英文版计算机试题及答案
计算机网络英文题库(附答案)chapter3解析

计算机⽹络英⽂题库(附答案)chapter3解析Chapter 3 Transport Layer1. A transport-layer protocol provides for logical communication between ____.A Application processesB HostsC RoutersD End systems2. Transport-layer protocols run in ____.A ServersB ClientsC RoutersD End systems3. In transport layer, the send side breaks application messages into ____, passes to network layer.A FramesB SegmentsC Data-gramsD bit streams4. Services provided by transport layer include ____.A HTTP and FTPB TCP and IPC TCP and UDPD SMTP5. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers6. These two minimal transport-layer services----____ and ____----are the only two services that UDP provides!A process-to-process data delivery, error checkingB congestion control, reliable data transferC flow control, congestion controlD In-order data transfer, error checking7. Port number’s scop e is ____ to ____.A 0, 1023B 0, 65535C 0, 127D 0,2558. The port numbers ranging from ____to ____ are called well-known port number and are restricted.A 0, 1023B 0, 65535C 0, 127D 0,2559. UDP socket identified by two components, they are ____.A source IP addresses and source port numbersB source IP addresses and destination IP addressesC destination IP address and destination port numbersD destination port numbers and source port numbers10. TCP socket identified by a (an) ____.A 1-tupleB 2-tupleC 3-tupleD 4-tuple11. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP12. Reliable data transfer protocol over a perfectly reliable channel is____.A rdt1.0B rdt2.0C rdt3.0D rdt2.113. Reliable data transfer protocol over a channel with bit errors and packet losses is _ ___.A rdt1.0B rdt2.0C rdt3.0D rdt2.114. Which of the following about reliable data transfer over a channel with bit errors i s not correct?A RDT2.0: assuming ACK and NAK will not be corruptedB RDT2.1: assuming ACK and NAK can be corruptedC RDT2.2: only use ACK-sD RDT2.2: use both ACK-s and NAK-s15. Which of the following protocols is not pipelining protocols?A TCPB rdt3.0C GO-BACK-ND selective repeat16. Which of the following is not correct about GBN protocol?A Only using ACK-sB Using cumulative ACK-sC Receiver discards all out-of-order packetsD It is not pipelined protocol17. Which of the following is not correct about SR protocol?A receiver individually acknowledges all correctly received packetsB sender only resends packets for which ACK not receivedC It limits sequence number of sent but un-ACK-ed packetsD It is not a pipelined protocol18. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection19. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection20. The FIN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection21.How does TCP sender perceive congestion?A Through a timeout eventB Through a receiving duplicate ACK-s eventC Both A and BD Either A or B22. Extending host-to-host delivery to process-to-process delivery is called transport-layer ____ and .A multiplexing and de-multiplexingB storing and forwardingC forwarding and filteringD switching and routing23. UDP is a ____ service while TCP is a connection-oriented service.A ConnectionlessB ReliableC Connection-orientedD In-order24. The UDP header has only four fields, they are____.A Source port number, destination port number, length and checksumB Source port number, destination port number, source IP and destination IPC source IP, destination IP, source MAC address and destination MAC addressD source IP, destination IP, sequence number and ACK sequence number25. There are two 16-bit integers: 1110 0110 0110 0110, 1101 0101 0101 0101. Their checksum is____.A 0100010001000011B 1011101110111100C 1111111111111111D 100000000000000026.The maximum amount of data that can be grabbed and placed in a segment is limited by the____.A Maximum segment size (MSS)B MTUC ChecksumD Sequence number27.The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host----the so-called____.A Maximum transmission unit (MTU)B MSSC ChecksumD Sequence number28. A File size of 500,000bytes, MSS equals 1000bytes. When we want to transmit this file with TCP, the sequence number of the first segment is 0, and the sequence number of the second segment is ____.A 1000B 999C 1001D 50000029.Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide____.A Cumulative acknowledgementsB Selective acknowledgementsC 3 duplicate ACKsD positive ACKs30. Provided α=0.125, current value of Estimated-RTT is 0.4s, Sample-RTT is 0.8s, then the new value of Estimated-RTT is ____s.A 0.45B 0.6C 0.7D 0.831.Provided RcvBuffer=20,LastByteRcvd=20,LastByteRead=15, thenRcvWindow=____.A 14B 15C 16D 1032. TCP service does not provide____.A Reliable data transferB Flow controlC Delay guaranteeD Congestion control33. There are two states in TCP congestion control, which are ____.A slow start and congestion avoidanceB safe start and congestion avoidanceC slow start and congestion abandonD safe start and congestion abandon34. The transport-layer protocol provides logical communication between ____, and the network-layer protocol provides logical communication ____.A hosts, processesB processes, hostsC threads, processesD processes, threads35. To implement the multicast services the Internet employs the ____ protocol.A FTPB TCPC IGMPD UDP36. If an application developer chooses ____ protocol, then the application process is almost directly talking with IP.A HTTPB RIPC CSMA/CDD UDP37. ____ maintains connection-state in the end systems. This connection state includes receive and send buffers, congestion-control parameters, and sequence and acknowledgment number parameters.A UDPB TCPC DNSD HTTP38. The host that initiates the session in the Internet is labeled as ____.A serverB user agentC clientD router39. With TCP there is no _____ between sending and receiving transport-layer entities.A flow controlB handshakingC. congestion control D VC setup40. The Internet’s ____service helps prevent the Internet from entering a state of gridlock.A datagramB congestion controlC sliding windowD timeout event41. Connection setup at the transport layer involves ____.A serverB only the two end systemsC clientD router42. A ____layer protocol provides for logical communication between applications.A transportB applicationC networkingD MAC43. In static congestion window, if it satisfies W*S/R > RTT + S/R, the Latency is ____.A W*S/R – ( RTT+ S/R)B 2RTT + O/RC 2RTT + O/R + (k-1)[W* S/R- (RTT + S/R)]D 2RTT + S/R44. The receive side of transport layer reassembles segments into messages, passes to ____layer.A ApplicationB NetworkingC PhysicalD MAC45. In the following four options, which one is correct?A The variations in the SampleRTT are smoothed out in the computation of the EstimatedRTTB The timeout should be less than the connection’s RTTC Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≥1 secD Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≤1 sec46. The port number used by HTTP is ____.A 80B 25C 110D 5347. The port number used by SMTP is ____.A 80B 25C 110D 5348. The port number used by pop3 is ____.A 80B 25C 110D 5349. The port number used by DNS is ____.A 80B 25C 110D 5350. The port number used by FTP is ____.A 20 and 21B 20C 21D 5351. A UDP socket identified by a ____ tuple(s).A 2B 4C 1D 352. A TCP socket identified by a ____ tuple(s).A 2B 4C 1D 353. A TCP socket does not include____.A Source MAC addressB Source port numberC Destination IP addressD Destination port number54. Which of following about UDP is not correct.A It is a reliable data transfer protocolB It is connectionlessC no handshaking between UDP sender, receiverD it is a best effort service protocol55. DNS uses ____ service.A TCPB UDPC Both TCP and UDPD None of above56. Which of following about UDP is correct?A Finer application-level control over what data is sent, and whenB No connection establishment (which can add delay), so no delay for establish a connectionC No connection state (so, UDP can typically support many active clients)D Large packet header overhead (16-B)57. Streaming media uses a ____ service normally.A TCPB UDPC Both TCP and UDPD None of above58. The UDP header has only ____ fields.A 2B 4C 1D 359. Which of the following does not included in UDP header.A Source port numberB Destination port numberC ChecksumD Sequence number60. Which of the following is not a pipelining protocol.A Rdt1.0B Go-Back-NC Selective repeatD TCP61. In the following four descriptions about MSS and MTU, which one is not correct?A The MSS is the maximum amount of application-layer data in the segmentB The MSS is the maximum size of the TCP segment including headersC The MSS is typically set by MTUD The MTU means the largest link-layer frame62. The job of gathering data chunks, encapsulating each data chunk with header information to create segments and passing the segments to the network is called ____.A multiplexingB de-multiplexingC forwardingD routing63. In the following four descriptions about the relationship between the transport layer and the network layer, which one is not correct?A The transport-layer protocol provides logical communication between hostsB The transport-layer protocol provides logical communication between processesC The services that a transport-layer protocol can provide are often constrained by the service model of the network-layer protocolD A computer network may make available multiple transport protocols64. Suppose the following three 8-bit bytes: 01010101, 01110000, 01001100. What’s the 1s complement of the sum of these 8-bit bytes?A 00010001B 11101101C 00010010D 1000100065. The following four descriptions about multiplexing and de-multiplexing, which one is correct?A A UDP socket is identified by a two-tuples consisting of a source port number and a destination port number.B If two UDP segment have different source port number, they may be directed to the same destination process.C If two TCP segments with different source port number, they may be directed to the same destination process.D If two TCP segments with same destination IP address and destination port number, they must be the same TCP connection.66. UDP and TCP both have the fields except ____.A source port numberB destination port numberC checksumD receive window67. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [nextseqnum,base+N-1] corresponds to packet that ____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged68. Which of the following about TCP is not correct?A It is a connectionless protocolB Point-to-point protocolC Reliable, in-order byte steam protocolD Pipelined protocol69. Which of the following about TCP is not correct?A It is a connectionless protocolB full duplex data transfer protocolC connection-oriented protocolD flow controlled protocol70. The maximum amount of data that can be grabbed and placed in a segment is limited by the ____.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum71. The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host (the so-called____), and then will fit into a single link-layer frame.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum72. The MSS is the maximum amount of ____layer data in the segment, not the maximum size of the TCP segment including headers.A ApplicationB TransportC NetworkingD Link73. Which of the following field is not used for connection setup and teardown?A Sequence numberB TSTC SYND FIN74. ____ is the byte stream number of first byte in the segment.A Sequence numberB ACK numberC ChecksumD port number75. ____ is the byte sequence numbers of next byte expected from other side.A Sequence numberB ACK numberC ChecksumD port number76. Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide ____ acknowledgements.B SelectiveC SingleD Negative77. Fast retransmit means in the case that ____ duplicate ACK-s are received, the TCP sender resend segment before timer expires.A 3B 4C 5D 678. TCP____ means sender won’t overflow receiver’s buffer by tran smitting too much, too fast.A Flow controlB Congestion controlC Reliable data transferD Connection-oriented service79. TCP provides flow control by having the sender maintain a variable called the ____.A Receive windowB Congestion windowC Sliding windowD buffer80. How does TCP sender perceive congestion?A TimeoutB 3 duplicate ACK-sC Both A and BD None of above81. Transport protocols run in ____.A ServersB ClientsC RoutersD End systems82. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers83. Which service does UDP not provide?B de-multiplexingC error-detectionD error-correction84. There are three major events related to data transmission and retransmission in the TCP sender, which one is not in it?A data received from application aboveB de-multiplexing segmentC timer timeoutD ACK receipt85. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP86. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection87. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection88. Which service helps prevent the internet from entering a state of gridlock?A reliable data transferB flow controlC congestion controlD handshaking procedure89. The Internet’s _____is responsible for moving packets from one host to another.A application layerB transport layerC network layerD link layer90.In the following applications, which one is a bandwidth-sensitive application?A E-mailB web applicationC real-time audioD file transfer91. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS92. In the following four descriptions, which one is correct?A If one host’s transport layer uses TCP, then its network layer must use virtual-circuit network.B Datagram network provides connection serviceC The transport-layer connection service is implemented in the routerD The network-layer connection service is implemented in the router as well as in the end system.93.____ is a speeding-matching service---matching the rate which the sender is sending against the rate at which the receiving application is reading.A congestion controlB flow controlC sliding-window controlD variable control94. In the following four descriptions about Rcv-Window, which one is correct?A The size of the TCP RcvWindow never changes throughout the duration of the connectionB The size of the TCP RcvWindow will change with the size of the TCP RcvBufferC The size of the TCP RcvWindow must be less than or equal to the size of the TCP RcvBufferD Suppose host A sends a file to host B over a TCP connection, the number of unacknowledged bytes that A sends cannot exceed the size of the size of the RcvWindow.95. There are 6 flag fields. Which one is to indicate that the receiver should pass the data to the upper layer immediately?A PSHB URGC ACKD RST96. Suppose the TCP receiver receives the segment that partially or completely fills in gap in received data, it will ____.A immediately send ACKB immediately send duplicate ACKC wait some time for arrival of another in-order segmentD send single cumulative97. _____ imposes constrain on the rate at which a TCP sender can send traffic into the network.A sliding windowB congestion windowC receive windowD variable window98. Flow control and congestion control are same at that they all limit the rate of the sender, but differ in that ____.A flow control limits its rate by the size of RcvWindow, but congestion control by the traffic on the linkB congestion control limits its rate by the size of RcvWindow, but flow control by the traffic on the linkC flow control mainly is accomplished by the sender, but congestion control by the receiver.D flow control mainly is accomplished by the receiver, but congestion control bythe link.99. This job of delivering the data in a transport-layer segment to the correct socket is called ____.A multiplexingB de-multiplexingC forwardingD routing100. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [base, nextseqnum-1] corresponds to packet that____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged101. ____ are the two types of transport services that the Internet provides to the applications.A TCP and UDPB connection-oriented and connectionless serviceC TCP and IPD reliable data transfer and flow control102. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a responseB Each TCP connection is closed after the server sending one objectC There are two versions of persistent connection: without pipelining and with pipeliningD The default mode of HTTP uses persistent connection with pipelining103. The field of Length in UDP segment specifies the length of ____.A the UDP segment, not including the headerB the UDP segment, including the headerC the UDP segment’s headerD the Length field104. In TCP segment header, which field can implement the reliable data transfer?A source port number and destination port numberB sequence number and ACK numberC urgent data pointerD Receive window105. In the following four descriptions about TCP connection management, which one is not correct?A Either of the two processes participating in a TCP connection can end the connectionB If the FIN bit is set to 1, it means that it wants to close the connectionC In the first two step of the three-way handshake, the client and server randomly choose an initial sequence numberD In the three segments of the three-way handshake, the SYN bit must be set to 1 106. Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 42, and the second has sequence number 110. If the 1st is lost and 2nd arrives at host B. What will be the acknowledgment number?A 43B ACK42C 109D ACK1101.Consider sending an object of size O=500,000bytes from server to client. LetS=500 bytes and RTT=0.2s. Suppose the transport protocol uses static windows with window size 5. For a transmission rate of 100Kbps, determine the latency for sending the whole object. Recall the number of windows K=O/ WS), and there is K-1 stalled state (that is idle time gaps).2.Consider the following plot of TCP congestion window size as a function of time.Fill in the blanks as follow:a) The initial value of Threshold at the first transmission round is ____. b) The value of Threshold at the 11st transmission round is ____. c) The value of Threshold at the 21st transmission round is ____. d) After the 9th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKe) After the 19th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKf) During ____ transmission round, the 18th segment is sent.3.Consider the TCP reliable data transfer in the given graph. If in Segment 1’s Sequence number =10,data=“AC”, please fill in the following blanks. a) In Segment 2, ACK number=____;b) In Segment 3, Sequence number =____; data=“0123456789”c) If there are some bits corrupted in segment 3 when it arrives Host B, then the ACK number in Segment 5 is ____; and the ACK number in Segment 6 is ____.0 00 Congestion window sizeTransmission round4. The client A wants to request a Web page from Server B. Suppose the URL of the page is 172.16.0.200/experiment, and also it wants to receive French version of object. The time-sequence diagram is shown below, please fill in the blanks.Packet① to Packet③are TCP connection’s segment, then:Packet ①: SYN flag bit= aACK flag bit= bSequence number= 92Packet ②: SYN flag bit=1ACK flag bit= c Sequence number=100 Packet ③: SYN flag bit= d ACK flag bit=1Sequence number= e5. Consider sending an object of size O=100 Kbytes from server to client. Let S=536 bytes and RTT=100msec. Suppose the transport protocol uses static windows with window size W.(1) For a transmission rate of 25 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency.(2) Repeat (1) for 100 kbps.6. Consider the following plot of TCP congestion window size as a function of time. Please fill in the blanks as below.a) The initial value of Threshold at the first transmission round is____. b) The value of Threshold at the 11th transmission round is_____. c) The value of Threshold at the 21st transmission round is_____.Congestion window sizeTransmission roundd) After the 9th transmission round, _____ occurs.e) After the 19th transmission round, ____ are detected.。
计算机组成与体系结构英文版课后练习题含答案
Chapter 1 - Introduction
Exercise 1.1
What are the three mn functions of a computer?
