思科CCNA新版第3学期final-期末考试答案
CCNA第三学期期末

36有问题。
答案可能是1请参见图示。
所有中继链路工作正常,而且允许所有VLAN使用所有中继链路。
计算机5发送了一条请求。
哪台或哪些设备会收到此消息?仅计算机4计算机3和T R-A计算机4和T R-A计算机1、计算机2、计算机4和T R-A计算机1、计算机2、计算机3、计算机4和T R-A所有计算机和路由器2 points for Option22下列关于在接入点上启用开放式身份验证的陈述,哪一项是正确的?不需要身份验证使用64位加密算法需要使用身份验证服务器需要共同商定的密码2 points for Option13请参见图示。
该交换机用于让图中所示部门的成员实现连接,但不存在路由。
连接到Fa0/22的一位用户应该能够与t ing VLAN中的用户通信。
下列哪项更改可实现所需通信?将该用户连接到Gi0/1。
将该用户连接到Fa0/6。
将该用户添加到本征N。
将该用户添加到默认N。
2 points for Option24分层网络模型具有哪三项优点?(选择三项。
)带宽争用现象减少物理布局范围减小网络的容错能力提高无需配线间无需第三层功能管理和故障排除工作简化Option1, Option3, and Option6 are correc t.5下列关于新交换机默认配置的说法中哪三项正确?(选择三项。
)禁用了生成树协议。
使能口令被配置为o。
所有交换机端口都被分配给V LAN1。
闪存目录中包含IOS映像。
VLAN1配置有管理地址。
所有接口均设置为自动协商速度和双工模式。
Option3, Option4, and Option6 are correc t.6请参见图示。
最近安装了SW1用于取代集线器。
主机1和主机4同时传送数据。
网络设备会如何处理此事件?(选择两项。
)当冲突发生时,会调用回退算法。
由于主机1和主机4都连接到交换机,因此不会发生冲突。
交换机将根据交换机地址表中的信息将数据转发到相应的端口。
主机2和主机3会获分配更短的回退值,从而获得访问介质的优先权。
思科ccna第3学期_final_第1套_V_4
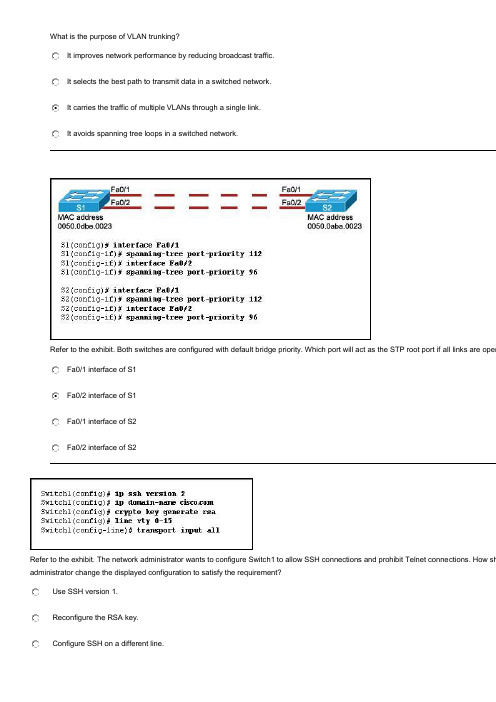
What is the purpose of VLAN trunking?It improves network performance by reducing broadcast traffic.It selects the best path to transmit data in a switched network.It carries the traffic of multiple VLANs through a single link.It avoids spanning tree loops in a switched network.Refer to the exhibit. Both switches are configured with default bridge priority. Which port will act as the STP root port if all links are oper Fa0/1 interface of S1Fa0/2 interface of S1Fa0/1 interface of S2Fa0/2 interface of S2Refer to the exhibit. The network administrator wants to configure Switch1 to allow SSH connections and prohibit Telnet conne ctions. How sh administrator change the displayed configuration to satisfy the requirement?Use SSH version 1.Reconfigure the RSA key.Configure SSH on a different line.Modify the transport input command.Refer to the exhibit. Which two facts about STP can be determined from the displayed output? (Choose two.)Switch S1 has the lowest configured STP priority in the network.Switch S1 is configured as the root bridge for VLAN1.Fa0/21 is the root port of switch S1.Fa0/22 is the redundant link.Fa0/24 is considered the best path to the root bridge.Which statement correctly describes the spanning-tree path cost?It is calculated based on the total number of switches connected in a loop.It is calculated based on the utilization of all the switches along a given path.It is calculated based on the bridge priority of the switches along a given path.It is calculated based on the sum of the port cost value, determined by link speed, for each switch port along a given path What are two requirements for configuring inter-VLAN routing using the router-on-a-stick model? (Choose two.)Each subinterface should be configured with its own IP address, subnet mask, and unique VLAN assignment.The physical interface of the router must be connected to a trunk link on the adjacent switch.The number of physical interfaces on the router should match the number of VLANs.Different static VLANs should be assigned to different interfaces of the router.The router should be configured as the VTP serverRefer to the exhibit. Which two options correctly describe the router configuration that is shown? (Choose two.)Routing between the 192.168.1.0 and 192.168.3.0 networks will not succeed until a routing protocol is configured on the route r.VLANs have not been appropriately configured on the router subinterfaces.The configuration is appropriate for a router-on-a-stick network design.Trunking has been appropriately configured on the router subinterfaces.An IP address should be applied to interface Fa0/1 for routing to occurRefer to the exhibit. What is true of the configuration of switch S1?A Cisco proprietary protocol is in use for ports Fa0/1 and Fa0/3.Switch ports Fa0/1 and Fa0/3 have been configured with the switchport mode access command.Untagged frames received on ports Fa0/1 and Fa0/3 will be placed on VLAN 1.Switch ports Fa0/1 and Fa0/3 are configured to carry data from multiple VLANs.Refer to the exhibit. Switches S2 and S3 are properly connected using an ethernet cable. A network administrator has configured both s is unable to propagate VLANs to S2. What could be the reason for this?The VTP configuration revision is different on both switches.The VTP domains are different on both switches.VTP pruning is disabled.VTP v2 is disabled.Refer to the exhibit. Router R1 is properly configured for router on a stick inter-VLAN routing, but PC1 is unable to ping PC2. What needs problem?Rename VLAN1.Connect one more port of S1 to R1.Configure the Fa0/1 port of S1 as a trunk port.Move the Fa0/0 interface of R1 to another VLAN.Refer to the exhibit. Router R-West and switch S-West1 are connected via a single ethernet cable between the router interface fa0/0 an fa0/1. The router and switch have been configured with the commands that are displayed in the exhib it. The network administrator ente trunk command and receives the output as shown. What is the cause of the "not-trunking" status for switch port Fa0/1?The trunk is established, but no VLANs have been configured to use it.The router is missing the dynamic trunking protocol statements necessary to form a trunk.Because the router does not support Dynamic Trunking Protocol, the trunk has not been established.The router, the switch, or both must be configured with the dynamic desirable option for Dynamic Trunking Protocol to establish aRefer to the exhibit. All trunk links are operational and all VLANs are allowed on all trunk links. An ARP request is sent by computer 5. W receive this message?only computer 4computer 3 and RTR-Acomputer 4 and RTR-Acomputer 1, computer 2, computer 4, and RTR-Acomputer 1, computer 2, computer 3, computer 4, and RTR-Aall of the computers and the routerRefer to the exhibit. A network administrator enters the displayed commands to configure VLAN 30. What is the result of running these commVLAN 30 will be added to S1, S2, and S3, but not to S4.VLAN 30 will be pruned from the VLAN database of S3.VLAN 30 will be added to the VLAN database of S3 but will not be propagated to S4, S2 or S1.VLAN 30 will not be added to the VLAN database of S3 and an error message will be displayedRefer to the exhibit. VTP pruning is enabled in the VTP domain that is shown. How will switch ST-1 handle Layer 2 broadcast traf host A on switch ST-C?It will be dropped.It will be forwarded out port Fa0/5 only.It will be forwarded out ports Fa0/5 and Fa0/10.It will be forwarded out ports Fa0/5, Fa0/10, and Fa0/15Refer to the exhibit. The devices in the network are operational and configured as indicated in the exhibit. However, hosts A and D other. What is the most likely cause of this problem?The link between the switches is up but not trunked.The Fa0/11 interface of Switch1 is not configured as a trunk.Hosts A and D are configured with IP addresses from different subnets.VLAN 20 and VLAN 30 are not allowed on the trunk between the switches.After unpacking a new Linksys WRT300N wireless multifunction device, a user needs to change the default administrator passwor d and make other configuration changes. What must the user do to access the device in order to make these changes?Use a wireless client to associate with the WRT300N and then open a HyperTerminal session with the device.Establish a wired connection with the device and then reboot the attached computer to launch the configuration software.Establish a wired connection from a computer in the same IP subnet as the WRT300N and enter the default IP address of the device into a web browser on the computer.Modify