计算机网络英文题库(附答案)chapter
计算机网络英文题库(附答案)chapter2
计算机网络英文题库(附答案)c h a p t e r2本页仅作为文档封面,使用时可以删除This document is for reference only-rar21year.MarchChapter 2 Application Layer1. In the following four descriptions, which one is correctA In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2. In the context of a communication session between a pair of process, the process that initiates the communication is labeled as the , the process that waits to be contacted to begin the session is labeled as the .A client process, server processB sending process, receiving processC input process, output processD communicating process, connecting process3. A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant applicationA E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive applicationA E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’t guarantee .A delivery of all data without errorB delivery of all data in the proper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDPA E-mailB web applicationC file transferD DNS8. In the following descriptions about HTTP, which one is not correctA HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9. Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining, the total response timeis .A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is .A 200B 301C 400D 5051~5 CACDC 6~10 CDABD11. The port number of web application is .A 25B 20C 80D 5312. A network entity that satisfies HTTP requests on the behalf of an origin web server is .A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correctA The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCP connections to transfer a file, there are .A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correctA FTP is p2p architecture.B FTP sends its control information out-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16. In the commands of FTP, which one does not have parameterA USERB PASSC LISTD STOR17. The Internet mail system has three components which they are .A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means .A Request succeeded.B The requested document doesn’t exit on this server.C This is a generic error code indicating that the request could not be understood by the server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is .A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message’s objects into one message, and SMTP sends every object one by one.D HTTP requires each message to be in 7-bit ASCII format, and SMTP doesn’t impose this restriction.20. The headers in the MIME message must include except .A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB 16~20 DDBBD21. In the following protocol, which one is statelessA POP3B SMTPC FTPD IMAP22. DNS means .A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except .A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except .A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25. There are three architectures for locating content in P2P file sharing, KaZaA uses .A Centralized Directory (Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity (p141)D Incentive Priorities26. There are three architectures for locating content in P2P file sharing, Napster uses .A Centralized Directory (p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27. The following architectures in P2P file sharing, which is an overlay networkA Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server and then back to the client is .A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29. Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not usedA HTTPB SMTPC POP3D IMAP30. In the four following options, which protocol is included in Mail Access ProtocolA SMTPB DHCPC IMAPD FTP31. In FTP commands, is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIME Content-Type is .A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33. In the four following options, which application is organized as hybrid of C/S and P2P architectureA E-mailB OICQC File transferD Web application34. In the four following options, which is not a centralized DNS design’s problemA a single point of failureB traffic volumeC distant centralized databaseD slow (maintenance)35.In t he following options, from the application developer’s perspective, which is not correctA the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not includedA the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37. In the following options about C/S architecture, which is not correctA In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38. are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its .A socketB programC clientD peer40. Which one is not defined by an application-layer protocolA the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are .A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42. takes for a small packet to travel from client to server and then back to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses .A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields, there are .A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection is close, it specifies .A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sending the requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means .A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47. is a network entity that satisfies HTTP requests on the behalf of an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correctA A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the header line.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If –Referenced-Since50. FTP uses two parallel connections to transfer a file, they are .A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51. In FTP commands, which one is used to ask the server to send back a list of all files in the current remote directoryA USERB PASSC LISTD RETR52. In the Internet mail system, allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are .A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to .A transfer mail from the recipient’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are .A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNSA Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are .A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58. In the following four options about POP3, which one is not correctA The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to create remote folders and assign messages to folders.59. A resource record in DNS distributed database is a four-tuple, which field can be ignored(p132) A Name B Value C Type D TTL 60. In the following four options about DNSresource record, which one is correctA The meaning of Name and Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A, then Name is a domain and Value is the IP address for the hostname.D If Type=MX, then Name is domain and Value is the IP address for the hostname.61. In the following four options about DNS messages, which one is not correctA There are only two kinds of DNS message.(p133)B Both query and reply message have the same format.C The header section in DNS message has 12 bytes.D The authority section contains the resource records for the same that was originally queri ed.62. In DNS message, contains information about the query that is being made.(p133)A authority sectionB question sectionC answer sectionD additional section63. There are three techniques are employed in most any P2P file-sharing systems, which one is not include (p144)A Request queuingB incentive prioritiesC parallel downloadingD Response queuing64. In the following four options about P2P file-sharing, which one is not correctA P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software, documents and images.65. In MIME header lines, specifies the name of the SMTP server that sent the message (f rom),the name of the SMTP server that received the message (by), and the time an which the rec eiving server received the message.A ReceivedB FromC ToD MIME-Version66. If the header line Connection is close, it means that the client wants .A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method, but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri. 08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be .A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00 GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options, which one is not the part of cookie technologyA Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user’s end system and managed by the user’s browser.C A network entity that satisfies HTTP requests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP, can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to .A programsB threadsC socketsD channels72. In the following four options about network architecture, which one is not correctA The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized over special server.73. In Client-Server architecture, the clients visit the server’s through .A client’s socketB client’s IP addressC server’s socketD server’s IP address74. can be thought of as a program that is running within end system.A processB threadC socketD context75. API means .A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76. One host can be running many network applications, so the system assigns them differentto distinguish each other.A IP addressB port numberC hostnameD section77. In the following four applications, which one is both bandwith-sensitive and require tight timing constraintsA real-time audioB file transferC E-mailD Web documents78. The port number of the Web server is .A 25B 20C 80D 808079. The port number of the mail server is .A 25B 20C 80D 808080. Look the URL the object’s path name is .A B /rjxy/ D81. Each URL has components, they are .A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Suppose the URL of the page is /somedir/. The client does not want to use persistent connections and want to receive French version of the object. The user agent is Windows NT . Give the request message according to the given format.2. Telnet into a Web server and send a multiline request message. Include in the request message the If-modified-since: header line to force a response message with the 304 Not Modified status code.Solution:Request line:Header lines:3. Suppose within you Web browser you click on a link to obtain a Web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1,…,RTT n. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like。
强烈推荐计算机网络英文试题库(附答案)chapter.doc
Chapter 2 Application Layer1. In the following four descriptions, which one is correct?A In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2. In the context of a communication session between a pair of process, the process that initiates the communication is labeled as the , the process that waits to be contacted to begin the session is labeled as the .A client process, server processB sending process, receiving processC input process, output processD communicating process, connecting process3. A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant application?A E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive application?A E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’t guarantee .A delivery of all data without errorB delivery of all data in the proper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS8. In the following descriptions about HTTP, which one is not correct?A HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9. Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining, the total response time is .A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is .A 200B 301C 400D 5051~5CACDC6~10CDABD11. The port number of web application is .A 25B 20C 80D 5312. A network entity that satisfies HTTP requests on the behalf of an origin web server is .A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCP connections to transfer a file, there are .A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correct?A FTP is p2p architecture.B FTP sends its control information out-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16.In the commands of FTP,which one does not have parameter?A USERB PASSC LISTD STOR17. The Internet mail system has three components which they are .A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means .A Request succeeded.B The requested document doesn’t exit on this server.C This is a generic error code indicating that the request could not be understood bythe server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is .A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message’s objects into one message, and SMTP sends every object one by one.D HTTP requires each message to be in 7-bit ASCII format, and SMTP doesn’t impose this restriction.20. The headers in the MIME message must include except .A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB16~20DDBBD21. In the following protocol, which one is stateless?A POP3B SMTPC FTPD IMAP22. DNS means .A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except .A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except .A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25.There are three architectures for locating content in P2P file sharing,KaZaA uses.A Centralized Directory(Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity(p141)D Incentive Priorities26.There are three architectures for locating content in P2P file sharing,Napster uses.A Centralized Directory(p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27.The following architectures in P2P file sharing,which is an overlay network?A Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server and then back to the client is .A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29. Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not used?A HTTPB SMTPC POP3D IMAP30. In the four following options, which protocol is included in Mail Access Protocol?A SMTPB DHCPC IMAPD FTP31. In FTP commands, is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIME Content-Type is .A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33. In the four following options, which application is organized as hybrid of C/S and P2P architecture?A E-mailB OICQC File transferD Web application34.In the four following options,which is not a centralized DNS design’s problem?A a single point of failureB traffic volumeC distant centralized databaseD slow(maintenance)35.In the following options, from the application developer’s perspective, which is not correct?A the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not included?A the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37. In the following options about C/S architecture, which is not correct?A In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38.are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its .A socketB programC clientD peer40. Which one is not defined by an application-layer protocol?A the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are .A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42. takes for a small packet to travel from client to server and then back to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses .A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields, there are .A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection is close, it specifies .A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sending the requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means .A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47. is a network entity that satisfies HTTP requests on the behalf of an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correct?A A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the header line.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If –Referenced-Since50. FTP uses two parallel connections to transfer a file, they are .A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51. In FTP commands, which one is used to ask the server to send back a list of all files in the current remote directory?A USERB PASSC LISTD RETR52. In the Internet mail system, allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are .A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to .A transfer mail from the recipient’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are .A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNS?A Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are .A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58. In the following four options about POP3, which one is not correct?A The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to create remote folders and assign messages to folders.59.A resource record in DNS distributed database is a four-tuple,which field can be ign ored?(p132)A Name B Value C Type D TTL60.In the following four options about DNSresource record,which one is correct?A The meaning of Name and Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A,then Name is a domain and Value is the IP address for the hostname.D If Type=MX,then Name is domain and Value is the IP address for the hostname.61.In the following four options about DNS messages,which one is not correct?A There are only two kinds of DNS message.