DecryptBlock(ElemType cipherBlock[8], ElemType subKeys[16][48], ElemType plainBlock[8]); int DES_Encrypt(char *plainFile, char *keyStr,char *cipherFile); int DES_Decrypt(char *cipherFile, char *keyStr,char *plainFile);
AES密码学课程设计(C语言实现)
成都信息工程学院课程设计报告AES加密解密软件的实现课程名称:应用密码算法程序设计学生姓名:樊培学生学号:2010121058专业班级:信息对抗技术101任课教师:陈俊2012 年6月7日课程设计成绩评价表目录1、选题背景 (4)2、设计的目标 (4)2.1基本目标: (4)2.2较高目标: (5)3、功能需求分析 (5)4、模块划分 (6)4.1、密钥调度 (6)4.2、加密 (8)4.2.1、字节代替(SubBytes) (8)4.2.2、行移位(ShiftRows) (10)4.2.3、列混合(MixColumn) (11)4.2.4、轮密钥加(AddRoundKey) (13)4.2.5、加密主函数 (14)4.3、解密 (16)4.3.1、逆字节替代(InvSubBytes) (16)4.3.2、逆行移位(InvShiftRows) (17)4.3.3、逆列混合(InvMixCloumns) (17)4.3.4、轮密钥加(AddRoundKey) (18)4.3.5、解密主函数 (18)5.测试报告 (20)5.1主界面 (20)5.2测试键盘输入明文和密钥加密 (20)5.3测试键盘输入密文和密钥加密 (21)5.3测试文件输入明文和密钥加密 (22)5.4测试文件输入密文和密钥加密 (22)5.5软件说明 (23)6.课程设计报告总结 (23)7.参考文献 (24)1、选题背景高级加密标准(Advanced Encryption Standard,AES),在密码学中又称Rijndael加密法,是美国联邦政府采用的一种区块加密标准。
这个标准用来替代原先的DES,已经被多方分析且广为全世界所使用。
经过五年的甄选流程,高级加密标准由美国国家标准与技术研究院(NIST)于2001年11月26日发布于FIPS PUB 197,并在2002年5月26日成为有效的标准。
2006年,高级加密标准已然成为对称密钥加密中最流行的算法之一。
aes加密算法的输入c语言实例
aes加密算法的输入c语言实例1.引言1.1 概述概述部分应该对文章的主题进行一个简要介绍,提供一些背景信息和基本概念,以帮助读者了解接下来要讨论的内容。
下面是一个示例:在当今信息安全领域,数据的加密和保护是至关重要的。
随着互联网的发展和应用的广泛,如何确保用户的机密信息在传输和存储过程中不被未经授权的人访问和窃取,成为了一个极具挑战性的问题。
为了应对这个问题,许多加密算法被开发和广泛应用,其中AES(Advanced Encryption Standard,高级加密标准)算法就是其中之一。
AES算法是一种对称加密算法,它可以对数据进行高强度的加密和解密,以保护数据的机密性。
它是目前最常用和最可靠的加密算法之一,被广泛应用于各种安全通信和数据存储场景。
AES算法采用了分组加密和替代-置换网络结构,通过多轮的迭代运算和密钥扩展过程,将输入的明文数据转换为密文数据。
解密过程与加密过程相反,通过逆向的操作将密文数据恢复为明文数据。
本文的主要目的是介绍如何使用C语言来实现AES加密算法。
在接下来的内容中,我们将首先简要介绍AES算法的基本原理和步骤,然后详细讲解如何使用C语言来实现这些步骤。
通过本文的学习,读者将可以了解AES算法的基本运作原理,并掌握使用C语言编写AES加密算法的技巧。
在下一节中,我们将开始介绍AES加密算法的基本原理和步骤。
1.2 文章结构文章结构部分将对本文的组织结构和各章节内容进行介绍。
本文分为以下几个部分:1. 引言:本部分包括概述、文章结构和目的三个小节。
在概述中,将简要介绍AES加密算法和其在信息安全领域的重要性。
文章结构部分将重点介绍本文的整体组织架构和各章节内容的概括。
目的部分将明确本文的主要目标和意义。
2. 正文:本部分包括AES加密算法简介和C语言实现AES算法的基本步骤两个小节。
在AES加密算法简介中,将对AES算法的基本原理进行阐述,包括密钥长度、分组长度、轮数等方面的内容。
AES算法C语言讲解与实现

AES算法C语言讲解与实现AES(Advanced Encryption Standard)是一种对称加密算法,被广泛应用于各种应用中,如保护通信、数据安全等。
AES算法采用分组密码的方式,将明文数据分成若干个大小相等的分组,然后对每个分组进行加密操作。
1. 密钥扩展(Key Expansion):AES算法中使用的密钥长度分为128位、192位和256位三种,密钥长度不同,密钥扩展的轮数也不同。
根据密钥长度,需要扩展成多少个轮密钥。
扩展过程中需要进行字节代换、循环左移、模2乘法等操作。
2. 子密钥生成(Subkey Generation):根据密钥扩展的结果,生成每一轮需要使用的子密钥。
3. 字节替换(SubBytes):将每个字节替换为S盒中对应的值。
S盒是一个固定的预先计算好的查找表。
4. 行移位(ShiftRows):对矩阵的行进行循环左移,左移的位数根据行数而定。
5. 列混合(MixColumns):将每列的四个字节进行混合。
混合操作包括乘法和异或运算。
6. 轮密钥加(AddRoundKey):将每一轮得到的结果与轮密钥进行异或运算。
以上就是AES算法的六个步骤的实现过程,下面我们来具体讲解一下。
首先,我们需要定义一些辅助函数,如字节代换函数、循环左移函数等。
```cuint8_t substitution(uint8_t byte) return sBox[byte];void shiftRows(uint8_t *state)uint8_t temp;//第二行循环左移1位temp = state[1];state[1] = state[5];state[5] = state[9];state[9] = state[13];state[13] = temp;//第三行循环左移2位temp = state[2];state[2] = state[10];state[10] = temp;temp = state[6];state[6] = state[14];state[14] = temp;//第四行循环左移3位temp = state[15];state[15] = state[11];state[11] = state[7];state[7] = state[3];state[3] = temp;void mixColumns(uint8_t *state)int i;uint8_t temp[4];for(i = 0; i < 4; i++)temp[0] = xTime(state[i * 4]) ^ xTime(state[i * 4 + 1]) ^ state[i * 4 + 1] ^state[i * 4 + 2] ^ state[i * 4 + 3];temp[1] = state[i * 4] ^ xTime(state[i * 4 + 1]) ^xTime(state[i * 4 + 2]) ^state[i * 4 + 2] ^ state[i * 4 + 3];temp[2] = state[i * 4] ^ state[i * 4 + 1] ^ xTime(state[i * 4 + 2]) ^xTime(state[i * 4 + 3]) ^ state[i * 4 + 3];temp[3] = xTime(state[i * 4]) ^ state[i * 4] ^ state[i * 4 + 1] ^state[i * 4 + 2] ^ xTime(state[i * 4 + 3]);state[i * 4] = temp[0];state[i * 4 + 1] = temp[1];state[i * 4 + 2] = temp[2];state[i * 4 + 3] = temp[3];}```接下来,我们实现密钥扩展和子密钥生成的过程。
AES加密算法(C++实现,附源码)
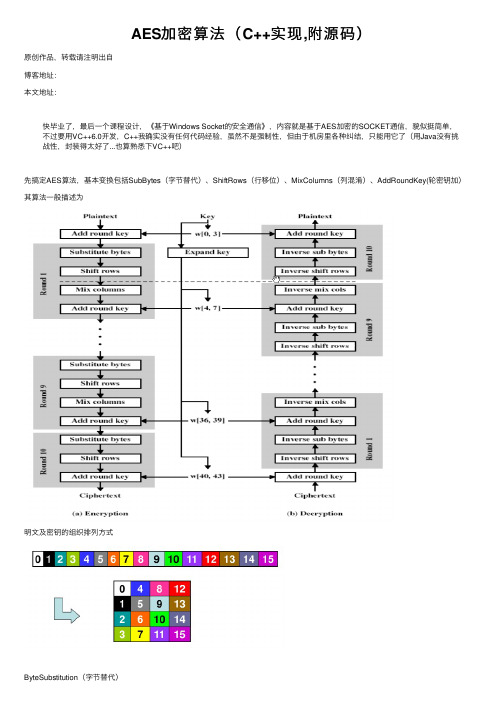
AES加密算法(C++实现,附源码)原创作品,转载请注明出⾃博客地址:本⽂地址:快毕业了,最后⼀个课程设计,《基于Windows Socket的安全通信》,内容就是基于AES加密的SOCKET通信,貌似挺简单,不过要⽤VC++6.0开发,C++我确实没有任何代码经验,虽然不是强制性,但由于机房⾥各种纠结,只能⽤它了(⽤Java没有挑战性,封装得太好了...也算熟悉下VC++吧)先搞定AES算法,基本变换包括SubBytes(字节替代)、ShiftRows(⾏移位)、MixColumns(列混淆)、AddRoundKey(轮密钥加)其算法⼀般描述为明⽂及密钥的组织排列⽅式ByteSubstitution(字节替代)⾮线性的字节替代,单独处理每个字节:求该字节在有限域GF(28)上的乘法逆,"0"被映射为⾃⾝,即对于α∈GF(28),求β∈GF(28),使得α·β=β·α=1mod(x 8+x 4+x 2+x+1)。
对上⼀步求得的乘法逆作仿射变换y i =x i + x (i+4)mod8 + x (i+6)mod8 + x (i+7)mod8 + c i(其中c i 是6310即011000112的第i位),⽤矩阵表⽰为本来打算把求乘法逆和仿射变换算法敲上去,最后还是放弃了...直接打置换表12345678910111213141516171819unsigned char sBox[] ={ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, /*0*/0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, /*1*/0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, /*2*/ 0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, /*3*/ 0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, /*4*/0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, /*5*/0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, /*6*/0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, /*7*/0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, /*8*/ 0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, /*9*/ 0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, /*a*/0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, /*b*/0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, /*c*/0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, /*d*/ 0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, /*e*/ 0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 /*f*/};下⾯是逆置换表,解密时使⽤12345678*********unsigned char invsBox[256] ={ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb, /*0*/ 0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb, /*1*/ 0x54,0x7b,0x94,0x32,0xa6,0xc2,0x23,0x3d,0xee,0x4c,0x95,0x0b,0x42,0xfa,0xc3,0x4e, /*2*/0x08,0x2e,0xa1,0x66,0x28,0xd9,0x24,0xb2,0x76,0x5b,0xa2,0x49,0x6d,0x8b,0xd1,0x25, /*3*/0x72,0xf8,0xf6,0x64,0x86,0x68,0x98,0x16,0xd4,0xa4,0x5c,0xcc,0x5d,0x65,0xb6,0x92, /*4*/0x6c,0x70,0x48,0x50,0xfd,0xed,0xb9,0xda,0x5e,0x15,0x46,0x57,0xa7,0x8d,0x9d,0x84, /*5*/ 0x90,0xd8,0xab,0x00,0x8c,0xbc,0xd3,0x0a,0xf7,0xe4,0x58,0x05,0xb8,0xb3,0x45,0x06, /*6*/ 0xd0,0x2c,0x1e,0x8f,0xca,0x3f,0x0f,0x02,0xc1,0xaf,0xbd,0x03,0x01,0x13,0x8a,0x6b, /*7*/ 0x3a,0x91,0x11,0x41,0x4f,0x67,0xdc,0xea,0x97,0xf2,0xcf,0xce,0xf0,0xb4,0xe6,0x73, /*8*/0x96,0xac,0x74,0x22,0xe7,0xad,0x35,0x85,0xe2,0xf9,0x37,0xe8,0x1c,0x75,0xdf,0x6e, /*9*/0x47,0xf1,0x1a,0x71,0x1d,0x29,0xc5,0x89,0x6f,0xb7,0x62,0x0e,0xaa,0x18,0xbe,0x1b, /*a*/ 0xfc,0x56,0x3e,0x4b,0xc6,0xd2,0x79,0x20,0x9a,0xdb,0xc0,0xfe,0x78,0xcd,0x5a,0xf4, /*b*/14 15 16 17 18 19 0x1f,0xdd,0xa8,0x33,0x88,0x07,0xc7,0x31,0xb1,0x12,0x10,0x59,0x27,0x80,0xec,0x5f, /*c*/ 0x60,0x51,0x7f,0xa9,0x19,0xb5,0x4a,0x0d,0x2d,0xe5,0x7a,0x9f,0x93,0xc9,0x9c,0xef, /*d*/ 0xa0,0xe0,0x3b,0x4d,0xae,0x2a,0xf5,0xb0,0xc8,0xeb,0xbb,0x3c,0x83,0x53,0x99,0x61, /*e*/ 0x17,0x2b,0x04,0x7e,0xba,0x77,0xd6,0x26,0xe1,0x69,0x14,0x63,0x55,0x21,0x0c,0x7d /*f*/ };这⾥遇到问题了,本来⽤纯c初始化数组很正常,封装成类以后发现不能初始化,不管是声明、构造函数都⽆法初始化,百歌⾕度了⼀通后没有任何答案,⽆奈只能在构造函数中声明⼀个局部变量数组并初始化,然后⽤memcpy,(成员变量名为Sbox/InvSbox,局部变量名sBox/invsBox)12 3 4 5 6 7 8 9 10 11void AES::SubBytes(unsigned char state[][4]) {int r,c;for(r=0; r<4; r++){for(c=0; c<4; c++){state[r][c] = Sbox[state[r][c]];}}}ShiftRows(⾏移位变换)⾏移位变换完成基于⾏的循环位移操作,变换⽅法:即⾏移位变换作⽤于⾏上,第0⾏不变,第1⾏循环左移1个字节,第2⾏循环左移2个字节,第3⾏循环左移3个字节。
AES加密算法实现C
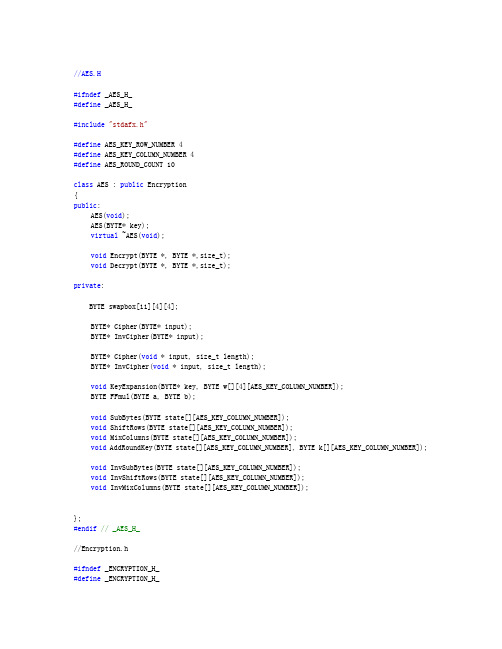
AES加密算法实现C/S模式的通信设计任务:掌握AES的加密算法原理;掌握用socket编程实现C/S模式的加密通信。
设计内容:Socket编程实现客户端和服务器模式的通信;编程实现AES加解密的过程;将AES应用在C/S的通信中,对信息进行加密传输。
设计原理:1、socket编程实现C/S模式的通信,当用户在客户端发出请求时,会在服务器端做出相应的反应,并给出应答信息返回给客户端。
2、AES――对称密码新标准:高级加密标准。
对称密码体制的发展趋势将以分组密码为重点。
分组密码算法通常由密钥扩展算法和加密(解密)算法两部分组成。
密钥扩展算法将b字节用户主密钥扩展成r个子密钥。
加密算法由一个密码学上的弱函数f与r个子密钥迭代r次组成。
混乱和密钥扩散是分组密码算法设计的基本原则。
抵御已知明文的差分和线性攻击,可变长密钥和分组是该体制的设计要点。
AES是美国国家标准技术研究所NIST旨在取代DES的21世纪的加密标准。
AES的基本要求是,采用对称分组密码体制,密钥长度的最少支持为128、192、256,分组长度128位,算法应易于各种硬件和软件实现。
1998年NIST开始AES第一轮分析、测试和征集,共产生了15个候选算法。
1999年3月完成了第二轮AES 2的分析、测试。
最终将Rijndael数据加密算法作为高级加密标准AES。
在应用方面,尽管DES在安全上是脆弱的,但由于快速DES芯片的大量生产,使得DES仍能暂时继续使用,为提高安全强度,通常使用独立密钥的三级DES。
但是DES迟早要被AES代替。
3、AES的主要算法原理:AES 算法是基于置换和代替的。
置换是数据的重新排列,而代替是用一个单元数据替换另一个。
AES 使用了几种不同的技术来实现置换和替换。
为了阐明这些技术,让我们用 Figure 1 所示的数据讨论一个具体的 AES 加密例子。
下面是你要加密的128位值以及它们对应的索引数组:00 11 22 33 44 55 66 77 88 99 aa bb cc dd ee ff0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15192位密钥的值是:00 01 02 03 04 05 06 07 08 09 0a 0b 0c 0d 0e 0f 10 11 12 13 14 15 16 170 1 2 3 4 5 6 7 8 9 10 1112 13 14 15 16 17 18 19 20 21 22 23Figure 2 S-盒( Sbox )当 AES 的构造函数(constructor)被调用时,用于加密方法的两个表被初始化。
AES算法C语言讲解与实现
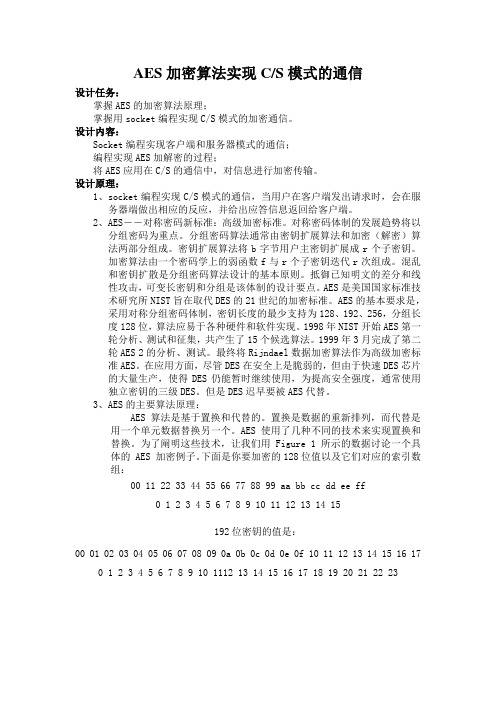
字节替换Void AES::SubBytes(unsigned char state[][4]) {Int r,c;for(r=0; r<4; r++){for(c=0; c<4; c++){state[r][c] = Sbox[state[r][c]];}}}行移位Void AES::ShiftRows(unsigned char state[][4]) {unsigned char t[4];Int r,c;for(r=1; r<4; r++){for(c=0; c<4; c++){t[c] = state[r][(c+r)%4];}for(c=0; c<4; c++){state[r][c] = t[c];}}}列混淆Void AES::MixColumns(unsigned char state[][4]) {unsigned char t[4];Int r,c;for(c=0; c< 4; c++){for(r=0; r<4; r++){t[r] = state[r][c];}for(r=0; r<4; r++){state[r][c] = FFmul(0x02, t[r])^ FFmul(0x03, t[(r+1)%4])^ FFmul(0x01, t[(r+2)%4])^ FFmul(0x01, t[(r+3)%4]);}}}unsigned char AES::FFmul(unsigned char a, unsigned char b) {unsigned char bw[4];unsigned char res=0;Int i;bw[0] = b;for(i=1; i<4; i++){bw[i] = bw[i-1]<<1;if(bw[i-1]&0x80){bw[i]^=0x1b;}}for(i=0; i<4; i++){if((a>>i)&0x01){res ^= bw[i];}}Return res;}轮密钥加算法Void AES::AddRoundKey(unsigned char state[][4], unsigned char k[][4]) {Int r,c;for(c=0; c<4; c++){for(r=0; r<4; r++){state[r][c] ^= k[r][c];}}}密钥扩展算法Void AES::KeyExpansion(unsigned char* key, unsigned char w[][4][4]) {Int i,j,r,c;unsigned char rc[] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36};for(r=0; r<4; r++){for(c=0; c<4; c++){w[0][r][c] = key[r+c*4];}}for(i=1; i<=10; i++){for(j=0; j<4; j++){unsigned char t[4];for(r=0; r<4; r++){t[r] = j ? w[i][r][j-1] : w[i-1][r][3];}if(j == 0){unsigned char temp = t[0];for(r=0; r<3; r++){t[r] = Sbox[t[(r+1)%4]];}t[3] = Sbox[temp];t[0] ^= rc[i-1];}for(r=0; r<4; r++){w[i][r][j] = w[i-1][r][j] ^ t[r]; }}}}解密过程(只有逆字节替换,逆行移位,逆列混淆)Void AES::InvSubBytes(unsigned char state[][4]) {Int r,c;for(r=0; r<4; r++){for(c=0; c<4; c++){state[r][c] = InvSbox[state[r][c]];}}}Void AES::InvShiftRows(unsigned char state[][4]) {unsigned char t[4];Int r,c;for(r=1; r<4; r++){for(c=0; c<4; c++){t[c] = state[r][(c-r+4)%4];}for(c=0; c<4; c++){state[r][c] = t[c];}}}Void AES::InvMixColumns(unsigned char state[][4]) {unsigned char t[4];Int r,c;for(c=0; c< 4; c++){for(r=0; r<4; r++){t[r] = state[r][c];}for(r=0; r<4; r++){state[r][c] = FFmul(0x0e, t[r])^ FFmul(0x0b, t[(r+1)%4])^ FFmul(0x0d, t[(r+2)%4])^ FFmul(0x09, t[(r+3)%4]);}}}整体加密过程unsigned char* AES::Cipher(unsigned char* input){unsigned char state[4][4];int i,r,c;for(r=0; r<4; r++){for(c=0; c<4 ;c++){state[r][c] = input[c*4+r];}}AddRoundKey(state,w[0]);for(i=1; i<=10; i++){SubBytes(state);ShiftRows(state);if(i!=10)MixColumns(state);AddRoundKey(state,w[i]);}for(r=0; r<4; r++){for(c=0; c<4 ;c++){input[c*4+r] = state[r][c];}}return input;}整体解密过程unsigned char* AES::InvCipher(unsigned char* input) {unsigned char state[4][4];Int i,r,c;for(r=0; r<4; r++){for(c=0; c<4 ;c++){state[r][c] = input[c*4+r];}}AddRoundKey(state, w[10]);for(i=9; i>=0; i--){InvShiftRows(state);InvSubBytes(state);AddRoundKey(state, w[i]); if(i)InvMixColumns(state); }for(r=0; r<4; r++){for(c=0; c<4 ;c++){input[c*4+r] = state[r][c]; }}Return input;}。