the TCP/IP properties of the computer that is connected to the WRT300N so that the computer and the WRT300N exist on the same network. Then reboot the computer to establish a connection.Refer to the exhibit. How is port Gi1/1 on SWT-A functioning in the spanning-tree topology?It is sending and receiving data frames.It is receiving BPDUs, but not sending data frames.It is participating in the election process by forwarding the BPDUs it receives.It is receiving BPDUs and populating the MAC address table, but not sending data.Refer to the exhibit. The switches have been configured as shown. The hosts that are connected to switch 101-2FL are not able to communicate with the hosts in their corresponding VLANs that are connected to switch 101-3FL. What should be done to fix the problem?Configure port Fa0/2 on switch 101-3FL as a static trunk link.Introduce a Layer 3 device or a switch with Layer 3 capability into the topology.Utilize the switchport trunk allowed vlan all command on switch 101-3FL to permit the VLAN traffic.Apply IP addresses that are in the same subnet to the interfaces that are used to connect switches 101-2FL and 101-3FLAfter listening for the presence of a signal on the network media, hosts A and C transmit data at the same time. In what two ways do the hosts respond to this situation? (Choose two.)The hosts transmit a jam signal to ensure that all hosts on the network are aware that a collision has occured.Because they are operating in full-duplex mode, the hosts resume listening for traffic in preparation for sending future messages.Because the hub will temporarily block traffic from one of the hosts, that host will be allowed to transmit once the wire is clear.Hosts A and C are assigned shorter backoff values to provide them priority to access the media for retransmission.After the backoff period of a host, the host checks to determine if the line is idle before retransmittingRefer to the exhibit. Hosts PC_A and PC_B send traffic simultaneously, and the frames from the transmitting stations collide.What is the last device to receive the collision?hub HB1switch SW1router R1switch SW2router R2switch SW4Refer to the exhibit. Switch SW2 has been newly purchased and added to the network. What configuration should be applied to SW2 so thatit participates in the same VTP domain as switch SW1, receives VLAN information from SW1, and synchronizes VLAN information?Disable VTP pruning on SW2.Configure SW2 in VTP transparent mode.Configure SW2 with the VTP domain password.Configure SW2 as a VTP server with a higher revision numberWhen configuring a router to act as an SSH server, what should be configured before issuing the crypto key generate rsacommand?the security domain namethe VTP domain namethe IP domain namethe host nameRefer to the exhibit. The switch VTY lines have been properly configured, but PC1 is unable to remotely manage the switch. How can this problem be resolved?Configure the Fa0/1 interface of the switch in trunk mode.Configure a default gateway on the switch.Configure the native VLAN on the switch.Configure the Fa0/1 interface of the switch to allow all VLANsRefer to the exhibit. A network administrator has segmented the network into two VLANs. The connected hosts can only access r esources in their own VLAN. What is the most scalable and cost effective solution to allow inter-VLAN communication in this network?Replace S1 with a router that has one FastEthernet interface for each PC.Add a second switch and divide the PCs so that each VLAN is connected to its own switch.Configure a router with two subinterfaces on one of its FastEthernet ports and connect it to S1 using a trunk link.Connect a router to a port on S1 and assign the IP address of VLAN1 to the connecting router interfaceRefer to the exhibit. An administrator documented the output of a CAM table from an Ethernet switch as shown. What action will the switch take when it receives the frame shown at the bottom of the exhibit?discard the frameforward the frame out port 2forward the frame out port 3forward the frame out all portsforward the frame out all ports except port 3add station 00-00-3D-1F-11-05 to port 2 in the forwarding tableWhich statement regarding the service password-encryption command is true?The service password-encryption command is entered at the privileged EXEC mode prompt.The service password-encryption command encrypts only passwords for the console and VTY ports.The service password-encryption command encrypts all previously unencrypted passwords in the running configuration.To see the passwords encrypted by the service password-encryption command, enter the no servicepassword-encryption commandWhich statement correctly describes the function of a Layer 2 switch?It performs switching and filtering based on the destination network layer address.It automatically uses STP to prevent switching loops in redundant topologies.It uses VTP to allow data from multiple VLANs to travel across a single link.It routes packets between different LAN segmentsWhich three statements are correct concerning the default configuration of a new switch? (Choose three.)It is configured in VTP server mode.STP is automatically enabled.The first VTY line is automatically configured to allow remote connections.VLAN1 is configured with a management IP address.All switch ports are assigned to VLAN1.The enable password is configured as ciscoRefer to the exhibit. How will switch S2 manage traffic coming from host PC1?S2 will drop the traffic, unless it is management traffic.S2 will tag the frame with VLAN ID 99 when it forwards it over the trunk link.S2 will leave the traffic untagged when it forwards it over a trunk link.S2 will tag the traffic with the highest VLAN ID value when it forwards it over the trunk link.Refer to the exhibit. The network administrator needs to remove the east-hosts VLAN and use the switch port from that VLAN in one of the existing VLANs. Which two sets of commands should be used when completely removing VLAN 2 from S1-Central while leaving the switch and all its interfaces operational? (Choose two.)S1-Central>enableS1-Central# reloadS1-Central>enableS1-Central# erase flash:S1-Central>enableS1-Central# delete flash:vlan.datS1-Central>enableS1-Central# configure terminalS1-Central(config)# no vlan 2S1-Central>enableS1-Central# configure terminalS1-Central(config-if)# interface fastethernet 0/1 S1-Central(config-if)# switchport access vlan 3Refer to the exhibit. The network administrator configures both switches as displayed. However, host C is unable to ping host D and host E is unable to ping host F. What action should the administrator take to enable this communication?Include a router in the topology.Associate hosts A and B with VLAN 10 instead of VLAN 1.Remove the native VLAN from the trunk.Configure one trunk port in the dynamic desirable mode.Add the switchport nonegotiate command to the configuration of S2Which two statements are correct about wireless infrastructure components? (Choose two.)An AP converts the TCP/IP data packets from their 802.11 frame encapsulation format to the 802.3 Ethernetframe format on the wired Ethernet network.A wireless AP does not require any physical connection to allow wireless clients to access the Internet.An AP is a layer 2 device, similar to a switch, that provides dedicated bandwidth to each connected wireless host.Collisions do not occur between wireless NICs and APs.The wireless router performs the roles of AP and router.Refer to the exhibit. The switches are configured for VTP as shown. Which