计算机专业英语的第四版课后习题翻译
计算机专业英语的第四版课后习题翻译讲课教案

中译英参考答案Unit 1A computer system consists of hardware system and software system. The hardware of the computer is usually divided into three major parts or three primary subsystems: the CPU, the memory subsystem, and the I/O subsystem.The CPU performs many operations and controls computer. The memory subsystem is used to store program being executed by the CPU, along with the program’s data. The I/O subsystem allows the CPU to interact with input and output devices such as the keyboard and monitor of a personal computer. The components of the computer are connected to the buses.The part of the computer that performs the bulk of data processing operations is called the central processing unit and is referred to as the CPU. In microcomputer, it is often called the microprocessor. The CPU is made up of three major parts: control unit, ALU, and register set.Memory is also known as internal memory or main memory. It refers to the circuits in the computer that hold whatever programs and data are available for immediate use by the CPU.I/O subsystem includes I/O devices and interface. There are a wide variety of I/O devices, such as mouse, printer, sensor, disk, and so on. Input-output interface provides a method for transferring information between internal storage and external I/O devices. Peripherals connected to a computer need special communication links for interfacing them with the CPU. The purpose of the communication link is to resolve the differences that exist between the central computer and each peripheral.Unit 2Storage hardware provides permanent storage of information and programs for retrieval by the computer. Hard disk drives store information in magnetic particles embedded in a disk. Usually a permanent part of the computer, hard disk drives can store large amounts of information and retrieve that information very quickly.Although fixed hard drive systems offer faster access and have a higher storage capacity than optical discs, optical disc systems use removable media –a distinct benefit. Optical discs –primary CDs and DVDs – are much more widely used than removable hard drive systems. They are the standard today for software delivery, as well as commonly used for storing high-capacity music and video files. There are also versions of both CD and DVD drives available for home audio and home theater use. Optical discs are commonly referred to as compact discs.CD and DVD discs are read by CD and DVD drives. The speed of a CD or DVD drive is rated as 24x, 32x, 36x, and so on. These labels describe how fast the drive is compared to the first version of that drive. For example, a 36x drive is 36 times the speed of the baseline unit that was originally manufactured. Most optical discs have a title and other text printed only on one side and they are inserted into the drive with the printed side facing up. When inserting such a CD or DVD, be careful not to get dirt, fingerprints, scratches, or anything else that might hinder light reflectivity on the disc’s surface.Unit 3(a) A program is a list of instructions or statements for directing the computer to perform arequired data processing task. Programming is a multistep process for creating that list of instructions.(b) It is important to understand the difference between a class and an object of that class. A class is simply a specification for creating objects. Thus, a single class may create multiple objects.(c) Java is an object-oriented, network-friendly high-lever programming language that allows programmers to build applications that can run on almost any operating system.(d) ActiveX is a set of controls, or reusable components that enables programs or content of almost any type to be embedded within a Web page. Whereas a Java must be downloaded each time you visit a Web site, with ActiveX the component is downloaded only once, then stored on your hard disk for later, repeated use.(e) Programming involves a great deal of creativity. The design is guide to the function or purpose of each component, but the programmer has great flexibility in implementing the design as code. No matter what language is used, each program component involves at least three major aspects: control structures, algorithms, and data structures.Unit 4The software system can be divided into two broad categories: application software and system software. Application software consists of the program for performing tasks particular to the machine’s utilization. In contrast to application software, system software comprises a large number of programs. These programs start up the computer and function as the principle coordinator of all hardware components and application software. Without system software loaded into RAM of your computer, your hardware and application software are useless.System software can be grouped into three basic parts: operating system, utility software, and language translators. The majority of an installation’s utility software consists of programs for performing activities that are fundamental to computer installations yet not included in the operating system. In a sense, utility software consists of software units that extend the capabilities of the operating system.A computer’s OS is the main collection of programs that manage its activities. The primary chores of an OS are management and control. The OS ensures that all actions requested by a user are valid and processed in an orderly fashion. It also manages the computer system’s resources to perform these operations with efficiency and consistency.Application software is the software designed to help you solve problems specific to business or perform specific business tasks. Application software then is the layer of software closest to you. Basically, there are four categories of application software: productivity software, business and specialty software, entertainment software and education/reference software.Unit 5A computer network is often classified as being either a local area network (LAN), a metropolitan area network (WAN), or a wide area network (WAN). The connection of two or more networks is called an internetwork. The worldwide Internet is a well-known example of an internetwork.LANs are privately owned networks within a single building or campus of up to a few kilometers in size. They are widely used to connect personal computers and workstations incompany offices and factories to share resources and exchange information.In general, a given LAN will use only one type of transmission medium. Various topologies are possible for LANs. The most common LAN topologies are bus, ring and star.A MAN is basically a bigger version of a LAN and normally uses similar technology. MAN is designed to extend over an entire city. It may be a single network such as a cable television network, or it may be a means of connecting a number of LANs into a large network so that resources may be shared LAN-to-LAN as well as device-to-device. For example, a company can use a MAN to connect the LANs in all of its offices throughout a city.A W AN spans a large geographical area that may comprise a country, a continent, or even the world. It provides long-distance transmission of data, voice, image, and video information over large geographical area.In contrast to LANs, W ANs may utilize public leased, or private communication devices, usually in combinations, and can therefore span an unlimited number of miles.Unit 6Transmission media are used to transfer messages over a network. For instance, the transmission media used in a network may be a privately owned set of cables, the public phone lines, or a satellite system. Transmission media can either be wired or wireless.The three types of wired media most commonly used to carry messages are twisted-pair wire, coaxial cable, and fiber-optic cable. One of the most successful developments in transmission media in recent years has been fiber optics. Fiber-optic cable is commonly used for the high-speed backbone lines of a network, or for Internet infrastructure.Wireless transmission media have become especially popular in recent years. They support communications in situations in which physical wiring is impractical or inconvenient, as well as facilitate mobility. Wireless media are commonly used to connect devices to a network, to share information between computers, to connect wireless mice to a computer, and for handheld PCs, wireless phones, and other mobile devices. Radio signals transferred through the air are the heart of most types of wireless media. In addition to conventional broadcast radio application, the microwave, cellular, and satellite transmission media also use radio signals to transmit data.Radio transmissions require the use of a transmitter to send the radio signals through the air.A receiver (usually containing some type of antenna) accepts the date at the other end. When a device functions as both a receiver and transmitter, it is commonly called a transceiver or transmitter-receiver.Unit 7(a) Since many database systems users are not computer trained, developers hide the complexity from users through several levels of abstraction, to simplify user’s interactions with the system: physical level, logical level, and view level.(b) A database schema is specified by a set of definitions expressed by a special language called a data-definition language (DDL). The result of compilation of DDL statements is a set of tables that is stored in a special file called data dictionary, or data directory.(c) The structured query language (SQL) is the most widely used and standard query language for relational database management systems. It is a kind of non-procedural language.(d) An entity is a “thing”or “object”in the real world that is distinguishable from otherobjects. For example, each person is an entity, and bank accounts can be considered to be entities. Entities are described in a database by a set of attributes.(e) Data warehouse is one of the newest and hottest buzzwords and concepts in the IT field and the business environment. A data warehouse is a logical collection of information——gathered from many different operational databases——that supports business analysis activities and decision-making tasks.Unit 8Animation is the term used to describe a series of graphical images that are displayed one after the other to simulate movement. Cartoons on television are one example of animation.Video differs from animation in that it usually begins as a continuous stream of visual information that is broken into separate images or frames when the video is recorded. When the frames are projected—typically at a rate of 30 frames per second—the effect is a smooth reconstruction of the original continuous stream of information. As you might imagine, at 30 frames per second, the amount of data involved in displaying a video during a multimedia presentation can require a substantial amount of storage space. Consequently, video data—like audio data—is often compressed. A variety of compression standards exist. Some of the most common video file formats are .avi, .mpeg, .mov, .rm.For multimedia presentation, video may be recorded using a standard (analog) video camera and then converted to digital form as it is input into a computer. Alternatively, the film can be recording digitally using a digital video camera. Streaming video is frequently used on Web pages to reduce file size. Similar to streaming audio, Streaming video files can begin playing once a portion of the video has been downloaded.Unit 9(a) AI is currently being applied in business in the form of knowledge systems, which use human knowledge to solve problems. The most popular type of knowledge-based system is the expert system. An expert system is a computer program that attempts to represent the knowledge of human experts in the form of heuristics. The term heuristic is derived from the same Greek root as the word eureka, which means “to discover”.