AES加密C语言实现代码
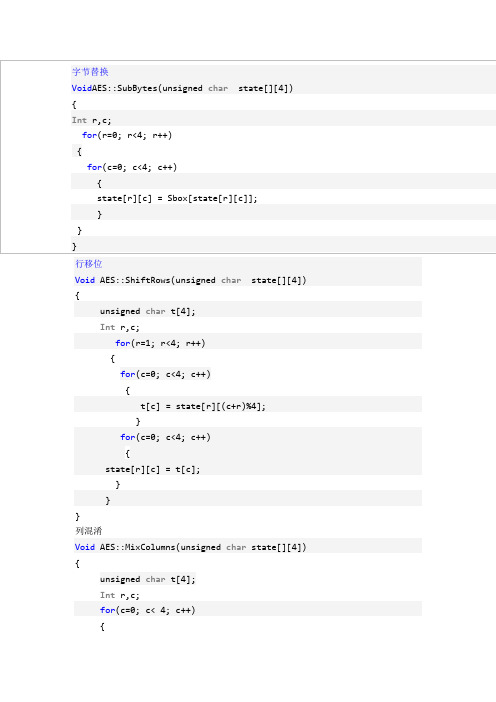
#define BPOLY 0x1b //!< Lower 8 bits of (x^8+x^4+x^3+x+1), ie. (x^4+x^3+x+1).#define BLOCKSIZE 16 //!< Block size in number of bytes.#define KEY_COUNT 3#if KEY_COUNT == 1#define KEYBITS 128 //!< Use AES128.#elif KEY_COUNT == 2#define KEYBITS 192 //!< Use AES196.#elif KEY_COUNT == 3#define KEYBITS 256 //!< Use AES256.#else#error Use 1, 2 or 3 keys!#endif#if KEYBITS == 128#define ROUNDS 10 //!< Number of rounds.#define KEYLENGTH 16 //!< Key length in number of bytes.#elif KEYBITS == 192#define ROUNDS 12 //!< Number of rounds.#define KEYLENGTH 24 //!< // Key length in number of bytes.#elif KEYBITS == 256#define ROUNDS 14 //!< Number of rounds.#define KEYLENGTH 32 //!< Key length in number of bytes.#else#error Key must be 128, 192 or 256 bits!#endif#define EXPANDED_KEY_SIZE (BLOCKSIZE * (ROUNDS+1)) //!< 176, 208 or 240 bytes.unsigned char AES_Key_Table[32] ={0xd0, 0x94, 0x3f, 0x8c, 0x29, 0x76, 0x15, 0xd8,0x20, 0x40, 0xe3, 0x27, 0x45, 0xd8, 0x48, 0xad,0xea, 0x8b, 0x2a, 0x73, 0x16, 0xe9, 0xb0, 0x49,0x45, 0xb3, 0x39, 0x28, 0x0a, 0xc3, 0x28, 0x3c,};unsigned char block1[256]; //!< Workspace 1.unsigned char block2[256]; //!< Worksapce 2.unsigned char tempbuf[256];unsigned char *powTbl; //!< Final location of exponentiation lookup table.unsigned char *logTbl; //!< Final location of logarithm lookup table. unsigned char *sBox; //!< Final location of s-box.unsigned char *sBoxInv; //!< Final location of inverse s-box. unsigned char *expandedKey; //!< Final location of expanded key.void CalcPowLog(unsigned char *powTbl, unsigned char *logTbl) {unsigned char i = 0;unsigned char t = 1;do {// Use 0x03 as root for exponentiation and logarithms.powTbl[i] = t;logTbl[t] = i;i++;// Muliply t by 3 in GF(2^8).t ^= (t << 1) ^ (t & 0x80 ? BPOLY : 0);}while( t != 1 ); // Cyclic properties ensure that i < 255.powTbl[255] = powTbl[0]; // 255 = '-0', 254 = -1, etc.}void CalcSBox( unsigned char * sBox ){unsigned char i, rot;unsigned char temp;unsigned char result;// Fill all entries of sBox[].i = 0;do {//Inverse in GF(2^8).if( i > 0 ){temp = powTbl[ 255 - logTbl[i] ];}else{temp = 0;}// Affine transformation in GF(2).result = temp ^ 0x63; // Start with adding a vector in GF(2).for( rot = 0; rot < 4; rot++ ){// Rotate left.temp = (temp<<1) | (temp>>7);// Add rotated byte in GF(2).result ^= temp;}// Put result in table.sBox[i] = result;} while( ++i != 0 );}void CalcSBoxInv( unsigned char * sBox, unsigned char * sBoxInv ) {unsigned char i = 0;unsigned char j = 0;// Iterate through all elements in sBoxInv using i.do {// Search through sBox using j.do {// Check if current j is the inverse of current i.if( sBox[ j ] == i ){// If so, set sBoxInc and indicate search finished.sBoxInv[ i ] = j;j = 255;}} while( ++j != 0 );} while( ++i != 0 );}void CycleLeft( unsigned char * row ){// Cycle 4 bytes in an array left once.unsigned char temp = row[0];row[0] = row[1];row[1] = row[2];row[2] = row[3];row[3] = temp;}void InvMixColumn( unsigned char * column ){unsigned char r0, r1, r2, r3;r0 = column[1] ^ column[2] ^ column[3];r1 = column[0] ^ column[2] ^ column[3];r2 = column[0] ^ column[1] ^ column[3];r3 = column[0] ^ column[1] ^ column[2];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);r0 ^= column[0] ^ column[1];r1 ^= column[1] ^ column[2];r2 ^= column[2] ^ column[3];r3 ^= column[0] ^ column[3];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);r0 ^= column[0] ^ column[2];r1 ^= column[1] ^ column[3];r2 ^= column[0] ^ column[2];r3 ^= column[1] ^ column[3];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);column[0] ^= column[1] ^ column[2] ^ column[3];r0 ^= column[0];r1 ^= column[0];r2 ^= column[0];r3 ^= column[0];column[0] = r0;column[1] = r1;column[2] = r2;column[3] = r3;}void SubBytes( unsigned char * bytes, unsigned char count ){do {*bytes = sBox[ *bytes ]; // Substitute every byte in state.bytes++;} while( --count );}void InvSubBytesAndXOR( unsigned char * bytes, unsigned char * key, unsigned char count ){do {// *bytes = sBoxInv[ *bytes ] ^ *key; // Inverse substitute every byte in state and add key.*bytes = block2[ *bytes ] ^ *key; // Use block2 directly. Increases speed.bytes++;key++;} while( --count );}void InvShiftRows( unsigned char * state ){unsigned char temp;// Note: State is arranged column by column.// Cycle second row right one time.temp = state[ 1 + 3*4 ];state[ 1 + 3*4 ] = state[ 1 + 2*4 ];state[ 1 + 2*4 ] = state[ 1 + 1*4 ];state[ 1 + 1*4 ] = state[ 1 + 0*4 ];state[ 1 + 0*4 ] = temp;// Cycle third row right two times.temp = state[ 2 + 0*4 ];state[ 2 + 0*4 ] = state[ 2 + 2*4 ];state[ 2 + 2*4 ] = temp;temp = state[ 2 + 1*4 ];state[ 2 + 1*4 ] = state[ 2 + 3*4 ];state[ 2 + 3*4 ] = temp;// Cycle fourth row right three times, ie. left once.temp = state[ 3 + 0*4 ];state[ 3 + 0*4 ] = state[ 3 + 1*4 ];state[ 3 + 1*4 ] = state[ 3 + 2*4 ];state[ 3 + 2*4 ] = state[ 3 + 3*4 ];state[ 3 + 3*4 ] = temp;}void InvMixColumns( unsigned char * state ){InvMixColumn( state + 0*4 );InvMixColumn( state + 1*4 );InvMixColumn( state + 2*4 );InvMixColumn( state + 3*4 );}void XORBytes( unsigned char * bytes1, unsigned char * bytes2, unsigned char count ) {do {*bytes1 ^= *bytes2; // Add in GF(2), ie. XOR.bytes1++;bytes2++;} while( --count );}void CopyBytes( unsigned char * to, unsigned char * from, unsigned char count ) {do {*to = *from;to++;from++;} while( --count );}void KeyExpansion( unsigned char * expandedKey ){unsigned char temp[4];unsigned char i;unsigned char Rcon[4] = { 0x01, 0x00, 0x00, 0x00 }; // Round constant.unsigned char * key = AES_Key_Table;// Copy key to start of expanded key.i = KEYLENGTH;do {*expandedKey = *key;expandedKey++;key++;} while( --i );// Prepare last 4 bytes of key in temp.expandedKey -= 4;temp[0] = *(expandedKey++);temp[1] = *(expandedKey++);temp[2] = *(expandedKey++);temp[3] = *(expandedKey++);// Expand key.i = KEYLENGTH;while( i < BLOCKSIZE*(ROUNDS+1) ){// Are we at the start of a multiple of the key size?if( (i % KEYLENGTH) == 0 ){CycleLeft( temp ); // Cycle left once.SubBytes( temp, 4 ); // Substitute each byte.XORBytes( temp, Rcon, 4 ); // Add constant in GF(2).*Rcon = (*Rcon << 1) ^ (*Rcon & 0x80 ? BPOLY : 0);}// Keysize larger than 24 bytes, ie. larger that 192 bits?#if KEYLENGTH > 24// Are we right past a block size?else if( (i % KEYLENGTH) == BLOCKSIZE ) {SubBytes( temp, 4 ); // Substitute each byte.}#endif// Add bytes in GF(2) one KEYLENGTH away.XORBytes( temp, expandedKey - KEYLENGTH, 4 );// Copy result to current 4 bytes.*(expandedKey++) = temp[ 0 ];*(expandedKey++) = temp[ 1 ];*(expandedKey++) = temp[ 2 ];*(expandedKey++) = temp[ 3 ];i += 4; // Next 4 bytes.}}void InvCipher( unsigned char * block, unsigned char * expandedKey ) {unsigned char round = ROUNDS-1;expandedKey += BLOCKSIZE * ROUNDS;XORBytes( block, expandedKey, 16 );expandedKey -= BLOCKSIZE;do {InvShiftRows( block );InvSubBytesAndXOR( block, expandedKey, 16 );expandedKey -= BLOCKSIZE;InvMixColumns( block );} while( --round );InvShiftRows( block );InvSubBytesAndXOR( block, expandedKey, 16 );}void aesDecInit(void){powTbl = block1;logTbl = block2;CalcPowLog( powTbl, logTbl );sBox = tempbuf;CalcSBox( sBox );expandedKey = block1;KeyExpansion( expandedKey );sBoxInv = block2; // Must be block2.CalcSBoxInv( sBox, sBoxInv );}void aesDecrypt( unsigned char * buffer, unsigned char * chainBlock ) {unsigned char temp[ BLOCKSIZE ];CopyBytes( temp, buffer, BLOCKSIZE );InvCipher( buffer, expandedKey );XORBytes( buffer, chainBlock, BLOCKSIZE );CopyBytes( chainBlock, temp, BLOCKSIZE );}unsigned char Multiply( unsigned char num, unsigned char factor ){unsigned char mask = 1;unsigned char result = 0;while( mask != 0 ){// Check bit of factor given by mask.if( mask & factor ){// Add current multiple of num in GF(2).result ^= num;}// Shift mask to indicate next bit.mask <<= 1;// Double num.num = (num << 1) ^ (num & 0x80 ? BPOLY : 0);}return result;}unsigned char DotProduct( unsigned char * vector1, unsigned char * vector2 ) {unsigned char result = 0;result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1 , *vector2 );return result;}void MixColumn( unsigned char * column ){unsigned char row[8] = {0x02, 0x03, 0x01, 0x01, 0x02, 0x03, 0x01, 0x01};// Prepare first row of matrix twice, to eliminate need for cycling.unsigned char result[4];// Take dot products of each matrix row and the column vector.result[0] = DotProduct( row+0, column );result[1] = DotProduct( row+3, column );result[2] = DotProduct( row+2, column );result[3] = DotProduct( row+1, column );// Copy temporary result to original column.column[0] = result[0];column[1] = result[1];column[2] = result[2];column[3] = result[3];}void MixColumns( unsigned char * state ){MixColumn( state + 0*4 );MixColumn( state + 1*4 );MixColumn( state + 2*4 );MixColumn( state + 3*4 );}void ShiftRows( unsigned char * state ){unsigned char temp;// Note: State is arranged column by column.// Cycle second row left one time.temp = state[ 1 + 0*4 ];state[ 1 + 0*4 ] = state[ 1 + 1*4 ];state[ 1 + 1*4 ] = state[ 1 + 2*4 ];state[ 1 + 2*4 ] = state[ 1 + 3*4 ];state[ 1 + 3*4 ] = temp;// Cycle third row left two times.temp = state[ 2 + 0*4 ];state[ 2 + 0*4 ] = state[ 2 + 2*4 ];state[ 2 + 2*4 ] = temp;temp = state[ 2 + 1*4 ];state[ 2 + 1*4 ] = state[ 2 + 3*4 ];state[ 2 + 3*4 ] = temp;// Cycle fourth row left three times, ie. right once.temp = state[ 3 + 3*4 ];state[ 3 + 3*4 ] = state[ 3 + 2*4 ];state[ 3 + 2*4 ] = state[ 3 + 1*4 ];state[ 3 + 1*4 ] = state[ 3 + 0*4 ];state[ 3 + 0*4 ] = temp;}void Cipher( unsigned char * block, unsigned char * expandedKey ) {unsigned char round = ROUNDS-1;XORBytes( block, expandedKey, 16 );expandedKey += BLOCKSIZE;do {SubBytes( block, 16 );ShiftRows( block );MixColumns( block );XORBytes( block, expandedKey, 16 );expandedKey += BLOCKSIZE;} while( --round );SubBytes( block, 16 );ShiftRows( block );XORBytes( block, expandedKey, 16 );}void aesEncInit(void){powTbl = block1;logTbl = tempbuf;CalcPowLog( powTbl, logTbl );sBox = block2;CalcSBox( sBox );expandedKey = block1;KeyExpansion( expandedKey );}void aesEncrypt( unsigned char * buffer, unsigned char * chainBlock ) {XORBytes( buffer, chainBlock, BLOCKSIZE );Cipher( buffer, expandedKey );CopyBytes( chainBlock, buffer, BLOCKSIZE );}#include <string.h>void AES_Test(void){unsigned char dat[16]="0123456789ABCDEF";unsigned char chainCipherBlock[16];unsigned char i;for(i=0;i<32;i++) AES_Key_Table[i]=i;//做运算之前先要设置好密钥,这里只是设置密钥的DEMO。