(p133)B Both query and reply message have the same format.C The header section in DNS message has12bytes.D The authority section contains the resource records for the same that was originally q ueried.62.In DNS message,contains information about the query that is being made.(p133)A authority sectionB question sectionC answer sectionD additional section63.There are three techniques are employed in most any P2P file-sharing systems,which one is not include?(p144)A Request queuingB incentive prioritiesC parallel downloadingD Response queui ng64. In the following four options about P2P file-sharing, which one is not correct?A P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software, documents and images.65.In MIME header lines,specifies the name of the SMTP server that sent the messag e(from),the name of the SMTP server that received the message(by),and the time an which the receiving server received the message.A ReceivedB FromC ToD MIME-Version66. If the header line Connection is close, it means that the client wants .A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method, but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri. 08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be .A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00 GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options, which one is not the part of cookie technology?A Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user’s end system and managed by the user’s browser.C A network entity that satisfies HTTP requests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP, can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to .A programsB threadsC socketsD channels72. In the following four options about network architecture, which one is not correct?A The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized over special server.73. In Client-Server architecture, the clients visit the server’s through .A client’s socketB client’s IP addressC server’s socketD server’s IP address74. can be thought of as a program that is running within end system.A processB threadC socketD context75. API means .A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76. One host can be running many network applications, so the system assigns them differentto distinguish each other.A IP addressB port numberC hostnameD section77. In the following four applications, which one is both bandwith-sensitive and require tight timing constraints?A real-time audioB file transferC E-mailD Web documents78. The port number of the Web server is .A 25B 20C 80D 808079. The port number of the mail server is .A 25B 20C 80D 808080. Look the URL /rjxy/index.html, the object’s path name is .A B /rjxyC /rjxy/index.htmlD index.html81. Each URL has components, they are .A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Suppose the URL of the page is /somedepartment /somedir/exp.html. The client does not want to use persistent connections and want to receive French version of the object. The user agent is Windows NT 5.1. Give the request message according to the given format.Request line:Header lines:2. Telnet into a Web server and send a multiline request message. Include in the request message the If-modified-since: header line to force a response message with the 304 Not Modified status code.Solution:Request line:Header lines:3. Suppose within you Web browser you click on a link to obtain a Web page. The IPaddress for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1,…,RTT n. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object?5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like?。
计算机网络英文题库附答案chapter5
Chapter 5 The Link Layer and Local Area Network1.A ( ) protocol is used to move a datagram over an individual link.A application-layerB transport-layerC network-layerD link-layer2.The units of data exchanged by a link-layer protocol are called ( ).A datagramsB framesC segmentsD messages3.Which of the following protocols is not a link-layer protocol? ( )A EthernetB PPPC HDLCD IP4.In the following four descriptions, which one is not correct? ( )A link-layer protocol has the node-to-node job of moving network-layer datagrams over a single link in the path.B The services provided by the link-layer protocols may be different.C A datagram must be handled by the same link-layer protocols on the different links in the path.D The actions taken by a link-layer protocol when sending and receiving frames include error detection, flow control and random access.5.Which of the following services can not offered by a link-layer protocol? ( )A congestion controlB Link AccessC Error controlD Framing6.( ) protocol serves to coordinate the frame transmissions of the many nodes when multiple nodes share a single broadcast link.A ARPB MACC ICMPD DNS7.In the following four descriptions about the adapter, which one is not correct? ( )A The adapter is also called as NIC.B The adapter is a semi-autonomous unit.C The main components of an adapter are bus interface and the link interface.D The adapter can provide all the link-layer services.8.Consider CRC error checking approach, the four bit generator G is 1011, and suppose that the data D is 10101010, then the value of R is().A 010B 100C 011D 1109.In the following four descriptions about random access protocol, which one is not correct? ( )A In slotted ALOHA, nodes can transmit at random time.B In pure ALOHA, if a frame experiences a collision, the node will immediately retransmit it with probability p.C The maximum efficiency of a slotted ALOHA is higher than a pure ALOHA.D In CSMA/CD, one node listens to the channel before transmitting.10.In the following descriptions about MAC address, which one is not correct? ( )A The MAC address is the address of one node ' s adapter.B No two adapters have the same MAC address.C The MAC address doesn ' t change no matter where the adapter goes.D MAC address has a hierarchical structure.11.The ARP protocol can translate ( ) into ( ). ( )A host name, IP addressB host name, MAC addressC IP address, MAC addressD broadcast address, IP address12.The value of Preamble field in Ethernet frame structure is ( )A 10101010 10101010 ……10101010 11111111B 10101011 10101011 ……10101011 10101011C 10101010 10101010 …… 10101010 10101011D 10101010 10101010 …… 10101010 1010101013.There are four steps in DHCP, the DHCP server can complete ().A DHCP server discoveryB DHCP server offersC DHCP requestD DHCP response14.In CSMA/CD, the adapter waits some time and then returns to sensing the channel.In the following four times, which one is impossible? ( )A 0 bit timesB 512 bit timesC 1024 bit timesD 1028 bit times1 5.The most common Ethernet technologies are 10BaseT and 100BaseT. “10”and “ 100” indic(ate).A the maximum length between two adaptersB the minimum length between two adaptersC the transmission rate of the channelD the transmission rate of the node16.The principal components of PPP include but not( ).A framingB physical-control protocolD network-layer protocol17.In the following four options, which service can not be provided by switch? ( ) A filteringB self-learningC forwardingD optimal routing18.In the following four services, which one was be required in PPP? ( )A packet framingB error detectionC error correctionD multiple types of link19.The ability to determine the interfaces to which a frame should be directed, and then directing the frame to those interfaces is( ).A filteringB forwardingC self-learningD optimal routing20.In ( ) transmission(s), the nodes at both ends of a link may transmit packets at the same time.A full-duplexB half-duplexC single-duplexD both full-duplex and half-duplex21.Consider the data D is 01110010001, if use even parity checking approach, the parity bitis(①),if use odd parity check ing approach, the parity bit is(②).() A ①0 ②1B ①0 ②0C ①1 ②1D ①1 ②022.In the following four descriptions about parity checks, which one is correct? ( ) A Single-bit parity can detect all errors.B Single-bit parity can correct one errors.C Two-dimensional parity not only can detect a single bit error, but also can correct that error.D Two-dimensional parity not only can detect any combination of two errors, but also can correct them.23.MAC address is ( ) bits long.A 32B 48C 128D 6424.Wireless LAN using protocol ( ).A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.1125.The following protocols are belonging to multiple accessprotocols except for ( ).A channel partitioning protocolsC random access protocolsD taking-turns protocols26.Which of the following is not belonging to channel partitioning protocols? ( )A CSMAB FDMC CDMAD TDM27.In the following four descriptions about CSMA/CD, which one is not correct?( )A A node listens to the channel before transmitting.B If someone else begins talking at the same time, stop talking.C A transmitting node listens to the channel while it is transmitting.D With CSMA/CD, the collisions can be avoided completely.28.( ) provides a mechanism for nodes to translate IP addressesto link-layer address.A IPB ARPC RARPD DNS29.A MAC address is a ( )address.A physical-layerB application-layerC link-layerD network-layer30.Which of the following is correct? ( )A No two adapters have the same MAC address.B MAC broadcast address is FF-FF-FF-FF-FF-FF.C A portable computer with an Ethernet card always has the same MAC address, no matter where the computer goes.D All of the above31.In the following four descriptions, which one is not correct? ( )A ARP resolves an IP address to a MAC address.B DNS resolves hostnames to IP addresses.C DNS resolves hostnames for hosts anywhere in the Internet.D ARP resolves IP addresses for nodes anywhere in the Internet.32.In the LAN, ( )protocol dynamically assign IP addresses to hosts. A DNSB ARPC DHCPD IP33.DHCP protocol is a four-step process①DHCP request.② DHCP ACK.③DHCP server discovery.® DHCP server offer(s). The correct seque nee is ()A ①②③④B ③②①④C ③④①②D ①④③②34.In the Ethernet frame structure, the CRC field is ( )bytes.A 2B4C 8D 3235.In the Ethernet frame structure, the Data field carries the ( ).A IP datagramB segmentC frameD message36.In the following four descriptions, which one is not correct? ( )A Ethernet uses baseband transmission.B All of the Ethernet technologies provide connection-oriented reliable service to the network layer.C The Ethernet 10Base2 technology uses a thin coaxial cable for the bus.D The Ethernet 10BaseT technology uses a star topology.37.Ethernet 's multiple access protoc(ol is).A CDMAB CSMA/CDC slotted ALOHAD token-passing protocol38.In the following four descriptions about CSMA/CD, which one is not correct? ( )A An adapter may begin to transmit at any time.B An adapter never transmits a frame when it sensesthat some other adapter is transmitting.C A transmitting adapter aborts its transmission as soon as it detects that another adapter is also transmitting.D An adapter retransmits when it detects a collision.39.Which of the following descriptions about CSMA/CD is correct? ( )A No slots are used.B It uses carrier sensing.C It uses collision detection.D All of the above.40.The Ethernet 10BaseT technology uses( )as its physical media.A fiber opticsB twisted-pair copper wireC coaxial cableD satellite radio channel41.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( )meters.A 100B 200C 500D 1042.A ( )is a physical-layer device that acts on individual bits rather than on frames. A switchC routerD gateway43.A hub is a ( )device that acts on individual bits rather than on frames. A physical-layerB link-layerC network-layerD ransport-layer44.A switch is a( )device that acts on frame.A physical-layerB link-layerC network-layerD transport-layer45.In the following four descriptions, which one is not correct? ( )A Switches can interconnect different LAN technologies.B Hubs can interconnect different LAN technologies.C There is no limit to how large a LAN can be when switches are used to interconnect LAN segments.D There is restriction on the maximum allowable number of nodes in a collision domain when hubs are used to interconnect LAN segments.46.The ability to determine whether a frame should be forwarded to some interface or should just be dropped is ( ).A filteringB forwardingC self-learningD optimal routing47.Which of the following devices is not a plug and play device? ( )A hubB routerC switchD repeater48.Which of the following devices is not cut-through device? ( )A hubB routerC switchD repeater49.In the following four descriptions, which one is not correct? ( )A Switches do not offer any protection against broadcast storms.B Routers provide firewall protection against layer-2 broadcast storms.C Both switches and routers are plug and play devices.D A router is a layer-3 packet switch, a switch is a layer-2 packet switch.50.Which device has the same collision domain? ( )A HubB SwitchC Router51.IEEE802.2 protocol belong to ( )layerA networkB MACC LLCD physical52.IEEE802.11 protocol defines ( )rules.A Ethernet BusB wireless WANC wireless LAND Token Bus53.In data link-layer, which protocol is used to share bandwidth? ( )A SMTPB ICMPC ARPD CSMA/CD54.When two or more nodes on the LAN segments transmit at the same time, there will be a collision and all of the transmitting nodes well enter exponential back-off, that is all of the LAN segments belong to the same( ).A collision domainB switchC bridgeD hub55.( )allows different nodes to transmit simultaneously and yet have their respective receivers correctly receive a sender ' s encoded data bits.A CDMAB CSMAC CSMA/CDD CSMA/CA56 .Because there are both network-layer addresses (for example, Internet IP addresses)and link-layer addresses(that is, LAN addresses),there is a need to translate between them. For the Internet, this is the job of ( ).A RIPB OSPFC ARPD IP57.PPP defines a special control escape byte,( ). If the flag sequence, 01111110 appears anywhere in the frame, except in the flag field, PPP precedes that instance of the flag pattern with the control escape byte.A 01111110B 01111101C 10011001D 1011111058.The device ( ) can isolate collision domains for each of the LAN segment.B switchC hubD NIC59.In the following four descriptions about PPP, which one is not correct? ( )A PPP is required to detect and correct errors.B PPP is not required to deliver frames to the link receiver in the same order in which they were sent by the link sender.C PPP need only operate over links that have a single sender and a single receiver.D PPP is not required to provide flow control.60.In the PPP data frame, the( ) field tells the PPP receivers the upper-layer protocol to which the received encapsulated data belongs.A flagB controlC protocolD checksum61.PPP' s lin-kcontrol protocols (LCP) accomplish ( ).A initializing the PPP linkB maintaining the PPP linkC taking down the PPP linkD all of the above62.The PPP link always begins in the ( ) state and ends in the ( ) state. ( )A open, terminatingB open, deadC dead, deadD dead, terminating63.For( ) links that have a single sender at one end of the link and a single receiver at the other end of the link.A point-to-pointB broadcastC multicastD all of the above64.With ( )transmission, the nodes at both ends of a link may transmit packets at the same time.A half-duplexB full-duplexC simplex( 单工)D synchronous65.With ( ) transmission, a node can not both transmit and receive at the same time. A half-duplexB full-duplexC simplex( 单工)D synchronous66.Which of the following functions can 't be implemented i(n th) e NIC?A encapsulation and decapsulationB error detectionC multiple access protocolD routing67.Which of the following four descriptions is wrong? ( )A The bus interface of an adapter is responsible for communication with the adapter ' s parent node.B The link interface of an adapter is responsible for implementing the link-layer protocol.C The bus interface may provide error detection, random access functions.D The main components of an adapter are the bus interface and the link interface.68.For odd parity schemes, which of the following is correct? ( )A 011010001B 111000110C 110101110D 00011011069.( )divides time into time frames and further divides each time frame into N time slots.A FDMB TMDC CDMAD CSMA70.With CDMA, each node is assigned a different ( )A codeB time slotC frequencyD link71.Which of the following four descriptions about random accessprotocol is not correct? ( )A A transmission node transmits at the full rate of the channelB When a collision happens, each node involved in the collision retransmits at once.C Both slotted ALOHA and CSMA/CD are random access protocols.D With random access protocol, there may be empty slots.72 .PPP defines a special control escape byte 01111101. If the data is b1b201111110b3b4b5, the value is( )after byte stuffing.A b1b20111110101111110b3b4b5B b1b20111111001111101b3b4b5C b5b4b30111111001111101b2b1D b5b4b30111110101111110b2b173.MAC address is in ( ) of the computer.A RAMB NICC hard diskD cache74.Which of the following is wrong? ( )A ARP table is configured by a system administratorB ARP table is built automaticallyC ARP table is dynamicD ARP table maps IP addresses to MAC addresses75.NIC works in ( )layer.A physicalB linkC networkD transport76.In LAN, if UTP is used, the common connector is( ).A AUIB BNCC RJ-45D NNI77.The modem' s function(s) is(are() ).A translates digital signal into analog signalB translates analog signal into digital signalC both translates analog signal into digital signal and translates digital signal into analog signalD translates one kind of digital signal into another digital signal78.