(b) The user interface enables the manager to enter instructions and information into the expert system and to receive information from it. The instructions specify the parameters that guide the expert system through its reasoning processing. The information is in the form of values assigned to certain variables.(c) The knowledge base contains both facts that describe the problem area and knowledge representation techniques that describe how the facts fit together in a logical manner. The term problem domain is used to describe the problem area.(d) An expert system, also called a knowledge-based system, is an artificial intelligence system that applies reasoning capabilities to reach a conclusion. Expert systems are excellent for diagnostic and prescriptive problems.(e) The DSS is not intended to replace the manager. The computer can be applied to the structured portion of the problem, but the manager is responsible for the unstructured portion——applying judgment or intuition and conducting analyses.Unit 10The linked list (see figure 1) consists of a series of nodes, which are not necessarily adjacent in memory. Each node contains the element and a link to a node containing its successor. We call this the next link. The last cell’s next link references null.To execute printList or find(x) we merely start at the first node in the list and then traverse the list by following the next links. This operation is clearly linear-time, as in the array implementation, although the constant is likely to be larger than if an array implementation were used. The findKth operation is no longer quite as efficient as an array implementation; findKth(i) takes O(i) time and works by traversing down the list in the obvious manner. In practice, this bound is pessimistic, because frequently the calls to findKth are in sorted order (by i). As an example, findKth(2), findKth(3), findKth(4), and findKth(6) can all be executed in one scan down the list.The remove method can be executed in one next reference change. Figure 2 shows the result of deleting the second element in the original list.The insert method requires obtaining a new node from the system by using a new call and then executing two reference maneuvers. The general idea is shown in figure 3. The dashed line represents the old next reference.figure 1figure 2figure 3Unit 11(a) A set is pure if all of its members are sets, all members of its members are sets, and so on. For example, the set containing only the empty set is a nonempty pure set.(b) A language is a describable set of finite strings, drawn from a fixed alphabet. A grammar is one way to "describe" the language. The grammar consists of a finite list of rules, where each rule replaces one substring with another. The string on the left must contain at least one nonterminal. The first string "produces" or "generates" the second. Thus a rule is also called a production.(c) A finite-state machine (FSM) or finite-state automaton(FA)is a mathematical abstraction sometimes used to design digital logic or computer programs. It is a behavior model composed of a finite number of states, transitions between those states, and actions, similar to a flow graph in which one can inspect the way logic runs when certain conditions are met.(d) Sometimes it is inconvenient or impossible to describe a set by listing all of its elements. Another useful way to define a set is by specifying a property that the elements of the set have in common. The notation P(x) is used to denote a sentence or statement P concerning the variable object x. The set defined by P(x) written {x | P(x)}, is just a collection of all the objects for whichP is true.Unit 12(a) Because drawings are typically displayed in 3D, CAD is especially helpful in designing automobiles, aircraft, ships, buildings, electrical circuits (including computer chips), and even clothing.(b) Computer-integrated manufacturing (CIM) is the manufacturing approach of using computers to control the entire production process. This integration allows individual processes to exchange information with each other and initiate actions. Through the integration of computers, manufacturing can be faster and less error-prone, although the main advantage is the ability to create automated manufacturing processes.(c) In addition to supporting decision making, coordination, and control, information system may also help managers and workers analyze problems, visualize complex subjects, and create new products.(d) Knowing the history and evolution of ERP is essential to understanding its current application and its future developments.(e) In addition to monitoring operational activities such as tracking the status of orders and inventory levels, enterprise system also improve organization-wide reporting and decision making.Unit 13(a) There are a wide variety of educational application programs available. Educational software is designed to teach one or more skills, such as reading, math, spelling, a foreign language, world geography, or to help prepare for standardized tests.(b) Electronic business (e-business) is the use of information technology and electronic communication networks to exchange business information and conduct transactions in electronic, paperless form.(c) Word processing software allows you to use computers to create, edit, store, and print documents. You can easily insert, delete, and move words, sentences, and paragraphs——without ever using an eraser.(d) What is a spreadsheet? Spreadsheet software takes its name from the accountant’s columnar worksheet, which it imitates. A spreadsheet is a worksheet consisting of a collection of cells formed by the intersection of rows and columns. Each cell can store one piece of information: a number, word or phrase, or formula.Unit 14(a) A geographic information system (GIS) is a system that captures, stores, analyzes, manages and presents data with reference to geographic location data. In the simplest terms, GIS is the merging of cartography, statistical analysis and database technology.(b) The GPS receiver uses the messages it receives to determine the transit time of each message and computes the distance to each satellite. These distances along with the satellites' locations are used to compute the position of the receiver. This position is then displayed, perhaps with a moving map display or latitude and longitude; elevation information may be included.(c) Virtual reality (VR) is a term that applies to computer-simulated environments that can simulate physical presence in the real world. Most current virtual reality environments areprimarily visual experiences, displayed either on a computer screen or through special stereoscopic displays, but some simulations include additional sensory information, such as sound through speakers or headphones.Unit 15(a) The software development process is sometimes called the software development life cycle (SDLC), because it describes the life of a software product from its conception to its implementation, delivery, use, and maintenance.(b) How can the CMM help your organization? There are three key roles the CMM plays. First, the CMM helps build an understanding of software process by describing the practices that contribute to a level of process maturity. The second role of the CMM is to provide a consistent basis for conducting appraisals of software processes. The CMM’s third key role is to serve as a blueprint for software process improvement.(c) The UML offers a standard way to write a system’s blueprints, including conceptual things such as business processes and system functions as well as concrete things such as programming language statements, database schemas, and reusable software components. The UML represents a collection of the best engineering practices that have proven successful in the modeling of large and complex systems.(d) Object modeling is a technique for identifying objects within the system environment and the relationships between those objects. The object-oriented approach to system development is based on several concepts, such as object, attribute, behavior, encapsulation, class, inheritance, polymorphism, persistence, etc.Unit 16“Security” is an all-encompassing term that describes all the concepts, techniques, and technologies to protect information from unauthorized access. There are several requirements for information security.Confidentiality: hiding data, usually with encryption, to prevent unauthorized viewing and access.Authenticity: the ability to know that the person or system you are communicating with is who or what you think it is.Access control: once a person or system has been authenticated, their ability to access data and use systems is determined by access controls.Data integrity: providing assurance that an information system or data is genuine.Availability: making sure that information is available to users in a secure way.To prevent unauthorized access, some type of identification procedure must be used. These vary from passwords to physical access object (access cards, etc.) to biometric devices that verify some type of personal characteristic, such as a fingerprint.Some of the most secure access control systems address both identification and authentication. Identification involves verifying that the person’s name or other identifying feature is listed as an authorized user; authentication refers to determining whether or not the person is actually who he or she claims to be.Unit 17A distributed system is a collection of independent computers which appear to the users of system as a single computer. Nearly all large software systems are distributed. For example, enterprise-wide business systems must support multiple users running common applications across different sites.A distributed system encompasses a variety of applications, their underlying support software, the hardware they run on, and the communication links connecting the distributed hardware. The largest and best-known distributed system is the set of computers, software, and services comprising the World Wide Web, which is so pervasive that it coexists with and connects to most other existing distributed systems. The most common distributed systems are networked client/server systems. Distributed systems share the general properties described below.●Multiple nodes●Message passing or communication●Resource sharing●Decentralized control●Concurrency or parallelism●Fault tolerance●Heterogeneity●OpennessDistributed systems have many inherent advantages, especially over centralized systems. Some applications are inherent distributed as well. In general, distributed systems:●Yield higher performance●Allow incremental growth●Allow one user to run a program on many different machines in parallel●Provide higher reliability。
计算机专业英语教程(第四版)习题答案