AES加密算法的C++实现过程
0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, /*3*/
0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, /*4*/
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */ 0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb,
/*0*/ 0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb,
0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, /*b*/
0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, /*c*/
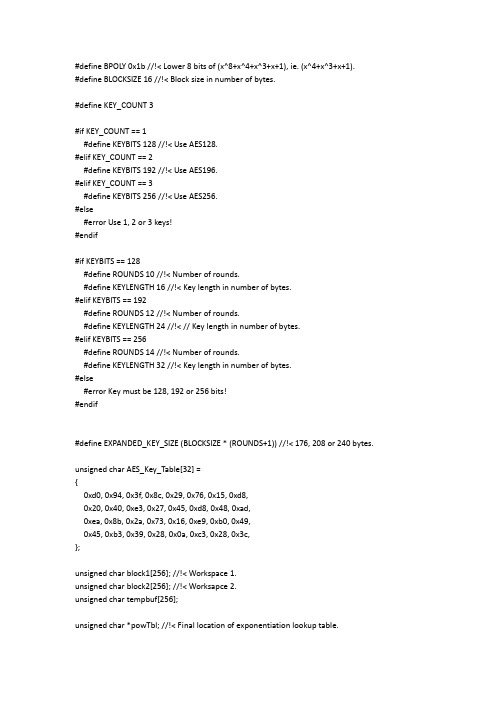
//AES.H
#ifndef _AES_H_ #define _AES_H_
#include "stdafx.h"
#define AES_KEY_ROW_NUMBER 4 #define AES_KEY_COLUMN_NUMBER 4 #define AES_ROUND_COUNT 10
class AES : public Encryption { public:
AES算法的C语言实现

( (uint32) MUL( 0x0E, y ) << 24 );
RT0[i] &= 0xFFFFFFFF;
RT1[i] = ROTR8( RT0[i] );
0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B,
0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF,
0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, uint32 Fra bibliotekT3[256];
/* reverse S-box & tables */
uint32 RSb[256];
uint32 RT0[256];
uint32 RT1[256];
uint32 RT2[256];
uint32 RT3[256];
/* round constants */
0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76,
0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0,
0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0,
x ^= y; y = ( y << 1 ) | ( y >> 7 );
x ^= y ^ 0x63;
FSb[i] = x;
RSb[x] = i;
}
/* generate the forward and reverse tables */
AES-256算法C语言实现
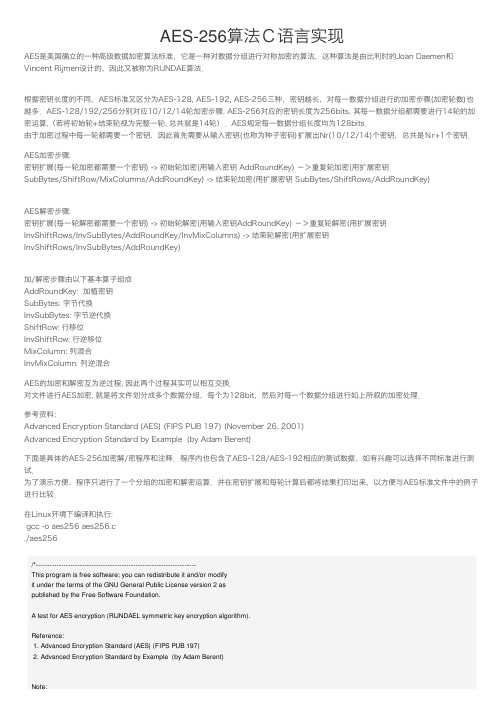
AES-256算法C语⾔实现AES是美国确⽴的⼀种⾼级数据加密算法标准,它是⼀种对数据分组进⾏对称加密的算法,这种算法是由⽐利时的Joan Daemen和Vincent Rijmen设计的,因此⼜被称为RIJNDAE算法.根据密钥长度的不同,AES标准⼜区分为AES-128, AES-192, AES-256三种,密钥越长,对每⼀数据分组进⾏的加密步骤(加密轮数)也越多.AES-128/192/256分别对应10/12/14轮加密步骤. AES-256对应的密钥长度为256bits, 其每⼀数据分组都需要进⾏14轮的加密运算,(若将初始轮+结束轮视为完整⼀轮, 总共就是14轮).AES规定每⼀数据分组长度均为128bits.由于加密过程中每⼀轮都需要⼀个密钥,因此⾸先需要从输⼊密钥(也称为种⼦密码)扩展出Nr(10/12/14)个密钥,总共是Nr+1个密钥.AES加密步骤:密钥扩展(每⼀轮加密都需要⼀个密钥) -> 初始轮加密(⽤输⼊密钥 AddRoundKey) ->重复轮加密(⽤扩展密钥SubBytes/ShiftRow/MixColumns/AddRoundKey) -> 结束轮加密(⽤扩展密钥 SubBytes/ShiftRows/AddRoundKey)AES解密步骤:密钥扩展(每⼀轮解密都需要⼀个密钥) -> 初始轮解密(⽤输⼊密钥AddRoundKey) ->重复轮解密(⽤扩展密钥InvShiftRows/InvSubBytes/AddRoundKey/InvMixColumns) -> 结束轮解密(⽤扩展密钥InvShiftRows/InvSubBytes/AddRoundKey)加/解密步骤由以下基本算⼦组成AddRoundKey: 加植密钥SubBytes: 字节代换InvSubBytes: 字节逆代换ShiftRow: ⾏移位InvShiftRow: ⾏逆移位MixColumn: 列混合InvMixColumn: 列逆混合AES的加密和解密互为逆过程, 因此两个过程其实可以相互交换.对⽂件进⾏AES加密, 就是将⽂件划分成多个数据分组,每个为128bit,然后对每⼀个数据分组进⾏如上所叙的加密处理.参考资料:Advanced Encryption Standard (AES) (FIPS PUB 197) (November 26, 2001)Advanced Encryption Standard by Example (by Adam Berent)下⾯是具体的AES-256加密解/密程序和注释.程序内也包含了AES-128/AES-192相应的测试数据,如有兴趣可以选择不同标准进⾏测试.为了演⽰⽅便,程序只进⾏了⼀个分组的加密和解密运算.并在密钥扩展和每轮计算后都将结果打印出来,以⽅便与AES标准⽂件中的例⼦进⾏⽐较.在Linux环境下编译和执⾏:gcc -o aes256 aes256.c./aes256/*---------------------------------------------------------------------This program is free software; you can redistribute it and/or modifyit under the terms of the GNU General Public License version 2 aspublished by the Free Software Foundation.A test for AES encryption (RIJNDAEL symmetric key encryption algorithm).Reference:1. Advanced Encryption Standard (AES) (FIPS PUB 197)2. Advanced Encryption Standard by Example (by Adam Berent)Note:1. Standard and parameters.Key Size Block Size Number of Rounds(Nk words) (Nb words) (Nr)AES-128 4 4 10AES-192 6 4 12AES-256 8 4 14Midas Zhoumidaszhou@https:///widora/wegi----------------------------------------------------------------------*/#include <stdio.h>#include <stdint.h>#include <string.h>/* S_BOX S盒 */static const uint8_t sbox[256] = {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84, 0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2, 0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73, 0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB, 0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF, 0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16 };/* Reverse S_BOX 反向S盒 */static const uint8_t rsbox[256] = {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB, 0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB, 0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E, 0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25, 0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92, 0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84, 0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06, 0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B, 0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73, 0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E, 0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B, 0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4, 0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F, 0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF, 0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61, 0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D };/* Galois Field Multiplication E-table GF乘法E表 */static const uint8_t Etab[256]= {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x01, 0x03, 0x05, 0x0F, 0x11, 0x33, 0x55, 0xFF, 0x1A, 0x2E, 0x72, 0x96, 0xA1, 0xF8, 0x13, 0x35,0xE5, 0x34, 0x5C, 0xE4, 0x37, 0x59, 0xEB, 0x26, 0x6A, 0xBE, 0xD9, 0x70, 0x90, 0xAB, 0xE6, 0x31,0x53, 0xF5, 0x04, 0x0C, 0x14, 0x3C, 0x44, 0xCC, 0x4F, 0xD1, 0x68, 0xB8, 0xD3, 0x6E, 0xB2, 0xCD,0x4C, 0xD4, 0x67, 0xA9, 0xE0, 0x3B, 0x4D, 0xD7, 0x62, 0xA6, 0xF1, 0x08, 0x18, 0x28, 0x78, 0x88,0x83, 0x9E, 0xB9, 0xD0, 0x6B, 0xBD, 0xDC, 0x7F, 0x81, 0x98, 0xB3, 0xCE, 0x49, 0xDB, 0x76, 0x9A,0xB5, 0xC4, 0x57, 0xF9, 0x10, 0x30, 0x50, 0xF0, 0x0B, 0x1D, 0x27, 0x69, 0xBB, 0xD6, 0x61, 0xA3,0xFE, 0x19, 0x2B, 0x7D, 0x87, 0x92, 0xAD, 0xEC, 0x2F, 0x71, 0x93, 0xAE, 0xE9, 0x20, 0x60, 0xA0,0xFB, 0x16, 0x3A, 0x4E, 0xD2, 0x6D, 0xB7, 0xC2, 0x5D, 0xE7, 0x32, 0x56, 0xFA, 0x15, 0x3F, 0x41,0xC3, 0x5E, 0xE2, 0x3D, 0x47, 0xC9, 0x40, 0xC0, 0x5B, 0xED, 0x2C, 0x74, 0x9C, 0xBF, 0xDA, 0x75,0x9F, 0xBA, 0xD5, 0x64, 0xAC, 0xEF, 0x2A, 0x7E, 0x82, 0x9D, 0xBC, 0xDF, 0x7A, 0x8E, 0x89, 0x80,0x9B, 0xB6, 0xC1, 0x58, 0xE8, 0x23, 0x65, 0xAF, 0xEA, 0x25, 0x6F, 0xB1, 0xC8, 0x43, 0xC5, 0x54,0xFC, 0x1F, 0x21, 0x63, 0xA5, 0xF4, 0x07, 0x09, 0x1B, 0x2D, 0x77, 0x99, 0xB0, 0xCB, 0x46, 0xCA,0x45, 0xCF, 0x4A, 0xDE, 0x79, 0x8B, 0x86, 0x91, 0xA8, 0xE3, 0x3E, 0x42, 0xC6, 0x51, 0xF3, 0x0E,0x12, 0x36, 0x5A, 0xEE, 0x29, 0x7B, 0x8D, 0x8C, 0x8F, 0x8A, 0x85, 0x94, 0xA7, 0xF2, 0x0D, 0x17,0x39, 0x4B, 0xDD, 0x7C, 0x84, 0x97, 0xA2, 0xFD, 0x1C, 0x24, 0x6C, 0xB4, 0xC7, 0x52, 0xF6, 0x01};/* Galois Field Multiplication L-table GF乘法L表 */static const uint8_t Ltab[256]= {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x0, 0x0, 0x19, 0x01, 0x32, 0x02, 0x1A, 0xC6, 0x4B, 0xC7, 0x1B, 0x68, 0x33, 0xEE, 0xDF, 0x03, // 00x64, 0x04, 0xE0, 0x0E, 0x34, 0x8D, 0x81, 0xEF, 0x4C, 0x71, 0x08, 0xC8, 0xF8, 0x69, 0x1C, 0xC1, // 10x7D, 0xC2, 0x1D, 0xB5, 0xF9, 0xB9, 0x27, 0x6A, 0x4D, 0xE4, 0xA6, 0x72, 0x9A, 0xC9, 0x09, 0x78, // 20x65, 0x2F, 0x8A, 0x05, 0x21, 0x0F, 0xE1, 0x24, 0x12, 0xF0, 0x82, 0x45, 0x35, 0x93, 0xDA, 0x8E, // 30x96, 0x8F, 0xDB, 0xBD, 0x36, 0xD0, 0xCE, 0x94, 0x13, 0x5C, 0xD2, 0xF1, 0x40, 0x46, 0x83, 0x38, // 40x66, 0xDD, 0xFD, 0x30, 0xBF, 0x06, 0x8B, 0x62, 0xB3, 0x25, 0xE2, 0x98, 0x22, 0x88, 0x91, 0x10, // 50x7E, 0x6E, 0x48, 0xC3, 0xA3, 0xB6, 0x1E, 0x42, 0x3A, 0x6B, 0x28, 0x54, 0xFA, 0x85, 0x3D, 0xBA, // 60x2B, 0x79, 0x0A, 0x15, 0x9B, 0x9F, 0x5E, 0xCA, 0x4E, 0xD4, 0xAC, 0xE5, 0xF3, 0x73, 0xA7, 0x57, // 70xAF, 0x58, 0xA8, 0x50, 0xF4, 0xEA, 0xD6, 0x74, 0x4F, 0xAE, 0xE9, 0xD5, 0xE7, 0xE6, 0xAD, 0xE8, // 80x2C, 0xD7, 0x75, 0x7A, 0xEB, 0x16, 0x0B, 0xF5, 0x59, 0xCB, 0x5F, 0xB0, 0x9C, 0xA9, 0x51, 0xA0, // 90x7F, 0x0C, 0xF6, 0x6F, 0x17, 0xC4, 0x49, 0xEC, 0xD8, 0x43, 0x1F, 0x2D, 0xA4, 0x76, 0x7B, 0xB7, // A0xCC, 0xBB, 0x3E, 0x5A, 0xFB, 0x60, 0xB1, 0x86, 0x3B, 0x52, 0xA1, 0x6C, 0xAA, 0x55, 0x29, 0x9D, // B0x97, 0xB2, 0x87, 0x90, 0x61, 0xBE, 0xDC, 0xFC, 0xBC, 0x95, 0xCF, 0xCD, 0x37, 0x3F, 0x5B, 0xD1, // C0x53, 0x39, 0x84, 0x3C, 0x41, 0xA2, 0x6D, 0x47, 0x14, 0x2A, 0x9E, 0x5D, 0x56, 0xF2, 0xD3, 0xAB, // D0x44, 0x11, 0x92, 0xD9, 0x23, 0x20, 0x2E, 0x89, 0xB4, 0x7C, 0xB8, 0x26, 0x77, 0x99, 0xE3, 0xA5, // E0x67, 0x4A, 0xED, 0xDE, 0xC5, 0x31, 0xFE, 0x18, 0x0D, 0x63, 0x8C, 0x80, 0xC0, 0xF7, 0x70, 0x07 // F};/* RCON 表 */static const uint32_t Rcon[15]= {0x01000000,0x02000000,0x04000000,0x08000000,0x10000000,0x20000000,0x40000000,0x80000000,0x1B000000,0x36000000,0x6C000000,0xD8000000,0xAB000000,0x4D000000,0x9A000000};/* Functions */void print_state(const uint8_t *s); /* 打印分组数据 */int aes_ShiftRows(uint8_t *state); /* ⾏移位 */int aes_InvShiftRows(uint8_t *state); /* ⾏逆移位 */int aes_ExpRoundKeys(uint8_t Nr, uint8_t Nk, const uint8_t *inkey, uint32_t *keywords); /* 密钥扩展 */int aes_AddRoundKey(uint8_t Nr, uint8_t Nk, uint8_t round, uint8_t *state, const uint32_t *keywords); /* 加植密钥 */ int aes_EncryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state); /* 分组加密 */int aes_DecryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state); /* 分组解密 *//*==============MAIN===============*/int main(void){int i,k;const uint8_t Nb=4; /* 分组长度 Block size in words, 4/4/4 for AES-128/192/256 */uint8_t Nk; /* 密钥长度 column