AES对称加密算法源码
aes加密算法的输入c语言实例
aes加密算法的输入c语言实例1.引言1.1 概述概述部分应该对文章的主题进行一个简要介绍,提供一些背景信息和基本概念,以帮助读者了解接下来要讨论的内容。
下面是一个示例:在当今信息安全领域,数据的加密和保护是至关重要的。
随着互联网的发展和应用的广泛,如何确保用户的机密信息在传输和存储过程中不被未经授权的人访问和窃取,成为了一个极具挑战性的问题。
为了应对这个问题,许多加密算法被开发和广泛应用,其中AES(Advanced Encryption Standard,高级加密标准)算法就是其中之一。
AES算法是一种对称加密算法,它可以对数据进行高强度的加密和解密,以保护数据的机密性。
它是目前最常用和最可靠的加密算法之一,被广泛应用于各种安全通信和数据存储场景。
AES算法采用了分组加密和替代-置换网络结构,通过多轮的迭代运算和密钥扩展过程,将输入的明文数据转换为密文数据。
解密过程与加密过程相反,通过逆向的操作将密文数据恢复为明文数据。
本文的主要目的是介绍如何使用C语言来实现AES加密算法。
在接下来的内容中,我们将首先简要介绍AES算法的基本原理和步骤,然后详细讲解如何使用C语言来实现这些步骤。
通过本文的学习,读者将可以了解AES算法的基本运作原理,并掌握使用C语言编写AES加密算法的技巧。
在下一节中,我们将开始介绍AES加密算法的基本原理和步骤。
1.2 文章结构文章结构部分将对本文的组织结构和各章节内容进行介绍。
本文分为以下几个部分:1. 引言:本部分包括概述、文章结构和目的三个小节。
在概述中,将简要介绍AES加密算法和其在信息安全领域的重要性。
文章结构部分将重点介绍本文的整体组织架构和各章节内容的概括。
目的部分将明确本文的主要目标和意义。
2. 正文:本部分包括AES加密算法简介和C语言实现AES算法的基本步骤两个小节。
在AES加密算法简介中,将对AES算法的基本原理进行阐述,包括密钥长度、分组长度、轮数等方面的内容。
JAVA实现AES的加密和解密算法

JAVA实现AES的加密和解密算法AES(高级加密标准)是一种对称加密算法,可以通过Java的javax.crypto库来实现。
下面我们将介绍一种基于Java的AES加密和解密算法的实现方法。
1.导入所需的包在Java中使用AES加密和解密算法需要导入以下两个包:```import javax.crypto.Cipher;import javax.crypto.spec.SecretKeySpec;```2.创建加密和解密函数首先,我们需要创建加密函数和解密函数。
加密函数将输入的明文数据加密为密文,解密函数将输入的密文数据解密为明文。
```javaprivate static byte[] encrypt(byte[] key, byte[] data) throws ExceptionSecretKeySpec secretKeySpec = new SecretKeySpec(key, "AES");Cipher cipher = Cipher.getInstance("AES/ECB/PKCS5Padding");cipher.init(Cipher.ENCRYPT_MODE, secretKeySpec);return cipher.doFinal(data);private static byte[] decrypt(byte[] key, byte[] encryptedData) throws ExceptionSecretKeySpec secretKeySpec = new SecretKeySpec(key, "AES");Cipher cipher = Cipher.getInstance("AES/ECB/PKCS5Padding");cipher.init(Cipher.DECRYPT_MODE, secretKeySpec);return cipher.doFinal(encryptedData);```3.测试加密和解密函数为了验证加密和解密函数的正确性,我们可以创建一个测试函数来测试它们。
AES加密C语言实现代码
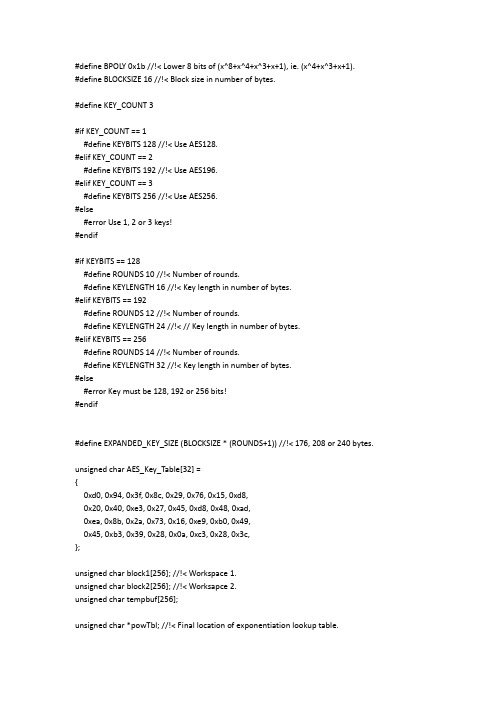
#define BPOLY 0x1b //!< Lower 8 bits of (x^8+x^4+x^3+x+1), ie. (x^4+x^3+x+1).#define BLOCKSIZE 16 //!< Block size in number of bytes.#define KEY_COUNT 3#if KEY_COUNT == 1#define KEYBITS 128 //!< Use AES128.#elif KEY_COUNT == 2#define KEYBITS 192 //!< Use AES196.#elif KEY_COUNT == 3#define KEYBITS 256 //!< Use AES256.#else#error Use 1, 2 or 3 keys!#endif#if KEYBITS == 128#define ROUNDS 10 //!< Number of rounds.#define KEYLENGTH 16 //!< Key length in number of bytes.#elif KEYBITS == 192#define ROUNDS 12 //!< Number of rounds.#define KEYLENGTH 24 //!< // Key length in number of bytes.#elif KEYBITS == 256#define ROUNDS 14 //!< Number of rounds.#define KEYLENGTH 32 //!< Key length in number of bytes.#else#error Key must be 128, 192 or 256 bits!#endif#define EXPANDED_KEY_SIZE (BLOCKSIZE * (ROUNDS+1)) //!< 176, 208 or 240 bytes.unsigned char AES_Key_Table[32] ={0xd0, 0x94, 0x3f, 0x8c, 0x29, 0x76, 0x15, 0xd8,0x20, 0x40, 0xe3, 0x27, 0x45, 0xd8, 0x48, 0xad,0xea, 0x8b, 0x2a, 0x73, 0x16, 0xe9, 0xb0, 0x49,0x45, 0xb3, 0x39, 0x28, 0x0a, 0xc3, 0x28, 0x3c,};unsigned char block1[256]; //!< Workspace 1.unsigned char block2[256]; //!< Worksapce 2.unsigned char tempbuf[256];unsigned char *powTbl; //!< Final location of exponentiation lookup table.unsigned char *logTbl; //!< Final location of logarithm lookup table. unsigned char *sBox; //!< Final location of s-box.unsigned char *sBoxInv; //!< Final location of inverse s-box. unsigned char *expandedKey; //!< Final location of expanded key.void CalcPowLog(unsigned char *powTbl, unsigned char *logTbl) {unsigned char i = 0;unsigned char t = 1;do {// Use 0x03 as root for exponentiation and logarithms.powTbl[i] = t;logTbl[t] = i;i++;// Muliply t by 3 in GF(2^8).t ^= (t << 1) ^ (t & 0x80 ? BPOLY : 0);}while( t != 1 ); // Cyclic properties ensure that i < 255.powTbl[255] = powTbl[0]; // 255 = '-0', 254 = -1, etc.}void CalcSBox( unsigned char * sBox ){unsigned char i, rot;unsigned char temp;unsigned char result;// Fill all entries of sBox[].i = 0;do {//Inverse in GF(2^8).if( i > 0 ){temp = powTbl[ 255 - logTbl[i] ];}else{temp = 0;}// Affine transformation in GF(2).result = temp ^ 0x63; // Start with adding a vector in GF(2).for( rot = 0; rot < 4; rot++ ){// Rotate left.temp = (temp<<1) | (temp>>7);// Add rotated byte in GF(2).result ^= temp;}// Put result in table.sBox[i] = result;} while( ++i != 0 );}void CalcSBoxInv( unsigned char * sBox, unsigned char * sBoxInv ) {unsigned char i = 0;unsigned char j = 0;// Iterate through all elements in sBoxInv using i.do {// Search through sBox using j.do {// Check if current j is the inverse of current i.if( sBox[ j ] == i ){// If so, set sBoxInc and indicate search finished.sBoxInv[ i ] = j;j = 255;}} while( ++j != 0 );} while( ++i != 0 );}void CycleLeft( unsigned char * row ){// Cycle 4 bytes in an array left once.unsigned char temp = row[0];row[0] = row[1];row[1] = row[2];row[2] = row[3];row[3] = temp;}void InvMixColumn( unsigned char * column ){unsigned char r0, r1, r2, r3;r0 = column[1] ^ column[2] ^ column[3];r1 = column[0] ^ column[2] ^ column[3];r2 = column[0] ^ column[1] ^ column[3];r3 = column[0] ^ column[1] ^ column[2];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);r0 ^= column[0] ^ column[1];r1 ^= column[1] ^ column[2];r2 ^= column[2] ^ column[3];r3 ^= column[0] ^ column[3];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);r0 ^= column[0] ^ column[2];r1 ^= column[1] ^ column[3];r2 ^= column[0] ^ column[2];r3 ^= column[1] ^ column[3];column[0] = (column[0] << 1) ^ (column[0] & 0x80 ? BPOLY : 0);column[1] = (column[1] << 1) ^ (column[1] & 0x80 ? BPOLY : 0);column[2] = (column[2] << 1) ^ (column[2] & 0x80 ? BPOLY : 0);column[3] = (column[3] << 1) ^ (column[3] & 0x80 ? BPOLY : 0);column[0] ^= column[1] ^ column[2] ^ column[3];r0 ^= column[0];r1 ^= column[0];r2 ^= column[0];r3 ^= column[0];column[0] = r0;column[1] = r1;column[2] = r2;column[3] = r3;}void SubBytes( unsigned char * bytes, unsigned char count ){do {*bytes = sBox[ *bytes ]; // Substitute every byte in state.bytes++;} while( --count );}void InvSubBytesAndXOR( unsigned char * bytes, unsigned char * key, unsigned char count ){do {// *bytes = sBoxInv[ *bytes ] ^ *key; // Inverse substitute every byte in state and add key.*bytes = block2[ *bytes ] ^ *key; // Use block2 directly. Increases speed.bytes++;key++;} while( --count );}void InvShiftRows( unsigned char * state ){unsigned char temp;// Note: State is arranged column by column.// Cycle second row right one time.temp = state[ 1 + 3*4 ];state[ 1 + 3*4 ] = state[ 1 + 2*4 ];state[ 1 + 2*4 ] = state[ 1 + 1*4 ];state[ 1 + 1*4 ] = state[ 1 + 0*4 ];state[ 1 + 0*4 ] = temp;// Cycle third row right two times.temp = state[ 2 + 0*4 ];state[ 2 + 0*4 ] = state[ 2 + 2*4 ];state[ 2 + 2*4 ] = temp;temp = state[ 2 + 1*4 ];state[ 2 + 1*4 ] = state[ 2 + 3*4 ];state[ 2 + 3*4 ] = temp;// Cycle fourth row right three times, ie. left once.temp = state[ 3 + 0*4 ];state[ 3 + 0*4 ] = state[ 3 + 1*4 ];state[ 3 + 1*4 ] = state[ 3 + 2*4 ];state[ 3 + 2*4 ] = state[ 3 + 3*4 ];state[ 3 + 3*4 ] = temp;}void InvMixColumns( unsigned char * state ){InvMixColumn( state + 0*4 );InvMixColumn( state + 1*4 );InvMixColumn( state + 2*4 );InvMixColumn( state + 3*4 );}void XORBytes( unsigned char * bytes1, unsigned char * bytes2, unsigned char count ) {do {*bytes1 ^= *bytes2; // Add in GF(2), ie. XOR.bytes1++;bytes2++;} while( --count );}void CopyBytes( unsigned char * to, unsigned char * from, unsigned char count ) {do {*to = *from;to++;from++;} while( --count );}void KeyExpansion( unsigned char * expandedKey ){unsigned char temp[4];unsigned char i;unsigned char Rcon[4] = { 0x01, 0x00, 0x00, 0x00 }; // Round constant.unsigned char * key = AES_Key_Table;// Copy key to start of expanded key.i = KEYLENGTH;do {*expandedKey = *key;expandedKey++;key++;} while( --i );// Prepare last 4 bytes of key in temp.expandedKey -= 4;temp[0] = *(expandedKey++);temp[1] = *(expandedKey++);temp[2] = *(expandedKey++);temp[3] = *(expandedKey++);// Expand key.i = KEYLENGTH;while( i < BLOCKSIZE*(ROUNDS+1) ){// Are we at the start of a multiple of the key size?if( (i % KEYLENGTH) == 0 ){CycleLeft( temp ); // Cycle left once.SubBytes( temp, 4 ); // Substitute each byte.XORBytes( temp, Rcon, 4 ); // Add constant in GF(2).*Rcon = (*Rcon << 1) ^ (*Rcon & 0x80 ? BPOLY : 0);}// Keysize larger than 24 bytes, ie. larger that 192 bits?#if KEYLENGTH > 24// Are we right past a block size?else if( (i % KEYLENGTH) == BLOCKSIZE ) {SubBytes( temp, 4 ); // Substitute each byte.}#endif// Add bytes in GF(2) one KEYLENGTH away.XORBytes( temp, expandedKey - KEYLENGTH, 4 );// Copy result to current 4 bytes.*(expandedKey++) = temp[ 0 ];*(expandedKey++) = temp[ 1 ];*(expandedKey++) = temp[ 2 ];*(expandedKey++) = temp[ 3 ];i += 4; // Next 4 bytes.