( )defines Token-Ring protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.279.( )defines Token-Bus protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.280.( ) defines CSMA/CD protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.281.The computer network that concentrated in a geographical area, such as in a building or on a university campus, is ( )A a LANB a MANC a WAND the Internet82.The MAC address is ( ) bits long.A 32B 48C 128D 25683.Which of the following four descriptions about MAC addresses is wrong? ( )A a MAC address is burned into the adapter ' s ROMB No two adapters have the same addressC An adapter ' s MAC address is dynamicD A MAC address is a link-layer address84.Which of the following four descriptions about DHCP is correct? ( )A DHCP is C/S architectureB DHCP uses TCP as its underlying transport protocolC The IP address offered by a DHCP server is valid foreverD The DHCP server will offer the same IP address to a host when the host requests an IP address 85.The ( )field permits Ethernet to multiplex network-layer protocols.A preambleB typeC CRCD destination MAC address86.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( ) meters.A 50B 100C 200D 50087.An entry in the switch table contains the following information excepts for ( )A the MAC address of a nodeB the switch interface that leads towards the nodeC the time at which the entry for the node was placed in the tableD the IP address of a nodeA nswers:1 〜5DBDCA 6 〜10BDAAD 11 〜15 CCBDD 16-20 BDCBA 21-25 DCBDB26-30ADBCD 31 〜35DCCBA 3670 BBDDB 41-45 ABABB 46-50 ABBCA51 〜55CCDAA 56-60CBBAC 61 "5 DCABA 66-70 DCBBA 71-75 BAB AB76-80 CCCBA 81~g5ABCBB86-87BD88. Consider the 4-bit generator , G is 1001, and suppose that D has the value 101110000. What is the value of R?1010 1001 110 0001100 1010 1001OilR 89. Consider the following graph of the network. Suppose Host A will send a datagram to Host B, HostA run OICQ on port 4000, HostB run OICQ on port 8000.All of ARP tables are up to date. Enu merate all the steps whe n message“ Hellosent from host A to host B. Host A192.168.0.2/24 1111-2222-AAAA1010110111 0(0 0 01001~ 1HostB192.169.1.2/241111-2222-BBBB Router RSwitch S1192.168.0.3/245555-6666^7777E1192.166.1.3/245555-6666^8888Switch S289.host A application-layer Hellohost A transport-layer: 4000 8000 Hellohost A met work-1 aver 192.168.0.2 192.168.1.2J4000 8000 Hellohost A link-layer: 5555-6666-7777 1111-22 22-AAAA 192.16802 192.168 4000 5000 Hello FCS(CRC)router R El: 1111-2222-BBBB 5 5 55-6666-88 88 192.168.0.2 192.168.1.2 4000 8000 Hello FCS(CRC)host B network-layer 192.168.0.2 1 92.168.1.2 4000 8000 HellohostB transport-layer 4000 8000 Hellohost B application-lay er Hello。
计算机网络英文试题库(附答案)chapter

.Chapter 2 Application Layer1. In the following four descriptions, which one is correct?A In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2.In the context of a communication session between a pair of process, theprocess that initiates the communication is labeled as the,the process that waits to be contacted to begin the session is labeled as the.A client process, server processB sending process, receivingprocessC input process,output processD communicating process, connecting process3.A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant application?A E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive application?.A E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’tguarantee.A delivery of all data without errorB delivery of all data in theproper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS8.In the following descriptions about HTTP, which one is not correct?A HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9.Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining,the total response time is.A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is.A 200B 301C 400D 5051~5 CACDC6~10 CDABD11. The port number of web application is.A25B20C80D5312. A network entity that satisfies HTTP requests on the behalf of an originweb server is.A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCPconnections to transfer a file, there are.A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correct?A FTP is p2p architecture.B FTP sends its control informationout-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16. In the commandsof FTP, which one does not have parameter?A USERB PASSC LISTD STOR17. The Internet mail system has three components which they are.A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means.A Request succeeded.B The requested document doesn’texit on this server.C This is a generic error code indicating that the request could not be understood by the server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is.A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message ’s objects into one message, and SMTP sendsevery object one by one.D HTTP requires each messageto be in 7-bit ASCII format,and SMTPdoesn’t impose this restriction.20. The headers in the MIME message must include except.A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB16~20 DDBBD21. In the following protocol, which one is stateless?A POP3B SMTPC FTPD IMAP22. DNS means.A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except.A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except.A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25. There are three architectures for locating content in P2Pfile sharing,KaZaA uses.A Centralized Directory(Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity (p141)D Incentive Priorities26. There are three architectures for locating content in P2Pfile sharing, Napst er uses.A Centralized Directory (p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27. The following architectures in P2Pfile sharing, which is an overlay network?A Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server andthen back to the client is.A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29.Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not used?A HTTPB SMTPC POP3D IMAP30.In the four following options, which protocol is included in Mail Access Protocol?A SMTPB DHCPC IMAPD FTP31. In FTP commands,is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIMEContent-Type is.A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33.In the four following options, which application is organized as hybrid ofC/S and P2P architecture?A E-mailB OICQC File transferD Web application34. In the four following options, which is not a centralized DNSdesign ’s problem ?A a single point of failureB traffic volumeC distant centralized databaseD slow(maintenance)35. In the following options, from the application developer’s perspective, which is not correct?A the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not included?A the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37.In the following options about C/S architecture, which is not correct?A In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38.are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its.A socketB programC clientD peer40.Which one is not defined by an application-layer protocol?A the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are.A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42.takes for a small packet to travel from client to server and thenback to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses.A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields,there are.A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection isclose, it specifies.A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sendingthe requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means.A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47.is a network entity that satisfies HTTP requests on the behalfof an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correct?A A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the headerline.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If–Referenced-Since50. FTP uses two parallel connections to transfer a file, they are.A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51.In FTP commands, which one is used to ask the server to send back alist of all files in the current remote directory?A USERB PASSC LISTD RETR52. In the Internet mail system,allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are.A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to.A transfer mail from the recipient ’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are.A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNS?A Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are.A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58.In the following four options about POP3, which one is not correct?A The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to createremote folders and assign messages to folders.59. A resource record in DNSdistributed database is a four-tuple,which field ca n be ignored?(p132) A Name B Value C Type D TTL60. In the following four options about DNSresource record, which one is correct?A The meaning of Nameand Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A, then Nameis a domain and Value is the IP address for the hostname.D If Type=MX,then Nameis domain and Value is the IP address for the hostname.61.In the following four options about DNSmessages, which one is not correct?A There are only two kinds of DNSmessage.(p133)B Both query and reply messagehave the sameformat.C The header section in DNSmessagehas 12 bytes.D The authority section contains the resource records for the samethat wasorigi nally queried.62.In DNSmessage,contains information about the query that is being made.(p 133)A authority sectionB question sectionC answer sectionD additional sec tion63.There are three techniques are employed in most any P2Pfile-sharing systems, which one is not include?(p144)A Request queuingB incentive prioritiesC parallel downloadingD Responseq ueuing64. In the following four options about P2P file-sharing, which one isnot correct?A P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software,documents and images.65.In MIMEheader lines,specifies the nameof the SMTPserver that sent the m essage (from),the nameof the SMTPserver that received the message(by), and the time an which t he receiving server received the message.A ReceivedB FromC ToD MIME-Version66.If the header line Connection is close, it means that the client wants.A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method,but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri.08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be.A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options,which one is not the part of cookie technology?A Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user ’s end system and managedby the user ’s browser.C A network entity that satisfies HTTPrequests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP,can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to.A programsB threadsC socketsD channels72.In the following four options about network architecture, which one isnot correct?A The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized overspecial server.73. In Client-Server architecture,the clients visit the server ’s through.A client’s socketB client’s IP addressC server’s socketD server’s IP address74.can be thought of as a program that is running within end system.A processB threadC socketD context75. API means.A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76.One host can be running many network applications, so the system assignsthem differentto distinguish each other.A IP addressB port numberC hostnameD section77.In the following four applications, which one is both bandwith-sensitive and require tight timing constraints?A real-time audioB file transferC E-mailD Webdocuments78.The port number of the Web server is.A 25B 20C 80D 808079.The port number of the mail server is.A 25B 20C 80D 808080.Look the URL/rjxy/index.html,the object ’s path nameis.A B /rjxyC /rjxy/index.htmlD index.html81. Each URL has components, they are.A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Supposethe URLof the page is /somedepartment /somedir/exp.html. The client does not want to use persistent connections and want to receive Frenchversion of the object. The user agent is WindowsNT 5.1. Give the request message according to the given format.Request line:Header lines:.2.Telnet into a Web server and send a multiline request message. Includein the request message the If-modified-since: header line to force aresponse message with the 304 Not Modified status code.Solution:Request line:Header lines:3.Suppose within you Web browser you click on a link to obtain a Web page. The.look-up is necessary to obtain the IP address. Suppose that n DNS servers arevisited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT, ⋯, RTT. Further suppose that the Webpage associated with1nthe link contains exactly one object,consisting of a small HTML text.Let RTT0 denote the RTT between the local host and the server containing the object.Assuming zero transmission time of the object, how much time elapses from whenthe client clicks on the link until the client receives the object?5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like?。
计算机网络英文题库附答案chater
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computernetwork, that is, a network that interconnectsmillionsofcomputing devices throughout theworld. ppt3 A public InternetB IntranetC switch netD television net2.Which kind of media is not a guidedmedia ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following optionbelongs to the circuit-switchednetworks ( )A FDMB TDMC VCnetworksD both A and B 6.( )makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch mustreceive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagramnetworksandvirtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination.D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packetstoward their destination.9.In the following options, which one is not a guided media ( )A twisted-pairwireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet ’s headerB wait to transmit the packet onto the linkC determine where to direct thepacketD check bit-error in the packet 11.In the following four descriptions, which one is correct ( )A The traffic intensity must begreater than 1.B The fraction of lost packetsincreases as the trafficintensity decreases.C If the traffic intensity isclose to zero, the averagequeuing delay will be close tozero.D If the traffic intensity isclose to one, the averagequeuing delay will be close toone.12.The Internet’s network layer is responsible for movingnetwork-layer packets known as( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layersare called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes ofpacket-switched networks: ( )networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be looselyclassified into threecategories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue,R is the transmission rate, and all packets consist of L bits, then thetraffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR /aB La /RC Ra /LD LR /a 17.A 2B 1C 0D -118.In the Internet, the equivalentconcept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics 20.End systems access to the Internet through its ( ). A modemsB protocolsC ISPD sockets21.End systems, packet switches,and other pieces of the Internet, run ( ) that control thesending and receiving ofinformation within theInternet.A programsB processesC applicationsD protocols22.There are many private networks,such as many corporate andgovernment networks, whosehosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) runningon its end systems to exchangedata with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and ()service.A flowcontrolB connection-oriented reliableC congestion controlD TCP25.It defines the format and theorder of messages exchangedbetween two or morecommunicating entities, as wellas the actions taken on thetransmission and/or receipt ofa message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messagesexchanged between two or morecommunicating entitiesB the order of messagesexchanged between two or morecommunicating entitiesC the actions taken on thetransmission of a message orother eventD the transmission signals aredigital signals or analogsignals27.In the following options, which is defined in protocol ( )A the actions taken on thetransmission and/or receiptof a message or other event B the objects exchanged between communicating entities C the content in the exchangedmessagesD the location of the hosts28.In the following options, whichdoes not belong to the network edge( )A end systemsB routersC clientsD servers29.In the following options, whichbelongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, whichis not the bundled with theInternet’sconnection-oriented service( )A reliable data transferB guarantee of thetransmission timeC flow controlD congestion-control31.An application can rely on theconnection to deliver all of itsdata without error and in theproper order. The sentencedescribes ( ). A flow controlB congestion-controlC reliable datatransferD connection-oriented service 32.It makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast. The sentence describes ( ). A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internetfrom entering a state of gridlock. When a packet switchbecomes congested, its bufferscan overflow and packet loss canoccur. The sentence describes( ).A flowcontrolB congestion-controlC connection-oriented serviceD reliable data transfer 34.TheInternet ’sconnection-oriented service has aname, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet ’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A InternetphoneB video conferencingC streamingmultimediaD telnet39.There are two fundamentalapproaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resourcesneeded along a path to provide for communication between the end system are reserved for theduration of the communicationsession.