number, as of 4xNk, 4/6/8 for AES-128/192/256 */uint8_t Nr; /* 加密轮数 Number of rounds, 10/12/14 for AES-128/192/256 */uint8_t state[4*4]; /* 分组数据 State array, data in row sequence! */uint64_t ns; /* 总分组数 Total number of states *//* 待加密数据 */const uint8_t input_msg[]= {0x00,0x11,0x22,0x33,0x44,0x55,0x66,0x77,0x88,0x99,0xaa,0xbb,0xcc,0xdd,0xee,0xff};/* AES-128/192/256 对应的密钥长度,加密轮数, 输⼊密钥 */#if 0 /* TEST data --- AES-128 */Nk=4;Nr=10;const uint8_t inkey[4*4]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f};#endif#if 0 /* TEST data --- AES-192 */Nk=6;Nr=12;const uint8_t inkey[4*6]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f,0x10,0x11,0x12,0x13,0x14,0x15,0x16,0x17};#endif#if 1 /* TEST data --- AES-256 */Nk=8;Nr=14;const uint8_t inkey[4*8]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f,0x10,0x11,0x12,0x13,0x14,0x15,0x16,0x17,0x18,0x19,0x1a,0x1b,0x1c,0x1d,0x1e,0x1f};#endif/* 密钥扩展测试数据------TEST: For Key expansion */#if 0Nk=4;Nr=10;const uint8_t inkey[4*4]= /* Nb*Nk */{ 0x2b, 0x7e, 0x15, 0x16, 0x28, 0xae, 0xd2, 0xa6, 0xab, 0xf7, 0x15, 0x88, 0x09, 0xcf, 0x4f, 0x3c }; #endif#if 0Nk=6;Nr=12;const uint8_t inkey[4*6]= /* Nb*Nk */{ 0x8e, 0x73, 0xb0, 0xf7, 0xda, 0x0e, 0x64, 0x52, 0xc8, 0x10, 0xf3, 0x2b,0x80, 0x90, 0x79, 0xe5, 0x62, 0xf8, 0xea, 0xd2, 0x52, 0x2c, 0x6b, 0x7b };#endif#if 0Nk=8;const uint8_t inkey[4*8]= /* Nb*Nk */{ 0x60, 0x3d, 0xeb, 0x10, 0x15, 0xca, 0x71, 0xbe, 0x2b, 0x73, 0xae, 0xf0, 0x85, 0x7d, 0x77, 0x81,0x1f, 0x35, 0x2c, 0x07, 0x3b, 0x61, 0x08, 0xd7, 0x2d, 0x98, 0x10, 0xa3, 0x09, 0x14, 0xdf, 0xf4 };#endifuint32_t keywords[Nb*(Nr+1)]; /* ⽤于存放扩展密钥,总共Nr+1把密钥 Nb==4, All expended keys, as of words in a column: 0xb0b1b2b3 *//* 从输⼊密钥产⽣Nk+1个轮密,每轮需要⼀个密钥 Generate round keys */aes_ExpRoundKeys(Nr, Nk, inkey, keywords);/* 数据分组数量,这⾥我们只设定为1组. Cal. total states *///ns=(strlen(input_msg)+15)/16;ns=1;/* 如果是多个分组,那么分别对每个分组进⾏加密,i=0 ~ ns-1 */i=0; /* i=0 ~ ns-1 *//* 将待加密数据放⼊到数据分组state[]中,注意:state[]中数据按column顺序存放! */bzero(state,16);for(k=0; k<16; k++)state[(k%4)*4+k/4]=input_msg[i*16+k];/* 加密数据分组 Encrypt each state */aes_EncryptState(Nr, Nk, keywords, state);/* 打印加密后的分组数据 */printf("***********************************\n");printf("******* Finish Encryption *******\n");printf("***********************************\n");print_state(state);/* 解密数据分组 Decrypt state */aes_DecryptState(Nr, Nk, keywords, state);//printf("Finish decrypt message, Round Nr=%d, KeySize Nk=%d, States ns=%llu.\n", Nr, Nk, ns);/* 打印解密后的分组数据 */printf("***********************************\n");printf("******* Finish Decryption *******\n");printf("***********************************\n");print_state(state);return 0;}/* 打印分组数据 Print state */void print_state(const uint8_t *s){int i,j;for(i=0; i<4; i++) {for(j=0; j<4; j++) {printf("%02x",s[i*4+j]);//printf("'%c'",s[i*4+j]); /* A control key MAY erase previous chars on screen! */printf(" ");}printf("\n");}printf("\n");}/*------------------------------⾏移位Shift operation of the state.Return:0 OK<0 Fails-------------------------------*/int aes_ShiftRows(uint8_t *state){int j,k;uint8_t tmp;if(state==NULL)return -1;for(k=0; k<4; k++) {/* each row shift k times */for(j=0; j<k; j++) {tmp=*(state+4*k); /* save the first byte *///memcpy(state+4*k, state+4*k+1, 3);memmove(state+4*k, state+4*k+1, 3);*(state+4*k+3)=tmp; /* set the last byte */}}return 0;}/*------------------------------⾏逆移位Shift operation of the state.@state[4*4]Return:0 OK<0 Fails-------------------------------*/int aes_InvShiftRows(uint8_t *state){int j,k;uint8_t tmp;if(state==NULL)return -1;for(k=0; k<4; k++) {/* each row shift k times */for(j=0; j<k; j++) {tmp=*(state+4*k+3); /* save the last byte */memmove(state+4*k+1, state+4*k, 3);*(state+4*k)=tmp; /* set the first byte */}}return 0;}/*-------------------------------------------------------------加植密钥Add round key to the state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256 @Nk: Key size, in words.@round: Current round number.@state: Pointer to state.@keywords[Nb*(Nr+1)]: All round keys, in words.int aes_AddRoundKey(uint8_t Nr, uint8_t Nk, uint8_t round, uint8_t *state, const uint32_t *keywords){int k;if(state==NULL || keywords==NULL)return -1;for(k=0; k<4*4; k++)state[k] = ( keywords[round*4+k%4]>>((3-(k>>2))<<3) &0xFF )^state[k];return 0;}/*----------------------------------------------------------------------------------------------------------密钥扩展从输⼊密钥(也称为种⼦密码)扩展出Nr(10/12/14)个密钥,总共是Nr+1个密钥Generate round keys.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key size, in words.@inkey[4*Nk]: Original key, 4*Nk bytes, arranged row by row.@keywords[Nb*(Nr+1)]: Output keys, in words. Nb*(Nr+1)one keywords(32 bytes) as one column of key_bytes(4 bytes)Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails---------------------------------------------------------------------------------------------------------------*/int aes_ExpRoundKeys(uint8_t Nr, uint8_t Nk, const uint8_t *inkey, uint32_t *keywords){int i;const int Nb=4;uint32_t temp;if(inkey==NULL || keywords==NULL)return -1;/* Re_arrange inkey to keywords, convert 4x8bytes each row_data to a 32bytes keyword, as a complex column_data. */ for( i=0; i<Nk; i++ ) {keywords[i]=(inkey[4*i]<<24)+(inkey[4*i+1]<<16)+(inkey[4*i+2]<<8)+inkey[4*i+3];}/* Expend round keys */for(i=Nk; i<Nb*(Nr+1); i++) {temp=keywords[i-1];if( i%Nk==0 ) {/* RotWord */temp=( temp<<8 )+( temp>>24 );/* Subword */temp=(sbox[temp>>24]<<24) +(sbox[(temp>>16)&0xFF]<<16) +(sbox[(temp>>8)&0xFF]<<8)+sbox[temp&0xFF];/* temp=SubWord(RotWord(temp)) XOR Rcon[i/Nk-1] */temp=temp ^ Rcon[i/Nk-1];}else if (Nk>6 && i%Nk==4 ) {/* Subword */temp=(sbox[temp>>24]<<24) +(sbox[(temp>>16)&0xFF]<<16) +(sbox[(temp>>8)&0xFF]<<8)+sbox[temp&0xFF];}/* Get keywords[i] */}/* Print all keys */for(i=0; i<Nb*(Nr+1); i++)printf("keywords[%d]=0x%08X\n", i, keywords[i]);return 0;}/*----------------------------------------------------------------------数据分组加密Encrypt state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key length, in words.@keywordss[Nb*(Nr+1)]: All round keys, in words.@state[4*4]: The state block.Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails------------------------------------------------------------------------*/int aes_EncryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state) {int i,k;uint8_t round;uint8_t mc[4]; /* Temp. var */if(keywords==NULL || state==NULL)return -1;/* 1. AddRoundKey: 加植密钥 */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, 0, state, keywords);print_state(state);/* 循环Nr-1轮加密运算 Run Nr round functions */for( round=1; round<Nr; round++) { /* Nr *//* 2. SubBytes: 字节代换 Substitue State Bytes with SBOX */printf(" --- SubBytes() Round:%d ---\n",round);for(k=0; k<16; k++)state[k]=sbox[state[k]];print_state(state);/* 3. ShiftRow: ⾏移位 Shift State Rows */printf(" --- ShiftRows() Round:%d ---\n",round);aes_ShiftRows(state);print_state(state);/* 4. MixColumn: 列混合 Mix State Cloumns *//* Galois Field Multiplication, Multi_Matrix:2 3 1 11 2 3 11 12 33 1 1 2Note:1. Any number multiplied by 1 is equal to the number itself.2. Any number multiplied by 0 is 0!*/printf(" --- MixColumn() Round:%d ---\n",round);mc[0]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[2])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[3])%0xFF] )^state[i+8]^state[i+12];mc[1]= state[i]^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[2])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[3])%0xFF] )^state[i+12];mc[2]= state[i]^state[i+4]^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[2])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[3])%0xFF] );mc[3]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[3])%0xFF] )^state[i+4]^state[i+8]^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[2])%0xFF] );state[i+0]=mc[0];state[i+4]=mc[1];state[i+8]=mc[2];state[i+12]=mc[3];}print_state(state);/* 5. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);} /* END Nr rounds *//* 6. SubBytes: 字节代换 Substitue State Bytes with SBOX */printf(" --- SubBytes() Round:%d ---\n",round);for(k=0; k<16; k++)state[k]=sbox[state[k]];print_state(state);/* 7. ShiftRow: ⾏移位 Shift State Rows */printf(" --- ShiftRows() Round:%d ---\n",round);aes_ShiftRows(state);print_state(state);/* 8. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);return 0;}/*----------------------------------------------------------------------Decrypt the state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key length, in words.@keywordss[Nb*(Nr+1)]: All round keys, in words.@state[4*4]: The state block.Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails------------------------------------------------------------------------*/int aes_DecryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state)int i,k;uint8_t round;uint8_t mc[4]; /* Temp. var */if(keywords==NULL || state==NULL)return -1;/* 1. AddRoundKey: 加植密钥 Add round key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, Nr, state, keywords); /* From Nr_th round */ print_state(state);/* 循环Nr-1轮加密运算 Run Nr round functions */for( round=Nr-1; round>0; round--) { /* round [Nr-1 1] *//* 2. InvShiftRow: ⾏逆移位 InvShift State Rows */printf(" --- InvShiftRows() Round:%d ---\n",Nr-round);aes_InvShiftRows(state);print_state(state);/* 3. InvSubBytes: 字节逆代换 InvSubstitue State Bytes with R_SBOX */printf(" --- (Inv)SubBytes() Round:%d ---\n",Nr-round);for(k=0; k<16; k++)state[k]=rsbox[state[k]];print_state(state);/* 4. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key Round:%d ---\n", Nr-round);aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);/* 5. InvMixColumn: 列逆混合 Inverse Mix State Cloumns *//* Galois Field Multiplication, Multi_Matrix:0x0E 0x0B 0x0D 0x090x09 0x0E 0x0B 0x0D0x0D 0x09 0x0E 0x0B0x0B 0x0D 0x09 0x0ENote:1. Any number multiplied by 1 is equal to the number itself.2. Any number multiplied by 0 is 0!*/printf(" --- InvMixColumn() Round:%d ---\n",Nr-round);for(i=0; i<4; i++) { /* i as column index */mc[0]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0E])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0B])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0D])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x09])%0xFF] );mc[1]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x09])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0E])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0B])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0D])%0xFF] );mc[2]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0D])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x09])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0E])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0B])%0xFF] );mc[3]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0B])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0D])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x09])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0E])%0xFF] );state[i+0]=mc[0];state[i+4]=mc[1];state[i+8]=mc[2];state[i+12]=mc[3];print_state(state);} /* END Nr rounds *//* 6. InvShiftRow: ⾏逆移位 Inverse Shift State Rows */printf(" --- InvShiftRows() Round:%d ---\n",Nr-round);aes_InvShiftRows(state);print_state(state);/* 7. InvSubBytes: 字节逆代换 InvSubstitue State Bytes with SBOX */ printf(" --- InvSubBytes() Round:%d ---\n",Nr-round);for(k=0; k<16; k++)state[k]=rsbox[state[k]];print_state(state);/* 8. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key Round:%d ---\n",Nr-round);aes_AddRoundKey(Nr, Nk, 0, state, keywords);print_state(state);return 0;}。