What is the purpose of the control unit?
Answer:The purpose of the control unit is to control the flow of data and instructions within the CPU.
Exercise 4.2
Chapter 5 - Memory Organization
Exercise 5.1
What is the difference between RAM and ROM?
Answer:RAM (Random Access Memory) is volatile memory that can be read from and written to. ROM (Read-Only Memory) is non-volatile memory that can only be read.
What is the difference between a RISC and a CISC processor?
Answer:A RISC (Reduced Instruction Set Computer) processor has a simplified instruction set with fewer instructions that are executed more quickly. A CISC (Complex Instruction Set Computer) processor has a more complex instruction set with more instructions that can perform complex operations in a single instruction.
浙大研究生 2017-2018学年《计算机理论》期末考试英文版及答案

浙江大学2017-2018学年秋冬学期《计算理论》课程期末考试试卷课程号:21120520开课学院:计算机学院考试试卷: A卷 B卷考试形式: 闭卷 开卷,允许带入场考试日期:2018年1月24日,考试时间:120分钟诚信考试,沉着应考,杜绝违纪考生姓名学号所属院系题序123456总分得分评卷人Zhejiang UniversityTheory of Computation,Fall-Winter2017Final Exam1.(24pts)Determine whether the following statements are true or false.Ifit is truefill a T otherwise a F in the bracket before the statement.(a)()Let A,B be two languages.If both A and A∪B are regular,then B isdefinitely regular.(b)()If A is regular and B is non-regular,then A◦B must be non-regular.(c)()Language{xcy|x,y∈{a,b}∗,|x|≤|y|≤3|x|}is context-free.(d)()Every regular language can be generated by a context-free grammar.(e)()If A is recursive and B⊆A,then B is recursive as well.(f)()Recursively enumerable languages are always infinite.(g)()There’s a functionφsuch thatφcan be computed by some Turing ma-chines,yetφis not a primitive recursive function.(h)()Let A and B be recursively enumerable languages and A∩B=∅.If A∪Bis also recursively enumerable,then both A and B is decidable.(i)()The language{“M”“w”|TM M accepts w in less than2018steps}isrecursive.(j)()The language{“M”|TM M accepts exactly2018strings}is recursively enumerable but not recursive.(k)()Let H e={“M”|TM M halts on e}.If H e≤L,then L is recursive enumerable but not recursive.(l)()A language L is recursive if and only if it is Turing-enumerable.2.(18pts)On FA and Regular LanguagesSay whether each of the following languages is regular or not regular?Prove your answers,where{a,b}+={a,b}∗◦{a,b}.(a)L1={wtw|w,t∈{a,b}+}(b)L2={wtw|w,t∈{a,b}∗}3.(20pts)On PDA and Context-Free LanguagesLet L3={ww R ca m b n|w∈{a,b}∗,m,n∈N,m=n}.(a)Construct a context-free grammar that generates the language L3.(b)Construct a pushdown automata that accepts L3.Solution:(a)(b)The PDA M=(K,Σ,Γ,∆,s,F)is defined below:(q,σ,β)(p,γ)K=Σ={a,b,c}Γ=s=F=4.(10pts)On Turing MachineDesign a single tape Turing machine M that decides the language L4L4={uvcww R|u,v,w∈{a,b}∗,|u|=2|v|}When describing the Turing machines above,you can use the elementary Turing machines described in textbook.Always assume that your Turing machine starts from the configuration◃⊔x,where x is the input string.5.(10pts)On Primitive Recursive Function→N,and k∈N,k≥2 Show the following functionφk:N×N×···×Nk{n1,n2,···,n k}φk(n1,n2,···,n k)=maxkis primitive recursive.6.(18pts)On UndecidabilityClassify whether each of the following languages are recursive,recursively enumerable but not recursive,or non-recursively enumerable.Prove your answers,but you may not simply appeal to Rice’s theorem.(a)L5={“M”|M is a TM,and L(M)is uncountable}(b)L6={“M”|TM M accepts at least two strings of different lengths}Enjoy Your Spring Festival!。
英文版计算机试题库及答案

英文版计算机试题库及答案English Version of Computer Test Bank and AnswersIn today's interconnected world, computer literacy is of utmost importance. Aspiring computer professionals should possess not only theoretical knowledge but also practical skills. To aid in the assessment of such competencies, an English version of the computer test bank, along with comprehensive answers, has been developed.Introduction: The Importance of a Computer Test BankA computer test bank serves as a valuable resource for both teachers and students. It provides a collection of carefully curated questions that cover various topics in computer science and information technology. This enables instructors to assess the depth of understanding and problem-solving abilities of their students while allowing learners to gauge their own proficiency.The Purpose of an English VersionWith the increasing global demand for computer professionals, it is essential to have a standardized assessment tool that can be easily accessed and understood by individuals with different linguistic backgrounds. Thus, the development of an English version of the computer test bank aims to facilitate international exchange and provide a standardized evaluation of computer skills worldwide.Features of the English Version Computer Test Bank1. Inclusive Question Categories: The computer test bank covers a broad range of categories, including programming languages, algorithms, databasemanagement, computer networks, cybersecurity, software engineering, and more. This ensures a comprehensive evaluation of the test-takers' knowledge.2. Multiple Difficulty Levels: The questions in the test bank are categorized into different difficulty levels, such as beginner, intermediate, and advanced. This allows users to select questions that align with their skill level and progressively enhance their understanding.3. Real-world Scenarios: Many questions in the test bank are designed to simulate real-world scenarios, requiring critical thinking and problem-solving skills. This approach helps to bridge the gap between theoretical knowledge and practical application.4. Comprehensive Answer Key: Alongside the test bank, a detailed answer key is provided, offering step-by-step explanations and solutions. This ensures that users not only know the correct answer but also understand the reasoning behind it, fostering deeper comprehension.Benefits of the English Version Computer Test Bank1. Global Standardization: The English version of the computer test bank establishes a global standard for evaluating computer proficiency. Institutions from various countries can adopt the same assessment tool, allowing for accurate comparisons on an international scale.2. Enhancing Teaching: For educators, the test bank serves as an invaluable resource to prepare classroom assessments and track students' progress. It offers a wide range of questions that can be tailored to specific course objectives, facilitating effective teaching methodologies.3. Personal Skill Enhancement: Test bank users can self-administer quizzes to evaluate their understanding, identify knowledge gaps, and focus on areas that require improvement. By regularly practicing with the test bank, individuals can enhance their overall computer skills.4. Career Advancement: The English version of the computer test bank serves as a reliable certification of computer proficiency, augmenting one's resume and potential job prospects. Employers can trust the standardized assessment results, simplifying the hiring process.ConclusionThe availability of the English version of the computer test bank and its accompanying answer key is a significant step forward in standardizing computer proficiency evaluation. Whether used by educators, students, or professionals, it contributes to the enhancement of computer literacy worldwide. By adopting this comprehensive assessment tool, individuals can strengthen their computer skills and open doors to rewarding opportunitiesin the ever-evolving field of technology.。
(完整版)计算机网络课后作业以及答案(中英文对照)

Chapter11-11.What are two reasons for using layered protocols?(请说出使用分层协议的两个理由)答:通过协议分层可以把设计问题划分成较小的易于处理的片段。
分层意味着某一层的协议的改变不会影响高层或低层的协议。
1-13. What is the principal difference between connectionless communication and connection-oriented communication?(在无连接通信和面向连接的通信两者之间,最主要的区别是什么?)答:主要的区别有两条。
其一:面向连接通信分为三个阶段,第一是建立连接,在此阶段,发出一个建立连接的请求。
只有在连接成功建立之后,才能开始数据传输,这是第二阶段。
接着,当数据传输完毕,必须释放连接。
而无连接通信没有这么多阶段,它直接进行数据传输。
其二:面向连接的通信具有数据的保序性,而无连接的通信不能保证接收数据的顺序与发送数据的顺序一致。
1-20. A system has an n-layer protocol hierarchy. Applications generate messages of length M bytes. At each of the layers, an h-byte header is added. What fraction of the network bandwidth is filled with headers?(一个系统有n层协议的层次结构。
应用程序产生的消息的长度为M字节。
在每一层上需要加上一个h字节的头。
请问,这些头需要占用多少比例的网络带宽)答:hn/(hn+m)*100%1-28. An image is 1024 x 768 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps Ethernet? Over 100-Mbps Ethernet?(一幅图像的分辨率为1024 x 768像素,每个像素用3字节来表示。
计算机专业英语模拟试题附参考答案

计算机专业英语模拟试题一参考答案一、词汇(选择一个最合适的词汇,将对应的英文字母填入空格内。
每题1分,共10分)1、 B refers to the parts of the computer that you can see and touch.A. SoftwareB. HardwareC. HardshipD. Instruction2、primary memory which is stored on chips located A .A. on the motherboardB. outsideC. inside the processorD. on the CPU3、The display screen is the most common C device used to show you what the computer is doing.A. inputB. printingC. outputD. electronic4、Windows gives you more control over the A you work.A. operationB. wayC. energyD. power5、The most important program on any computer is A .A. Operating SystemB. VirusC. softwareD. Office 20006、There are D separate products that form the Windows 2000。
A. only oneB. twoC. threeD. four7、C might best be D as a 'medium-level language'.A. developedB. decodedC. programmedD. described8、Anti-Virus protects your computer from viruses by C your computer's memory and disk devices.A. deletingB. changingC. scanningD. replacing9、Multimedia will become increasingly D throughout every aspect of our lives.A. passB. preciseC. permitD. pervasive10、Communication through the Internet, the C performs the reverse function.A. A station controller (STACO)B. DTEC. Data communications equipment (DCE)D. CRT二、语法——单项选择题(每小题1.5分,共15分)1、The girl I saw D brown hair and blue eyes.A. had sheB. she hadC. herD. had2、I didn't hear the phone last night, I D asleep.A. must beB. must have beenC. should beD. should have been3、He was glad to find the fire A brightly.A. burningB. burnedC. to bumD. have bum4、Though D by what he said ,she didn't believe in him.A. attractingB. she attractedC. attractedD. have been attracted5、 D that ,I could do it much better.A. If I doB. If I were doC. Were I to doD. Were I do6、It was in this very place A I bought the laser printer.A. whereB. whenC. in whichD. that7、He is old enough to tell right C wrong.A. ofB. inC. fromD. to8、 A he did was quite wrong.A. WhatB. ThatC. IfD. Which9、 C , we missed our plane.A. The train being lateB. To be lateC. The train is being lateD. The train which is late10、I wish that I C the concert last night.A. couldB. have attendedC. could have attendedD. attended三、多选(每小题2分,共20分)1、Windows 2000 is abda. new lease of Windows c. the same as Windows NTb. an inventive technology d. used for building a scalable network2、C++ is abc .a. object-oriented c. extended from Cb. procedure-oriented d. a superset of C3、Office automation is ad .a. the application of computer c. communications technologyb. the computer d. used to improve the productivity of people4、Microsoft Office Professional 2000 include abcd .a. Word 2000 c. Excel 2000b. PowerPoint 2000 d. Outlook 20005、Types of media include abd .a. text c. animationb. full-motion video d. audio6、Modem is c .a. a modulator c. a modulator/demodulatorb. a demodulator d. a data set7、The Internet is acd .a. as a common internet c. constrained by a set of IP suiteb. a specific kind of internet d. defined as the network of networks8、Viruses can delay their attack for abcd .a. daysb. weeksc. monthsd. years9、The attributes of the stack are b .a. FIFO c. queueb. LIFO d. built into their circuitry10、With an Internet connection you can get some of the basic services available are:abcda. E-mailb. Telnetc. FTPd. Usenet news四、完形填空(选择一个最合适的答案,将对应的英文字母填入空格内。
计算机英语考试试题以及答案
计算机英语考试试题以及答案一、词汇(选择一个最合适的词汇,将对应的英文字母填入空格内。
每题2分,共20分)1、__B__ is used to communicate with another computer over telephone lines.A. keyboardB. modemC. mouseD. printer2、__C__ is a device that enables the computer to handle sounds.A. network cardB. video cardC. sound cardD. monitor3、__A__ is a word processing tool that helps you to create quality documents.A. Word 2000B. Outlook 2000C. Access 2000D. Excel 20004、__D__ is a fast and powerful operating system, based on the UNIX O.S.A. Windows 2000B. Office 2000C. Windows 98D. Linux5、The OSI model has __D__ layers.A. fourB. fiveC. sixD. seven6、The purpose of the __A__ is to provide fully integrated analog services to users.A. ISDNB. WWWC. FTPD. HTTP7、Which one is not a computer languages? __A__A. word 2000B. PASCALC. CD. C++8、The __C__ turns the object file into an executable program.A. linkerB. compilerC. interpreterD. computer9、The RGB value is composed of__C __components.A. oneB. twoC. threeD. four10、Virus is a __A__ .A. programB. computerC. bad manD. beast二、语法单项选择题(每小题1.5分,共15分)1、With Windows, you can run several powerful applications at once and switch quickly __B__ them.A. betweenB. amongC. inD. on2、He doesnt mind __A__ her birthday party.A. being not invited toB. not to be invited toC. not being invited toD. not inviting to3、Only when you have told him __A__ take this book out of the library.A. can youB. would youC. you willD. you can4、Well go to Paris for our holiday, __D __it isnt too expensive.A. exceptB. providedC. so far asD. unless15、The prisoners request __B__ more and better food is now__B__ consideration(考虑).A. for, onB. for, underC. for, inD. for, into6、Mrs. Snow __B__ in the office for two years before she got a raise.A. have been workingB. had been workingC. has been workingD. was working7、The teacher has repeatedly reminded him __C__ it.A. ofB. forC. withD. to8、You went to the wrong shop .You ought __D__ to the shop next to the cinema.A. goB. to goC. have goneD. to have gone9、After __C__ my lessons I went to bed.A. reviewB. to reviewC. reviewingD. be reviewing10、 I find __A__ not so difficult to learn a foreign language.A. itB. thatC. theyD. which三、多选(每小题1.5分,共15分)1、Input devices include: __abcd__ .a. the keyboard c. the mouseb. touch screen d. microphone2、A processor is composed of: __abcd __.a. a control unit c. an arithmeticb. logic unit d. Registers3、The Windows 2000 product line includes __abcd __.a. Windows 2000 Professional c. Windows 2000 Advanced Serverb. Windows 2000 Server d. Windows 2000 Datacenter Server4、Windows 2000s advantages are lies in the sections that follow: __abcd__a. Active Directory c. Networkingb. Storage d. Enterprise Management5、C++ include the following pillars: __abcd__ .a. encapsulation c. inheritanceb. data hiding d. polymorphism6、The major functional components of an office automation system include: __abcd__ .a. text processing c. electronic mailb. information storage and retrievald. personal assistance features7、Static graphics include __cd__ .a. movies c. pictures2b. animators d. photographs8、The end equipment in a communication system includes __acd__a. computers c. CRTsb. DCE d. keyboards9、Applications in the Internet can be found everywhere: __abc__a. in libraries c. at homeb. in conference rooms d. at the moon10、Many viruses do harmful things such as __abcd__ .a. deleting files c. simulating typosb. changing random data on your disk d. slowing your PC down四、完形填空(选择一个最合适的答案,将对应的英文字母填入空格内。