two statements correctly describe the operation of these switches? (Choose two.)A new VLAN can be added to Switch1 and that information will be added only to Switch2.A new VLAN can be added to Switch1 and that information will be added to Switch2 and Switch4.An existing VLAN can be deleted from Switch4 and that VLAN will be deleted from Switch1 and Switch2.An existing VLAN can be deleted from Switch2 and that VLAN will be deleted from Switch1 and Switch4.A new VLAN can be added to Switch4 and that information will be added to Switch1, Switch2, and Switch3.A new VLAN can be added to Switch3 and that information will be added to Switch1, Switch2, and Switch4A new switch is to be added to an exis ting network in a remote office. The network administrator does not wantthe technicians in the remote office to be able to add new VLANs to the switch, but the switch should receive VLAN updates from the VTP domain. Which two steps must be performed to configure VTP on the new switch to meet these conditions? (Choose two.)Configure an IP address on the new switch.Configure the existing VTP domain name on the new switch.Configure all ports of both switches to access mode.Configure the new switch as a VTP client.Enable VTP pruningWhich two statements describe Spanning Tree Protocol? (Choose two.)It is only used at Layer 2.It is configured on routers.It eliminates Layer 2 loops in network topologies.It limits the number of valid MAC addresses allowed on a port.It allows VLAN information to propagate to other switches in the network.Refer to the exhibit. Which switch will be elected as the root bridge of the spanning tree topology?Cat-ACat-BCat-CCat-DRefer to the exhibit. What three statements describe why Host1 and Host2 are unable to communicate? (Choose three.)The switch ports are on different VLANs.The switch IP address is on the wrong subnet.The hosts are configured on different logical networks.A router is required to forward traffic between Host1 and Host2.The VLAN port assignments must be contiguous for each VLAN.The host default gateway addresses must be on the same logical network.Refer to the exhibit. A new host needs to be connected to VLAN 3. Which IP address should be assigned to this new host?192.168.1.22 /28192.168.1.31 /28192.168.1.32 /28192.168.1.52 /28192.168.1.63 /28Refer to the exhibit. Router RA receives a packet with a source address of 192.168.1.65 and a destination address of 192.168.1.161. What will the router do with this packet?The router will drop the packet.The router will forward the packet out interface FastEthernet 0/1.1.The router will forward the packet out interface FastEthernet 0/1.2.The router will forward the packet out interface FastEthernet 0/1.3.The router will forward the packet out interface FastEthernet 0/1.2 and interface FastEthernet 0/1.3Refer to the exhibit. On which of the devices in this network should routing between VLANs take place?the core layer devicesthe access layer devicesthe distribution layer devicesthe core and distribution layer devicesRefer to the exhibit. The teacher host is connected to port Fa0/7 on switch STW. A student has decided to share access to the Internet by attaching a hub and laptop to STW as shown. What will be the result of the student making this connection?The Fa0/7 port of STW will be shutdown.The student will gain full access to the Internet.Both the teacher and student will be able to receive data but only the teacher will be able to send.The frames from the laptop will be dropped, but the teacher host will maintain connectivity with the network.Refer to the exhibit. In what two ways will the router handle VLAN traffic that is received on the trunk? (Choose two.)Traffic to VLAN 1 received by the router interface Fa0/0 will be dropped by the router.Because interface Fa0/0 requires an IP address, the router will not be able to route between the VLANs.Packets that are received from network 192.168.20.0 /24 will be handled by subinterface Fa0/0.20.The router will use subinterface MAC addresses to identify the VLAN traffic that is received on the physical interface.The router will continue to process traffic from the attached VLANs even if the physical interface goes downRefer to the exhibit. Switch SW-A is to be used as a temporary replacement for another switch in the VTP Studentdomain. What two pieces of information are indicated from the exhibited output? (Choose two.)The other switches in the domain can be running either VTP version 1 or 2.There is a risk that the switch may cause incorrect VLAN information to be sent through the domain.VTP will block frame forwarding on at least one redundant trunk port that is configured on this switch.VLAN configuration changes made on this switch will be sent to other devices in the VTP domain.This switch will update its VLAN configuration when VLAN changes are made on a VTP server in the same domainWhat are three benefits of employing a hierarchical network design? (Choose three.)Hierarchically designed networks can more easily be expanded to suit future needs.Hierarchical design models enhance existing bandwidth through the use of link aggregation.The hierarchical model allows for specialized functionality at each layer, simplifying devicemanagement.Use of a hierarchical design allows replacement of redundant devices with high-capacity network equipment.A hierarchical design uses firewalls instead of complicated port-based and distribution layer securitypolicies.The hierarchical model allows the use of high-performance switches at all design layers, thus allowing for a fully-meshed topologyRefer to the exhibit. Hosts A and B attempt to transmit a frame at the same time and a collision occurs. When will host D be able to transmit?immediatelyafter sending its jam signalafter host A and host B have completed transmissionafter the jam signal clears and its backoff delay expiresWhat provides an authentication mechanism for 802.11-based wireless networks?DSSSOFDMSSIDWPARefer to the exhibit. What is the effect of setting the security mode to WEP on the Linksys integrated router?WEP identifies the wireless LAN.WEP allows the access point to inform clients of its presence.WEP translates IP addresses into easy-to-remember domain names.WEP encrypts data between the wireless client and the access point.WEP ensures that only authenticated users are allowed access to the WLAN.WEP translates an internal address or group of addresses into an outside, public address.Refer to the exhibit. SW-T has been configured with a single trunking interface. Which VLANs will be allowed across the trunk?Only VLAN 1 will be allowed across the trunk.All configured VLANs will be allowed across the trunk.Only the native VLAN will be allowed across the trunk.Only the the management and native VLANs will be allowed across the trunk.Only VLANs that are configured on the VTP server in the dom ain will be allowed across the trunkRefer to the exhibit. What does the term DYNAMIC indicate in the output that is shown?This entry can only be removed from the MAC address table by a network administrator.When forwarding a frame to the device with address 0060.5c5b.cd23, the switch does not have to perform a lookup to determine the final destination port.Only the device with MAC address 0060.5c5b.cd23 will be allowed to connect to port Fa0/18.The switch learned this MAC address from the source address in a frame received on Fa0/18.Refer to the exhibit. What is the purpose of the configuration commands that are shown?to activate port Fa0/10to make the port a member of VLAN 30to activate port security on port Fa0/10to add VLAN 30 to the trunk that is connected to port Fa0/10。