}}void InvCipher( unsigned char * block, unsigned char * expandedKey ) {unsigned char round = ROUNDS-1;expandedKey += BLOCKSIZE * ROUNDS;XORBytes( block, expandedKey, 16 );expandedKey -= BLOCKSIZE;do {InvShiftRows( block );InvSubBytesAndXOR( block, expandedKey, 16 );expandedKey -= BLOCKSIZE;InvMixColumns( block );} while( --round );InvShiftRows( block );InvSubBytesAndXOR( block, expandedKey, 16 );}void aesDecInit(void){powTbl = block1;logTbl = block2;CalcPowLog( powTbl, logTbl );sBox = tempbuf;CalcSBox( sBox );expandedKey = block1;KeyExpansion( expandedKey );sBoxInv = block2; // Must be block2.CalcSBoxInv( sBox, sBoxInv );}void aesDecrypt( unsigned char * buffer, unsigned char * chainBlock ) {unsigned char temp[ BLOCKSIZE ];CopyBytes( temp, buffer, BLOCKSIZE );InvCipher( buffer, expandedKey );XORBytes( buffer, chainBlock, BLOCKSIZE );CopyBytes( chainBlock, temp, BLOCKSIZE );}unsigned char Multiply( unsigned char num, unsigned char factor ){unsigned char mask = 1;unsigned char result = 0;while( mask != 0 ){// Check bit of factor given by mask.if( mask & factor ){// Add current multiple of num in GF(2).result ^= num;}// Shift mask to indicate next bit.mask <<= 1;// Double num.num = (num << 1) ^ (num & 0x80 ? BPOLY : 0);}return result;}unsigned char DotProduct( unsigned char * vector1, unsigned char * vector2 ) {unsigned char result = 0;result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1++, *vector2++ );result ^= Multiply( *vector1 , *vector2 );return result;}void MixColumn( unsigned char * column ){unsigned char row[8] = {0x02, 0x03, 0x01, 0x01, 0x02, 0x03, 0x01, 0x01};// Prepare first row of matrix twice, to eliminate need for cycling.unsigned char result[4];// Take dot products of each matrix row and the column vector.result[0] = DotProduct( row+0, column );result[1] = DotProduct( row+3, column );result[2] = DotProduct( row+2, column );result[3] = DotProduct( row+1, column );// Copy temporary result to original column.column[0] = result[0];column[1] = result[1];column[2] = result[2];column[3] = result[3];}void MixColumns( unsigned char * state ){MixColumn( state + 0*4 );MixColumn( state + 1*4 );MixColumn( state + 2*4 );MixColumn( state + 3*4 );}void ShiftRows( unsigned char * state ){unsigned char temp;// Note: State is arranged column by column.// Cycle second row left one time.temp = state[ 1 + 0*4 ];state[ 1 + 0*4 ] = state[ 1 + 1*4 ];state[ 1 + 1*4 ] = state[ 1 + 2*4 ];state[ 1 + 2*4 ] = state[ 1 + 3*4 ];state[ 1 + 3*4 ] = temp;// Cycle third row left two times.temp = state[ 2 + 0*4 ];state[ 2 + 0*4 ] = state[ 2 + 2*4 ];state[ 2 + 2*4 ] = temp;temp = state[ 2 + 1*4 ];state[ 2 + 1*4 ] = state[ 2 + 3*4 ];state[ 2 + 3*4 ] = temp;// Cycle fourth row left three times, ie. right once.temp = state[ 3 + 3*4 ];state[ 3 + 3*4 ] = state[ 3 + 2*4 ];state[ 3 + 2*4 ] = state[ 3 + 1*4 ];state[ 3 + 1*4 ] = state[ 3 + 0*4 ];state[ 3 + 0*4 ] = temp;}void Cipher( unsigned char * block, unsigned char * expandedKey ) {unsigned char round = ROUNDS-1;XORBytes( block, expandedKey, 16 );expandedKey += BLOCKSIZE;do {SubBytes( block, 16 );ShiftRows( block );MixColumns( block );XORBytes( block, expandedKey, 16 );expandedKey += BLOCKSIZE;} while( --round );SubBytes( block, 16 );ShiftRows( block );XORBytes( block, expandedKey, 16 );}void aesEncInit(void){powTbl = block1;logTbl = tempbuf;CalcPowLog( powTbl, logTbl );sBox = block2;CalcSBox( sBox );expandedKey = block1;KeyExpansion( expandedKey );}void aesEncrypt( unsigned char * buffer, unsigned char * chainBlock ) {XORBytes( buffer, chainBlock, BLOCKSIZE );Cipher( buffer, expandedKey );CopyBytes( chainBlock, buffer, BLOCKSIZE );}#include <string.h>void AES_Test(void){unsigned char dat[16]="0123456789ABCDEF";unsigned char chainCipherBlock[16];unsigned char i;for(i=0;i<32;i++) AES_Key_Table[i]=i;//做运算之前先要设置好密钥,这里只是设置密钥的DEMO。
C#对称加密和非对称加密(AES和RSA)

C#对称加密和⾮对称加密(AES和RSA)using System;using System.Collections.Generic;using System.IO;using System.Security.Cryptography;using System.Text;namespace 加密{class Program{static void Main(string[] args){//RSA//var dicKey = RSAHelper.GetKey();//Console.WriteLine($"{dicKey["PublicKey"]}\r\n{dicKey["PrivateKey"]}");//string strText = "aaabbbcc";//Console.WriteLine("要加密的字符串是:{0}", strText);//string str1 = RSAHelper.Encrypt(strText, dicKey["PublicKey"]);//Console.WriteLine("加密后的字符串:{0}", str1);//string str2 = RSAHelper.Decrypt(str1, dicKey["PrivateKey"]);//Console.WriteLine("解密后的字符串:{0}", str2);//AESstring password = "abcAE#$M&*987";Console.WriteLine($"原始密码为:{password} ");// AES的key⽀持128位,最⼤⽀持256位。
256位需要32个字节。
Python中如何使用AES算法进行加密和解密
Python中如何使用AES算法进行加密和解密一、引言随着互联网的快速发展,财务交易、个人资料和敏感数据被传输在网络上的频率越来越高。
因此,保护数据的安全性和私密性成为了一项至关重要的任务。
加密技术是一种重要的手段,可以解决这个问题。
其中最受欢迎和应用广泛的加密算法是AES。
本文主要介绍Python中如何使用AES算法进行加密和解密的方法。
二、AES算法简介AES算法是高级加密标准(Advanced Encryption Standard)的缩写。
它是目前广泛使用的对称加密算法之一,是一种分组密码,加密和解密使用相同的秘钥(Key)进行。
AES算法的加密和解密都是基于密钥和明文的操作。
AES算法对明文进行加密时需要三个参数:明文、密钥和向量(IV),其中向量是用于增加随机性和异质性以增强密码体制的安全性的。
加密后,得到的密文只有通过使用相同的密钥和向量才能被解密。
因此,必须确保密钥和向量的安全性。
AES算法的强度与密钥长度有关,通常使用128、192或256位密钥。
三、Python中使用AES算法加密和解密的方法Python中使用AES算法加密和解密需要使用Crypto库,它是Python中专门提供密码学操作的库。
在使用之前,需要先安装Crypto 库:```pythonpip install pycrypto```在Crypto库中,有很多算法可以使用。
在这里,我们使用AES算法。
首先,需要导入Crypto库中的AES模块,如下所示:```pythonfrom Crypto.Cipher import AES```接下来,定义用于加密和解密的key和iv:```pythonkey = '0123456789abcdef'iv = 'fedcba9876543210'```key和iv都是以字符串形式定义的,长度分别为16个字符(128位)和16个字符(128位)。
aesencrypt函数

aesencrypt函数AES(Advanced Encryption Standard)是一种对称加密算法,广泛用于保护信息的安全。
在编程中,你可以使用编程语言提供的库或模块来实现AES加密。
以下是一个通用的AES加密函数示例,使用Python和Crypto库:首先,确保你已经安装了Crypto库。
你可以使用以下命令安装:pip install pycryptodome然后,你可以使用以下示例代码创建一个AES加密函数:from Crypto.Cipher import AESfrom Crypto.Random import get_random_bytesfrom Crypto.Util.Padding import pad, unpadimport base64def aes_encrypt(data, key):# 生成16字节的随机初始化向量iv = get_random_bytes(16)# 创建AES加密对象cipher = AES.new(key, AES.MODE_CBC, iv)# 使用PKCS7填充对数据进行加密ciphertext = cipher.encrypt(pad(data.encode('utf-8'), AES.block_size))# 将加密后的数据和初始化向量进行Base64编码encrypted_data = base64.b64encode(iv + ciphertext).decode('utf-8')return encrypted_datadef aes_decrypt(encrypted_data, key):# 对Base64编码的数据进行解码encrypted_data = base64.b64decode(encrypted_data)# 提取初始化向量iv = encrypted_data[:16]# 创建AES解密对象cipher = AES.new(key, AES.MODE_CBC, iv)# 解密数据并去除填充decrypted_data = unpad(cipher.decrypt(encrypted_data[16:]),AES.block_size).decode('utf-8')return decrypted_data# 示例用法key = b'ThisIsASecretKey'data_to_encrypt = 'Hello, AES Encryption!'encrypted_data = aes_encrypt(data_to_encrypt, key)print('Encrypted Data:', encrypted_data)decrypted_data = aes_decrypt(encrypted_data, key)print('Decrypted Data:', decrypted_data)请注意,实际应用中,密钥的生成、存储和传递都需要谨慎处理,以确保系统的安全性。
AES-256算法C语言实现
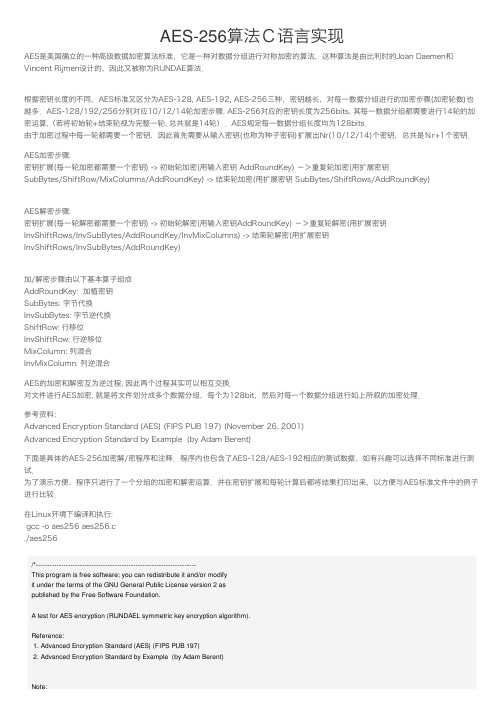
AES-256算法C语⾔实现AES是美国确⽴的⼀种⾼级数据加密算法标准,它是⼀种对数据分组进⾏对称加密的算法,这种算法是由⽐利时的Joan Daemen和Vincent Rijmen设计的,因此⼜被称为RIJNDAE算法.根据密钥长度的不同,AES标准⼜区分为AES-128, AES-192, AES-256三种,密钥越长,对每⼀数据分组进⾏的加密步骤(加密轮数)也越多.AES-128/192/256分别对应10/12/14轮加密步骤. AES-256对应的密钥长度为256bits, 其每⼀数据分组都需要进⾏14轮的加密运算,(若将初始轮+结束轮视为完整⼀轮, 总共就是14轮).AES规定每⼀数据分组长度均为128bits.由于加密过程中每⼀轮都需要⼀个密钥,因此⾸先需要从输⼊密钥(也称为种⼦密码)扩展出Nr(10/12/14)个密钥,总共是Nr+1个密钥.AES加密步骤:密钥扩展(每⼀轮加密都需要⼀个密钥) -> 初始轮加密(⽤输⼊密钥 AddRoundKey) ->重复轮加密(⽤扩展密钥SubBytes/ShiftRow/MixColumns/AddRoundKey) -> 结束轮加密(⽤扩展密钥 SubBytes/ShiftRows/AddRoundKey)AES解密步骤:密钥扩展(每⼀轮解密都需要⼀个密钥) -> 初始轮解密(⽤输⼊密钥AddRoundKey) ->重复轮解密(⽤扩展密钥InvShiftRows/InvSubBytes/AddRoundKey/InvMixColumns) -> 结束轮解密(⽤扩展密钥InvShiftRows/InvSubBytes/AddRoundKey)加/解密步骤由以下基本算⼦组成AddRoundKey: 加植密钥SubBytes: 字节代换InvSubBytes: 字节逆代换ShiftRow: ⾏移位InvShiftRow: ⾏逆移位MixColumn: 列混合InvMixColumn: 列逆混合AES的加密和解密互为逆过程, 因此两个过程其实可以相互交换.对⽂件进⾏AES加密, 就是将⽂件划分成多个数据分组,每个为128bit,然后对每⼀个数据分组进⾏如上所叙的加密处理.参考资料:Advanced Encryption Standard (AES) (FIPS PUB 197) (November 26, 2001)Advanced Encryption Standard by Example (by Adam Berent)下⾯是具体的AES-256加密解/密程序和注释.程序内也包含了AES-128/AES-192相应的测试数据,如有兴趣可以选择不同标准进⾏测试.为了演⽰⽅便,程序只进⾏了⼀个分组的加密和解密运算.并在密钥扩展和每轮计算后都将结果打印出来,以⽅便与AES标准⽂件中的例⼦进⾏⽐较.在Linux环境下编译和执⾏:gcc -o aes256 aes256.c./aes256/*---------------------------------------------------------------------This program is free software; you can redistribute it and/or modifyit under the terms of the GNU General Public License version 2 aspublished by the Free Software Foundation.A test for AES encryption (RIJNDAEL symmetric key encryption algorithm).Reference:1. Advanced Encryption Standard (AES) (FIPS PUB 197)2. Advanced Encryption Standard by Example (by Adam Berent)Note:1. Standard and parameters.Key Size Block Size Number of Rounds(Nk words) (Nb words) (Nr)AES-128 4 4 10AES-192 6 4 12AES-256 8 4 14Midas Zhoumidaszhou@https:///widora/wegi----------------------------------------------------------------------*/#include <stdio.h>#include <stdint.h>#include <string.h>/* S_BOX S盒 */static const uint8_t sbox[256] = {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84, 0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2, 0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73, 0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB, 0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF, 0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16 };/* Reverse S_BOX 反向S盒 */static const uint8_t rsbox[256] = {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB, 0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB, 0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E, 0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25, 0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92, 0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84, 0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06, 