AES加密算法的C++实现过程

//AES.H#ifndef _AES_H_#define _AES_H_#include"stdafx.h"#define AES_KEY_ROW_NUMBER 4#define AES_KEY_COLUMN_NUMBER 4#define AES_ROUND_COUNT 10class AES : public Encryption{public:AES(void);AES(BYTE* key);virtual ~AES(void);void Encrypt(BYTE *, BYTE *,size_t);void Decrypt(BYTE *, BYTE *,size_t);private:BYTE swapbox[11][4][4];BYTE* Cipher(BYTE* input);BYTE* InvCipher(BYTE* input);BYTE* Cipher(void * input, size_t length);BYTE* InvCipher(void * input, size_t length);void KeyExpansion(BYTE* key, BYTE w[][4][AES_KEY_COLUMN_NUMBER]);BYTE FFmul(BYTE a, BYTE b);void SubBytes(BYTE state[][AES_KEY_COLUMN_NUMBER]);void ShiftRows(BYTE state[][AES_KEY_COLUMN_NUMBER]);void MixColumns(BYTE state[][AES_KEY_COLUMN_NUMBER]);void AddRoundKey(BYTE state[][AES_KEY_COLUMN_NUMBER], BYTE k[][AES_KEY_COLUMN_NUMBER]);void InvSubBytes(BYTE state[][AES_KEY_COLUMN_NUMBER]);void InvShiftRows(BYTE state[][AES_KEY_COLUMN_NUMBER]);void InvMixColumns(BYTE state[][AES_KEY_COLUMN_NUMBER]);};#endif// _AES_H_//Encryption.h#ifndef _ENCRYPTION_H_#define _ENCRYPTION_H_#include"stdafx.h"class Encryption{public:virtualvoid Encrypt(BYTE *, BYTE *,size_t) = 0;virtualvoid Decrypt(BYTE *, BYTE *,size_t) = 0;};#endif//EncryptionFactory.h#ifndef _ENCRYPTION_FACTORY_H_#define _ENCRYPTION_FACTORY_H_#include"Encryption.h"#include"stdafx.h"class EncryptionFactory{public:EncryptionFactory(void);virtual ~EncryptionFactory(void);static Encryption* getEncryption(int encryptionType,BYTE* key);private :static Encryption* encry;};#endif//AES.cpp#include"stdafx.h"#include"AES.h"#include<stdlib.h>#include<memory.h>//permuteboxstaticunsignedchar permutebox[] ={ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */ 0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, /*0*/0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, /*1*/0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, /*2*/0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, /*3*/0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, /*4*/0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, /*5*/0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, /*6*/0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, /*7*/0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, /*8*/0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, /*9*/0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, /*a*/0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, /*b*/0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, /*c*/0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, /*d*/0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, /*e*/0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 /*f*/};//inversepermutationboxstatic unsignedchar inversepermutationbox[]={ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */ 0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb, /*0*/0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb, /*1*/0x54,0x7b,0x94,0x32,0xa6,0xc2,0x23,0x3d,0xee,0x4c,0x95,0x0b,0x42,0xfa,0xc3,0x4e, /*2*/0x08,0x2e,0xa1,0x66,0x28,0xd9,0x24,0xb2,0x76,0x5b,0xa2,0x49,0x6d,0x8b,0xd1,0x25, /*3*/0x72,0xf8,0xf6,0x64,0x86,0x68,0x98,0x16,0xd4,0xa4,0x5c,0xcc,0x5d,0x65,0xb6,0x92, /*4*/0x6c,0x70,0x48,0x50,0xfd,0xed,0xb9,0xda,0x5e,0x15,0x46,0x57,0xa7,0x8d,0x9d,0x84, /*5*/0x90,0xd8,0xab,0x00,0x8c,0xbc,0xd3,0x0a,0xf7,0xe4,0x58,0x05,0xb8,0xb3,0x45,0x06, /*6*/0xd0,0x2c,0x1e,0x8f,0xca,0x3f,0x0f,0x02,0xc1,0xaf,0xbd,0x03,0x01,0x13,0x8a,0x6b, /*7*/0x3a,0x91,0x11,0x41,0x4f,0x67,0xdc,0xea,0x97,0xf2,0xcf,0xce,0xf0,0xb4,0xe6,0x73, /*8*/0x96,0xac,0x74,0x22,0xe7,0xad,0x35,0x85,0xe2,0xf9,0x37,0xe8,0x1c,0x75,0xdf,0x6e, /*9*/0x47,0xf1,0x1a,0x71,0x1d,0x29,0xc5,0x89,0x6f,0xb7,0x62,0x0e,0xaa,0x18,0xbe,0x1b, /*a*/0xfc,0x56,0x3e,0x4b,0xc6,0xd2,0x79,0x20,0x9a,0xdb,0xc0,0xfe,0x78,0xcd,0x5a,0xf4, /*b*/0x1f,0xdd,0xa8,0x33,0x88,0x07,0xc7,0x31,0xb1,0x12,0x10,0x59,0x27,0x80,0xec,0x5f, /*c*/0x60,0x51,0x7f,0xa9,0x19,0xb5,0x4a,0x0d,0x2d,0xe5,0x7a,0x9f,0x93,0xc9,0x9c,0xef, /*d*/0xa0,0xe0,0x3b,0x4d,0xae,0x2a,0xf5,0xb0,0xc8,0xeb,0xbb,0x3c,0x83,0x53,0x99,0x61, /*e*/0x17,0x2b,0x04,0x7e,0xba,0x77,0xd6,0x26,0xe1,0x69,0x14,0x63,0x55,0x21,0x0c,0x7d /*f*/};AES::AES(void){}AES::AES(unsignedchar* key){KeyExpansion(key, swapbox);}AES::~AES(void){}/************************************************************************//* create a Encrypt method *//* param : data encrypt data *//* param :encryptArrayencryptArray *//* param :len encrypt data length *//* return : void *//************************************************************************/void AES::Encrypt(unsignedchar* data ,unsignedchar * encryptArray,size_tlen){memcpy(encryptArray,data,len);Cipher((void *)encryptArray,len);}/************************************************************************//* create a Decrypt method *//* param : data decrypt data *//* param :decryptArraydecryptArray *//* param :len decrypt data length *//* return : void *//************************************************************************/void AES::Decrypt(unsignedchar * data,unsignedchar * decryptArray,size_tlen){memcpy(decryptArray,data,len);InvCipher((void *)decryptArray,len);}/************************************************************************/ /* create a Cipher method only one time Encrypt */ /* param : input input encrypt data */ /* return : unsigned char * */ /************************************************************************/unsignedchar* AES::Cipher(unsignedchar* input){unsignedchar state[AES_KEY_ROW_NUMBER][AES_KEY_COLUMN_NUMBER];int i,r,c;for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER ;c++){state[r][c] = input[c*AES_KEY_COLUMN_NUMBER+r];}}AddRoundKey(state,swapbox[0]);for(i=1; i<=AES_ROUND_COUNT; i++){SubBytes(state);ShiftRows(state);if(i!=AES_ROUND_COUNT)MixColumns(state);AddRoundKey(state,swapbox[i]);}for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER ;c++){input[c*AES_KEY_COLUMN_NUMBER+r] = state[r][c];}}return input;}/************************************************************************/ /* create a InvCipher method only one time decrypt */ /* param : input input decrypt data */ /* return : unsigned char * */ /************************************************************************/ unsignedchar* AES::InvCipher(unsignedchar* input){unsignedchar state[AES_KEY_ROW_NUMBER][AES_KEY_COLUMN_NUMBER];int i,r,c;for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER ;c++){state[r][c] = input[c*AES_KEY_COLUMN_NUMBER+r];}}AddRoundKey(state, swapbox[10]);for(i=9; i>=0; i--){InvShiftRows(state);InvSubBytes(state);AddRoundKey(state, swapbox[i]);if(i){InvMixColumns(state);}}for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER ;c++){input[c*AES_KEY_COLUMN_NUMBER+r] = state[r][c];}}return input;}/************************************************************************/ /* Create a specified length of data encryption method */ /* param : input input data encryption */ /* param : length Input the length of the encrypted data */ /* return : unsigned char * */ /************************************************************************/ unsignedchar* AES::Cipher(void * input, size_t length){unsignedchar* in = (unsignedchar*) input;size_t i;if(!length){while(*(in+length++));in = (unsignedchar*) input;}for(i=0; i<length; i+=16){Cipher(in+i);}return (unsignedchar*)input;}/************************************************************************/ /* Create a specified length of InvCipher method */ /* param : input input data InvCipher *//* param : length Input the length of the InvCipher data *//* return : unsigned char * *//************************************************************************/ unsignedchar* AES::InvCipher(void * input, size_t length){unsignedchar* in = (unsignedchar*) input;size_t i;for(i=0; i<length; i+=16){InvCipher(in+i);}return (unsignedchar*)input;}/************************************************************************//*Create key method *//* param : key input data encryption key *//* param :swapbox Conversion of key array *//* return : void *//************************************************************************/void AES::KeyExpansion(unsignedchar* key, unsignedchar swapbox[][4][4]){int i,j,r,c;unsignedchar rc[] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36};for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){swapbox[0][r][c] = key[r+c*AES_KEY_COLUMN_NUMBER];}}for(i=1; i<=10; i++){for(j=0; j<AES_KEY_COLUMN_NUMBER; j++){unsignedchar t[AES_KEY_ROW_NUMBER];for(r=0; r<AES_KEY_ROW_NUMBER; r++){t[r] = j ? swapbox[i][r][j-1] : swapbox[i-1][r][3];}if(j == 0){unsignedchar temp = t[0];for(r=0; r<AES_KEY_ROW_NUMBER-1; r++){t[r] = permutebox[t[(r+1)%AES_KEY_ROW_NUMBER]];}t[3] = permutebox[temp];t[0] ^= rc[i-1];}for(r=0; r<AES_KEY_ROW_NUMBER; r++){swapbox[i][r][j] = swapbox[i-1][r][j] ^ t[r];}}}}/************************************************************************/ /*Create mixed operation method ranks */ /* param : a row char */ /* param : b column char */ /* return : unsigned char */ /************************************************************************/unsignedchar AES::FFmul(unsignedchar a, unsignedchar b){unsignedchar bw[AES_KEY_ROW_NUMBER];unsignedchar res=0;int i;bw[0] = b;for(i=1; i<AES_KEY_ROW_NUMBER; i++){bw[i] = bw[i-1]<<1;if(bw[i-1]&0x80){bw[i]^=0x1b;}}for(i=0; i<AES_KEY_ROW_NUMBER; i++){if((a>>i)&0x01){res ^= bw[i];}}return res;}/************************************************************************/ /* Create bytes alternatives */ /* param : state[][] Byte array alternative */ /* return : void */ /************************************************************************/ void AES::SubBytes(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){int r,c;for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){state[r][c] = permutebox[state[r][c]];}}}/************************************************************************//* Create rows transform method */ /* param : state[][] line array alternative */ /* return : void */ /************************************************************************/ void AES::ShiftRows(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){unsignedchar t[AES_KEY_COLUMN_NUMBER];int r,c;for(r=1; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){t[c] = state[r][(c+r)%AES_KEY_COLUMN_NUMBER];}for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){state[r][c] = t[c];}}}/************************************************************************/ /* Create columns transform method */ /* param : state[][] columns array alternative */ /* return : void */ /************************************************************************/ void AES::MixColumns(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){unsignedchar t[AES_KEY_ROW_NUMBER];int r,c;for(c=0; c< AES_KEY_COLUMN_NUMBER; c++){for(r=0; r<AES_KEY_ROW_NUMBER; r++){t[r] = state[r][c];}for(r=0; r<AES_KEY_ROW_NUMBER; r++){state[r][c] = FFmul(0x02, t[r])^ FFmul(0x03, t[(r+1)%AES_KEY_COLUMN_NUMBER])^ FFmul(0x01, t[(r+2)%AES_KEY_COLUMN_NUMBER])^ FFmul(0x01, t[(r+3)%AES_KEY_COLUMN_NUMBER]);}}}/************************************************************************/ /*Create round keys plus transform method */ /* param : state[][] keys plus array alternative */ /* param : k[][] temp array alternative */ /* return : void */ /************************************************************************/ void AES::AddRoundKey(unsignedchar state[][AES_KEY_COLUMN_NUMBER],unsignedchar k[][AES_KEY_COLUMN_NUMBER]){int r,c;for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){for(r=0; r<AES_KEY_ROW_NUMBER; r++){state[r][c] ^= k[r][c];}}}/************************************************************************//* CreateInvSubBytes alternatives *//* param : state[][] InvSubBytes array alternative *//* return : void *//************************************************************************/void AES::InvSubBytes(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){int r,c;for(r=0; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){state[r][c] = inversepermutationbox[state[r][c]];}}}/************************************************************************//* CreateInvShiftRows transform method *//* param : state[][] InvShiftRows array alternative *//* return : void *//************************************************************************/void AES::InvShiftRows(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){unsignedchar t[AES_KEY_COLUMN_NUMBER];int r,c;for(r=1; r<AES_KEY_ROW_NUMBER; r++){for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){t[c] = state[r][(c-r+AES_KEY_COLUMN_NUMBER)%AES_KEY_COLUMN_NUMBER];}for(c=0; c<AES_KEY_COLUMN_NUMBER; c++){state[r][c] = t[c];}}}/************************************************************************//* CreateInvMixColumns transform method *//* param : state[][] InvMixColumns array alternative *//* return : void *//************************************************************************/ void AES::InvMixColumns(unsignedchar state[][AES_KEY_COLUMN_NUMBER]){unsignedchar t[AES_KEY_ROW_NUMBER];int r,c;for(c=0; c< AES_KEY_COLUMN_NUMBER; c++){for(r=0; r<AES_KEY_ROW_NUMBER; r++){t[r] = state[r][c];}for(r=0; r<AES_KEY_ROW_NUMBER; r++){state[r][c] = FFmul(0x0e, t[r])^ FFmul(0x0b, t[(r+1)%AES_KEY_ROW_NUMBER])^ FFmul(0x0d, t[(r+2)%AES_KEY_ROW_NUMBER])^ FFmul(0x09, t[(r+3)%AES_KEY_ROW_NUMBER]);}}}//TestEncryption.cpp用于测试主方法#include<stdio.h>#include<string.h>#include<istream>#include<vector>unsignedchar key[] ={'v' ,'b','c','d','f' ,'i','n','o','e' ,'w','t','i','q' ,'x','l','p',/*0xff, 0x7e, 0x15, 0x16,0x28, 0xae, 0xd2, 0xa6,0xab, 0xf7, 0x15, 0x88,0x09, 0xcf, 0x4f, 0x3c*/};int main(){Encryption* aes = EncryptionFactory::getEncryption(0,key);char* s="1234567891234567abcdefghijklmnop";unsignedchar * strEncrypt = aes->encrypt(s);puts((char*)strEncrypt);unsignedchar * strDecrypt = aes->decrypt((char*)strEncrypt);puts((char*)strDecrypt);getchar();return 0;}。
AES加密C语言实现代码
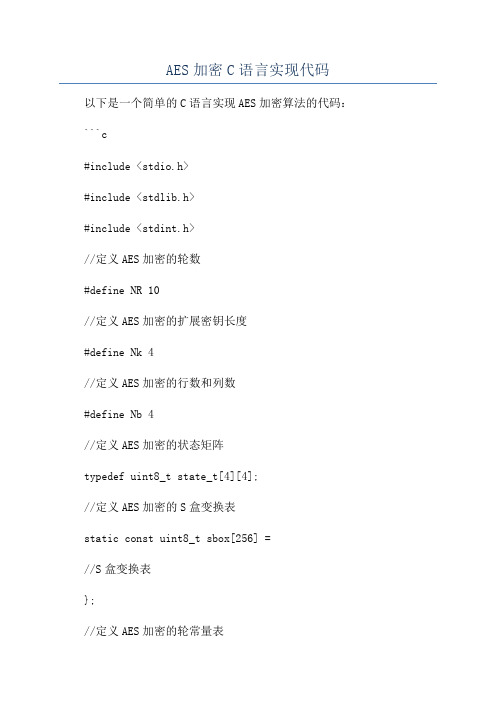
AES加密C语言实现代码以下是一个简单的C语言实现AES加密算法的代码:```c#include <stdio.h>#include <stdlib.h>#include <stdint.h>//定义AES加密的轮数#define NR 10//定义AES加密的扩展密钥长度#define Nk 4//定义AES加密的行数和列数#define Nb 4//定义AES加密的状态矩阵typedef uint8_t state_t[4][4];//定义AES加密的S盒变换表static const uint8_t sbox[256] =//S盒变换表};//定义AES加密的轮常量表static const uint8_t Rcon[11] =//轮常量表};//定义AES加密的密钥扩展变换函数void KeyExpansion(const uint8_t* key, uint8_t* expandedKey) uint32_t* ek = (uint32_t*)expandedKey;uint32_t temp;//密钥拷贝到扩展密钥中for (int i = 0; i < Nk; i++)ek[i] = (key[4 * i] << 24) , (key[4 * i + 1] << 16) ,(key[4 * i + 2] << 8) , (key[4 * i + 3]);}//扩展密钥生成for (int i = Nk; i < Nb * (NR + 1); i++)temp = ek[i - 1];if (i % Nk == 0)//对上一个密钥的字节进行循环左移1位temp = (temp >> 8) , ((temp & 0xFF) << 24);//对每个字节进行S盒变换temp = (sbox[temp >> 24] << 24) , (sbox[(temp >> 16) & 0xFF] << 16) , (sbox[(temp >> 8) & 0xFF] << 8) , sbox[temp & 0xFF];// 取轮常量Rcontemp = temp ^ (Rcon[i / Nk - 1] << 24);} else if (Nk > 6 && i % Nk == 4)//对每个字节进行S盒变换temp = (sbox[temp >> 24] << 24) , (sbox[(temp >> 16) & 0xFF] << 16) , (sbox[(temp >> 8) & 0xFF] << 8) , sbox[temp & 0xFF];}//生成下一个密钥ek[i] = ek[i - Nk] ^ temp;}//定义AES加密的字节替换函数void SubBytes(state_t* state)for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[i][j] = sbox[(*state)[i][j]];}}//定义AES加密的行移位函数void ShiftRows(state_t* state) uint8_t temp;//第2行循环左移1位temp = (*state)[1][0];(*state)[1][0] = (*state)[1][1]; (*state)[1][1] = (*state)[1][2]; (*state)[1][2] = (*state)[1][3]; (*state)[1][3] = temp;//第3行循环左移2位temp = (*state)[2][0];(*state)[2][0] = (*state)[2][2]; (*state)[2][2] = temp;temp = (*state)[2][1];(*state)[2][1] = (*state)[2][3]; (*state)[2][3] = temp;//第4行循环左移3位temp = (*state)[3][0];(*state)[3][0] = (*state)[3][3];(*state)[3][3] = (*state)[3][2];(*state)[3][2] = (*state)[3][1];(*state)[3][1] = temp;//定义AES加密的列混淆函数void MixColumns(state_t* state)uint8_t temp, tmp, tm;for (int i = 0; i < 4; i++)tmp = (*state)[i][0];tm = (*state)[i][0] ^ (*state)[i][1] ^ (*state)[i][2] ^ (*state)[i][3] ;temp = (*state)[i][0] ^ (*state)[i][1];(*state)[i][0] ^= temp ^ tm;temp = (*state)[i][1] ^ (*state)[i][2];(*state)[i][1] ^= temp ^ tm;temp = (*state)[i][2] ^ (*state)[i][3];(*state)[i][2] ^= temp ^ tm;temp = (*state)[i][3] ^ tmp;(*state)[i][3] ^= temp ^ tm;}//定义AES加密的轮密钥加函数void AddRoundKey(state_t* state, const uint8_t* roundKey) for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[j][i] ^= roundKey[i * 4 + j];}}//定义AES加密函数void AES_Encrypt(const uint8_t* plainText, const uint8_t* key, uint8_t* cipherText)state_t* state = (state_t*)cipherText;uint8_t expandedKey[4 * Nb * (NR + 1)];//密钥扩展KeyExpansion(key, expandedKey);//初始化状态矩阵for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[j][i] = plainText[i * 4 + j];}}//第1轮密钥加AddRoundKey(state, key);//迭代执行第2至第10轮加密for (int round = 1; round < NR; round++) SubBytes(state);ShiftRows(state);MixColumns(state);AddRoundKey(state, expandedKey + round * 16); }//执行第11轮加密SubBytes(state);ShiftRows(state);AddRoundKey(state, expandedKey + NR * 16);int maiuint8_t plainText[16] =//明文数据};uint8_t key[16] =//密钥数据};uint8_t cipherText[16];AES_Encrypt(plainText, key, cipherText);。
AES算法C语言实现源码
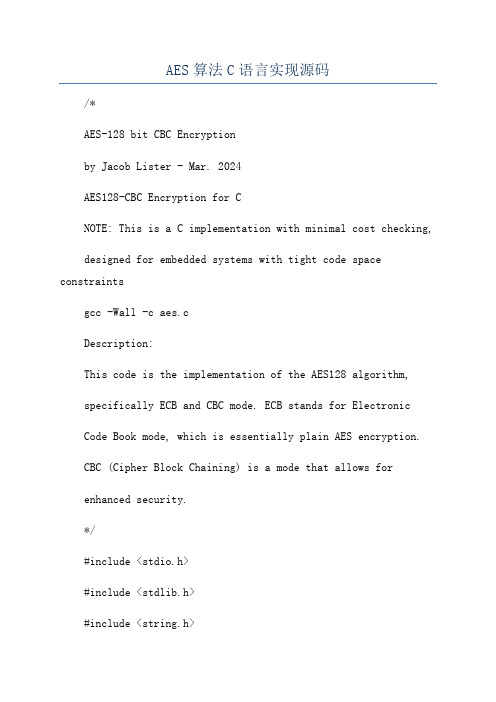
AES算法C语言实现源码/*AES-128 bit CBC Encryptionby Jacob Lister - Mar. 2024AES128-CBC Encryption for CNOTE: This is a C implementation with minimal cost checking, designed for embedded systems with tight code space constraintsgcc -Wall -c aes.cDescription:This code is the implementation of the AES128 algorithm,specifically ECB and CBC mode. ECB stands for ElectronicCode Book mode, which is essentially plain AES encryption.CBC (Cipher Block Chaining) is a mode that allows forenhanced security.*/#include <stdio.h>#include <stdlib.h>#include <string.h>typedef unsigned char AES_BYTE;/*constant in AES. Value=4*/#define Nb 4/* The number of 32 bit words in a key. */#define Nk 4/*Key length in bytes [128 bit](Nk * 4), or 16 bytes.*/#define KEYLEN 16/*The number of rounds in AES Cipher.Number of rounds=10, 12, 14.*/#define Nr 14AES_BYTE * AES_Encrypt(AES_BYTE *plainText, AES_BYTE *key); AES_BYTE * AES_Decrypt(AES_BYTE *cipherText, AES_BYTE *key);Function to store the round keysgenerated from the cipher key.*/void AES_KeyExpansion(AES_BYTE key[4*Nk], AES_BYTE roundKey[4*Nb*(Nr+1)]);/*Cipher is the main function that encryptsthe plaintext given the key [128 bit].*/void AES_Cipher(AES_BYTE *in, AES_BYTE *out, AES_BYTE *roundKey);/*The SubBytes Function is usedto substitute each byte of the statewith its corresponding byte in theRijndael S-box.*/void SubBytes(AES_BYTE *state);The ShiftRows function is usedto shift the rows cyclically aroundthe state.*/void ShiftRows(AES_BYTE *state);/*The MixColumns function is usedto mix the columns of the statematrix.*/void MixColumns(AES_BYTE *state);/*The AddRoundKey function is usedto add round key word to thestate matrix to produce the output.*/void AddRoundKey(AES_BYTE *state, AES_BYTE* roundKey); /*The SubBytes Function is usedto substitute each byte of the state with its inverse in the Rijndael S-box. */void InvSubBytes(AES_BYTE *state);/*The InvShiftRows function is usedto shift the rows cyclically aroundthe state in the opposite direction.*/void InvShiftRows(AES_BYTE *state);/*The InvMixColumns function is usedto mix the columns of the statematrix in the opposite direction.*/void InvMixColumns(AES_BYTE *state);/*The AES_Encrypt functionencrypts the plaintext usingthe provided AES_128 encryptionkey.*/AES_BYTE* AES_Encrypt(AES_BYTE *plainText, AES_BYTE *key) //struct to store ciphertextAES_BYTE *cipherText;int stat_len = 4 * Nb;// The KeyExpansion routine must be called// before encryption.AES_BYTE roundKey[4 * Nb * (Nr + 1)];。