思科三期期末题

三期期末题1请参见图示。
主机A 无法ping 通R1。
应在R1 上执行哪两项配置步骤以解决此问题?(选择两项。
)C正确配置访问该路由器的线路口令。
配置接口速率。
管理性启用接口。
在路由器上配置动态路由协议。
在路由器上正确配置子网掩码。
2 一个网络横跨相距500 英尺(152 米)的两栋楼房。
在电缆路径附近装有一台电力变压器。
该网络应使用哪种类型的电缆?DSTPUTP同轴光纤3 以下哪种说法正确描述了AAA 的功能?A防止对网络进行未授权的访问。
根据目的IP 和端口号过滤流量。
使用户可以发送信息到运行在管理站上的守护进程。
加密数据以保障网络安全性。
4请参见图示。
从图中所示的输出中可得出什么结论? C此路由器上启用了PPP。
接口的带宽设置符合T1 连接要求。
serial0/0/0 接口已管理性关闭。
``````````````````````````````serial0/0/0 接口设置了默认封装。
serial0/0/0 接口设置了子网掩码255.255.255.255。
5请参见图示。
哪些电缆路径段需要使用交叉电缆?CA、D、FB、C、EB、D、EA、C、F6 为了将初始配置加载到一台新的交换机上,网络管理员将一台笔记本电脑通过控制台电缆连接到这台交换机上。
大约一分钟后,网络管理员启动了该交换机,发现交换机前部的SYST LED 从闪烁的绿色转为琥珀色。
请问这意味着什么?笔记本电脑与交换机之间的物理连接不正确。
交换机正在等待配置文件加载。
交换机的一个端口出现故障。
```````````````````` 交换机POST 失败。
D7 UDP 具有哪项特点? C是一种可靠的传输协议。
要求源主机重新发送未得到确认的数据包。
```````````````````````数据传输时所增加的开销较低。
是一种面向连接的协议。
8请参见图示。
主机 A 无法ping 通主机B。
为解决此问题可采取哪两项措施?(选择两项。
CCNA第三学期期末答案
假设没有使用 VLSM,添加 ip route 172.16.64.0 255.255.240.0 serial0/0 命令会对网络中正在工作的路由器造成什么影响?3目的地址处于 172.16.64.1 到 172.16.80.254 之间的所有数据包都会通过serial0/0 转发出去。
目的地址处于 172.16.64.1 到 172.16.255.254 之间的所有数据包都会通过serial0/0 转发出去。
目的地址处于 172.16.64.1 到 172.16.79.254 之间的所有数据包都会通过serial0/0 转发出去。
目的地址处于 172.16.0.1 到 172.16.64.254 之间的所有数据包都会通过serial0/0 转发出去。
2请参见图示。
管理员正在向网络中添加新路由器。
IP 地址 192.168.13.6/30 已被分配给 R2 上的相连串行接口。
管理员必须为新路由器的串行接口分配什么IP 地址?2192.168.13.4/30192.168.13.5/30192.168.13.7/30192.168.13.58/30192.168.13.61/27192.168.13.63/273OSPF 路由协议身份验证使用 MD5 验证时,下列有关密钥的说法中哪两项正确?(选择两项。
)24密钥以明文形式在路由器之间传递。
密钥用于帮助生成验证用的加密数字。
密钥以加密形式在路由器之间传递。
密钥永远不会在网络上传输。
数据包嗅探器可以捕获密钥。
4请参见图示。
路由表中将显示哪些路由?1R 10.10.4.0/24 [120/1] via 10.10.10.1, 00:00:12, FastEthernet0/1R 10.10.4.0/24 [120/1] via 10.10.20.1, 00:00:12, FastEthernet0/0R 10.10.4.0/24 [120/2] via 10.10.20.1, 00:00:12, FastEthernet0/0R 10.10.4.0/24 [120/3] via 10.10.30.1, 00:00:12, FastEthernet1/0R 10.10.4.0/24 [120/1] via 10.10.30.1, 00:00:12, FastEthernet1/05请参见图示。
cisco第三学期finalexam

请参见图示。
SWT-A 的端口Gi1/1 在该生成树拓扑中有何功能?接收BPDU 并填充MAC 地址表,但不发送数据。
2一台新交换机将加入远程办公室的现有网络。
网络管理员希望远程办公室的技术人员无法将新VLAN 添加到该交换机,但又收来自VTP 域的VLAN 更新。
要满足这些条件,必须在新交换机上执行哪两个VTP 配置步骤?(选择两项。
)在新交换机上配置现有VTP 域名。
将新交换机配置为VTP 客户端。
3请参见图示。
两台交换机都配置有默认的网桥优先级。
如果所有链路都在相同的带宽下运行,哪个端口将作为STP 根端口S2 的Fa0/2 接口4下列关于service password-encryption命令的说法中哪项正确?service password-encryption命令对运行配置中先前未加密的所有口令进行加密。
5请参见图示。
从图中显示的输出可以得到有关STP 的哪两项结论?(选择两项。
)Fa0/21 是交换机S1 的根端口。
Fa0/22 是冗余链路。
请参见图示。
交换机SW-A 将用于临时替代VTP Student 域中的另一台交换机。
从图中所示的输出可获得哪两点信息?(选择存在以下风险:该交换机可能会导致不正确的VLAN 信息在域中发送。
当同一域内的VTP 服务器上做出VLAN 更改后,此交换机会更新其VLAN 配置。
7经过侦听发现网络介质上不存在信号后,主机 A 和主机C 同时传送数据。
针对这种情况,主机会以哪两种方式作出响应?(主机会发送堵塞信号,以此确保网络中的所有主机都获悉已发生冲突。
回退时间结束后,主机会在重传前检查确定线路是否空闲。
8请参见图示。
网络管理员需要删除east-hosts VLAN 并将属于该VLAN 的交换机端口用到一个现有VLAN 中。
如果要从全删除VLAN 2,同时保证交换机及其所有接口工作正常,应该使用哪两组命令?(选择两项。
)S1-Central> enableS1-Central# configure terminalS1-Central(config)# no vlan 2S1-Central> enableS1-Central# configure terminalS1-Central(config-if)# interface fastethernet 0/1S1-Central(config-if)# switchport access vlan 39下列关于无线基础架构组件的说法中哪两项正确?(选择两项。
思科 期末考试答案【范本模板】
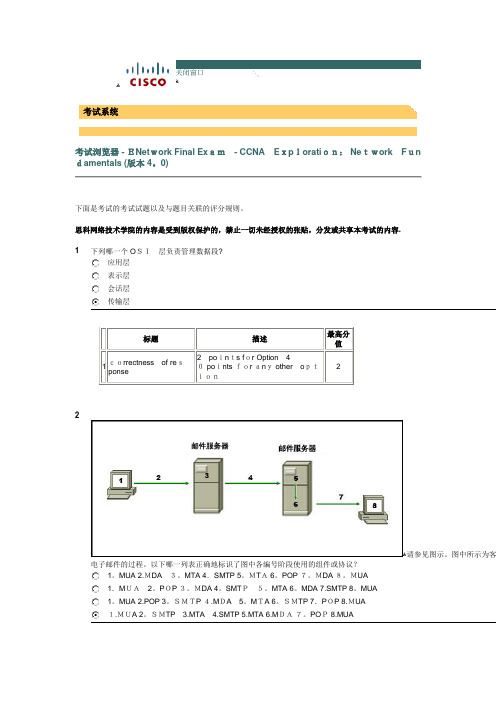
ﻫ关闭窗口ﻫ考试系统考试浏览器 - ENet work Final Ex am - CCNA E xp lorati on: Ne twork F un damentals (版本 4。
0)下面是考试的考试试题以及与题目关联的评分规则。
思科网络技术学院的内容是受到版权保护的,禁止一切未经授权的张贴,分发或共享本考试的内容. 1下列哪一个 O SI 层负责管理数据段?应用层表示层会话层传输层标题描述最高分值 1correctness of re sponse2 po in ts f or Option 40 po ints for an y other o ption22ﻫ请参见图示。
图中所示为客电子邮件的过程。
以下哪一列表正确地标识了图中各编号阶段使用的组件或协议?1。
MUA 2.MDA 3。
MTA 4.SMTP 5。
MT A 6。
POP 7。
MDA 8。
MUA1.M UA 2。
P OP 3。
MDA 4。
SMT P 5。
MTA 6。
MDA 7.SMTP 8。
MUA1。
MUA 2.POP 3。
SMTP 4.M DA 5。
M TA 6。
SMTP 7.P OP 8.MUA1.MUA 2。
SMTP 3.MTA 4.SMTP 5.MTA 6.M DA 7。
PO P 8.MUAﻫ3第 4 层报头包含帮助数据传输的哪一类信息?服务端口号主机逻辑地址设备物理地址虚拟连接标识符ﻫ4哪个OSI 层提供面向连接的可靠数据通信服务?应用层表示层会话层传输层网络层ﻫ5当 OSI模型下层执行无连接协议时,通常使用什么来确认数据已收到并请求重传丢失的数据?IPUDP以太网无连接确认面向连接的上层协议或服务6下列哪三项是CSMA/CD 的特征?(选择三项。
)设备会侦听介质,并且仅当无法检测到介质上存在其它信号时才会传输数据.介质上的所有设备均可侦听所有通信。
设备根据配置的优先级来进行通信。
发生冲突后,引起冲突的设备会优先尝试传输数据。
思科期末考试题库和答案
思科期末考试题库和答案一、单选题1. 在思科网络技术中,OSI模型的第4层是什么?A. 传输层B. 会话层C. 表示层D. 应用层答案:A2. 以下哪个协议是用于在网络层进行路由选择的?A. TCPB. IPC. UDPD. FTP答案:B3. 动态主机配置协议(DHCP)工作在OSI模型的哪一层?A. 应用层B. 传输层C. 网络层D. 数据链路层答案:D4. 以下哪个命令用于在思科设备上查看当前配置?A. show running-configB. show startup-configC. show interface statusD. show ip route答案:A5. 在思科设备上,哪个命令用于保存当前的配置到启动配置中?A. copy running-config startup-configB. copy startup-config running-configC. saveD. write答案:A二、多选题6. 以下哪些是思科交换机上常用的端口类型?A. FastEthernetB. GigabitEthernetC. TenGigabitEthernetD. Serial答案:A, B, C, D7. 在思科设备上,以下哪些命令用于管理VLAN?A. vlan databaseB. enableC. configure terminalD. exit答案:A, C8. 以下哪些是思科路由器上常用的接口类型?A. FastEthernetB. GigabitEthernetC. SerialD. ATM答案:A, B, C, D9. 以下哪些是思科设备上用于查看网络状态的命令?A. show ip interface briefB. show running-configC. show interface statusD. ping答案:A, C, D10. 在思科设备上,以下哪些命令用于配置静态路由?A. ip routeB. ip routingC. routeD. configure terminal答案:A, D三、判断题11. 思科的IOS(Internetworking Operating System)是运行在所有思科设备上的软件。
思科第三学期期末考试答案

请参见图示。
所有中继链路工作正常,而且允许所有VLAN使用所有中继链路。
计算机5 ARP请求。
哪台或哪些设备会收到此消息?仅计算机4* 计算机3和RTR-A计算机4和RTR-A计算机1、计算机2、计算机4和RTR-A计算机1、计算机2、计算机3、计算机4和RTR-A所有计算机和路由器F列关于在接入点上启用开放式身份验证的陈述,哪一项是正确的? *不需要身份验证使用64位加密算法需要使用身份验证服务器需要共同商定的密码VL^N Flane Status Ports1ctefauft active FaOl Fa0/2 FaO/3. Fa0/4 10accounting FaO/5. FaCVG Fa0.7 Fa0/820marking actr/e FaO/5, FaO'10, Fa(V11FaO/12. FaO/U FaO/14 research Faons, FaO/16 FaOH7FaO/16. FaO/19. Fa0/201QQ management adve FaO/21, FaQ/22. FaO'23Fa0/24, GiOJ1, G iO/21002W-default act/unsup1003loken-ring-1 efault act/unsup1004■fddinet-ctefaijlt act/unsup1005act/unsup请参见图示。
该交换机用于让图中所示部门的成员实现连接,但不存在路由。
连接到应该能够与accounting VLAN 中的用户通信。
下列哪项更改可实现所需通信?将该用户连接到GiO/1。
*将该用户连接到FaO/6。
将该用户添加到本征VLAN将该用户添加到默认VLAN分层网络模型具有哪三项优点?(选择三项。
)Opti on 1,36带宽争用现象减少」物理布局范围减小网络的容错能力提高无需配线间」无需第三层功能管理和故障排除工作简化FaO/22 IF列关于新交换机默认配置的说法中哪三项正确?(选择三项。
ccna第3本期末
c c n a第3本期末work Information Technology Company.2020YEAR1请参见图示。
需要将一台新主机连接到 VLAN 3。
应该为此新主机分配什么 IP 地址?192.168.1.22 /28192.168.1.31 /28192.168.1.32 /28192.168.1.52 /28192.168.1.63 /282请参见图示。
将 Linksys 集成路由器上的安全模式设置为 WEP 有什么作用?WEP 可标识无线 LAN。
WEP 允许该接入点通知客户端它的存在。
WEP 将 IP 地址转换为容易记忆的域名。
WEP 可加密无线客户端与接入点之间的数据。
WEP 可确保只有授权用户可以访问该 WLAN。
WEP 将一个或一组内部地址转换为外部公有地址。
3请参见图示。
交换机的配置如图所示。
连接到交换机 101-2FL 的主机无法与连接到交换机 101-3FL 且位于对应 VLAN 中的主样才能纠正此问题?将交换机 101-3FL 的 Fa0/2 端口配置为静态中继链路。
在拓扑中加入第 3 层设备或具备第 3 层功能的交换机。
在交换机 101-3FL 上使用switchport trunk allowed vlan all命令允许 VLAN 流量。
4下列哪两种说法正确地描述了生成树协议(选择两项。
)它只在第 2 层使用。
它在交换机上配置。
它消除了网络拓扑中的第 2 层环路。
它限制了端口上所允许的有效 MAC 地址的数量。
5请参见图示。
教师主机连接到交换机 STW 的 Fa0/7 端口。
一位学生想要共享 Internet 访问,于是决定将集线器和笔记本电脑示连接到 STW。
学生如此连接的结果是什么?STW 的 Fa0/7 端口会关闭。
学生会获得访问 Internet 的安全权限。
教师和学生都能接收数据,但只有教师才能发送数据。
从笔记本电脑发出的帧将被丢弃,但教师主机仍与网络保持连通。
ccna_第三学期期末考试

1.VLAN 中继有何用途?通过减少广播流量提高网络性能。
选择在交换网络中传输数据的最佳路径。
通过一条链路传送多个VLAN 的流量。
避免交换网络中出现生成树环路。
请参见图示。
两台交换机都配置有默认的网桥优先级。
如果所有链路都在相同的带宽下运行,哪个端口将作为STP 根端口?S1 的Fa0/1 接口S1 的Fa0/2 接口S2 的Fa0/1 接口S2 的Fa0/2 接口请参见图示。
从图中显示的输出可以得到有关STP 的哪两项结论?(选择两项。
)交换机S1 所配置的STP 优先级值在该网络中最低。
交换机S1 被配置为VLAN1 的根桥。
Fa0/21 是交换机S1 的根端口。
Fa0/22 是冗余链路。
Fa0/24 被视为通往根桥的最佳路径。
下列哪种说法正确描述了生成树路径开销?根据环路中连接的交换机总数计算。
根据给定路径上所有交换机的使用率计算。
根据给定路径上交换机的网桥优先级计算。
根据给定路径上每个交换机端口的端口开销值(由端口速度决定)的总和计算。
使用单臂路由器模型配置VLAN 间路由有哪两项要求?(选择两项。
)每个子接口都应配置有自己的IP 地址、子网掩码和唯一的VLAN 分配。
路由器的物理接口必须连接到相邻交换机上的中继链路。
路由器的物理接口数量应该与VLAN 数量匹配。
应该将不同的静态VLAN 分配给路由器的不同接口。
路由器应该配置为VTP 服务器。
请参见图示。
下列哪两项正确描述了图中所示的路由器配置。
(选择两项。
)在路由器上配置路由协议之前,网络192.168.1.0 与网络192.168.3.0 之间无法成功路由。
路由器子接口上未正确配置VLAN。
该配置适用于单臂路由器网络设计。
路由器子接口上未正确配置中继。
应该为接口Fa0/1 分配IP 地址,否则无法进行路由请参见图示。
下列有关交换机S1 配置的说法中哪项正确?端口Fa0/1 和Fa0/3 使用的是Cisco 专有协议。
已使用switchport mode access命令配置交换机的Fa0/1 和Fa0/3 端口。
思科CCNA新版第3学期final-期末考试答案