计算机专业英语教程(第四版)习题答案计算机专业英语教程(第四版)习题答案计算机专业英语(第四版)课后习题答案Unit 1 [Ex 1] Fb5E2RGbCAP [Ex 2] 1. input, storage, processing, and output 2. power; speed; 1. F 2. T 3. T 4. F 5. T 6. T 7. T 8. T 9. T 10.memoryp1EanqFDPw 3. central processing unit memoryDXDiTa9E3d 5. keyboard; [Ex 3] B. A. central processing unit; 1. F 2. D 2. monitor 3. G 4. C 5. B main memory; 6. A 7. E monitorRTCrpUDGiT 8. H5PCzVD7HxA 4. internal; primary;1. user3. data4. keyboard5. data processingjLBHrnAILg6. information [Ex 4] instructions7. computer8. memory 3. manipulates 4.1. input device2. screen, screen 5. retrievexHAQX74J0X 8. Function6. code7. hard copy[Ex. 5] 新处理器开始IT 技术的新时代New Processors Open New Era of IT Technologies Last week, Intel introduced to the public in Russia and other CIS countries a family of processors Intel Xeon E5-2600. They are more powerful and reliable and, importantly, are very economical in terms of energy consumption. Their1 / 30presence opens a new era in the field of IT technologies and means that the cloud technology is getting closer.LDAYtRyKfEThese processors are primarily designed for servers, data centers (DPC) and supercomputers. The emergence of this class of devices is not accidental. According to the regional director of Intel in Russia and other CIS states Dmitri Konash who spoke at the event, the market of IT-technology is developing so rapidly that, according to forecasts, by 2015 there will be 15 billion devices connected to the Internet, and over 3 billion of active users.Zzz6ZB2Ltk 上周,英特尔公司向俄罗斯和其它独联体国家的公众推出了英特尔Xeon E5-2600 系列处理器,它们更加强大可靠,尤其是在能量消耗方面更加经济实惠。
《计算机英语(第4版)》课后练习参考答案.8-12selectA
Unit Eight: The InternetUnit Eight/Section AI.Fill in the blanks with the information given in the text:1.research2.ICANN或the Internet Corporation for Assigned Names and Numbers3.router; gateway4.temporary/dial-up; permanent/dedicated5.ISP或Internet service providerwork; host7.decimal8.mnemonicII.Translate the following terms or phrases from English into Chinese and vice versa:1.cell phone 蜂窝电话,移动电话,手机2.IP address 网际协议地址,IP地址3.autonomous system 自主系统4.dial-up connection 拨号连接work identifier 网络标识符6.binary notation 二进制记数法7.mnemonic name 助记名,缩写名8.Internet-wide directory system 因特网范围的目录系统 server 名称服务器10.Internet infrastructure 因特网基础结构11.助记地址mnemonic address12.网吧cyber cafe13.宽带因特网访问broadband Internet access14.顶级域名top-level domain (TLD)15.因特网编址Internet addressing16.点分十进制记数法dotted decimal notation17.因特网服务提供商Internet service provider (ISP)18.专用因特网连接dedicated Internet connection19.主机地址host address20.硬件与软件支持hardware and software supportIII.Fill in each of the blanks with one of the words given in the following list, making changes if necessary:Early computer networks used leased telephone company lines for their connections.Telephone company systems of that time established a single connection between sender and receiver for each telephone call, and that connection carried all data along a single path. Whena company wanted to connect computers it owned at two different locations, the companyplaced a telephone call to establish the connection, and then connected one computer to each end of that single connection.The U.S. Defense Department was concerned about the inherent risk of this single-channel method for connecting computers, and its researchers developed a different method of sending information through multiple channels. In this method, files and messages are broken into packets that are labeled electronically with codes for their origins, sequences, and destinations. In 1969, Defense Department researchers in the Advanced Research Projects Agency (ARPA) used this network model to connect four computers into a network called the ARPANET. The ARPANET was the earliest of the networks that eventually combined to become what we now call the Internet. Throughout the 1970s and 1980s, many researchers in the academic community connected to the ARPANET and contributed to the technological developments that increased its speed and efficiency.IV.Translate the following passage from English into Chinese:因特网只是提供了将许许多多的计算机连接在一起的物理与逻辑基础结构。
计算机英语(第4版)--刘艺--课文参考译文
《计算机英语(第4版)》参考译文第一单元:计算机与计算机科学课文A:计算机概览一、引言计算机是一种电子设备,它能接收一套指令或一个程序,然后通过对数字数据进行运算或对其他形式的信息进行处理来执行该程序。
要不是由于计算机的发展,现代的高科技世界是不可能产生的。
不同类型和大小的计算机在整个社会被用于存储和处理各种数据,从保密政府文件、银行交易到私人家庭账目。
计算机通过自动化技术开辟了制造业的新纪元,而且它们也增强了现代通信系统的性能。
在几乎每一个研究和应用技术领域,从构建宇宙模型到产生明天的气象报告,计算机都是必要的工具,并且它们的应用本身就开辟了人们推测的新领域。
数据库服务和计算机网络使各种各样的信息源可供使用。
同样的先进技术也使侵犯个人隐私和商业秘密成为可能。
计算机犯罪已经成为作为现代技术代价组成部分的许多风险之一。
二、历史第一台加法机是法国科学家、数学家和哲学家布莱斯•帕斯卡于1642年设计的,它是数字计算机的先驱。
这个装置使用了一系列带有10个齿的轮子,每个齿代表从0到9的一个数字。
轮子互相连接,从而通过按照正确的齿数向前转动轮子,就可以将数字彼此相加。
17世纪70年代,德国哲学家和数学家戈特弗里德•威廉•莱布尼兹对这台机器进行了改良,设计了一台也能做乘法的机器。
法国发明家约瑟夫―玛丽•雅卡尔,在设计自动织机时,使用了穿孔的薄木板来控制复杂图案的编织。
在19世纪80年代期间,美国统计学家赫尔曼•何勒里斯,想出了使用类似雅卡尔的木板那样的穿孔卡片来处理数据的主意。
通过使用一种将穿孔卡片从电触点上移过的系统,他得以为1890年的美国人口普查汇编统计信息。
1、分析机也是在19世纪,英国数学家和发明家查尔斯•巴比奇,提出了现代数字计算机的原理。
他构想出旨在处理复杂数学题的若干机器,如差分机。
许多历史学家认为,巴比奇及其合伙人,数学家奥古斯塔•埃达•拜伦,是现代数字计算机的真正先驱。
巴比奇的设计之一,分析机,具有现代计算机的许多特征。
计算机专业英语教程 第四版 部分翻译和简答题

翻译:1、C++’s advantages include strong typing, operator overloading, and less emphasis on the preprocessor.C++的优点包括强类型,运算符重载和较少地强调预处理器。
2、A program instruction or a piece of data is stored in a specific primary storage location called an address.程序指令和数据是存储在主存中一个特殊的位置,称为地址空间3、A high-level language is an artificial language with which we can write various instructions. This is possible not because computer processors are now so technologically advanced that they can ‘understand’ these langu ages. You should translate from programming languages into machine language which can be understood by the computer processors. Compilers can accomplish this task. This does mean that a high-level language program is not directly executable: it must be compiled to produce processor program, which is executable.高级语言是一门人工的我们可以写入各种各样指令的语言。
计算机专业英语教程(第4版)译文8.1
计算机专业英语教程(第4版)译文8.1IntroductionMultimedia means, from the user’s perspective, that computer information can be represented through audio and/or video, in addition to text, image, graphics and animation .从用户的观点,多媒体技术意味着,计算机信息不仅可以通过文本、图象、图形和动画,还可以通过音频或者视频表现出来。
For example, using audio and video, a variety of dynamic situations in different areas, such as sport or ornithology lexicon, can often be presented better than just using text and image alone.例如,利用音频或者视频,许多不同领域的动态情形,例如运动场面、鸟类生活,能够比仅仅使用文本和图象更生动形象的表现出来。
The integration of these media into the computer provides additional possibilities for the use of computational power currently available (e.g., for interactive presentation of huge amounts of information ).多媒体与计算机的综合为计算机的普遍应用提供了额外的可行性(例如:大量信息的交互式表现)。
Furthermore, these data can be transmitted though computer andtelecommunication networks, which implies applications in the areas of information distribution and cooperative work.另外,这些数据可以通过意味着信息分工和合作工作。
《计算机专业英语(第4版)》Unit 1 Hardware Knowledge
2023/12/28
计算机专业英语第4版
14
• Gates stepped down as chief executive officer of Microsoft in January 2000.
• He remained as chairman and created the position of chief software architect.
• In June 2006, Gates announced that he would be transitioning from full-time work at Microsoft to part-time work, and full-time work at the Bill & Melinda Gates Foundation.
four basic units of simplified computer: the input unit, central processing unit (CPU), memory unit, and output unit.
2023/12/28
计算机专业英语第4版
20
2023/12/28
2023/12/28
计算机专业英语第4版
19
1.2 Computer Development
1.2.1 Text A • The hardware of a digital computer system
计算机英语(第4版)课文翻译与课后答案

第一部分《计算机英语》参考译文第一单元:计算机与计算机科学课文A:计算机概览一、引言计算机是一种电子设备,它能接收一套指令或一个程序,然后通过对数字数据进行运算或对其他形式的信息进行处理来执行该程序。
要不是由于计算机的发展,现代的高科技世界是不可能产生的。
不同类型和大小的计算机在整个社会被用于存储和处理各种数据,从保密政府文件、银行交易到私人家庭账目。
计算机通过自动化技术开辟了制造业的新纪元,而且它们也增强了现代通信系统的性能。
在几乎每一个研究和应用技术领域,从构建宇宙模型到产生明天的气象报告,计算机都是必要的工具,并且它们的应用本身就开辟了人们推测的新领域。
数据库服务和计算机网络使各种各样的信息源可供使用。
同样的先进技术也使侵犯个人隐私和商业秘密成为可能。
计算机犯罪已经成为作为现代技术代价组成部分的许多风险之一。
二、历史第一台加法机是法国科学家、数学家和哲学家布莱斯?帕斯卡于1642年设计的,它是数字计算机的先驱。
这个装置使用了一系列带有10个齿的轮子,每个齿代表从0到9的一个数字。
轮子互相连接,从而通过按照正确的齿数向前转动轮子,就可以将数字彼此相加。
17世纪70年代,德国哲学家和数学家戈特弗里德?威廉?莱布尼兹对这台机器进行了改良,设计了一台也能做乘法的机器。
法国发明家约瑟夫―玛丽?雅卡尔,在设计自动织机时,使用了穿孔的薄木板来控制复杂图案的编织。
在19世纪80年代期间,美国统计学家赫尔曼?何勒里斯,想出了使用类似雅卡尔的木板那样的穿孔卡片来处理数据的主意。
通过使用一种将穿孔卡片从电触点上移过的系统,他得以为1890年的美国人口普查汇编统计信息。
1、分析机也是在19世纪,英国数学家和发明家查尔斯?巴比奇,提出了现代数字计算机的原理。
他构想出旨在处理复杂数学题的若干机器,如差分机。
许多历史学家认为,巴比奇及其合伙人,数学家奥古斯塔?埃达?拜伦,是现代数字计算机的真正先驱。
巴比奇的设计之一,分析机,具有现代计算机的许多特征。
计算机专业英语教程第四版翻译课后练习题含答案
计算机专业英语教程第四版翻译课后练习题含答案简介《计算机专业英语教程》是针对计算机专业学生编写的一本英语教材。
本书旨在帮助学生通过学习计算机领域的专业英语词汇和语法,提升他们的英语能力和技能。
本文将为读者提供该教材第四版的课后练习题及答案。
第一课练习题1.将下列单词从易到难排序:chip, computer, algorithm, software,desktop2.将下列单词从中文翻译为英文:程序设计,硬件,操作系统,输入,输出3.请解释下列缩略语的全称:RAM,CPU,OS答案1.desktop, chip, computer, software, algorithm2.programming, hardware, operating system, input, output3.RAM(Random Access Memory),CPU(Central Processing Unit),OS(Operating System)第二课练习题1.请翻译下列句子:计算机的功能越来越强大,它可以执行许多任务。
2.请解释下列单词的意思:interface,protocol,server,router答案puters are becoming more and more powerful and they canperform many tasks.2.interface(接口), protocol(协议),server(服务器),router(路由器)第三课练习题1.请将下列单词按字母顺序排列:database,file,program,server,storage2.请填写下列句子的空格:计算机会读取从硬盘 __ (into)内存。
3.请解释下列单词的意思:database,algorithm,client,browser答案1.algorithm,database,file,program,server,storage2.into3.database(数据库),algorithm(算法),client(客户端),browser(浏览器)第四课练习题1.请翻译下列句子:今天我学会了如何编写计算机程序。
《计算机英语(第4版)》课后练习进步标准参考答案
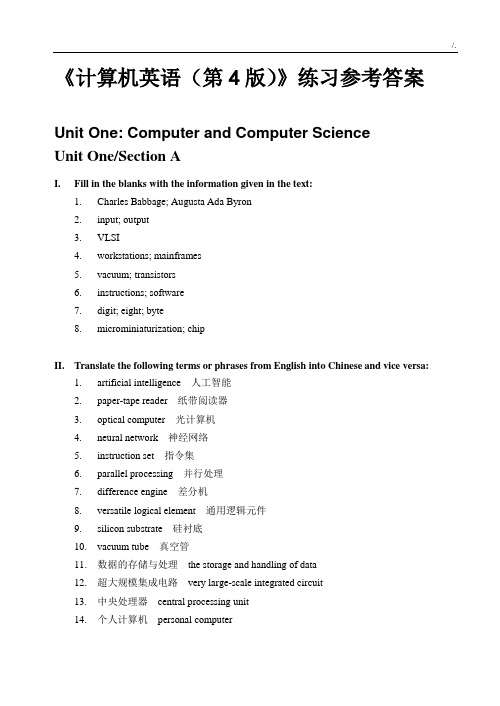
《计算机英语(第4版)》练习参考答案Unit One: Computer and Computer ScienceUnit One/Section AI.Fill in the blanks with the information given in the text:1. Charles Babbage; Augusta Ada Byron2. input; output3. VLSI4. workstations; mainframes5. vacuum; transistors6. instructions; software7. digit; eight; byte8. microminiaturization; chipII.Translate the following terms or phrases from English into Chinese and vice versa:1. artificial intelligence 人工智能2. paper-tape reader 纸带阅读器3. optical computer 光计算机4. neural network 神经网络5. instruction set 指令集6. parallel processing 并行处理7. difference engine 差分机8. versatile logical element 通用逻辑元件9. silicon substrate 硅衬底10. vacuum tube 真空管11. 数据的存储与处理the storage and handling of data12. 超大规模集成电路very large-scale integrated circuit13. 中央处理器central processing unit14. 个人计算机personal computer15. 模拟计算机analogue computer16. 数字计算机digital computer17. 通用计算机general-purpose computer18. 处理器芯片processor chip19. 操作指令operating instructions20. 输入设备input deviceIII.Fill in each of the blanks with one of the words given in the following list, making changes if necessary:We can define a computer as a device that accepts input, processes data, stores data, and produces output. According to the mode of processing, computers are either analog or digital.They can also be classified as mainframes, minicomputers, workstations, or microcomputers.All else (for example, the age of the machine) being equal, this categorization provides some indication of the compu ter’s speed, size, cost, and abilities.Ever since the advent of computers, there have been constant changes. First-generation computers of historic significance, such as UNIVAC(通用自动计算机), introduced in the early 1950s, were based on vacuum tubes. Second-generation computers, appearing in the early 1960s, were those in which transistors replaced vacuum tubes. In third-generation computers, dating from the 1960s, integrated circuits replaced transistors. In fourth-generation computers such as microcomputers, which first appeared in the mid-1970s, large-scale integration enabled thousands of circuits to be incorporated on one chip. Fifth-generation computers are expected to combine very-large-scale integration with sophisticated approaches to computing, including artificial intelligence and true distributed processing.IV. Translate the following passage from English into Chinese:计算机将变得更加先进,也将变得更加容易使用。
《计算机英语(第4版)》课后练习参考答案