0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B, 0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73, 0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E, 0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B, 0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4, 0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F, 0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF, 0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61, 0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D };/* Galois Field Multiplication E-table GF乘法E表 */static const uint8_t Etab[256]= {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x01, 0x03, 0x05, 0x0F, 0x11, 0x33, 0x55, 0xFF, 0x1A, 0x2E, 0x72, 0x96, 0xA1, 0xF8, 0x13, 0x35,0xE5, 0x34, 0x5C, 0xE4, 0x37, 0x59, 0xEB, 0x26, 0x6A, 0xBE, 0xD9, 0x70, 0x90, 0xAB, 0xE6, 0x31,0x53, 0xF5, 0x04, 0x0C, 0x14, 0x3C, 0x44, 0xCC, 0x4F, 0xD1, 0x68, 0xB8, 0xD3, 0x6E, 0xB2, 0xCD,0x4C, 0xD4, 0x67, 0xA9, 0xE0, 0x3B, 0x4D, 0xD7, 0x62, 0xA6, 0xF1, 0x08, 0x18, 0x28, 0x78, 0x88,0x83, 0x9E, 0xB9, 0xD0, 0x6B, 0xBD, 0xDC, 0x7F, 0x81, 0x98, 0xB3, 0xCE, 0x49, 0xDB, 0x76, 0x9A,0xB5, 0xC4, 0x57, 0xF9, 0x10, 0x30, 0x50, 0xF0, 0x0B, 0x1D, 0x27, 0x69, 0xBB, 0xD6, 0x61, 0xA3,0xFE, 0x19, 0x2B, 0x7D, 0x87, 0x92, 0xAD, 0xEC, 0x2F, 0x71, 0x93, 0xAE, 0xE9, 0x20, 0x60, 0xA0,0xFB, 0x16, 0x3A, 0x4E, 0xD2, 0x6D, 0xB7, 0xC2, 0x5D, 0xE7, 0x32, 0x56, 0xFA, 0x15, 0x3F, 0x41,0xC3, 0x5E, 0xE2, 0x3D, 0x47, 0xC9, 0x40, 0xC0, 0x5B, 0xED, 0x2C, 0x74, 0x9C, 0xBF, 0xDA, 0x75,0x9F, 0xBA, 0xD5, 0x64, 0xAC, 0xEF, 0x2A, 0x7E, 0x82, 0x9D, 0xBC, 0xDF, 0x7A, 0x8E, 0x89, 0x80,0x9B, 0xB6, 0xC1, 0x58, 0xE8, 0x23, 0x65, 0xAF, 0xEA, 0x25, 0x6F, 0xB1, 0xC8, 0x43, 0xC5, 0x54,0xFC, 0x1F, 0x21, 0x63, 0xA5, 0xF4, 0x07, 0x09, 0x1B, 0x2D, 0x77, 0x99, 0xB0, 0xCB, 0x46, 0xCA,0x45, 0xCF, 0x4A, 0xDE, 0x79, 0x8B, 0x86, 0x91, 0xA8, 0xE3, 0x3E, 0x42, 0xC6, 0x51, 0xF3, 0x0E,0x12, 0x36, 0x5A, 0xEE, 0x29, 0x7B, 0x8D, 0x8C, 0x8F, 0x8A, 0x85, 0x94, 0xA7, 0xF2, 0x0D, 0x17,0x39, 0x4B, 0xDD, 0x7C, 0x84, 0x97, 0xA2, 0xFD, 0x1C, 0x24, 0x6C, 0xB4, 0xC7, 0x52, 0xF6, 0x01};/* Galois Field Multiplication L-table GF乘法L表 */static const uint8_t Ltab[256]= {/* 0 1 2 3 4 5 6 7 8 9 A B C D E F */0x0, 0x0, 0x19, 0x01, 0x32, 0x02, 0x1A, 0xC6, 0x4B, 0xC7, 0x1B, 0x68, 0x33, 0xEE, 0xDF, 0x03, // 00x64, 0x04, 0xE0, 0x0E, 0x34, 0x8D, 0x81, 0xEF, 0x4C, 0x71, 0x08, 0xC8, 0xF8, 0x69, 0x1C, 0xC1, // 10x7D, 0xC2, 0x1D, 0xB5, 0xF9, 0xB9, 0x27, 0x6A, 0x4D, 0xE4, 0xA6, 0x72, 0x9A, 0xC9, 0x09, 0x78, // 20x65, 0x2F, 0x8A, 0x05, 0x21, 0x0F, 0xE1, 0x24, 0x12, 0xF0, 0x82, 0x45, 0x35, 0x93, 0xDA, 0x8E, // 30x96, 0x8F, 0xDB, 0xBD, 0x36, 0xD0, 0xCE, 0x94, 0x13, 0x5C, 0xD2, 0xF1, 0x40, 0x46, 0x83, 0x38, // 40x66, 0xDD, 0xFD, 0x30, 0xBF, 0x06, 0x8B, 0x62, 0xB3, 0x25, 0xE2, 0x98, 0x22, 0x88, 0x91, 0x10, // 50x7E, 0x6E, 0x48, 0xC3, 0xA3, 0xB6, 0x1E, 0x42, 0x3A, 0x6B, 0x28, 0x54, 0xFA, 0x85, 0x3D, 0xBA, // 60x2B, 0x79, 0x0A, 0x15, 0x9B, 0x9F, 0x5E, 0xCA, 0x4E, 0xD4, 0xAC, 0xE5, 0xF3, 0x73, 0xA7, 0x57, // 70xAF, 0x58, 0xA8, 0x50, 0xF4, 0xEA, 0xD6, 0x74, 0x4F, 0xAE, 0xE9, 0xD5, 0xE7, 0xE6, 0xAD, 0xE8, // 80x2C, 0xD7, 0x75, 0x7A, 0xEB, 0x16, 0x0B, 0xF5, 0x59, 0xCB, 0x5F, 0xB0, 0x9C, 0xA9, 0x51, 0xA0, // 90x7F, 0x0C, 0xF6, 0x6F, 0x17, 0xC4, 0x49, 0xEC, 0xD8, 0x43, 0x1F, 0x2D, 0xA4, 0x76, 0x7B, 0xB7, // A0xCC, 0xBB, 0x3E, 0x5A, 0xFB, 0x60, 0xB1, 0x86, 0x3B, 0x52, 0xA1, 0x6C, 0xAA, 0x55, 0x29, 0x9D, // B0x97, 0xB2, 0x87, 0x90, 0x61, 0xBE, 0xDC, 0xFC, 0xBC, 0x95, 0xCF, 0xCD, 0x37, 0x3F, 0x5B, 0xD1, // C0x53, 0x39, 0x84, 0x3C, 0x41, 0xA2, 0x6D, 0x47, 0x14, 0x2A, 0x9E, 0x5D, 0x56, 0xF2, 0xD3, 0xAB, // D0x44, 0x11, 0x92, 0xD9, 0x23, 0x20, 0x2E, 0x89, 0xB4, 0x7C, 0xB8, 0x26, 0x77, 0x99, 0xE3, 0xA5, // E0x67, 0x4A, 0xED, 0xDE, 0xC5, 0x31, 0xFE, 0x18, 0x0D, 0x63, 0x8C, 0x80, 0xC0, 0xF7, 0x70, 0x07 // F};/* RCON 表 */static const uint32_t Rcon[15]= {0x01000000,0x02000000,0x04000000,0x08000000,0x10000000,0x20000000,0x40000000,0x80000000,0x1B000000,0x36000000,0x6C000000,0xD8000000,0xAB000000,0x4D000000,0x9A000000};/* Functions */void print_state(const uint8_t *s); /* 打印分组数据 */int aes_ShiftRows(uint8_t *state); /* ⾏移位 */int aes_InvShiftRows(uint8_t *state); /* ⾏逆移位 */int aes_ExpRoundKeys(uint8_t Nr, uint8_t Nk, const uint8_t *inkey, uint32_t *keywords); /* 密钥扩展 */int aes_AddRoundKey(uint8_t Nr, uint8_t Nk, uint8_t round, uint8_t *state, const uint32_t *keywords); /* 加植密钥 */ int aes_EncryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state); /* 分组加密 */int aes_DecryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state); /* 分组解密 *//*==============MAIN===============*/int main(void){int i,k;const uint8_t Nb=4; /* 分组长度 Block size in words, 4/4/4 for AES-128/192/256 */uint8_t Nk; /* 密钥长度 column number, as of 4xNk, 4/6/8 for AES-128/192/256 */uint8_t Nr; /* 加密轮数 Number of rounds, 10/12/14 for AES-128/192/256 */uint8_t state[4*4]; /* 分组数据 State array, data in row sequence! */uint64_t ns; /* 总分组数 Total number of states *//* 待加密数据 */const uint8_t input_msg[]= {0x00,0x11,0x22,0x33,0x44,0x55,0x66,0x77,0x88,0x99,0xaa,0xbb,0xcc,0xdd,0xee,0xff};/* AES-128/192/256 对应的密钥长度,加密轮数, 输⼊密钥 */#if 0 /* TEST data --- AES-128 */Nk=4;Nr=10;const uint8_t inkey[4*4]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f};#endif#if 0 /* TEST data --- AES-192 */Nk=6;Nr=12;const uint8_t inkey[4*6]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f,0x10,0x11,0x12,0x13,0x14,0x15,0x16,0x17};#endif#if 1 /* TEST data --- AES-256 */Nk=8;Nr=14;const uint8_t inkey[4*8]= { /* Nb*Nk */0x00,0x01,0x02,0x03,0x04,0x05,0x06,0x07,0x08,0x09,0x0a,0x0b,0x0c,0x0d,0x0e,0x0f,0x10,0x11,0x12,0x13,0x14,0x15,0x16,0x17,0x18,0x19,0x1a,0x1b,0x1c,0x1d,0x1e,0x1f};#endif/* 密钥扩展测试数据------TEST: For Key expansion */#if 0Nk=4;Nr=10;const uint8_t inkey[4*4]= /* Nb*Nk */{ 0x2b, 0x7e, 0x15, 0x16, 0x28, 0xae, 0xd2, 0xa6, 0xab, 0xf7, 0x15, 0x88, 0x09, 0xcf, 0x4f, 0x3c }; #endif#if 0Nk=6;Nr=12;const uint8_t inkey[4*6]= /* Nb*Nk */{ 0x8e, 0x73, 0xb0, 0xf7, 0xda, 0x0e, 0x64, 0x52, 0xc8, 0x10, 0xf3, 0x2b,0x80, 0x90, 0x79, 0xe5, 0x62, 0xf8, 0xea, 0xd2, 0x52, 0x2c, 0x6b, 0x7b };#endif#if 0Nk=8;const uint8_t inkey[4*8]= /* Nb*Nk */{ 0x60, 0x3d, 0xeb, 0x10, 0x15, 0xca, 0x71, 0xbe, 0x2b, 0x73, 0xae, 0xf0, 0x85, 0x7d, 0x77, 0x81,0x1f, 0x35, 0x2c, 0x07, 0x3b, 0x61, 0x08, 0xd7, 0x2d, 0x98, 0x10, 0xa3, 0x09, 0x14, 0xdf, 0xf4 };#endifuint32_t keywords[Nb*(Nr+1)]; /* ⽤于存放扩展密钥,总共Nr+1把密钥 Nb==4, All expended keys, as of words in a column: 0xb0b1b2b3 *//* 从输⼊密钥产⽣Nk+1个轮密,每轮需要⼀个密钥 Generate round keys */aes_ExpRoundKeys(Nr, Nk, inkey, keywords);/* 数据分组数量,这⾥我们只设定为1组. Cal. total states *///ns=(strlen(input_msg)+15)/16;ns=1;/* 如果是多个分组,那么分别对每个分组进⾏加密,i=0 ~ ns-1 */i=0; /* i=0 ~ ns-1 *//* 将待加密数据放⼊到数据分组state[]中,注意:state[]中数据按column顺序存放! */bzero(state,16);for(k=0; k<16; k++)state[(k%4)*4+k/4]=input_msg[i*16+k];/* 加密数据分组 Encrypt each state */aes_EncryptState(Nr, Nk, keywords, state);/* 打印加密后的分组数据 */printf("***********************************\n");printf("******* Finish Encryption *******\n");printf("***********************************\n");print_state(state);/* 解密数据分组 Decrypt state */aes_DecryptState(Nr, Nk, keywords, state);//printf("Finish decrypt message, Round Nr=%d, KeySize Nk=%d, States ns=%llu.\n", Nr, Nk, ns);/* 打印解密后的分组数据 */printf("***********************************\n");printf("******* Finish Decryption *******\n");printf("***********************************\n");print_state(state);return 0;}/* 打印分组数据 Print state */void print_state(const uint8_t *s){int i,j;for(i=0; i<4; i++) {for(j=0; j<4; j++) {printf("%02x",s[i*4+j]);//printf("'%c'",s[i*4+j]); /* A control key MAY erase previous chars on screen! */printf(" ");}printf("\n");}printf("\n");}/*------------------------------⾏移位Shift operation of the state.Return:0 OK<0 Fails-------------------------------*/int aes_ShiftRows(uint8_t *state){int j,k;uint8_t tmp;if(state==NULL)return -1;for(k=0; k<4; k++) {/* each row shift k times */for(j=0; j<k; j++) {tmp=*(state+4*k); /* save the first byte *///memcpy(state+4*k, state+4*k+1, 3);memmove(state+4*k, state+4*k+1, 3);*(state+4*k+3)=tmp; /* set the last byte */}}return 0;}/*------------------------------⾏逆移位Shift operation of the state.@state[4*4]Return:0 OK<0 Fails-------------------------------*/int aes_InvShiftRows(uint8_t *state){int j,k;uint8_t tmp;if(state==NULL)return -1;for(k=0; k<4; k++) {/* each row shift k times */for(j=0; j<k; j++) {tmp=*(state+4*k+3); /* save the last byte */memmove(state+4*k+1, state+4*k, 3);*(state+4*k)=tmp; /* set the first byte */}}return 0;}/*-------------------------------------------------------------加植密钥Add round key to the state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256 @Nk: Key size, in words.@round: Current round number.@state: Pointer to state.@keywords[Nb*(Nr+1)]: All round keys, in words.int aes_AddRoundKey(uint8_t Nr, uint8_t Nk, uint8_t round, uint8_t *state, const uint32_t *keywords){int k;if(state==NULL || keywords==NULL)return -1;for(k=0; k<4*4; k++)state[k] = ( keywords[round*4+k%4]>>((3-(k>>2))<<3) &0xFF )^state[k];return 0;}/*----------------------------------------------------------------------------------------------------------密钥扩展从输⼊密钥(也称为种⼦密码)扩展出Nr(10/12/14)个密钥,总共是Nr+1个密钥Generate round keys.