AES加密的C语言实现
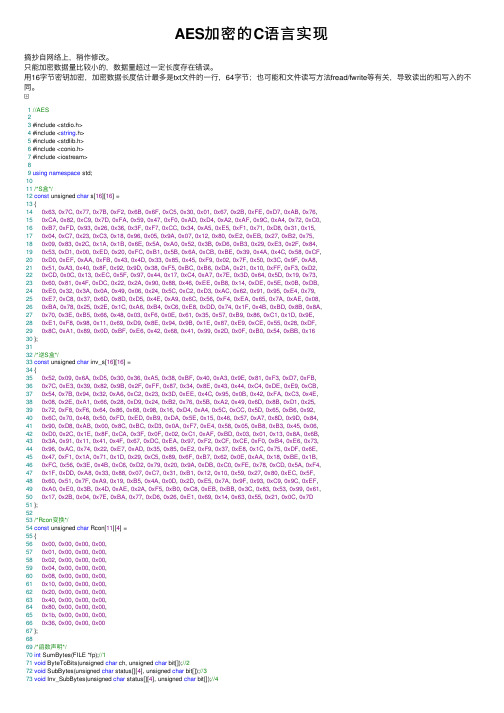
AES加密的C语⾔实现摘抄⾃⽹络上,稍作修改。
只能加密数据量⽐较⼩的,数据量超过⼀定长度存在错误。
⽤16字节密钥加密,加密数据长度估计最多是txt⽂件的⼀⾏,64字节;也可能和⽂件读写⽅法fread/fwrite等有关,导致读出的和写⼊的不同。
1//AES23 #include <stdio.h>4 #include <string.h>5 #include <stdlib.h>6 #include <conio.h>7 #include <iostream>89using namespace std;1011/*S盒*/12const unsigned char s[16][16] =13 {140x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76,150xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0,160xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15,170x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75,180x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84,190x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF,200xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8,210x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2,220xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73,230x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB,240xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79,250xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08,260xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A,270x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E,280xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF,290x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x1630 };3132/*逆S盒*/33const unsigned char inv_s[16][16] =34 {350x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB,360x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB,370x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E,380x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25,390x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92,400x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84,410x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06,420xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B,430x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73,440x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E,450x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B,460xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4,470x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F,480x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF,490xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61,500x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D51 };5253/*Rcon变换*/54const unsigned char Rcon[11][4] =55 {560x00, 0x00, 0x00, 0x00,570x01, 0x00, 0x00, 0x00,580x02, 0x00, 0x00, 0x00,590x04, 0x00, 0x00, 0x00,600x08, 0x00, 0x00, 0x00,610x10, 0x00, 0x00, 0x00,620x20, 0x00, 0x00, 0x00,630x40, 0x00, 0x00, 0x00,640x80, 0x00, 0x00, 0x00,650x1b, 0x00, 0x00, 0x00,660x36, 0x00, 0x00, 0x0067 };6869/*函数声明*/70int SumBytes(FILE *fp);//171void ByteToBits(unsigned char ch, unsigned char bit[]);//272void SubBytes(unsigned char status[][4], unsigned char bit[]);//373void Inv_SubBytes(unsigned char status[][4], unsigned char bit[]);//474void ShiftRows(unsigned char status[][4]);//575void Inv_ShiftRows(unsigned char status[][4]);//676 unsigned char ByteMultiply(unsigned char c);//777void MixColumns(unsigned char status[][4]);//878void Inv_MixColumns(unsigned char status[][4]);//979void RotWord(unsigned char c[], unsigned char temp[]);//1080void SubWord(unsigned char temp[], unsigned char bit[]);//1181void KeyExpansion(char *k, unsigned char key[][4], unsigned char bit[]);//1282void RoundKeyChoice(unsigned char key[][4], unsigned char RoundKey[][4], int cnt); //1383void AddRoundKey(unsigned char RoundKey[][4], unsigned char status[][4]);//1484void BytesWrite(FILE *fp, unsigned char status[][4]);//1585void DataEncrypt(char *k, unsigned char key[][4], unsigned char bit[], FILE *fp1, FILE *fp2, unsigned char RoundKey[][4], unsigned char status[][4]); 86void DataDecrypt(char *k1, unsigned char key[][4], FILE *fp1, FILE *fp2, unsigned char status[][4], unsigned char RoundKey[][4], unsigned char bit[]); 8788/*1、计算被加密⽂件数据的字节数⽬*/89int SumBytes(FILE *fp){90int num = 0;91char ch = fgetc(fp);92while (ch != EOF){93 num++;94 ch = fgetc(fp);95 }96return num;97 }9899/*2、字节转换为⼆进制位存放在数组中*/100void ByteToBits(unsigned char ch, unsigned char bit[]){101for (int i = 0; i < 8; i++)102 bit[i] = (ch >> i) & 1;103 }104105/*3、S盒变换*/106void SubBytes(unsigned char status[][4], unsigned char bit[]){107for (int i = 0; i < 4; i++)108for (int j = 0; j < 4; j++){109 ByteToBits(status[i][j], bit);110 status[i][j] = s[(bit[7] * 8 + bit[6] * 4 + bit[5] * 2 + bit[4])][(bit[3] * 8 + bit[2] * 4 + bit[1] * 2 + bit[0])];111 }112 }113114/*4、逆S盒变换*/115void Inv_SubBytes(unsigned char status[][4], unsigned char bit[]){116for (int i = 0; i < 4; i++)117for (int j = 0; j < 4; j++){118 ByteToBits(status[i][j], bit);119 status[i][j] = inv_s[(bit[7] * 8 + bit[6] * 4 + bit[5] * 2 + bit[4])][(bit[3] * 8 + bit[2] * 4 + bit[1] * 2 + bit[0])];120 }121 }122123/*5、⾏变换*/124void ShiftRows(unsigned char status[][4]){125 unsigned char temp1 = status[1][0];126 unsigned char temp2 = status[2][0];127 unsigned char temp3 = status[2][1];128 unsigned char temp4 = status[3][0];129 unsigned char temp5 = status[3][1];130 unsigned char temp6 = status[3][2];131for (int i = 0; i < 3; i++)132 status[1][i] = status[1][(i + 1)];133 status[1][3] = temp1;134for (int i = 0; i < 2; i++)135 status[2][i] = status[2][(i + 2)];136 status[2][2] = temp2;137 status[2][3] = temp3;138 status[3][0] = status[3][3];139 status[3][1] = temp4;140 status[3][2] = temp5;141 status[3][3] = temp6;142 }143144/*6、逆⾏变换*/145void Inv_ShiftRows(unsigned char status[][4]){146 unsigned char temp1 = status[1][3];147 unsigned char temp2 = status[2][2];148 unsigned char temp3 = status[2][3];149 unsigned char temp4 = status[3][1];150for (int i = 3; i > 0; i--)151 status[1][i] = status[1][i - 1];152 status[1][0] = temp1;153for (int i = 3; i > 1; i--)154 status[2][i] = status[2][i - 2];155 status[2][0] = temp2;156 status[2][1] = temp3;157for (int i = 1; i < 4; i++)158 status[3][i] = status[3][(i + 1) % 4];159 status[3][0] = temp4;160 }161162/*7、列变换被调⽤函数x乘法(02乘法)*/163 unsigned char ByteMultiply(unsigned char c){164 unsigned char temp;165 temp = c << 1;166if (c & 0x80){167 temp ^= 0x1b;168 }169return temp;170 }171172/*8、列变换*/173void MixColumns(unsigned char status[][4]){174 unsigned char temp[4][4];175for (int j = 0; j < 4; j++)176for (int i = 0; i < 4; i++)177 temp[i][j] = ByteMultiply(status[i % 4][j]) //0x02乘法178 ^ (status[(i + 1) % 4][j] ^ ByteMultiply(status[(i + 1) % 4][j])) //0x03乘法179 ^ status[(i + 2) % 4][j] //0x01乘法180 ^ status[(i + 3) % 4][j]; //0x01乘法181for (int i = 0; i < 4; i++)182for (int j = 0; j < 4; j++)183 status[i][j] = temp[i][j];184 }185186/*9、逆列变换*/187void Inv_MixColumns(unsigned char status[][4]){188 unsigned char temp[4][4];189for (int j = 0; j< 4; j++)190for (int i = 0; i<4; i++)191 temp[i][j] = (ByteMultiply(ByteMultiply(ByteMultiply(status[i % 4][j]))) ^ ByteMultiply(ByteMultiply(status[i % 4][j])) ^ ByteMultiply(status[i % 4][j])) //0x0E乘法192 ^ (ByteMultiply(ByteMultiply(ByteMultiply(status[(i + 1) % 4][j]))) ^ ByteMultiply(status[(i + 1) % 4][j]) ^ status[(i + 1) % 4][j]) //0x0B乘法193 ^ (ByteMultiply(ByteMultiply(ByteMultiply(status[(i + 2) % 4][j]))) ^ ByteMultiply(ByteMultiply(status[(i + 2) % 4][j])) ^ status[(i + 2) % 4][j]) //0x0D乘法194 ^ (ByteMultiply(ByteMultiply(ByteMultiply(status[(i + 3) % 4][j]))) ^ status[(i + 3) % 4][j]); //0x09乘法195for (int i = 0; i < 4; i++)196for (int j = 0; j < 4; j++)197 status[i][j] = temp[i][j];198 }199200/*10、位置变换*/201void RotWord(unsigned char c[], unsigned char temp[]){202for (int i = 1; i < 4; i++)203 temp[i - 1] = c[i];204 temp[3] = c[0];205 }206207/*11、⼩S盒变换*/208void SubWord(unsigned char temp[], unsigned char bit[]){209for (int i = 0; i < 4; i++){210 ByteToBits(temp[i], bit);211 temp[i] = s[(bit[7] * 8 + bit[6] * 4 + bit[5] * 2 + bit[4])][(bit[3] * 8 + bit[2] * 4 + bit[1] * 2 + bit[0])];212 }213 }214215/*12、密钥扩展函数*/216void KeyExpansion(char *k, unsigned char key[][4], unsigned char bit[]){217int i, j;218 unsigned char temp[4];219for (i = 0; i < 44; i++)220for (j = 0; j < 4; j++){221if (i < 4) key[i][j] = *(k + 4 * i + j);222else if ((i != 0) && (i % 4 == 0)){223 RotWord(key[i - 1], temp);224 SubWord(temp, bit);225 key[i][j] = key[i - 4][j] ^ temp[j] ^ Rcon[i / 4][j];226 }227else key[i][j] = key[i - 1][j] ^ key[i - 4][j];228 }229 }230231/*13、从扩展密钥中选择轮密钥的函数*/232void RoundKeyChoice(unsigned char key[][4], unsigned char RoundKey[][4], int cnt){233int cnt1 = 4 * cnt;234for (int i = 0; i < 4; i++){235for (int j = 0; j < 4; j++){236 RoundKey[i][j] = key[cnt1][j];237 }238 cnt1++;239 }240 }241242/*14、与扩展密钥的异或运算*/243void AddRoundKey(unsigned char RoundKey[][4], unsigned char status[][4]){244for (int j = 0; j < 4; j++)245for (int i = 0; i < 4; i++)246 status[i][j] = status[i][j] ^ RoundKey[j][i];247 }248249/*15、将状态矩阵中的字节写⼊⽂件中函数*/250void BytesWrite(FILE *fp, unsigned char status[][4]){251char ch;252for (int i = 0; i < 4; i++)253for (int j = 0; j < 4; j++){254 ch = status[i][j];255 fputc(ch, fp);256 }257 }258259/*16.加密总函数*/260void DataEncrypt(char *k, unsigned char key[][4], unsigned char bit[], FILE *fp1, FILE *fp2, unsigned char RoundKey[][4], unsigned char status[][4]) { 261int sum, numOfBlock, numOfSurplus;262char ch;263int len = strlen(k);264if (len != 16){265 free(k);266 printf("\n\n输⼊密钥长度不满⾜要求!