Unit Two/Section AI.Fill in the blanks with the information given in the text:1.input; output; storage2.Basic Input/Output System3.flatbed; hand-held4.LCD-based5.dot-matrix; inkjet6.disk; memory7.volatile8.serial; parallelII.Translate the following terms or phrases from English into Chinese and vice versa:1.function key功能键,操作键,函数键2.voice recognition module 语音识别模块3.touch-sensitive region 触敏区4.address bus 地址总线5.flatbed scanner 平板扫描仪6.dot-matrix printer点阵打印机(针式打印机)7.parallel connection 并行连接8.cathode ray tube 阴极射线管9.video game 电子游戏10.audio signal 音频信号11.操作系统operating system12.液晶显示(器) LCD (liquid crystal display)13.喷墨打印机inkjet printer14.数据总线data bus15.串行连接serial connection16.易失性存储器volatile memory17.激光打印机laser printer18.磁盘驱动器disk drive19.基本输入 / 输出系统BIOS (Basic Inpul/Output System)changes if necessary:An access control mechanism mediates between a user (or a process executing on behalf of a user) and system resources、such as applications, operating systems, firewalls, routers, files, and databases. The system must first authenticate(验证)a user seeking access. Typically the authemiccition function determines whether the user is permitted to access the system at all. Then the access control function determines if the specific requested access by this user is permitted. A security administrator maintains an authorization(授权)d-sbase that specifies what type of access to which resources is allowed for this user. The access control function consults this database to detemine whether to grant access. An auditing function monitors and keeps a record of user accesses to system resources.In practice, a number of com—cmetus may cooperatively share the access control function. All mii,戏systems have at least a rudimentary(基本的),and in many cases a quite robust. access control component. Add-on security packages can add to the witi*access control capabilities of the OS. Particular applications or utilities,such as a database management system, also incorporate access control functions. External devices, such as firewalls, can also provide access control services.IV. Translate the following passage from English into Chinese:入侵者攻击从温和的到严重的形形色色。
计算机专业英语教程(第四版)习题答案

计算机专业英语(第四版)课后习题答案Unit 1[Ex 1] 1. F 2. T 3. T 4. F 5. T 6. T 7. T 8. T 9. T 10. F[Ex 2] 1. input, storage, processing, and output 2. power; speed; memory3. central processing unit4. internal; primary; memory5. keyboard; central processing unit; main memory; monitor[Ex 3] A. 1. F 2. D 3. G 4. C 5. B 6. A 7. E 8. HB. 1. user 2. monitor 3. data 4. keyboard 5. data processing6. information7. computer8. memory[Ex 4] 1. input device 2. screen, screen 3. manipulates 4. instructions 5. retrieve6. code7. hard copy8. Function[Ex. 5] 新处理器开始IT技术的新时代New Processors Open New Era of IT TechnologiesLast week, Intel introduced to the public in Russia and other CIS countries a family of processors Intel Xeon E5-2600. They are more powerful and reliable and, importantly, are very economical in terms of energy consumption. Their presence opens a new era in the field of IT technologies and means that the cloud technology is getting closer.These processors are primarily designed for servers, data centers (DPC) and supercomputers. The emergence of this class of devices is not accidental. According to the regional director of Intel in Russia and other CIS states Dmitri Konash who spoke at the event, the market of IT-technology is developing so rapidly that, according to forecasts, by 2015 there will be 15 billion devices connected to the Internet, and over 3 billion of active users.上周,英特尔公司向俄罗斯和其它独联体国家的公众推出了英特尔Xeon E5-2600系列处理器,它们更加强大可靠,尤其是在能量消耗方面更加经济实惠。
《计算机英语(第4版)》课后练习参考答案
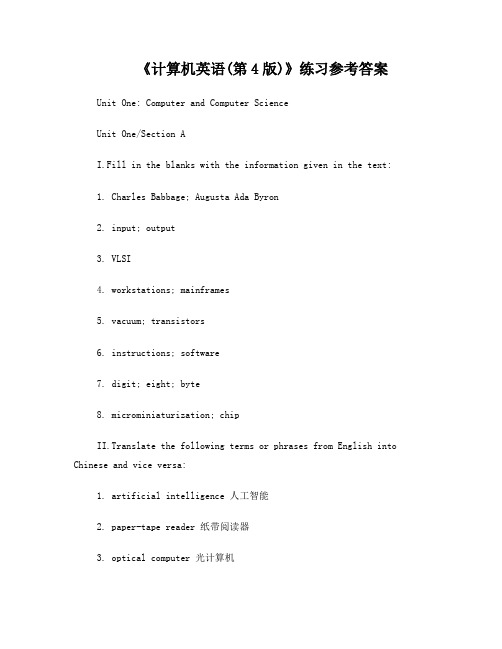
《计算机英语(第4版)》练习参考答案Unit One: Computer and Computer ScienceUnit One/Section AI.Fill in the blanks with the information given in the text:1. Charles Babbage; Augusta Ada Byron2. input; output3. VLSI4. workstations; mainframes5. vacuum; transistors6. instructions; software7. digit; eight; byte8. microminiaturization; chipII.Translate the following terms or phrases from English into Chinese and vice versa:1. artificial intelligence 人工智能2. paper-tape reader 纸带阅读器3. optical computer 光计算机4. neural network 神经网络5. instruction set 指令集6. parallel processing 并行处理7. difference engine 差分机8. versatile logical element 通用逻辑元件9. silicon substrate 硅衬底10. vacuum tube 真空管11. 数据的存储与处理the storage and handling of data12. 超大规模集成电路very large-scale integrated circuit13. 中央处理器central processing unit14. 个人计算机personal computer15. 模拟计算机analogue computer16. 数字计算机digital computer17. 通用计算机general-purpose computer18. 处理器芯片processor chip19. 操作指令operating instructions20. 输入设备input deviceIII.Fill in each of the blanks with one of the words given in the following list, making changes if necessary:We can define a computer as a device that accepts input, processes data, stores data, and produces output. According to the mode of processing, computers are either analog or digital.They can also be classified as mainframes, minicomputers, workstations, or microcomputers.All else (for example, the age of the machine) being equal, this categorization p rovides some indication of the compu ter’s speed, size, cost, and abilities.Ever since the advent of computers, there have been constant changes. First-generation computers of historic significance, such as UNIVAC(通用自动计算机), introduced in the early 1950s, were based on vacuum tubes. Second-generation computers, appearing in the early 1960s, were those in which transistors replaced vacuum tubes. In third-generation computers, dating from the 1960s, integrated circuitsreplaced transistors. In fourth-generation computers such as microcomputers, which first appeared in the mid-1970s, large-scale integration enabled thousands of circuits to be incorporated on one chip. Fifth-generation computers are expected to combine very-large-scale integration with sophisticated approaches to computing, includingartificial intelligence and true distributed processing.IV. Translate the following passage from English into Chinese:计算机将变得更加先进,也将变得更加容易使用。
《计算机英语(第4版)》课后练习参考答案
Unit Four/Section BI. Fill in the blanks with the information given in the text:1. Information engineering emphasizes a modeling tool called entityrelationship diagrams.2. One of the disadvantages of model-driven development is the long durationof projects.3. Unlike structured analysis and design and information engineering,object-oriented analysis and design attempt to emerge the data and process concerns into singular constructs called objects.4. Unlike logical models, physical models show not only what a system is ordoes , but also how the system is physically and technically implemented.II. Translate the following terms or phrases from English into Chinese and vice versa:1. check box 复选框.选择框.校验框2. structured design 结构化设计3. building block 积木块.构建模块.构件4. database schema 数据库模式5. radio button 单选(按)钮6. 系统建模技术 system modeling technique7. 模型驱动开发 model-driven development8. 数据流程图 data flow diagram9. 下拉式菜单 drop-down (或pull-down) menu10. 滚动条 scroll barUnit Five: Software ProcessUnit Five/Section AI. Fill in the blanks with the information given in the text:1. New software may be developed from scratch or through the use of existingsystems and off-the-shelf software or system components.2. The three generic process models discussed in the text are often complementaryrather than mutually exclusive, especially for large system development.3. The waterfall model is so named because of the cascade from one phase to anotherin the software development process.4. The fundamental development activities of the waterfall model arerequirements analysis and definition, system and software design, implementation and unit testing, integration and system testing, and operation and maintenance.5. The two fundamental types of evolutionary development are exploratorydevelopment and throwaway prototyping.6. The evolutionary approach is often more effective than the waterfall approachin producing systems that meet the immediate needs of customers, but it is difficult to establish a(n) stable system architecture using this approach.7. CBSE is a(n) reuse-oriented approach to software development, which relieson a large base of reusable software components and an integrating framework for these components.8. While CBSE can reduce the amount of software to be developed and the associatedcost and risks, it cannot avoid requirements compromises which may lead to a system that does not meet the real needs of users.II. Translate the following terms or phrases from English into Chinese and vice versa:1. system specification 系统规格说明2. unit testing 单位(或单元、部件)测试3. software life cycle 软件生命周期(或生存周期)4. system validation testing 系统验证测试5. evolutionary development process 演化开发过程6. linear model 线性模型7. program unit 程序单元8. throwaway prototype 抛弃式原型9. text formatting 正文格式编排.文本格式化10. system evolution 系统演变11. 系统设计范例 system design paradigm12. 需求分析与定义 requirements analysis and definition13. 探索式编程方法 exploratory programming approach14. 系统文件编制 system documentation15. 瀑布模型 waterfall model16. 系统集成 system integration17. 商用现成软件 commercial off-the-shelf (或COTS) software18. 基于组件的软件工程 component-based software engineering (CBSE)19. 软件维护工具 software maintenance tool20. 软件复用 software reuseIV. Translate the following passage from English into Chinese:Software processes are complex and, like all intellectual and creative processes, rely on people making decisions and judgments. Because of the need for judgment and creativity, attempts to automate software processes have met with limited success. Computer-aided software engineering (CASE) tools can support some process activities. However, there is no possibility, at least in the next few years, of more extensive automation where software takes over creative design from the engineers involved in the software process.One reason the effectiveness of CASE tools is limited is because of the immense diversity of software processes. There is no ideal process, and many organization have developed their own approach to software development.Processes have evolved to exploit the capabilities of the people in an organization and the specific characteristics of the systems that are being developed. For some systems, a very structured development process is required while for others a flexible, agile process is likely to be more effective.软件过程比较复杂.而且像所有其他的智能和创造性过程一样.依靠人们作出决定和判断。
计算机专业英语教程(第4版)全书译文

计算机专业英语教程(第4版)全书译文第1章:介绍计算机专业英语教程(第4版)全书是一本为计算机专业学生编写的英语教材。
本书旨在帮助学生提高英语水平,特别是在计算机领域的专业术语和技能方面。
本书是由经验丰富的专业人士编写的,其中包含了大量的案例研究和实践活动,以帮助学生更好地理解和应用所学知识。
第2章:计算机基础知识本章介绍了计算机的基础知识,包括计算机的组成部分、工作原理以及常见的计算机系统和网络。
通过学习这些内容,学生将能够了解计算机的主要组成部分以及它们之间的相互作用关系。
第3章:软件工程这一章节主要介绍了软件工程的基本概念和原则。
学生将学习软件生命周期、软件开发过程以及不同的软件工程方法和模型。
此外,本章还探讨了软件测试和质量保证的重要性。
第4章:数据库管理系统数据库管理系统是计算机专业中的重要主题。
本章介绍了数据库的基本概念和原理,包括数据库设计、数据模型和查询语言。
学生将通过学习数据库的相关内容,了解数据库在计算机领域中的应用以及其重要性。
第5章:计算机网络计算机网络是现代计算机技术中的关键领域。
本章讲解了计算机网络的基本概念、协议和技术,包括局域网、广域网和互联网。
学生将通过学习计算机网络的知识,了解网络通信的原理和实现方式,并掌握网络管理和安全方面的基本技能。
第6章:人工智能人工智能是计算机科学中的前沿领域,对计算机专业学生来说具有重要的意义。
本章介绍了人工智能的基本概念、算法和应用领域。
学生将通过学习人工智能的知识,了解智能系统的模型和设计原理,以及在现实生活中的实际应用。
第7章:计算机图形学计算机图形学是计算机专业的重要分支之一。
本章介绍了计算机图形学的基本原理和技术,包括图像处理、渲染和动画等方面。
学生将通过学习计算机图形学的知识,了解图形图像的生成和处理过程,掌握图形设计和开发的基本技能。
第8章:计算机安全计算机安全是计算机专业中的一个重要议题。
本章主要介绍了计算机安全的基本概念和技术,包括身份认证、访问控制和网络安全等方面。
《计算机英语(第4版)》课后练习参考答案课后习题答案.docx