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key size, in words.@inkey[4*Nk]: Original key, 4*Nk bytes, arranged row by row.@keywords[Nb*(Nr+1)]: Output keys, in words. Nb*(Nr+1)one keywords(32 bytes) as one column of key_bytes(4 bytes)Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails---------------------------------------------------------------------------------------------------------------*/int aes_ExpRoundKeys(uint8_t Nr, uint8_t Nk, const uint8_t *inkey, uint32_t *keywords){int i;const int Nb=4;uint32_t temp;if(inkey==NULL || keywords==NULL)return -1;/* Re_arrange inkey to keywords, convert 4x8bytes each row_data to a 32bytes keyword, as a complex column_data. */ for( i=0; i<Nk; i++ ) {keywords[i]=(inkey[4*i]<<24)+(inkey[4*i+1]<<16)+(inkey[4*i+2]<<8)+inkey[4*i+3];}/* Expend round keys */for(i=Nk; i<Nb*(Nr+1); i++) {temp=keywords[i-1];if( i%Nk==0 ) {/* RotWord */temp=( temp<<8 )+( temp>>24 );/* Subword */temp=(sbox[temp>>24]<<24) +(sbox[(temp>>16)&0xFF]<<16) +(sbox[(temp>>8)&0xFF]<<8)+sbox[temp&0xFF];/* temp=SubWord(RotWord(temp)) XOR Rcon[i/Nk-1] */temp=temp ^ Rcon[i/Nk-1];}else if (Nk>6 && i%Nk==4 ) {/* Subword */temp=(sbox[temp>>24]<<24) +(sbox[(temp>>16)&0xFF]<<16) +(sbox[(temp>>8)&0xFF]<<8)+sbox[temp&0xFF];}/* Get keywords[i] */}/* Print all keys */for(i=0; i<Nb*(Nr+1); i++)printf("keywords[%d]=0x%08X\n", i, keywords[i]);return 0;}/*----------------------------------------------------------------------数据分组加密Encrypt state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key length, in words.@keywordss[Nb*(Nr+1)]: All round keys, in words.@state[4*4]: The state block.Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails------------------------------------------------------------------------*/int aes_EncryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state) {int i,k;uint8_t round;uint8_t mc[4]; /* Temp. var */if(keywords==NULL || state==NULL)return -1;/* 1. AddRoundKey: 加植密钥 */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, 0, state, keywords);print_state(state);/* 循环Nr-1轮加密运算 Run Nr round functions */for( round=1; round<Nr; round++) { /* Nr *//* 2. SubBytes: 字节代换 Substitue State Bytes with SBOX */printf(" --- SubBytes() Round:%d ---\n",round);for(k=0; k<16; k++)state[k]=sbox[state[k]];print_state(state);/* 3. ShiftRow: ⾏移位 Shift State Rows */printf(" --- ShiftRows() Round:%d ---\n",round);aes_ShiftRows(state);print_state(state);/* 4. MixColumn: 列混合 Mix State Cloumns *//* Galois Field Multiplication, Multi_Matrix:2 3 1 11 2 3 11 12 33 1 1 2Note:1. Any number multiplied by 1 is equal to the number itself.2. Any number multiplied by 0 is 0!*/printf(" --- MixColumn() Round:%d ---\n",round);mc[0]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[2])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[3])%0xFF] )^state[i+8]^state[i+12];mc[1]= state[i]^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[2])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[3])%0xFF] )^state[i+12];mc[2]= state[i]^state[i+4]^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[2])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[3])%0xFF] );mc[3]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[3])%0xFF] )^state[i+4]^state[i+8]^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[2])%0xFF] );state[i+0]=mc[0];state[i+4]=mc[1];state[i+8]=mc[2];state[i+12]=mc[3];}print_state(state);/* 5. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);} /* END Nr rounds *//* 6. SubBytes: 字节代换 Substitue State Bytes with SBOX */printf(" --- SubBytes() Round:%d ---\n",round);for(k=0; k<16; k++)state[k]=sbox[state[k]];print_state(state);/* 7. ShiftRow: ⾏移位 Shift State Rows */printf(" --- ShiftRows() Round:%d ---\n",round);aes_ShiftRows(state);print_state(state);/* 8. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);return 0;}/*----------------------------------------------------------------------Decrypt the state.@Nr: Number of rounds, 10/12/14 for AES-128/192/256@Nk: Key length, in words.@keywordss[Nb*(Nr+1)]: All round keys, in words.@state[4*4]: The state block.Note:1. The caller MUST ensure enough mem space of input params.Return:0 Ok<0 Fails------------------------------------------------------------------------*/int aes_DecryptState(uint8_t Nr, uint8_t Nk, uint32_t *keywords, uint8_t *state)int i,k;uint8_t round;uint8_t mc[4]; /* Temp. var */if(keywords==NULL || state==NULL)return -1;/* 1. AddRoundKey: 加植密钥 Add round key */printf(" --- Add Round_key ---\n");aes_AddRoundKey(Nr, Nk, Nr, state, keywords); /* From Nr_th round */ print_state(state);/* 循环Nr-1轮加密运算 Run Nr round functions */for( round=Nr-1; round>0; round--) { /* round [Nr-1 1] *//* 2. InvShiftRow: ⾏逆移位 InvShift State Rows */printf(" --- InvShiftRows() Round:%d ---\n",Nr-round);aes_InvShiftRows(state);print_state(state);/* 3. InvSubBytes: 字节逆代换 InvSubstitue State Bytes with R_SBOX */printf(" --- (Inv)SubBytes() Round:%d ---\n",Nr-round);for(k=0; k<16; k++)state[k]=rsbox[state[k]];print_state(state);/* 4. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key Round:%d ---\n", Nr-round);aes_AddRoundKey(Nr, Nk, round, state, keywords);print_state(state);/* 5. InvMixColumn: 列逆混合 Inverse Mix State Cloumns *//* Galois Field Multiplication, Multi_Matrix:0x0E 0x0B 0x0D 0x090x09 0x0E 0x0B 0x0D0x0D 0x09 0x0E 0x0B0x0B 0x0D 0x09 0x0ENote:1. Any number multiplied by 1 is equal to the number itself.2. Any number multiplied by 0 is 0!*/printf(" --- InvMixColumn() Round:%d ---\n",Nr-round);for(i=0; i<4; i++) { /* i as column index */mc[0]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0E])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0B])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0D])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x09])%0xFF] );mc[1]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x09])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0E])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0B])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0D])%0xFF] );mc[2]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0D])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x09])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x0E])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0B])%0xFF] );mc[3]= ( state[i]==0 ? 0 : Etab[(Ltab[state[i]]+Ltab[0x0B])%0xFF] )^( state[i+4]==0 ? 0 : Etab[(Ltab[state[i+4]]+Ltab[0x0D])%0xFF] )^( state[i+8]==0 ? 0 : Etab[(Ltab[state[i+8]]+Ltab[0x09])%0xFF] )^( state[i+12]==0 ? 0 : Etab[(Ltab[state[i+12]]+Ltab[0x0E])%0xFF] );state[i+0]=mc[0];state[i+4]=mc[1];state[i+8]=mc[2];state[i+12]=mc[3];print_state(state);} /* END Nr rounds *//* 6. InvShiftRow: ⾏逆移位 Inverse Shift State Rows */printf(" --- InvShiftRows() Round:%d ---\n",Nr-round);aes_InvShiftRows(state);print_state(state);/* 7. InvSubBytes: 字节逆代换 InvSubstitue State Bytes with SBOX */ printf(" --- InvSubBytes() Round:%d ---\n",Nr-round);for(k=0; k<16; k++)state[k]=rsbox[state[k]];print_state(state);/* 8. AddRoundKey: 加植密钥 Add State with Round Key */printf(" --- Add Round_key Round:%d ---\n",Nr-round);aes_AddRoundKey(Nr, Nk, 0, state, keywords);print_state(state);return 0;}。
JAVA实现AES加密算法代码

JAVA实现AES加密算法代码JA V A实现AES加密算法代码近些年DES使用越来越少,原因就在于其使用56位密钥,比较容易被破解,近些年来逐渐被AES替代,AES已经变成目前对称加密中最流行算法之一;AES可以使用128、192、和256位密钥,并且用128位分组加密和解密数据。
本文就简单介绍如何通过JA V A实现AES加密。
1. JA V A 实现闲话少许,掠过AES加密原理及算法,关于这些直接搜索专业网站吧,我们直接看JA V A的具体实现。
1.1 加密代码有详细解释,不多废话。
/*** 加密** @param content 需要加密的内容*@param password 加密密码* @return*/public static byte[] encrypt(String content, String password) {try {KeyGenerator kgen =KeyGenerator.getInstance("AES");kgen.init(128, new SecureRandom(password.getBytes()));SecretKey secretKey = kgen.generateKey();byte[] enCodeFormat = secretKey.getEncoded();SecretKeySpec key = new SecretKeySpec(enCodeFormat, "AES");Cipher cipher = Cipher.getInstance("AES");// 创建密码器byte[] byteContent = content.getBytes("utf-8");cipher.init(Cipher.ENCRYPT_MODE, key);// 初始化byte[] result = cipher.doFinal(byteContent);return result; // 加密} catch (NoSuchAlgorithmException e) { e.printStackTrace();} catch (NoSuchPaddingException e) { e.printStackTrace();} catch (InvalidKeyException e){ e.printStackTrace();} catch (UnsupportedEncodingException e){ e.printStackTrace();} catch (IllegalBlockSizeException e) { e.printStackTrace();} catch (BadPaddingException e){ e.printStackTrace();}return null;}/*** 加密** @param content 需要加密的内容* @param password 加密密码* @return*/ public static byte[] encrypt(String content, String password) {try {KeyGenerator kgen =KeyGenerator.getInstance("AES");kgen.init(128, new SecureRandom(password.getBytes()));SecretKey secretKey = kgen.generateKey();byte[] enCodeFormat = secretKey.getEncoded();SecretKeySpec key = new SecretKeySpec(enCodeFormat, "AES");Cipher cipher = Cipher.getInstance("AES");// 创建密码器byte[] byteContent = content.getBytes("utf-8");SecretKeySpec(enCodeFormat, "AES");Cipher cipher = Cipher.getInstance("AES");// 创建密码器cipher.init(Cipher.DECRYPT_MODE, key);// 初始化byte[] result = cipher.doFinal(content);return result; //加密} catch (NoSuchAlgorithmException e){ e.printStackTrace();} catch (NoSuchPaddingException e) { e.printStackTrace();} catch (InvalidKeyException e){ e.printStackTrace();} catch (IllegalBlockSizeException e) { e.printStackTrace();} catch (BadPaddingException e){ e.printStackTrace();}return null;}/**解密* @param content 待解密内容* @param password 解密密钥* @return*/public static byte[] decrypt(byte[] content, String password) {try {KeyGenerator kgen =KeyGenerator.getInstance("AES");kgen.init(128, new SecureRandom(password.getBytes()));SecretKey secretKey = kgen.generateKey();byte[] enCodeFormat = secretKey.getEncoded();SecretKeySpec key = new SecretKeySpec(enCodeFormat, "AES");Cipher cipher = Cipher.getInstance("AES");// 创建密码器cipher.init(Cipher.DECRYPT_MODE, key);// 初始化byte[] result = cipher.doFinal(content);return result; //加密} catch (NoSuchAlgorithmException e){ e.printStackTrace();} catch (NoSuchPaddingException e) { e.printStackTrace();} catch (InvalidKeyException e){ e.printStackTrace();} catch (IllegalBlockSizeException e) { e.printStackTrace();} catch (BadPaddingException e){ e.printStackTrace();}return null;}2.3 测试代码String content = "test";String password = "12345678";//加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);//解密byte[] decryptResult = decrypt(encryptResult,password); System.out.println("解密后:" + new String(decryptResult)); String content = "test";String password = "12345678"; //加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);//解密byte[] decryptResult =decrypt(encryptResult,password);System.out.println("解密后:" + new String(decryptResult));输出结果如下:加密前:test解密后:test 2.4 容易出错的地方但是如果我们将测试代码修改一下,如下:String content = "test";String password = "12345678";//加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);try {String encryptResultStr = newString(encryptResult,"utf-8");//解密byte[] decryptResult =decrypt(encryptResultStr.getBytes("utf-8"),password); System.out.println("解密后:" + newString(decryptResult));} catch (UnsupportedEncodingException e){ e.printStackTrace();}String content = "test"; String password = "12345678";//加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);try {String encryptResultStr = newString(encryptResult,"utf-8");//解密byte[] decryptResult =decrypt(encryptResultStr.getBytes("utf-8"),password); System.out.println("解密后:" + newString(decryptResult));} catch(UnsupportedEncodingException e){ e.printStackTrace();}则,系统会报出如下异常:javax.crypto.IllegalBlockSizeException: Input length must be multiple of 16 when decrypting with padded cipher atcom.sun.crypto.provider.SunJCE_f.b(DashoA13*..)at com.sun.crypto.provider.SunJCE_f.b(DashoA13*..)at com.sun.crypto.provider.AESCipher.engineDoFinal(DashoA 13*..)at javax.crypto.Cipher.doFinal(DashoA13*..)这主要是因为加密后的byte数组是不能强制转换成字符串的,换言之:字符串和byte数组在这种情况下不是互逆的;要避免这种情况,我们需要做一些修订,可以考虑将二进制数据转换成十六进制表示,主要有如下两个方法: 2.4.1将二进制转换成16进制/**将二进制转换成16进制* @param buf* @return*/public static String parseByte2HexStr(byte buf[]) {StringBuffer sb = new StringBuffer();for (int i = 0; i String hex = Integer.toHexString(buf[i] & 0xFF);if (hex.length() == 1) {hex = '0' + hex;}sb.append(hex.toUpperCase());}returnsb.toString();}/**将二进制转换成16进制*@param buf* @return*/public static StringparseByte2HexStr(byte buf[]) {StringBuffer sb = new StringBuffer();for (int i = 0; i String hex = Integer.toHexString(buf[i] & 0xFF);if (hex.length() == 1) {hex = '0' + hex;}sb.append(hex.toUpperCase());}returnsb.toString();} 2.4.2 将16进制转换为二进制/**将16进制转换为二进制* @param hexStr*@return*/public static byte[]parseHexStr2Byte(String hexStr) {if (hexStr.length() return null;byte[] result = new byte[hexStr.length()/2]; for (int i = 0;i int high =Integer.parseInt(hexStr.substring(i*2, i*2+1), 16);intlow = Integer.parseInt(hexStr.substring(i*2+1, i*2+2), 16); result[i] = (byte) (high * 16 + low);}return result;}/**将16进制转换为二进制* @param hexStr*@return*/public static byte[]parseHexStr2Byte(String hexStr) {if (hexStr.length() return null;byte[] result = new byte[hexStr.length()/2]; for (int i = 0;i int high =Integer.parseInt(hexStr.substring(i*2, i*2+1), 16);intlow = Integer.parseInt(hexStr.substring(i*2+1, i*2+2), 16);result[i] = (byte) (high * 16 + low);}return result;}然后,我们再修订以上测试代码,如下:String content = "test";String password = "12345678"; //加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);String encryptResultStr = parseByte2HexStr(encryptResult); System.out.println("加密后:" + encryptResultStr);//解密byte[] decryptFrom =parseHexStr2Byte(encryptResultStr);byte[] decryptResult = decrypt(decryptFrom,password); System.out.println("解密后:" + new String(decryptResult)); String content = "test";String password = "12345678"; //加密System.out.println("加密前:" + content);byte[] encryptResult = encrypt(content, password);String encryptResultStr = parseByte2HexStr(encryptResult); System.out.println("加密后:" + encryptResultStr);//解密byte[] decryptFrom =parseHexStr2Byte(encryptResultStr);byte[] decryptResult = decrypt(decryptFrom,password); System.out.println("解密后:" + new String(decryptResult));测试结果如下:加密前:test加密后:73C58BAFE578C59366D8C995CD0B9D6D解密后:test2.5 另外一种加密方式还有一种加密方式,大家可以参考如下:/*** 加密** @param content 需要加密的内容* @param password 加密密码*@return*/public static byte[] encrypt2(String content, String password) {try {SecretKeySpec key = new SecretKeySpec(password.getBytes(), "AES");Cipher cipher =Cipher.getInstance("AES/ECB/NoPadding");byte[] byteContent = content.getBytes("utf-8");cipher.init(Cipher.ENCRYPT_MODE, key);// 初始化byte[] result = cipher.doFinal(byteContent);return result; // 加密} catch (NoSuchAlgorithmException e) { e.printStackTrace();} catch (NoSuchPaddingException e) { e.printStackTrace();} catch (InvalidKeyException e){ e.printStackTrace();} catch (UnsupportedEncodingException e){ e.printStackTrace();} catch (IllegalBlockSizeException e) { e.printStackTrace();} catch (BadPaddingException e){ e.printStackTrace();}return null;}/*** 加密** @param content 需要加密的内容* @param password 加密密码* @return*/ public static byte[] encrypt2(String content, String password) {try {SecretKeySpec key = newSecretKeySpec(password.getBytes(), "AES");Cipher cipher = Cipher.getInstance("AES/ECB/NoPadding");byte[] byteContent = content.getBytes("utf-8");cipher.init(Cipher.ENCRYPT_MODE, key);// 初始化byte[] result = cipher.doFinal(byteContent);return result; // 加密} catch (NoSuchAlgorithmException e) { e.printStackTrace();} catch (NoSuchPaddingException e) { e.printStackTrace();} catch (InvalidKeyException e){ e.printStackTrace();} catch (UnsupportedEncodingException e){ e.printStackTrace();} catch (IllegalBlockSizeException e) { e.printStackTrace();} catch (BadPaddingException e){ e.printStackTrace();}return null;}这种加密方式有两种限制密钥必须是16位的待加密内容的长度必须是16的倍数,如果不是16的倍数,就会出如下异常:javax.crypto.IllegalBlockSizeException: Input length not multiple of 16 bytes atcom.sun.crypto.provider.SunJCE_f.a(DashoA13*..)at com.sun.crypto.provider.SunJCE_f.b(DashoA13*..)at com.sun.crypto.provider.SunJCE_f.b(DashoA13*..)at com.sun.crypto.provider.AESCipher.engineDoFinal(DashoA 13*..)at javax.crypto.Cipher.doFinal(DashoA13*..)要解决如上异常,可以通过补全传入加密内容等方式进行避免。
AES加密C语言实现代码
AES加密C语言实现代码以下是一个简单的C语言实现AES加密算法的代码:```c#include <stdio.h>#include <stdlib.h>#include <stdint.h>//定义AES加密的轮数#define NR 10//定义AES加密的扩展密钥长度#define Nk 4//定义AES加密的行数和列数#define Nb 4//定义AES加密的状态矩阵typedef uint8_t state_t[4][4];//定义AES加密的S盒变换表static const uint8_t sbox[256] =//S盒变换表};//定义AES加密的轮常量表static const uint8_t Rcon[11] =//轮常量表};//定义AES加密的密钥扩展变换函数void KeyExpansion(const uint8_t* key, uint8_t* expandedKey) uint32_t* ek = (uint32_t*)expandedKey;uint32_t temp;//密钥拷贝到扩展密钥中for (int i = 0; i < Nk; i++)ek[i] = (key[4 * i] << 24) , (key[4 * i + 1] << 16) ,(key[4 * i + 2] << 8) , (key[4 * i + 3]);}//扩展密钥生成for (int i = Nk; i < Nb * (NR + 1); i++)temp = ek[i - 1];if (i % Nk == 0)//对上一个密钥的字节进行循环左移1位temp = (temp >> 8) , ((temp & 0xFF) << 24);//对每个字节进行S盒变换temp = (sbox[temp >> 24] << 24) , (sbox[(temp >> 16) & 0xFF] << 16) , (sbox[(temp >> 8) & 0xFF] << 8) , sbox[temp & 0xFF];// 取轮常量Rcontemp = temp ^ (Rcon[i / Nk - 1] << 24);} else if (Nk > 6 && i % Nk == 4)//对每个字节进行S盒变换temp = (sbox[temp >> 24] << 24) , (sbox[(temp >> 16) & 0xFF] << 16) , (sbox[(temp >> 8) & 0xFF] << 8) , sbox[temp & 0xFF];}//生成下一个密钥ek[i] = ek[i - Nk] ^ temp;}//定义AES加密的字节替换函数void SubBytes(state_t* state)for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[i][j] = sbox[(*state)[i][j]];}}//定义AES加密的行移位函数void ShiftRows(state_t* state) uint8_t temp;//第2行循环左移1位temp = (*state)[1][0];(*state)[1][0] = (*state)[1][1]; (*state)[1][1] = (*state)[1][2]; (*state)[1][2] = (*state)[1][3]; (*state)[1][3] = temp;//第3行循环左移2位temp = (*state)[2][0];(*state)[2][0] = (*state)[2][2]; (*state)[2][2] = temp;temp = (*state)[2][1];(*state)[2][1] = (*state)[2][3]; (*state)[2][3] = temp;//第4行循环左移3位temp = (*state)[3][0];(*state)[3][0] = (*state)[3][3];(*state)[3][3] = (*state)[3][2];(*state)[3][2] = (*state)[3][1];(*state)[3][1] = temp;//定义AES加密的列混淆函数void MixColumns(state_t* state)uint8_t temp, tmp, tm;for (int i = 0; i < 4; i++)tmp = (*state)[i][0];tm = (*state)[i][0] ^ (*state)[i][1] ^ (*state)[i][2] ^ (*state)[i][3] ;temp = (*state)[i][0] ^ (*state)[i][1];(*state)[i][0] ^= temp ^ tm;temp = (*state)[i][1] ^ (*state)[i][2];(*state)[i][1] ^= temp ^ tm;temp = (*state)[i][2] ^ (*state)[i][3];(*state)[i][2] ^= temp ^ tm;temp = (*state)[i][3] ^ tmp;(*state)[i][3] ^= temp ^ tm;}//定义AES加密的轮密钥加函数void AddRoundKey(state_t* state, const uint8_t* roundKey) for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[j][i] ^= roundKey[i * 4 + j];}}//定义AES加密函数void AES_Encrypt(const uint8_t* plainText, const uint8_t* key, uint8_t* cipherText)state_t* state = (state_t*)cipherText;uint8_t expandedKey[4 * Nb * (NR + 1)];//密钥扩展KeyExpansion(key, expandedKey);//初始化状态矩阵for (int i = 0; i < 4; i++)for (int j = 0; j < 4; j++)(*state)[j][i] = plainText[i * 4 + j];}}//第1轮密钥加AddRoundKey(state, key);//迭代执行第2至第10轮加密for (int round = 1; round < NR; round++) SubBytes(state);ShiftRows(state);MixColumns(state);AddRoundKey(state, expandedKey + round * 16); }//执行第11轮加密SubBytes(state);ShiftRows(state);AddRoundKey(state, expandedKey + NR * 16);int maiuint8_t plainText[16] =//明文数据};uint8_t key[16] =//密钥数据};uint8_t cipherText[16];AES_Encrypt(plainText, key, cipherText);。