\n"); return;267 }268 KeyExpansion(k, key, bit);269 sum = SumBytes(fp1);270 fp1 = fopen("源⽂件.txt", "r");271 numOfBlock = sum / 16;272 numOfSurplus = sum % 16;273 ch = fgetc(fp1);274/*第⼀种情况*/275if (numOfBlock != 0 && numOfSurplus == 0){276for (int n = 1; n <= numOfBlock; n++){277for (int i = 0; i < 4; i++)278for (int j = 0; j < 4; j++){279 status[i][j] = ch;280 ch = fgetc(fp1);281 }//status赋值282 RoundKeyChoice(key, RoundKey, 0);283 AddRoundKey(RoundKey, status);284for (int nr = 1; nr <= 10; nr++){285 SubBytes(status, bit);286 ShiftRows(status);287 MixColumns(status);288 RoundKeyChoice(key, RoundKey, nr);289 AddRoundKey(RoundKey, status);290 }//10轮加密291 SubBytes(status, bit);292 ShiftRows(status);293 RoundKeyChoice(key, RoundKey, 4);294 AddRoundKey(RoundKey, status);295 BytesWrite(fp2, status);296 }//Block循环297 }//if298//第⼆种情况299else if (numOfBlock == 0 && numOfSurplus != 0){300for (int i = 0; i < 4; i++)301for (int j = 0; j < 4; j++){302if (ch == EOF) break;303 status[i][j] = ch;304 ch = fgetc(fp1);305 }306for (int i = sum / 4; i < 4; i++)307for (int j = sum % 4; j < 4; j++)308 status[i][j] = 0x00;309 RoundKeyChoice(key, RoundKey, 0);310 AddRoundKey(RoundKey, status);311for (int nr = 1; nr <= 10; nr++){312 SubBytes(status, bit);313 ShiftRows(status);314 MixColumns(status);315 RoundKeyChoice(key, RoundKey, nr);316 AddRoundKey(RoundKey, status);317 }//10轮加密318 SubBytes(status, bit);319 ShiftRows(status);320 RoundKeyChoice(key, RoundKey, 4);321 AddRoundKey(RoundKey, status);322 BytesWrite(fp2, status);323 }//else if324//第三种情况325else if (numOfBlock != 0 && numOfSurplus != 0){326for (int n = 1; n <= numOfBlock; n++){327for (int i = 0; i <4; i++)328for (int j = 0; j < 4; j++){329 status[i][j] = ch;330 ch = fgetc(fp1);331 }//status赋值332 RoundKeyChoice(key, RoundKey, 0);333 AddRoundKey(RoundKey, status);334for (int nr = 1; nr <= 10; nr++){335 SubBytes(status, bit);336 ShiftRows(status);337 MixColumns(status);338 RoundKeyChoice(key, RoundKey, nr);339 AddRoundKey(RoundKey, status);340 }//10轮加密341 SubBytes(status, bit);342 ShiftRows(status);343 RoundKeyChoice(key, RoundKey, 4);344 AddRoundKey(RoundKey, status);345 BytesWrite(fp2, status);346 }//Block循环347for (int i = 0; i < 4; i++)348for (int j = 0; j < 4; j++){349if (ch == EOF) break;350 status[i][j] = ch;351 ch = fgetc(fp1);352 }353for (int i = sum / 4; i < 4; i++)354for (int j = sum % 4; j < 4; j++)355 status[i][j] = 0x00;356 RoundKeyChoice(key, RoundKey, 0);357 AddRoundKey(RoundKey, status);358for (int nr = 1; nr <= 10; nr++){359 SubBytes(status, bit);360 ShiftRows(status);361 MixColumns(status);362 RoundKeyChoice(key, RoundKey, nr);363 AddRoundKey(RoundKey, status);364 }//10轮加密365 SubBytes(status, bit);366 ShiftRows(status);367 RoundKeyChoice(key, RoundKey, 4);368 AddRoundKey(RoundKey, status);369 BytesWrite(fp2, status);370 }//else371 free(k);372 fclose(fp1);373 fclose(fp2);374 printf("\n\n加密⽂件成功!\n\n");375 }376377/*17.解密总函数*/378void DataDecrypt(char *k1, unsigned char key[][4], FILE *fp1, FILE *fp2, unsigned char status[][4], unsigned char RoundKey[][4], unsigned char bit[]) { 379int numOfBlock, sum;380char ch;381int len = strlen(k1);382if (len != 16){383 free(k1);384 printf("\n\n输⼊密钥长度不满⾜要求!\n"); return;385 }386 sum = SumBytes(fp1);387 fp1 = fopen("加密后⽂件.txt", "r");388 numOfBlock = sum / 16;389 ch = fgetc(fp1);390for (int i = 1; i <= numOfBlock; i++){391for (int i = 0; i < 4; i++)392for (int j = 0; j < 4; j++){393 status[i][j] = ch;394 ch = fgetc(fp1);395 }396 RoundKeyChoice(key, RoundKey, 4);397 AddRoundKey(RoundKey, status);398 Inv_ShiftRows(status);399 Inv_SubBytes(status, bit);400for (int nr = 10; nr >= 1; nr--){401 RoundKeyChoice(key, RoundKey, nr);402 AddRoundKey(RoundKey, status);403 Inv_MixColumns(status);404 Inv_ShiftRows(status);405 Inv_SubBytes(status, bit);406 }//10轮解密407 RoundKeyChoice(key, RoundKey, 0);408 AddRoundKey(RoundKey, status);409 BytesWrite(fp2, status);410 }//Block411 free(k1);412 fclose(fp1);413 fclose(fp2);414 printf("\n\n解密⽂件成功!\n\n");415 }416417int main(){418int choice, sum1;419int flag = 1;420char *k, *k1;421 FILE *fp1, *fp2;422 unsigned char status[4][4] = { 0x00 };423 unsigned char key[44][4] = { 0x00 };424 unsigned char RoundKey[4][4] = { 0x00 };425 unsigned char bit[8] = { 0x00 };426do{427 printf("*****************************AES加密解密⽂件************************************"); 428 printf("\n");429 printf(" 1.加密⽂件\n\n");430 printf(" 2.解密⽂件\n\n");431 printf(" 3.退出\n\n");432 printf("\n请选择要进⾏的操作:");433 scanf("%d", &choice);434switch (choice){435case1: fp1 = fopen("源⽂件.txt", "r");436if (fp1 == NULL){437 printf("打开源⽂件失败!\n");438 getchar();439 exit(0);440 }441 fp2 = fopen("加密后⽂件.txt", "w");442if (fp2 == NULL){443 printf("打开加密后⽂件失败!\n");444 getchar();445 exit(0);446 }447 printf("\n请输⼊加密密钥(128bit):");448 k = (char *)malloc(20 * sizeof(char));449 cin >> k;450 DataEncrypt(k, key, bit, fp1, fp2, RoundKey, status);451break;452case2: fp1 = fopen("加密后⽂件.txt", "r");453if (fp1 == NULL){454 printf("\n打开加密后⽂件失败!\n");455 getchar();456 exit(0);457 }458 fp2 = fopen("解密后⽂件.txt", "w");459if (fp2 == NULL){460 printf("\n打开解密后⽂件失败!\n");461 getchar();462 exit(0);463 }464 printf("\n\n请输⼊解密密钥(128bit):");465 k1 = (char *)malloc(20 * sizeof(char));466 cin >> k1;467 DataDecrypt(k1, key, fp1, fp2, status, RoundKey, bit);468break;469case3: flag = 0; break;470default: printf("\n\n所选操作不合法!\n");471 }//switch472 } while (flag);473 }C Code。
aes算法c语言实现
aes算法c语言实现AES(Advanced Encryption Standard)是一种广泛应用于数据加密的算法。
以下是一个使用C语言实现的AES加密算法示例,用于对字符串进行加密和解密。
这个实现是基于ECB模式的,这是一种常用的加密模式,因为它简单且易于实现。
注意:这个实现是为了教学目的而提供的,可能不适合用于生产环境。
生产环境中的加密实现通常需要更复杂和安全的方法。
```c #include <stdio.h> #include <string.h> #include <stdint.h> #include <openssl/aes.h>void AES_encrypt(const uint8_t *key, const uint8_t*plaintext, uint8_t *ciphertext) { AES_KEY aesKey; AES_set_encrypt_key(key, 128, &aesKey);AES_encrypt(plaintext, ciphertext, &aesKey); }void AES_decrypt(const uint8_t *key, const uint8_t*ciphertext, uint8_t *plaintext) { AES_KEY aesKey; AES_set_decrypt_key(key, 128, &aesKey);AES_decrypt(ciphertext, plaintext, &aesKey); }int main() { // 定义密钥和明文/密文缓冲区uint8_t key[AES_BLOCK_SIZE]; // AES_BLOCK_SIZE是AES算法的块大小,通常是16字节(128位) uint8_tplaintext[AES_BLOCK_SIZE], ciphertext[AES_BLOCK_SIZE];// 填充密钥和明文/密文缓冲区 // 这里省略了填充代码,因为在实际应用中,你应该使用合适的填充方案来保护数据的完整性。
AES原理及其在c语言上的实现
AES加密解密算法及其在c语言上的实现引言对称密码算法主要用于保证数据的机密性,通信双方在加密/ 解密过程中使用它们共享的单一密钥。
对称密码算法的使用相当广泛,密码学界已经对它们进行了深入的研究[1] 。
最常用的对称密码算法是数据加密标准(DES) 算法,它是由IBM在美国国家安全局(NSA) 授意之下研制的一种使用56 位密钥的分组密码算法。
自1977 年公布成为美国政府的商用加密标准以来已使用20 多年[2] 。
DES 的主要问题是其密钥长度较短,已不适合于当今分布式开放网络对数据加密安全性的要求。
在DES 每隔五年的评估会议中,最后一次在1998 年美国政府终于决定不再继续延用DES作为联邦加密标准,也就表明了DES 将退出加密标准的舞台,而新的标准AES(AdvancedEncryptionStandard ) 将粉墨登场[3] 。
AES是美国国家标准技术研究所NIST旨在取代DES的新一代的加密标准[3~5] 。
NIST对AES候选算法的基本要求是:对称分组密码体制;密钥长度支持128,192,256位;明文分组长度128 位;算法应易于各种硬件和软件实现。
1998年NIST开始AES第一轮征集、分析、测试,共产生了15 个候选算法。
1999 年3 月完成了第二轮AES 的分析、测试。
1999 年8 月NIST公布了五种算法(MARS,RC6,Rijndael,Serpent,Twofish) 成为候选算法。
最后,Rijn2dael[5] ,这个由比利时人设计的算法与其它候选算法在成为高级加密标准(AES) 的竞争中取得成功,于2000 年10月被NIST宣布成为取代DES的新一代的数据加密标准,即AES。
尽管人们对AES还有不同的看法[6~8] ,但总体来说,Rijndael作为新一代的数据加密标准汇聚了强安全性、高性能、高效率、易用和灵活等优点。
AES设计有三个密钥长度:128,192,256 比特, 相对而言,AES 的128 比特密钥比DES的56 比特密钥强1021倍[4] 。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
0x60,0x81,0x4F,0xDC,0x22,0x2A,0x90,0x88,0x46,0xEE,0xB8,0x14,0xDE,0x5E,0x0B,0xDB,
0x08,0x0,0x0,0x0,
0x10,0x0,0x0,0x0,
0x20,0x0,0x0,0x0,
0x40,0x0,0x0,0x0,
0x80,0x0,0x0,0x0,
0x1B,0x0,0x0,0x0,
0x36,0x0,0x0,0x0,
};//书上63页
{
k=j*4+i;
sta2.a[i][j]=sta.a[i][j]^[k];
}
}
return sta2;
}
int RCon[10][4]={ //前十轮的常量
0x01,0x0,0x0,0x0,
0x02,0x0,0x0,0x0,
0x04,0x0,0x0,0x0,
0xBA,0x78,0x25,0x2E,0x1C,0xA6,0xB4,0xC6,0xE8,0xDD,0x74,0x1F,0x4B,0xBD,0x8B,0x8A,
0x70,0x3E,0xB5,0x66,0x48,0x03,0xF6,0x0E,0x61,0x35,0x57,0xB9,0x86,0xC1,0x1D,0x9E,
for(j=0;j<4;j++)
{
l=i-4;
Wkey[i][j]=Wkey[l][j]^temp[j]; //第i-4列与第i-1列列向量异或
}
}
}
for(i=0;i<11;i++) ///把Wkey[0]~Wkey[43]共44列列向量依次存入到NewKey中
state MixColumn(state sta); //MixColumn 列混合
text *KeyExpansion(text key); //KeyExpansion 密钥扩展
text AESCTR(text t,text key); //CTR模式的AES加密函数,密钥为key,明文为t
}
}
return sta2;
}
int SBoxReplace(int num,int SBox[]) //S盒置换
{
int x,y,k,xy;
x=num%16; //个位,列值
y=(num/16)%16; //十位,行值
0x09,0x83,0x2C,0x1A,0x1B,0x6E,0x5A,0xA0,0x52,0x3B,0xD6,0xB3,0x29,0xE3,0x2F,0x84,
0x53,0xD1,0x00,0xED,0x20,0xFC,0xB1,0x5B,0x6A,0xCB,0xBE,0x39,0x4A,0x4C,0x58,0xCF,
int SBoxReplace(int num,int SBox[]); //S盒置换
int *LeftMove(int b[],int n); //左移
state PrintSTATE(text t); //把一列数t转换成矩阵的形式
int SBox[]={ //定义S盒
typedef struct{
int a[M][M];
}state;
#define N 17 //矩阵中有16个元素
typedef struct{
int la[N];
}text;
int BitRandNum( unsigned int bits ); //定义随机函数
state InitState(text t); //初始化t
Newkey=(text *)malloc(11*sizeof(text));
temp2=(int *)malloc(4*sizeof(int));
for(i=0;i<4;i++){ //前4列列向量为初始密钥
for(j=0;j<4;j++)
{
l=4*i+j;
Wkey[i][j]=[l];
}
}
return sta;
}
state AddRoundKey(state sta,text key) //轮密钥加,即与密钥进行异或运算
{
state sta2;
int k,i,j;
for( i=0;i<M;i++){ //M=4
for(j=0;j<M;j++)
sta1=ShiftRows(sta); //行移位
sta=AddRoundKey(sta1,RoundKey[10]); //轮密钥加
mingwen1 = InitState(mingwen); //初始化明文块
for( i=0;i<4;i++){ //初始后的明文mingwen1与得到的输出块sta异或得到密文
for(j=0;j<4;j++)
{
k=j*4+i;
sta2.a[i][j]=sta.a[i][j]^mingwen1.a[k][j];
[k]=sta2.a[i][j];
}
}
free(RoundKey);
return miwen;
#include <stdio.h>
#include <time.h>
#include <stdlib.h>
#include <math.h>
#include <string.h>
#include <malloc.h>
#define SIZE 17
#define M 4 //定义4*4的矩阵
}
}
for(i=4;i<44;i++){ //需要扩展40列列向量.(书上62页)
for(j=0;j<4;j++)
temp[j]=Wkey[i-1][j];
if(i%4==0) //i是4的倍数
{
temp2=LeftMove(temp,1); //左移
}
}
RoundKey=KeyExpansion(key); //密钥扩展,得到子密钥
sta1=AddRoundKey(sta,RoundKey[0]); //首轮轮密钥加。随机数和子密钥
//共 10 轮
for(i=1;i<10;i++) //中间轮变换
{
sta=SubBytes(sta1); //字节变换
0xE1,0xF8,0x98,0x11,0x69,0xD9,0x8E,0x94,0x9B,0x1E,0x87,0xE9,0xCE,0x55,0x28,0xDF,
0x8C,0xA1,0x89,0x0D,0xBF,0xE6,0x42,0x68,0x41,0x99,0x2D,0x0F,0xB0,0x54,0xBB,0x16
};
text AESCTR(text t,text key) //CTR模式的AES加密函数,随机数为t。密钥为key
{
state sta,sta1,sta2,mingwen1; //mingwen1为初始后的明文,输出块为最终的sta
int i,j,k,s;
text mingwen,miwen; //明文为mingwen,密文为miwen
}
state SubBytes(state sta) //字节变换
{
state sta2;
int i,j;
for(i=0;i<M;i++){
for(j=0;j<M;j++)
{
sta2.a[i][j]=SBoxReplace(sta.a[i][j],SBox); //S盒置换
}
state InitState(text t) //初始化State,列向填充矩阵
{
state sta;
int k,i,j;
for(i=0;i<M;i++) {
for(j=0;j<M;j++)
{
k=j*4+i;
sta.a[i][j]=[k];
0xE0,0x32,0x3A,0x0A,0x49,0x06,0x24,0x5C,0xC2,0xD3,0xAC,0x62,0x91,0x95,0xE4,0x79,
0xE7,0xC8,0x37,0x6D,0x8D,0xD5,0x4E,0xA9,0x6C,0x56,0xF4,0xEA,0x65,0x7A,0xAE,0x08,
sta1=ShiftRows(sta); //行移位
sta=MixColumn(sta1); //列混合
sta1=AddRoundKey(sta,RoundKey[i]); //轮密钥加,RoundKey[i]表示第i列子密钥
}
//最后轮变换(无列混合)
sta=SubBytes(sta1); //字节变换
for(k=0;k<4;k++) //k表示四个字节
{
l=i/4-1;
temp1[k]=SBoxReplace(*(temp2+k),SBox); //S盒置换
temp[k]=temp1[k]^RCon[l][k]; //计算常量