计算机专业英语考试试题及答案
计算机专业英语考试试题及答案一、选择题1. Which of the following is NOT a programming language?A. JavaB. PythonC. HTMLD. CSS2. What does the acronym "SQL" stand for?A. Structured Query LanguageB. Simple Query LanguageC. Script Query LanguageD. Secure Query Language3. Which protocol is commonly used for sending and receiving emails?A. FTPB. HTTPC. SMTPD. TCP4. What does the term "CPU" refer to?A. Central Processing UnitB. Computer Processing UnitC. Central Program UnitD. Computer Program Unit5. Which of the following is NOT a type of network topology?A. StarB. RingC. MeshD. Scroll二、填空题1. HTML stands for Hypertext Markup Language, which is used for ____________.2. The process of converting source code into machine code is called ____________.3. IP address stands for ____________.4. The act of copying files from a remote server to a local computer is known as ____________.5. The programming language developed by Apple Inc. for iOS and macOS is ____________.三、简答题1. What is the difference between a compiler and an interpreter? Provide examples of programming languages that use each of these methods.2. Explain the concept of object-oriented programming (OOP) and provide an example of a programming language that utilizes this paradigm.3. Describe the client-server model and provide an example of a commonly used protocol within this model.四、论述题Discuss the impact of artificial intelligence (AI) on various industries. Provide examples of how AI is being used in fields such as healthcare, finance, and transportation. Analyze the potential benefits and challenges of implementing AI in these industries.答案:一、选择题1. C. HTML2. A. Structured Query Language3. C. SMTP4. A. Central Processing Unit5. D. Scroll二、填空题1. creating and structuring the content of a webpage2. compilation3. Internet Protocol4. downloading5. Swift三、简答题1. A compiler translates the entire source code into machine code before the program is executed. Examples of languages that use compilers are C, C++, and Java. On the other hand, an interpreter translates and executes the source code line by line. Python and Ruby are examples of languages that use interpreters.2. Object-oriented programming (OOP) is a programming paradigm that organizes data and functions into reusable objects. It focuses on the concept of classes and objects, allowing for code reuse and encapsulation. An example of a programming language that uses OOP is Java, where objects are instances of classes and can interact with each other through methods and attributes.3. The client-server model is a distributed computing architecture wherea server provides services or resources to multiple clients. The clients request and receive these resources through the network. An example of a commonly used protocol within this model is the Hypertext Transfer Protocol (HTTP), which is used for communication between web browsers (clients) and web servers.四、论述题Artificial intelligence (AI) has had a significant impact on various industries. In healthcare, AI is being used for diagnoses and treatments, analyzing medical images, and personalized medicine. For example, AI-powered algorithms can help detect diseases like cancer at an early stage, leading to better treatment outcomes. In finance, AI is utilized for fraud detection, algorithmic trading, and customer service. AI algorithms can analyze large amounts of financial data to identify patterns and make accurate predictions. In transportation, AI is being employed for autonomous vehicles, traffic management, and logistics optimization. Self-driving cars, for instance, use AI algorithms to navigate and make decisions on the road.The implementation of AI in these industries brings about many benefits, such as increased efficiency, improved accuracy, and cost savings. AI systems can process and analyze vast amounts of data much faster than humans, leading to faster and more accurate results. However, there are also challenges to consider. Privacy and security concerns arise as AI systems handle sensitive information. There is also the worry of job displacement, as AI automation may replace certain human tasks. Additionally, ethical considerations need to be addressed, such as bias in algorithms and the potential for AI to be used for malicious purposes.Overall, the impact of AI on various industries is undeniable. It has the potential to revolutionize healthcare, finance, transportation, and many other sectors. However, careful implementation and regulation are necessary to ensure its responsible and beneficial use.。
计算机专业英语教程第四版翻译课后练习题含答案
计算机专业英语教程第四版翻译课后练习题含答案简介《计算机专业英语教程》是针对计算机专业学生编写的一本英语教材。
本书旨在帮助学生通过学习计算机领域的专业英语词汇和语法,提升他们的英语能力和技能。
本文将为读者提供该教材第四版的课后练习题及答案。
第一课练习题1.将下列单词从易到难排序:chip, computer, algorithm, software,desktop2.将下列单词从中文翻译为英文:程序设计,硬件,操作系统,输入,输出3.请解释下列缩略语的全称:RAM,CPU,OS答案1.desktop, chip, computer, software, algorithm2.programming, hardware, operating system, input, output3.RAM(Random Access Memory),CPU(Central Processing Unit),OS(Operating System)第二课练习题1.请翻译下列句子:计算机的功能越来越强大,它可以执行许多任务。
2.请解释下列单词的意思:interface,protocol,server,router答案puters are becoming more and more powerful and they canperform many tasks.2.interface(接口), protocol(协议),server(服务器),router(路由器)第三课练习题1.请将下列单词按字母顺序排列:database,file,program,server,storage2.请填写下列句子的空格:计算机会读取从硬盘 __ (into)内存。
3.请解释下列单词的意思:database,algorithm,client,browser答案1.algorithm,database,file,program,server,storage2.into3.database(数据库),algorithm(算法),client(客户端),browser(浏览器)第四课练习题1.请翻译下列句子:今天我学会了如何编写计算机程序。
计算机网络英文题库(附答案)chapter5
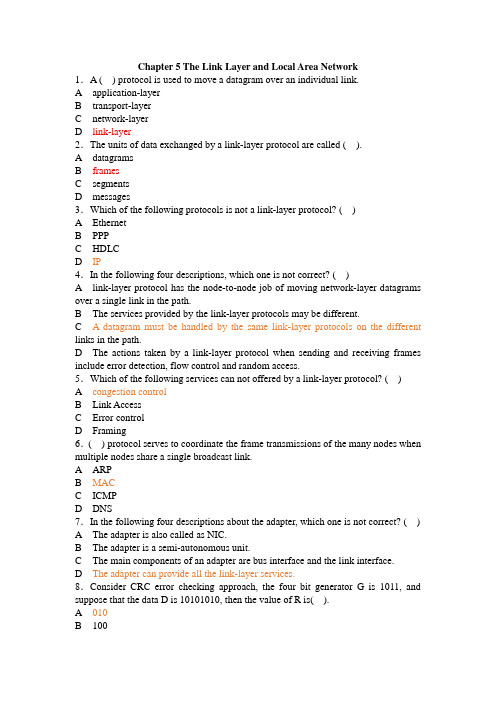
Chapter 5 The Link Layer and Local Area Network1.A ( ) protocol is used to move a datagram over an individual link.A application-layerB transport-layerC network-layerD link-layer2.The units of data exchanged by a link-layer protocol are called ( ).A datagramsB framesC segmentsD messages3.Which of the following protocols is not a link-layer protocol? ( )A EthernetB PPPC HDLCD IP4.In the following four descriptions, which one is not correct? ( )A link-layer protocol has the node-to-node job of moving network-layer datagrams over a single link in the path.B The services provided by the link-layer protocols may be different.C A datagram must be handled by the same link-layer protocols on the different links in the path.D The actions taken by a link-layer protocol when sending and receiving frames include error detection, flow control and random access.5.Which of the following services can not offered by a link-layer protocol? ( )A congestion controlB Link AccessC Error controlD Framing6.( ) protocol serves to coordinate the frame transmissions of the many nodes when multiple nodes share a single broadcast link.A ARPB MACC ICMPD DNS7.In the following four descriptions about the adapter, which one is not correct? ( )A The adapter is also called as NIC.B The adapter is a semi-autonomous unit.C The main components of an adapter are bus interface and the link interface.D The adapter can provide all the link-layer services.8.Consider CRC error checking approach, the four bit generator G is 1011, and suppose that the data D is 10101010, then the value of R is( ).A 010B 100C 011D 1109.In the following four descriptions about random access protocol, which one is not correct? ( )A I n slotted ALOHA, nodes can transmit at random time.B I n pure ALOHA, if a frame experiences a collision, the node will immediately retransmit it with probability p.C T he maximum efficiency of a slotted ALOHA is higher than a pure ALOHA.D I n CSMA/CD, one node listens to the channel before transmitting.10.In the following descriptions about MAC address, which one is not correct? ( )A T he MAC address is the address of one node’s adapter.B N o two adapters have the same MAC address.C T he MAC address doesn’t change no matter where the adapter goes.D M AC address has a hierarchical structure.11.The ARP protocol can translate ( ) into ( ). ( )A h ost name, IP addressB h ost name, MAC addressC I P address, MAC addressD broadcast address, IP address12.The value of Preamble field in Ethernet frame structure is ( )A 10101010 10101010……10101010 11111111B 10101011 10101011……10101011 10101011C 10101010 10101010……10101010 10101011D 10101010 10101010……10101010 1010101013.There are four steps in DHCP, the DHCP server can complete ( ).A DHCP server discoveryB DHCP server offersC DHCP requestD DHCP response14.In CSMA/CD, the adapter waits some time and then returns to sensing the channel. In the following four times, which one is impossible? ( )A 0 bit timesB 512 bit timesC 1024 bit timesD 1028 bit times15.The most common Ethernet technologies are 10BaseT and 100BaseT. “10” and “100” indicate( ).A the maximum length between two adaptersB the minimum length between two adaptersC the transmission rate of the channelD the transmission rate of the node16.The principal components of PPP include but not( ).A framingB physical-control protocolC link-layer protocolD network-layer protocol17.In the following four options, which service can not be provided by switch? ( )A filteringB self-learningC forwardingD optimal routing18.In the following four services, which one was be required in PPP? ( )A packet framingB error detectionC error correctionD multiple types of link19.The ability to determine the interfaces to which a frame should be directed, and then directing the frame to those interfaces is( ).A filteringB forwardingC self-learningD optimal routing20.In ( ) transmission(s), the nodes at both ends of a link may transmit packets at the same time.A full-duplexB half-duplexC single-duplexD both full-duplex and half-duplex21.Consider the data D is 01110010001, if use even parity checking approach, the parity bit is( ① ), if use odd parity checking approach, the parity bit is( ② ). ( )A ①0 ②1B ①0 ②0C ①1 ②1D ①1 ②022.In the following four descriptions about parity checks, which one is correct? ( )A Single-bit parity can detect all errors.B Single-bit parity can correct one errors.C Two-dimensional parity not only can detect a single bit error, but also can correct that error.D Two-dimensional parity not only can detect any combination of two errors, but also can correct them.23.MAC address is ( ) bits long.A 32B 48C 128D 6424.Wireless LAN using protocol ( ).A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.1125.The following protocols are belonging to multiple access protocols except for ( ).A channel partitioning protocolsB routing protocolsC random access protocolsD taking-turns protocols26.Which of the following is not belonging to channel partitioning protocols? ( )A CSMAB FDMC CDMAD TDM27.In the following four descriptions about CSMA/CD, which one is not correct? ( )A A node listens to the channel before transmitting.B If someone else begins talking at the same time, stop talking.C A transmitting node listens to the channel while it is transmitting.D With CSMA/CD, the collisions can be avoided completely.28.( ) provides a mechanism for nodes to translate IP addresses to link-layer address.A IPB ARPC RARPD DNS29.A MAC address is a ( )address.A physical-layerB application-layerC link-layerD network-layer30.Which of the following is correct? ( )A No two adapters have the same MAC address.B MAC broadcast address is FF-FF-FF-FF-FF-FF.C A portable computer with an Ethernet card always has the same MAC address, no matter where the computer goes.D All of the above31.In the following four descriptions, which one is not correct? ( )A ARP resolves an IP address to a MAC address.B DNS resolves hostnames to IP addresses.C DNS resolves hostnames for hosts anywhere in the Internet.D ARP resolves IP addresses for nodes anywhere in the Internet.32.In the LAN, ( )protocol dynamically assign IP addresses to hosts.A DNSB ARPC DHCPD IP33.DHCP protocol is a four-step process: ①DHCP request. ②DHCP ACK. ③DHCP server discovery. ④DHCP server offer(s). The correct sequence is ( )A ①②③④B ③②①④C ③④①②D ①④③②34.In the Ethernet frame structure, the CRC field is ( )bytes.A 2B 4C 8D 3235.In the Ethernet frame structure, the Data field carries the ( ).A IP datagramB segmentC frameD message36.In the following four descriptions, which one is not correct? ( )A Ethernet uses baseband transmission.B All of the Ethernet technologies provide connection-oriented reliable service to the network layer.C The Ethernet 10Base2 technology uses a thin coaxial cable for the bus.D The Ethernet 10BaseT technology uses a star topology.37.Ethernet’s multiple access protocol is ( ).A CDMAB CSMA/CDC slotted ALOHAD token-passing protocol38.In the following four descriptions about CSMA/CD, which one is not correct? ( )A An adapter may begin to transmit at any time.B An adapter never transmits a frame when it senses that some other adapter is transmitting.C A transmitting adapter aborts its transmission as soon as it detects that another adapter is also transmitting.D An adapter retransmits when it detects a collision.39.Which of the following descriptions about CSMA/CD is correct? ( )A No slots are used.B It uses carrier sensing.C It uses collision detection.D All of the above.40.The Ethernet 10BaseT technology uses( )as its physical media.A fiber opticsB twisted-pair copper wireC coaxial cableD satellite radio channel41.