《计算机英语(第4版)》练习参考答案Unit One: Computer and Computer ScienceUnit One/Section AI.Fill in the blanks with the information given in the text:1.Charles Babbage; Augusta Ada Byron2.input; output3.VLSI4.workstations; mainframes5.vacuum; transistors6.instructions; software7.digit; eight; byte8.microminiaturization; chipII.Translate the following terms or phrases from English into Chinese and vice versa:1.artificial intelligence 人工智能2.paper-tape reader 纸带阅读器3.optical computer 光计算机4.neural network 神经网络5.instruction set 才旨令集6.parallel processing 并行处理7.difference engine 差分机8.versatile logical element 通用逻辑元件9.silicon substrate 硅衬底10.vacuum tube 真空管11.数据的存储与处理the storage and handling of data12.超大规模集成电路very large-scale integrated circuit13.中央处理器central processing unit14.个人计算机personal computeranalogue computerdigital computergeneral-purpose computerprocessor chip19. 操作指令 operating instructions20. 输入设备 input deviceIII. Fill in each of the blanks with one of the words given in the following list, making changes ifnecessary:We can define a computer as a device that accepts input, processes data, stores data, and produces output. According to the mode of processing, computers are either analog or digital. They can also be classified as mainframes, minicomputers, workstations, or microcomputers. All else (for example, the age of the machine) being equal, this categorization provides some indication of the computer's speed, size, cost, and abilities.Ever since the advent of computers, there have been constant changes. First-generation computers of historic significance, such as UNIVAC (通用自动计算机),introduced in the early 1950s, were based on vacuum tubes. Second-generation computers, appearing in the early 1960s, were those in which transistors replaced vacuum tubes. In third-generation computers, dating from the 1960s, integrated circuits replaced transistors. In fourth-generation computers such as microcomputers 、which first appeared in the mid-1970s, large-scale integmtion enabled thousands of circuits to be incorporated on one chip. Fifth-generation computers are expected to combine very-large-scale integration with sophisticated approaches to computing, including artificial intelligence and true distributed processing.IV. Translate the following passage from English into Chinese:计算机将变得更加先进,也将变得更加容易使用。
计算机专业英语的第四版课后习题翻译

中译英参考答案Unit 1A computer system consists of hardware system and software system. The hardware of the computer is usually divided into three major parts or three primary subsystems: the CPU, the memory subsystem, and the I/O subsystem.The CPU performs many operations and controls computer. The memory subsystem is used to store program being executed by the CPU, along with the program’s data. The I/O subsystem allows the CPU to interact with input and output devices such as the keyboard and monitor of a personal computer. The components of the computer are connected to the buses.The part of the computer that performs the bulk of data processing operations is called the central processing unit and is referred to as the CPU. In microcomputer, it is often called the microprocessor. The CPU is made up of three major parts: control unit, ALU, and register set.Memory is also known as internal memory or main memory. It refers to the circuits in the computer that hold whatever programs and data are available for immediate use by the CPU.I/O subsystem includes I/O devices and interface. There are a wide variety of I/O devices, such as mouse, printer, sensor, disk, and so on. Input-output interface provides a method for transferring information between internal storage and external I/O devices. Peripherals connected to a computer need special communication links for interfacing them with the CPU. The purpose of the communication link is to resolve the differences that exist between the central computer and each peripheral.Unit 2Storage hardware provides permanent storage of information and programs for retrieval by the computer. Hard disk drives store information in magnetic particles embedded in a disk. Usually a permanent part of the computer, hard disk drives can store large amounts of information and retrieve that information very quickly.Although fixed hard drive systems offer faster access and have a higher storage capacity than optical discs, optical disc systems use removable media – a distinct benefit. Optical discs – primary CDs and DVDs – are much more widely used than removable hard drive systems. They are the standard today for software delivery, as well as commonly used for storing high-capacity music and video files. There are also versions of both CD and DVD drives available for home audio and home theater use. Optical discs are commonly referred to as compact discs.CD and DVD discs are read by CD and DVD drives. The speed of a CD or DVD drive is rated as 24x, 32x, 36x, and so on. These labels describe how fast the drive is compared to the first version of that drive. For example, a 36x drive is 36 times the speed of the baseline unit that was originally manufactured.Most optical discs have a title and other text printed only on one side and they are inserted into the drive with the printed side facing up. When inserting such a CD or DVD, be careful not to get dirt, fingerprints, scratches, or anything else that might hinder light reflectivity on the disc’s surface.Unit 3(a) A program is a list of instructions or statements for directing the computer to perform a required data processing task. Programming is a multistep process for creating that list of instructions.(b) It is important to understand the difference between a class and an object of that class. A class is simply a specification for creating objects. Thus, a single class may create multiple objects.(c) Java is an object-oriented, network-friendly high-lever programming language that allows programmers to build applications that can run on almost any operating system.(d) ActiveX is a set of controls, or reusable components that enables programs or content of almost any type to be embedded within a Web page. Whereas a Java must be downloaded each time you visit a Web site, with ActiveX the component is downloaded only once, then stored on your hard disk for later, repeated use.(e) Programming involves a great deal of creativity. The design is guide to the function or purpose of each component, but the programmer has great flexibility in implementing the design as code. No matter what language is used, each program component involves at least three major aspects: control structures, algorithms, and data structures.Unit 4The software system can be divided into two broad categories: application software and system software. Application software consists of the program for performing tasks particular to the machine’s utilization. In contrast to application software, system software comprises a large number of programs. These programs start up the computer and function as the principle coordinator of all hardware components and application software. Without system software loaded into RAM of your computer, your hardware and application software are useless.System software can be grouped into three basic parts: operating system, utility software, and language translators. The majority of an installation’s utility software consists of programs for performing activities that are fundamental to computer installations yet not included in the operating system. In a sense, utility software consists of software units that extend the capabilities of the operating system.A computer’s OS is the main collection of programs that manage its activities.The primary chores of an OS are management and control. The OS ensures that all actions requested by a user are valid and processed in an orderly fashion. It also manages the computer system’s resources to perform these operations with efficiency and consistency.Application software is the software designed to help you solve problems specific to business or perform specific business tasks. Application software then is the layer of software closest to you. Basically, there are four categories of application software: productivity software, business and specialty software, entertainment software and education/reference software.Unit 5A computer network is often classified as being either a local area network (LAN), a metropolitan area network (WAN), or a wide area network (WAN). The connection of two or more networks is called an internetwork. The worldwide Internet is a well-known example of an internetwork.LANs are privately owned networks within a single building or campus of up to a few kilometers in size. They are widely used to connect personal computers and workstations in company offices and factories to share resources and exchange information.In general, a given LAN will use only one type of transmission medium. Various topologies are possible for LANs. The most common LAN topologies are bus, ring and star.A MAN is basically a bigger version of a LAN and normally uses similar technology. MAN is designed to extend over an entire city. It may be a single network such as a cable television network, or it may be a means of connecting a number of LANs into a large network so that resources may be shared LAN-to-LAN as well as device-to-device. For example, a company can use a MAN to connect the LANs in all of its offices throughout a city.A W AN spans a large geographical area that may comprise a country, a continent, or even the world. It provides long-distance transmission of data, voice, image, and video information over large geographical area.In contrast to LANs, W ANs may utilize public leased, or private communication devices, usually in combinations, and can therefore span an unlimited number of miles.Unit 6Transmission media are used to transfer messages over a network. For instance, the transmission media used in a network may be a privately owned set of cables, the public phone lines, or a satellite system. Transmission media can either be wired or wireless.The three types of wired media most commonly used to carry messages are twisted-pair wire, coaxial cable, and fiber-optic cable. One of the most successful developments in transmission media in recent years has been fiber optics. Fiber-optic cable is commonly used for the high-speed backbone lines of a network, or for Internet infrastructure.Wireless transmission media have become especially popular in recent years. They support communications in situations in which physical wiring is impractical or inconvenient, as well as facilitate mobility. Wireless media are commonly used to connect devices to a network, to share information between computers, to connect wireless mice to a computer, and for handheld PCs, wireless phones, and other mobile devices. Radio signals transferred through the air are the heart of most types of wireless media. In addition to conventional broadcast radio application, the microwave, cellular, and satellite transmission media also use radio signals to transmit data.Radio transmissions require the use of a transmitter to send the radio signals through the air. A receiver (usually containing some type of antenna) accepts the date at the other end. When a device functions as both a receiver and transmitter, it is commonly called a transceiver or transmitter-receiver.Unit 7(a) Since many database systems users are not computer trained, developers hide the complexity from users through several levels of abstraction, to simplify user’s interactions with the system: physical level, logical level, and view level.(b) A database schema is specified by a set of definitions expressed by a special language called a data-definition language (DDL). The result of compilation of DDL statements is a set of tables that is stored in a special file called data dictionary, or data directory.(c) The structured query language (SQL) is the most widely used and standard query language for relational database management systems. It is a kind of non-procedural language.(d) An entity is a “thing” or “object” in the real world that is distinguishable from other objects. For example, each person is an entity, and bank accounts can be considered to be entities. Entities are described in a database by a set of attributes.