思科CCNA新版第3学期final-期末考试答案1出于维护目的,已将路由器从网络中移除。
并已将新的 Cisco IOS 软件映 像成功下载到服务器并复制到路由器的闪存中。
应该在进行什么操作后再 将路由器放回网络中运行?备份新的映像。
将运行配置复制到 NVRAM 。
从闪存中删除之前版本的 Cisco IOS 软件。
重新启动路由器并检验新的映像是否成功启动。
答案 说明最高分值correctness of response Option 422请参见图示。
管理员尝试在路由器上配置 IPv6 的 EIGRP ,但收到如图所示 的错误消息。
配置 IPv6 的 EIGRP 之前,管理员必须发出什么命令?no shutdowneigrp router-id 100.100.100.100ipv6 unicast-routingipv6 eigrp 100ipv6 cef答案 说明 最高分值correctness of response Option 323IPv6 EIGRP 路由器使用哪个地址作为 hello 消息的来源?32 位路由器ID接口上配置的 IPv6 全局单播地址所有 EIGRP 路由器组播地址接口 IPv6 本地链路地址答案 说明 最高分值correctness of response Option 424下列关于 EIGRP 确认数据包的说法,哪两项是正确的?(请选择两项。
)发送该数据包是为了响应 hello 数据包。
该数据包用于发现接口上连接的邻居。
该数据包作为单播发送。
该数据包需要确认。
该数据包不可靠。
答案 说明 最高分值correctness of response Option 3 and Option 5 are correct.25何时发送 EIGRP 更新数据包?仅在必要时当获取的路由过期时每 5 秒通过组播发送每 30 秒通过广播发送答案 说明 最高分值correctness of response Option 126请参见图示。
思科网院[Cisco]第三学期Final题目及答案
![思科网院[Cisco]第三学期Final题目及答案](https://img.taocdn.com/s3/m/8c75bd0c7cd184254b353560.png)
1请参见图示。
网络支持技术人员需要为新路由器的一个FastEthernet 接口设置IP 地址。
但接口拒绝该地址,其原因是什么该IP 地址已在使用中。
技术人员使用的是网络地址。
技术人员为/26 使用了错误的子网掩码。
技术人员必须在该接口上启用VLSM。
2一个销售代表准备从酒店使用Internet 向公司总部发送敏感信息。
旅行前,IT 工作人员进行了必要工作以允许其安全访问该销售代表实施了什么解决方VPN帧中继带有CHAP 身份验证的PPP带有PAP 身份验证的PPP3下列哪两种说法正确描述了IEEE STP 的功能?(选择两项。
)它会立即将不处于丢弃状态的所有端口转换为转发状态。
它提供了一种在交换网络中禁用冗余链路的机制。
它有三种端口状态:丢弃、学习和转发。
它可确保交换网络中没有环路。
它可在不到 1 秒的时间内使交换网络收敛。
4请参见图示。
网络管理员必须为ISP 手动总结POP 路由器上的所有IP 地址。
下列哪项是正确的总结地址?192.168.0.0/2192.168.0.0/23192.168.0.0/24192.168.0.0/255请参见图示。
所有路由器都配置为使用带有默认设置的OSPF 协议。
如果同时启动所有路由器,哪台路由器将被选为BDRR1R2R3R46有关单区域OSPF 网络的说法中,哪两项正确?(选择两项。
)DR 和BDR 会减少在广播网络中发送的更新数量。
BDR 负责将更改发布到所有其它的OSPF 路由器。
路由器使用hello 数据包建立和维护邻居邻接关系。
所有OSPF 路由器都会接收组播地址224.0.0.6 上的更新。
区域 1 必须始终存在。
7请参见图示。
网络管理员按图示配置R1。
但是,网络 A 的一些主机无法访问Internet。
下列哪两个措施可解决此问题?(在正确的接口上配置ip nat inside和ip nat outside命令。
在NAT 地址池中增加IP 地址数量。
CCNA_3_Final_Exam_V4.0_Answers
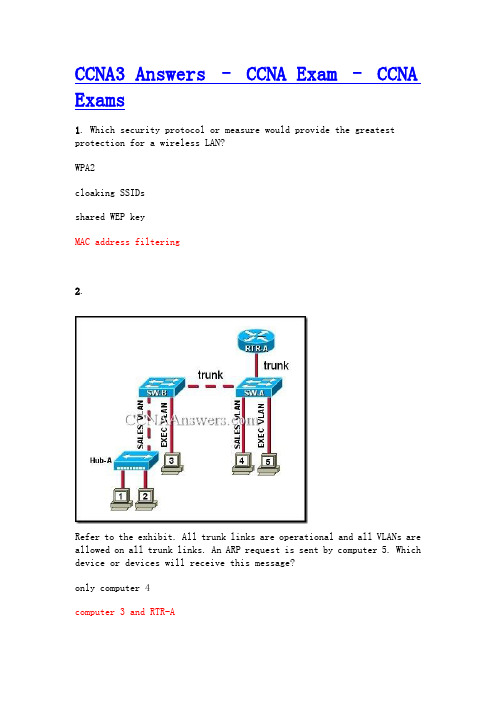
CCNA3 Answers – CCNA Exam – CCNA Exams1. Which security protocol or measure would provide the greatest protection for a wireless LAN?WPA2cloaking SSIDsshared WEP keyMAC address filtering2.Refer to the exhibit. All trunk links are operational and all VLANs are allowed on all trunk links. An ARP request is sent by computer 5. Which device or devices will receive this message?only computer 4computer 3 and RTR-Acomputer 4 and RTR-Acomputer 1, computer 2, computer 4, and RTR-Acomputer 1, computer 2, computer 3, computer 4, and RTR-Aall of the computers and the router3.Refer to the exhibit. Hosts A and B, connected to hub HB1, attempt to transmit a frame at the same time but a collision occurs. Which hosts will receive the collision jamming signal?only hosts A and Bonly hosts A, B, and Conly hosts A, B, C, and Donly hosts A, B, C, and E4.Refer to the exhibit. Router RA receives a packet with a source address of 192.168.1.65 and a destination address of 192.168.1.161. What will the router do with this packet?The router will drop the packet.The router will forward the packet out interface FastEthernet 0/1.1.The router will forward the packet out interface FastEthernet 0/1.2.The router will forward the packet out interface FastEthernet 0/1.3.The router will forward the packet out interface FastEthernet 0/1.2 and interface FastEthernet 0/1.3.5.Refer to the exhibit. Which two settings show the default value of VTP configuration on a Cisco 2960 switch? (Choose two.)revision numberexisting VLANsoperating modedomain namepruning mode6. Which value determines if a switch becomes the central point of reference in the spanning tree topology?lowest bridge IDhighest revision numberlowest numeric IP addresshighest numeric MAC address7. What is the purpose of the Spanning Tree algorithm?It propagates VLAN configurations to other switches.It restricts broadcast packets to a single VLAN.It segments a network into multiple broadcast domains.It prevents loops in a switched network with redundant paths.8. What are two benefits of the IEEE 802.11n standard over the IEEE 802.11G? (Choose two.)requires less equipmentprovides improved rangepermits increased data rateshas a single-input and a single-outputneeds no hardware upgrade for compatibility9.Which configuration changes will increment the configuration revision number on the VTP server?configuring trunk links on the VTP serverconfiguring or changing the VTP passwordconfiguring or changing the VTP domain nameconfiguring or changing the VTP version numberconfiguring or deleting a VLAN or creating a VLAN name10.Refer to the exhibit. A company has acquired a new office in a campus environment. Switches in the existing office and the new office are directly connected by a trunk link. The VLANs and IP addressing are setup as shown in the exhibit. The computers in each office are not able to ping each other. What will fix the problem?Use an access link between S2 and S3.Connect S2 and S3 to a common router.Set the subnet mask in the new office to /24.Configure the new office default gateway to 172.17.10.1Change the port assignments in the new office to a different VLAN.11. What is a possible impact of setting too short an aging time in the MAC address table of a switch?overly large address tableunnecessary flooding of packetsexcessive timeouts of static addressesimpaired ability to dynamically learn new addresses12.Refer to the exhibit. The network administrator has just added VLAN 50 to Switch1 and Switch2. Hosts A, B, C, and D are correctly configured with IP addresses in the subnet range for VLAN 50. Host A can communicate with host B, but cannot communicate with host C or host D. What is the cause of this problem?There is a native VLAN mismatch.The Fa0/11 interface of Switch1 is not configured as a trunk.The link between Switch1 and Switch2 is up but not trunked.VLAN 50 is not allowed on the trunk link between Switch1 and Switch2.Refer to the exhibit. Users complain that they do not have connectivity to the web server that is connected to SW1. What should be done to remedy the problem?Allow all VLANs on the trunk link.Configure VLAN 100 as the native VLAN for SW1.Configure the trunk port in trunk mode on SW1.Attach the web server to a router and configure inter-VLAN routing.14. What VLANs are allowed across a trunk when the range of allowed VLANs is set to the default value?only the management VLANall VLANs except the extended range VLANsall VLANs except 1 and 1002-1005all VLANs15.Refer to the exhibit. A new host needs to be connected to VLAN 1. Which IP address should be assigned to this new host?192.168.1.11 /28192.168.1.22 /28192.168.1.33 /28192.168.1.44 /28192.168.1.55 /2816. Using the command copy tftp:backup.cfg startup-config, an administrator downloaded a saved configuration from a TFTP server to a switch. Why does the administrator not detect any changes in the switch configuration after the download completes?The command should have been copy startup-config tftp:backup.cfg.A backup configuration from a TFTP server cannot be copied directly into the startup-config.The command copy running-config startup-config should be used to save the changes on the switch.Downloading to the startup-config requires the switch to be reloaded in order for the configuration to take effect.17. What two methods can be used to remove MAC address table entries froma switch? (Choose two.)Power cycle the switch to clear all dynamically learned addresses.The clear switching-tables command will remove statically configured entries.The clear mac-address-table command will remove statically and dynamically configured table entries.The erase flash command will clear all statically configured table