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( )meters.A 100B 200C 500D 1042.A ( )is a physical-layer device that acts on individual bits rather than on frames.A switchB hubC routerD gateway43.A hub is a ( )device that acts on individual bits rather than on frames.A physical-layerB link-layerC network-layerD ransport-layer44.A switch is a( )device that acts on frame.A physical-layerB link-layerC network-layerD transport-layer45.In the following four descriptions, which one is not correct? ( )A Switches can interconnect different LAN technologies.B Hubs can interconnect different LAN technologies.C There is no limit to how large a LAN can be when switches are used to interconnect LAN segments.D There is restriction on the maximum allowable number of nodes in a collision domain when hubs are used to interconnect LAN segments.46.The ability to determine whether a frame should be forwarded to some interface or should just be dropped is ( ).A f ilteringB f orwardingC s elf-learningD o ptimal routing47.Which of the following devices is not a plug and play device? ( )A hubB routerC switchD repeater48.Which of the following devices is not cut-through device? ( )A hubB routerC switchD repeater49.In the following four descriptions, which one is not correct? ( )A Switches do not offer any protection against broadcast storms.B Routers provide firewall protection against layer-2 broadcast storms.C Both switches and routers are plug and play devices.D A router is a layer-3 packet switch, a switch is a layer-2 packet switch. 50.Which device has the same collision domain? ( )A HubB SwitchC RouterD Bridge51.IEEE802.2 protocol belong to ( )layerA networkB MACC LLCD physical52.IEEE802.11 protocol defines ( )rules.A Ethernet BusB wireless WANC wireless LAND Token Bus53.In data link-layer, which protocol is used to share bandwidth? ( )A SMTPB ICMPC ARPD CSMA/CD54.When two or more nodes on the LAN segments transmit at the same time, there will be a collision and all of the transmitting nodes well enter exponential back-off, that is all of the LAN segments belong to the same( ).A collision domainB switchC bridgeD hub55.( )allows different nodes to transmit simultaneously and yet have their respective receivers correctly receive a sender’s encoded data bits.A CDMAB CSMAC CSMA/CDD CSMA/CA56.Because there are both network-layer addresses (for example, Internet IPaddresses) and link-layer addresses (that is, LAN addresses), there is a need to translate between them. For the Internet, this is the job of ( ).A RIPB OSPFC ARPD IP57.PPP defines a special control escape byte, ( ). If the flag sequence, 01111110 appears anywhere in the frame, except in the flag field, PPP precedes that instance of the flag pattern with the control escape byte.A 01111110B 01111101C 10011001D 1011111058.The device ( ) can isolate collision domains for each of the LAN segment.A modemB switchC hubD NIC59.In the following four descriptions about PPP, which one is not correct? ( )A PPP is required to detect and correct errors.B PPP is not required to deliver frames to the link receiver in the same order in which they were sent by the link sender.C PPP need only operate over links that have a single sender and a single receiver.D PPP is not required to provide flow control.60.In the PPP data frame, the( ) field tells the PPP receivers the upper-layer protocol to which the received encapsulated data belongs.A flagB controlC protocolD checksum61.PPP’s link-control protocols (LCP) accomplish ( ).A initializing the PPP linkB maintaining the PPP linkC taking down the PPP linkD all of the above62.The PPP link always begins in the ( ) state and ends in the ( ) state. ( )A open, terminatingB open, deadC dead, deadD dead, terminating63.For( ) links that have a single sender at one end of the link and a single receiver at the other end of the link.A point-to-pointB broadcastC multicastD all of the above64.With ( )transmission, the nodes at both ends of a link may transmit packets at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous65.With ( ) transmission, a node can not both transmit and receive at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous66.Which of the following functions can’t be implemented in the NIC? ( )A encapsulation and decapsulationB error detectionC multiple access protocolD routing67.Which of the following four descriptions is wrong? ( )A The bus interface of an adapter is responsible for communication with the adapter’s parent node.B The link interface of an adapter is responsible for implementing the link-layer protocol.C The bus interface may provide error detection, random access functions.D The main components of an adapter are the bus interface and the link interface. 68.For odd parity schemes, which of the following is correct? ( )A 011010001B 111000110C 110101110D 00011011069.( )divides time into time frames and further divides each time frame into N time slots.A FDMB TMDC CDMAD CSMA70.With CDMA, each node is assigned a different ( )A codeB time slotC frequencyD link71.Which of the following four descriptions about random access protocol is not correct? ( )A A transmission node transmits at the full rate of the channelB When a collision happens, each node involved in the collision retransmits at once.C Both slotted ALOHA and CSMA/CD are random access protocols.D With random access protocol, there may be empty slots.72.PPP defines a special control escape byte 01111101. If the data is b1b201111110b3b4b5, the value is( )after byte stuffing.A b1b20111110101111110b3b4b5B b1b20111111001111101b3b4b5C b5b4b30111111001111101b2b1D b5b4b30111110101111110b2b173.MAC address is in ( ) of the computer.A RAMB NICC hard diskD cache74.Which of the following is wrong? ( )A ARP table is configured by a system administratorB ARP table is built automaticallyC ARP table is dynamicD ARP table maps IP addresses to MAC addresses75.NIC works in ( )layer.A physicalB linkC networkD transport76.In LAN, if UTP is used, the common connector is( ).A AUIB BNCC RJ-45D NNI77.The modem’s function(s) is(are) ( ).A translates digital signal into analog signalB translates analog signal into digital signalC both translates analog signal into digital signal and translates digital signal into analog signalD translates one kind of digital signal into another digital signal78.( )defines Token-Ring protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.279.( )defines Token-Bus protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.280.( ) defines CSMA/CD protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.281.The computer network that concentrated in a geographical area, such as in a building or on a university campus, is ( )A a LANB a MANC a WAND the Internet82.The MAC address is ( ) bits long.A 32B 48C 128D 25683.Which of the following four descriptions about MAC addresses is wrong? ( )A a MAC address is burned into the adapter’s ROMB No two adapters have the same addressC An adapter’s MAC address is dynamicD A MAC address is a link-layer address84.Which of the following four descriptions about DHCP is correct? ( )A DHCP is C/S architectureB DHCP uses TCP as its underlying transport protocolC The IP address offered by a DHCP server is valid foreverD The DHCP server will offer the same IP address to a host when the host requests an IP address85.The ( )field permits Ethernet to multiplex network-layer protocols.A preambleB typeC CRCD destination MAC address86.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( ) meters.A 50B 100C 200D 50087.An entry in the switch table contains the following information excepts for ( )A the MAC address of a nodeB the switch interface that leads towards the nodeC the time at which the entry for the node was placed in the tableD the IP address of a node88.Consider the 4-bit generator , G is 1001, and suppose that D has the value 101110000. What is the value of R?89.Consider the following graph of the network. Suppose Host A will send a datagram to Host B, Host A run OICQ on port 4000, Host B run OICQ on port 8000. All of ARP tables are up to date. Enumerate all the steps when message “Hello” is sent from host A to host B.。
计算机英语考试题及答案

计算机英语考试题及答案一、选择题(每题2分,共20分)1. Which of the following is not a type of computer hardware?A. CPUB. RAMC. SoftwareD. Hard Disk答案:C2. What does the acronym "USB" stand for?A. Universal Serial BusB. User System BusC. User Storage BusD. Universal Storage Bus答案:A3. What is the primary function of a router in a computer network?A. To store dataB. To process dataC. To connect multiple devicesD. To print documents答案:C4. Which of the following is a programming language?A. HTMLB. CSSC. JavaScriptD. All of the above答案:D5. What does "RAM" stand for in computer terminology?A. Random Access MethodB. Random Access MemoryC. Remote Access MemoryD. Rapid Access Memory答案:B6. What is the term for a collection of data stored on a computer?A. FileB. FolderC. DatabaseD. Memory答案:A7. Which of the following is a type of computer virus?A. WormB. TrojanC. Both A and BD. None of the above答案:C8. What is the purpose of a firewall in a computer system?A. To prevent unauthorized accessB. To speed up internet connectionsC. To store dataD. To print documents答案:A9. What does "GUI" stand for in the context of computer systems?A. Graphical User InterfaceB. General User InterfaceC. Global User InterfaceD. Graphical Universal Interface答案:A10. What is the term for a small computer program that performs a specific task?A. ApplicationB. SoftwareC. UtilityD. Script答案:D二、填空题(每题2分,共20分)1. The basic unit of data in a computer is called a____________.答案:bit2. A computer's operating system is an example of______________.答案:system software3. The process of converting data into a form that can be understood by a computer is called ______________.答案:encoding4. The term used to describe the speed of a computer's processor is ______________.答案:clock speed5. A computer network that spans a large geographical area is known as a ______________.答案:WAN (Wide Area Network)6. The process of recovering lost data is called______________.答案:data recovery7. A computer program that is designed to disrupt or damage a computer system is known as a ______________.答案:malware8. The primary storage medium for a computer's operating system and most frequently used programs is the______________.答案:hard drive9. The term used to describe the process of transferring data from one computer to another is ______________.答案:data transfer10. A computer that is part of a network and shares its resources with other computers is called a ______________.答案:server三、简答题(每题10分,共40分)1. What are the main components of a computer system?答案:The main components of a computer system include the central processing unit (CPU), memory (RAM), storage devices (hard disk, solid-state drive, etc.), input devices (keyboard, mouse, etc.), output devices (monitor, printer, etc.), andthe operating system.2. Explain the difference between hardware and software in a computer system.答案:Hardware refers to the physical components of a computer, such as the CPU, memory, and storage devices. Software, on the other hand, comprises the programs and instructions that run on the hardware, including theoperating system, applications, and utilities.3. What is the role of a firewall in a computer network?答案:A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted internal network and untrusted external networks,such as the Internet, to prevent unauthorized access and protect the internal network from potential threats.4. Describe the process of data encryption and its importance in computer security.答案:Data encryption is the process of converting readable data into an unreadable format, called ciphertext, using an algorithm and a key. This process ensures that only authorized parties with the correct key can access and decrypt the data. Encryption is crucial for protecting sensitive information from unauthorized access, ensuring data privacy and security in computer systems and networks.。
计算机网络英文题库附答案chapter定稿版