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’smessages use the resources ondemand, and as a consequence,may have to wait for access tocommunication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, foreach link used by the end-to-endconnection, the connection gets( ) of the link’s bandwidthfor the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rateof a circuit is equal to theframe rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch mustreceive the entire packetbefore it can begin to transmitthe first bit of the packet ontothe outbound link.A Queuing delayB Store-and-forwardtransmissionC Packet lossD Propagation45.The network that forwardspackets according to host destination addresses is called( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwardspackets according tovirtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, whichis not a kind of access network( )A residentialaccessB company accessC wirelessaccessD local access48.Suppose there is exactly onepacket switch between a sendinghost and a receiving host. The transmission rates between thesending host and the switch and between the switch and the receiving host are R 1 and R 2,respectively. Assuming that theswitch uses store-and-forwardpacket switching, what is thetotal end-to-end delay to senda packet of length L (Ignorequeuing delay, propagationdelay, and processing delay.) ( ) A L /R 1+L /R 2B L /R 1C L /R 2D none of the above49.The time required to examine thepacket ’s header and determinewhere to direct the packet ispart of the ( ). A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagatefrom the beginning of the linkto the next router is ( ). A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of3000bits over a path of 5 links. Eachlink transmits at 1000bps. Queuingdelays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is apacket-switched virtual circuitnetwork. VC setup time is seconds.Suppose the sending layers add atotal of 500 bits of header to eachpacket. How long does it take to sendthe file from source to destination(2).Suppose the network is a packet-switched datagram networkand a connectionless service is used.Now suppose each packet has 200 bitsof header. How long does it take tosend the file(3).Suppose that the network is acircuit-switched network. Furthersuppose that the transmission rate of the circuit between source anddestination is 200bps. Assumingsetup time and 200 bits of header appended to the packet, how longdoes it take to send the packetS olution:(1).t=5*(3000+500)/1000+=( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+=。
最新计算机网络英文题库(附答案)chapter1word版本

Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, andvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andvirtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuitnetworks use VC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers and virtual-circuit networksuse destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensitydecreases.C If the traffic intensity is close to zero, the average queuing delaywill be close to zero.D If the traffic intensity is close to one, the average queuing delaywill be close to one.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within theInternet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages withhosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or more communicating entities, as well as the actions taken on thetransmission and/or receipt of a message or other event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or morecommunicating entitiesB the order of messages exchanged between two or morecommunicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message orother eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP 38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2,respectively. Assuming that the switch uses store-and-forward packetswitching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.)( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s header and determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution: (1). t=5*(3000+500)/1 000+0.1=17.6s(2). t=5*(3000+200)/1 000=16s(3). t=(3000+200)/200+0.02=16.02s 相对压力一般指表压,是测量系统相对于大气压的压力值。
计算机网络(第四版)课后习题(英文)+习题答案(中英文)

ANDREW S. TANENBAUM由于请求和应答都必须通过卫星,因此传输总路径长度为和真空中的光速为300,000 公里/秒,因此最佳的传播延迟为160,000/300,000medium-speed line, a low-speed line, or no line. If it takes 100 ms of computer timeto generate and inspect each topology, how long will it take to inspect all ofthem?(E)将路由器称为A,B,C,D 和 E.则有10 条可能的线路;AB, AC, AD, AE, BC, BD, BE, CD, CE,和DE每条线路有 4 种可能性(3 速度或者不是线路),拓扑的总数为410 = 1,048,576。
检查每个拓扑需要100 ms,全部检查总共需要104,857. 6 秒,或者稍微超过29 个小时。
9. A group of 2n - 1 routers are interconnected in a centralized binary tree, with a router at each tree node. Router i communicates with router j by sending a message to the root of the tree. The root then sends the message back down to j. Derive an approximate expression for the mean number of hops per message for large n, assuming that all router pairs are equally likely.(H)这意味着,从路由器到路由器的路径长度相当于路由器到根的两倍。
计算机网络英文题库(附答案)chapter1(推荐文档)

Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, andvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andvirtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuitnetworks use VC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers and virtual-circuit networksuse destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensitydecreases.C If the traffic intensity is close to zero, the average queuing delaywill be close to zero.D If the traffic intensity is close to one, the average queuing delaywill be close to one.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within theInternet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages withhosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or more communicating entities, as well as the actions taken on thetransmission and/or receipt of a message or other event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or morecommunicating entitiesB the order of messages exchanged between two or morecommunicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message orother eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2,respectively. Assuming that the switch uses store-and-forward packetswitching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.)( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s header and determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution: (1). t=5*(3000+500)/1 000+0.1=17.6s(2). t=5*(3000+200)/1 000=16s(3). t=(3000+200)/20 0+0.02=16.02s。
计算机网络英文题库(附答案)chapter3
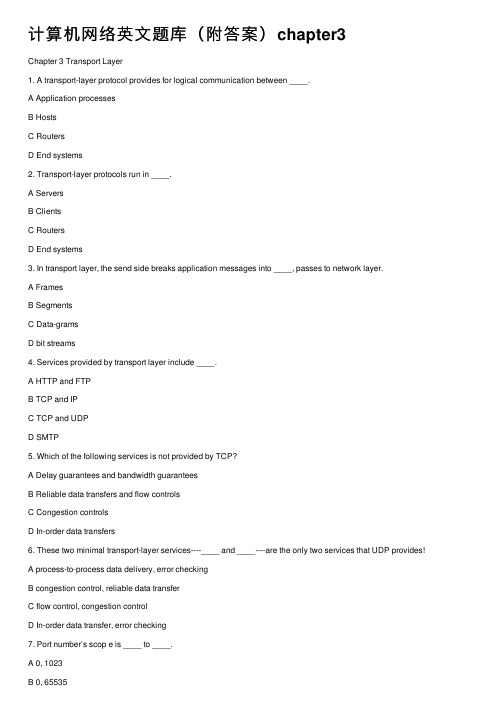
计算机⽹络英⽂题库(附答案)chapter3Chapter 3 Transport Layer1. A transport-layer protocol provides for logical communication between ____.A Application processesB HostsC RoutersD End systems2. Transport-layer protocols run in ____.A ServersB ClientsC RoutersD End systems3. In transport layer, the send side breaks application messages into ____, passes to network layer.A FramesB SegmentsC Data-gramsD bit streams4. Services provided by transport layer include ____.A HTTP and FTPB TCP and IPC TCP and UDPD SMTP5. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers6. These two minimal transport-layer services----____ and ____----are the only two services that UDP provides!A process-to-process data delivery, error checkingB congestion control, reliable data transferC flow control, congestion controlD In-order data transfer, error checking7. Port number’s scop e is ____ to ____.A 0, 1023B 0, 65535C 0, 127D 0,2558. The port numbers ranging from ____to ____ are called well-known port number and are restricted.A 0, 1023B 0, 65535C 0, 127D 0,2559. UDP socket identified by two components, they are ____.A source IP addresses and source port numbersB source IP addresses and destination IP addressesC destination IP address and destination port numbersD destination port numbers and source port numbers10. TCP socket identified by a (an) ____.A 1-tupleB 2-tupleC 3-tupleD 4-tuple11. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP12. Reliable data transfer protocol over a perfectly reliable channel is____.A rdt1.0B rdt2.0C rdt3.0D rdt2.113. Reliable data transfer protocol over a channel with bit errors and packet losses is _ ___.A rdt1.0B rdt2.0C rdt3.0D rdt2.114. Which of the following about reliable data transfer over a channel with bit errors i s not correct?A RDT2.0: assuming ACK and NAK will not be corruptedB RDT2.1: assuming ACK and NAK can be corruptedC RDT2.2: only use ACK-sD RDT2.2: use both ACK-s and NAK-s15. Which of the following protocols is not pipelining protocols?A TCPB rdt3.0C GO-BACK-ND selective repeat16. Which of the following is not correct about GBN protocol?A Only using ACK-sB Using cumulative ACK-sC Receiver discards all out-of-order packetsD It is not pipelined protocol17. Which of the following is not correct about SR protocol?A receiver individually acknowledges all correctly received packetsB sender only resends packets for which ACK not receivedC It limits sequence number of sent but un-ACK-ed packetsD It is not a pipelined protocol18. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection19. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection20. The FIN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection21.How does TCP sender perceive congestion?A Through a timeout eventB Through a receiving duplicate ACK-s eventC Both A and BD Either A or B22. Extending host-to-host delivery to process-to-process delivery is called transport-layer ____ and .A multiplexing and de-multiplexingB storing and forwardingC forwarding and filteringD switching and routing23. UDP is a ____ service while TCP is a connection-oriented service.A ConnectionlessB ReliableC Connection-orientedD In-order24. The UDP header has only four fields, they are____.A Source port number, destination port number, length and checksumB Source port number, destination port number, source IP and destination IPC source IP, destination IP, source MAC address and destination MAC addressD source IP, destination IP, sequence number and ACK sequence number25. There are two 16-bit integers: 1110 0110 0110 0110, 1101 0101 0101 0101. Their checksum is____.A 0100010001000011B 1011101110111100C 1111111111111111D 100000000000000026.The maximum amount of data that can be grabbed and placed in a segment is limited by the____.A Maximum segment size (MSS)B MTUC ChecksumD Sequence number27.The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host----the so-called____.A Maximum transmission unit (MTU)B MSSC ChecksumD Sequence number28. A File size of 500,000bytes, MSS equals 1000bytes. When we want to transmit this file with TCP, the sequence number of the first segment is 0, and the sequence number of the second segment is ____.A 1000B 999C 1001D 50000029.Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide____.A Cumulative acknowledgementsB Selective acknowledgementsC 3 duplicate ACKsD positive ACKs30. Provided α=0.125, current value of Estimated-RTT is 0.4s, Sample-RTT is 0.8s, then the new value of Estimated-RTT is ____s.A 0.45B 0.6C 0.7D 0.831.Provided RcvBuffer=20,LastByteRcvd=20,LastByteRead=15, thenRcvWindow=____.A 14B 15C 16D 1032. TCP service does not provide____.A Reliable data transferB Flow controlC Delay guaranteeD Congestion control33. There are two states in TCP congestion control, which are ____.A slow start and congestion avoidanceB safe start and congestion avoidanceC slow start and congestion abandonD safe start and congestion abandon34. The transport-layer protocol provides logical communication between ____, and the network-layer protocol provides logical communication ____.A hosts, processesB processes, hostsC threads, processesD processes, threads35. To implement the multicast services the Internet employs the ____ protocol.A FTPB TCPC IGMPD UDP36. If an application developer chooses ____ protocol, then the application process is almost directly talking with IP.A HTTPB RIPC CSMA/CDD UDP37. ____ maintains connection-state in the end systems. This connection state includes receive and send buffers, congestion-control parameters, and sequence and acknowledgment number parameters.A UDPB TCPC DNSD HTTP38. The host that initiates the session in the Internet is labeled as ____.A serverB user agentC clientD router39. With TCP there is no _____ between sending and receiving transport-layer entities.A flow controlB handshakingC. congestion control D VC setup40. The Internet’s ____service helps prevent the Internet from entering a state of gridlock.A datagramB congestion controlC sliding windowD timeout event41. Connection setup at the transport layer involves ____.A serverB only the two end systemsC clientD router42. A ____layer protocol provides for logical communication between applications.A transportB applicationC networkingD MAC43. In static congestion window, if it satisfies W*S/R > RTT + S/R, the Latency is ____.A W*S/R – ( RTT+ S/R)B 2RTT + O/RC 2RTT + O/R + (k-1)[W* S/R- (RTT + S/R)]D 2RTT + S/R44. The receive side of transport layer reassembles segments into messages, passes to ____layer.A ApplicationB NetworkingC PhysicalD MAC45. In the following four options, which one is correct?A The variations in the SampleRTT are smoothed out in the computation of the EstimatedRTTB The timeout should be less than the connection’s RTTC Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≥1 secD Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then the current value of TimeoutInterval will necessarily be≤1 sec46. The port number used by HTTP is ____.A 80B 25C 110D 5347. The port number used by SMTP is ____.A 80B 25C 110D 5348. The port number used by pop3 is ____.A 80B 25C 110D 5349. The port number used by DNS is ____.A 80B 25C 110D 5350. The port number used by FTP is ____.A 20 and 21B 20C 21D 5351. A UDP socket identified by a ____ tuple(s).A 2B 4C 1D 352. A TCP socket identified by a ____ tuple(s).A 2B 4C 1D 353. A TCP socket does not include____.A Source MAC addressB Source port numberC Destination IP addressD Destination port number54. Which of following about UDP is not correct.A It is a reliable data transfer protocolB It is connectionlessC no handshaking between UDP sender, receiverD it is a best effort service protocol55. DNS uses ____ service.A TCPB UDPC Both TCP and UDPD None of above56. Which of following about UDP is correct?A Finer application-level control over what data is sent, and whenB No connection establishment (which can add delay), so no delay for establish a connectionC No connection state (so, UDP can typically support many active clients)D Large packet header overhead (16-B)57. Streaming media uses a ____ service normally.A TCPB UDPC Both TCP and UDPD None of above58. The UDP header has only ____ fields.A 2B 4C 1D 359. Which of the following does not included in UDP header.A Source port numberB Destination port numberC ChecksumD Sequence number60. Which of the following is not a pipelining protocol.A Rdt1.0B Go-Back-NC Selective repeatD TCP61. In the following four descriptions about MSS and MTU, which one is not correct?A The MSS is the maximum amount of application-layer data in the segmentB The MSS is the maximum size of the TCP segment including headersC The MSS is typically set by MTUD The MTU means the largest link-layer frame62. The job of gathering data chunks, encapsulating each data chunk with header information to create segments and passing the segments to the network is called ____.A multiplexingB de-multiplexingC forwardingD routing63. In the following four descriptions about the relationship between the transport layer and the network layer, which one is not correct?A The transport-layer protocol provides logical communication between hostsB The transport-layer protocol provides logical communication between processesC The services that a transport-layer protocol can provide are often constrained by the service model of the network-layer protocolD A computer network may make available multiple transport protocols64. Suppose the following three 8-bit bytes: 01010101, 01110000, 01001100. What’s the 1s complement of the sum of these 8-bit bytes?A 00010001B 11101101C 00010010D 1000100065. The following four descriptions about multiplexing and de-multiplexing, which one is correct?A A UDP socket is identified by a two-tuples consisting of a source port number and a destination port number.B If two UDP segment have different source port number, they may be directed to the same destination process.C If two TCP segments with different source port number, they may be directed to the same destination process.D If two TCP segments with same destination IP address and destination port number, they must be the same TCP connection.66. UDP and TCP both have the fields except ____.A source port numberB destination port numberC checksumD receive window67. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [nextseqnum,base+N-1] corresponds to packet that ____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged68. Which of the following about TCP is not correct?A It is a connectionless protocolB Point-to-point protocolC Reliable, in-order byte steam protocolD Pipelined protocol69. Which of the following about TCP is not correct?A It is a connectionless protocolB full duplex data transfer protocolC connection-oriented protocolD flow controlled protocol70. The maximum amount of data that can be grabbed and placed in a segment is limited by the ____.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum71. The MSS is typically set by first determining the length of the largest link-layer frame that can be sent by the local sending host (the so-called____), and then will fit into a single link-layer frame.A Maximum segment size (MSS)B MTUC Sequence numberD Check sum72. The MSS is the maximum amount of ____layer data in the segment, not the maximum size of the TCP segment including headers.A ApplicationB TransportC NetworkingD Link73. Which of the following field is not used for connection setup and teardown?A Sequence numberB TSTC SYND FIN74. ____ is the byte stream number of first byte in the segment.A Sequence numberB ACK numberC ChecksumD port number75. ____ is the byte sequence numbers of next byte expected from other side.A Sequence numberB ACK numberC ChecksumD port number76. Because TCP only acknowledges bytes up to the first missing byte in the stream, TCP is said to provide ____ acknowledgements.B SelectiveC SingleD Negative77. Fast retransmit means in the case that ____ duplicate ACK-s are received, the TCP sender resend segment before timer expires.A 3B 4C 5D 678. TCP____ means sender won’t overflow receiver’s buffer by tran smitting too much, too fast.A Flow controlB Congestion controlC Reliable data transferD Connection-oriented service79. TCP provides flow control by having the sender maintain a variable called the ____.A Receive windowB Congestion windowC Sliding windowD buffer80. How does TCP sender perceive congestion?A TimeoutB 3 duplicate ACK-sC Both A and BD None of above81. Transport protocols run in ____.A ServersB ClientsC RoutersD End systems82. Which of the following services is not provided by TCP?A Delay guarantees and bandwidth guaranteesB Reliable data transfers and flow controlsC Congestion controlsD In-order data transfers83. Which service does UDP not provide?B de-multiplexingC error-detectionD error-correction84. There are three major events related to data transmission and retransmission in the TCP sender, which one is not in it?A data received from application aboveB de-multiplexing segmentC timer timeoutD ACK receipt85. Which of the following applications normally uses UDP services?A SMTPB Streaming multimediaC FTPD HTTP86. Which of the following about TCP connection is not correct?A It is a broadcast connectionB It is a point-to-point connectionC It is a pipelined connectionD It is a full duplex connection87. The SYN segment is used for____.A TCP connection setupB TCP flow controlC TCP congestion controlD Closing a TCP connection88. Which service helps prevent the internet from entering a state of gridlock?A reliable data transferB flow controlC congestion controlD handshaking procedure89. The Internet’s _____is responsible for moving packets from one host to another.A application layerB transport layerC network layerD link layer90.In the following applications, which one is a bandwidth-sensitive application?A E-mailB web applicationC real-time audioD file transfer91. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS92. In the following four descriptions, which one is correct?A If one host’s transport layer uses TCP, then its network layer must use virtual-circuit network.B Datagram network provides connection serviceC The transport-layer connection service is implemented in the routerD The network-layer connection service is implemented in the router as well as in the end system.93.____ is a speeding-matching service---matching the rate which the sender is sending against the rate at which the receiving application is reading.A congestion controlB flow controlC sliding-window controlD variable control94. In the following four descriptions about Rcv-Window, which one is correct?A The size of the TCP RcvWindow never changes throughout the duration of the connectionB The size of the TCP RcvWindow will change with the size of the TCP RcvBufferC The size of the TCP RcvWindow must be less than or equal to the size of the TCP RcvBufferD Suppose host A sends a file to host B over a TCP connection, the number of unacknowledged bytes that A sends cannot exceed the size of the size of the RcvWindow.95. There are 6 flag fields. Which one is to indicate that the receiver should pass the data to the upper layer immediately?A PSHB URGC ACKD RST96. Suppose the TCP receiver receives the segment that partially or completely fills in gap in received data, it will ____.A immediately send ACKB immediately send duplicate ACKC wait some time for arrival of another in-order segmentD send single cumulative97. _____ imposes constrain on the rate at which a TCP sender can send traffic into the network.A sliding windowB congestion windowC receive windowD variable window98. Flow control and congestion control are same at that they all limit the rate of the sender, but differ in that ____.A flow control limits its rate by the size of RcvWindow, but congestion control by the traffic on the linkB congestion control limits its rate by the size of RcvWindow, but flow control by the traffic on the linkC flow control mainly is accomplished by the sender, but congestion control by the receiver.D flow control mainly is accomplished by the receiver, but congestion control bythe link.99. This job of delivering the data in a transport-layer segment to the correct socket is called ____.A multiplexingB de-multiplexingC forwardingD routing100. If we define N to be the window size, base to be the sequence number of the oldest unacknowledged packet, and next-seq-num to be the smallest unused sequence number, then the interval [base, nextseqnum-1] corresponds to packet that____.A can be sent immediatelyB have already been transmitted and acknowledgedC cannot be usedD have been sent but not yet acknowledged101. ____ are the two types of transport services that the Internet provides to the applications.A TCP and UDPB connection-oriented and connectionless serviceC TCP and IPD reliable data transfer and flow control102. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a responseB Each TCP connection is closed after the server sending one objectC There are two versions of persistent connection: without pipelining and with pipeliningD The default mode of HTTP uses persistent connection with pipelining103. The field of Length in UDP segment specifies the length of ____.A the UDP segment, not including the headerB the UDP segment, including the headerC the UDP segment’s headerD the Length field104. In TCP segment header, which field can implement the reliable data transfer?A source port number and destination port numberB sequence number and ACK numberC urgent data pointerD Receive window105. In the following four descriptions about TCP connection management, which one is not correct?A Either of the two processes participating in a TCP connection can end the connectionB If the FIN bit is set to 1, it means that it wants to close the connectionC In the first two step of the three-way handshake, the client and server randomly choose an initial sequence numberD In the three segments of the three-way handshake, the SYN bit must be set to 1 106. Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 42, and the second has sequence number 110. If the 1st is lost and 2nd arrives at host B. What will be the acknowledgment number?A 43B ACK42C 109D ACK1101.Consider sending an object of size O=500,000bytes from server to client. LetS=500 bytes and RTT=0.2s. Suppose the transport protocol uses static windows with window size 5. For a transmission rate of 100Kbps, determine the latency for sending the whole object. Recall the number of windows K=O/ WS), and there is K-1 stalled state (that is idle time gaps).2.Consider the following plot of TCP congestion window size as a function of time.Fill in the blanks as follow:a) The initial value of Threshold at the first transmission round is ____. b) The value of Threshold at the 11st transmission round is ____. c) The value of Threshold at the 21st transmission round is ____. d) After the 9th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKe) After the 19th transmission round, segment loss detected by ____.(A) Timeout(B) Triple duplicate ACKf) During ____ transmission round, the 18th segment is sent.3.Consider the TCP reliable data transfer in the given graph. If in Segment 1’s Sequence number =10,data=“AC”, please fill in the following blanks. a) In Segment 2, ACK number=____;b) In Segment 3, Sequence number =____; data=“0123456789”c) If there are some bits corrupted in segment 3 when it arrives Host B, then the ACK number in Segment 5 is ____; and the ACK number in Segment 6 is ____.0 00 Congestion window sizeTransmission round4. The client A wants to request a Web page from Server B. Suppose the URL of the page is 172.16.0.200/experiment, and also it wants to receive French version of object. The time-sequence diagram is shown below, please fill in the blanks.Packet① to Packet③are TCP connection’s segment, then:Packet ①: SYN flag bit= aACK flag bit= bSequence number= 92Packet ②: SYN flag bit=1ACK flag bit= c Sequence number=100 Packet ③: SYN flag bit= d ACK flag bit=1Sequence number= e5. Consider sending an object of size O=100 Kbytes from server to client. Let S=536 bytes and RTT=100msec. Suppose the transport protocol uses static windows with window size W.(1) For a transmission rate of 25 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency.(2) Repeat (1) for 100 kbps.6. Consider the following plot of TCP congestion window size as a function of time. Please fill in the blanks as below.a) The initial value of Threshold at the first transmission round is____. b) The value of Threshold at the 11th transmission round is_____. c) The value of Threshold at the 21st transmission round is_____.Congestion window sizeTransmission roundd) After the 9th transmission round, _____ occurs.e) After the 19th transmission round, ____ are detected.。
计算机网络英文题库附答案chapter定稿版

计算机网络英文题库附答案c h a p t e r精编W O R D版IBM system office room 【A0816H-A0912AAAHH-GX8Q8-GNTHHJ8】Chapter 1 Computer Networks and the Internet 1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switchednetworks, and virtual-circuit networks arepacket-switched networks.B datagram networks are packet-switchednetworks, and virtual-circuit networks arecircuit-switched networks.C datagram networks use destinationaddresses and virtual-circuit networks useVC. numbers to forward packets towardtheir destination.D datagram networks use VC. numbersand virtual-circuit networks use destinationaddresses to forward packets toward theirdestination.9.In the following options, which one is not a guided media ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct ( )A The traffic intensity must be greaterthan 1.B The fraction of lost packets increases asthe traffic intensity decreases.C If the traffic intensity is close to zero,the average queuing delay will be close tozero.D If the traffic intensity is close to one, theaverage queuing delay will be close to one.12.The Internet’s network layer isresponsible for moving network-layerpackets known as ( ) from one host toanother.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16.A LR/aB La/RC Ra/LD LR/a 17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that controlthe sending and receiving of informationwithin the Internet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks,whose hosts cannot exchange messageswith hosts outside of the private network.These private networks are often referredto as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or morecommunicating entities, as well as theactions taken on the transmission and/orreceipt of a message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messages exchangedbetween two or more communicatingentitiesB the order of messages exchangedbetween two or more communicatingentitiesC the actions taken on the transmission ofa message or other eventD the transmission signals are digitalsignals or analog signals27.In the following options, which is defined in protocol ( )A the actions taken on the transmissionand/or receipt of a message or othereventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error andin the proper order. The sentencedescribes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of aconnection overwhelms the other side bysending too many packets too fast. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from enteringa state of gridlock. When a packet switchbecomes congested, its buffers canoverflow and packet loss can occur. Thesentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP 35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP()A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packetswitching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide forcommunication between the end systemare reserved for the duration of thecommunication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use theresources on demand, and as aconsequence, may have to wait for accessto communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by theend-to-end connection, the connectiongets ( ) of the link’s bandwidth for theduration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM 44.( ) means that the switch must receive the entire packet before it can begin totransmit the first bit of the packet onto theoutbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packetsaccording to host destination addresses iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packetsaccording to virtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network()A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receivinghost. The transmission rates between thesending host and the switch and betweenthe switch and the receiving host are R1and R2, respectively. Assuming that theswitch uses store-and-forward packetswitching, what is the total end-to-enddelay to send a packet of length L (Ignorequeuing delay, propagation delay, andprocessing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine thepacket’s header and determine where todirect the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points) (1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless serviceis used. Now suppose each packet has 200 bitsof header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between sourceand destination is 200bps. Assuming 0.02s setuptime and 200 bits of header appended to the packet, how long does it take to send the packet?So lution:(1).t=5*(3000+500)/1000+0.1=17.6s( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+0.02=16.02s。
计算机网络英文题库附答案chapter1