entries.Statically configured MAC addresses will automatically be removed from the address table 300 minutes after the last activity on a switch port.18. Which type of traffic can still be received on a switch interface that is in STP blocking mode?BPDU framesmulticast framesbroadcast framesLayer 3 packets19. Which method establishes an administrative connection for configuring the Linksys WRT300N wireless access point?Associate with the access point and then open a HyperTerminal session with the access point.Physically connect to the access point and then reboot the computer to launch the configuration software.From a computer in the same IP subnet as the access point, enter the default IP address of the access point in a web browser.Modify the TCP/IP properties of the computer connected to the access point so that it exists on the same network, and then reboot your computer to establish a connection.20.Refer to the exhibit. All edge ports are configured with the spanning-tree portfast command. Host1 is recently connected to port Fa0/1 on switch SW1 . Which statement is true about the status of port Fa0/1?The port will transition into blocking state.The port will transition immediately into forwarding state.The port will transition into blocking state and then immediately into forwarding state.The port will transition into blocking state and immediately transition through the listening and learning states.21.Refer to the exhibit. What is true of the configuration of switch S1?A Cisco proprietary protocol is in use for ports Fa0/1 and Fa0/3.Switch ports Fa0/1 and Fa0/3 have been configured with the switchport mode access command.Untagged frames received on ports Fa0/1 and Fa0/3 will be placed on VLAN 1.Switch ports Fa0/1 and Fa0/3 are configured to carry data from multiple VLANs.22.Refer to the exhibit. The configuration steps that are listed in the exhibit have been entered in switch S1 via the console. Subsequent attempts to telnet to the switch are not successful. What is causing the problem?The switch must be configured with SSH version 1.The transport input command must specify Telnet access.The RSA keys must be returned to zero before SSH will permit Telnet access.The ip domain-name command must also be entered in line configuration mode for the vty lines.23.Refer to the exhibit. Which switch will be elected as the root bridge of the spanning tree topology?Cat-ACat-BCat-CCat-D24.Refer to the exhibit. VTP has been configured with VTP pruning enabled on all switches. If HostA sends a broadcast frame to SW1, which devices will receive the frame?SW1, SW3, HostFSW1, HostB, HostCSW1, SW2, SW3, SW4, HostFSW1, SW2, SW3, SW4, all hosts25.Refer to the exhibit. Which two statements are true about the operation of the interfaces? (Choose two.)Incoming traffic with VLAN ID 0 is processed by interface fa0/0.Incoming traffic that has a VLAN ID of 2 is processed by subinterface fa0/0.2.Both subinterfaces remain up with line protocol up, even if fa0/0 line protocol is down.Subinterfaces use unique MAC addresses by adding the 802.1Q VLAN ID to the hardware address.Traffic inbound on this router is processed by different subinterfaces, depending on the VLAN from which the traffic originated.26. The network administrator wants to configure a switch to pass VLAN update information to other switches in the domain but not update its own local VLAN database. Which two steps should the administrator perform to achieve this? (Choose two.)Reset the VTP counters.Configure VTP version 1 on the switch.Configure the VTP mode of the switch to transparent.Verify that the switch has a higher configuration revision number.Configure the switch with the same VTP domain name as other switches in the network.27.Refer to the exhibit. The devices in the network are operational and configured as indicated in the exhibit. However, hosts B and D cannot ping each other. What is the most likely cause of this problem?The link between the switches is up but not trunked.The Fa0/11 interface of Switch1 is not configured as a trunk.Hosts B and D are configured with IP addresses from different subnets. VLAN 20 and VLAN 30 are not allowed on the trunk between the switches.28.Refer to the exhibit. Users A and B are reporting intermittent connectivity problems. Pre-installation surveys showed strong signal strength from the AP locations to the client locations. Outside electrical interference has been eliminated. What will fix the problem?Relocate the APs closer to each other.Increase the distance between the clients.Change the channel on AP-B to 6 or 11.Place AP-A and AP-B on the same wireless channel.29. Why is it advisable that a network administrator use SSH instead of Telnet when managing switches?SSH uses TCP whereas Telnet does not.SSH encrypts only the username and password when logging in.SSH encrypts all remote management communications whereas Telnet does not.SSH sends a clear text message steam which reduces the bandwidth use for management.30.Refer to the exhibit. The teacher host is connected to port Fa0/7 on switch STW. A student has decided to share access to the Internet by attaching a hub and laptop to STW as shown. What will be the result of the student making this connection?The Fa0/7 port of STW will be shutdown.The student will gain full access to the Internet.Both the teacher and student will be able to receive data but only the teacher will be able to send.The frames from the laptop will be dropped, but the teacher host will maintain connectivity with the network.31. A network administrator configures a switch port with the command switchport mode dynamic auto. What is the resulting behavior of the switch port?The switch port is able to trunk if the remote switch port is set to auto.The switch port is able to trunk if the remote switch port is set to desirable.The switch port will be disabled if it is unable to successfully negotiate trunking.A successful trunk will be established if the remote switch is non-Cisco but the port is configured for trunking.32. Which STP port type can only appear once on a segment, and must be present in order for traffic to flow on that segment?non-root portdisabled portdesignated portnon-designated port33.Refer to the exhibit. What would happen if the network administrator moved the network cable of Host A from interface Fa0/1 to Fa0/3 on switch SW1?Host A remains a member of VLAN 10, because the router is routing traffic between VLANs.Host A is no longer a member of VLAN 10, because port Fa0/3 has been manually assigned to VLAN 30.Host A remains a member of VLAN 10, because the switch provides dynamic VLAN assignment for the port.Host A maintains connectivity to all members of VLAN 10, because it is connected to the same physical network.Host A is no longer a member of VLAN 10, but because port Fa0/3 was unused, it is now a member of VLAN 1.34.Refer to the exhibit. VLAN 10 has been configured on the VTP server. Users who are assigned to VLAN 10 are connected as shown in the exhibit. On the basis of the outputs that are provided, which group of users will be able to communicate with the users on VLAN 10 on SW1?all the users who are connected only to SW2users on VLAN 10 who are connected only to SW3users on VLAN 10 who are connected only to SW4users on VLAN 10 who are connected to both SW3 and SW435.Refer to the exhibit. Which three options correctly identify information that could be associated with this output?