计算机网络英文题库附答案c h a p t e r精编W O R D版IBM system office room 【A0816H-A0912AAAHH-GX8Q8-GNTHHJ8】Chapter 1 Computer Networks and the Internet 1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switchednetworks, and virtual-circuit networks arepacket-switched networks.B datagram networks are packet-switchednetworks, and virtual-circuit networks arecircuit-switched networks.C datagram networks use destinationaddresses and virtual-circuit networks useVC. numbers to forward packets towardtheir destination.D datagram networks use VC. numbersand virtual-circuit networks use destinationaddresses to forward packets toward theirdestination.9.In the following options, which one is not a guided media ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct ( )A The traffic intensity must be greaterthan 1.B The fraction of lost packets increases asthe traffic intensity decreases.C If the traffic intensity is close to zero,the average queuing delay will be close tozero.D If the traffic intensity is close to one, theaverage queuing delay will be close to one.12.The Internet’s network layer isresponsible for moving network-layerpackets known as ( ) from one host toanother.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16.A LR/aB La/RC Ra/LD LR/a 17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that controlthe sending and receiving of informationwithin the Internet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks,whose hosts cannot exchange messageswith hosts outside of the private network.These private networks are often referredto as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or morecommunicating entities, as well as theactions taken on the transmission and/orreceipt of a message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messages exchangedbetween two or more communicatingentitiesB the order of messages exchangedbetween two or more communicatingentitiesC the actions taken on the transmission ofa message or other eventD the transmission signals are digitalsignals or analog signals27.In the following options, which is defined in protocol ( )A the actions taken on the transmissionand/or receipt of a message or othereventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error andin the proper order. The sentencedescribes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from enteringa state of gridlock. When a packet switchbecomes congested, its buffers canoverflow and packet loss can occur. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP 35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP()A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packetswitching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide forcommunication between the end systemare reserved for the duration of thecommunication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use theresources on demand, and as aconsequence, may have to wait for accessto communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by theend-to-end connection, the connectiongets ( ) of the link’s bandwidth for theduration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM 44.( ) means that the switch must receive the entire packet before it can begin totransmit the first bit of the packet onto theoutbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packetsaccording to host destination addresses iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packetsaccording to virtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network()A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receivinghost. The transmission rates between thesending host and the switch and betweenthe switch and the receiving host are R1and R2, respectively. Assuming that theswitch uses store-and-forward packetswitching, what is the total end-to-enddelay to send a packet of length L (Ignorequeuing delay, propagation delay, andprocessing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine thepacket’s header and determine where todirect the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points) (1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless serviceis used. Now suppose each packet has 200 bitsof header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between sourceand destination is 200bps. Assuming 0.02s setuptime and 200 bits of header appended to the packet, how long does it take to send the packet?So lution:(1).t=5*(3000+500)/1000+0.1=17.6s( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+0.02=16.02s。
计算机英语试题及答案
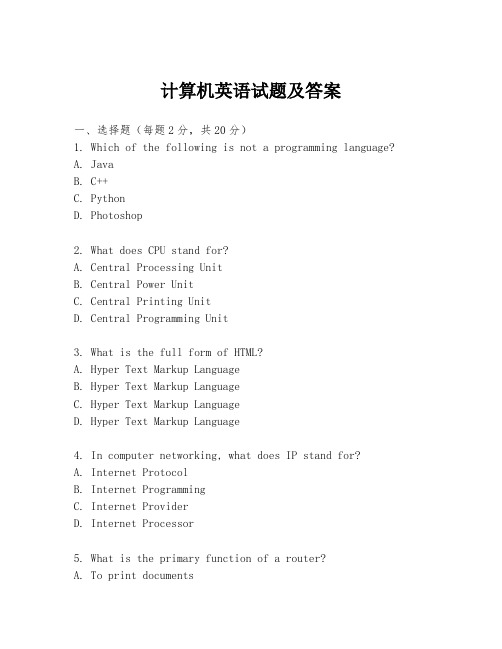
计算机英语试题及答案一、选择题(每题2分,共20分)1. Which of the following is not a programming language?A. JavaB. C++C. PythonD. Photoshop2. What does CPU stand for?A. Central Processing UnitB. Central Power UnitC. Central Printing UnitD. Central Programming Unit3. What is the full form of HTML?A. Hyper Text Markup LanguageB. Hyper Text Markup LanguageC. Hyper Text Markup LanguageD. Hyper Text Markup Language4. In computer networking, what does IP stand for?A. Internet ProtocolB. Internet ProgrammingC. Internet ProviderD. Internet Processor5. What is the primary function of a router?A. To print documentsB. To store dataC. To connect multiple networksD. To provide internet access6. Which of the following is a type of database management system?A. MS WordB. MS ExcelC. MS AccessD. MS PowerPoint7. What does the acronym RAM stand for?A. Random Access MemoryB. Rapid Access MemoryC. Remote Access MemoryD. Real Access Memory8. What is the term for a collection of data stored in a computer in a structured format?A. FileB. DocumentC. DatabaseD. Folder9. Which of the following is not a type of computer virus?A. TrojanB. WormC. AntivirusD. Ransomware10. What does the term "bandwidth" refer to in the context ofinternet usage?A. The width of the cableB. The speed of data transferC. The number of usersD. The quality of the connection二、填空题(每题2分,共20分)1. The basic unit of data in computing is called a ________.2. A ________ is a type of software that is designed to prevent, detect, and remove malware.3. The process of converting data into a form that can be easily transmitted or stored is known as ________.4. A ________ is a hardware device that allows a computer to connect to a network.5. The term "cybersecurity" refers to the practice of protecting systems, networks, and programs from ________ and other types of cyber attacks.6. A ________ is a collection of related data and the way it is organized.7. The ________ is a type of computer memory that retains data even when the power is off.8. The process of finding and fixing errors in a program is known as ________.9. A ________ is a type of software that allows users to create and edit documents.10. The ________ is a set of rules that define how data is formatted, transmitted, and received.三、简答题(每题10分,共30分)1. Explain the difference between a server and a client in a network.2. Describe the role of an operating system in a computer system.3. What are the key components of a computer system?四、论述题(每题30分,共30分)1. Discuss the importance of data backup and recovery in a computer system.答案:一、选择题1. D2. A3. A4. A5. C6. C7. A8. C9. C10. B二、填空题1. bit2. Antivirus3. Encoding4. Network Interface Card (NIC)5. unauthorized access6. Database7. Hard disk8. Debugging9. Word processor10. Protocol三、简答题1. In a network, a server is a computer system or device that provides resources or services to other computers, known as clients. The server manages network traffic, centralizes data storage, and provides access to shared resources, while the client is a computer that requests and uses these resourcesor services.2. An operating system is the software that manages computer hardware, software resources, and provides services for computer programs. It acts as an intermediary between theuser and the computer hardware, allowing users to interactwith the computer without needing detailed knowledge of the hardware.3. The key components of a computer system include thecentral processing unit (CPU), memory (RAM), storage devices (hard disk, SSD), input devices (keyboard, mouse), output devices (monitor, printer), and peripheral devices (scanner, webcam).四、论述题1. Data backup and recovery are critical in a computer system because they ensure that data is preserved in case ofhardware failure, data loss, or cyber attacks. Regularbackups allow for the restoration of data to a previous state, minimizing downtime and potential loss of information. This process is essential for maintaining business continuity and protecting against data loss.。
计算机网络英文版习题答案

P63 #5 Consider sending a packet of F bits over a path of Q links. Each link transmits at R bps. The network is lightly loaded so that there are no queuing delays. Propagation delay is negligible.a.Suppose the network is a packet-switched virtual-circuit network. Denote the VC setup time by t s seconds. Suppose the sending layers add a total of h bits of header to the packet. How long does it take to send the file from source to destination?t s+[(F+h)/R]Qb.Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 2h bits of header. How long does it take to send the packet?[(F+2h)/R]Qc.Finally, suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is R bps. Assuming ts setup time and h bits of header appended to the packet, how long does it take to send the packet?t s+(F+h)/RP64 #6 This elementary problem begins to explore propagation delay and transmission delay, two central concepts in data networking. Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts are separated by m meters and suppose that the propagation speed along the link is s meters/sec. Host A sends a packet of size L bits to host B.[a] Express the propagation delay, d prop, in terms of m and s.[b] Determine the transmission time of the packet, d trans, in terms of L and R.[c] Ignoring processing and queueing delays, obtain an expression for the end-to-end delay.[d] Suppose Host A begins to transmit the packets at time t=0. At time t=d trans, where is the last bit of the packet?[e] Suppose d prop is greater than d trans. At time t=d trans, where is the first bit of the packet?[f] Suppose d prop is less than d trans. At time t=d trans, where is the first bit of the packet?[g] Suppose s=2.5 x 108, L=100 bits and R=28kbps. Find the distance m so that d prop = d trans.[a] d prop = m/s[b] d trans = L/R[c] end-to-end delay = d prop + d trans=m/s+L/R[d] The beginning position of the link.[e] On the channel between A and B.[f] On the host B.[g] m/s = L/R = > m = sL/R = > m = 892.86 kmP65 #10 Consider the queueing delay in a router buffer. Suppose that all packets are L bits, the transmission rate is R bps, and that N packets simultaneously arrive at the buffer every LN/R seconds. Find the average queueing delay of a packet (in terms of L, R and N). (Hint: The queueing delay for the first packet is zero; for the second packet L/R; for the third packet 2L/R. The Nth packet has already been transmitted when the second batch of packets arrives.)As the Nth packet has already been transmitted when the next batch of packets arrive, we only need to consider the delay for a single batch of packets.Average delay = Total delay / Number of packetsDelay for 1st packet = 0Delay for 2nd packet = L/RDelay for 3rd packet = 2L/R......Delay for Nth packet = (N-1)L/RTotal delay for N packets = (0 + 1 + 2 ... +(N-1) ) * (L/R)Using the formulas for sum of integer series, this can be written as: Total delay for N packets = (N-1) * (N/2) * (L/R)Therefore, average delay for N packets = ((N-1) * L) / 2RP170 #12 What is the difference between persistent HTTP with pipelining and persistent HTTP without pipelinning? Which of the two is used by HTTP/1.1?For the persistent connection without pipelining, the client issues a new request only when the previous has been received. In this case, the client experiences one RTT in order to request and receive each of the referenced objects.For the persistent connection with pipelining, the client issues a request as soon as it encounters a reference. It is possible for only RTT to be expended for all the referenced objects.P170 #14 Telnet into a Web server and send a multiline request message. Include in the request message theIf-modified-since: header line to force a response message with the 304 Not Modified status code.GET/somedir/exp.html HTTP/1.1Host: Connection: closeUser-agent: Mozilla/4.0If-Modified-Since: Thu, 30 May 2007 12:00:00 GMTAccept-language: frP172 #6 Suppose within your web browser you click on a link to obtain a web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT (Round Trip Time) of RTT1, ... RTTn. Further suppose that the web page associated with the link contains exactly one object, consisting of a small amount of HTTP text. Let RTT0 denote the RTT between the local host and the remote server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object? (Hint: read pages 90 .. 93)Time to visit DNS servers and get IP address = RTT1 + RTT2 + ... + RTTnTime to establish TCP connection (SYN and SYNACK) = RTT0Time to send HTTP request and receive reply = RTT0Total time = 2 * RTT0 + (RTT1 + RTT2 + ... + RTTn)P171 #16 Suppose Alice with a Web-based e-mail account (such as Yahoo! Mail or Hotmail) sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.The series of application-layer protocols: HTTP、SMTP、POP3Suppose that you send an e-mail message whose only data is a Microsoft Excel attachment. What might the header lines (including MIME lines) look like?From:***********To:***********Subject: helloMIME-Version: 1.0Content-Transfer-Encoding: base64Content-Type: Application/MS-ExcelP286 #5 Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 90: the second has sequence number 110.a.How much data is in the first segment?a.20 bytesb.Suppose that the first segment is lost but the second segment arrives at B. In the acknowledgement that host B sends to host A, what will be the acknowledgement number?b.ACK90P291 #27 Consider the following plot of TCP window size as a function of time. (reproduced below for you) Assuming TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your answer.a. Identify the intervals of time when TCP slow start is operating.b. Identify the intervals of time when TCP congestion avoidance is operating.c. After the 16th transmission round, is segment loss detected by a tripleduplicate ACK or by a timeout?d. After the 22nd transmission round, is segment loss detected by a triple duplicate ACK or by a timeout?e. What is the initial value of Threshold at the first transmission round?f. What is the value of Threshold at the 18th transmission round?g. What is the value of Threshold at the 24th transmission round?h. During what transmission round is the 70th segment sent?i. Assuming a packet loss is detected after the 26th round by the receipt of a triple duplicate ACK, what will be the values of the congestion-window size and of Threshold?Solution:a.1-6, 23-26b.6-16, 17-22c.a triple duplicate ACKd.timeoute.32f.21g.13h.7i.4, 4P293 #34 Consider sending an object of size O = 100 Kbytes from server to client. Let S = 536 bytes and RTT = 100 msec. suppose the transport protocol uses static windows with window size W. (See Section 3.7.2)a.For a transmission rate of 28 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency.b.Repeat (a) for 100 kbps.tency=28.8s W=2tency=8.2s W=4P405 #8 Consider a datagram network using 8-bit host addresses. Suppose a router uses longest prefix matching and has t he following forwarding table:-----------------------------------------------------Prefix Match Interface-----------------------------------------------------00 001 110 211 3-----------------------------------------------------For each of the four interfaces, give the associated range of destination host addresses and the number of addresses in the range.6P407 #15 Consider sending a 3000-byte datagram into a link that has a MTU of 500 bytes. Suppose the original datagram is stamped with the identification number 422. How many fragments are generated? What are their characteristics?there are「2980/480」=7 fragments be generatedP408 #22 Consider the network shown in Problem 21 (reproduced below). Using Dijkstra’s algorithm, and showing your work using a table similar to Table 4.3, do the following:a. Compute the shortest path from s to all network nodesSteps D(t),P(t) D(u),P(u)D(v),P(v)D(w),P(w)D(x),P(x)D(y),P(y)D(z),P(z)0 1,s 4,s ∞∞∞∞∞1 3.t 10,t ∞∞5,t 3,t2 4,u 6,u ∞5,t 3,t3 4,u 6,u ∞5,t4 5,v 7,v 5,v5 6,w 5,v6 6,wPlease fill in the following tables using DV algorithm:For the node Z in the graph shown in the 22nd topic (P408), please fill in the following routing table in the router z about the initial distance-vector Destination node Next hop Current shortest distancevalue-DzS —∞T T 2U —∞V —∞W —∞X —∞Y Y 14Z Z 0following rout-ing table in the node z to update this routing tableDestination node Currentdistance-DyDestination node Current distance-DtS 5 S 1 T 4 T 0 U 2 U 2P493 #7 How big is the MAC address space?The IPv4 address space?The IPv6 address space?MAC address: 6 bytes, MAC address space 2^48IPV4 address: 4 bytes, IPV4 address space 2^32IPV6 address: 16 bytes, IPV6 address space 2^128P494 #4 Consider the 4-bit generator, G, shown in Figure 5.8, and suppose the D has the value 10101010. What is the value of R?G=1001, D=10101010, R=101。