networks use VC. numbers to forward packets toward their Chapter 1 Computer Networks and the Internet destination.thatis, a network is a worldwide computer network, that 1.The ( )Ddatagram networks use VC. numbers and virtual-circuit of computing devices throughout the world. interconnects millions networks use destination addresses to forward packets toward their ppt3destination. A public InternetB Intranet9.In the following options, which one is not a guided media ( )A twisted-pair wire C switch netfiber opticsD B television netcoaxial cable C 2.Which kind of media is not a guided media ( ) A D satellite twisted-pair copper wirea coaxial cableB 10.Processing delay does not include the time to ( ).C fiber optics A examine the packet's headerB wait to transmit the packet onto the linkdigital satellite channel DC determine where to direct the packet)3.Which kind of media is a guided media (D check bit-error in the packet A geostationary satellite11.In the following four descriptions, which one is correct ( )low-altitude satelliteB A The traffic intensity must be greater than 1. C fiber optics B The fraction of lost packets increases as the traffic intensity Dwireless LANdecreases.).The units of data exchanged by a link-layer protocol are called ( 4.C If the traffic intensity is close to zero, the average queuing delay A Frames will be close to zero.B SegmentsDIf the traffic intensity is close to one, the average queuing delayC Datagrams will be close to one.D bit streams12.The Internet's network layer is responsible for moving network-layerWhich of the following option belongs to the circuit-switched networks5.packets known as ( ) from one host to another.)( A frameA FDMB datagram B TDMC segmentVC networks C D message both A and BD13.The protocols of various layers are called ( ).)makes sure that neither side of a connection overwhelms the other( 6.A the protocol stackside by sending too many packets too fast.B TCP/IP Reliable data transfer A C ISPFlow controlB Dnetwork protocol C Congestion control 14.There are two classes of packet-switched networks: ( ) networks andDHandshaking procedurevirtual-circuit networks.) means that the switch must receive the entire packet before it can.7( A datagram begin to transmit the first bit of the packet onto the outbound link.B circuit-switched A Store-and-forward transmissionC television B FDM End-to-end connection C DtelephoneD TDM15.Access networks can be loosely classified into three categories:residential access, company access and ( ) access.8Datagram networks and virtual-circuit networks differ in that ( .).datagram networks are circuit-switched networks, and A A cabledvirtual-circuit networks are packet-switched networks.B wirelessdatagram networks are packet-switched networks, and B C campus virtual-circuit networks are circuit-switched networks.city areaDdatagram networks use destination addresses and virtual-circuitCC P2P applications 17Question 16~distributed applicationsDRSuppose, a is the average rate at which packets arrive at the queue, 24.The Internet provides two services to its distributed applications: atraffic then the is the transmission rate, and all packets consist of L bits, connectionless unreliable service and () service. intensity is ( 16 ), and it should no greater than ( 17 ).A flow controlLR16.A/a connection-oriented reliableBB La/R congestion control CTCPD/C RaL25.It defines the format and the order of messages exchanged betweenLRD /atwo or more communicating entities, as well as the actions taken on .17A 2the transmission and/or receipt of a message or other event. TheB1sentence describes ( ).C 0 A InternetD -1B protocol).18.In the Internet, the equivalent concept to end systems is ( C intranethosts A D networkB servers26.In the following options, which does not define in protocol ( )C clients A the format of messages exchanged between two or moreroutersD communicating entities). 19.In the Internet, end systems are connected together by ( B the order of messages exchanged between two or moreA copper wire communicating entitiescoaxial cableB C the actions taken on the transmission of a message or otherC communication links eventfiber opticsD Dthe transmission signals are digital signals or analog signals).End systems access to the Internet through its ( 20.27.In the following options, which is defined in protocol ( )A modems A the actions taken on the transmission and/or receipt of a message protocolsB or other eventISP C B the objects exchanged between communicating entitiesDsockets C the content in the exchanged messages).End systems, packet switches, and other pieces of the Internet, run ( 21 D the location of the hoststhat control the sending and receiving of information within the 28.In the following options, which does not belong to the network edgeInternet.( )A programs A end systemsB processes B routersapplications C C clientsDprotocols D serversThere are many private networks, such as many corporate and22.29.In the following options, which belongs to the network core ( )government networks, whose hosts cannot exchange messages with A end systemshosts outside of the private network. These private networks are often B routers). referred to as ( C clientsinternets A DserversB LAN30.In the following options, which is not the bundled with the Internet'sC intranets connection-oriented service ( )DWANA reliable data transfer) running on its end systems to exchange data.23The internet allows ( B guarantee of the transmission timewith each other.Cflow controlclients applications A congestion-controlDserver applicationsBA electrical current switching An application can rely on the connection to deliver all of its data.31circuit switching ).B without error and in the proper order. The sentence describes (data switching A flow control Cmessage switchingB Dcongestion-controlreliable data transfer C 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration connection-oriented serviceDof the communication session.32.It makes sure that neither side of a connection overwhelms the otherside by sending too many packets too fast. The sentence describes A packet-switchedB data-switched).(C circuit-switched A flow controlDB congestion-control message-switchedC connection-oriented service 41.In ( ) networks, the resources are not reserved; a session's messagesuse the resources on demand, and as a consequence, may have to wait reliable data transfer Dfor access to communication link.It helps prevent the Internet from entering a state of gridlock. When a33.A packet-switched packet switch becomes congested, its buffers can overflow and packetB data-switched loss can occur. The sentence describes ( ).C circuit-switched A flow controlDmessage-switched B congestion-controlC connection-oriented service 42.In a circuit-switched network, if each link has n circuits, for each linkused by the end-to-end connection, the connection gets ( ) of the D reliable data transferlink's bandwidth for the duration of the connection.34.The Internet's connection-oriented service has a name, it is ( ).A a fraction 1/n A TCPB all B UDPC 1/2 C TCP/IPDn times DIP43an to .For ( ), the transmission rate of a circuit is equal to the frame ratenot options, the .35In following which service does be providedmultiplied by the number of bits in a slot.application by TCP( )A CDMA reliable transport AB packet-switched network flow controlBC TDM C video conferencingDFDM D congestion control44)..( ) means that the switch must receive the entire packet before it can.36The Internet's connectionless service is called (begin to transmit the first bit of the packet onto the outbound link. TCP AA Queuing delay UDPBB C TCP/IP Store-and-forward transmissionC Packet loss IPDDPropagation)In the following options, which does not use TCP( 37.SMTP A 45.The network that forwards packets according to host destinationaddresses is called ( internet telephone ) network.BA C circuit-switched FTPB packet-switched HTTPDC virtual-circuit In the following options, which does not use UDP( .38 )DA Internet phone datagramB video conferencing46.The network that forwards packets according to virtual-circuit numbersis called ( ) network.streaming multimedia CA Dcircuit-switched telnetB packet-switched)39 There are two fundamental approaches to building a network core, ( .virtual-circuit Cand packet switching.D datagram=47.In the following entries, which is not a kind of access network( )A residential accessB company access wireless access Clocal accessD48.Suppose there is exactly one packet switch between a sending host anda receiving host. The transmission rates between the sending host andthe switch and between the switch and the receiving host are R and 1R, respectively. Assuming that the switch uses store-and-forward 2packet switching, what is the total end-to-end delay to send a packetof length L (Ignore queuing delay, propagation delay, and processingdelay.) ( )A L/R+L/R 21/B RL1L/C R 2none of the aboveD 49.The time required to examine the packet's header and determine whereto direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayDtransmission delay50.The time required to propagate from the beginning of the link to thenext router is ( ).A queuing delayB processing delayC propagation delayDtransmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each linktransmits at 1000bps. Queuing delays, propagation delay and processingdelay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VCsetup time is seconds. Suppose the sending layers add a total of 500 bitsof header to each packet. How long does it take to send the file from sourceto destination(2).Suppose the network is a packet-switched datagram network and aconnectionless service is used. Now suppose each packet has 200 bits ofheader. How long does it take to send the file(3).Suppose that the network is a circuit-switched network. Further supposethat the transmission rate of the circuit between source and destination is200bps. Assuming setup time and 200 bits of header appended to thepacket, how long does it take to send the packetSolution:(1).t=5*(3000+500)/1000+=(2).t=5*(3000+200)/1000=16s200+(3).t=(3000+200)/。
计算机网络英文题库(附答案)chapter

Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world. ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switchednetworks, and virtual-circuit networks arepacket-switched networks.B datagram networks are packet-switchednetworks, and virtual-circuit networks arecircuit-switched networks.C datagram networks use destinationaddresses and virtual-circuit networks useVC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers andvirtual-circuit networks use destinationaddresses to forward packets toward theirdestination.9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than1.B The fraction of lost packets increases asthe traffic intensity decreases.C If the traffic intensity is close to zero,the average queuing delay will be close tozero.D If the traffic intensity is close to one,the average queuing delay will be close toone.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control thesending and receiving of information within the Internet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messagesexchanged between two or more communicatingentities, as well as the actions taken on the transmission and/or receipt of a message orother event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged betweentwo or more communicating entitiesB the order of messages exchanged betweentwo or more communicating entitiesC the actions taken on the transmission ofa message or other eventD the transmission signals are digitalsignals or analog signals27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/orreceipt of a message or other eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’sconnection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to buildinga network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved;a session’s messages use the resources ondemand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of theconnection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( )network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and thereceiving host are R1 and R2, respectively.Assuming that the switch uses store-and-forward packet switching, what is the total end-to-end delay to send a packet of length L? (Ignorequeuing delay, propagation delay, andprocessing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s headerand determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution:?(1) .?t=5*(3000+500)/1000+0.1=17.6s?(2). t=5*(3000+200)/1000=16s(3). t=(3000+200)/200+0.02=16.02s。
(完整版)计算机网络英文题库(附答案)chapter5
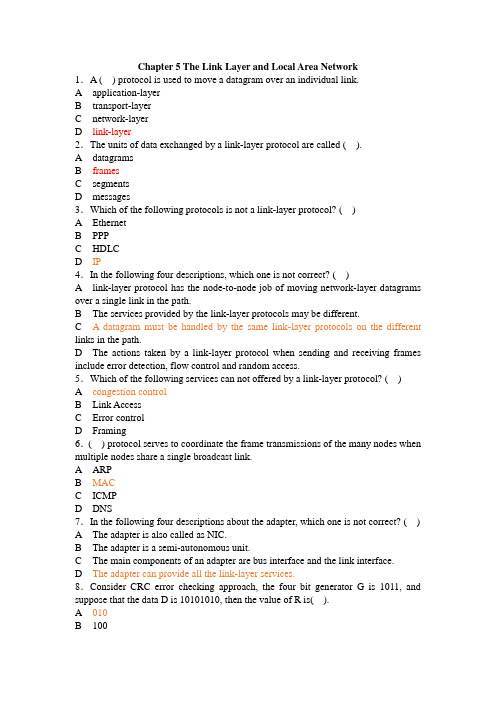
Chapter 5 The Link Layer and Local Area Network1.A ( ) protocol is used to move a datagram over an individual link.A application-layerB transport-layerC network-layerD link-layer2.The units of data exchanged by a link-layer protocol are called ( ).A datagramsB framesC segmentsD messages3.Which of the following protocols is not a link-layer protocol? ( )A EthernetB PPPC HDLCD IP4.In the following four descriptions, which one is not correct? ( )A link-layer protocol has the node-to-node job of moving network-layer datagrams over a single link in the path.B The services provided by the link-layer protocols may be different.C A datagram must be handled by the same link-layer protocols on the different links in the path.D The actions taken by a link-layer protocol when sending and receiving frames include error detection, flow control and random access.5.Which of the following services can not offered by a link-layer protocol? ( )A congestion controlB Link AccessC Error controlD Framing6.( ) protocol serves to coordinate the frame transmissions of the many nodes when multiple nodes share a single broadcast link.A ARPB MACC ICMPD DNS7.In the following four descriptions about the adapter, which one is not correct? ( )A The adapter is also called as NIC.B The adapter is a semi-autonomous unit.C The main components of an adapter are bus interface and the link interface.D The adapter can provide all the link-layer services.8.Consider CRC error checking approach, the four bit generator G is 1011, and suppose that the data D is 10101010, then the value of R is( ).A 010B 100C 011D 1109.In the following four descriptions about random access protocol, which one is not correct? ( )A I n slotted ALOHA, nodes can transmit at random time.B I n pure ALOHA, if a frame experiences a collision, the node will immediately retransmit it with probability p.C T he maximum efficiency of a slotted ALOHA is higher than a pure ALOHA.D I n CSMA/CD, one node listens to the channel before transmitting.10.In the following descriptions about MAC address, which one is not correct? ( )A T he MAC address is the address of one node’s adapter.B N o two adapters have the same MAC address.C T he MAC address doesn’t change no matter where the adapter goes.D M AC address has a hierarchical structure.11.The ARP protocol can translate ( ) into ( ). ( )A h ost name, IP addressB h ost name, MAC addressC I P address, MAC addressD broadcast address, IP address12.The value of Preamble field in Ethernet frame structure is ( )A 10101010 10101010……10101010 11111111B 10101011 10101011……10101011 10101011C 10101010 10101010……10101010 10101011D 10101010 10101010……10101010 1010101013.There are four steps in DHCP, the DHCP server can complete ( ).A DHCP server discoveryB DHCP server offersC DHCP requestD DHCP response14.In CSMA/CD, the adapter waits some time and then returns to sensing the channel. In the following four times, which one is impossible? ( )A 0 bit timesB 512 bit timesC 1024 bit timesD 1028 bit times15.The most common Ethernet technologies are 10BaseT and 100BaseT. “10” and “100” indicate( ).A the maximum length between two adaptersB the minimum length between two adaptersC the transmission rate of the channelD the transmission rate of the node16.The principal components of PPP include but not( ).A framingB physical-control protocolC link-layer protocolD network-layer protocol17.In the following four options, which service can not be provided by switch? ( )A filteringB self-learningC forwardingD optimal routing18.In the following four services, which one was be required in PPP? ( )A packet framingB error detectionC error correctionD multiple types of link19.The ability to determine the interfaces to which a frame should be directed, and then directing the frame to those interfaces is( ).A filteringB forwardingC self-learningD optimal routing20.In ( ) transmission(s), the nodes at both ends of a link may transmit packets at the same time.A full-duplexB half-duplexC single-duplexD both full-duplex and half-duplex21.Consider the data D is 01110010001, if use even parity checking approach, the parity bit is( ① ), if use odd parity checking approach, the parity bit is( ② ). ( )A ①0 ②1B ①0 ②0C ①1 ②1D ①1 ②022.In the following four descriptions about parity checks, which one is correct? ( )A Single-bit parity can detect all errors.B Single-bit parity can correct one errors.C Two-dimensional parity not only can detect a single bit error, but also can correct that error.D Two-dimensional parity not only can detect any combination of two errors, but also can correct them.23.MAC address is ( ) bits long.A 32B 48C 128D 6424.Wireless LAN using protocol ( ).A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.1125.The following protocols are belonging to multiple access protocols except for ( ).A channel partitioning protocolsB routing protocolsC random access protocolsD taking-turns protocols26.Which of the following is not belonging to channel partitioning protocols? ( )A CSMAB FDMC CDMAD TDM27.In the following four descriptions about CSMA/CD, which one is not correct? ( )A A node listens to the channel before transmitting.B If someone else begins talking at the same time, stop talking.C A transmitting node listens to the channel while it is transmitting.D With CSMA/CD, the collisions can be avoided completely.28.