(Choose three.)Interface FastEthernet3/0/0 is subinterfaced.A non-proprietary trunking protocol is in use.The configuration is appropriate for a router-on-a-stick network design.A shutdown command has been applied to interface FastEthernet3/0/0.Interface FastEthernet3/0/0.3 is mapped to the default management VLAN.An IP address should be applied to FastEthernet3/0/0 for correct data routing.36.Refer to the exhibit. The Layer 2 switching design that is shown has been implemented in a campus environment that is using Spanning Tree Protocol. All inter-switch links that are shown are trunks. Whenever an inter-switch link fails, the network takes nearly a minute to completely converge. How can the convergence time be reduced?Increase the capacity of the distribution and core trunk links to 10 Gb/s.Add a trunk link that directly connects D1 and D2.Use Layer 3 switching on the core switch.Implement Rapid Spanning Tree Protocol.37.Refer to the exhibit. Each switch is configured to participate in STP for VLANs 1, 10, 20, and 30. Which switch will become the root for VLAN 20?ABCD38.Refer to the exhibit. Switches S2 and S3 are properly connected using an ethernet cable. A network administrator has configured both switches with VTP, but S3 is unable to propagate VLANs to S2. What could be the reason for this?The VTP configuration revision is different on both switches.The VTP domains are different on both switches.VTP pruning is disabled.VTP v2 is disabled.39. In a three-layer hierarchical network design, which distribution layer function delineates broadcast domains?routing between VLANsaggregating traffic flowsproviding redundant linksreducing the network diameter40. Which parameter is used to uniquely identify one wireless network from another?SSIDOFDMWEPDSSS41. What is one disadvantage that 802.11a wireless has compared to 802.11g?Use of the 5GHz band requires much larger antennas.The OFDM modulation technique results in a slower data rate.There are fewer non-overlapping channels available to help reduce RF interference.The use of higher frequencies means that signals are more likely to be obstructed.42. Which three statements are correct concerning the default configuration of a new switch? (Choose three.)It is configured in VTP server mode.STP is automatically enabled.The first VTY line is automatically configured to allow remote connections.VLAN1 is configured with a management IP address.All switch ports are assigned to VLAN1.The enable password is configured as cisco.43.Refer to the exhibit. How is port Gi1/1 on SWT-A functioning in the spanning-tree topology?It is sending and receiving data frames.It is receiving BPDUs, but not sending data frames.It is participating in the election process by forwarding the BPDUs it receives.It is receiving BPDUs and populating the MAC address table, but not sending data.44. While configuring a new switch, a network administrator configures the switch as an HTTP server. What benefits does this configuration provide?This allows the switch to host web pages for the network.This allows remote VPN connections to the switch over the Internet.This is required if a web server or web farm is attached to the switch. This allows web-based configuration tools to be used with the switch.45. Which statement describes the use of voice VLANs in Cisco IP telephony? The voice VLAN carries both tagged and untagged traffic.The voice VLAN carries untagged traffic having special QoS markings.The voice VLAN must be configured on the switch port to which the IP phone attaches.Data and voice frames are tagged with same VLAN ID between the IP phone and the switch when a voice VLAN is configured.46.Refer to the exhibit. If switch SW1 is configured with the four VLANs as shown in the exhibit, how many physical interfaces are needed on router R1 to configure inter-VLAN routing using subinterfaces?zeroonetwofour47.Refer to the exhibit. What does the term DYNAMIC indicate in the output that is shown?This entry can only be removed from the MAC address table by a network administrator.When forwarding a frame to the device with address 0060.5c5b.cd23, the switch does not have to perform a lookup to determine the final destination port.Only the device with MAC address 0060.5c5b.cd23 will be allowed to connect to port Fa0/18.The switch learned this MAC address from the source address in a frame received on Fa0/18.48.Refer to the exhibit. The VTP domain has been configured as shown in the exhibit. The network technician accidentally configured the VTP server as a VTP client. After the technician reloaded the switches, all usersin the VTP domain started to complain that they lost connectivity to the users on the same VLANs that are connected to other switches. What should be done in the future to prevent losing all VLAN configurations in a VTP domain?Configure all switches in VTP transparent mode and copy the VLAN configuration into flash.Configure all switches in the network as VTP clients and copy the VLAN configuration into NVRAM.Create a new domain and configure a second switch as a VTP server to take over in case of a primary VTP server failure.In the same domain, configure a second switch as a VTP server to take over in case of a primary VTP server failure.49.Refer to the exhibit. How does SW1 manage traffic coming from Host A?SW1 drops the traffic because it is untagged.SW1 leaves the traffic untagged and forwards it over the trunk.SW1 tags the traffic with the lowest VLAN ID value and forwards it over the trunk link.SW1 encapsulates the traffic with 802.1Q encapsulation and forwards it over the trunk link.50. An administrator is troubleshooting a PC on the network which is suffering from slow and intermittent connectivity. The PC has a ping success rate to the default gateway of less than half the ping attempts. Other PCs on the switch can consistently ping the default gateway. The switch port is configured for auto duplex and the PC is configured for full duplex. What will commonly cause this problem?The PC is set to full duplex. The switch port fails to autonegotiate the duplex setting and defaults to half duplex, which causes a duplex mismatch.The switch traffic is exceeding available frame buffers. The result is that frames are being dropped.The PC and the default gateway have different bandwidth Ethernet ports.The default gateway is not on the same switch that the PC is.51.Refer to the exhibit. A network administrator has segmented the network into two VLANs and configured Router1 for inter-VLAN routing. A test of the network, however, shows that hosts on each VLAN can only access local resources and not resources on the other VLAN. What is the most likely cause of this problem?Switch port Fa0/1 is not trunking.Router interface Fa0/0 is possibly down.No routing protocol is configured on Router1.One of the router subinterfaces is possibly down.52.What impact does the use of the mdix auto configuration command have on an Ethernet interface on a switch?automatically detects duplex settingsautomatically detects interface speedautomatically detects copper cable typeautomatically assigns the first detected MAC address to an interface。
思科第三学期期末答案(final)
1如果共享内存缓冲区和端口内存缓冲区已满,以太网交换机会如何处理流量?交换机会在NVRAM 中分配更多缓冲区。
交换机会对帧进行碎片整理,然后将其存储到NVRAM 中。
交换机会将数据包路由到目的端口。
交换机会丢弃流量。
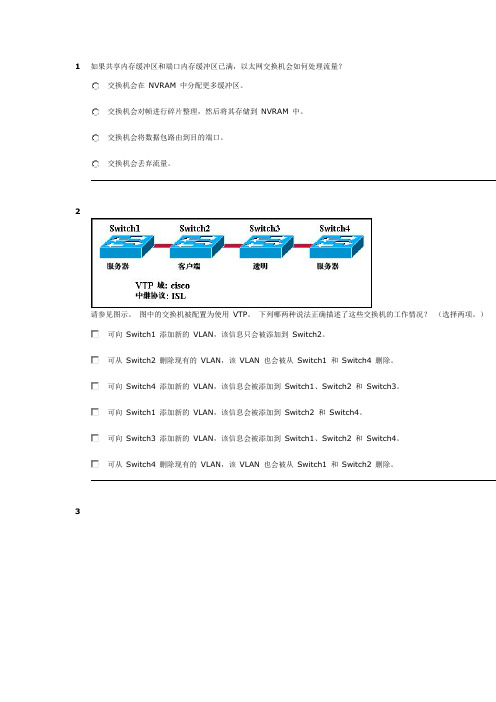
2请参见图示。
图中的交换机被配置为使用VTP。
下列哪两种说法正确描述了这些交换机的工作情况?(选择两项。
)可向Switch1 添加新的VLAN,该信息只会被添加到Switch2。
可从Switch2 删除现有的VLAN,该VLAN 也会被从Switch1 和Switch4 删除。
可向Switch4 添加新的VLAN,该信息会被添加到Switch1、Switch2 和Switch3。
可向Switch1 添加新的VLAN,该信息会被添加到Switch2 和Switch4。
可向Switch3 添加新的VLAN,该信息会被添加到Switch1、Switch2 和Switch4。
可从Switch4 删除现有的VLAN,该VLAN 也会被从Switch1 和Switch2 删除。
3请参见图示。