(e) Data warehouse is one of the newest and hottest buzzwords and concepts in the IT field and the business environment. A data warehouse is a logical collection of information——gathered from many different operational databases——that supports business analysis activities and decision-making tasks.Unit 8Animation is the term used to describe a series of graphical images that are displayed one after the other to simulate movement. Cartoons on television are one example of animation.Video differs from animation in that it usually begins as a continuous stream of visual information that is broken into separate images or frames when the video is recorded. When the frames are projected—typically at a rate of 30 frames per second—the effect is a smooth reconstruction of the original continuous stream of information. As you might imagine, at 30 frames per second, the amount of data involved in displaying a video during a multimedia presentation can require a substantial amount of storage space. Consequently, video data—like audio data—is often compressed. A variety of compression standards exist. Some of the most common video file formats are .avi, .mpeg, .mov, .rm.For multimedia presentation, video may be recorded using a standard (analog) video camera and then converted to digital form as it is input into a computer. Alternatively, the film can be recording digitally using a digital video camera. Streaming video is frequently used on Web pages to reduce file size. Similar to streaming audio, Streaming video files can begin playing once a portion of the video has been downloaded.Unit 9(a) AI is currently being applied in business in the form of knowledge systems, which use human knowledge to solve problems. The most popular type of knowledge-based system is the expert system. An expert system is a computer program that attempts to represent the knowledge of human experts in the form of heuristics. The term heuristic is derived from the same Greek root as the word eureka, which means “to discover”.(b) The user interface enables the manager to enter instructions and information into the expert system and to receive information from it. The instructions specify the parameters that guide the expert system through its reasoning processing. The information is in the form of values assigned to certain variables.(c) The knowledge base contains both facts that describe the problem area and knowledge representation techniques that describe how the facts fit together in a logical manner. The term problem domain is used to describe the problem area.(d) An expert system, also called a knowledge-based system, is an artificial intelligence system that applies reasoning capabilities to reach a conclusion. Expert systems are excellent for diagnostic and prescriptive problems.(e) The DSS is not intended to replace the manager. The computer can be applied to the structured portion of the problem, but the manager is responsible for the unstructured portion——applying judgment or intuition and conducting analyses.Unit 10The linked list (see figure 1) consists of a series of nodes, which are not necessarily adjacent in memory. Each node contains the element and a link to a node containing its successor. We call this the next link. The last cell’s next link references null.To execute printList or find(x) we merely start at the first node in the list and then traverse the list by following the next links. This operation is clearly linear-time, as in the array implementation, although the constant is likely to be larger than if an array implementation were used. The findKth operation is no longer quite as efficient as an array implementation; findKth(i) takes O(i) time and works by traversing down the list in the obvious manner. In practice, this bound is pessimistic, because frequently the calls to findKth are in sorted order (by i). As an example, findKth(2), findKth(3), findKth(4), and findKth(6) can all be executed in one scan down the list.The remove method can be executed in one next reference change. Figure 2 shows the result of deleting the second element in the original list.The insert method requires obtaining a new node from the system by using a new call and then executing two reference maneuvers. The general idea is shown in figure 3. The dashed line represents the old next reference.Unit 11(a) A set is pure if all of its members are sets, all members of its members are sets, and so on. For example, the set containing only the empty set is a nonempty pure set.(b) A language is a describable set of finite strings, drawn from a fixed alphabet. A grammar is one way to "describe" the language. The grammar consists of a finite list of rules, where each rule replaces one substring with another. The string on the left must contain at least one nonterminal. The first string "produces" or "generates" the second. Thus a rule is also called a production.(c) A finite-state machine (FSM) or finite-state automaton(FA)is a mathematical abstraction sometimes used to design digital logic or computer programs. It is a behavior model composed of a finite number of states, transitions between those states, and actions, similar to a flow graph in which one can inspect the way logic runs when certain conditions are met.(d) Sometimes it is inconvenient or impossible to describe a set by listing all of its elements. Another useful way to define a set is by specifying a property that the elements of the set have in common. The notation P(x) is used to denote a sentence or statementP concerning the variable object x. The set defined by P(x) written {x | P(x)}, is just a collection of all the objects for which P is true.Unit 12(a) Because drawings are typically displayed in 3D, CAD is especially helpful in designing automobiles, aircraft, ships, buildings, electrical circuits (including computer chips), and even clothing.(b) Computer-integrated manufacturing (CIM) is the manufacturing approach of using computers to control the entire production process. This integration allows individual processes to exchange information with each other and initiate actions. Through the integration of computers, manufacturing can be faster and less error-prone, although the main advantage is the ability to create automated manufacturing processes.(c) In addition to supporting decision making, coordination, and control, information system may also help managers and workers analyze problems, visualize complex subjects, and create new products.(d) Knowing the history and evolution of ERP is essential to understanding its current application and its future developments.(e) In addition to monitoring operational activities such as tracking the status of orders and inventory levels, enterprise system also improve organization-wide reporting and decision making.Unit 13(a) There are a wide variety of educational application programs available. Educational software is designed to teach one or more skills, such as reading, math, spelling, a foreign language, world geography, or to help prepare for standardized tests.(b) Electronic business (e-business) is the use of information technology and electronic communication networks to exchange business information and conduct transactions in electronic, paperless form.(c) Word processing software allows you to use computers to create, edit, store, and print documents. You can easily insert, delete, and move words, sentences, and paragraphs——without ever using an eraser.(d) What is a spreadsheet? Spreadsheet software takes its name from the accountant’s columnar worksheet, which it imitates. A spreadsheet is a worksheet consisting of a collection of cells formed by the intersection of rows and columns. Each cell can store one piece of information: a number, word or phrase, or formula.Unit 14(a) A geographic information system (GIS) is a system that captures, stores, analyzes, manages and presents data with reference to geographic location data. In the simplest terms, GIS is the merging of cartography, statistical analysis and database technology.(b) The GPS receiver uses the messages it receives to determine the transit time of each message and computes the distance to each satellite. These distances along with the satellites' locations are used to compute the position of the receiver. This position is then displayed, perhaps with a moving map display or latitude and longitude; elevation information may be included.(c) Virtual reality (VR) is a term that applies to computer-simulated environments that can simulate physical presence in the real world. Most current virtual reality environments are primarily visual experiences, displayed either on a computer screen or through special stereoscopic displays, but some simulations include additional sensory information, such as sound through speakers or headphones.Unit 15(a) The software development process is sometimes called the software development life cycle (SDLC), because it describes the life of a software product from its conception to its implementation, delivery, use, and maintenance.(b) How can the CMM help your organization? There are three key roles the CMM plays. First, the CMM helps build an understanding of software process by describing the practices that contribute to a level of process maturity. The second role of the CMM is to provide a consistent basis for conducting appraisals of software processes. The CMM’s third key role is to serve as a blueprint for software process improvement.(c) The UML offers a standard way to write a system’s blueprints, including conceptual things such as business processes and system functions as well as concrete things such as programming language statements, database schemas, and reusable software components. The UML represents a collection of the best engineering practices that have proven successful in the modeling of large and complex systems.(d) Object modeling is a technique for identifying objects within the system environment and the relationships between those objects. The object-oriented approach to system development is based on several concepts, such as object, attribute, behavior, encapsulation, class, inheritance, polymorphism, persistence, etc.Unit 16“Security” is an all-encompassing term that describes all the concepts, techniques, and technologies to protect information from unauthorized access. There are several requirements for information security.Confidentiality: hiding data, usually with encryption, to prevent unauthorized viewing and access.Authenticity: the ability to know that the person or system you are communicating with is who or what you think it is.Access control: once a person or system has been authenticated, their ability to access data and use systems is determined by access controls.Data integrity: providing assurance that an information system or data is genuine.Availability: making sure that information is available to users in a secure way.To prevent unauthorized access, some type of identification procedure must be used. These vary from passwords to physical access object (access cards, etc.) to biometric devices that verify some type of personal characteristic, such as a fingerprint.Some of the most secure access control systems address both identification and authentication. Identification involves verifying that the person’s name or other identifying feature is listed as an authorized user; authentication refers to determining whether or not the person is actually who he or she claims to be.Unit 17A distributed system is a collection of independent computers which appear to the users of system as a single computer. Nearly all large software systems are distributed. For example, enterprise-wide business systems must support multiple users running common applications across different sites.A distributed system encompasses a variety of applications, their underlying support software, the hardware they run on, and the communication links connecting the distributed hardware. The largest and best-known distributed system is the set of computers, software, and services comprising the World Wide Web, which is so pervasive that it coexists with and connects to most other existing distributed systems. The most common distributed systems are networked client/server systems. Distributed systems share the general properties described below.●Multiple nodes●Message passing or communication●Resource sharing●Decentralized control●Concurrency or parallelism●Fault tolerance●Heterogeneity●OpennessDistributed systems have many inherent advantages, especially over centralized systems. Some applications are inherent distributed as well. In general, distributed systems:●Yield higher performance●Allow incremental growth●Allow one user to run a program on many different machines in parallel ●Provide higher reliability● .●●。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