基于C++的AES算法完整源码

unsigned char state[4][4];
int i,r,c;
for(r=0; r<4; r++)
{
for(c=0; c<4 ;c++)
{
state[r][c] = input[c*4+r];
}
}
AddRoundKey(state,w[0]);
void MixColumns(unsigned char state[][4]);//列混淆
void AddRoundKey(unsigned char state[][4], unsigned char k[][4]);//轮密钥加
void InvSubBytes(unsigned char state[][4]);//逆字节代替
AES::AES(unsigned char* key)
{
unsigned char sBox[] =
{ /* 0 1 2 3 4 5 6 7 8 9 a b c d e f */
0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, /*0*/
0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, /*7*/
0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, /*8*/
0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, /*9*/
AES算法C语言实现源码
AES算法C语言实现源码/*AES-128 bit CBC Encryptionby Jacob Lister - Mar. 2024AES128-CBC Encryption for CNOTE: This is a C implementation with minimal cost checking, designed for embedded systems with tight code space constraintsgcc -Wall -c aes.cDescription:This code is the implementation of the AES128 algorithm,specifically ECB and CBC mode. ECB stands for ElectronicCode Book mode, which is essentially plain AES encryption.CBC (Cipher Block Chaining) is a mode that allows forenhanced security.*/#include <stdio.h>#include <stdlib.h>#include <string.h>typedef unsigned char AES_BYTE;/*constant in AES. Value=4*/#define Nb 4/* The number of 32 bit words in a key. */#define Nk 4/*Key length in bytes [128 bit](Nk * 4), or 16 bytes.*/#define KEYLEN 16/*The number of rounds in AES Cipher.Number of rounds=10, 12, 14.*/#define Nr 14AES_BYTE * AES_Encrypt(AES_BYTE *plainText, AES_BYTE *key); AES_BYTE * AES_Decrypt(AES_BYTE *cipherText, AES_BYTE *key);Function to store the round keysgenerated from the cipher key.*/void AES_KeyExpansion(AES_BYTE key[4*Nk], AES_BYTE roundKey[4*Nb*(Nr+1)]);/*Cipher is the main function that encryptsthe plaintext given the key [128 bit].*/void AES_Cipher(AES_BYTE *in, AES_BYTE *out, AES_BYTE *roundKey);/*The SubBytes Function is usedto substitute each byte of the statewith its corresponding byte in theRijndael S-box.*/void SubBytes(AES_BYTE *state);The ShiftRows function is usedto shift the rows cyclically aroundthe state.*/void ShiftRows(AES_BYTE *state);/*The MixColumns function is usedto mix the columns of the statematrix.*/void MixColumns(AES_BYTE *state);/*The AddRoundKey function is usedto add round key word to thestate matrix to produce the output.*/void AddRoundKey(AES_BYTE *state, AES_BYTE* roundKey); /*The SubBytes Function is usedto substitute each byte of the state with its inverse in the Rijndael S-box. */void InvSubBytes(AES_BYTE *state);/*The InvShiftRows function is usedto shift the rows cyclically aroundthe state in the opposite direction.*/void InvShiftRows(AES_BYTE *state);/*The InvMixColumns function is usedto mix the columns of the statematrix in the opposite direction.*/void InvMixColumns(AES_BYTE *state);/*The AES_Encrypt functionencrypts the plaintext usingthe provided AES_128 encryptionkey.*/AES_BYTE* AES_Encrypt(AES_BYTE *plainText, AES_BYTE *key) //struct to store ciphertextAES_BYTE *cipherText;int stat_len = 4 * Nb;// The KeyExpansion routine must be called// before encryption.AES_BYTE roundKey[4 * Nb * (Nr + 1)];。
java工具类-对称加密算法AES加密文件流

java⼯具类-对称加密算法AES加密⽂件流⽂件流加密涉及到⼤⽂件加密过程,不能直接使⽤Cipher.doFinal(byte[] bytes)⽅法进⾏直接加密超⼤⽂件会导致内存溢出。
解决⽅法:可以使⽤ Cipher.update(byte[] bytes) ⽅法进⾏⽂件流部分加密数据,当整个⽂件流数据都加密完后,使⽤ Cipher.doFinal()⽅法来⽣成填充内容,保证最后⼀段内容也是完整128位数据块所以会使⽤CipherInputStream 或者 CipherOutputStream进⾏⽂件加解密使⽤上⾯中了⼀个就可以了。
或者也可以混着⽤说下原理:CipherInputStream对输⼊流进⾏封装CipherInputStream.read()读取字节流时调⽤的cipher.update()⽅法进⾏流部分加密,当加密到最后⼀段时,会调⽤ doFinal() ⽅法。
CipherOutputStream对输出流进⾏封装,当要写⼊固定字节数据时,先加密,再写出CipherOutputStream.write() 中调⽤ cipher.update() ⽅法进⾏字节数组加密后写出再CipherOutputStream.close()中调⽤cipher.doFinal()⽅法填充最后⼀段内容贴个⽰例代码 public static void aesEncryptFile(String sourceFilePath, String destFilePath, String key) throws Exception {aesFile(sourceFilePath, destFilePath, key, Cipher.ENCRYPT_MODE);}public static void aesDecryptFile(String sourceFilePath, String destFilePath, String key) throws Exception {aesFile(sourceFilePath, destFilePath, key, Cipher.DECRYPT_MODE);}public static void aesEncryptFileForInput(String sourceFilePath, String destFilePath, String key) throws Exception {aesFileForInput(sourceFilePath, destFilePath, key, Cipher.ENCRYPT_MODE);}public static void aesDecryptFileForInput(String sourceFilePath, String destFilePath, String key) throws Exception {aesFileForInput(sourceFilePath, destFilePath, key, Cipher.DECRYPT_MODE);}/*** 通过⽂件输⼊流加密⽂件并输出到指定路径* CipherOutputStream进⾏加密数据*/public static void aesFile(String sourceFilePath, String destFilePath, String key, int mode) throws Exception {File sourceFile = new File(sourceFilePath);File destFile = new File(destFilePath);if (sourceFile.exists() && sourceFile.isFile()) {throw new IllegalArgumentException("加密源⽂件不存在");}if (!destFile.getParentFile().exists()) {destFile.getParentFile().mkdirs();}destFile.createNewFile();InputStream in = new FileInputStream(sourceFile);OutputStream out = new FileOutputStream(destFile);SecretKeySpec secretKeySpec = new SecretKeySpec(key.getBytes("UTF-8"), "AES/ECB/PKCS5Padding");Cipher cipher = Cipher.getInstance("AES/ECB/PKCS5Padding");cipher.init(mode, secretKeySpec);// 对输出流包装CipherOutputStream cout = new CipherOutputStream(out, cipher);byte[] cache = new byte[1024];int nRead = 0;while ((nRead = in.read(cache)) != -1) {cout.write(cache, 0, nRead);cout.flush();}cout.close();out.close();in.close();}/*** 通过⽂件输⼊流加密⽂件并输出到指定路径* CipherInputStream进⾏加密数据*/public static void aesFileForInput(String sourceFilePath, String destFilePath, String key, int mode) throws Exception {File sourceFile = new File(sourceFilePath);File destFile = new File(destFilePath);if (sourceFile.exists() && sourceFile.isFile()) {throw new IllegalArgumentException("加密源⽂件不存在");}if (!destFile.getParentFile().exists()) {destFile.getParentFile().mkdirs();}destFile.createNewFile();InputStream in = new FileInputStream(sourceFile);OutputStream out = new FileOutputStream(destFile);SecretKeySpec secretKeySpec = new SecretKeySpec(key.getBytes("UTF-8"), "AES/ECB/PKCS5Padding"); Cipher cipher = Cipher.getInstance("AES/ECB/PKCS5Padding");cipher.init(mode, secretKeySpec);// 对输⼊流包装CipherInputStream cin = new CipherInputStream(in, cipher);byte[] cache = new byte[1024];int nRead = 0;while ((nRead = cin.read(cache)) != -1) {out.write(cache, 0, nRead);out.flush();}out.close();cin.close();in.close();}。
sql对称密钥aes语句
sql对称密钥aes语句SQL中的对称密钥AES(Advanced Encryption Standard)用于加密和解密数据。
它是一种流行的对称加密算法,被广泛用于保护敏感数据的安全性。
下面是一些使用SQL语句进行AES加密和解密的示例:1. 使用AES加密函数对指定列进行加密:```UPDATE table SET column = AES_ENCRYPT(column, 'encryption_key');```这条语句将对指定表中的指定列进行AES加密,使用给定的加密密钥。
2. 使用AES解密函数对指定列进行解密:```SELECT AES_DECRYPT(column, 'encryption_key') FROM table;```这条语句将对指定表中的指定列进行AES解密,使用给定的解密密钥。
3. 创建一个包含AES加密函数的存储过程:```CREATE PROCEDURE encrypt_data(IN data VARCHAR(255), INencryption_key VARCHAR(255))BEGINDECLARE encrypted_data VARCHAR(255);SET encrypted_data = AES_ENCRYPT(data, encryption_key);SELECT encrypted_data;END;```这个存储过程接受一个字符串参数和一个加密密钥参数,将输入数据进行AES加密,并返回加密后的结果。
4. 创建一个包含AES解密函数的存储过程:```CREATE PROCEDURE decrypt_data(IN encrypted_data VARCHAR(255), IN decryption_key VARCHAR(255))BEGINDECLARE decrypted_data VARCHAR(255);SET decrypted_data = AES_DECRYPT(encrypted_data, decryption_key);SELECT decrypted_data;END;```这个存储过程接受一个加密数据参数和一个解密密钥参数,将输入数据进行AES解密,并返回解密后的结果。
对称(DESAES)与非对称(RSASSL数字证书)加密介绍及实际应用
对称(DESAES)与⾮对称(RSASSL数字证书)加密介绍及实际应⽤本⽂不对具体的算法做深⼊研究,只是讲解各种安全算法的原理和使⽤场景。
⼀、数据校验算法数据校验,是为保护数据的完整性,⽤⼀种指定的算法对原始数据计算出的⼀个校验值。
当接收⽅⽤同样的算法再算⼀次校验值,如果两次校验值⼀样,表⽰数据完整。
1、奇偶校验能检测出信息传输过程当中的⼀位误码。
出现错误不能检测出错误,只能要求重发。
2、 CRC循环冗余校验通过增加若⼲冗余位,可以检测出传输过程中的错误。
检错和纠错能⼒强,在通信领域运⽤较⼴泛。
3、MD5校验MD5算法是⼀种信息摘要算法,是通过哈希映射的原理得到⼀个⼤⽂件简短的MD5值。
该算法是⼀种不可逆算法,也就是说开发者不能通过MD5值得到原始⽂件的数据。
这⾥有⼀种可能性,不同的数据⽂件得到相同的MD5值,但是这种情况⼀般开发过程当中都不予考虑(数据碰撞)。
4、 SHA(Secure Hash Algorithm)是由美国专门制定密码算法的标准机构——美国国家标准技术研究院(NIST)制定的,SHA系列算法的摘要长度分别为:SHA为20字节(160位)、SHA256为32字节(256位)、 SHA384为48字节(384位)、SHA512为64字节(512位),由于它产⽣的数据摘要的长度更长,因此更难以发⽣碰撞,因此也更为安全,它是未来数据摘要算法的发展⽅向。
由于SHA系列算法的数据摘要长度较长,因此其运算速度与MD5相⽐,也相对较慢。
同MD5算法相同,他也是⼀种不可逆的算法。
⼆、对称加密算法1、Base64 编解码该算法只能称为⼀种校验,是对原始的数据进⾏了⼀个编码的过程。