计算机专业英语复习题含答案详细解释

计算机专业英语复习题注:本答案解释及翻译属本人分析,如有错误,敬请谅解!I.Choose the best answerI.选择最佳答案。
1.When you run your computer, A will be first started.A.Operation systemB. system softwareC. office softwareD. driven software译:当你运行你的电脑时,XX是首先被启动。
A是操作系统,B是系统软件,C是办公软件,D是驱动软件(指第三方驱动软件);因为操作系统包括开机自检的驱动软件,而不是第三方驱动。
所以选A2. Post is the short form for AA. power on self-testB. post office system testC. power on system-testD. personal operating system text 译:post是____的缩写。
The short from for某某的缩写形式。
A是开机自检B是办公系统测试C 是开机系统自检D是个人操作系统文本。
约定俗成的简写形式是A。
3. One of the benefits of video conferencing is low costs.A. specially equipped conference roomsB. saving travel timeC. low costsD.linking of local sites译:视频协商(视频会议)的好处之一是_____。
Benefit 好处,益处conference协商,讨论,商谈A是特别的协商会议室B是减少旅游时间C是低花费D是连接本地地址4. The menu bar of word 2003 has C menus orders.A. sevenB. eightC. nineD. ten Word 2003的菜单栏中有9个菜单命令。
计算机英译中测试题及答案
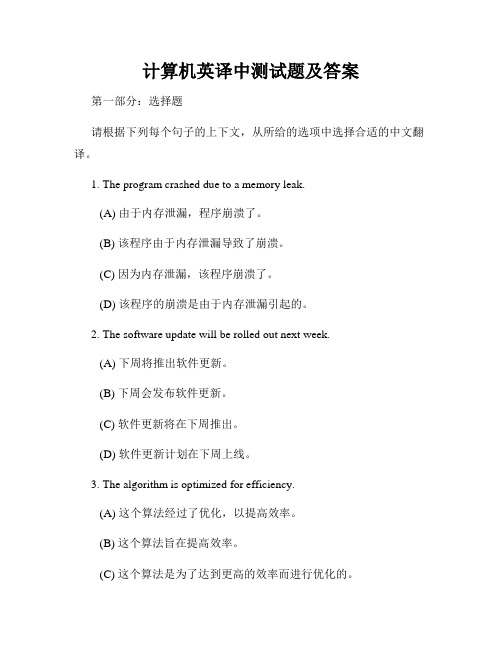
计算机英译中测试题及答案第一部分:选择题请根据下列每个句子的上下文,从所给的选项中选择合适的中文翻译。
1. The program crashed due to a memory leak.(A) 由于内存泄漏,程序崩溃了。
(B) 该程序由于内存泄漏导致了崩溃。
(C) 因为内存泄漏,该程序崩溃了。
(D) 该程序的崩溃是由于内存泄漏引起的。
2. The software update will be rolled out next week.(A) 下周将推出软件更新。
(B) 下周会发布软件更新。
(C) 软件更新将在下周推出。
(D) 软件更新计划在下周上线。
3. The algorithm is optimized for efficiency.(A) 这个算法经过了优化,以提高效率。
(B) 这个算法旨在提高效率。
(C) 这个算法是为了达到更高的效率而进行优化的。
(D) 这个算法被优化以提高效率。
4. The server is experiencing high latency.(A) 服务器延迟较高。
(B) 服务器正在高延迟状态下。
(C) 服务器正在遭受高延迟。
(D) 服务器的延迟问题比较严重。
5. The database was corrupted, resulting in data loss.(A) 数据库损坏,导致数据丢失。
(B) 数据库出现损坏,造成了数据丢失。
(C) 数据库受损,导致数据丢失。
(D) 由于数据库损坏,导致数据丢失。
第二部分:简答题请用完整的中文句子回答下列问题。
1. 什么是操作系统?操作系统是一种软件,它管理和控制计算机硬件资源,并为用户和其他软件提供统一的接口。
2. 简要解释一下什么是编程语言?编程语言是一套用于编写计算机程序的符号和规则的系统。
它们定义了程序的结构和行为,并通过编译或解释器将程序转换为机器可执行的指令。
3. 请简要描述一下传输控制协议(TCP)是如何工作的。
(完整版)计算机网络英文题库(附答案)chapter3
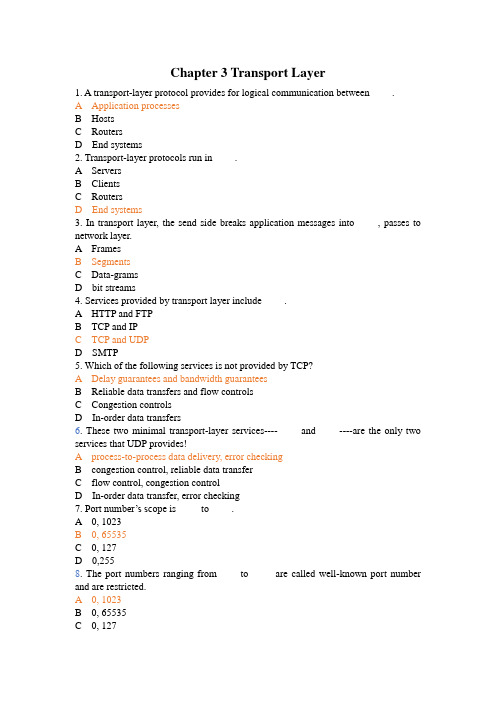
Chapter 3 Transport Layer1. A transport-layer protocol provides for logical communication between ____.A Application processesB HostsC RoutersD End systems2. Transport-layer protocols run in ____.A ServersB ClientsC RoutersD End systems3. In transport layer, the send side breaks application messages into ____, passes to network layer.A FramesB SegmentsC Data-gramsD bit streams4. Services provided by transport layer include ____.A HTTP and FTPB TCP and IPC TCP and UDPD SMTP5. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers6. These two minimal transport-layer services----____ and ____----are the only two services that UDP provides!A process-to-process data delivery, error checkingB congestion control, reliable data transferC flow control, congestion controlD In-order data transfer, error checking7. Port number’s scop e is ____ to ____.A 0, 1023B 0, 65535C 0, 127D 0,2558. The port numbers ranging from ____to ____ are called well-known port number and are restricted.A 0, 1023B 0, 65535C 0, 127D 0,2559. UDP socket identified by two components, they are ____.A source IP addresses and source port numbersB source IP addresses and destination IP addressesC destination IP address and destination port numbersD destination port numbers and source port numbers10. TCP socket identified by a (an) ____.A 1-tupleB 2-tupleC 3-tupleD 4-tuple11. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP12. Reliable data transfer protocol over a perfectly reliable channel is____.A rdt1.0B rdt2.0C rdt3.0D rdt2.113. Reliable data transfer protocol over a channel with bit errors and packet losses is _ ___.A rdt1.0B rdt2.0C rdt3.0D rdt2.114. Which of the following about reliable data transfer over a channel with bit errors i s not correct?A RDT2.0: assuming ACK and NAK will not be corruptedB RDT2.1: assuming ACK and NAK can be corruptedC RDT2.2: only use ACK-sD RDT2.2: use both ACK-s and NAK-s15. Which of the following protocols is not pipelining protocols?A TCPB rdt3.0C GO-BACK-ND selective repeat16. Which of the following is not correct about GBN protocol?A Only using ACK-sB Using cumulative ACK-sC Receiver discards all out-of-order packetsD It is not pipelined protocol17. Which of the following is not correct about SR protocol?A receiver individually acknowledges all correctly received packetsB sender only resends packets for which ACK not receivedC It limits sequence number of sent but un-ACK-ed packetsD It is not a pipelined protocol18. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection19. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection20. The FIN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection21.How does TCP sender perceive congestion?A Through a timeout eventB Through a receiving duplicate ACK-s eventC Both A and BD Either A or B22. Extending host-to-host delivery to process-to-process delivery is called transport-layer ____ and .A multiplexing and de-multiplexingB storing and forwardingC forwarding and filteringD switching and routing23. UDP is a ____ service while TCP is a connection-oriented service.A ConnectionlessB ReliableC Connection-orientedD In-order24. The UDP header has only four fields, they are____.A Source port number, destination port number, length and checksumB Source port number, destination port number, source IP and destination IPC source IP, destination IP, source MAC address and destination MAC addressD source IP, destination IP, sequence number and ACK sequence number25. There are two 16-bit integers: 1110 0110 0110 0110, 1101 0101 0101 0101. Their checksum is____.A 0100010001000011B 1011101110111100C 1111111111111111D 100000000000000026.The maximum amount of data that can be grabbed and placed in a segment is limited by the____.A Maximum segment size (MSS)B MTUC ChecksumD Sequence number27.The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host----the so-called____.A Maximum transmission unit (MTU)B MSSC ChecksumD Sequence number28. A File size of 500,000bytes, MSS equals 1000bytes. When we want to transmit this file with TCP, the sequence number of the first segment is 0, and the sequence number of the second segment is ____.A 1000B 999C 1001D 50000029.Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide____.A Cumulative acknowledgementsB Selective acknowledgementsC 3 duplicate ACKsD positive ACKs30. Provided α=0.125, current value of Estimated-RTT is 0.4s, Sample-RTT is 0.8s, then the new value of Estimated-RTT is ____s.A 0.45B 0.6C 0.7D 0.831.Provided RcvBuffer=20,LastByteRcvd=20,LastByteRead=15, thenRcvWindow=____.A 14B 15C 16D 1032. TCP service does not provide____.A Reliable data transferB Flow controlC Delay guaranteeD Congestion control33. There are two states in TCP congestion control, which are ____.A slow start and congestion avoidanceB safe start and congestion avoidanceC slow start and congestion abandonD safe start and congestion abandon34. The transport-layer protocol provides logical communication between ____, and the network-layer protocol provides logical communication ____.A hosts, processesB processes, hostsC threads, processesD processes, threads35. To implement the multicast services the Internet employs the ____ protocol.A FTPB TCPC IGMPD UDP36. If an application developer chooses ____ protocol, then the application process is almost directly talking with IP.A HTTPB RIPC CSMA/CDD UDP37. ____ maintains connection-state in the end systems. This connection state includes receive and send buffers, congestion-control parameters, and sequence and acknowledgment number parameters.A UDPB TCPC DNSD HTTP38. The host that initiates the session in the Internet is labeled as ____.A serverB user agentC clientD router39. With TCP there is no _____ between sending and receiving transport-layer entities.A flow controlB handshakingC. congestion control D VC setup40. The Internet’s ____service helps prevent the Internet from entering a state of gridlock.A datagramB congestion controlC sliding windowD timeout event41. Connection setup at the transport layer involves ____.A serverB only the two end systemsC clientD router42. A ____layer protocol provides for logical communication between applications.A transportB applicationC networkingD MAC43. In static congestion window, if it satisfies W*S/R > RTT + S/R, the Latency is ____.A W*S/R – ( RTT+ S/R)B 2RTT + O/RC 2RTT + O/R + (k-1)[W* S/R- (RTT + S/R)]D 2RTT + S/R44. The receive side of transport layer reassembles segments into messages, passes to ____layer.A ApplicationB NetworkingC PhysicalD MAC45. In the following four options, which one is correct?A The variations in the SampleRTT are smoothed out in the computation of the EstimatedRTTB The timeout should be less than the connection’s RTTC Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≥1 secD Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≤1 sec46. The port number used by HTTP is ____.A 80B 25C 110D 5347. The port number used by SMTP is ____.A 80B 25C 110D 5348. The port number used by pop3 is ____.A 80B 25C 110D 5349. The port number used by DNS is ____.A 80B 25C 110D 5350. The port number used by FTP is ____.A 20 and 21B 20C 21D 5351. A UDP socket identified by a ____ tuple(s).A 2B 4C 1D 352. A TCP socket identified by a ____ tuple(s).A 2B 4C 1D 353. A TCP socket does not include____.A Source MAC addressB Source port numberC Destination IP addressD Destination port number54. Which of following about UDP is not correct.A It is a reliable data transfer protocolB It is connectionlessC no handshaking between UDP sender, receiverD it is a best effort service protocol55. DNS uses ____ service.A TCPB UDPC Both TCP and UDPD None of above56. Which of following about UDP is correct?A Finer application-level control over what data is sent, and whenB No connection establishment (which can add delay), so no delay for establish a connectionC No connection state (so, UDP can typically support many active clients)D Large packet header overhead (16-B)57. Streaming media uses a ____ service normally.A TCPB UDPC Both TCP and UDPD None of above58. The UDP header has only ____ fields.A 2B 4C 1D 359. Which of the following does not included in UDP header.A Source port numberB Destination port numberC ChecksumD Sequence number60. Which of the following is not a pipelining protocol.A Rdt1.0B Go-Back-NC Selective repeatD TCP61. In the following four descriptions about MSS and MTU, which one is not correct?A The MSS is the maximum amount of application-layer data in the segmentB The MSS is the maximum size of the TCP segment including headersC The MSS is typically set by MTUD The MTU means the largest link-layer frame62. The job of gathering data chunks, encapsulating each data chunk with header information to create segments and passing the segments to the network is called ____.A multiplexingB de-multiplexingC forwardingD routing63. In the following four descriptions about the relationship between the transport layer and the network layer, which one is not correct?A The transport-layer protocol provides logical communication between hostsB The transport-layer protocol provides logical communication between processesC The services that a transport-layer protocol can provide are often constrained by the service model of the network-layer protocolD A computer network may make available multiple transport protocols64. Suppose the following three 8-bit bytes: 01010101, 01110000, 01001100. What’s the 1s complement of the sum of these 8-bit bytes?A 00010001B 11101101C 00010010D 1000100065. The following four descriptions about multiplexing and de-multiplexing, which one is correct?A A UDP socket is identified by a two-tuples consisting of a source port number and a destination port number.B If two UDP segment have different source port number, they may be directed to the same destination process.C If two TCP segments with different source port number, they may be directed to the same destination process.D If two TCP segments with same destination IP address and destination port number, they must be the same TCP connection.66. UDP and TCP both have the fields except ____.A source port numberB destination port numberC checksumD receive window67. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [nextseqnum,base+N-1] corresponds to packet that ____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged68. Which of the following about TCP is not correct?A It is a connectionless protocolB Point-to-point protocolC Reliable, in-order byte steam protocolD Pipelined protocol69. Which of the following about TCP is not correct?A It is a connectionless protocolB full duplex data transfer protocolC connection-oriented protocolD flow controlled protocol70. The maximum amount of data that can be grabbed and placed in a segment is limited by the ____.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum71. The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host (the so-called____), and then will fit into a single link-layer frame.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum72. The MSS is the maximum amount of ____layer data in the segment, not the maximum size of the TCP segment including headers.A ApplicationB TransportC NetworkingD Link73. Which of the following field is not used for connection setup and teardown?A Sequence numberB TSTC SYND FIN74. ____ is the byte stream number of first byte in the segment.A Sequence numberB ACK numberC ChecksumD port number75. ____ is the byte sequence numbers of next byte expected from other side.A Sequence numberB ACK numberC ChecksumD port number76. Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide ____ acknowledgements.A CumulativeB SelectiveC SingleD Negative77. Fast retransmit means in the case that ____ duplicate ACK-s are received, the TCP sender resend segment before timer expires.A 3B 4C 5D 678. TCP____ means sender won’t overflow receiver’s buffer by tran smitting too much, too fast.A Flow controlB Congestion controlC Reliable data transferD Connection-oriented service79. TCP provides flow control by having the sender maintain a variable called the ____.A Receive windowB Congestion windowC Sliding windowD buffer80. How does TCP sender perceive congestion?A TimeoutB 3 duplicate ACK-sC Both A and BD None of above81. Transport protocols run in ____.A ServersB ClientsC RoutersD End systems82. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers83. Which service does UDP not provide?A multiplexingB de-multiplexingC error-detectionD error-correction84. There are three major events related to data transmission and retransmission in the TCP sender, which one is not in it?A data received from application aboveB de-multiplexing segmentC timer timeoutD ACK receipt85. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP86. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection87. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection88. Which service helps prevent the internet from entering a state of gridlock?A reliable data transferB flow controlC congestion controlD handshaking procedure89. The Internet’s _____is responsible for moving packets from one host to another.A application layerB transport layerC network layerD link layer90.In the following applications, which one is a bandwidth-sensitive application?A E-mailB web applicationC real-time audioD file transfer91. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS92. In the following four descriptions, which one is correct?A If one host’s transport layer uses TCP, then its network layer must use virtual-circuit network.B Datagram network provides connection serviceC The transport-layer connection service is implemented in the routerD The network-layer connection service is implemented in the router as well as in the end system.93.____ is a speeding-matching service---matching the rate which the sender is sending against the rate at which the receiving application is reading.A congestion controlB flow controlC sliding-window controlD variable control94. In the following four descriptions about Rcv-Window, which one is correct?A The size of the TCP RcvWindow never changes throughout the duration of the connectionB The size of the TCP RcvWindow will change with the size of the TCP RcvBufferC The size of the TCP RcvWindow must be less than or equal to the size of the TCP RcvBufferD Suppose host A sends a file to host B over a TCP connection, the number of unacknowledged bytes that A sends cannot exceed the size of the size of the RcvWindow.95. There are 6 flag fields. Which one is to indicate that the receiver should pass the data to the upper layer immediately?A PSHB URGC ACKD RST96. Suppose the TCP receiver receives the segment that partially or completely fills in gap in received data, it will ____.A immediately send ACKB immediately send duplicate ACKC wait some time for arrival of another in-order segmentD send single cumulative97. _____ imposes constrain on the rate at which a TCP sender can send traffic into the network.A sliding windowB congestion windowC receive windowD variable window98. Flow control and congestion control are same at that they all limit the rate of the sender, but differ in that ____.A flow control limits its rate by the size of RcvWindow, but congestion control by the traffic on the linkB congestion control limits its rate by the size of RcvWindow, but flow control by the traffic on the linkC flow control mainly is accomplished by the sender, but congestion control by the receiver.D flow control mainly is accomplished by the receiver, but congestion control bythe link.99. This job of delivering the data in a transport-layer segment to the correct socket is called ____.A multiplexingB de-multiplexingC forwardingD routing100. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [base, nextseqnum-1] corresponds to packet that ____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged101. ____ are the two types of transport services that the Internet provides to the applications.A TCP and UDPB connection-oriented and connectionless serviceC TCP and IPD reliable data transfer and flow control102. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a responseB Each TCP connection is closed after the server sending one objectC There are two versions of persistent connection: without pipelining and with pipeliningD The default mode of HTTP uses persistent connection with pipelining103. The field of Length in UDP segment specifies the length of ____.A the UDP segment, not including the headerB the UDP segment, including the headerC the UDP segment’s headerD the Length field104. In TCP segment header, which field can implement the reliable data transfer?A source port number and destination port numberB sequence number and ACK numberC urgent data pointerD Receive window105. In the following four descriptions about TCP connection management, which one is not correct?A Either of the two processes participating in a TCP connection can end the connectionB If the FIN bit is set to 1, it means that it wants to close the connectionC In the first two step of the three-way handshake, the client and server randomly choose an initial sequence numberD In the three segments of the three-way handshake, the SYN bit must be set to 1 106. Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 42, and the second has sequence number 110. If the 1st is lost and 2nd arrives at host B. What will be the acknowledgment number?A 43B ACK42C 109D ACK1101.Consider sending an object of size O=500,000bytes from server to client. LetS=500 bytes and RTT=0.2s. Suppose the transport protocol uses static windows with window size 5. For a transmission rate of 100Kbps, determine the latency for sending the whole object. Recall the number of windows K=O/ WS), and there is K-1 stalled state (that is idle time gaps).2.Consider the following plot of TCP congestion window size as a function of time.Fill in the blanks as follow:a) The initial value of Threshold at the first transmission round is ____. b) The value of Threshold at the 11st transmission round is ____. c) The value of Threshold at the 21st transmission round is ____. d) After the 9th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKe) After the 19th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKf) During ____ transmission round, the 18th segment is sent.3.Consider the TCP reliable data transfer in the given graph. If in Segment 1’s Sequence number =10,data=“AC”, please fill in the following blanks. a) In Segment 2, ACK number=____;b) In Segment 3, Sequence number =____; data=“0123456789”c) If there are some bits corrupted in segment 3 when it arrives Host B, then the ACK number in Segment 5 is ____; and the ACK number in Segment 6 is ____.14 180 26 3000 2 6 4 8 10 12 16 20 22 240 28 32Congestion window sizeTransmission round48121612345674. The client A wants to request a Web page from Server B. Suppose the URL of the page is 172.16.0.200/experiment, and also it wants to receive French version of object. The time-sequence diagram is shown below, please fill in the blanks.12345Packet① to Packet③are TCP connection’s segment, then:Packet ①: SYN flag bit= aACK flag bit= bSequence number= 92Packet ②: SYN flag bit=1ACK flag bit= c Sequence number=100 Packet ③: SYN flag bit= d ACK flag bit=1Sequence number= e5. Consider sending an object of size O=100 Kbytes from server to client. Let S=536 bytes and RTT=100msec. Suppose the transport protocol uses static windows with window size W.(1) For a transmission rate of 25 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency. (2) Repeat (1) for 100 kbps.6. Consider the following plot of TCP congestion window size as a function of time. Please fill in the blanks as below.a) The initial value of Threshold at the first transmission round is____. b) The value of Threshold at the 11th transmission round is_____. c) The value of Threshold at the 21st transmission round is_____.14 18 26 30 0 2 6 4 8 10 12 16 20 22 24 28 32 Congestion window sizeTransmission round481216d) After the 9th transmission round, _____ occurs.e) After the 19th transmission round, ____ are detected.。
计算机网络英文题库(附答案)chapter1

Chapter 1 Computer Networks and the Internet 1.The The ( ( ) ) is is is a a a worldwide worldwide worldwide computer computer computer network, network, network, that that that is, is, is, a a a network network network that that interconnects millions of computing devices throughout the world. ppt3 A public Internet B Intranet C switch net D television net 2.Which kind of media is not a guided media? ( ) A twisted-pair copper wire B a coaxial cable C fiber optics D digital satellite channel 3.Which kind of media is a guided media? ( ) A geostationary satellite B low-altitude satellite C fiber optics D wireless LAN 4.The units of data exchanged by a link-layer protocol are called ( ). A Frames B Segments C Datagrams D bit streams 5.Which of the following option belongs to the circuit-switched networks? ( ) A FDM B TDM C VC networks D both A and B 6.( )makes sure that that neither neither neither side side side of of of a a a connection overwhelms connection overwhelms the the other other side by sending too many packets too fast. A Reliable data transfer B Flow control C Congestion control D Handshaking procedure 7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link. A Store-and-forward transmission B FDM C End-to-end connection D TDM 8.Datagram networks and virtual-circuit networks differ in that ( ). A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks. B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks. C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination. D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( ) A twisted-pair wire B fiber optics C coaxial cable D satellite 10.Processing delay does not include the time to ( ). A examine the packet ’s header B wait to transmit the packet onto the link C determine where to direct the packet D check bit-error in the packet 11.In the following four descriptions, which one is correct? ( ) A The traffic intensity must be greater than 1. B The fraction of lost packets increases as the traffic intensity decreases. C If the traffic intensity is close to zero, the average queuing delaywill be close to zero. D If the traffic intensity is close to one, the average queuing delay will be close to one. 12.The The Internet Internet Internet’’s s network network network layer layer layer is is is responsible responsible responsible for for for moving moving moving network-layer network-layer packets known as ( ) from one host to another. A frame B datagram C segment D message 13.The protocols of various layers are called ( ). A the protocol stack B TCP/IP C ISP D network protocol 14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks. A datagram B circuit-switched C television D telephone 15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access. A cabled B wireless C campus D city area Question 16~17 Suppose, a is the average rate at which packets arrive at the queue, R is the the transmission transmission transmission rate, rate, rate, and and and all all all packets packets packets consist consist consist of of L bits, bits, then then then the the the traffic traffic intensity is ( 16 ), and it should no greater than ( 17 ). 