中译英参考答案Unit 1A computer system consists of hardware system and software system. The hardware of the computer is usually divided into three major parts or three primary subsystems: the CPU, the memory subsystem, and the I/O subsystem.The CPU performs many operations and controls computer. The memory subsystem is used to store program being executed by the CPU, along with the program’s data. The I/O subsystem allows the CPU to interact with input and output devices such as the keyboard and monitor of a personal computer. The components of the computer are connected to the buses.The part of the computer that performs the bulk of data processing operations is called the central processing unit and is referred to as the CPU. In microcomputer, it is often called the microprocessor. The CPU is made up of three major parts: control unit, ALU, and register set.Memory is also known as internal memory or main memory. It refers to the circuits in the computer that hold whatever programs and data are available for immediate use by the CPU.I/O subsystem includes I/O devices and interface. There are a wide variety of I/O devices, such as mouse, printer, sensor, disk, and so on. Input-output interface provides a method for transferring information between internal storage and external I/O devices. Peripherals connected to a computer need special communication links for interfacing them with the CPU. The purpose of the communication link is to resolve the differences that exist between the central computer and each peripheral.Unit 2Storage hardware provides permanent storage of information and programs for retrieval by the computer. Hard disk drives store information in magnetic particles embedded in a disk. Usually a permanent part of the computer, hard disk drives can store large amounts of information and retrieve that information very quickly.Although fixed hard drive systems offer faster access and have a higher storage capacity than optical discs, optical disc systems use removable media – a distinct benefit. Optical discs – primary CDs and DVDs – are much more widely used than removable hard drive systems. They are the standard today for software delivery, as well as commonly used for storing high-capacity music and video files. There are also versions of both CD and DVD drives available for home audio and home theater use. Optical discs are commonly referred to as compact discs.CD and DVD discs are read by CD and DVD drives. The speed of a CD or DVD drive is rated as 24x, 32x, 36x, and so on. These labels describe how fast the drive is compared to the first version of that drive. For example, a 36x drive is 36 times the speed of the baseline unit that was originally manufactured. Most opticaldiscs have a title and other text printed only on one side and they are inserted into the drive with the printed side facing up. When inserting such a CD or DVD, be careful not to get dirt, fingerprints, scratches, or anything else that might hinder light reflectivity on the disc’s surface.Unit 3(a) A program is a list of instructions or statements for directing the computer to perform a required data processing task. Programming is a multistep process for creating that list of instructions.(b) It is important to understand the difference between a class and an object of that class. A class is simply a specification for creating objects. Thus, a single class may create multiple objects.(c) Java is an object-oriented, network-friendly high-lever programming language that allows programmers to build applications that can run on almost any operating system.(d) ActiveX is a set of controls, or reusable components that enables programs or content of almost any type to be embedded within a Web page. Whereas a Java must be downloaded each time you visit a Web site, with ActiveX the component is downloaded only once, then stored on your hard disk for later, repeated use.(e) Programming involves a great deal of creativity. The design is guide to the function or purpose of each component, but the programmer has great flexibility in implementing the design as code. No matter what language is used, each program component involves at least three major aspects: control structures, algorithms, and data structures.Unit 4The software system can be divided into two broad categories: application software and system software. Application software consists of the program for performing tasks particular to the machine’s utilization. In contrast to application software, system software comprises a large number of programs. These programs start up the computer and function as the principle coordinator of all hardware components and application software. Without system software loaded into RAM of your computer, your hardware and application software are useless.System software can be grouped into three basic parts: operating system, utility software, and language translators. The majority of an installation’s utility software consists of programs for performing activities that are fundamental to computer installations yet not included in the operating system. In a sense, utility software consists of software units that extend the capabilities of the operating system.A computer’s OS is the main collection of programs that manage its activities. The primary chores of an OS are management and control. The OS ensures that all actions requested by a user are valid and processed in an orderly fashion. It also manages the computer system’s resources to perform these operations withefficiency and consistency.Application software is the software designed to help you solve problems specific to business or perform specific business tasks. Application software then is the layer of software closest to you. Basically, there are four categories of application software: productivity software, business and specialty software, entertainment software and education/reference software.Unit 5A computer network is often classified as being either a local area network (LAN), a metropolitan area network (WAN), or a wide area network (WAN). The connection of two or more networks is called an internetwork. The worldwide Internet is a well-known example of an internetwork.LANs are privately owned networks within a single building or campus of up to a few kilometers in size. They are widely used to connect personal computers and workstations in company offices and factories to share resources and exchange information.In general, a given LAN will use only one type of transmission medium. Various topologies are possible for LANs. The most common LAN topologies are bus, ring and star.A MAN is basically a bigger version of a LAN and normally uses similar technology. MAN is designed to extend over an entire city. It may be a single network such as a cable television network, or it may be a means of connecting a number of LANs into a large network so that resources may be shared LAN-to-LAN as well as device-to-device. For example, a company can use a MAN to connect the LANs in all of its offices throughout a city.A WAN spans a large geographical area that may comprise a country, a continent, or even the world. It provides long-distance transmission of data, voice, image, and video information over large geographical area.In contrast to LANs, WANs may utilize public leased, or private communication devices, usually in combinations, and can therefore span an unlimited number of miles.Unit 6Transmission media are used to transfer messages over a network. For instance, the transmission media used in a network may be a privately owned set of cables, the public phone lines, or a satellite system. Transmission media can either be wired or wireless.The three types of wired media most commonly used to carry messages are twisted-pair wire, coaxial cable, and fiber-optic cable. One of the most successful developments in transmission media in recent years has been fiber optics. Fiber-optic cable is commonly used for the high-speed backbone lines of a network, or for Internet infrastructure.Wireless transmission media have become especially popular in recent years. They support communications in situations in which physical wiring isimpractical or inconvenient, as well as facilitate mobility. Wireless media are commonly used to connect devices to a network, to share information between computers, to connect wireless mice to a computer, and for handheld PCs, wireless phones, and other mobile devices. Radio signals transferred through the air are the heart of most types of wireless media. In addition to conventional broadcast radio application, the microwave, cellular, and satellite transmission media also use radio signals to transmit data.Radio transmissions require the use of a transmitter to send the radio signals through the air. A receiver (usually containing some type of antenna) accepts the date at the other end. When a device functions as both a receiver and transmitter, it is commonly called a transceiver or transmitter-receiver.Unit 7(a) Since many database systems users are not computer trained, developers hide the complexity from users through several levels of abstraction, to simplify user’s interactions with the system: physical level, logical level, and view level.(b) A database schema is specified by a set of definitions expressed by a special language called a data-definition language (DDL). The result of compilation of DDL statements is a set of tables that is stored in a special file called data dictionary, or data directory.(c) The structured query language (SQL) is the most widely used and standard query language for relational database management systems. It is a kind of non-procedural language.(d) An entity is a “thing” or “object” in the real world that is distinguishable from other objects. For example, each person is an entity, and bank accounts can be considered to be entities. Entities are described in a database by a set of attributes.(e) Data warehouse is one of the newest and hottest buzzwords and concepts in the IT field and the business environment. A data warehouse is a logical collection of information——gathered from many different operational databases ——that supports business analysis activities and decision-making tasks.Unit 8Animation is the term used to describe a series of graphical images that are displayed one after the other to simulate movement. Cartoons on television are one example of animation.Video differs from animation in that it usually begins as a continuous stream of visual information that is broken into separate images or frames when the video is recorded. When the frames are projected—typically at a rate of 30 frames per second—the effect is a smooth reconstruction of the original continuous stream of information. As you might imagine, at 30 frames per second, the amount of data involved in displaying a video during a multimedia presentation can require a substantial amount of storage space. Consequently, video data—like audio data—is often compressed. A variety of compression standards exist. Some of themost common video file formats are .avi, .mpeg, .mov, .rm.For multimedia presentation, video may be recorded using a standard (analog) video camera and then converted to digital form as it is input into a computer. Alternatively, the film can be recording digitally using a digital video camera. Streaming video is frequently used on Web pages to reduce file size. Similar to streaming audio, Streaming video files can begin playing once a portion of the video has been downloaded.Unit 9(a) AI is currently being applied in business in the form of knowledge systems, which use human knowledge to solve problems. The most popular type of knowledge-based system is the expert system. An expert system is a computer program that attempts to represent the knowledge of human experts in the form of heuristics. The term heuristic is derived from the same Greek root as the word eureka, which means “to discover”.