有编码就有解码,该过程是⼀个可逆的。
该算法安全性较差,可以很轻松的通过解码将密⽂转换为明⽂,从⽽获取信息。
2、DES 数据加密算法是对称加密算法领域中的典型算法,现在认为是⼀种不安全的加密算法,因为现在已经有⽤穷举法攻破DES密码的报道了。
aes128的编码和解码的例程
aes128的编码和解码的例程AES(Advanced Encryption Standard)是一种常用的对称加密算法,采用了128位密钥长度,通常被用于数据的加密和解密。
本文将提供AES-128编码和解码的例程,包括算法原理、具体代码实现和示例。
一、算法原理AES-128算法是基于替代-置换网络结构的分组密码算法,其加密和解密过程都是以128位(16字节)的数据块进行操作,密钥长度为128位(16字节)。
AES-128的核心是四个基本操作:字节代换(SubBytes)、行移位(ShiftRows)、列混淆(MixColumns)和轮密钥加(Round Key Additions)。
加密过程中,密钥被扩展为多个轮密钥,以便对数据进行多轮加密;解密过程中,密钥也需要被扩展为轮密钥,但操作次序和加密过程相反。
通过反复迭代执行这四个操作,每一轮的结果会作为下一轮的输入,最终得到加密或解密后的结果。
具体的算法原理可以参考AES算法相关的文献和资料,这里不再详述。
二、编码和解码例程下面是AES-128编码和解码的例程示例,以C语言为例:```c#include <stdio.h>#include <stdlib.h>#include <string.h>#include <stdint.h>#include <stdbool.h>/* AES-128加密*/void aes128_encrypt(uint8_t *plaintext, uint8_t *key, uint8_t *ciphertext){//实现AES-128加密的代码// ...}/* AES-128解密*/void aes128_decrypt(uint8_t *ciphertext, uint8_t *key, uint8_t *plaintext){//实现AES-128解密的代码// ...}int main(){uint8_t plaintext[16] = "Hello, AES!"; //明文数据uint8_t key[16] = "0123456789ABCDEF"; //密钥uint8_t ciphertext[16]; //加密后的数据uint8_t decrypted[16]; //解密后的数据aes128_encrypt(plaintext, key, ciphertext); aes128_decrypt(ciphertext, key, decrypted); printf("明文: %s\n", plaintext);printf("加密后: ");for (int i = 0; i < 16; i++) {printf("%02X ", ciphertext[i]);}printf("\n");printf("解密后: %s\n", decrypted);return 0;}```上述代码中,`aes128_encrypt`和`aes128_decrypt`函数分别用于进行AES-128的加密和解密操作。
AES加密解密与代码实现详解
AES加密解密与代码实现详解AES(Advanced Encryption Standard)是一种对称加密算法,其安全性和性能都得到了广泛的认可和应用。
在AES中,采用的是分组密码算法,即将明文分组加密,每个明文分组的长度为128比特(16字节),密钥长度可为128比特、192比特或256比特。
1.初始化轮秘钥:根据密钥生成一系列轮秘钥,用于每轮加密操作。
2.轮加密:对明文进行一系列的轮操作,每轮操作包括字节代换、行移位、列混淆和轮秘钥加。
- 字节代换(SubBytes):将每个字节替换为S盒中对应字节的值,S盒是一个由固定变换生成的字节替代表。
- 行移位(ShiftRows):将第1、2、3行循环左移0、1、2个字节。
- 列混淆(MixColumns):通过一系列的线性变换,完成每个列的混淆操作。
- 轮秘钥加(AddRoundKey):将当前轮的秘钥与状态矩阵进行异或操作。
3.最后一轮加密操作:最后一轮操作不包括列混淆操作。
4.密文生成:将最后一轮加密操作的状态矩阵输出为密文。
解密操作与加密操作相反,主要是将轮操作中的逆变换应用到密文上,恢复出明文。
以下是一个AES加密解密算法的示例代码(使用Python语言实现):```pythonfrom Crypto.Cipher import AESfrom Crypto.Util.Padding import pad, unpadfrom Crypto.Random import get_random_bytes#生成一个随机的16字节密钥key = get_random_bytes(16)def encrypt(plain_text):#创建一个AES对象并使用密钥进行初始化cipher = AES.new(key, AES.MODE_ECB)#对明文进行填充padded_plain_text = pad(plain_text, 16)#加密明文cipher_text = cipher.encrypt(padded_plain_text) return cipher_textdef decrypt(cipher_text):#创建一个AES对象并使用密钥进行初始化cipher = AES.new(key, AES.MODE_ECB)#解密密文decrypted_text = cipher.decrypt(cipher_text)#对解密后的明文进行去填充plain_text = unpad(decrypted_text, 16)return plain_text#要加密的明文plain_text = b"Hello World!"#加密明文得到密文cipher_text = encrypt(plain_text)#解密密文得到明文decrypted_text = decrypt(cipher_text)print("明文:", plain_text)print("密文:", cipher_text)print("解密后明文:", decrypted_text)```通过以上代码,可以实现对称加密算法AES的加密和解密操作。
C语言实现AES加密解密
C语言实现AES加密解密AES(Advanced Encryption Standard)是一种对称加密算法,它是目前广泛使用的加密标准之一、本文将介绍如何使用C语言实现AES加密和解密。
AES算法使用128位(16字节)的块进行加密和解密。
它支持128位、192位和256位长度的密钥。
在下面的示例中,我们将演示如何使用128位的密钥进行AES加密和解密。
首先,我们需要准备一个AES加密所需的密钥。
我们可以通过一个字符串来表示密钥,然后将其转换为字节数组。
在C语言中,可以使用`strncpy`函数将字符串复制到字节数组中。
```c#include <stdio.h>#include <stdlib.h>#include <string.h>#include <openssl/aes.h>#define AES_KEY_SIZE 128int mai//准备AES密钥unsigned char key[AES_KEY_SIZE/8];strncpy((char*)key, keyStr, AES_KEY_SIZE/8);//创建AES加密上下文AES_KEY aesKey;AES_set_encrypt_key(key, AES_KEY_SIZE, &aesKey); //待加密的数据unsigned char input[] = "Hello, AES!";int inputLen = sizeof(input)/sizeof(input[0]); //加密数据unsigned char encrypted[AES_BLOCK_SIZE];AES_encrypt(input, encrypted, &aesKey);//输出加密结果printf("Encrypted: ");for (int i = 0; i < AES_BLOCK_SIZE; i++)printf("%02x", encrypted[i]);}printf("\n");//创建AES解密上下文AES_set_decrypt_key(key, AES_KEY_SIZE, &aesKey); //解密数据unsigned char decrypted[AES_BLOCK_SIZE];AES_decrypt(encrypted, decrypted, &aesKey);//输出解密结果printf("Decrypted: ");for (int i = 0; i < AES_BLOCK_SIZE; i++)printf("%c", decrypted[i]);}printf("\n");return 0;```在上面的示例中,我们使用OpenSSL库提供的AES函数来执行加密和解密操作。
C语言实现数据加密算法
C语言实现数据加密算法数据加密是对敏感信息进行转换的过程,以保护数据的机密性和完整性。
C语言提供了强大的工具和库来实现各种加密算法,包括对称加密和非对称加密等。
对称加密算法是一种使用相同密钥加密和解密数据的方法。
其中最常见的算法是DES(Data Encryption Standard)和AES(Advanced Encryption Standard)。
下面是一个实现AES算法的示例代码:```c#include <stdio.h>#include <stdlib.h>#include <string.h>#include <openssl/aes.h>void encrypt_data(const unsigned char *data, size_t len, const unsigned char *key, unsigned char *encrypted_data) AES_KEY aes_key;AES_set_encrypt_key(key, 128, &aes_key);AES_encrypt(data, encrypted_data, &aes_key);void decrypt_data(const unsigned char *encrypted_data,size_t len, const unsigned char *key, unsigned char *data) AES_KEY aes_key;AES_set_decrypt_key(key, 128, &aes_key);AES_decrypt(encrypted_data, data, &aes_key);int maiunsigned char data[AES_BLOCK_SIZE] = "hello world!";size_t len = sizeof(data);unsigned char encrypted_data[AES_BLOCK_SIZE];encrypt_data(data, len, key, encrypted_data);unsigned char decrypted_data[AES_BLOCK_SIZE];decrypt_data(encrypted_data, len, key, decrypted_data);printf("Original Data: %s\n", data);printf("Encrypted Data: ");for (int i = 0; i < len; i++)printf("%02x ", encrypted_data[i]);}printf("\nDecrypted Data: %s\n", decrypted_data);return 0;```以上代码使用了OpenSSL库中的AES加密算法。
AES算法C源代码

#include<string.h>#include<stdio.h>#include<math.h>#include<conio.h>#include<stdlib.h>#define Nb 4 //分组大小为4int Nr=0; //轮数定义为0,实际值在程序中获取int Nk=0;//密钥长度定义为0,实际值在程序中获取int Nc = 128;//Nc为密钥长度,只能为128,192或256// in:存储明文的数组// out:存储密文的数组// state:存储中间状态的数组unsigned char in[16],out[32],state[4][4];unsigned char RoundKey[240];//存储轮密钥的数组unsigned char Key[32];//存储输入的密钥int getSBoxInvert(int num){//逆S盒子int rsbox[256] ={ 0x52, 0x09, 0x6a, 0xd5, 0x30, 0x36, 0xa5, 0x38, 0xbf, 0x40, 0xa3, 0x9e, 0x81, 0xf3, 0xd7, 0xfb, 0x7c, 0xe3, 0x39, 0x82, 0x9b, 0x2f, 0xff, 0x87, 0x34, 0x8e, 0x43, 0x44, 0xc4, 0xde, 0xe9, 0xcb, 0x54, 0x7b, 0x94, 0x32, 0xa6, 0xc2, 0x23, 0x3d, 0xee, 0x4c, 0x95, 0x0b, 0x42, 0xfa, 0xc3, 0x4e, 0x08, 0x2e, 0xa1, 0x66, 0x28, 0xd9, 0x24, 0xb2, 0x76, 0x5b, 0xa2, 0x49, 0x6d, 0x8b, 0xd1, 0x25, 0x72, 0xf8, 0xf6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xd4, 0xa4, 0x5c, 0xcc, 0x5d, 0x65, 0xb6, 0x92, 0x6c, 0x70, 0x48, 0x50, 0xfd, 0xed, 0xb9, 0xda, 0x5e, 0x15, 0x46, 0x57, 0xa7, 0x8d, 0x9d, 0x84, 0x90, 0xd8, 0xab, 0x00, 0x8c, 0xbc, 0xd3, 0x0a, 0xf7, 0xe4, 0x58, 0x05, 0xb8, 0xb3, 0x45, 0x06, 0xd0, 0x2c, 0x1e, 0x8f, 0xca, 0x3f, 0x0f, 0x02, 0xc1, 0xaf, 0xbd, 0x03, 0x01, 0x13, 0x8a, 0x6b, 0x3a, 0x91, 0x11, 0x41, 0x4f, 0x67, 0xdc, 0xea, 0x97, 0xf2, 0xcf, 0xce, 0xf0, 0xb4,0xe6, 0x73, 0x96, 0xac, 0x74, 0x22, 0xe7, 0xad, 0x35, 0x85, 0xe2, 0xf9, 0x37, 0xe8, 0x1c, 0x75,0xdf, 0x6e, 0x47, 0xf1, 0x1a, 0x71, 0x1d, 0x29, 0xc5, 0x89, 0x6f, 0xb7, 0x62, 0x0e, 0xaa, 0x18,0xbe, 0x1b, 0xfc, 0x56, 0x3e, 0x4b, 0xc6, 0xd2, 0x79, 0x20, 0x9a, 0xdb, 0xc0, 0xfe, 0x78, 0xcd,0x5a, 0xf4, 0x1f, 0xdd, 0xa8, 0x33, 0x88, 0x07, 0xc7, 0x31, 0xb1, 0x12, 0x10, 0x59, 0x27, 0x80,0xec, 0x5f, 0x60, 0x51, 0x7f, 0xa9, 0x19, 0xb5, 0x4a, 0x0d, 0x2d, 0xe5, 0x7a, 0x9f, 0x93, 0xc9,0x9c, 0xef, 0xa0, 0xe0, 0x3b, 0x4d, 0xae, 0x2a, 0xf5, 0xb0, 0xc8, 0xeb, 0xbb, 0x3c, 0x83, 0x53,0x99, 0x61, 0x17, 0x2b, 0x04, 0x7e, 0xba, 0x77, 0xd6, 0x26, 0xe1, 0x69, 0x14, 0x63, 0x55, 0x21,0x0c, 0x7d };return rsbox[num];}int getSBoxValue(int num){//S盒子int sbox[256] = {//0 1 2 3 4 5 6 7 8 9 A B C D E F0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe,0xd7, 0xab, 0x76,0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c,0xa4, 0x72, 0xc0,0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71,0xd8, 0x31, 0x15,0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb,0x27, 0xb2, 0x75,0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29,0xe3, 0x2f, 0x84,0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a,0x4c, 0x58, 0xcf,0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50,0x3c, 0x9f, 0xa8,0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10,0xff, 0xf3, 0xd2,0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64,0x5d, 0x19, 0x73,0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde,0x5e, 0x0b, 0xdb,0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79,0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08,0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a,0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e,0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf,0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16 };return sbox[num];}// The round constant word array, Rcon[i], contains the values given by// x to th e power (i-1) being powers of x (x is denoted as {02}) in the field GF(2^8) // Note that i starts at 1, not 0).int Rcon[255] = {0x8d, 0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36, 0x6c, 0xd8, 0xab, 0x4d, 0x9a,0x2f, 0x5e, 0xbc, 0x63, 0xc6, 0x97, 0x35, 0x6a, 0xd4, 0xb3, 0x7d, 0xfa, 0xef, 0xc5, 0x91, 0x39,0x72, 0xe4, 0xd3, 0xbd, 0x61, 0xc2, 0x9f, 0x25, 0x4a, 0x94, 0x33, 0x66, 0xcc, 0x83, 0x1d, 0x3a,0x74, 0xe8, 0xcb, 0x8d, 0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36, 0x6c, 0xd8,0xab, 0x4d, 0x9a, 0x2f, 0x5e, 0xbc, 0x63, 0xc6, 0x97, 0x35, 0x6a, 0xd4, 0xb3, 0x7d, 0xfa, 0xef,0xc5, 0x91, 0x39, 0x72, 0xe4, 0xd3, 0xbd, 0x61, 0xc2, 0x9f, 0x25, 0x4a, 0x94, 0x33, 0x66, 