( ) provides a mechanism for nodes to translate IP addresses to link-layer address.A IPB ARPC RARPD DNS29.A MAC address is a ( )address.A physical-layerB application-layerC link-layerD network-layer30.Which of the following is correct? ( )A No two adapters have the same MAC address.B MAC broadcast address is FF-FF-FF-FF-FF-FF.C A portable computer with an Ethernet card always has the same MAC address, no matter where the computer goes.D All of the above31.In the following four descriptions, which one is not correct? ( )A ARP resolves an IP address to a MAC address.B DNS resolves hostnames to IP addresses.C DNS resolves hostnames for hosts anywhere in the Internet.D ARP resolves IP addresses for nodes anywhere in the Internet.32.In the LAN, ( )protocol dynamically assign IP addresses to hosts.A DNSB ARPC DHCPD IP33.DHCP protocol is a four-step process: ①DHCP request. ②DHCP ACK. ③DHCP server discovery. ④DHCP server offer(s). The correct sequence is ( )A ①②③④B ③②①④C ③④①②D ①④③②34.In the Ethernet frame structure, the CRC field is ( )bytes.A 2B 4C 8D 3235.In the Ethernet frame structure, the Data field carries the ( ).A IP datagramB segmentC frameD message36.In the following four descriptions, which one is not correct? ( )A Ethernet uses baseband transmission.B All of the Ethernet technologies provide connection-oriented reliable service to the network layer.C The Ethernet 10Base2 technology uses a thin coaxial cable for the bus.D The Ethernet 10BaseT technology uses a star topology.37.Ethernet’s multiple access protocol is ( ).A CDMAB CSMA/CDC slotted ALOHAD token-passing protocol38.In the following four descriptions about CSMA/CD, which one is not correct? ( )A An adapter may begin to transmit at any time.B An adapter never transmits a frame when it senses that some other adapter is transmitting.C A transmitting adapter aborts its transmission as soon as it detects that another adapter is also transmitting.D An adapter retransmits when it detects a collision.39.Which of the following descriptions about CSMA/CD is correct? ( )A No slots are used.B It uses carrier sensing.C It uses collision detection.D All of the above.40.The Ethernet 10BaseT technology uses( )as its physical media.A fiber opticsB twisted-pair copper wireC coaxial cableD satellite radio channel41.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( )meters.A 100B 200C 500D 1042.A ( )is a physical-layer device that acts on individual bits rather than on frames.A switchB hubC routerD gateway43.A hub is a ( )device that acts on individual bits rather than on frames.A physical-layerB link-layerC network-layerD ransport-layer44.A switch is a( )device that acts on frame.A physical-layerB link-layerC network-layerD transport-layer45.In the following four descriptions, which one is not correct? ( )A Switches can interconnect different LAN technologies.B Hubs can interconnect different LAN technologies.C There is no limit to how large a LAN can be when switches are used to interconnect LAN segments.D There is restriction on the maximum allowable number of nodes in a collision domain when hubs are used to interconnect LAN segments.46.The ability to determine whether a frame should be forwarded to some interface or should just be dropped is ( ).A f ilteringB f orwardingC s elf-learningD o ptimal routing47.Which of the following devices is not a plug and play device? ( )A hubB routerC switchD repeater48.Which of the following devices is not cut-through device? ( )A hubB routerC switchD repeater49.In the following four descriptions, which one is not correct? ( )A Switches do not offer any protection against broadcast storms.B Routers provide firewall protection against layer-2 broadcast storms.C Both switches and routers are plug and play devices.D A router is a layer-3 packet switch, a switch is a layer-2 packet switch. 50.Which device has the same collision domain? ( )A HubB SwitchC RouterD Bridge51.IEEE802.2 protocol belong to ( )layerA networkB MACC LLCD physical52.IEEE802.11 protocol defines ( )rules.A Ethernet BusB wireless WANC wireless LAND Token Bus53.In data link-layer, which protocol is used to share bandwidth? ( )A SMTPB ICMPC ARPD CSMA/CD54.When two or more nodes on the LAN segments transmit at the same time, there will be a collision and all of the transmitting nodes well enter exponential back-off, that is all of the LAN segments belong to the same( ).A collision domainB switchC bridgeD hub55.( )allows different nodes to transmit simultaneously and yet have their respective receivers correctly receive a sender’s encoded data bits.A CDMAB CSMAC CSMA/CDD CSMA/CA56.Because there are both network-layer addresses (for example, Internet IP addresses) and link-layer addresses (that is, LAN addresses), there is a need totranslate between them. For the Internet, this is the job of ( ).A RIPB OSPFC ARPD IP57.PPP defines a special control escape byte, ( ). If the flag sequence, 01111110 appears anywhere in the frame, except in the flag field, PPP precedes that instance of the flag pattern with the control escape byte.A 01111110B 01111101C 10011001D 1011111058.The device ( ) can isolate collision domains for each of the LAN segment.A modemB switchC hubD NIC59.In the following four descriptions about PPP, which one is not correct? ( )A PPP is required to detect and correct errors.B PPP is not required to deliver frames to the link receiver in the same order in which they were sent by the link sender.C PPP need only operate over links that have a single sender and a single receiver.D PPP is not required to provide flow control.60.In the PPP data frame, the( ) field tells the PPP receivers the upper-layer protocol to which the received encapsulated data belongs.A flagB controlC protocolD checksum61.PPP’s link-control protocols (LCP) accomplish ( ).A initializing the PPP linkB maintaining the PPP linkC taking down the PPP linkD all of the above62.The PPP link always begins in the ( ) state and ends in the ( ) state. ( )A open, terminatingB open, deadC dead, deadD dead, terminating63.For( ) links that have a single sender at one end of the link and a single receiver at the other end of the link.A point-to-pointB broadcastC multicastD all of the above64.With ( )transmission, the nodes at both ends of a link may transmit packets at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous65.With ( ) transmission, a node can not both transmit and receive at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous66.Which of the following functions can’t be implemented in the NIC? ( )A encapsulation and decapsulationB error detectionC multiple access protocolD routing67.Which of the following four descriptions is wrong? ( )A The bus interface of an adapter is responsible for communication with the adapter’s parent node.B The link interface of an adapter is responsible for implementing the link-layer protocol.C The bus interface may provide error detection, random access functions.D The main components of an adapter are the bus interface and the link interface. 68.For odd parity schemes, which of the following is correct? ( )A 011010001B 111000110C 110101110D 00011011069.( )divides time into time frames and further divides each time frame into N time slots.A FDMB TMDC CDMAD CSMA70.With CDMA, each node is assigned a different ( )A codeB time slotC frequencyD link71.Which of the following four descriptions about random access protocol is not correct? ( )A A transmission node transmits at the full rate of the channelB When a collision happens, each node involved in the collision retransmits at once.C Both slotted ALOHA and CSMA/CD are random access protocols.D With random access protocol, there may be empty slots.72.PPP defines a special control escape byte 01111101. If the data is b1b201111110b3b4b5, the value is( )after byte stuffing.A b1b20111110101111110b3b4b5B b1b20111111001111101b3b4b5C b5b4b30111111001111101b2b1D b5b4b30111110101111110b2b173.MAC address is in ( ) of the computer.A RAMB NICC hard diskD cache74.Which of the following is wrong? ( )A ARP table is configured by a system administratorB ARP table is built automaticallyC ARP table is dynamicD ARP table maps IP addresses to MAC addresses75.NIC works in ( )layer.A physicalB linkC networkD transport76.In LAN, if UTP is used, the common connector is( ).A AUIB BNCC RJ-45D NNI77.The modem’s function(s) is(are) ( ).A translates digital signal into analog signalB translates analog signal into digital signalC both translates analog signal into digital signal and translates digital signal into analog signalD translates one kind of digital signal into another digital signal78.( )defines Token-Ring protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.279.( )defines Token-Bus protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.280.( ) defines CSMA/CD protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.281.The computer network that concentrated in a geographical area, such as in a building or on a university campus, is ( )A a LANB a MANC a WAND the Internet82.The MAC address is ( ) bits long.A 32B 48C 128D 25683.Which of the following four descriptions about MAC addresses is wrong? ( )A a MAC address is burned into the adapter’s ROMB No two adapters have the same addressC An adapter’s MAC address is dynamicD A MAC address is a link-layer address84.Which of the following four descriptions about DHCP is correct? ( )A DHCP is C/S architectureB DHCP uses TCP as its underlying transport protocolC The IP address offered by a DHCP server is valid foreverD The DHCP server will offer the same IP address to a host when the host requests an IP address85.The ( )field permits Ethernet to multiplex network-layer protocols.A preambleB typeC CRCD destination MAC address86.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( ) meters.A 50B 100C 200D 50087.An entry in the switch table contains the following information excepts for ( )A the MAC address of a nodeB the switch interface that leads towards the nodeC the time at which the entry for the node was placed in the tableD the IP address of a node88.Consider the 4-bit generator , G is 1001, and suppose that D has the value 101110000. What is the value of R?89.Consider the following graph of the network. Suppose Host A will send a datagram to Host B, Host A run OICQ on port 4000, Host B run OICQ on port 8000. All of ARP tables are up to date. Enumerate all the steps when message “Hello” is sent from host A to host B.。
计算机网络英文题库

计算机网络英文题库(附答案)c h a p t e r2(总17页) -本页仅作为预览文档封面,使用时请删除本页-Chapter 2 Application Layer1. In the following four descriptions, which one is correctA In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2. In the context of a communication session between a pair of process, the process that initiates the communication is labeled as the , the process that waits to be contacted to begin the session is labeled as the .A client process, server processB sending process, receiving processC input process, output processD communicating process, connecting process3. A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant applicationA E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive applicationA E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’t guarantee .A delivery of all data without errorB delivery of all data in the proper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDPA E-mailB web applicationC file transferD DNS8. In the following descriptions about HTTP, which one is not correctA HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9. Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining, the total response timeis .A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is .A 200B 301C 400D 5051~5 CACDC 6~10 CDABD11. The port number of web application is .A 25B 20C 80D 5312. A network entity that satisfies HTTP requests on the behalf of an origin web server is .A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correctA The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCP connections to transfer a file, there are .A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correctA FTP is p2p architecture.B FTP sends its control information out-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16. In the commands of FTP, which one does not have parameterA USERB PASSC LISTD STOR17. The Internet mail system has three components which they are .A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means .A Request succeeded.B The requested document doesn’t exit on this server.C This is a generic error code indicating that the request could not be understood by the server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is .A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP place s all of the message’s objects into one message, and SMTP sends every object one by one.D HTTP requires each message to be in 7-bit ASCII format, and SMTP doesn’t impose this restriction.20. The headers in the MIME message must include except .A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB 16~20 DDBBD21. In the following protocol, which one is statelessA POP3B SMTPC FTPD IMAP22. DNS means .A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except .A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except .A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25. There are three architectures for locating content in P2P file sharing, KaZaA uses .A Centralized Directory (Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity (p141)D Incentive Priorities26. There are three architectures for locating content in P2P file sharing, Napster uses .A Centralized Directory (p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27. The following architectures in P2P file sharing, which is an overlay networkA Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server and then back to the client is .A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29. Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not usedA HTTPB SMTPC POP3D IMAP30. In the four following options, which protocol is included in Mail Access ProtocolA SMTPB DHCPC IMAPD FTP31. In FTP commands, is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIME Content-Type is .A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33. In the four following options, which application is organized as hybrid of C/S and P2P architectureA E-mailB OICQC File transferD Web application34. In the four following options, which is not a centralized DNS design’s problemA a single point of failureB traffic volumeC distant centralized databaseD slow (maintenance)35.In the following options, from the application developer’s perspective, which is not correctA the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not includedA the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37. In the following options about C/S architecture, which is not correctA In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38. are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its .A socketB programC clientD peer40. Which one is not defined by an application-layer protocolA the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are .A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42. takes for a small packet to travel from client to server and then back to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses .A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields, there are .A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection is close, it specifies .A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sending the requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means .A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47. is a network entity that satisfies HTTP requests on the behalf of an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correctA A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the header line.