16. A LR /aB La /RC Ra /L D LR /a 17.A 2 B 1 C 0 D -1 18.In the Internet, the equivalent concept to end systems is ( ). A hosts B servers C clients D routers 19.In the Internet, end systems are connected together by ( ). A copper wire B coaxial cable C communication links D fiber optics 20.End systems access to the Internet through its ( ). A modems B protocols C ISP D sockets 21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within the Internet. A programs B processes C applications D protocols 22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ). A internets B LANC intranets D W AN 23.The internet allows ( ) running on its end systems to exchange data with each other. A clients applications B server applications C P2P applications D distributed applications 24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service. A flow control B connection-oriented reliable C congestion control D TCP 25.It defines the format and the order of messages exchanged between twoor more communicating entities, as well as the actions taken on the transmission and/or receipt of a message or other event. The sentence describes ( ). A Internet B protocol C intranet D network 26.In the following options, which does not define in protocol? ( ) A the format of messages exchanged between two or more communicating entities B the order of messages exchanged between two or more communicating entities C the actions taken on the transmission of a message or other evenD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( ) A the actions taken on the transmission and/or receipt of a message oother event B the objects exchanged between communicating entities C the content in the exchanged messages D the location of the hosts 28.In the following options, which does not belong to the network edge( ) A end systems B routers C clients D servers 29.In the following options, which belongs to the network core? ( ) A end systems B routers C clients D servers 30.In the following options, which is not the bundled with the Internet ’s connection-oriented service? ( ) A reliable data transfer B guarantee of the transmission time C flow control D congestion-control 31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ). A flow control B congestion-control C reliable data transfer D connection-oriented service 32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ). A flow control B congestion-control C connection-oriented service D reliable data transfer 33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ). A flow control B congestion-control C connection-oriented service D reliable data transfer 34.The Internet ’s connection-oriented service has a name, it is ( ). A TCP B UDP C TCP/IP D IP 35.In In the the the following following following options, options, options, which which which service service service does does does not not not be be be provided provided provided to to to an an application by TCP?( ) A reliable transport B flow control C video conferencing D congestion control 36.The Internet ’s connectionless service is called ( ). A TCP B UDP C TCP/IP D IP 37.In the following options, which does not use TCP?( ) A SMTP B internet telephone C FTP D HTTP 38.In the following options, which does not use UDP?( ) A Internet phone B video conferencing C streaming multimedia D telnet 39.There are two fundamental approaches to building a network core, ( ) and packet switching. A electrical current switching B circuit switching C data switching D message switching 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration ofthe communication session. A packet-switched B data-switched C circuit-switched D message-switched 41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link. A packet-switched B data-switched C circuit-switched D message-switched 42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of the link link’’s bandwidth for the duration of the connection. A a fraction 1/n B all C 1/2 D n times 43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot. A CDMA B packet-switched network C TDM D FDM 44.( ) means that the switch must receive the entire packet before it canbegin to transmit the first bit of the packet onto the outbound link. A Queuing delay B Store-and-forward transmission C Packet loss D Propagation 45.The network that forwards packets according to host destination addresses is called ( ) network. A circuit-switched B packet-switched C virtual-circuit D datagram 46.The network that forwards packets according to virtual-circuit numbers is called ( ) network. A circuit-switched B packet-switched C virtual-circuit D datagram 47.In the following entries, which is not a kind of access network?( ) A residential access B company access C wireless access D local access 48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R 1 and R 2, respectively. Assuming that the switch uses store-and-forward packet switching, what is the total end-to-end delay to send a packet of length L ? (Ignore queuing delay, propagation delay, and processing delay.) ( )A L /R 1+L /R 2 B L /R 1C L /R 2D none of the above 49.The time required to examine the packet ’s header and determine where to direct the packet is part of the ( ). A queuing delay B processing delay C propagation delay D transmission delay 50.The time required to propagate from the beginning of the link to the next router is ( ). A queuing delay B processing delay C propagation delay D transmission delay 51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits transmits at at at 1000bps. 1000bps. 1000bps. Queuing Queuing Queuing delays, delays, delays, propagation propagation propagation delay delay delay and and and processing processing delay are negligible. (6 points) (1).Suppose (1).Suppose the the the network network network is is is a a a packet-switched packet-switched packet-switched virtual virtual virtual circuit circuit circuit network. network. network. VC VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination? (2).Suppose the the network network network is is is a a a packet-switched packet-switched datagram datagram network network network and and and a a connectionless connectionless service service service is is is used. used. used. Now Now Now suppose suppose suppose each each each packet packet packet has has has 200 200 200 bits bits bits of of header. How long does it take to send the file? (3).Suppose that the network is a circuit-switched network. Further suppose that that the the the transmission transmission transmission rate rate rate of of of the the the circuit circuit circuit between between between source source source and and and destination destination destination is is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet? Solution: (1). t=5*(3000+500)/1000+0.1=17.6s(2). t=5*(3000+200)/1000=16s(3). t=(3000+200)/200+0.02=16.02s。
英文版计算机试题及答案
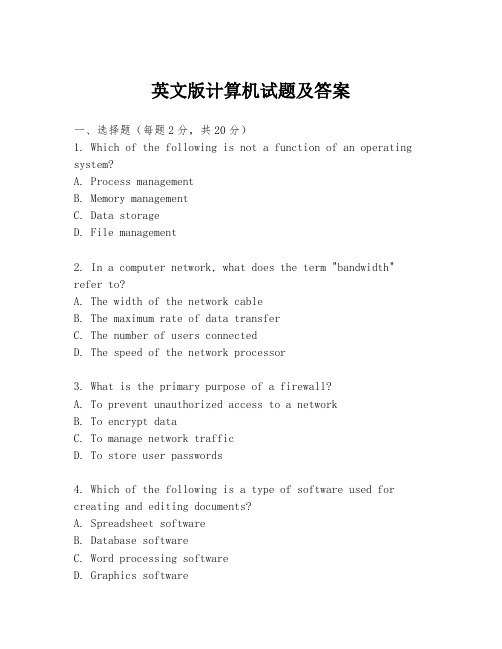
英文版计算机试题及答案一、选择题(每题2分,共20分)1. Which of the following is not a function of an operating system?A. Process managementB. Memory managementC. Data storageD. File management2. In a computer network, what does the term "bandwidth" refer to?A. The width of the network cableB. The maximum rate of data transferC. The number of users connectedD. The speed of the network processor3. What is the primary purpose of a firewall?A. To prevent unauthorized access to a networkB. To encrypt dataC. To manage network trafficD. To store user passwords4. Which of the following is a type of software used for creating and editing documents?A. Spreadsheet softwareB. Database softwareC. Word processing softwareD. Graphics software5. What is the term used to describe the process of converting data from one format to another?A. Data migrationB. Data transformationC. Data conversionD. Data translation6. What does the acronym "CPU" stand for in computing?A. Central Processing UnitB. Central Processing UnitC. Computer Processing UnitD. Computing Processing Unit7. What is the function of a router in a network?A. To connect multiple networksB. To store dataC. To provide power to devicesD. To print documents8. What is the process of finding and fixing errors in software called?A. DebuggingB. PatchingC. UpdatingD. Patching9. Which of the following is a type of computer virus that replicates itself by attaching to other programs?A. TrojanB. WormC. RansomwareD. Spyware10. What is the term for the graphical representation of data on a computer screen?A. Data visualizationB. Data representationC. Data graphingD. Data mapping二、填空题(每题2分,共20分)1. The _________ is the primary memory used by a computer to store data and instructions that are currently being processed.2. A _________ is a type of software that allows users to create and edit images.3. The process of converting analog signals to digital signals is known as _________.4. A _________ is a collection of data stored in a structured format.5. The _________ is a hardware component that connects a computer to a network.6. In computer programming, a _________ is a sequence of statements that perform a specific task.7. The _________ is a type of malware that hides its presence and waits for a trigger to activate.8. A _________ is a type of software that is designed to protect a computer from unauthorized access.9. The _________ is the process of organizing and managing data in a database.10. A _________ is a type of software that allows users tocreate and edit spreadsheets.三、简答题(每题10分,共30分)1. Describe the role of a server in a computer network.2. Explain the difference between a compiler and an interpreter in programming.3. Discuss the importance of data backup and recovery in a computing environment.四、编程题(每题15分,共30分)1. Write a simple program in Python that calculates the factorial of a given number.2. Create a function in Java that takes an array of integers and returns the largest number in the array.答案:一、选择题1. C2. B3. A4. C5. C6. A7. A8. A9. B10. A二、填空题1. RAM (Random Access Memory)2. Graphics software3. Analog-to-digital conversion4. Database5. Network interface card (NIC)6. Function or procedure7. Trojan8. Antivirus software9. Database management10. Spreadsheet software三、简答题1. A server in a computer network is a powerful computer or system that manages network resources, including hardware and software, and provides services to other computers on the network, such as file storage, web hosting, and print services.2. A compiler is a program that translates source codewritten in a programming language into machine code that a computer can execute. An interpreter, on the other hand, reads and executes the source code line by line without the need for a separate compilation step.3. Data backup and recovery are crucial in a computing environment to prevent data loss due to hardware failure, software bugs, or malicious attacks. Regular backups ensure that data can be restored to a previous state in case of corruption or deletion.四、编程题1. Python Program for Factorial Calculation:```pythondef factorial(n):if n == 0:return 1 else:。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
英文版计算机试题及答案Section 1: Multiple Choice Questions (MCQs)
1. Which of the following is NOT a programming language?
a) Java
b) HTML
c) Python
d) SQL
Answer: b) HTML
2. What does CPU stand for?
a) Central Processing Unit
b) Computer Processing Unit
c) Control Processing Unit
d) Central Program Unit
Answer: a) Central Processing Unit
3. Which of the following is NOT an input device?
a) Keyboard
b) Mouse
c) Printer
d) Scanner
Answer: c) Printer
4. What does RAM stand for?
a) Read-Only Memory
b) Random Access Memory
c) Recordable Audio Media
d) Runtime Activity Monitor
Answer: b) Random Access Memory
5. Which of the following is NOT a type of computer network?
a) LAN (Local Area Network)
b) WAN (Wide Area Network)
c) MAN (Metropolitan Area Network)
d) CAN (Campus Area Network)
Answer: d) CAN (Campus Area Network)
Section 2: Short Answer Questions
1. Define the term "algorithm."
Answer: An algorithm is a step-by-step procedure or set of rules for solving a specific problem or completing a specific task.
2. What is object-oriented programming (OOP)?
Answer: Object-oriented programming is a programming paradigm that organizes code into objects, which are instances of classes. It emphasizes the concept of objects and their interactions to solve complex problems.
3. Explain the difference between static and dynamic memory allocation.
Answer: Static memory allocation is performed at compile-time, where memory is allocated for variables and objects before the program execution starts. Dynamic memory allocation, on the other hand, is performed at runtime using functions like malloc() or new(). It allows for the allocation and deallocation of memory during program execution.
4. What is the purpose of an operating system?
Answer: The operating system is responsible for managing computer hardware and software resources, providing an interface between the user and the computer, and ensuring that various programs and applications can run smoothly. It also provides file management, process management, and memory management.
5. Name three programming paradigms.
Answer: Three programming paradigms are procedural programming, object-oriented programming, and functional programming.
Section 3: Coding Questions
1. Write a Java program to find the factorial of a given number.
```java
import java.util.Scanner;
public class Factorial {
public static void main(String[] args) {
Scanner input = new Scanner(System.in);
System.out.print("Enter a number: ");
int number = input.nextInt();
int factorial = 1;
for (int i = 1; i <= number; i++) {
factorial *= i;
}
System.out.println("The factorial of " + number + " is " + factorial); }
}
```
2. Write a Python program to check if a number is prime or not.
```python
def is_prime(number):
if number < 2:
return False
for i in range(2, int(number/2)+1):
if number % i == 0:
return False
return True
number = int(input("Enter a number: "))
if is_prime(number):
print(number, "is prime.")
else:
print(number, "is not prime.")
```
3. Write a C program to reverse a given string. ```c
#include <stdio.h>
#include <string.h>
void reverse_string(char* str) {
int length = strlen(str);
for (int i = 0; i < length/2; i++) {
char temp = str[i];
str[i] = str[length - i - 1];
str[length - i - 1] = temp;
}
}
int main() {
char str[100];
printf("Enter a string: ");
gets(str);
reverse_string(str);
printf("Reversed string: %s", str);
return 0;
}
```
Note: The code provided above is just examples for the coding questions. Please ensure to compile and test the programs before using them in production.
Conclusion:
In this article, we discussed multiple-choice questions, short answer questions, and coding questions related to computer science and programming. These questions cover various aspects of computer knowledge and can be used for self-assessment or preparation for exams or interviews.。