0xcc,0x83, 0x1d, 0x3a, 0x74, 0xe8, 0xcb, 0x8d, 0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1b,0x36, 0x6c, 0xd8, 0xab, 0x4d, 0x9a, 0x2f, 0x5e, 0xbc, 0x63, 0xc6, 0x97, 0x35, 0x6a, 0xd4, 0xb3,0x7d, 0xfa, 0xef, 0xc5, 0x91, 0x39, 0x72, 0xe4, 0xd3, 0xbd, 0x61, 0xc2, 0x9f, 0x25, 0x4a, 0x94,0x33, 0x66, 0xcc, 0x83, 0x1d, 0x3a, 0x74, 0xe8, 0xcb, 0x8d, 0x01, 0x02, 0x04, 0x08, 0x10, 0x20,0x40, 0x80, 0x1b, 0x36, 0x6c, 0xd8, 0xab, 0x4d, 0x9a, 0x2f, 0x5e, 0xbc, 0x63, 0xc6, 0x97, 0x35,0x6a, 0xd4, 0xb3, 0x7d, 0xfa, 0xef, 0xc5, 0x91, 0x39, 0x72, 0xe4, 0xd3, 0xbd, 0x61, 0xc2, 0x9f,0x25, 0x4a, 0x94, 0x33, 0x66, 0xcc, 0x83, 0x1d, 0x3a, 0x74, 0xe8, 0xcb, 0x8d,0x01, 0x02, 0x04,0x08, 0x10, 0x20, 0x40, 0x80, 0x1b, 0x36, 0x6c, 0xd8, 0xab, 0x4d, 0x9a, 0x2f, 0x5e, 0xbc, 0x63,0xc6, 0x97, 0x35, 0x6a, 0xd4, 0xb3, 0x7d, 0xfa, 0xef, 0xc5, 0x91, 0x39, 0x72, 0xe4, 0xd3, 0xbd,0x61, 0xc2, 0x9f, 0x25, 0x4a, 0x94, 0x33, 0x66, 0xcc, 0x83, 0x1d, 0x3a, 0x74, 0xe8, 0xcb };//密钥扩展,生成Nb(Nr+1)的轮密钥,用于每轮的解密密钥void KeyExpansion(){int i,j;unsigned char temp[4],k;//第一个密钥为密钥本身for(i=0;i<Nk;i++){RoundKey[i*4]=Key[i*4];RoundKey[i*4+1]=Key[i*4+1];RoundKey[i*4+2]=Key[i*4+2];RoundKey[i*4+3]=Key[i*4+3];}// 其它密钥由第一个密钥进行扩展得到while (i < (Nb * (Nr+1))){for(j=0;j<4;j++){temp[j]=RoundKey[(i-1) * 4 + j];}if (i % Nk == 0){// 将四个字节进行左移一位,即[a0,a1,a2,a3]变为[a1,a2,a3,a0]{k = temp[0];temp[0] = temp[1];temp[1] = temp[2];temp[2] = temp[3];temp[3] = k;}// SubWord() is a function that takes a four-byte input word and // applies the S-box to each of the four bytes to produce an output word. {temp[0]=getSBoxValue(temp[0]);temp[1]=getSBoxValue(temp[1]);temp[2]=getSBoxValue(temp[2]);temp[3]=getSBoxValue(temp[3]);}temp[0] = temp[0] ^ Rcon[i/Nk];}else if (Nk > 6 && i % Nk == 4){{temp[0]=getSBoxValue(temp[0]);temp[1]=getSBoxValue(temp[1]);temp[2]=getSBoxValue(temp[2]);temp[3]=getSBoxValue(temp[3]);}}RoundKey[i*4+0] = RoundKey[(i-Nk)*4+0] ^ temp[0];RoundKey[i*4+1] = RoundKey[(i-Nk)*4+1] ^ temp[1];RoundKey[i*4+2] = RoundKey[(i-Nk)*4+2] ^ temp[2];RoundKey[i*4+3] = RoundKey[(i-Nk)*4+3] ^ temp[3];i++;}}// This function adds the round key to state.// The round key is added to the state by an XOR function.void AddRoundKey(int round){int i,j;for(i=0;i<4;i++){for(j=0;j<4;j++){state[j][i] ^= RoundKey[round * Nb * 4 + i * Nb + j]; }}}// The SubBytes Function Substitutes the values in the// state matrix with values in an S-box.void InvSubBytes(){int i,j;for(i=0;i<4;i++){for(j=0;j<4;j++){state[i][j] = getSBoxInvert(state[i][j]);}}}// The ShiftRows() function shifts the rows in the state to the left.// Each row is shifted with different offset.// Offset = Row number. So the first row is not shifted.void InvShiftRows(){unsigned char temp;// Rotate first row 1 columns to righttemp=state[1][3];state[1][3]=state[1][2];state[1][2]=state[1][1];state[1][1]=state[1][0];state[1][0]=temp;// Rotate second row 2 columns to righttemp=state[2][0];state[2][0]=state[2][2];state[2][2]=temp;temp=state[2][1];state[2][1]=state[2][3];state[2][3]=temp;// Rotate third row 3 columns to righttemp=state[3][0];state[3][0]=state[3][1];state[3][1]=state[3][2];state[3][2]=state[3][3];state[3][3]=temp;}// xtime is a macro that finds the product of {02} and the argument to xtime modulo {1b}#define xtime(x) ((x<<1) ^ (((x>>7) & 1) * 0x1b))// Multiplty is a macro used to multiply numbers in the field GF(2^8)#define Multiply(x,y) (((y & 1) * x) ^ ((y>>1 & 1) * xtime(x)) ^ ((y>>2 & 1) * xtime(xtime(x))) ^ ((y>>3 & 1) * xtime(xtime(xtime(x)))) ^ ((y>>4 & 1) * xtime(xtime(xtime(xtime(x))))))// MixColumns function mixes the columns of the state matrix.// The method used to multiply may be difficult to understand for the inexperienced. // Please use the references to gain more information.void InvMixColumns(){int i;unsigned char a,b,c,d;for(i=0;i<4;i++){a = state[0][i];b = state[1][i];c = state[2][i];d = state[3][i];state[0][i] = Multiply(a, 0x0e) ^ Multiply(b, 0x0b) ^ Multiply(c, 0x0d) ^ Multiply(d, 0x09);state[1][i] = Multiply(a, 0x09) ^ Multiply(b, 0x0e) ^ Multiply(c, 0x0b) ^ Multiply(d, 0x0d);state[2][i] = Multiply(a, 0x0d) ^ Multiply(b, 0x09) ^ Multiply(c, 0x0e) ^ Multiply(d, 0x0b);state[3][i] = Multiply(a, 0x0b) ^ Multiply(b, 0x0d) ^ Multiply(c, 0x09) ^ Multiply(d, 0x0e);}}// InvCipher is the main function that decrypts the CipherText.void InvCipher(){int i,j,round=0;//Copy the input CipherText to state array.for(i=0;i<4;i++){for(j=0;j<4;j++){state[j][i] = in[i*4 + j];}}// Add the First round key to the state before starting the rounds. AddRoundKey(Nr);// There will be Nr rounds.// The first Nr-1 rounds are identical.// These Nr-1 rounds are executed in the loop below.for(round=Nr-1;round>0;round--){InvShiftRows();InvSubBytes();AddRoundKey(round);InvMixColumns();}// The last round is given below.// The MixColumns function is not here in the last round.InvShiftRows();InvSubBytes();AddRoundKey(0);// The decryption process is over.// Copy the state array to output array.for(i=0;i<4;i++){for(j=0;j<4;j++){out[i*4+j]=state[j][i];}}}// The SubBytes Function Substitutes the values in the// state matrix with values in an S-box.void SubBytes(){int i,j;for(i=0;i<4;i++){for(j=0;j<4;j++){state[i][j] = getSBoxValue(state[i][j]);}}// The ShiftRows() function shifts the rows in the state to the left.// Each row is shifted with different offset.// Offset = Row number. So the first row is not shifted.void ShiftRows(){unsigned char temp;// Rotate first row 1 columns to lefttemp=state[1][0];state[1][0]=state[1][1];state[1][1]=state[1][2];state[1][2]=state[1][3];state[1][3]=temp;// Rotate second row 2 columns to lefttemp=state[2][0];state[2][0]=state[2][2];state[2][2]=temp;temp=state[2][1];state[2][1]=state[2][3];state[2][3]=temp;// Rotate third row 3 columns to lefttemp=state[3][0];state[3][0]=state[3][3];state[3][3]=state[3][2];state[3][2]=state[3][1];state[3][1]=temp;}// xtime is a macro that finds the product of {02} and the argument to xtime modulo {1b}#define xtime(x) ((x<<1) ^ (((x>>7) & 1) * 0x1b))// MixColumns function mixes the columns of the state matrixvoid MixColumns(){int i;unsigned char Tmp,Tm,t;for(i=0;i<4;i++){t=state[0][i];Tmp = state[0][i] ^ state[1][i] ^ state[2][i] ^ state[3][i] ;Tm = state[0][i] ^ state[1][i] ; Tm = xtime(Tm); state[0][i] ^= Tm ^ Tmp ; Tm = state[1][i] ^ state[2][i] ; Tm = xtime(Tm); state[1][i] ^= Tm ^ Tmp ; Tm = state[2][i] ^ state[3][i] ; Tm = xtime(Tm); state[2][i] ^= Tm ^ Tmp ; Tm = state[3][i] ^ t ; Tm = xtime(Tm); state[3][i] ^= Tm ^ Tmp ;}}// Cipher is the main function that encrypts the PlainText.void Cipher(){int i,j,round=0;//Copy the input PlainText to state array.for(i=0;i<4;i++){for(j=0;j<4;j++){state[j][i] = in[i*4 + j];}}// Add the First round key to the state before starting the rounds.AddRoundKey(0);// There will be Nr rounds.// The first Nr-1 rounds are identical.// These Nr-1 rounds are executed in the loop below.for(round=1;round<Nr;round++){SubBytes();ShiftRows();MixColumns();AddRoundKey(round);}// The last round is given below.// The MixColumns function is not here in the last round.SubBytes();ShiftRows();AddRoundKey(Nr);// The encryption process is over.// Copy the state array to output array. for(i=0;i<4;i++){for(j=0;j<4;j++){out[i*4+j]=state[j][i];}}}char *encrypt(char *str, char *key){int i,j,Nl;double len;char *newstr;Nk = Nc / 32;Nr = Nk + 6;len= strlen(str);Nl = (int)ceil(len / 16);//printf("Nl:%d\n", Nl);newstr = (char *)malloc(Nl*32);memset(newstr,0,sizeof(newstr));for(i=0;i<Nl;i++){for(j=0;j<Nk*4;j++){Key[j]=key[j];in[j]=str[i*16+j];}KeyExpansion();Cipher();memcpy(&newstr[i*32], out, 32);}return newstr;}char *decrypt(char *str, char *key)int i,j,len,Nl;char *newstr;Nk = Nc / 32;Nr = Nk + 6;len= strlen(str);Nl = (int)ceil(len / 16);newstr = (char *)malloc(16*Nl);memset(newstr,0,sizeof(newstr));for(i=0;i<Nl;i++){for(j=0;j<Nk*4;j++){Key[j]=key[j];in[j]=str[i*16+j];}KeyExpansion();InvCipher();memcpy(&newstr[i*32], out, 32); }return newstr;}int main(){ char str_1[128];//存明文char str_2[128];//存加密密钥char str_3[128];//存解密密钥char *str;char *str2;printf("请输入明文:\n");scanf("%s",str_1);printf("请输入加密密钥:\n");scanf("%s",str_2);str= encrypt(str_1, str_2);printf("进行加密后:%s\n\n", str);printf("请输入解密密钥:\n");scanf("%s",str_3);str2 = decrypt(str,str_3);printf("进行解密后:%s\n", str2);getch();return 0;}。
对称加密的ase算法事例

对称加密中使用AES算法的例子如下:假设我们有一个需要加密的字符串"Hello, World!",我们将使用128位的AES密钥对其进行加密。
首先,我们需要将字符串转换为字节流,然后使用AES算法进行加密。
在这个例子中,我们将使用Python的pycryptodome库来实现AES加密。
```pythonfrom Crypto.Cipher import AESfrom Crypto.Random import get_random_bytes# 生成128位的随机密钥key = get_random_bytes(16)# 创建AES cipher对象cipher = AES.new(key, AES.MODE_ECB)# 将字符串转换为字节流data = b"Hello, World!"# 使用cipher对象进行加密encrypted_data = cipher.encrypt(data)print(encrypted_data) # 打印加密后的数据```在这个例子中,我们使用了ECB模式(电子密码本模式),这是最简单的AES加密模式。
然而,在实际应用中,我们通常会使用更安全的模式,如CBC(密码块链模式)或CFB(密码反馈模式)。
要解密这个加密的数据,我们只需要创建一个新的AES cipher对象,然后使用decrypt方法:```python# 创建新的AES cipher对象,用于解密cipher_dec = AES.new(key, AES.MODE_ECB)# 使用cipher对象进行解密decrypted_data = cipher_dec.decrypt(encrypted_data)print(decrypted_data) # 打印解密后的数据这就是一个对称加密中使用AES算法的例子。
请注意,在实际应用中,我们应该使用更安全的模式(如CBC或CFB),并确保密钥的安全存储。