(b) The user interface enables the manager to enter instructions and information into the expert system and to receive information from it. The instructions specify the parameters that guide the expert system through its reasoning processing. The information is in the form of values assigned to certain variables.(c) The knowledge base contains both facts that describe the problem area and knowledge representation techniques that describe how the facts fit together in a logical manner. The term problem domain is used to describe the problem area.(d) An expert system, also called a knowledge-based system, is an artificial intelligence system that applies reasoning capabilities to reach a conclusion. Expert systems are excellent for diagnostic and prescriptive problems.(e) The DSS is not intended to replace the manager. The computer can be applied to the structured portion of the problem, but the manager is responsible for the unstructured portion——applying judgment or intuition and conducting analyses.Unit 10The linked list (see figure 1) consists of a series of nodes, which are not necessarily adjacent in memory. Each node contains the element and a link to a node containing its successor. We call this the next link. The last cell’s next link references null.To execute printList or find(x) we merely start at the first node in the list and then traverse the list by following the next links. This operation is clearly linear-time, as in the array implementation, although the constant is likely to be larger than if an array implementation were used. The findKth operation is no longer quite as efficient as an array implementation; findKth(i) takes O(i) time and works by traversing down the list in the obvious manner. In practice, this bound is pessimistic, because frequently the calls to findKth are in sorted order (by i). Asan example, findKth(2), findKth(3), findKth(4), and findKth(6) can all be executed in one scan down the list.The remove method can be executed in one next reference change. Figure 2 shows the result of deleting the second element in the original list.The insert method requires obtaining a new node from the system by using a new call and then executing two reference maneuvers. The general idea is shown in figure 3. The dashed line represents the old next reference.figure 1figure 2figure 3Unit 11(a) A set is pure if all of its members are sets, all members of its members are sets, and so on. For example, the set containing only the empty set is a nonempty pure set.(b) A language is a describable set of finite strings, drawn from a fixed alphabet. A grammar is one way to "describe" the language. The grammar consists of a finite list of rules, where each rule replaces one substring with another.The string on the left must contain at least one nonterminal.The first string "produces" or "generates" the second.Thus a rule is also called a production.(c) A finite-state machine (FSM) or finite-state automaton(FA)is a mathematical abstraction sometimes used to design digital logic or computer programs. It is a behavior model composed of a finite number of states, transitions between those states, and actions, similar to a flow graph in which one can inspect the way logic runs when certain conditions are met.(d) Sometimes it is inconvenient or impossible to describe a set by listing all of its elements. Another useful way to define a set is by specifying a property that the elements of the set have in common. The notation P(x) is used to denote a sentence or statement P concerning the variable object x. The set defined by P(x) written {x | P(x)}, is just a collection of all the objects for which P is true.Unit 12(a) Because drawings are typically displayed in 3D, CAD is especially helpful in designing automobiles, aircraft, ships, buildings, electrical circuits (including computer chips), and even clothing.(b) Computer-integrated manufacturing (CIM) is the manufacturing approach of using computers to control the entire production process. This integration allows individual processes to exchange information with each other and initiate actions. Through the integration of computers, manufacturing can be faster and less error-prone, although the main advantage is the ability to create automated manufacturing processes.(c) In addition to supporting decision making, coordination, and control, information system may also help managers and workers analyze problems, visualize complex subjects, and create new products.(d) Knowing the history and evolution of ERP is essential to understanding its current application and its future developments.(e) In addition to monitoring operational activities such as tracking the status of orders and inventory levels, enterprise system also improve organization-wide reporting and decision making.Unit 13(a) There are a wide variety of educational application programs available. Educational software is designed to teach one or more skills, such as reading, math, spelling, a foreign language, world geography, or to help prepare for standardized tests.(b) Electronic business (e-business) is the use of information technology and electronic communication networks to exchange business information and conduct transactions in electronic, paperless form.(c) Word processing software allows you to use computers to create, edit, store, and print documents. You can easily insert, delete, and move words, sentences, and paragraphs——without ever using an eraser.(d) What is a spreadsheet? Spreadsheet software takes its name from the accountant’s columnar worksheet, which it imitates. A spreadsheet is a worksheet consisting of a collection of cells formed by the intersection of rows and columns. Each cell can store one piece of information: a number, word or phrase, or formula.Unit 14(a) A geographic information system (GIS) is a system that captures, stores, analyzes, manages and presents data with reference to geographic location data. In the simplest terms, GIS is the merging of cartography, statistical analysis and database technology.(b) The GPS receiver uses the messages it receives to determine the transit time of each message and computes the distance to each satellite. These distances along with the satellites' locations are used to compute the position of the receiver. This position is then displayed, perhaps with a moving map display or latitude and longitude; elevation information may be included.(c) Virtual reality (VR) is a term that applies to computer-simulated environments that can simulate physical presence in the real world. Most currentvirtual reality environments are primarily visual experiences, displayed either on a computer screen or through special stereoscopic displays, but some simulations include additional sensory information, such as sound through speakers or headphones.Unit 15(a) The software development process is sometimes called the software development life cycle (SDLC), because it describes the life of a software product from its conception to its implementation, delivery, use, and maintenance.(b) How can the CMM help your organization? There are three key roles the CMM plays. First, the CMM helps build an understanding of software process by describing the practices that contribute to a level of process maturity. The second role of the CMM is to provide a consistent basis for conducting appraisals of software processes. The CMM’s third key role is to serve as a blueprint for software process improvement.(c) The UML offers a standard way to write a system’s blueprints, including conceptual things such as business processes and system functions as well as concrete things such as programming language statements, database schemas, and reusable software components. The UML represents a collection of the best engineering practices that have proven successful in the modeling of large and complex systems.(d) Object modeling is a technique for identifying objects within the system environment and the relationships between those objects. The object-oriented approach to system development is based on several concepts, such as object, attribute, behavior, encapsulation, class, inheritance, polymorphism, persistence, etc.Unit 16“Security”is an all-encompassing term that describes all the concepts, techniques, and technologies to protect information from unauthorized access. There are several requirements for information security.Confidentiality: hiding data, usually with encryption, to prevent unauthorized viewing and access.Authenticity: the ability to know that the person or system you are communicating with is who or what you think it is.Access control: once a person or system has been authenticated, their ability to access data and use systems is determined by access controls.Data integrity: providing assurance that an information system or data is genuine.Availability: making sure that information is available to users in a secure way.To prevent unauthorized access, some type of identification procedure must be used. These vary from passwords to physical access object (access cards, etc.) to biometric devices that verify some type of personal characteristic, such as a fingerprint.Some of the most secure access control systems address both identification and authentication. Identification involves verifying that the person’s name or other identifying feature is listed as an authorized user; authentication refers to determining whether or not the person is actually who he or she claims to be.Unit 17A distributed system is a collection of independent computers which appear to the users of system as a single computer. Nearly all large software systems are distributed. For example, enterprise-wide business systems must support multiple users running common applications across different sites.A distributed system encompasses a variety of applications, their underlying support software, the hardware they run on, and the communication links connecting the distributed hardware. The largest and best-known distributed system is the set of computers, software, and services comprising the World Wide Web, which is so pervasive that it coexists with and connects to most other existing distributed systems. The most common distributed systems arenetworked client/server systems. Distributed systems share the general properties described below.●Multiple nodes●Message passing or communication●Resource sharing●Decentralized control●Concurrency or parallelism●Fault tolerance●Heterogeneity●OpennessDistributed systems have many inherent advantages, especially over centralized systems.Some applications are inherent distributed as well. In general, distributed systems:●Yield higher performance●Allow incremental growth●Allow one user to run a program on many different machines in parallel●Provide higher reliability。