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If –Referenced-Since50. FTP uses two parallel connections to transfer a file, they are .A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51. In FTP commands, which one is used to ask the server to send back a list of all files in the current remote directoryA USERB PASSC LISTD RETR52. In the Internet mail system, allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are .A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to .A transfer mail from the recipient’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail fr om the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are .A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNSA Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are .A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58. In the following four options about POP3, which one is not correctA The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to create remote folders and assign messages to folders.59. A resource record in DNS distributed database is a four-tuple, which field can be ignored(p132) A Name B Value C Type D TTL 60. In the following four options about DNSresource record, which one is correctA The meaning of Name and Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A, then Name is a domain and Value is the IP address for the hostname.D If Type=MX, then Name is domain and Value is the IP address for the hostname.61. In the following four options about DNS messages, which one is not correctA There are only two kinds of DNS message.(p133)B Both query and reply message have the same format.C The header section in DNS message has 12 bytes.D The authority section contains the resource records for the same that was originally queri ed.62. In DNS message, contains information about the query that is being made.(p133)A authority sectionB question sectionC answer sectionD additional section63. There are three techniques are employed in most any P2P file-sharing systems, which one is not include (p144)A Request queuingB incentive prioritiesC parallel downloadingD Response queuing64. In the following four options about P2P file-sharing, which one is not correctA P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software, documents and images.65. In MIME header lines, specifies the name of the SMTP server that sent the message (f rom),the name of the SMTP server that received the message (by), and the time an which the rec eiving server received the message.A ReceivedB FromC ToD MIME-Version66. If the header line Connection is close, it means that the client wants .A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method, but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri. 08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be .A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00 GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options, which one is not the part of cookie technologyA Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user’s end system and managed by the user’s browser.C A network entity that satisfies HTTP requests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP, can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to .A programsB threadsC socketsD channels72. In the following four options about network architecture, which one is not correctA The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized over special server.73. In Client-Server architecture, the clients visit the server’s through .A client’s socketB client’s IP addressC server’s socketD server’s IP address74. can be thought of as a program that is running within end system.A processB threadC socketD context75. API means .A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76. One host can be running many network applications, so the system assigns them differentto distinguish each other.A IP addressB port numberC hostnameD section77. In the following four applications, which one is both bandwith-sensitive and require tight timing constraintsA real-time audioB file transferC E-mailD Web documents78. The port number of the Web server is .A 25B 20C 80D 808079. The port number of the mail server is .A 25B 20C 80D 808080. Look the URL the object’s path name is .A B /rjxy/ D81. Each URL has components, they are .A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Suppose the URL of the page is /somedir/. The client does not want to use persistent connections and want to receive French version of the object. The user agent is Windows NT . Give the request message according to the given format.Request line:Header lines:2. Telnet into a Web server and send a multiline request message. Include in the request message the If-modified-since: header line to force a response message with the 304 Not Modified status code.Solution:Request line:Header lines:3. Suppose within you Web browser you click on a link to obtain a Web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1,…,RTT n. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like。
计算机网络英文题库(附答案)chapter1

Chapter 1 Computer Networks and the Internet 1.The The ( ( ) ) is is is a a a worldwide worldwide worldwide computer computer computer network, network, network, that that that is, is, is, a a a network network network that that interconnects millions of computing devices throughout the world. ppt3 A public Internet B Intranet C switch net D television net 2.Which kind of media is not a guided media? ( ) A twisted-pair copper wire B a coaxial cable C fiber optics D digital satellite channel 3.Which kind of media is a guided media? ( ) A geostationary satellite B low-altitude satellite C fiber optics D wireless LAN 4.The units of data exchanged by a link-layer protocol are called ( ). A Frames B Segments C Datagrams D bit streams 5.Which of the following option belongs to the circuit-switched networks? ( ) A FDM B TDM C VC networks D both A and B 6.( )makes sure that that neither neither neither side side side of of of a a a connection overwhelms connection overwhelms the the other other side by sending too many packets too fast. A Reliable data transfer B Flow control C Congestion control D Handshaking procedure 7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link. A Store-and-forward transmission B FDM C End-to-end connection D TDM 8.Datagram networks and virtual-circuit networks differ in that ( ). A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks. B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks. C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination. D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( ) A twisted-pair wire B fiber optics C coaxial cable D satellite 10.Processing delay does not include the time to ( ). A examine the packet ’s header B wait to transmit the packet onto the link C determine where to direct the packet D check bit-error in the packet 11.In the following four descriptions, which one is correct? ( ) A The traffic intensity must be greater than 1. B The fraction of lost packets increases as the traffic intensity decreases. C If the traffic intensity is close to zero, the average queuing delaywill be close to zero. D If the traffic intensity is close to one, the average queuing delay will be close to one. 12.The The Internet Internet Internet’’s s network network network layer layer layer is is is responsible responsible responsible for for for moving moving moving network-layer network-layer packets known as ( ) from one host to another. A frame B datagram C segment D message 13.The protocols of various layers are called ( ). A the protocol stack B TCP/IP C ISP D network protocol 14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks. A datagram B circuit-switched C television D telephone 15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access. A cabled B wireless C campus D city area Question 16~17 Suppose, a is the average rate at which packets arrive at the queue, R is the the transmission transmission transmission rate, rate, rate, and and and all all all packets packets packets consist consist consist of of L bits, bits, then then then the the the traffic traffic intensity is ( 16 ), and it should no greater than ( 17 ). 16. A LR /aB La /RC Ra /L D LR /a 17.A 2 B 1 C 0 D -1 18.In the Internet, the equivalent concept to end systems is ( ). A hosts B servers C clients D routers 19.In the Internet, end systems are connected together by ( ). A copper wire B coaxial cable C communication links D fiber optics 20.End systems access to the Internet through its ( ). A modems B protocols C ISP D sockets 21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within the Internet. A programs B processes C applications D protocols 22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ). A internets B LANC intranets D W AN 23.The internet allows ( ) running on its end systems to exchange data with each other. A clients applications B server applications C P2P applications D distributed applications 24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service. A flow control B connection-oriented reliable C congestion control D TCP 25.It defines the format and the order of messages exchanged between twoor more communicating entities, as well as the actions taken on the transmission and/or receipt of a message or other event. The sentence describes ( ). A Internet B protocol C intranet D network 26.In the following options, which does not define in protocol? ( ) A the format of messages exchanged between two or more communicating entities B the order of messages exchanged between two or more communicating entities C the actions taken on the transmission of a message or other evenD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( ) A the actions taken on the transmission and/or receipt of a message oother event B the objects exchanged between communicating entities C the content in the exchanged messages D the location of the hosts 28.In the following options, which does not belong to the network edge( ) A end systems B routers C clients D servers 29.In the following options, which belongs to the network core? ( ) A end systems B routers C clients D servers 30.In the following options, which is not the bundled with the Internet ’s connection-oriented service? ( ) A reliable data transfer B guarantee of the transmission time C flow control D congestion-control 31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ). A flow control B congestion-control C reliable data transfer D connection-oriented service 32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ). A flow control B congestion-control C connection-oriented service D reliable data transfer 33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ). A flow control B congestion-control C connection-oriented service D reliable data transfer 34.The Internet ’s connection-oriented service has a name, it is ( ). A TCP B UDP C TCP/IP D IP 35.In In the the the following following following options, options, options, which which which service service service does does does not not not be be be provided provided provided to to to an an application by TCP?( ) A reliable transport B flow control C video conferencing D congestion control 36.The Internet ’s connectionless service is called ( ). A TCP B UDP C TCP/IP D IP 37.In the following options, which does not use TCP?( ) A SMTP B internet telephone C FTP D HTTP 38.In the following options, which does not use UDP?( ) A Internet phone B video conferencing C streaming multimedia D telnet 39.There are two fundamental approaches to building a network core, ( ) and packet switching. A electrical current switching B circuit switching C data switching D message switching 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration ofthe communication session. A packet-switched B data-switched C circuit-switched D message-switched 41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link. A packet-switched B data-switched C circuit-switched D message-switched 42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of the link link’’s bandwidth for the duration of the connection. A a fraction 1/n B all C 1/2 D n times 43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot. A CDMA B packet-switched network C TDM D FDM 44.( ) means that the switch must receive the entire packet before it canbegin to transmit the first bit of the packet onto the outbound link. A Queuing delay B Store-and-forward transmission C Packet loss D Propagation 45.The network that forwards packets according to host destination addresses is called ( ) network. A circuit-switched B packet-switched C virtual-circuit D datagram 46.The network that forwards packets according to virtual-circuit numbers is called ( ) network. A circuit-switched B packet-switched C virtual-circuit D datagram 47.In the following entries, which is not a kind of access network?( ) A residential access B company access C wireless access D local access 48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R 1 and R 2, respectively. Assuming that the switch uses store-and-forward packet switching, what is the total end-to-end delay to send a packet of length L ? (Ignore queuing delay, propagation delay, and processing delay.) ( )A L /R 1+L /R 2 B L /R 1C L /R 2D none of the above 49.The time required to examine the packet ’s header and determine where to direct the packet is part of the ( ). A queuing delay B processing delay C propagation delay D transmission delay 50.The time required to propagate from the beginning of the link to the next router is ( ). A queuing delay B processing delay C propagation delay D transmission delay 51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits transmits at at at 1000bps. 1000bps. 1000bps. Queuing Queuing Queuing delays, delays, delays, propagation propagation propagation delay delay delay and and and processing processing delay are negligible. (6 points) (1).Suppose (1).Suppose the the the network network network is is is a a a packet-switched packet-switched packet-switched virtual virtual virtual circuit circuit circuit network. network. network. VC VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination? (2).Suppose the the network network network is is is a a a packet-switched packet-switched datagram datagram network network network and and and a a connectionless connectionless service service service is is is used. used. used. Now Now Now suppose suppose suppose each each each packet packet packet has has has 200 200 200 bits bits bits of of header. How long does it take to send the file? (3).Suppose that the network is a circuit-switched network. Further suppose that that the the the transmission transmission transmission rate rate rate of of of the the the circuit circuit circuit between between between source source source and and and destination destination destination is is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet? Solution: (1). t=5*(3000+500)/1000+0.1=17.6s(2). t=5*(3000+200)/1000=16s(3). t=(3000+200)/200+0.02=16.02s。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world. ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switchednetworks, and virtual-circuit networks arepacket-switched networks.B datagram networks are packet-switchednetworks, and virtual-circuit networks arecircuit-switched networks.C datagram networks use destinationaddresses and virtual-circuit networks useVC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers andvirtual-circuit networks use destinationaddresses to forward packets toward theirdestination.9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than1.B The fraction of lost packets increases asthe traffic intensity decreases.C If the traffic intensity is close to zero,the average queuing delay will be close tozero.D If the traffic intensity is close to one,the average queuing delay will be close toone.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control thesending and receiving of information within the Internet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messagesexchanged between two or more communicatingentities, as well as the actions taken on the transmission and/or receipt of a message orother event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged betweentwo or more communicating entitiesB the order of messages exchanged betweentwo or more communicating entitiesC the actions taken on the transmission ofa message or other eventD the transmission signals are digitalsignals or analog signals27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/orreceipt of a message or other eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’sconnection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to buildinga network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved;a session’s messages use the resources ondemand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of theconnection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( )network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and thereceiving host are R1 and R2, respectively.Assuming that the switch uses store-and-forward packet switching, what is the total end-to-end delay to send a packet of length L? (Ignorequeuing delay, propagation delay, andprocessing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s headerand determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution:?(1) .?t=5*(3000+500)/1000+0.1=17.6s?(2). t=5*(3000+200)/1000=16s(3). t=(3000+200)/200+0.02=16.02s。