网络中的所有设备均通过中继链路互连,且在所有三台交换机上启用了VTP 修剪。
交换机SW3 上的哪些修剪?VLAN 10 和VLAN 20VLAN 1、VLAN 10 和VLAN 20VLAN 1 以及VLAN 1002 至1005VLAN 1、VLAN 10、VLAN 20 以及VLAN 1002 至10054可采用哪两种方法删除交换机的MAC 地址表中的条目?(选择两项。
)关闭交换机电源并再次打开以清除所有动态获知的地址。
可采用clear switching-tables命令删除静态配置的条目。
可采用clear mac-address-table命令删除静态配置和动态配置的条目。
可采用erase flash命令删除静态配置的所有条目。
在交换机端口不活动达300 分钟后,地址表中静态配置的MAC 地址会被自动删除。
思科网院考试题库和答案

思科网院考试题库和答案一、单选题1. 思科网院课程中,CCNA(Cisco Certified Network Associate)认证主要涉及哪些技术领域?A. 网络基础B. 网络安全C. 无线网络D. 云服务答案:A2. 在思科网院的课程中,OSI模型的第3层是什么?A. 应用层B. 传输层C. 数据链路层D. 网络层答案:D3. 以下哪个协议是用于在IP网络中路由数据包的?A. TCPB. UDPC. IPD. ICMP答案:C4. 思科网院课程中,哪个设备用于连接不同网络或子网?A. 路由器B. 交换机C. 集线器D. 网桥答案:A5. 在思科网院课程中,VLAN(虚拟局域网)的主要作用是什么?A. 提高网络速度B. 提高网络安全性C. 增加网络带宽D. 减少网络延迟答案:B二、多选题6. 思科网院课程中,以下哪些因素会影响网络的性能?A. 带宽B. 延迟C. 丢包率D. 网络拓扑结构答案:A, B, C, D7. 在思科网院课程中,以下哪些设备属于网络核心层设备?A. 路由器B. 交换机C. 集线器D. 网桥答案:A, B8. 思科网院课程中,以下哪些协议属于传输层协议?A. TCPB. UDPC. IPD. ICMP答案:A, B9. 在思科网院课程中,以下哪些因素可以提高网络的安全性?A. 使用防火墙B. 定期更新软件C. 限制不必要的服务D. 使用VPN答案:A, B, C, D10. 思科网院课程中,以下哪些技术可以用于网络故障排除?A. PINGB. TRACEROUTEC. SHOW COMMANDSD. PACKET TRACER答案:A, B, C, D三、判断题11. 思科网院课程中,IP地址192.168.1.1是一个公网IP地址。
(对/错)答案:错12. 在思科网院课程中,交换机可以减少网络中的冲突域。
(对/错)答案:对13. 思科网院课程中,路由器的主要功能是在不同网络之间转发数据包。
思科CCNA第三学期期末考试完整版

参加考试-ESwitchingFinalExam-CCNAExploration:LAN交换和无线(版本4.0)以下哪项参数用于唯一标识一个无线网络,使其与其它网络区分开来?SSIDOFDMWEPDSSS分层网络模型具有哪三项优点?(选择三项。
)带宽争用现象减少物理布局范围减小网络的容错能力提高无需配线间无需第三层功能管理和故障排除工作简化在将Catalyst交换机迁移到其它VTP管理域之前,应该进行哪三项任务?(项。
)选择正确的VTP模式和版本。
使用新管理域的名称配置交换机。
从新域中的VTP服务器上下载VTP数据库。
配置新域内的VTP服务器,使其识别该交换机的BID。
重置VTP计数器,使交换机可与新域内的其它交换机同步。
检验交换机的配置修订版号是否比新域内的其它交换机的低。
下列哪两种说法正确地描述了生成树协议?(选择两项。
)它只在第2层使用。
它在交换机上配置。
它消除了网络拓扑中的第2层环路。
它限制了端口上所允许的有效MAC地址的数量。
它使VLAN信息得以传播到网络中的其它交换机。
下列哪种方法可建立用于配置LinksysWRT300N无线接入点的管理连接?与接入点关联,然后与接入点建立超级终端会话。
以物理方式连接到接入点,然后重新启动计算机以启动配置软件。
在接入点所在的IP子网内的计算机上的web浏览器中输入接入点的默认址。
修改与接入点连接的计算机的TCP/IP属性,使其与接入点处于同一个然后重新启动计算机以建立连接。
请参见图示。
源地址并非0019.d2e4.d9f7的帧进入接口Fa0/24时会发生什么Fa0/24会变为error-disabled(错误-禁用)状态。
传入帧会被丢弃。
Fa0/24端口LED会关闭。
安全违规计数会增加。
可采用哪两种方法删除交换机的MAC地址表中的条目?(选择两项。
)关闭交换机电源并再次打开以清除所有动态获知的地址。
可采用clearswitching-tables命令删除静态配置的条目。
思科 ccna第三册final试题及答案
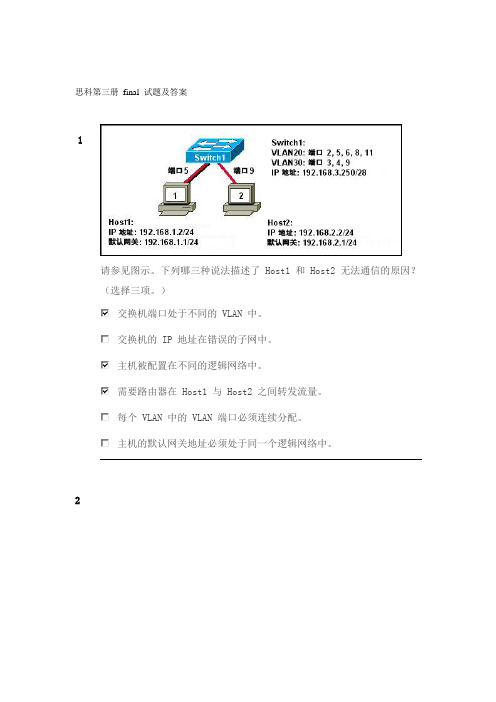
思科第三册final 试题及答案1请参见图示。
下列哪三种说法描述了 Host1 和 Host2 无法通信的原因?(选择三项。
)交换机端口处于不同的 VLAN 中。
交换机的 IP 地址在错误的子网中。
主机被配置在不同的逻辑网络中。
需要路由器在 Host1 与 Host2 之间转发流量。
每个 VLAN 中的 VLAN 端口必须连续分配。
主机的默认网关地址必须处于同一个逻辑网络中。
2请参见图示。
主机 PC_A 和主机 PC_B 同时发送流量,来自这两台发送站的帧发生了冲突。
最突信号的是哪台设备?集线器 HB1交换机 SW1路由器 R1交换机 SW2路由器 R2交换机 SW43请参见图示。
在生成树协议中,“学习”表示什么意思?交换机正在发送并接收数据帧。
交换机并未接收 BPDU,但正在发送并接收数据。
交换机正在通过转发收到的 BPDU 参与选举过程。
交换机正在接收 BPDU 并填充 MAC 地址表,但并未发送数据。
4请参见图示。
RTB 被配置为进行传统的 VLAN 间路由。
RTB 可以 ping 通计算机 A 但无法 pin 机 B。
此故障的原因可能是什么?Fa0/11 端口处于错误的 VLAN 中。
RTB 上没有有效的路由协议。
计算机 B 的 IP 地址在错误的逻辑网络中。
路由器的 Fa0/1 接口上配置了错误的中继封装类型。
5请参见图示。
网络管理员已将网络划分为两个 VLAN,R1 和 S1 的配置如图所示。
但是,PC1 无法问题很可能出在哪里?R1 上未配置路由协议。
S1 的 Fa0/1 端口不是中继端口。
S1 上未设置默认网关地址。
S1 和 R1 之间只配置了一条物理链路用于 VLAN 间路由。
6单臂路由器 VLAN 间路由有哪三项特征?(选择三项。
)需要使用 VTP需要使用子接口减少广播域的数量使用过多 VLAN 时会影响性能需要在路由器和至少一台交换机之间采用接入链路比用于 VLAN 间路由的其它方法更加经济规定至少要在路由器和交换机之间使用两个交换机端口7请参见图示。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1出于维护目的,已将路由器从网络中移除。
并已将新的 Cisco IOS 软件映 像成功下载到服务器并复制到路由器的闪存中。
应该在进行什么操作后再 将路由器放回网络中运行?备份新的映像。
将运行配置复制到 NVRAM 。
从闪存中删除之前版本的 Cisco IOS 软件。
重新启动路由器并检验新的映像是否成功启动。
答案 说明 最高分值correctness of response Option 422请参见图示。
管理员尝试在路由器上配置 IPv6 的EIGRP ,但收到如图所示 的错误消息。
配置 IPv6 的 EIGRP 之前,管理员必须发出什么命令?no shutdowneigrp router-id 100.100.100.100ipv6 unicast-routingipv6 eigrp 100ipv6 cef答案 说明 最高分值correctness of response Option 323IPv6 EIGRP 路由器使用哪个地址作为 hello 消息的来源?32 位路由器ID接口上配置的 IPv6 全局单播地址所有 EIGRP 路由器组播地址接口 IPv6 本地链路地址答案 说明 最高分值correctness of response Option 424下列关于 EIGRP 确认数据包的说法,哪两项是正确的?(请选择两项。
)发送该数据包是为了响应 hello 数据包。
该数据包用于发现接口上连接的邻居。
该数据包作为单播发送。
该数据包需要确认。
该数据包不可靠。
答案 说明 最高分值correctness of response Option 3 and Option 5 are correct.25何时发送 EIGRP 更新数据包?仅在必要时当获取的路由过期时每 5 秒通过组播发送每 30 秒通过广播发送答案 说明 最高分值correctness of response Option 126请参见图示。
从输出中可以得出哪两条结论?(请选择两项。
)有一个通向网络 192.168.1.8/30 的可行后继路由器。
网络 192.168.10.8/30 可通过 192.168.11.1 到达。
通向网络 192.168.1.0/24 的报告距离为 41024256。
邻居 172.16.6.1 符合到达 192.168.1.0/24 网络的可行性条件。
路由器 R1 具有通向 172.16.3.0/24 网络的两个后继路由器。
答案 说明 最高分值correctness of response Option 1 and Option 4 are correct.27请参见图示。
如果启用自动总结,则哪个或哪些路由会通告给路由器 ISP?10.0.0.0/810.1.0.0/1610.1.0.0/2810.1.1.0/2410.1.2.0/2410.1.3.0/2410.1.4.0/28答案说明最高分值correctness of responseOption 128请参见图示。
有关 R2 路由表中的网络 192.168.1.0 可以得出什么结论?此网络通过同一区域的内部路由器获知。
此网络通过来自 ABR 的总结 LSA 获知。
此网络直接连接到接口 GigabitEthernet0/0。
网络应用于将流量转发到外部网络。
答案 说明 最高分值correctness of response Option 229请参见图示。
公司已从单区域 OSPF 迁移到多区域。
但是,Branch1 办公室中 的用户无法联系新区域中网络 192.168.1.0/24 的任何用户。
根据图中所示的 输出,问题出在哪里?网络 192.168.1.0 的路由表中没有区域间路由。
OSPF 路由进程处于非活动状态。
通向新区域的链路出现故障。
该路由器未与其他 OSPF 路由器建立任何邻接关系。
答案 说明 最高分值correctness of response Option 1210OSPF 路由器何时成为 ABR ?当路由器的接口位于不同区域时当网络管理员将路由器配置为 ABR 时当路由器具有最高路由器 ID 时当路由器的 OSPF 优先级为 0 时答案 说明 最高分值correctness of response Option 1211网络管理员在路由器上升级 IOS 映像之前应检查下列哪个要求?FTP 服务器运行正常。
旧的 IOS 映像文件已删除。
闪存中有足够的空间。
所需的 IOS 映像文件下载到路由器。
答案 说明 最高分值correctness of response Option 3212Cisco IOS 12 和 IOS 15 版本之间有哪两点不同之处?(请选择两项。
)IOS 12 版本具有 15版本所没有的命令。
IOS 15 版许可证密钥对每个设备都是唯一的,而 IOS 12 版许可证密钥不特定于具体设备。
每个 Cisco ISR G2 平台路由器在 IOS 12 版中包括通用映像,但在 IOS 15 版中没有通用映像。
IOS 12.4(20) T1 版是主版本,而 IOS 15.1(1) T1 是新功能版本。
IOS 12 版有两个同时进行的系列,而 IOS 15 版也有两个系列,但是这两个 版本分别进行。
答案 说明 最高分值correctness of response Option 2 and Option 5 are correct.213网络管理员在路由器上发出命令 R1(config)# license boot module c1900 technology-package securityk9 。
此命令的用途是什么?IOS 会提示用户重新启动路由器。
安全软件包中的功能将立即可用。
IOS 会提示用户提供 UDI 以激活许可证。
激活安全技术包的评估使用权许可证。
答案 说明 最高分值correctness of response Option 4214网络管理员输入 spanning-tree portfast bpduguard default 命令。
在思科交换机上发出此命令会有什么结果?如果端口接收到 BPDU ,所有交换机端口将为错误禁用状态。
所有 TRUNK 端口可以立即连接到网络,而不是等待融合。
如果端口接收到 BPDU ,配置了 PortFast 的所有交换机端口将为错误禁用状态。
接收 BPDU 的所有交换机端口会忽略 BPDU 消息。
答案 说明 最高分值correctness of response Option 3215网络管理员正在对第 2 层交换网络中性能低下的问题进行故障排除。
在检查 IP 报头时,管理员发现 TTL 值没有减小。
为什么 TTL值没有减少?这是第2 层网络的正常行为。
MAC 地址表已满。
VLAN 数据库已损坏。
入站接口为半双工设置。
答案 说明最高分值correctness of response Option 1216STP 实例发生故障,并且帧在泛洪网络。
网络管理员应采取什么措施?网络管理员不需要做出响应,因为TTL 字段最终会阻止帧泛洪网络。
应禁用该 STP 实例的生成树,直至找到问题原因。
应调查并消除网络中的广播流量。
应以物理方式删除冗余链路,直到修复 STP 实例。
答案 说明 最高分值correctness of response Option 4217网络工程师正在配置 LAN 的冗余第一跳,以便更好地利用可用网络资源。
工程师应采用哪种协议?FHRP GLBP HSRPVRRP答案 说明 最高分值correctness of response Option 2218哪种模式配置设置可以在交换机 SW1 和 SW2 之间形成 EtherChannel 链路, 而无需发送协商流量?SW1:on SW2:onSW1:desirable SW2:desirableSW1:auto SW2:auto两台交换机均启用中继SW1:auto SW2:auto两台交换机均启用 PortFastSW1:passive SW2:active答案 说明 最高分值correctness of response Option 1219在两台交换机之间配置 EtherChannel 的两个必要条件是什么?(请选择两项。
)交换机上的相关接口必须是连续的。
所有接口要以相同速度运行。
所有接口要以相同的双工模式运行。
所有接口要分配给不同的 VLAN 。
链路两端必须存在不同的 VLAN 允许范围。
答案 说明 最高分值correctness of response Option 2 and Option 3 are correct.220什么时候应该关闭 EIGRP 自动总结?当路由器未在三分钟内发现相邻设备时当路由器具有三个以上的活动接口时当网络包含不连续的网络地址时当路由器具有五个以下的活动接口时当网络编址方案采用 VLSM 时答案 说明 最高分值correctness of response Option 3221要形成包括 5 个接入点的群集,必须满足哪两个条件?(请选择两项。
)必须在 AP 上启用群集模式。
形成群集至少要有两个控制器。
AP 必须连接在相同的网段上。
AP 必须配置使用不同的无线模式。
AP 必须使用不同群集名称。
答案 说明 最高分值correctness of response Option 1 and Option 3 are correct.222IEEE 801.11n 网络用户投诉速度慢。
网络管理员检查 AP 并检验其是否正常运行。
采取什么操作可以提高无线网络性能?分割 802.11n 2.4 GHz 频段和 5 GHz 频段之间的无线流量。
更改 AP 上的身份验证方法。
切换为 802.11g AP 。
将 AP 设置为混合模式。
答案说明 最高分值correctness of response Option 1223在当地一所大学里,学生不用密码即可连接到无线网络。
该接入点使用哪种模式? 网络开放被动共享密钥答案说明最高分值correctness of responseOption 2224哪种无线身份验证方法取决于 RADIUS 身份验证服务器?WEPWPA 个人WPA2 个人WPA2 企业答案说明最高分值correctness of responseOption 4225 请参见图示。
网络管理员可以从此输出得出哪两方面的信息?(请选择两项。
)R1 参与多区域 OSPF。
使用的 OSPF 进程号为 0。
接口 Fa0/1 不参与 OSPF 进程。
R1 是连接到 10.0.0.4 网络的路由器的分布点。
将要安装到路由表中的 10.0.0.0 路由的度量是 65 (64+1)。
